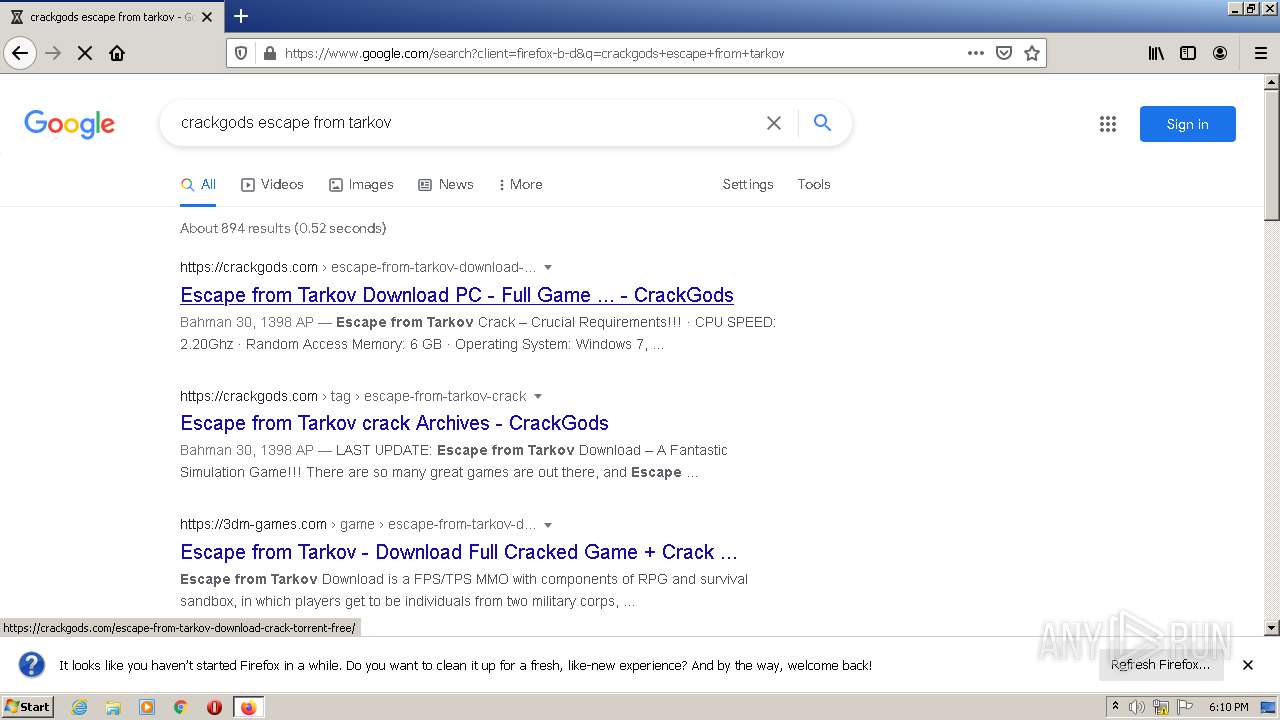
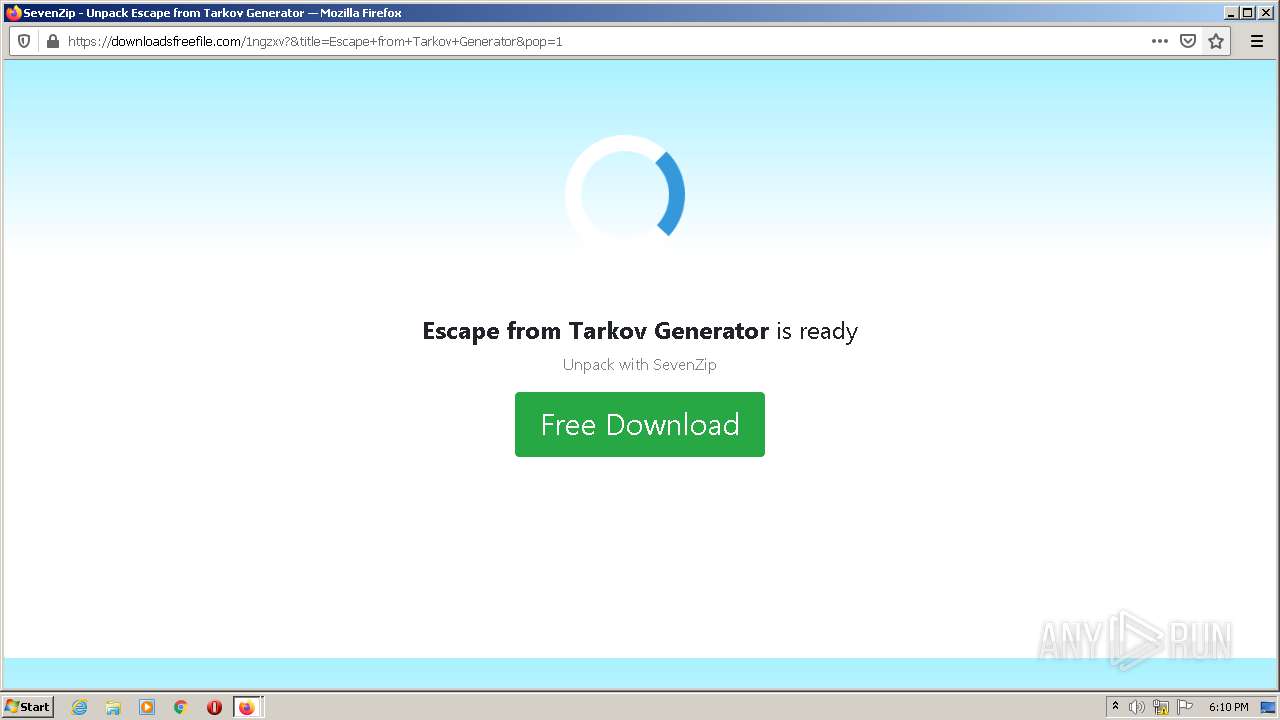
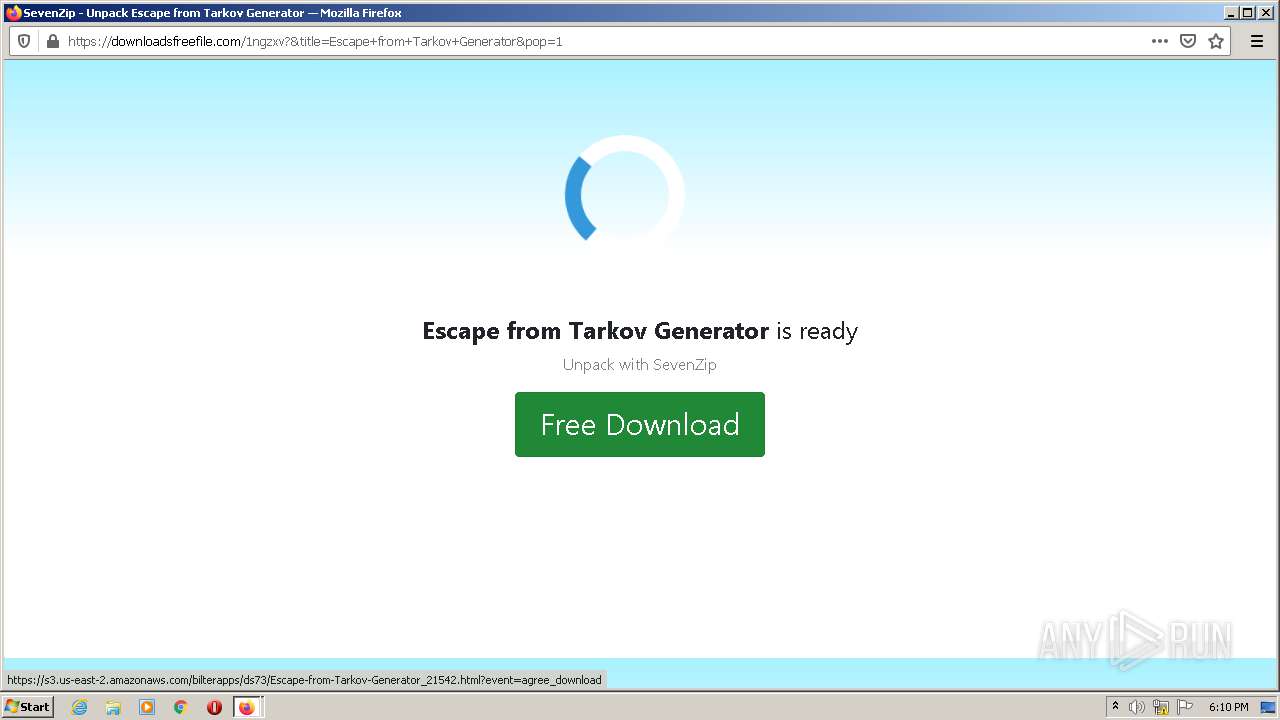
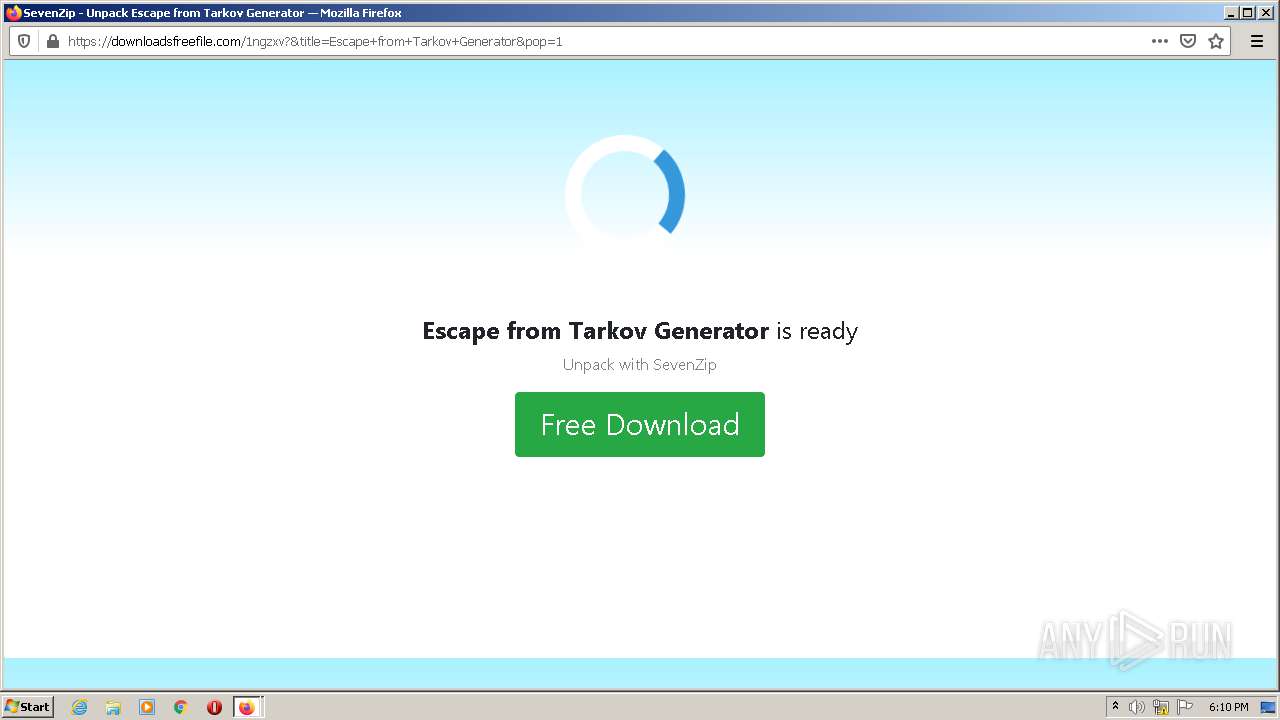
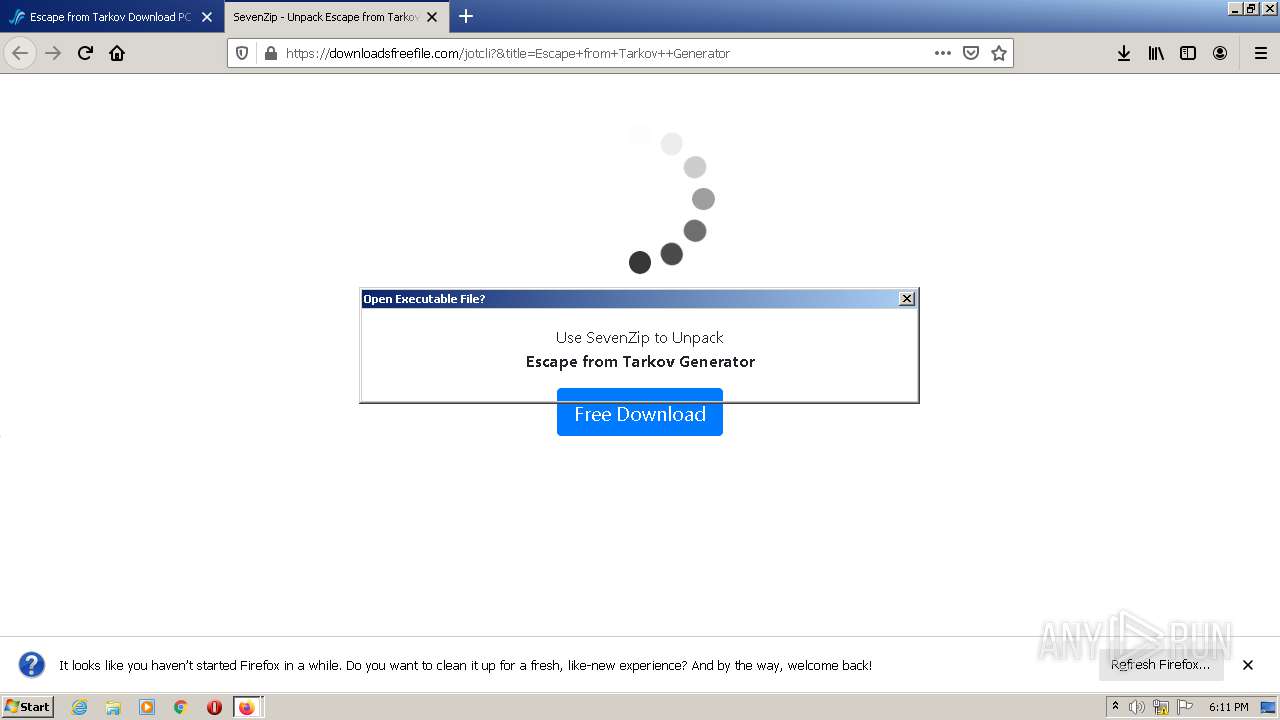
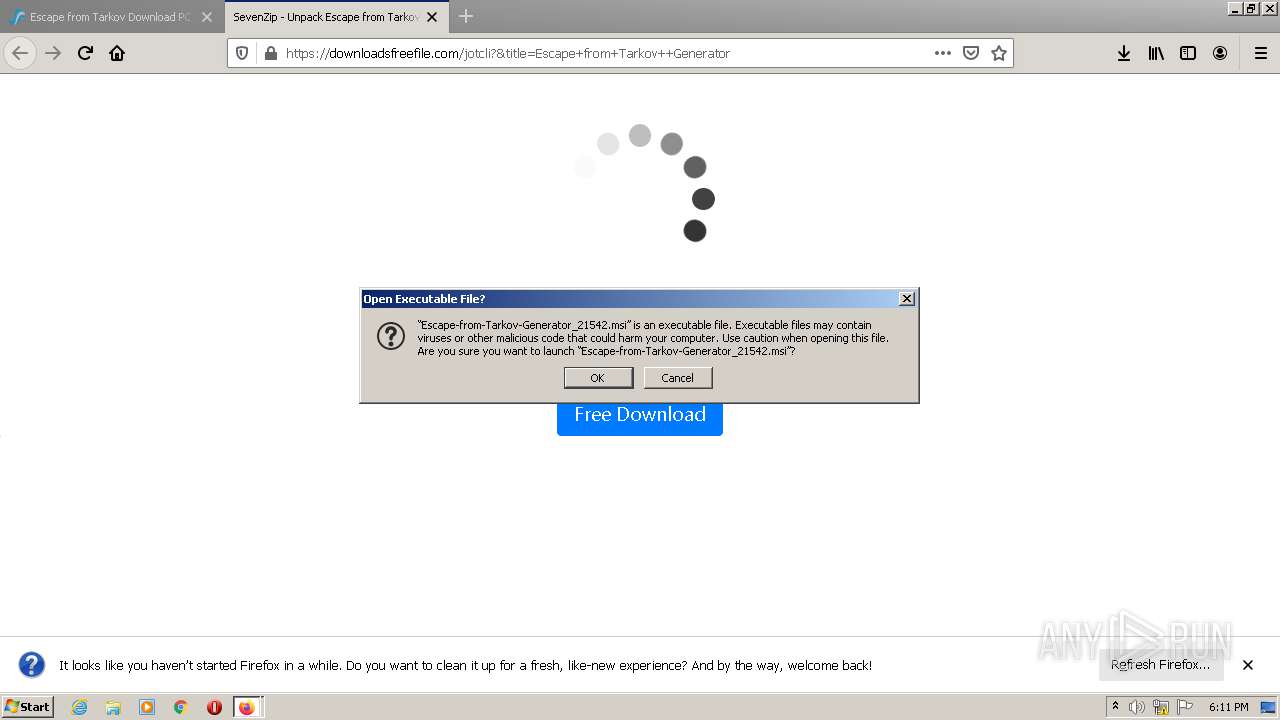
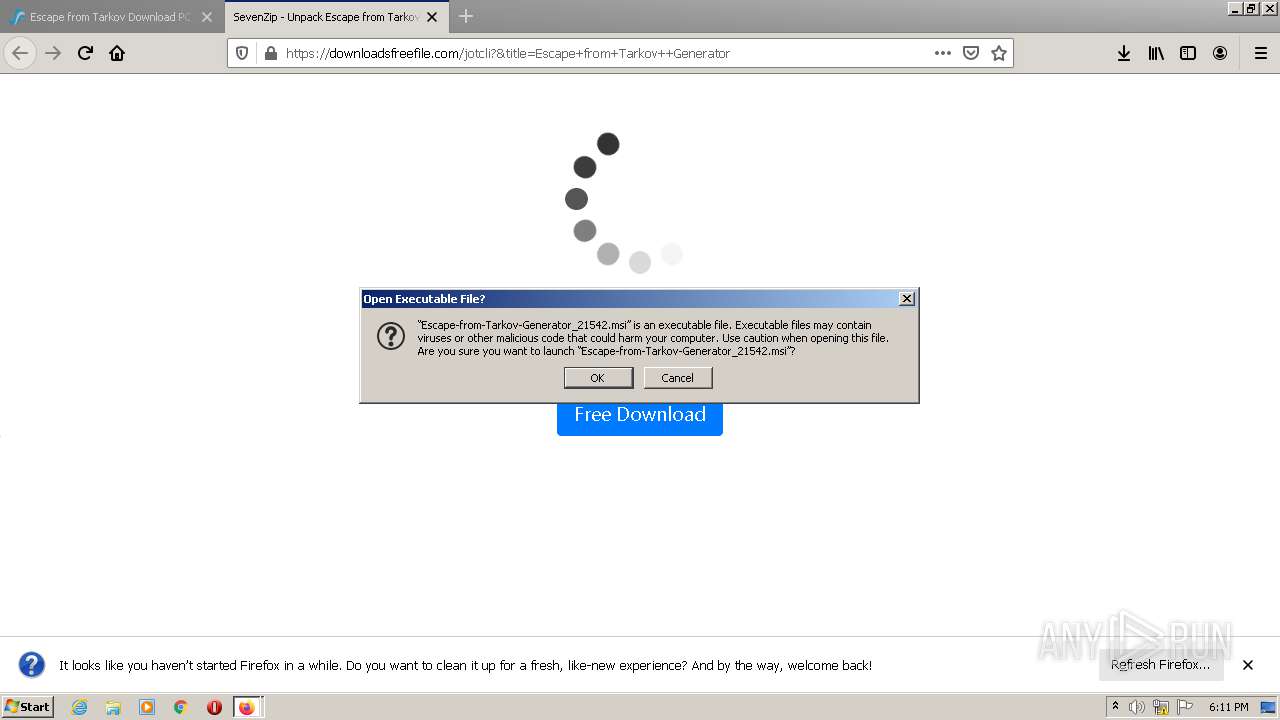
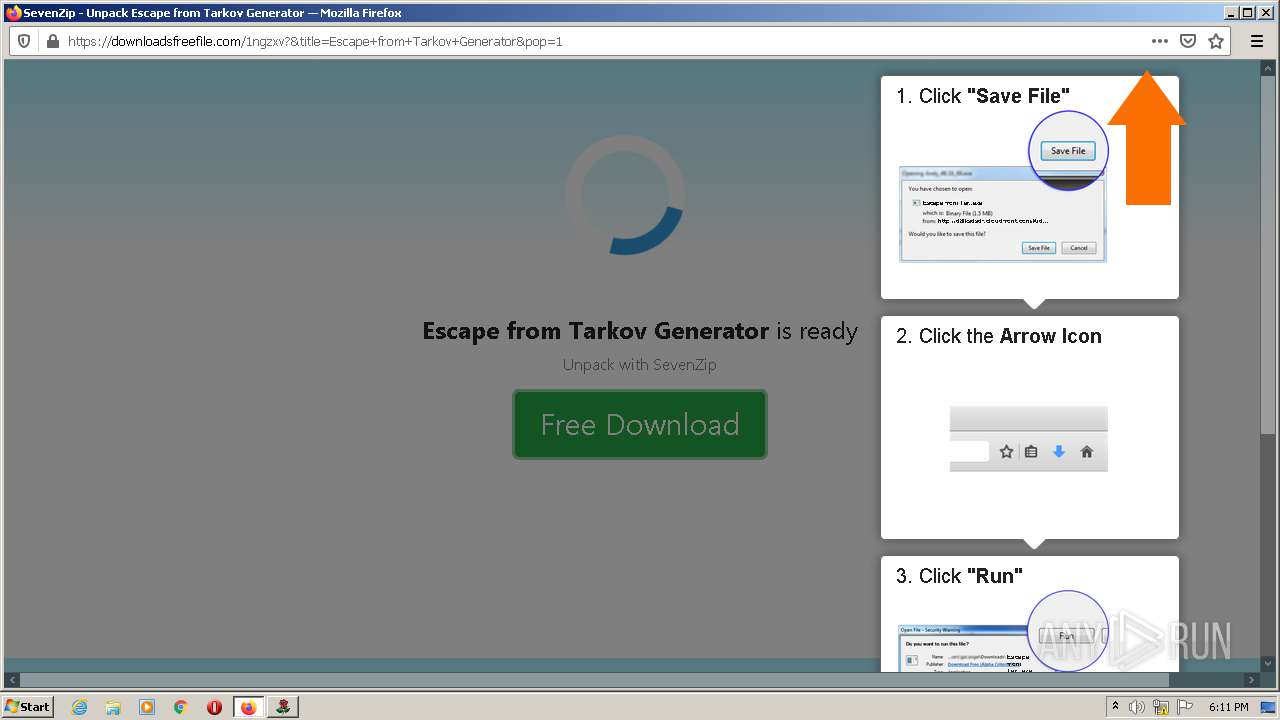
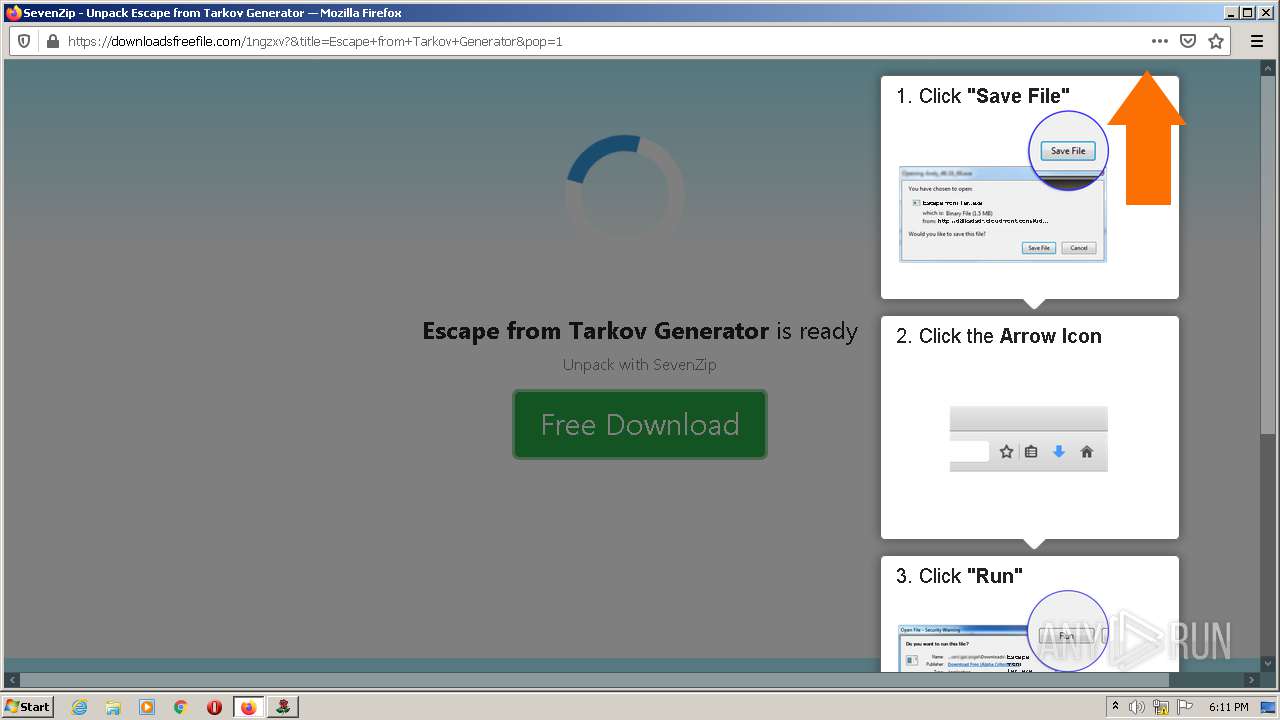
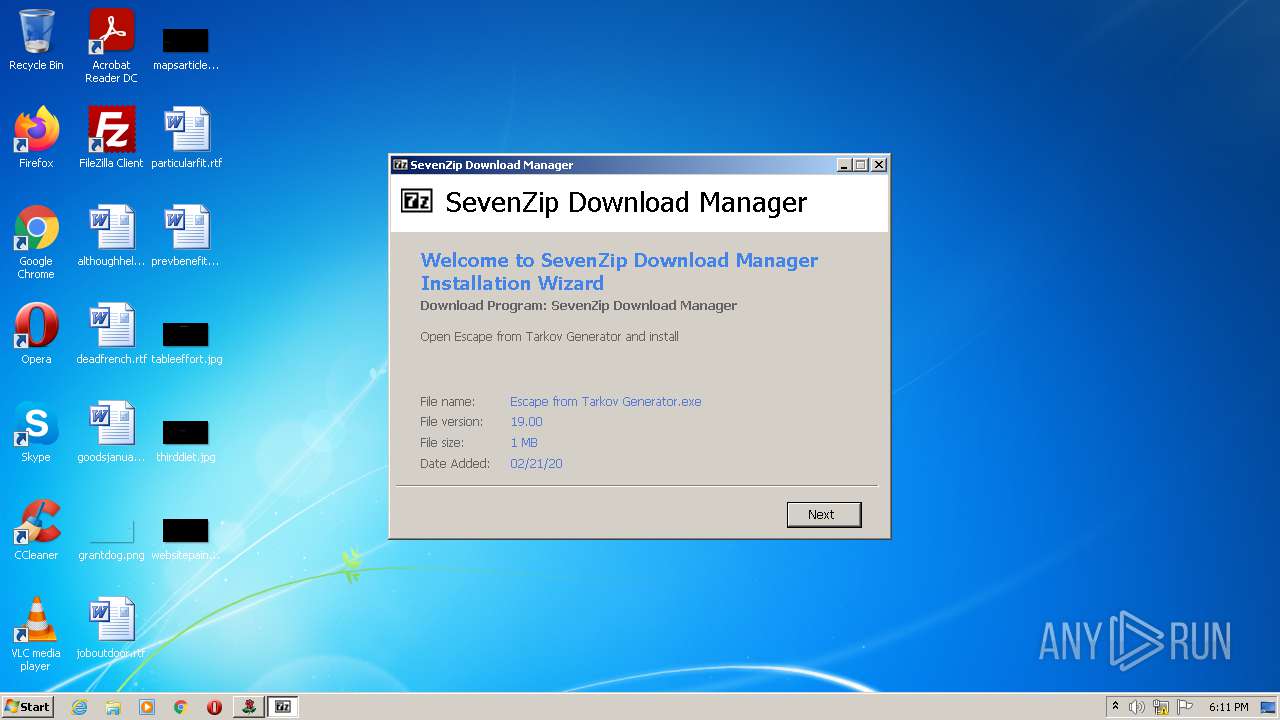
| File name: | Escape-from-Tarkov-Generator_29060.msi |
| Full analysis: | https://app.any.run/tasks/214427d2-9950-4cbe-bff2-17c815c2407e |
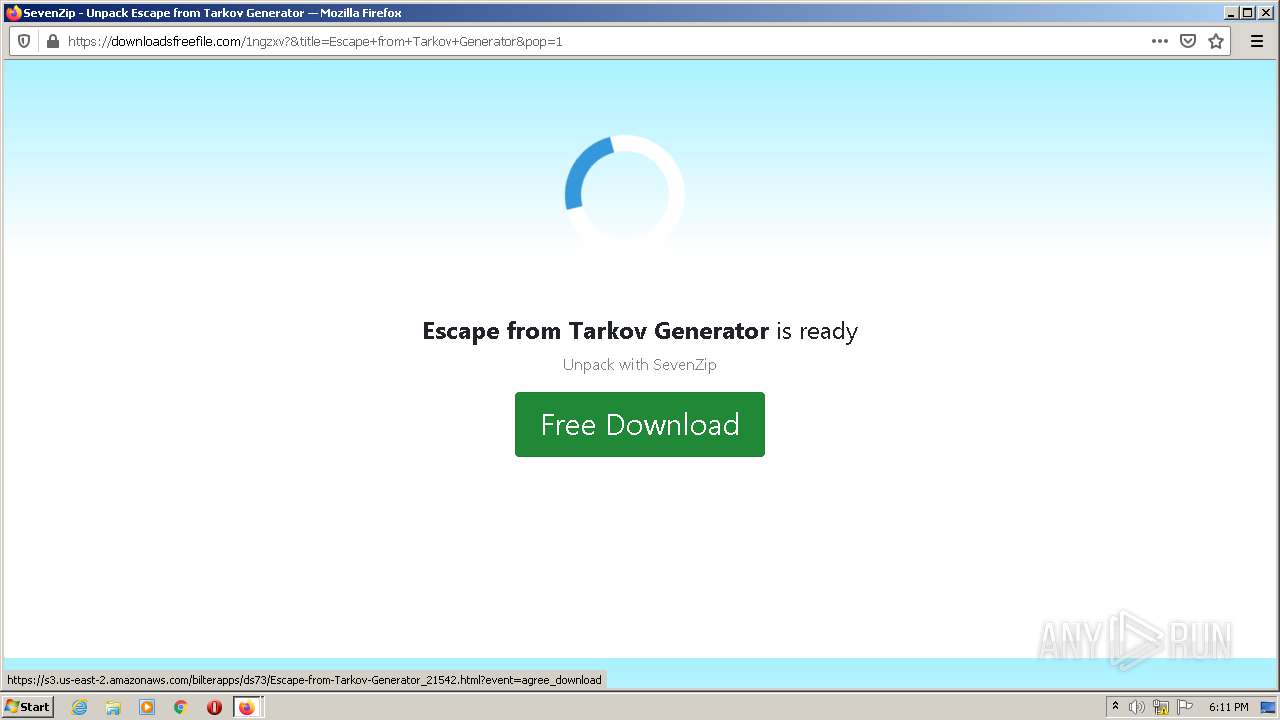
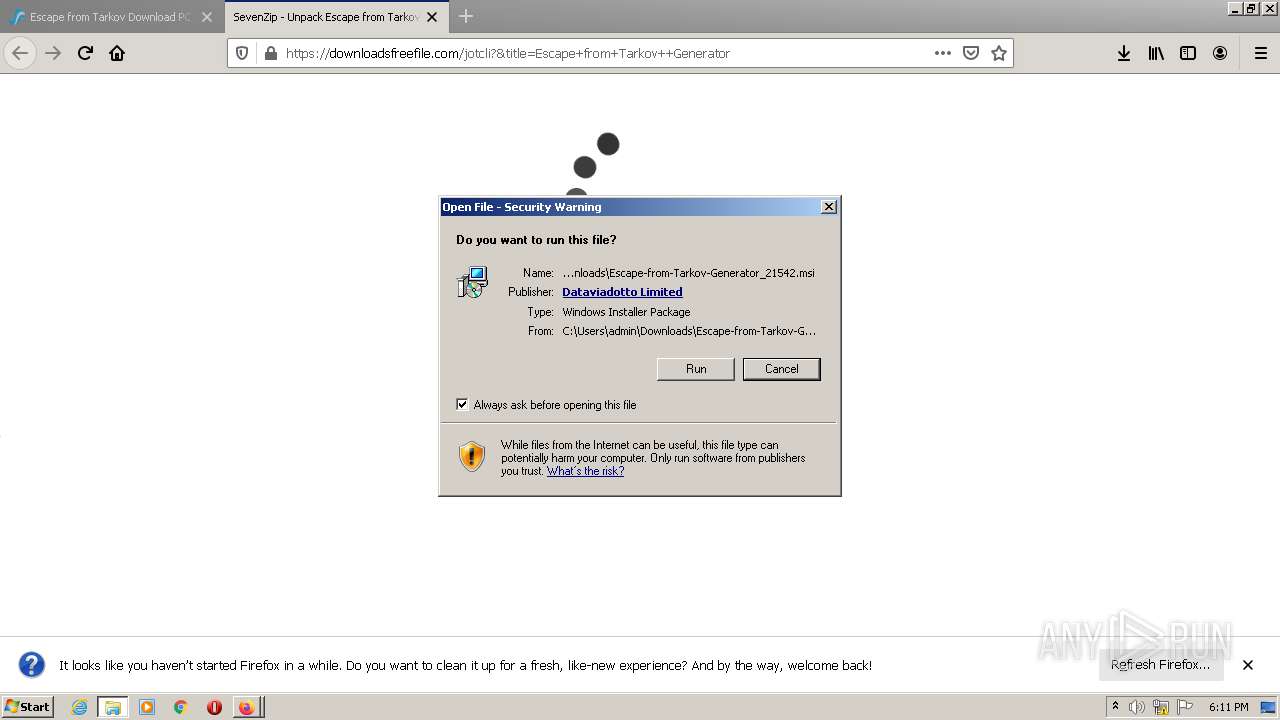
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2021, 17:09:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Original Application Setup Install, Author: Original Application Setup, Keywords: Installer, Comments: This installer database contains the logic and data required to install Original Application Setup., Template: Intel;1033, Revision Number: {2FED6AF0-36B7-478F-B752-28E974F9A211}, Create Time/Date: Tue Jun 22 10:57:58 2021, Last Saved Time/Date: Tue Jun 22 10:57:58 2021, Number of Pages: 200, Number of Words: 10, Name of Creating Application: Windows Installer XML Toolset (3.11.0.1528), Security: 2 |
| MD5: | 1D69A15E99914B7293F04BF4970B5809 |
| SHA1: | 439F40A44C35520E7C3F002C12CC03A5981B99AA |
| SHA256: | C0B9CB7EFB8784CF600286562216C0D79C0F47FE4FBF0F9BC36B5869DFA29C2E |
| SSDEEP: | 24576:ZxotmKJ0YoL1iEPYsB8ZkYEI7wFKilzD32yuogNCnFRIAA:zosm0ZsuB8ZkYD70H/3pgNCnF2AA |
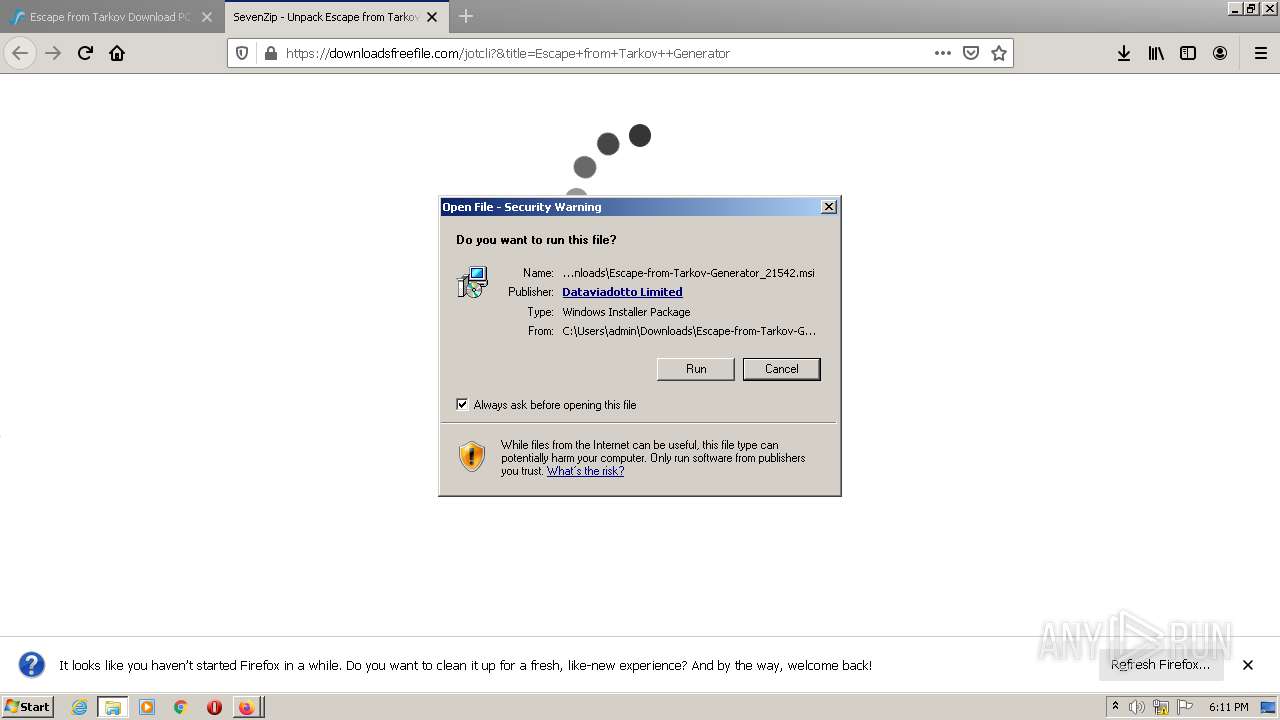
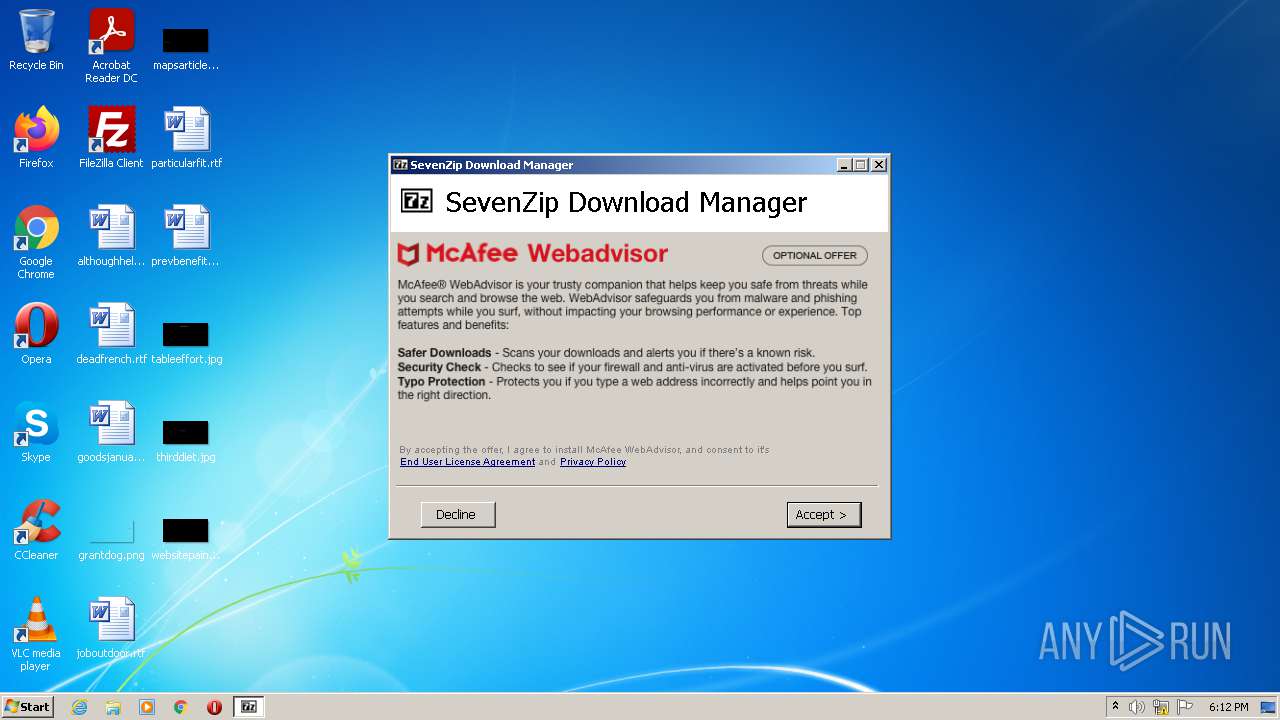
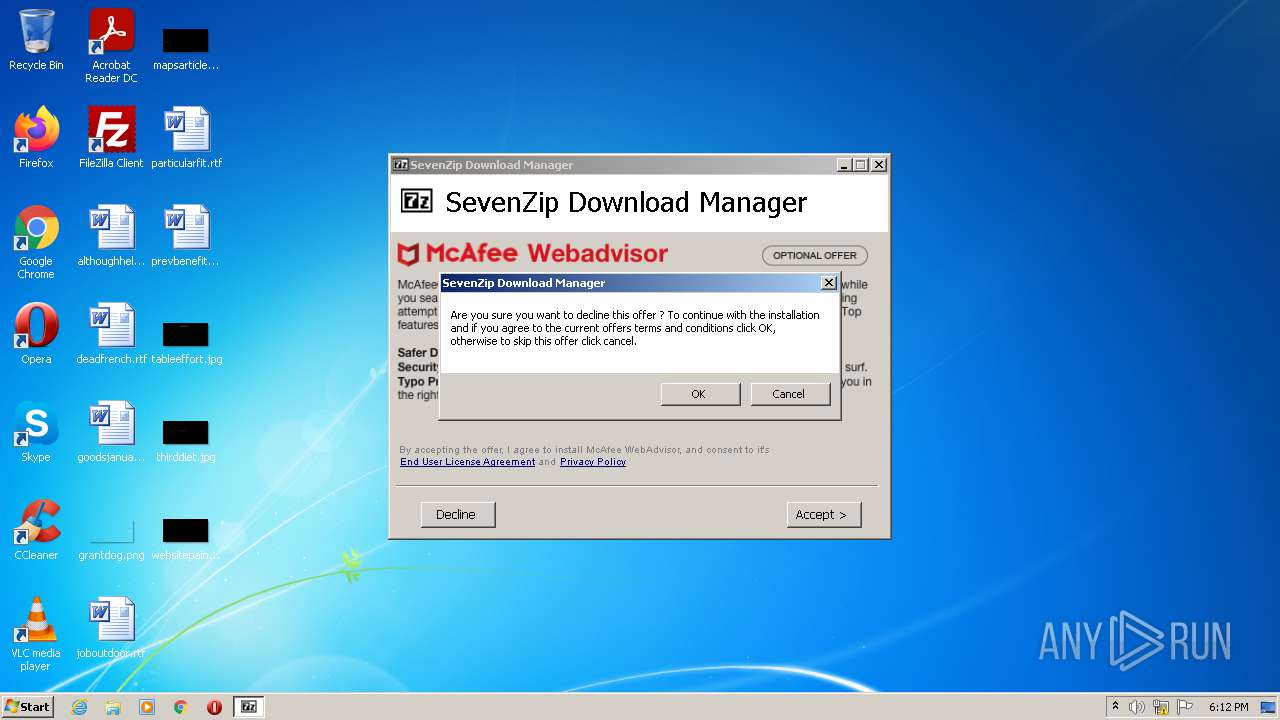
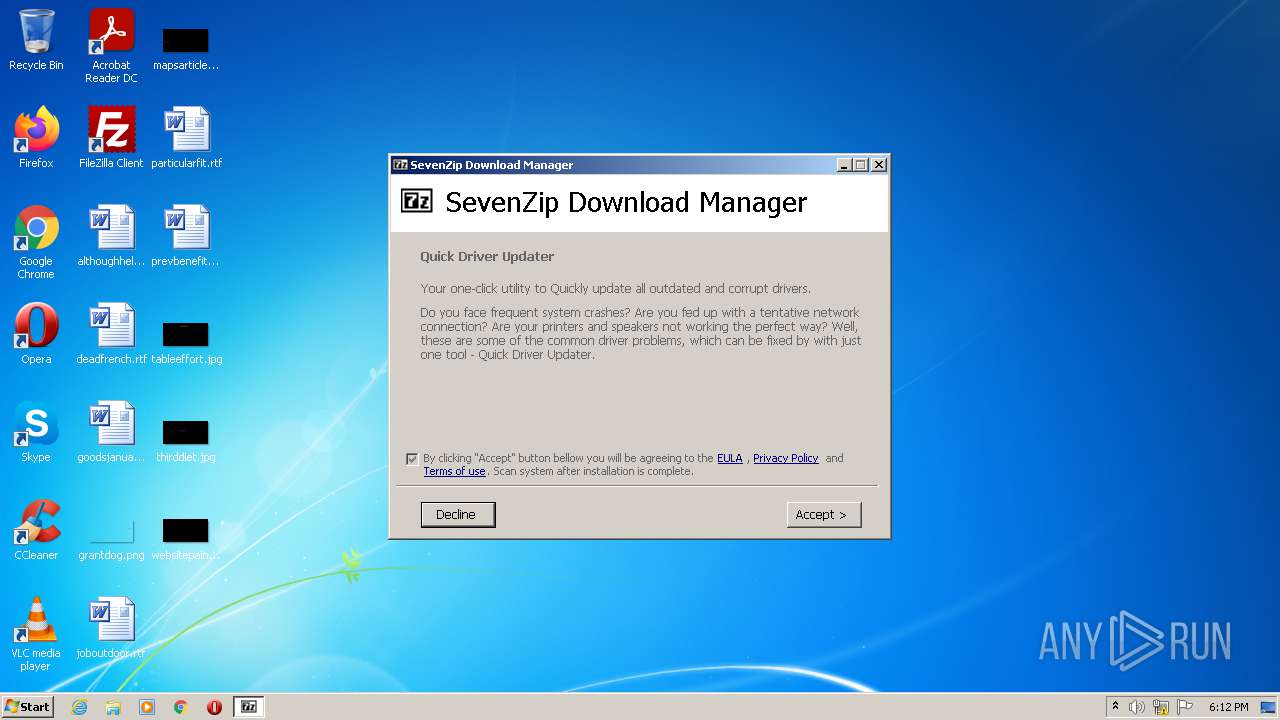
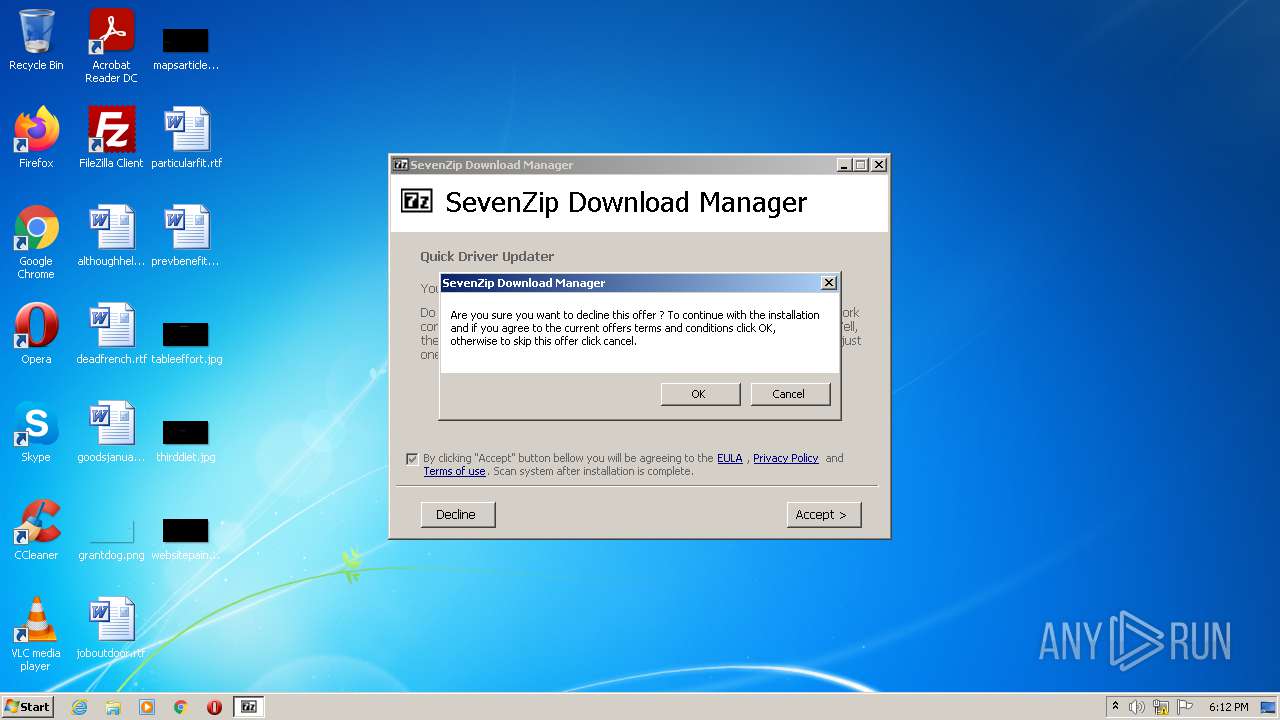
MALICIOUS
Application was dropped or rewritten from another process
- OriginalApplicationSetup.exe (PID: 2856)
- OriginalApplicationSetup.exe (PID: 1116)
- OriginalrApplication.exe (PID: 2976)
- OriginalApplicationSetup.exe (PID: 3288)
- OriginalApplicationSetup.exe (PID: 2348)
- OriginalmApplication.tmp (PID: 3352)
- saBSI.exe (PID: 3728)
Loads dropped or rewritten executable
- OriginalApplicationSetup.exe (PID: 1116)
- OriginalApplicationSetup.exe (PID: 2348)
Drops executable file immediately after starts
- OriginalrApplication.exe (PID: 2976)
Connects to CnC server
- OriginalmApplication.tmp (PID: 3352)
Changes settings of System certificates
- saBSI.exe (PID: 3728)
SUSPICIOUS
Reads the Windows organization settings
- msiexec.exe (PID: 2544)
- msiexec.exe (PID: 3004)
- OriginalrApplication.tmp (PID: 1808)
- msiexec.exe (PID: 2764)
Drops a file with a compile date too recent
- msiexec.exe (PID: 3004)
- OriginalApplicationSetup.exe (PID: 2348)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2544)
- msiexec.exe (PID: 3004)
- OriginalrApplication.tmp (PID: 1808)
- msiexec.exe (PID: 2764)
Executed as Windows Service
- msiexec.exe (PID: 3004)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3004)
- OriginalApplicationSetup.exe (PID: 1116)
- OriginalrApplication.exe (PID: 2976)
- firefox.exe (PID: 2856)
- OriginalApplicationSetup.exe (PID: 2348)
- OriginalmApplication.tmp (PID: 3352)
Checks supported languages
- OriginalApplicationSetup.exe (PID: 2856)
- cmd.exe (PID: 3788)
- OriginalApplicationSetup.exe (PID: 1116)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 1920)
- OriginalrApplication.exe (PID: 2976)
- cmd.exe (PID: 3824)
- OriginalrApplication.tmp (PID: 1808)
- cmd.exe (PID: 904)
- OriginalApplicationSetup.exe (PID: 3288)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 532)
- OriginalApplicationSetup.exe (PID: 2348)
- cmd.exe (PID: 3232)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 3996)
- OriginalmApplication.tmp (PID: 3352)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3584)
- cmd.exe (PID: 3824)
- saBSI.exe (PID: 3728)
- cmd.exe (PID: 3400)
Starts SC.EXE for service management
- cmd.exe (PID: 3788)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 1920)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 532)
- cmd.exe (PID: 3232)
- cmd.exe (PID: 3152)
Reads the computer name
- OriginalApplicationSetup.exe (PID: 2856)
- OriginalApplicationSetup.exe (PID: 1116)
- OriginalrApplication.tmp (PID: 1808)
- OriginalApplicationSetup.exe (PID: 3288)
- OriginalApplicationSetup.exe (PID: 2348)
- OriginalmApplication.tmp (PID: 3352)
- saBSI.exe (PID: 3728)
Starts CMD.EXE for commands execution
- OriginalApplicationSetup.exe (PID: 2856)
- OriginalApplicationSetup.exe (PID: 1116)
- cmd.exe (PID: 3824)
- OriginalApplicationSetup.exe (PID: 3288)
- OriginalApplicationSetup.exe (PID: 2348)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3304)
Application launched itself
- OriginalApplicationSetup.exe (PID: 2856)
- cmd.exe (PID: 3824)
- OriginalApplicationSetup.exe (PID: 3288)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 2100)
Creates a directory in Program Files
- OriginalApplicationSetup.exe (PID: 1116)
- OriginalApplicationSetup.exe (PID: 2348)
Creates files in the program directory
- OriginalApplicationSetup.exe (PID: 1116)
- saBSI.exe (PID: 3728)
- OriginalApplicationSetup.exe (PID: 2348)
Reads Environment values
- OriginalmApplication.tmp (PID: 3352)
Reads the date of Windows installation
- OriginalmApplication.tmp (PID: 3352)
Starts CMD.EXE for self-deleting
- OriginalApplicationSetup.exe (PID: 2348)
- cmd.exe (PID: 2100)
Starts application with an unusual extension
- cmd.exe (PID: 3584)
Drops a file that was compiled in debug mode
- OriginalmApplication.tmp (PID: 3352)
Adds / modifies Windows certificates
- saBSI.exe (PID: 3728)
Searches for installed software
- OriginalmApplication.tmp (PID: 3352)
INFO
Checks supported languages
- msiexec.exe (PID: 2544)
- msiexec.exe (PID: 3004)
- sc.exe (PID: 1620)
- find.exe (PID: 1228)
- sc.exe (PID: 1724)
- find.exe (PID: 3968)
- find.exe (PID: 3024)
- sc.exe (PID: 4060)
- sc.exe (PID: 3716)
- find.exe (PID: 2416)
- timeout.exe (PID: 4036)
- firefox.exe (PID: 2184)
- firefox.exe (PID: 3356)
- firefox.exe (PID: 2856)
- firefox.exe (PID: 2976)
- firefox.exe (PID: 4032)
- firefox.exe (PID: 572)
- firefox.exe (PID: 2224)
- firefox.exe (PID: 3444)
- firefox.exe (PID: 3448)
- msiexec.exe (PID: 2764)
- find.exe (PID: 3820)
- sc.exe (PID: 836)
- sc.exe (PID: 2940)
- find.exe (PID: 2944)
- sc.exe (PID: 352)
- find.exe (PID: 3724)
- sc.exe (PID: 3248)
- find.exe (PID: 4048)
- timeout.exe (PID: 3124)
Reads settings of System Certificates
- msiexec.exe (PID: 2544)
- msiexec.exe (PID: 3004)
- firefox.exe (PID: 2856)
- msiexec.exe (PID: 2764)
- OriginalmApplication.tmp (PID: 3352)
- saBSI.exe (PID: 3728)
Checks Windows Trust Settings
- msiexec.exe (PID: 2544)
- msiexec.exe (PID: 3004)
- firefox.exe (PID: 2856)
- msiexec.exe (PID: 2764)
- OriginalmApplication.tmp (PID: 3352)
- saBSI.exe (PID: 3728)
Reads the computer name
- msiexec.exe (PID: 2544)
- msiexec.exe (PID: 3004)
- sc.exe (PID: 1724)
- sc.exe (PID: 1620)
- sc.exe (PID: 3716)
- sc.exe (PID: 4060)
- firefox.exe (PID: 2856)
- firefox.exe (PID: 2976)
- firefox.exe (PID: 2184)
- firefox.exe (PID: 4032)
- firefox.exe (PID: 572)
- firefox.exe (PID: 2224)
- firefox.exe (PID: 3448)
- firefox.exe (PID: 3444)
- msiexec.exe (PID: 2764)
- sc.exe (PID: 836)
- sc.exe (PID: 2940)
- sc.exe (PID: 352)
- sc.exe (PID: 3248)
Application was dropped or rewritten from another process
- OriginalrApplication.tmp (PID: 1808)
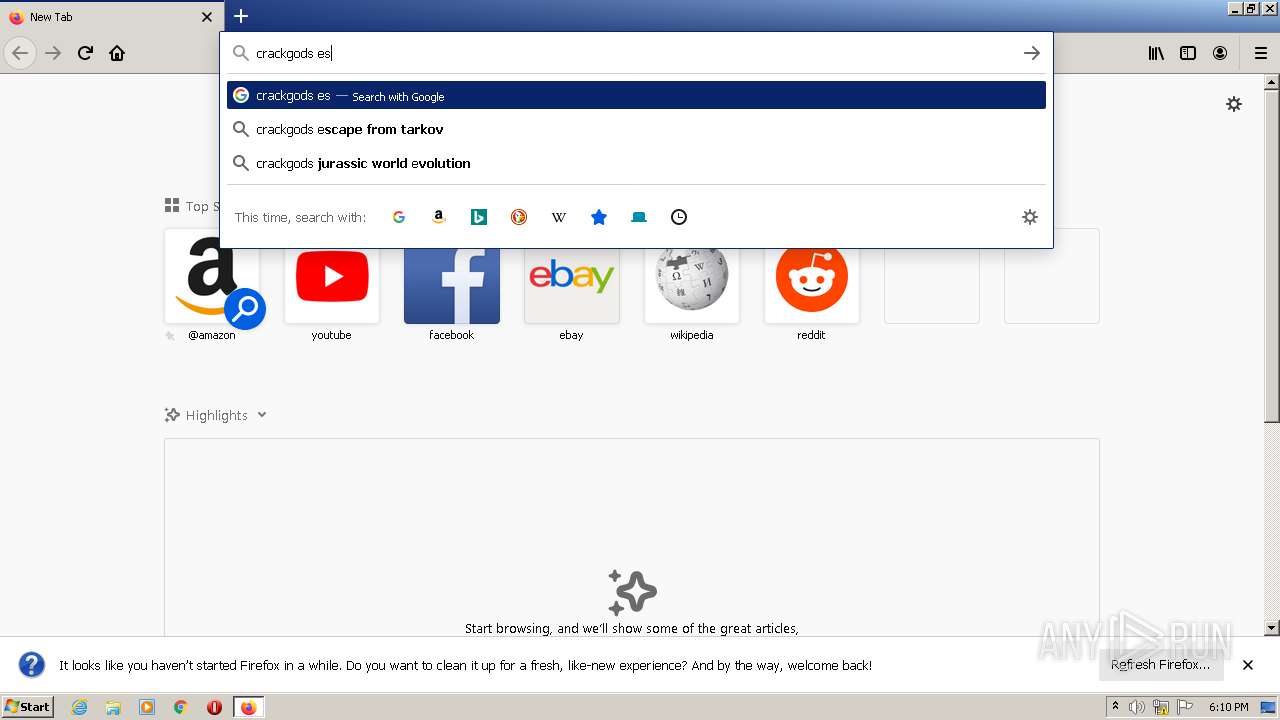
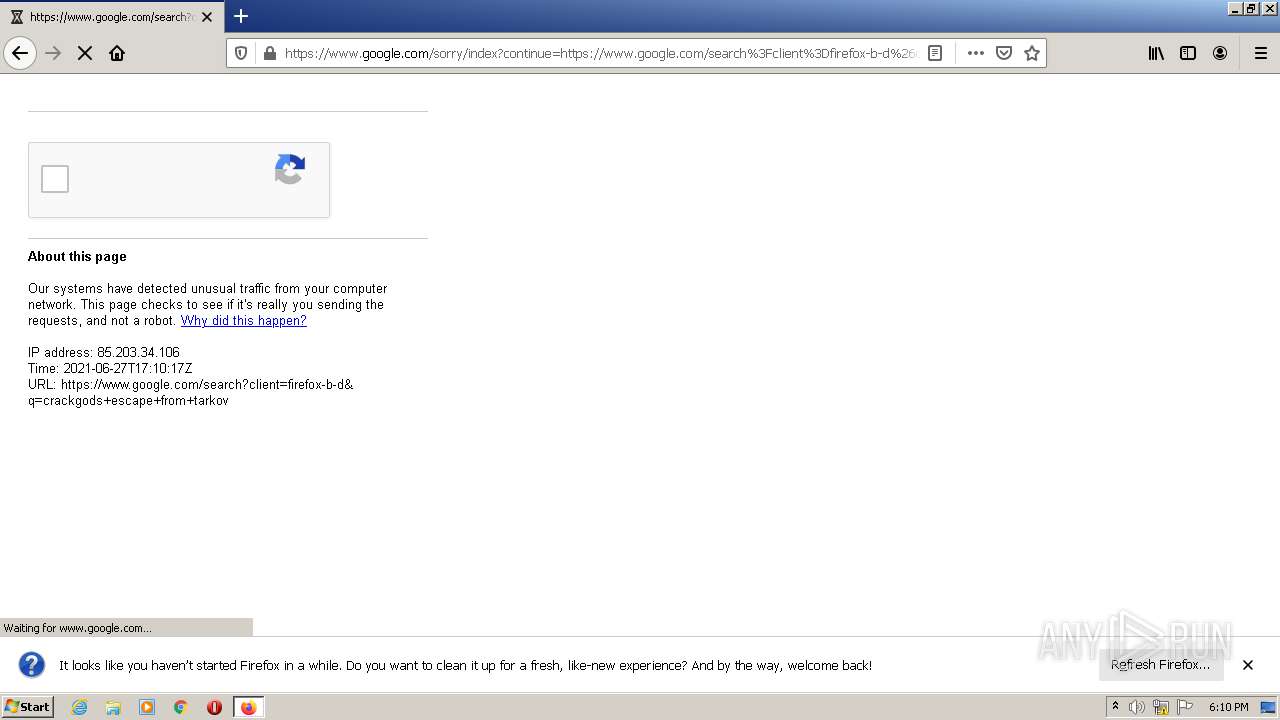
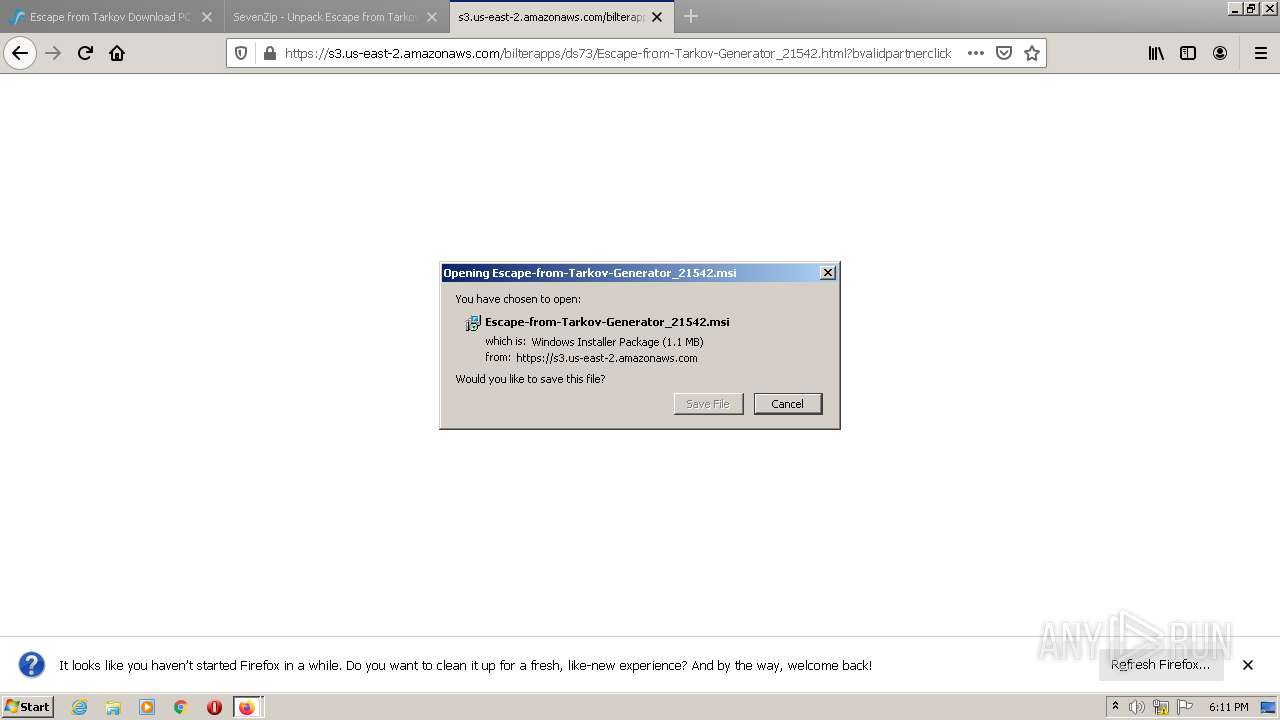
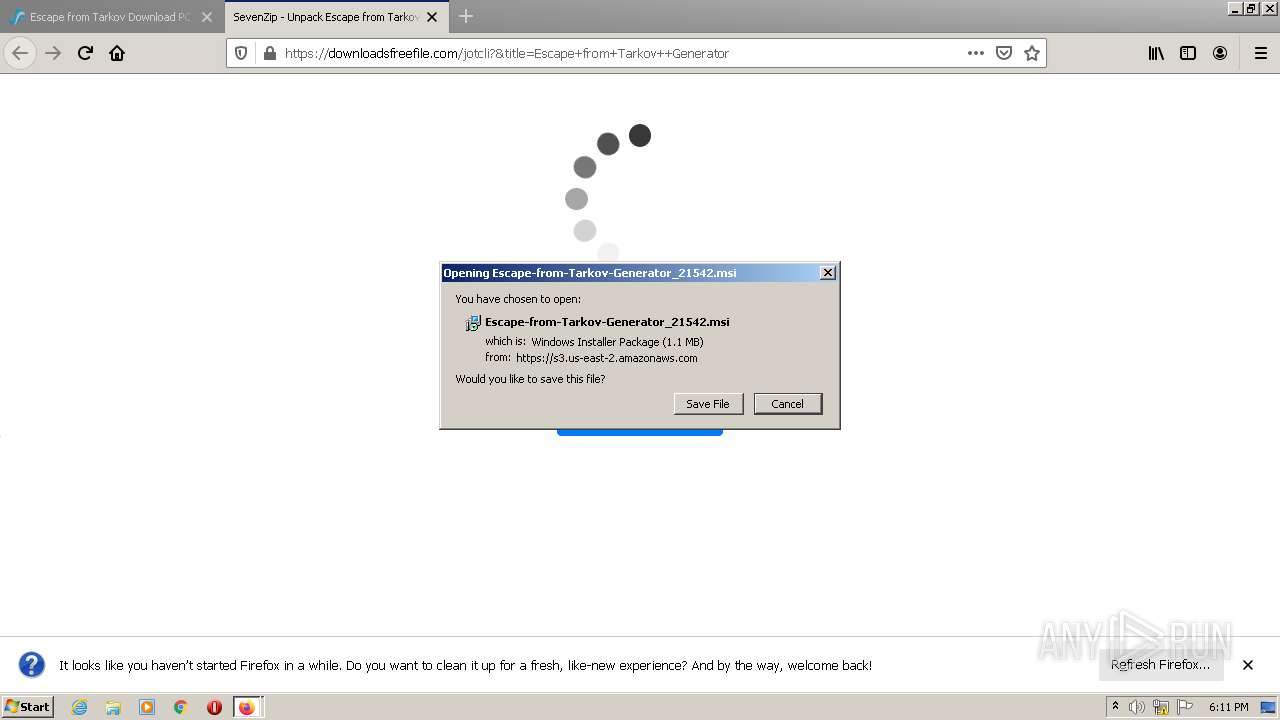
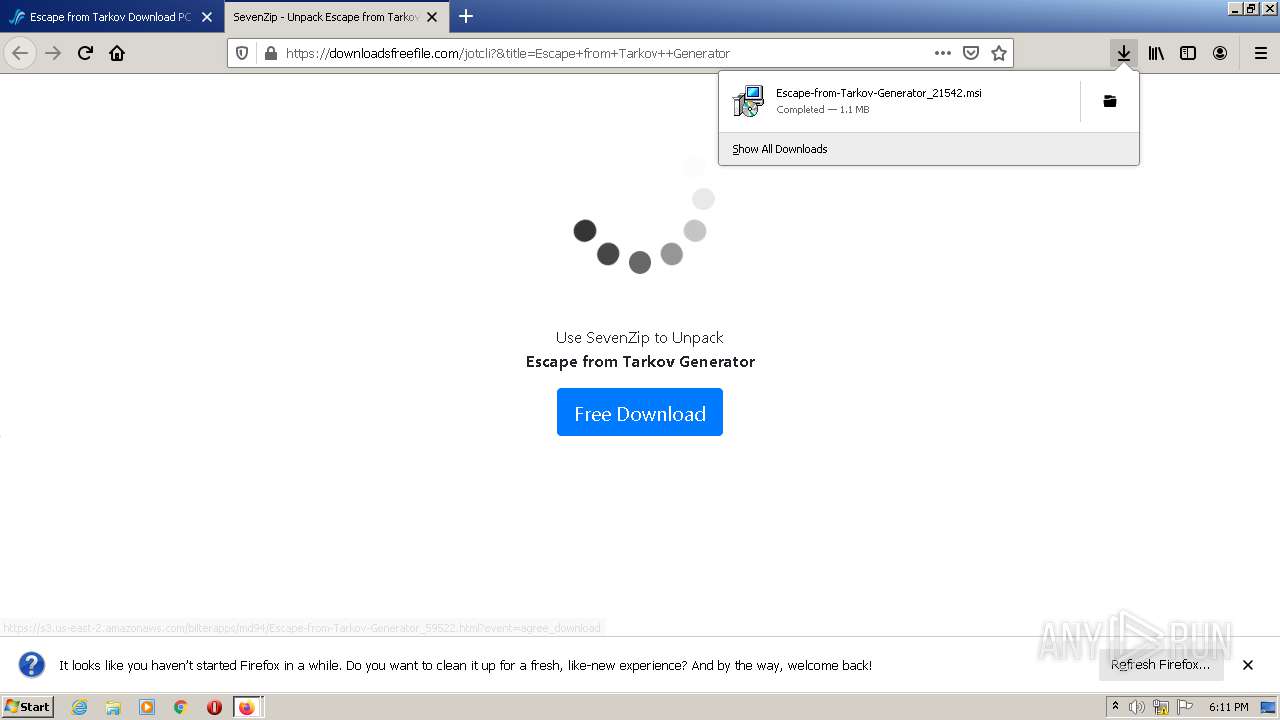
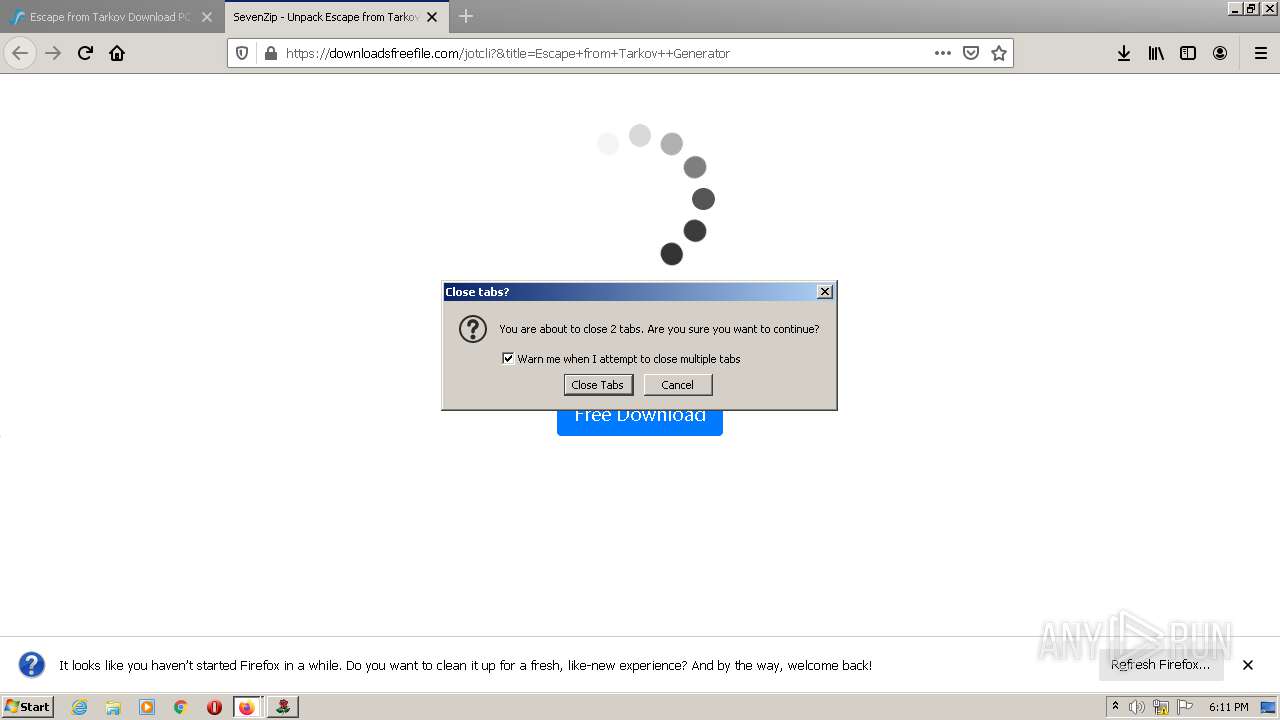
Manual execution by user
- firefox.exe (PID: 3356)
- msiexec.exe (PID: 2764)
Reads CPU info
- firefox.exe (PID: 2856)
Application launched itself
- firefox.exe (PID: 3356)
- firefox.exe (PID: 2856)
Creates files in the program directory
- firefox.exe (PID: 2856)
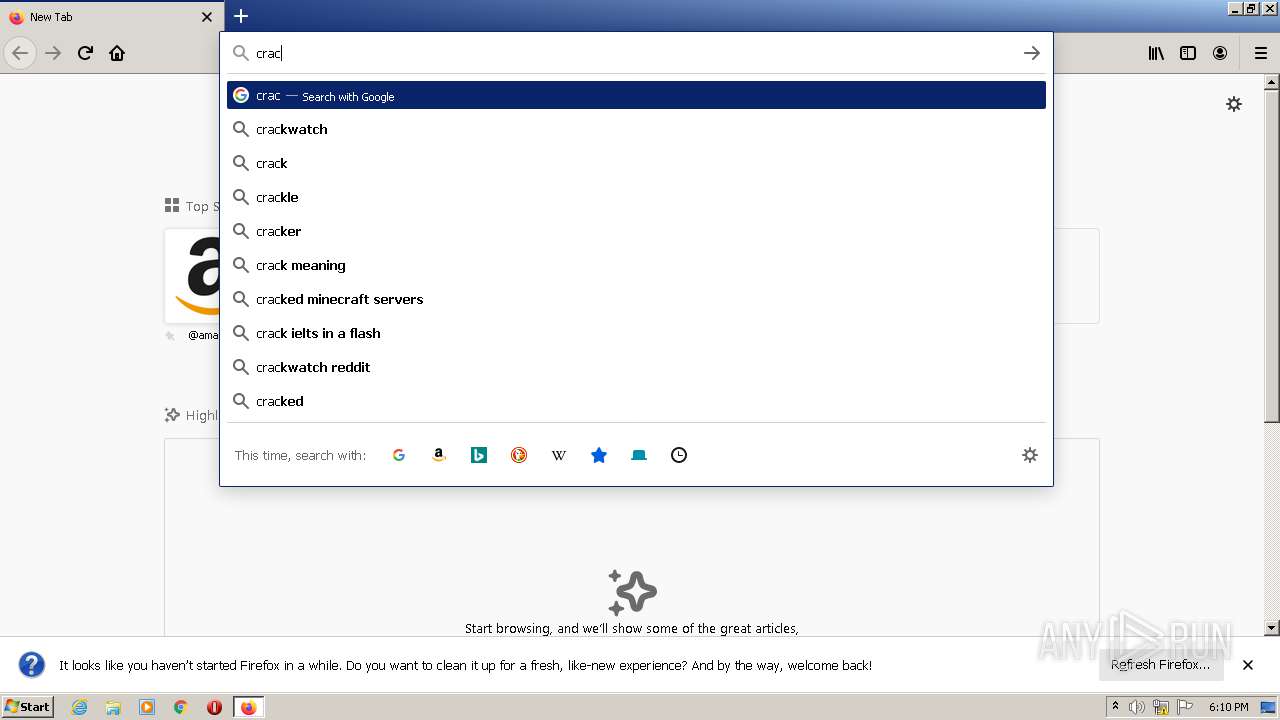
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2856)
Reads the date of Windows installation
- firefox.exe (PID: 2856)
Creates files in the user directory
- firefox.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| Security: | Read-only recommended |
|---|---|
| Software: | Windows Installer XML Toolset (3.11.0.1528) |
| Words: | 10 |
| Pages: | 200 |
| ModifyDate: | 2021:06:22 09:57:58 |
| CreateDate: | 2021:06:22 09:57:58 |
| RevisionNumber: | {2FED6AF0-36B7-478F-B752-28E974F9A211} |
| Template: | Intel;1033 |
| Comments: | This installer database contains the logic and data required to install Original Application Setup. |
| Keywords: | Installer |
| Author: | Original Application Setup |
| Subject: | Original Application Setup Install |
| Title: | Installation Database |
| CodePage: | Windows Latin 1 (Western European) |
Total processes
113
Monitored processes
57
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | sc query NPF | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | C:\Windows\system32\cmd.exe /c sc query npcap | FIND /C "RUNNING" | C:\Windows\system32\cmd.exe | — | OriginalApplicationSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 572 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2856.20.1631253195\36003382" -childID 3 -isForBrowser -prefsHandle 3132 -prefMapHandle 3336 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2856 "\\.\pipe\gecko-crash-server-pipe.2856" 3504 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 836 | sc query NPF | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | cmd /d /c rd /s /q "C:\Users\admin\AppData\Local\OriginalApplicationSetup" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\AppData\Local\OriginalApplicationSetup\OriginalApplicationSetup.exe" /elv C:\Users\admin\AppData\Local\Temp\Escape-from-Tarkov-Generator_29060.msi | C:\Users\admin\AppData\Local\OriginalApplicationSetup\OriginalApplicationSetup.exe | OriginalApplicationSetup.exe | ||||||||||||
User: admin Company: Original Application Setup Integrity Level: HIGH Description: Original Application Setup Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1228 | FIND /C "RUNNING" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | sc query NPF | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | sc query npcap | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1808 | "C:\Users\admin\AppData\Local\Temp\is-SP4UL.tmp\OriginalrApplication.tmp" /SL5="$3014A,28665901,295936,C:\Program Files\OriginalApplicationhivSetup\OriginalrApplication.exe" | C:\Users\admin\AppData\Local\Temp\is-SP4UL.tmp\OriginalrApplication.tmp | — | OriginalrApplication.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
42 340
Read events
42 111
Write events
200
Delete events
29
Modification events
| (PID) Process: | (2544) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: BC0B0000AF07592C776BD701 | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: D9FFFB1DB64766AA92E86A2BEAA4784DC8BCB5D32EAEADE3C96B79D7A9D3F4E3 | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\d6b3e.ipi | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\d6b3f.rbs |
Value: 30894975 | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\d6b3f.rbsLow |
Value: | |||
| (PID) Process: | (3004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1302019708-1500728564-335382590-1000\Components\8FDFD6B3197E39643906B545BFAC2571 |
| Operation: | write | Name: | 8FDFD6B3197E39643906B545CF90C3C2 |
Value: 01:\Software\WixSharp\Used\ | |||
Executable files
10
Suspicious files
148
Text files
60
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3004 | msiexec.exe | C:\Windows\Installer\d6b3d.msi | executable | |
MD5:1D69A15E99914B7293F04BF4970B5809 | SHA256:C0B9CB7EFB8784CF600286562216C0D79C0F47FE4FBF0F9BC36B5869DFA29C2E | |||
| 3004 | msiexec.exe | C:\Windows\Installer\d6b3e.ipi | binary | |
MD5:D312688E45877659717103242A95AA05 | SHA256:8B37AA0585C8131BA5E8208E57EA76D8A8A302CF677BEFE7C95651CA0C406E05 | |||
| 3004 | msiexec.exe | C:\Windows\Installer\SourceHash{3B6DFDF8-E791-4693-9360-5B54FC093C2C} | binary | |
MD5:528D4149D4E27B019280FEED023BB439 | SHA256:F8035466FECE63BA004BD925308FB1E908AED4BE73E4AD3B2FF9A7229737AEDE | |||
| 3004 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFE5D318E5EC2A1038.TMP | gmc | |
MD5:C968E78D2D9F1DC6737197F58A731CB1 | SHA256:D438E296A1B8D9872F45DABD2CE9233804839977F63A2F14F533CC46AC78AA89 | |||
| 3004 | msiexec.exe | C:\Config.Msi\d6b3f.rbs | binary | |
MD5:6EF2FC3618822E0EB4DB908186E6A4B4 | SHA256:8D22998960211A685465EF413C9175DA215A955AFF1DA9D74CE19F3C9F28329E | |||
| 2856 | OriginalApplicationSetup.exe | C:\Users\admin\AppData\Local\Temp\~DFE4FAA4045D8529F8.TMP | binary | |
MD5:8D50025EF1AD8680EC8144ECED4C735C | SHA256:592ABA730C5221E994D2CB6D756933257375129A3AE5918BC8172F9F6DFAC994 | |||
| 1116 | OriginalApplicationSetup.exe | C:\Users\admin\AppData\Local\Temp\~DF6B57CFEDDE83C1FA.TMP | binary | |
MD5:752782E6FE4489923FFD0DAE31A5AEEA | SHA256:A892C63E8CD16F7E96444C8B6686C9A58C37F9DE527E5DF72FE8190A3AC3BC8F | |||
| 3004 | msiexec.exe | C:\Users\admin\AppData\Local\OriginalApplicationSetup\OriginalApplicationSetup.exe | executable | |
MD5:A4A7101AE93E86B12FE45316F0EDD24F | SHA256:6161C997BE2C7C3EC4BA5641230F3C969CA43649213FF90943061D4C113D7414 | |||
| 2856 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:10FEEB5C1A5013A6BF382980A1682D67 | SHA256:C33DAACC876A306C9511F3F234B3FAE8A8040458FEB36546CE80B1ECE60C5A49 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
77
DNS requests
159
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2856 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
2856 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2856 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2856 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2856 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2856 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2856 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2856 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
2856 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
2856 | firefox.exe | POST | 200 | 13.224.194.18:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2856 | firefox.exe | 44.238.232.169:443 | push.services.mozilla.com | University of California, San Diego | US | unknown |
2856 | firefox.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2856 | firefox.exe | 13.225.87.20:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | suspicious |
2856 | firefox.exe | 13.224.193.14:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
2856 | firefox.exe | 34.215.35.6:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2856 | firefox.exe | 172.217.18.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2856 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2856 | firefox.exe | 13.225.87.51:443 | content-signature-2.cdn.mozilla.net | — | US | malicious |
2856 | firefox.exe | 52.26.168.11:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2856 | firefox.exe | 13.224.193.32:443 | tracking-protection.cdn.mozilla.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
realsoftwaretime.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
2856 | firefox.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3352 | OriginalmApplication.tmp | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3352 | OriginalmApplication.tmp | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3352 | OriginalmApplication.tmp | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
saBSI.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\mfeaaca.dll, WinVerifyTrust failed with 80092003
|