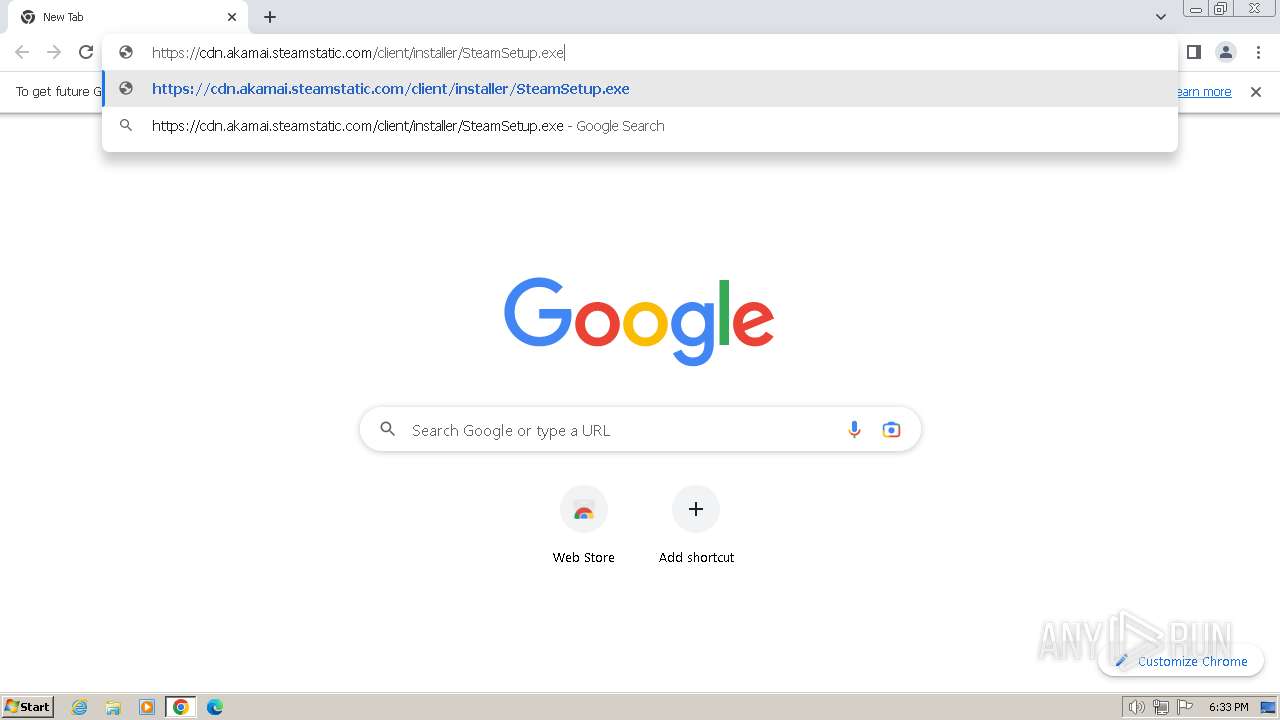
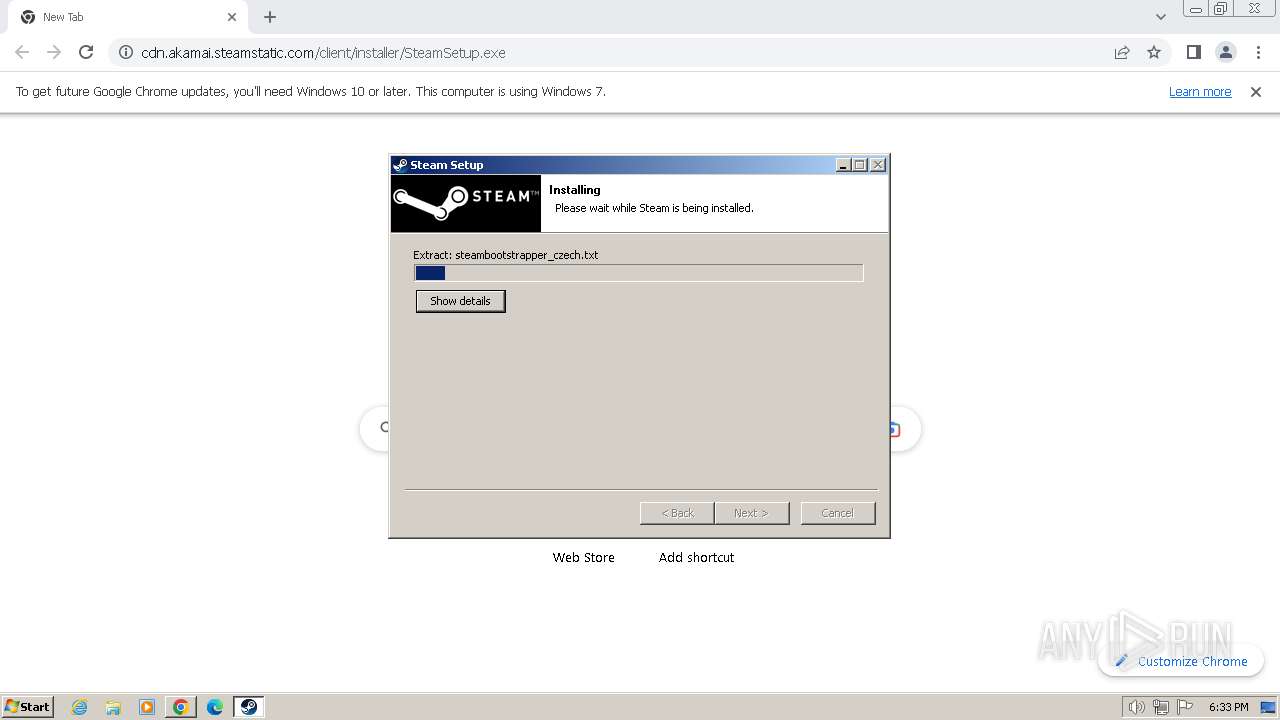
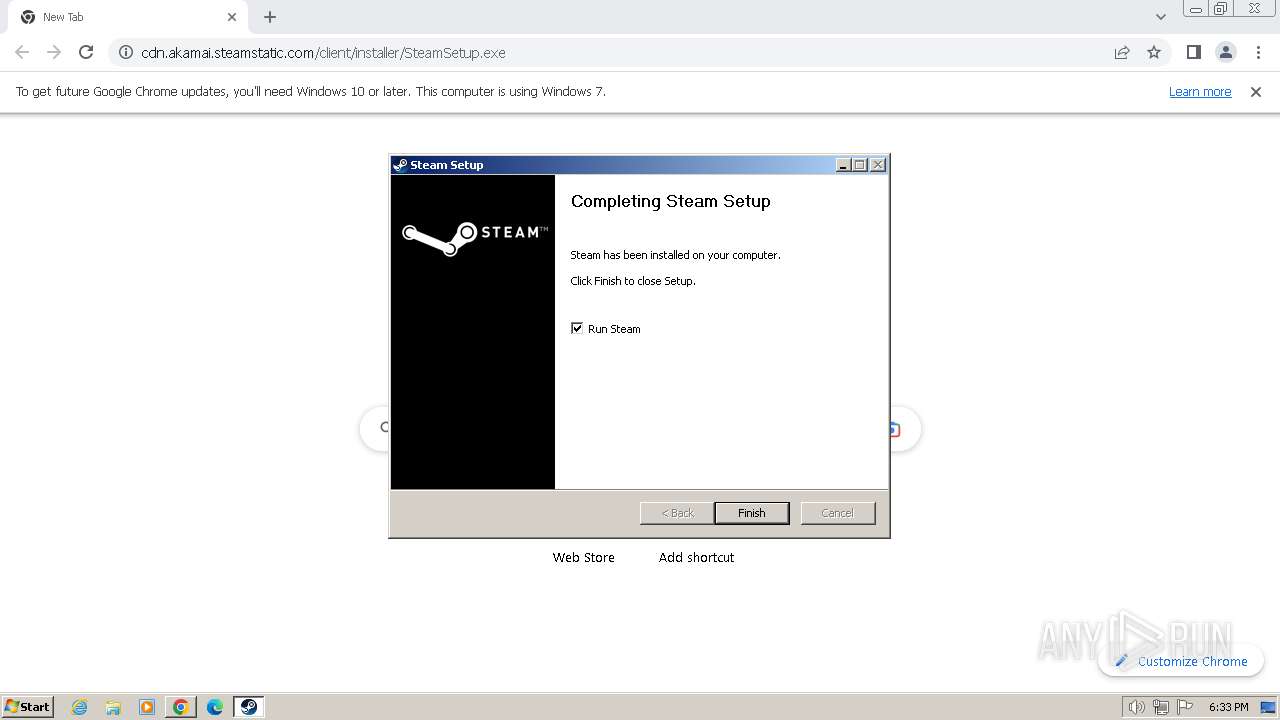
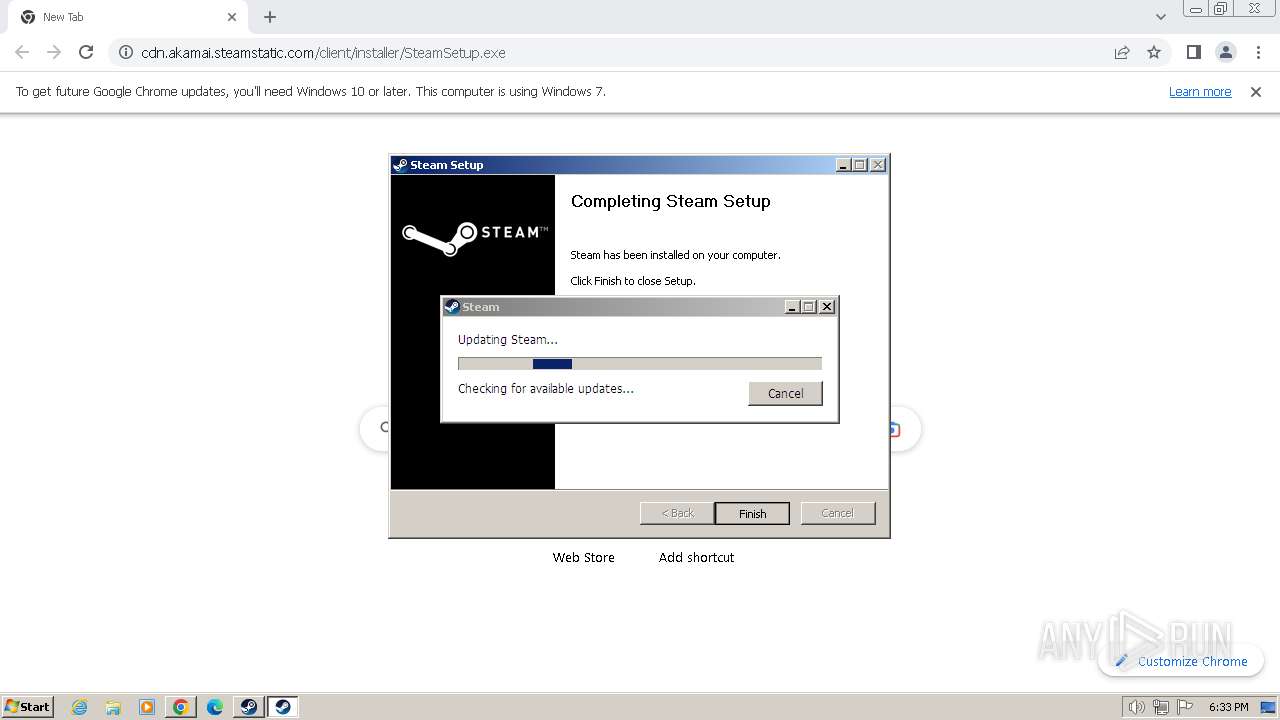
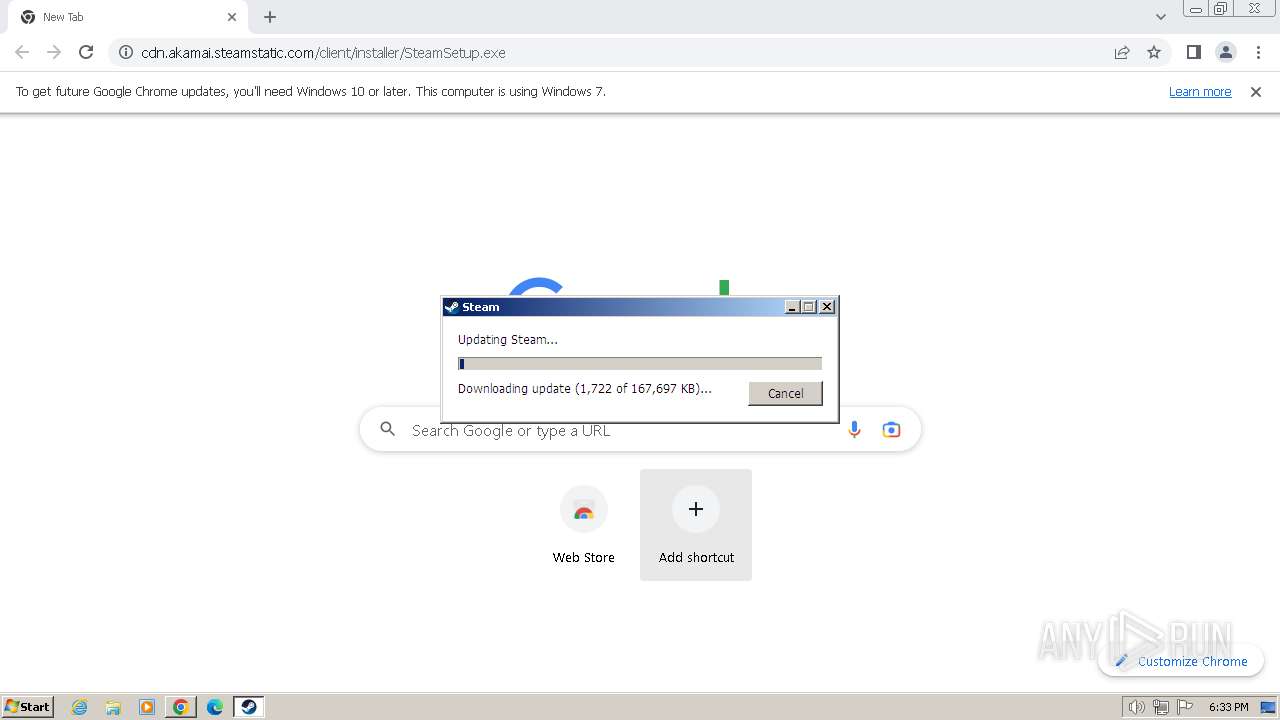
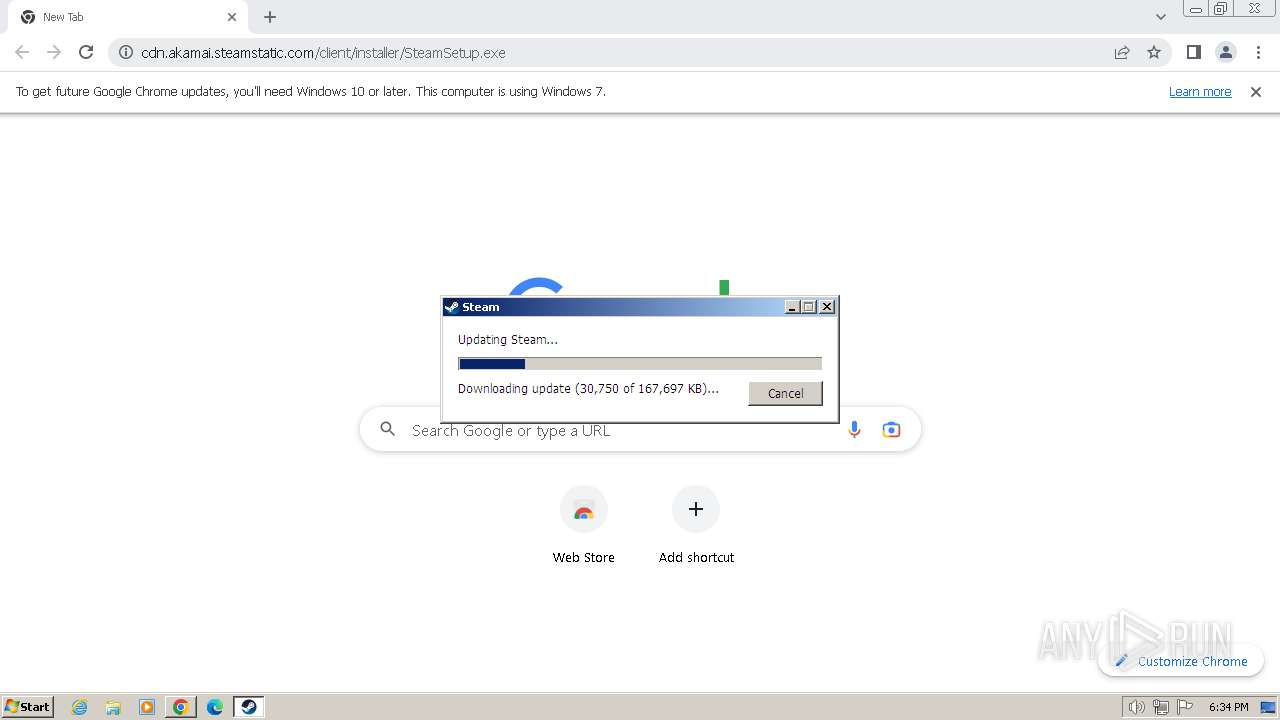
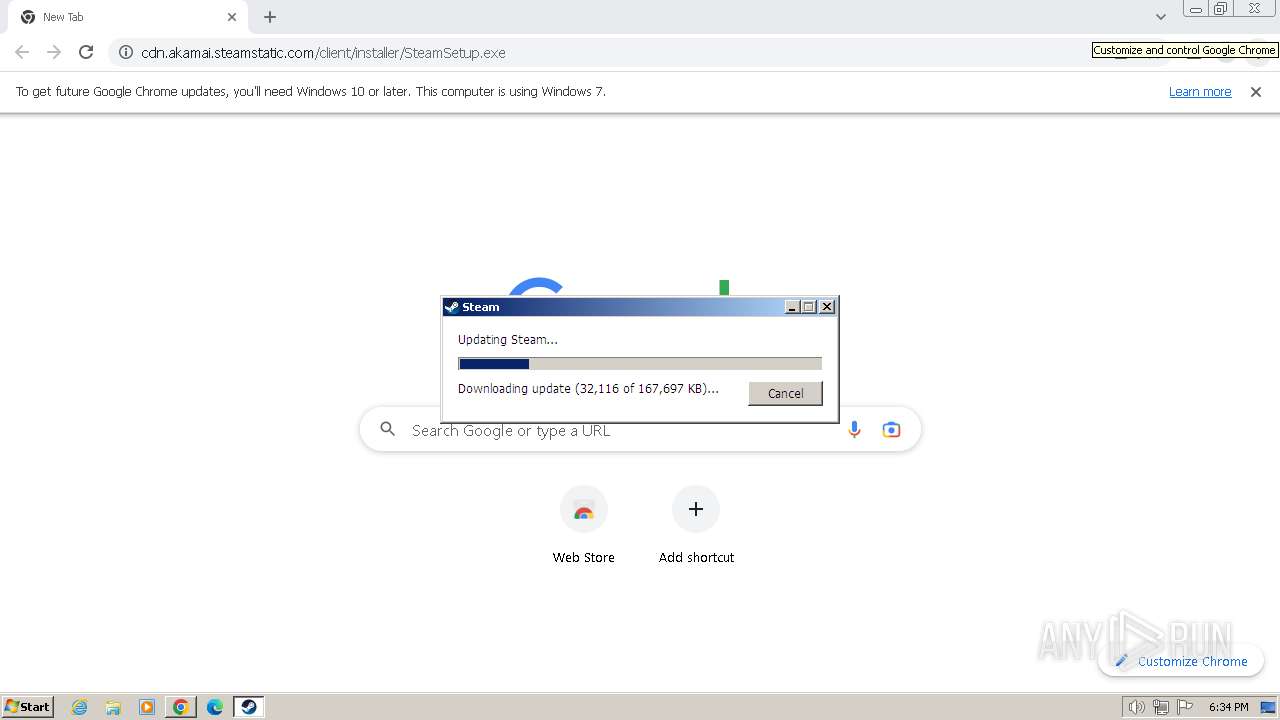
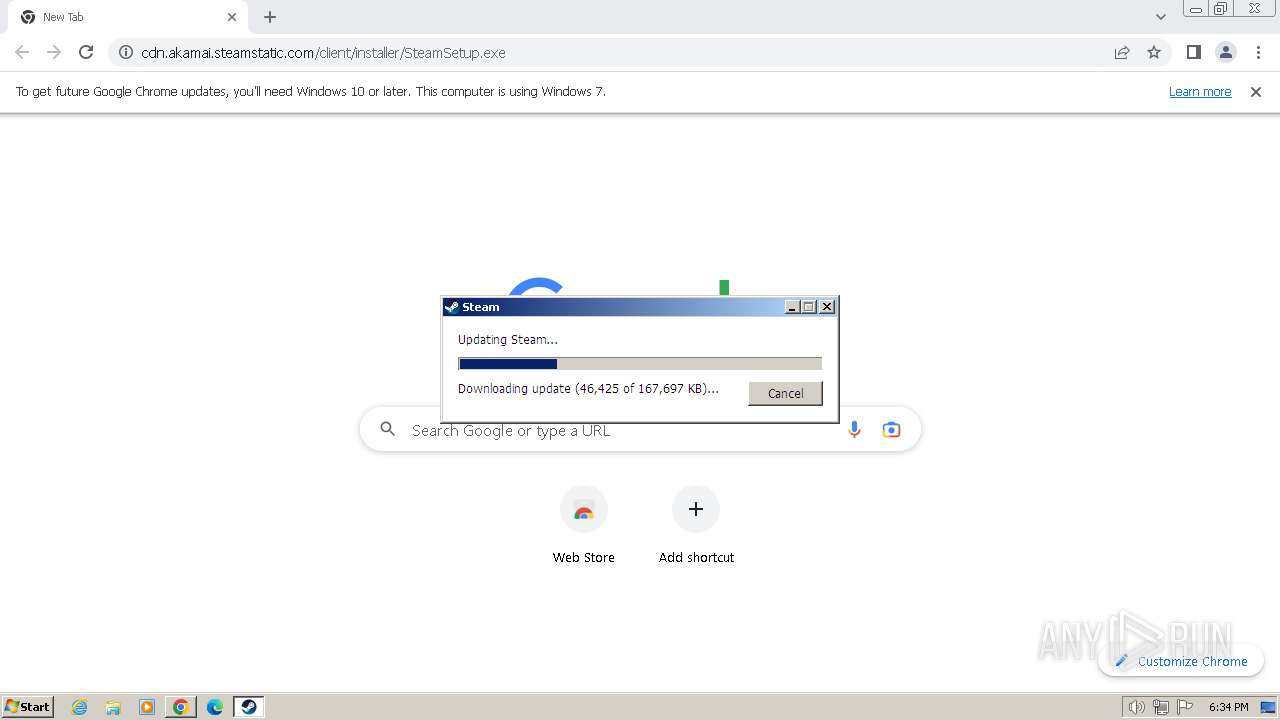
| URL: | https://cdn.akamai.steamstatic.com/client/installer/SteamSetup.exe |
| Full analysis: | https://app.any.run/tasks/20ca1c04-c04f-4d76-b441-e65dab10a33a |
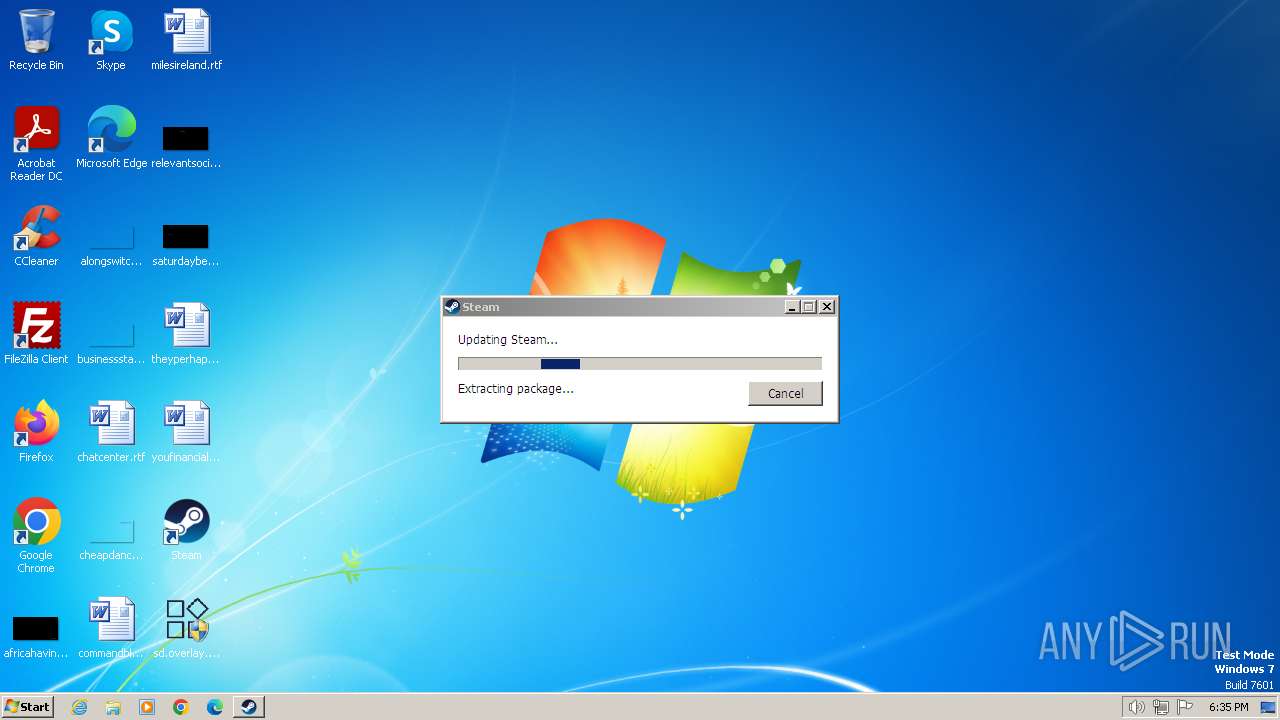
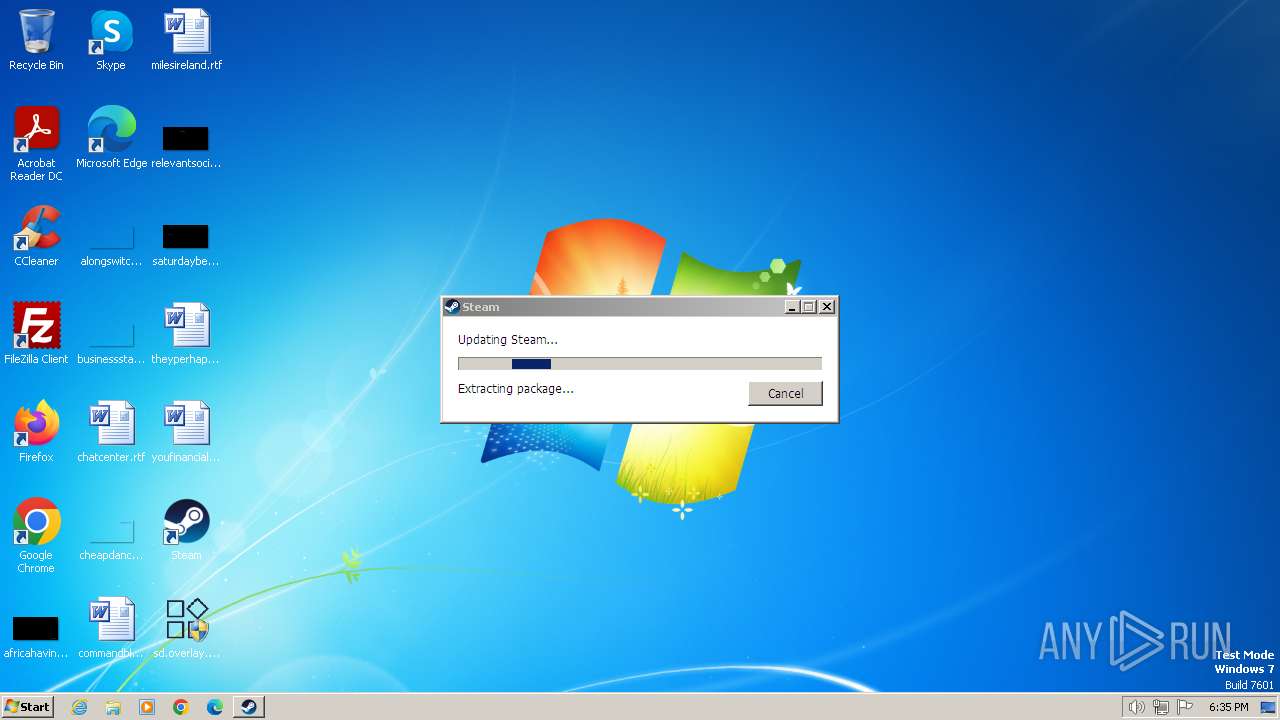
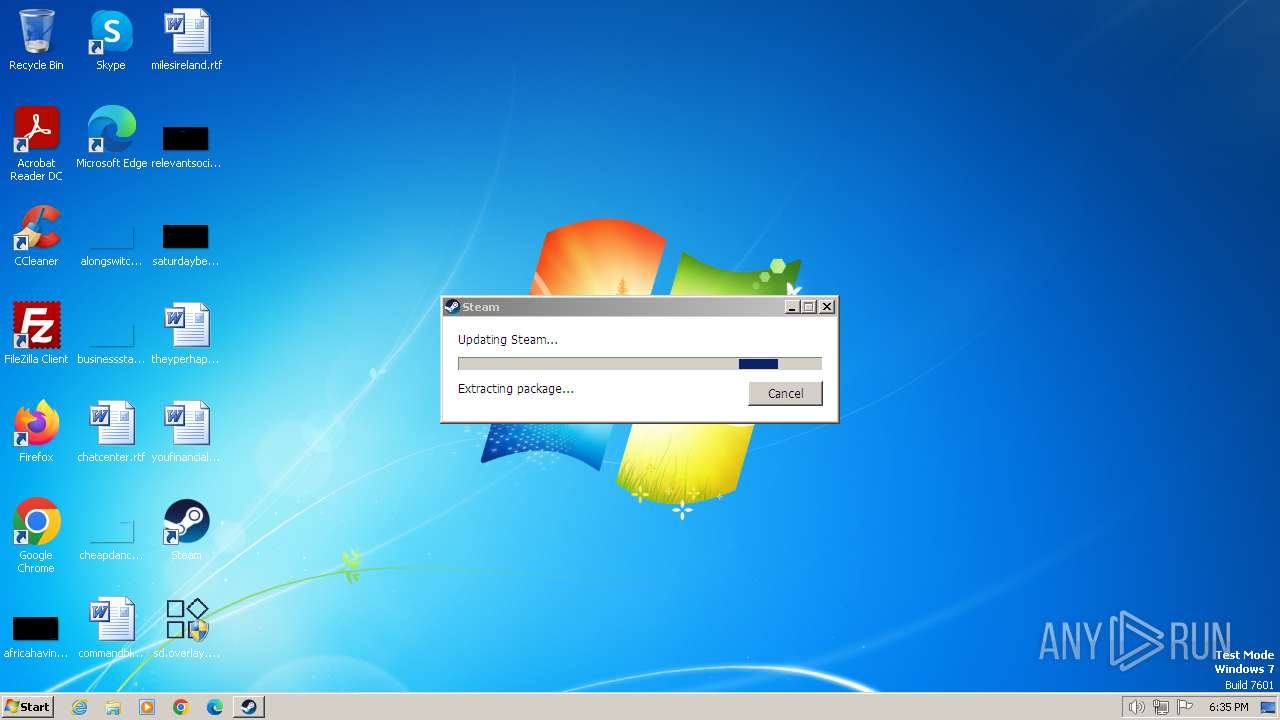
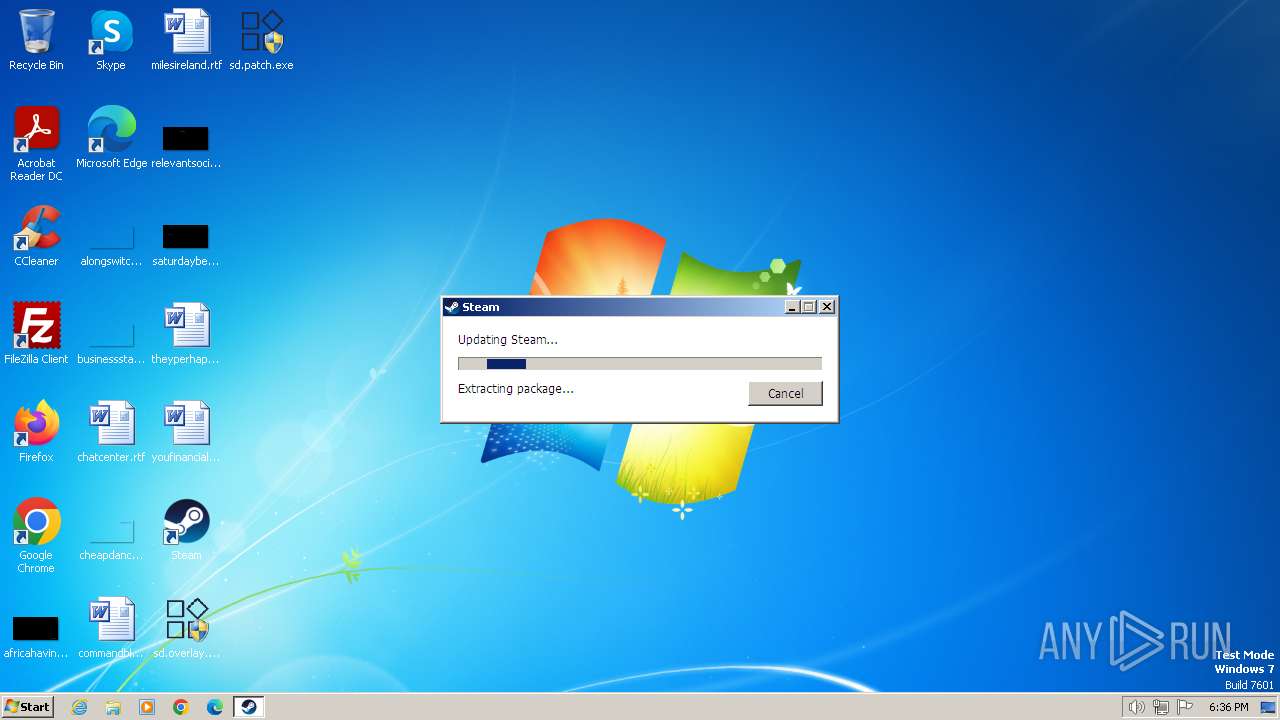
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2024, 18:33:01 |
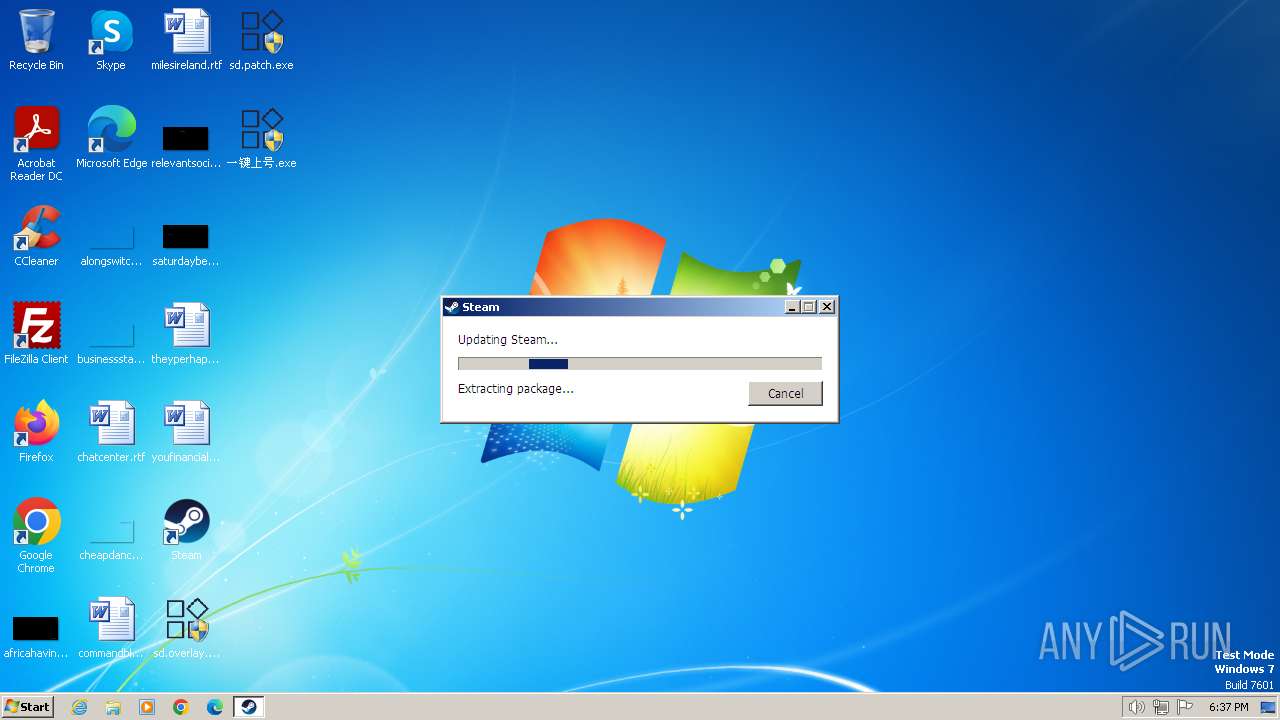
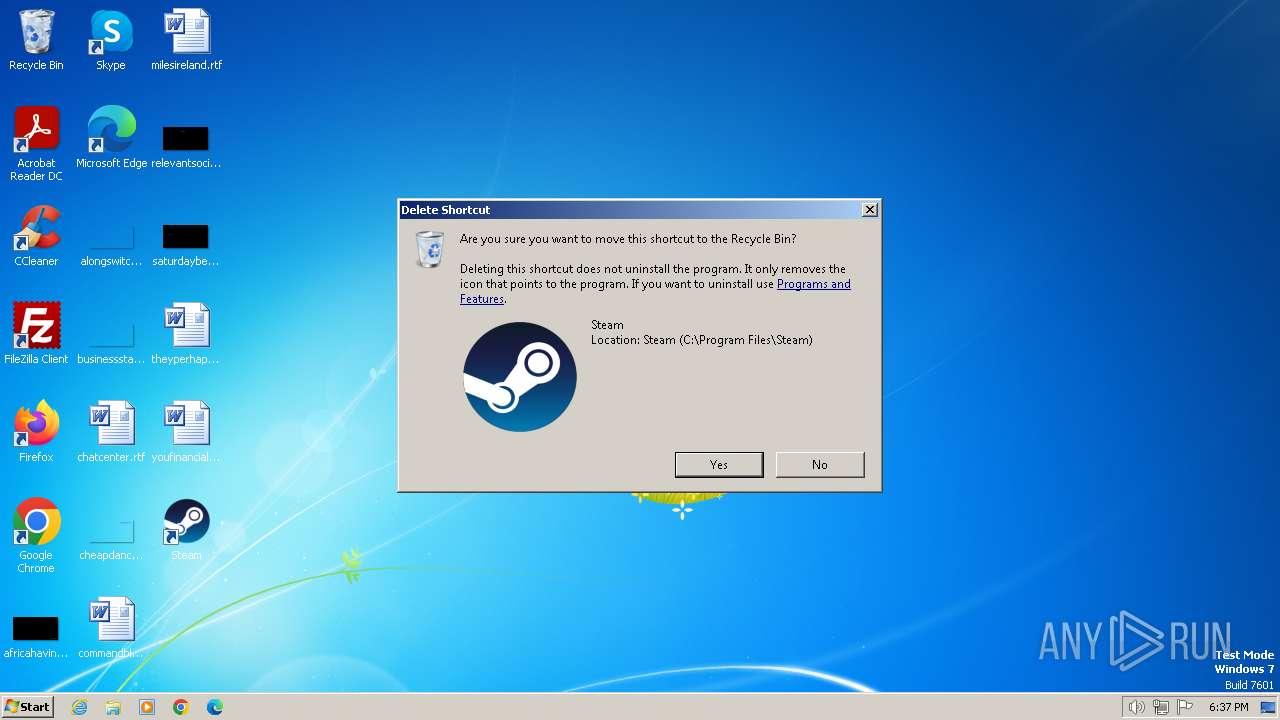
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 506D24DCD6153BD4FE5F6C484AD7B3B3 |
| SHA1: | 9BA5F8DFBFABD97DA4562C9E0DA13EE3711BCEBD |
| SHA256: | C0A0848B287B2767D26192A7459FC3D51D81EFA45A4DDE2485BE69A84DFF9DB0 |
| SSDEEP: | 3:N8cZTWiqGLduMu5VOXKngA2aA:2cZPpduMKOX8F2aA |
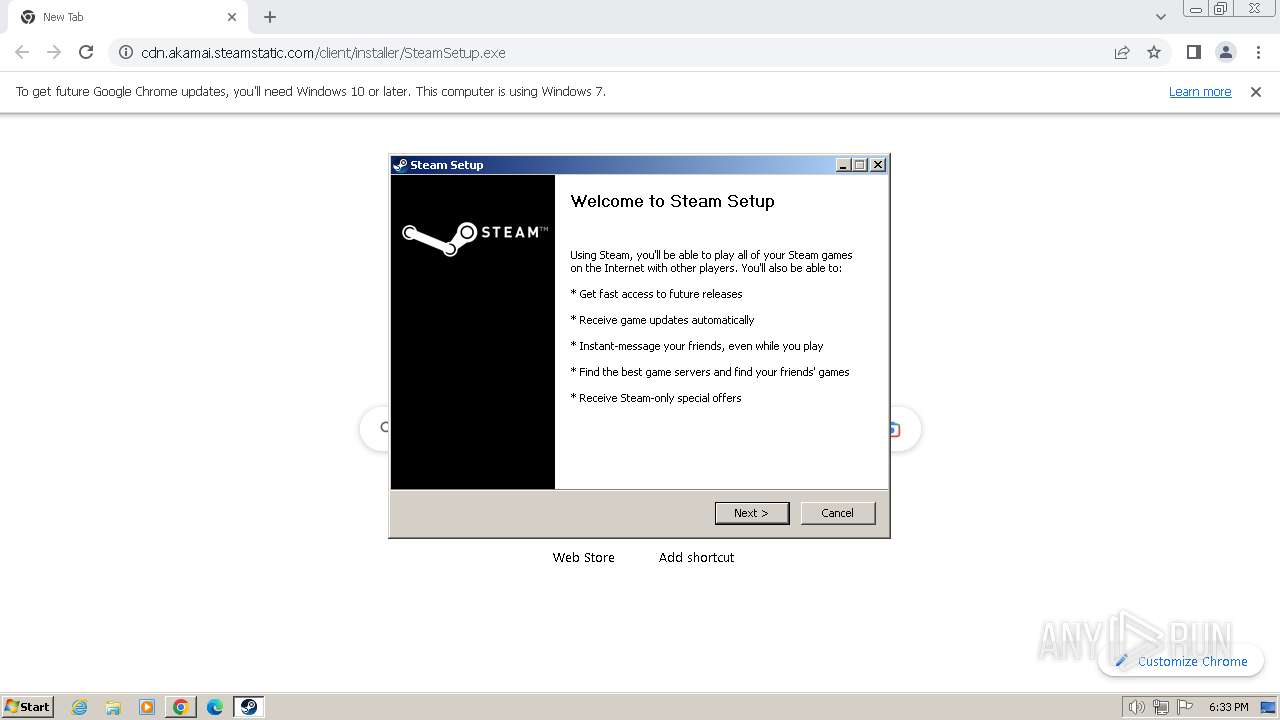
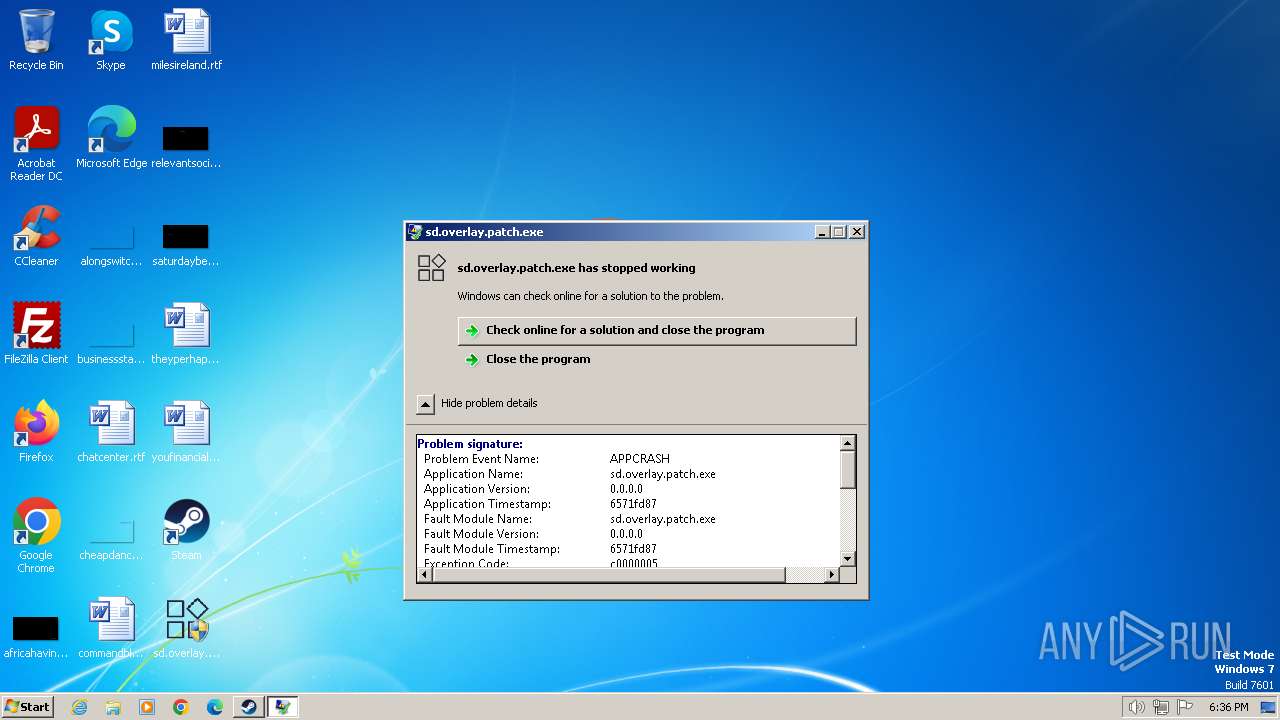
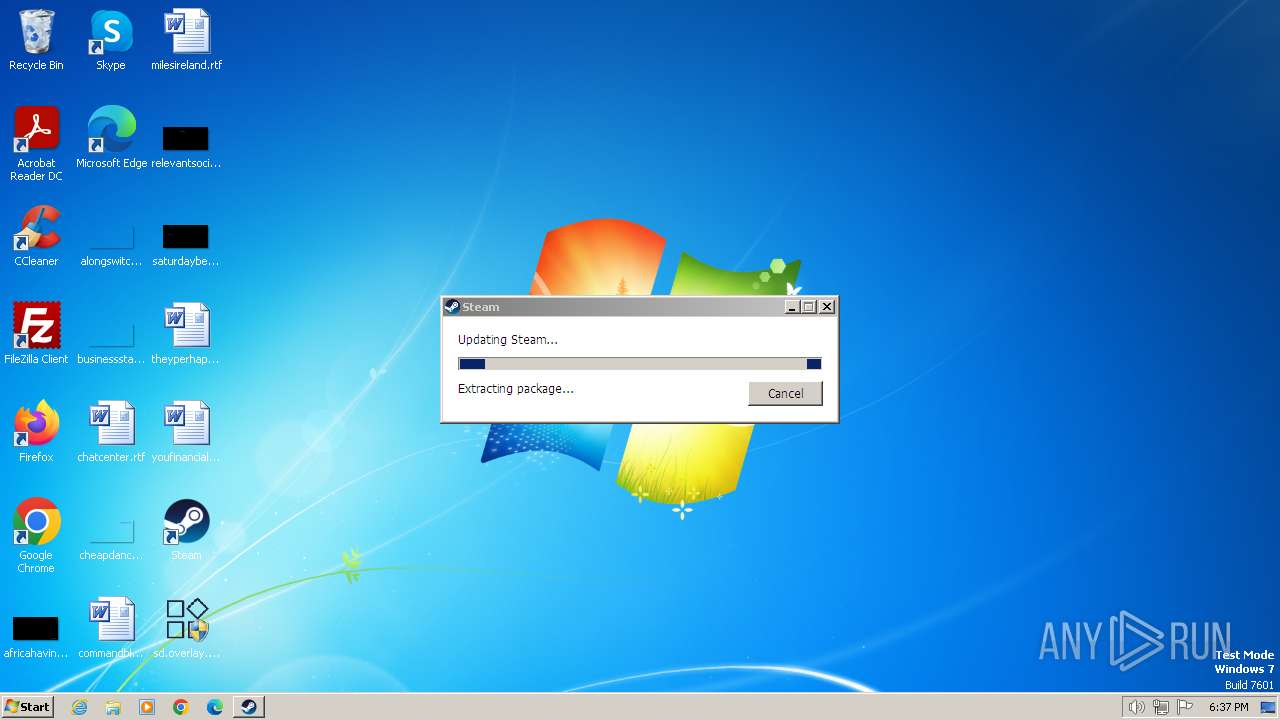
MALICIOUS
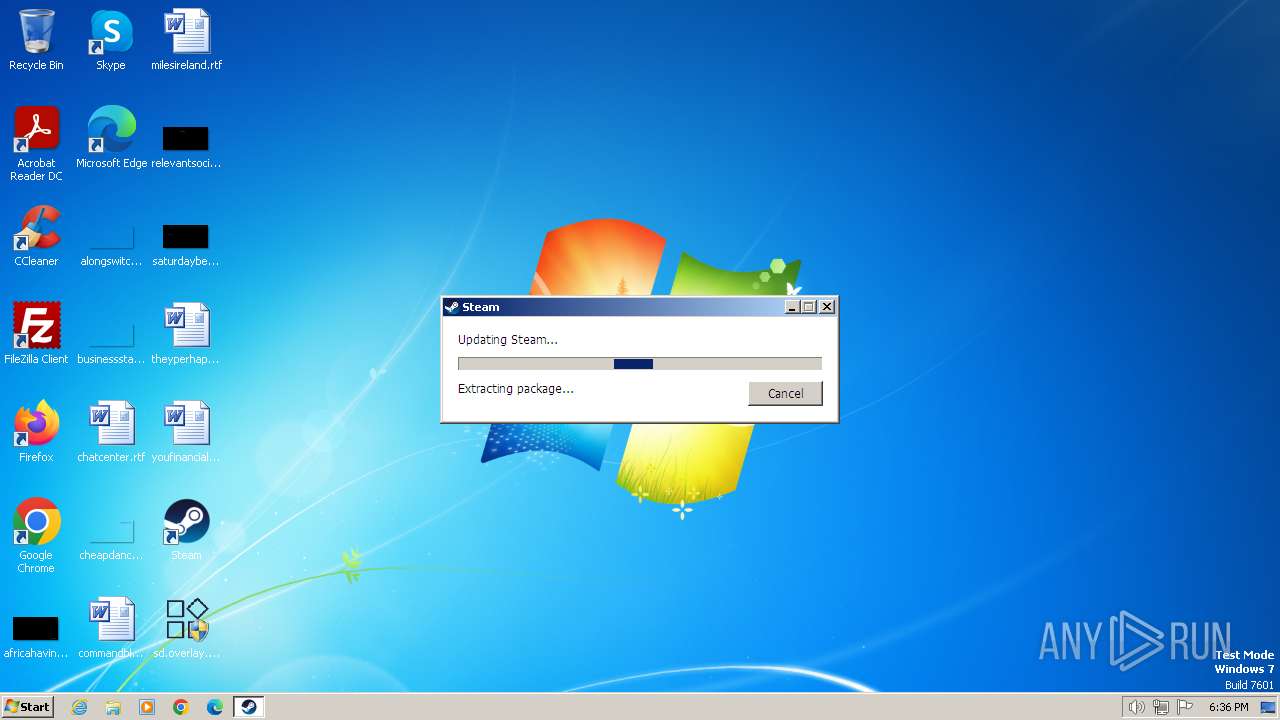
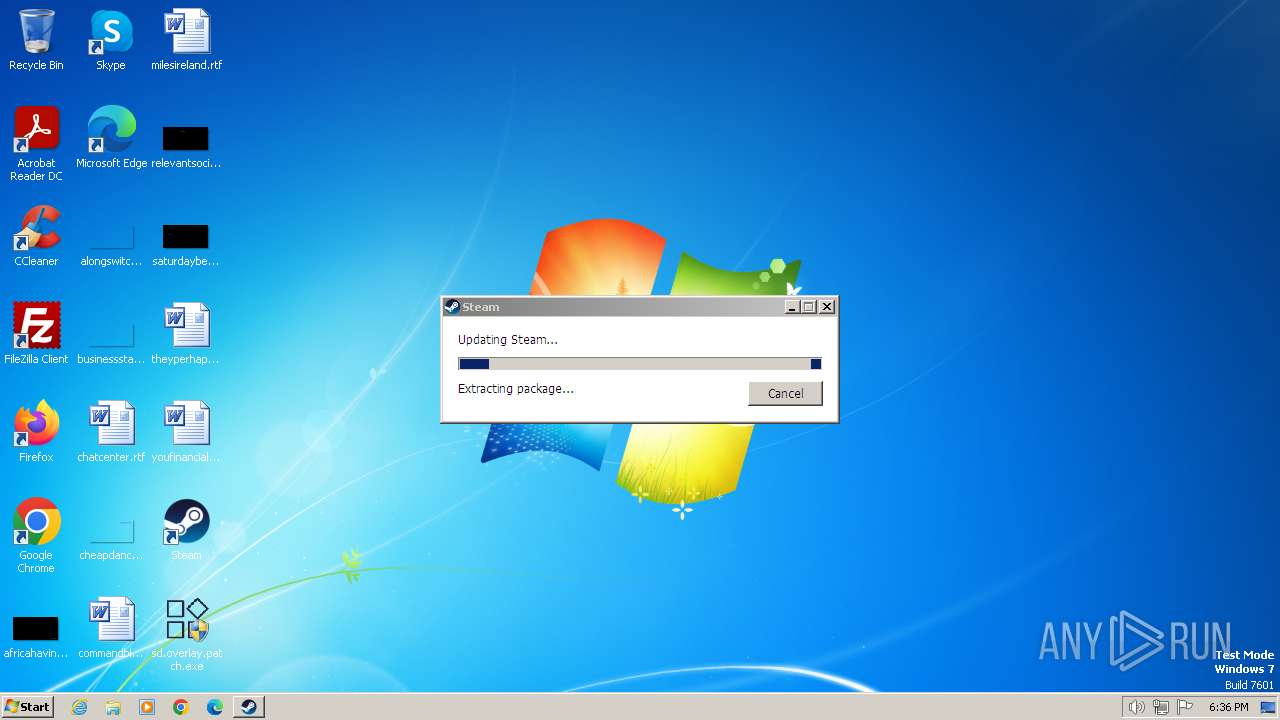
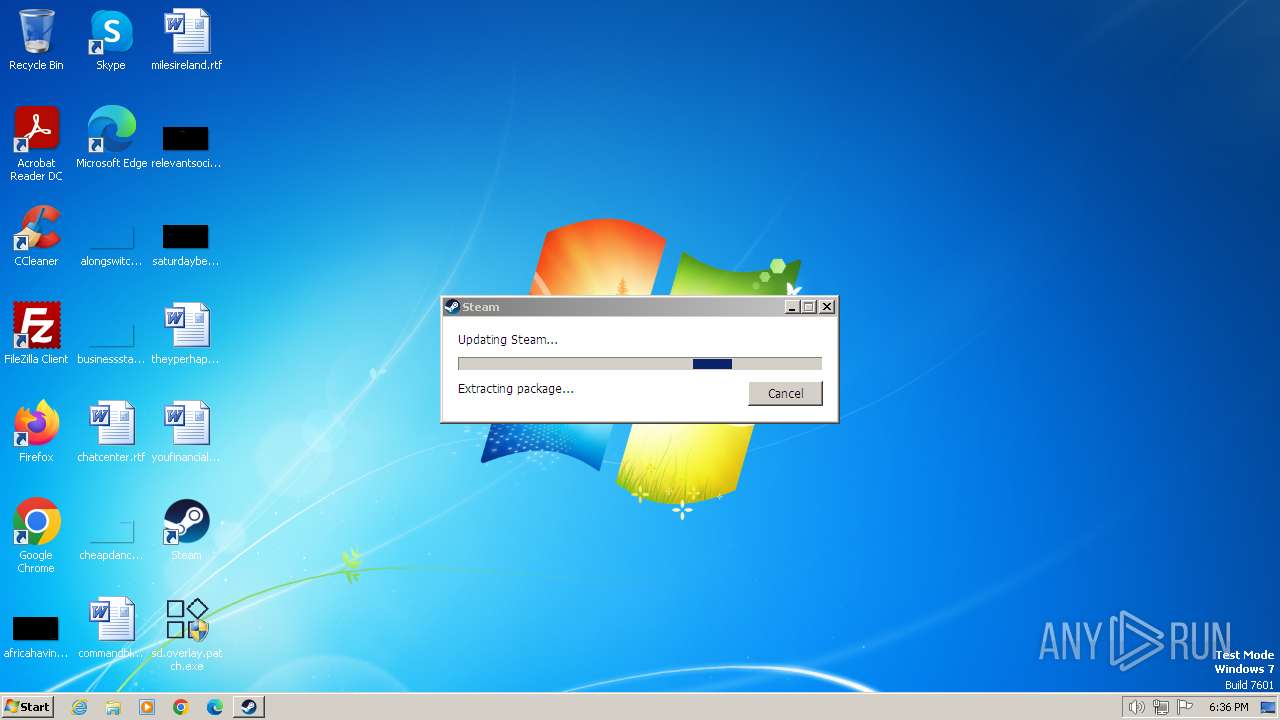
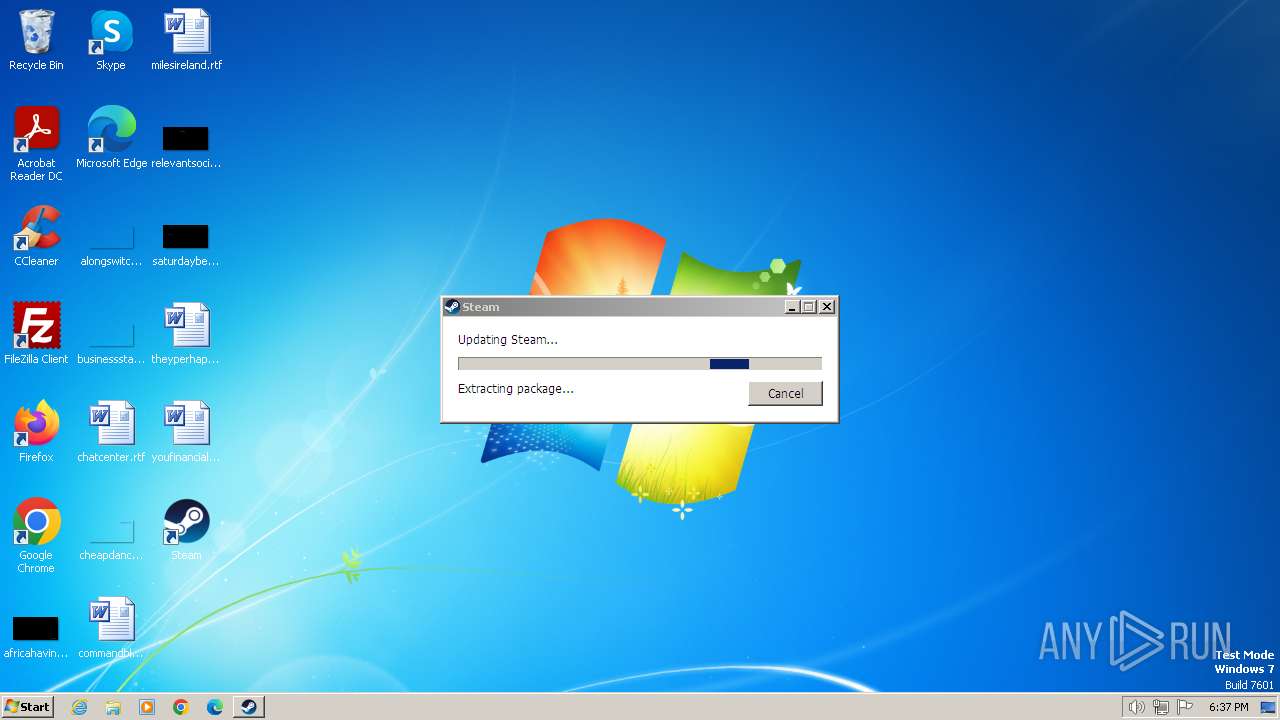
Drops the executable file immediately after the start
- SteamSetup.exe (PID: 2640)
- steamservice.exe (PID: 712)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- SteamSetup.exe (PID: 2640)
The process creates files with name similar to system file names
- SteamSetup.exe (PID: 2640)
Executable content was dropped or overwritten
- SteamSetup.exe (PID: 2640)
- steamservice.exe (PID: 712)
Reads the Internet Settings
- Steam.exe (PID: 2068)
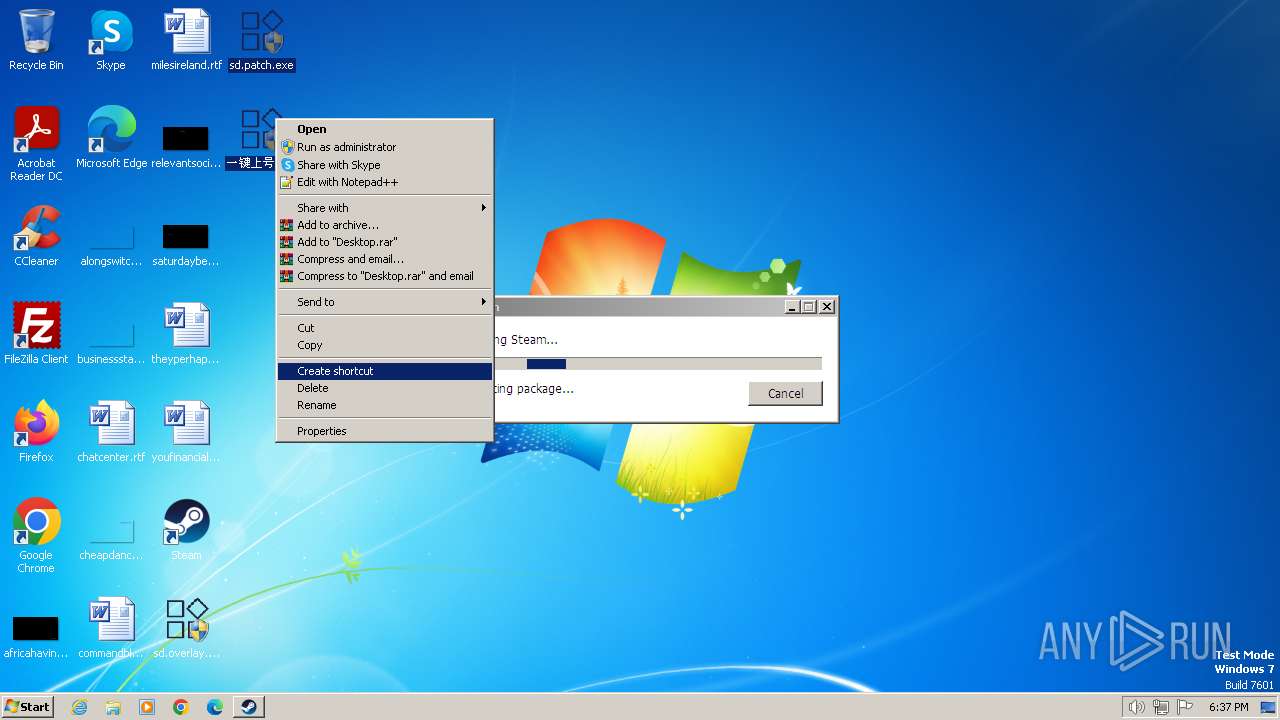
Starts application with an unusual extension
- SteamSetup.exe (PID: 2640)
INFO
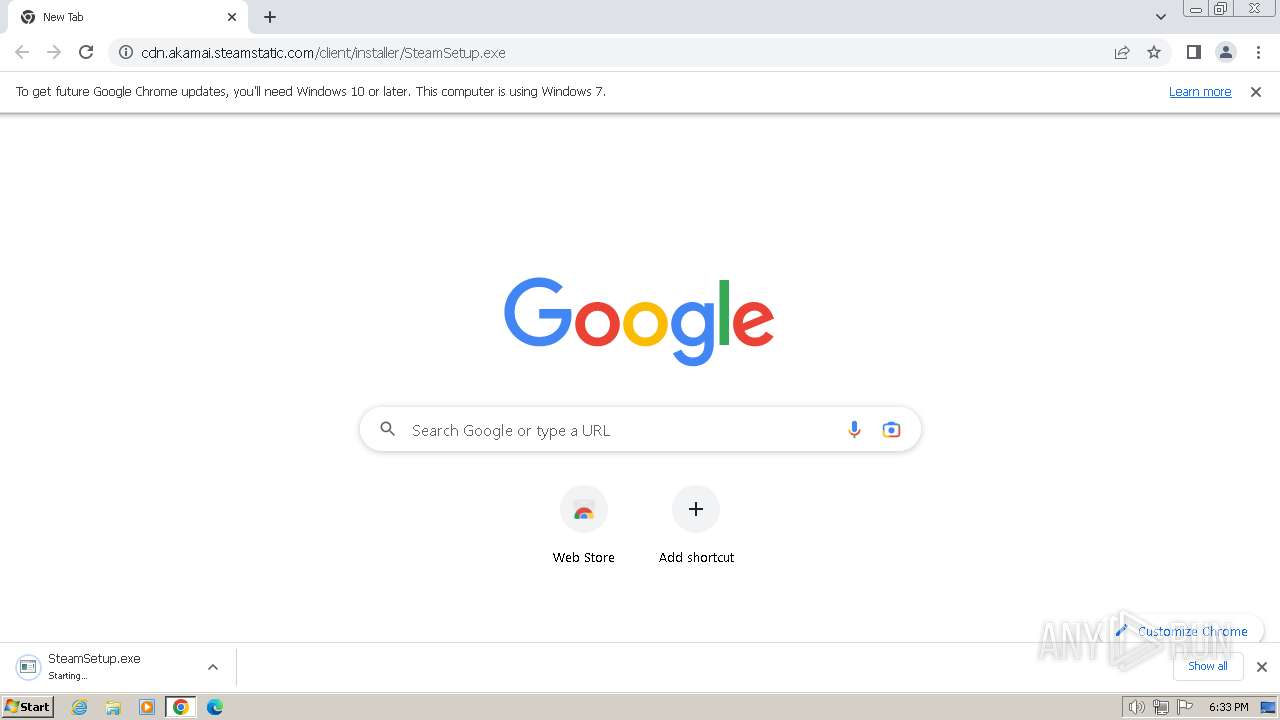
Executable content was dropped or overwritten
- chrome.exe (PID: 3820)
- chrome.exe (PID: 3452)
Application launched itself
- iexplore.exe (PID: 752)
- chrome.exe (PID: 3452)
Drops the executable file immediately after the start
- chrome.exe (PID: 3820)
- chrome.exe (PID: 3452)
Checks supported languages
- SteamSetup.exe (PID: 2640)
- steamservice.exe (PID: 712)
- Steam.exe (PID: 2068)
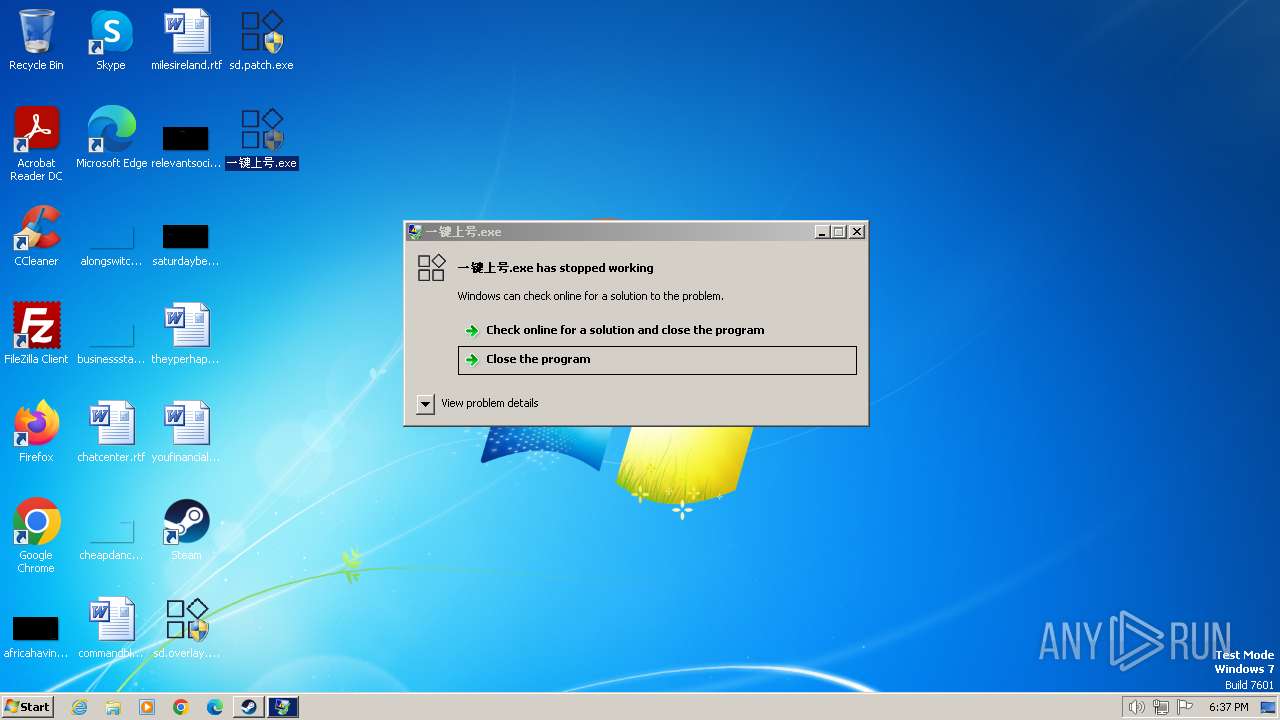
- nsCE35.tmp (PID: 2876)
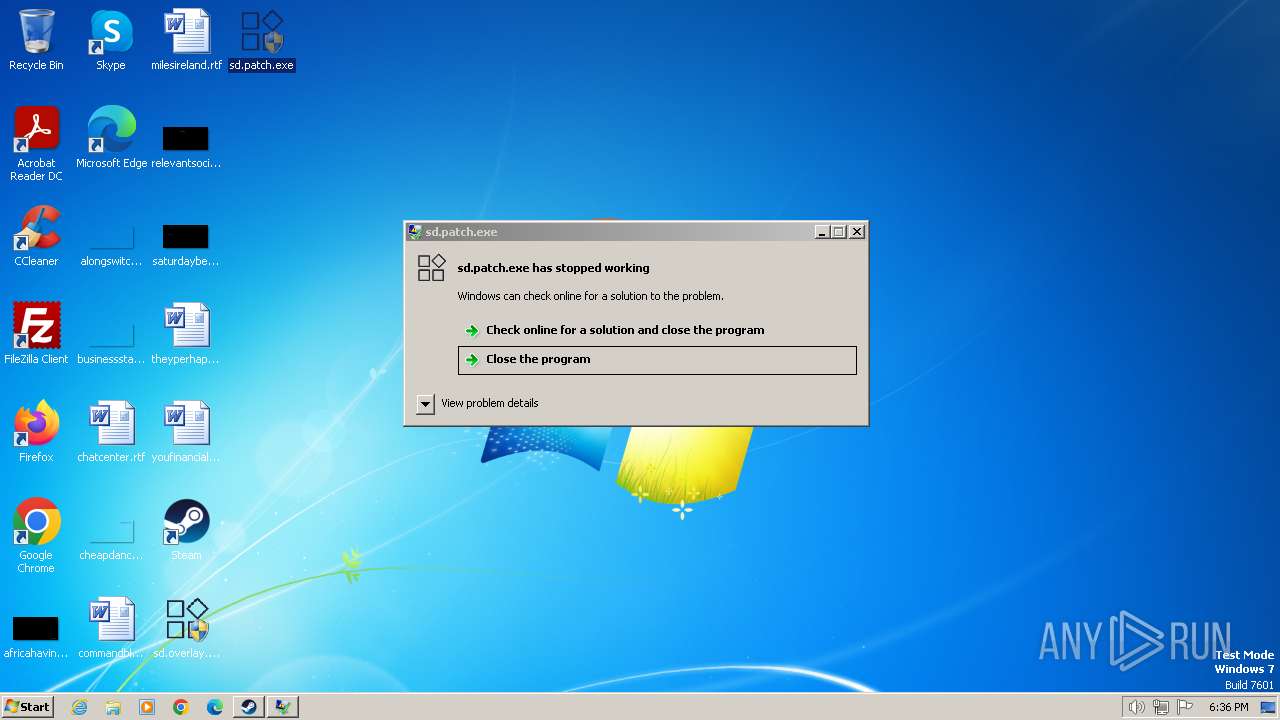
- sd.patch.exe (PID: 3404)
- 一键上号.exe (PID: 2324)
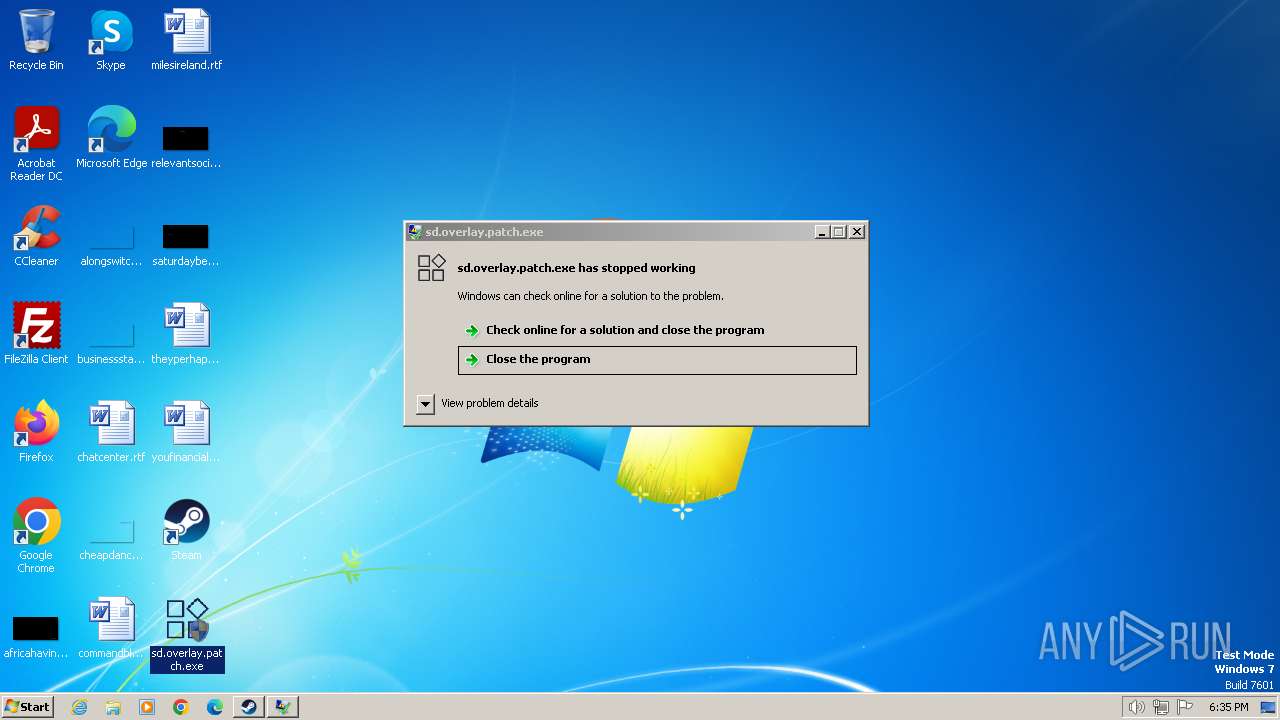
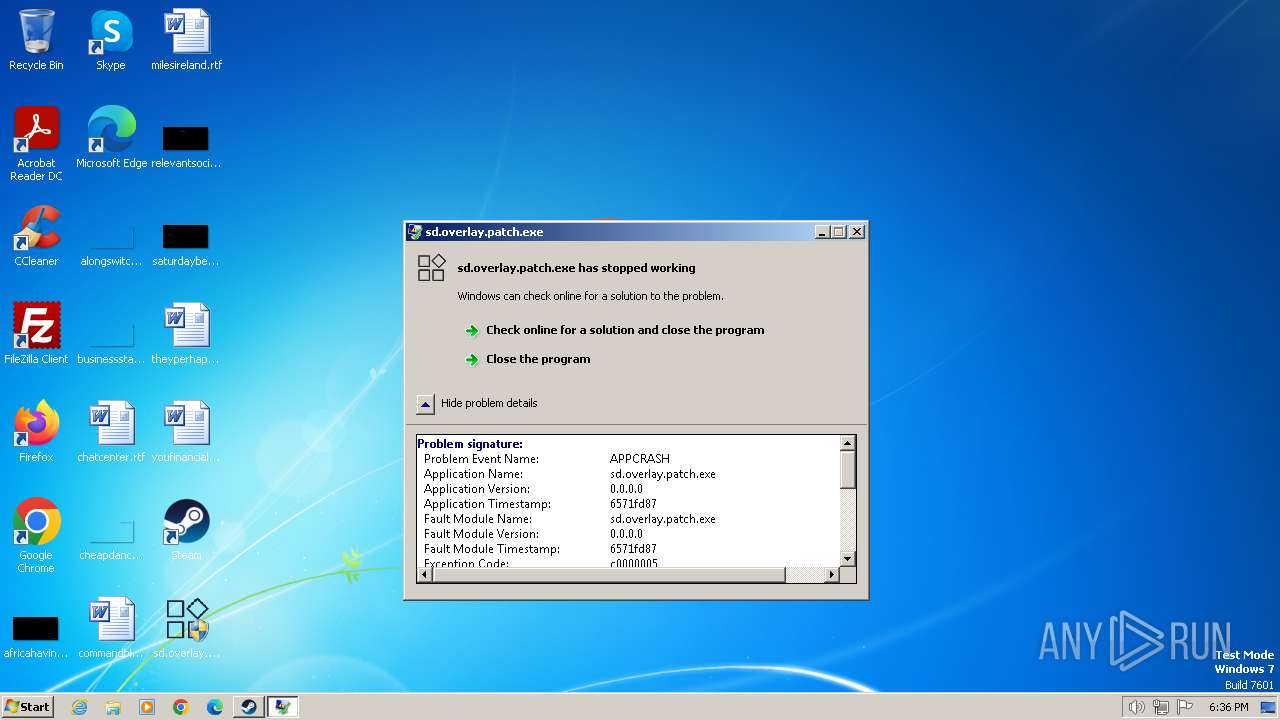
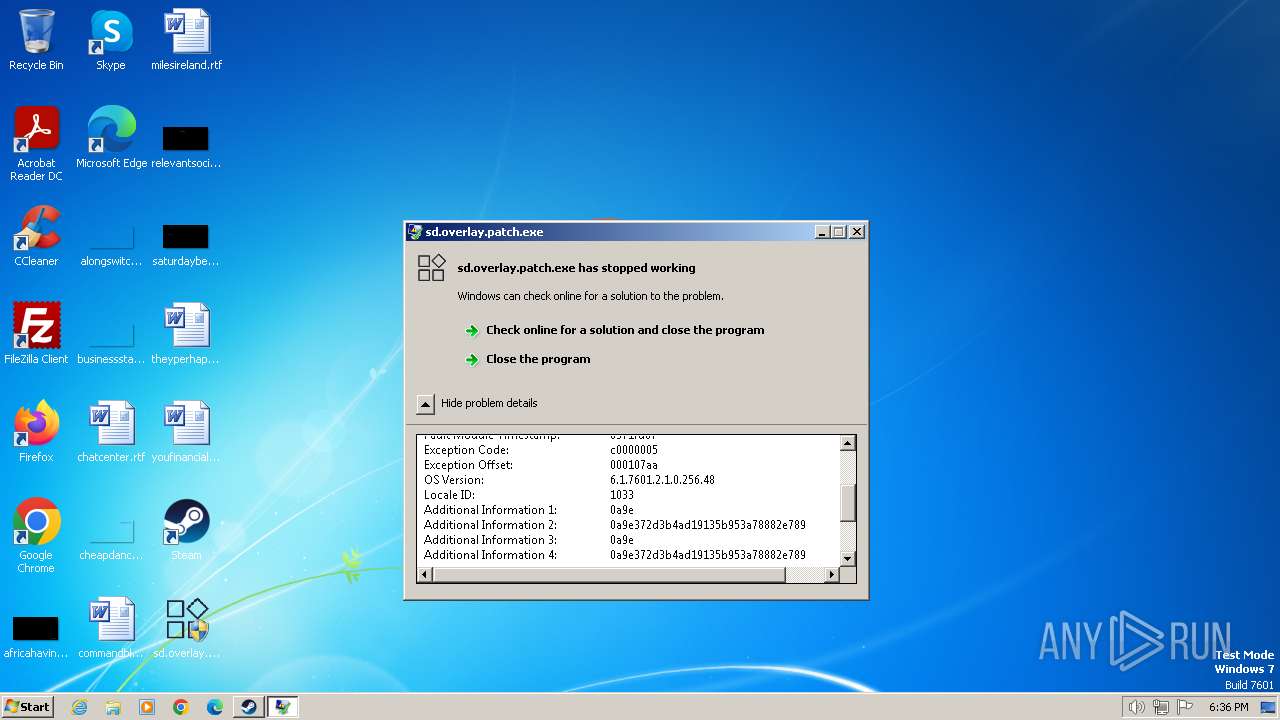
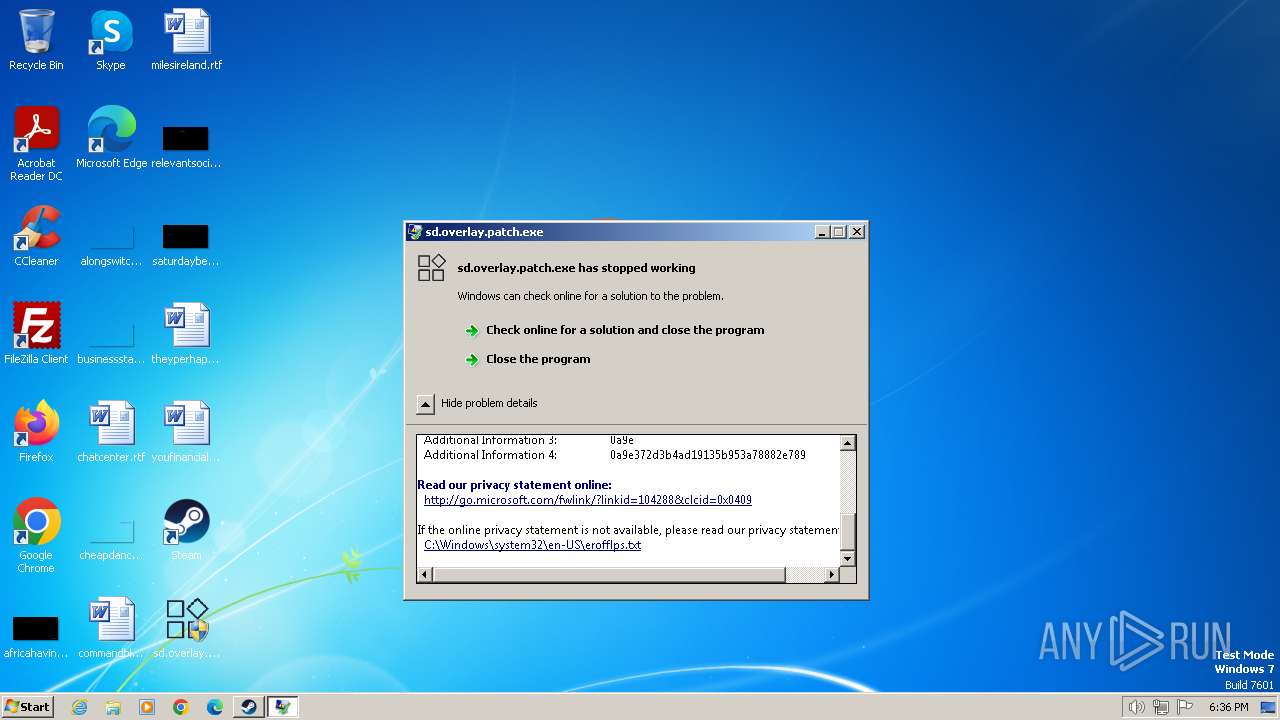
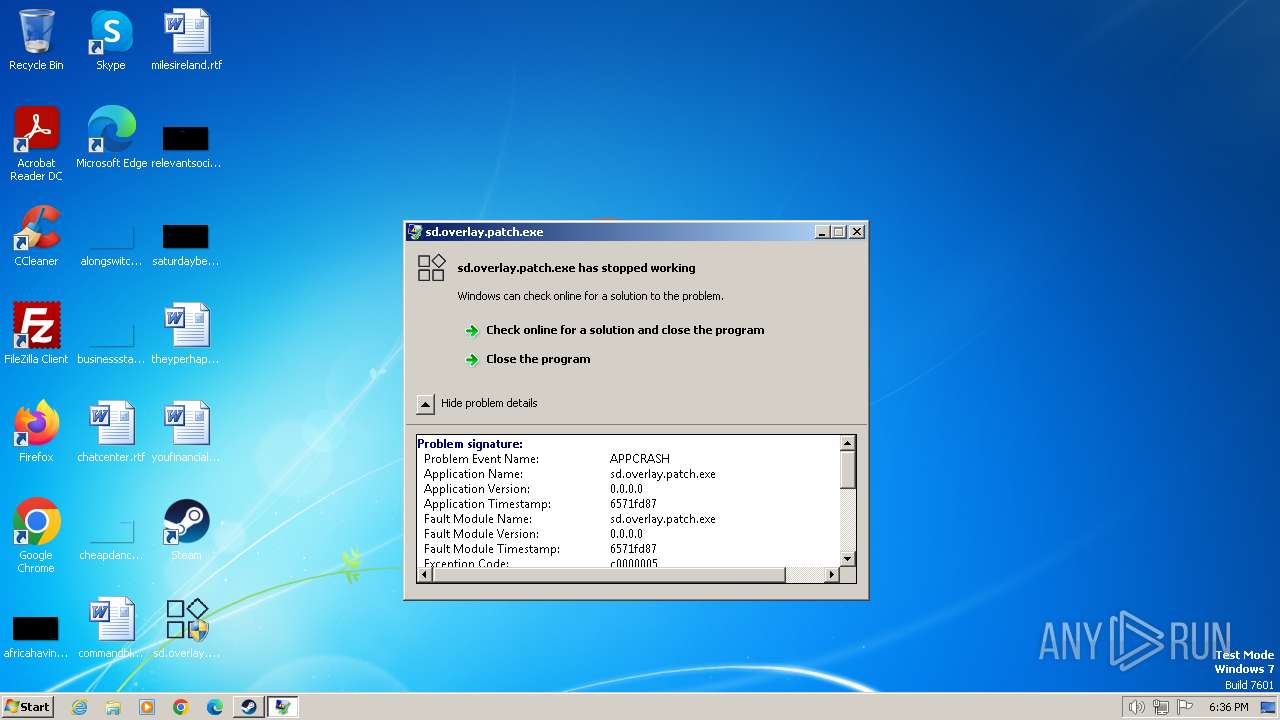
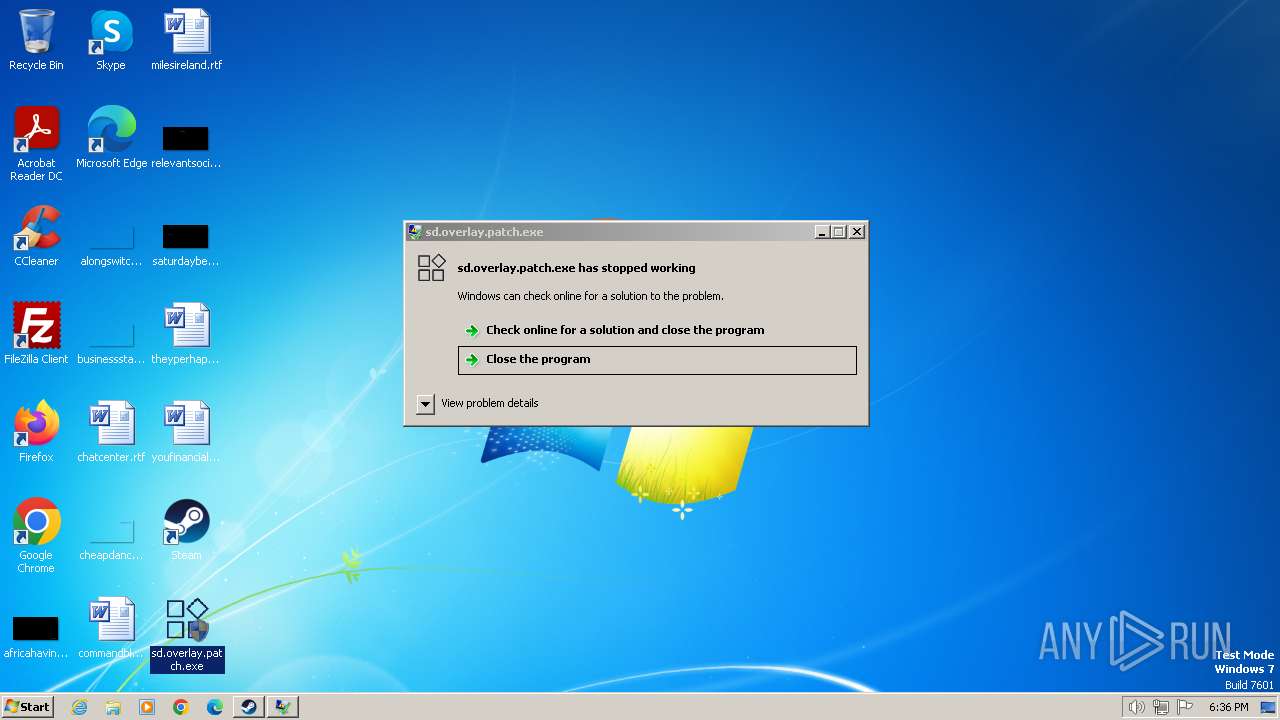
- sd.overlay.patch.exe (PID: 1876)
- sd.overlay.patch.exe (PID: 1644)
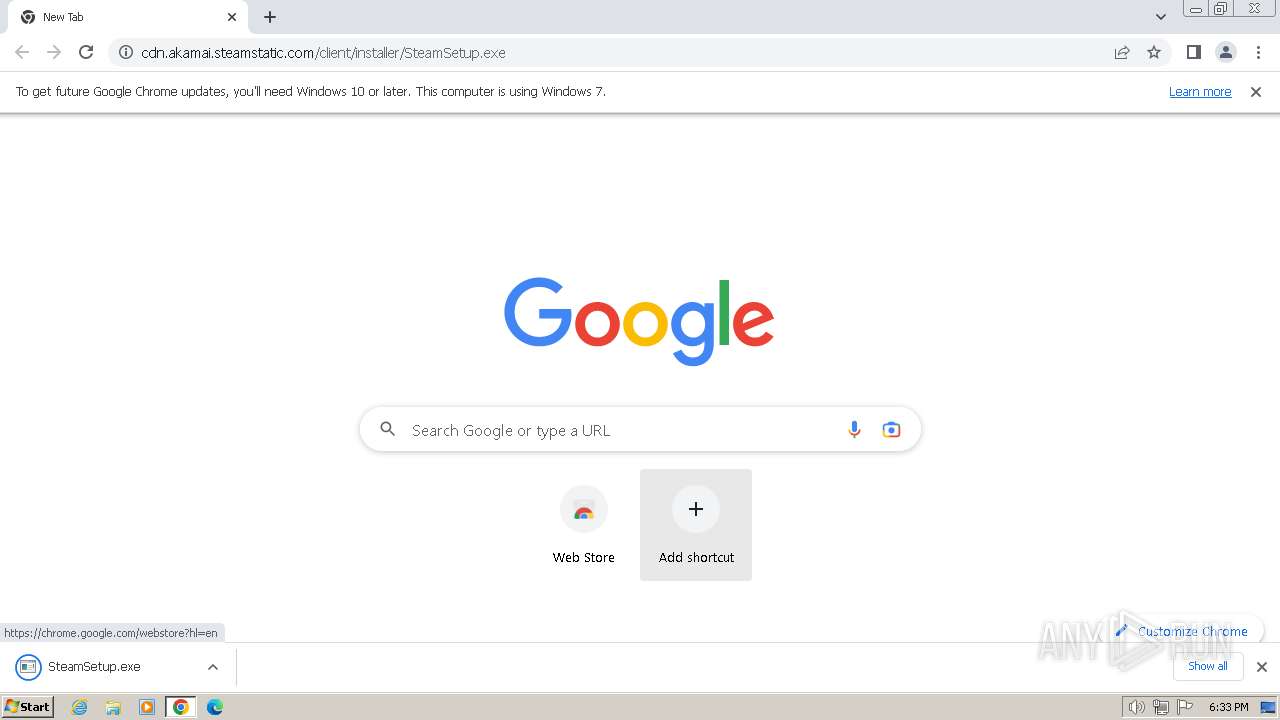
The process uses the downloaded file
- chrome.exe (PID: 1928)
- chrome.exe (PID: 3452)
Reads the computer name
- SteamSetup.exe (PID: 2640)
- Steam.exe (PID: 2068)
- steamservice.exe (PID: 712)
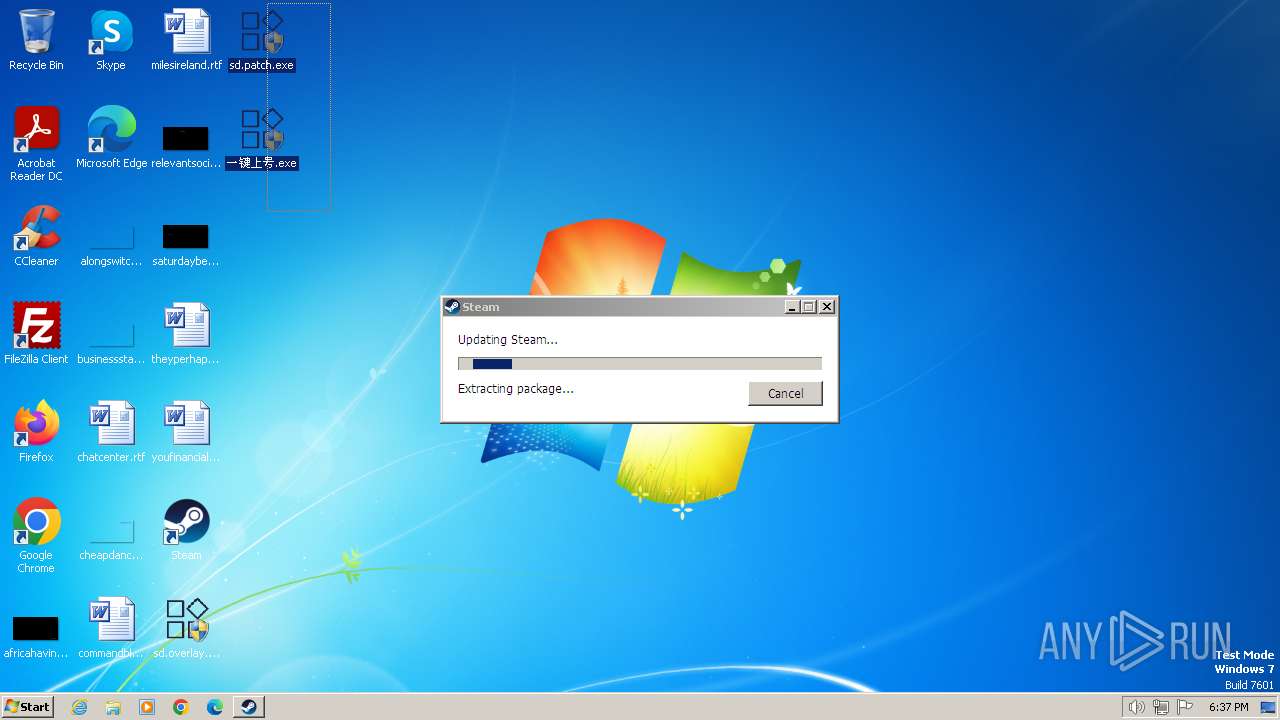
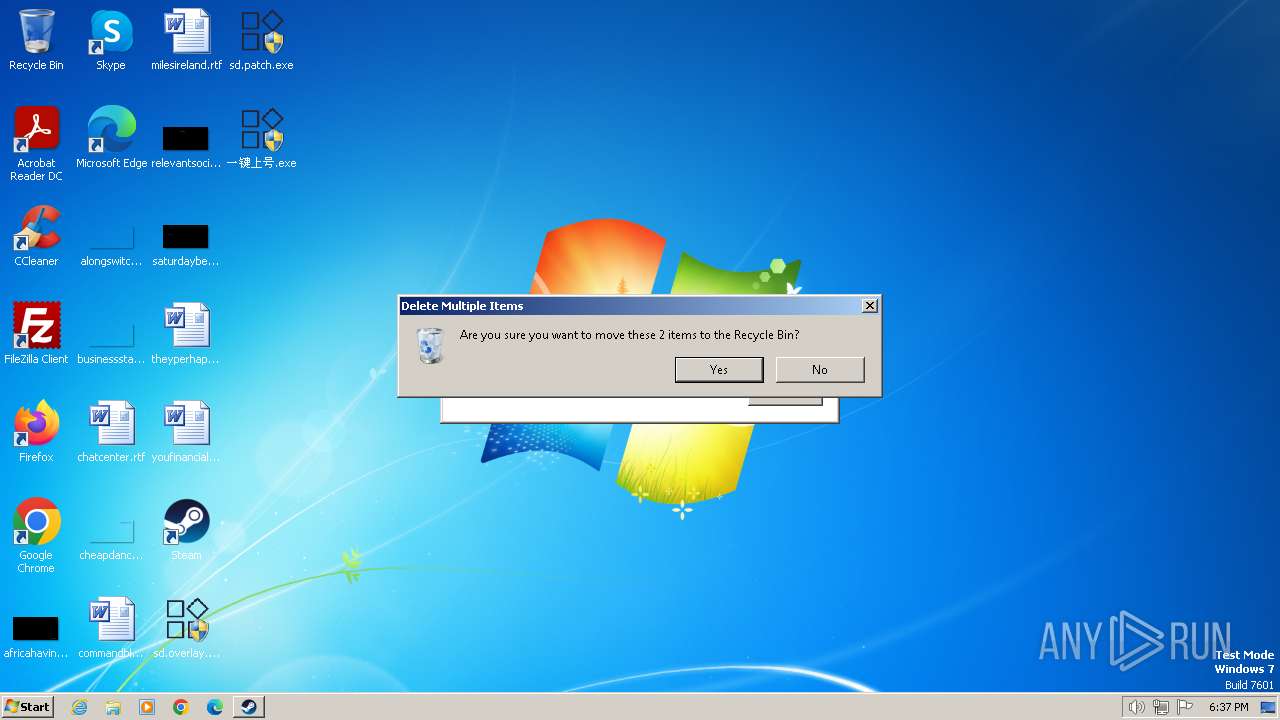
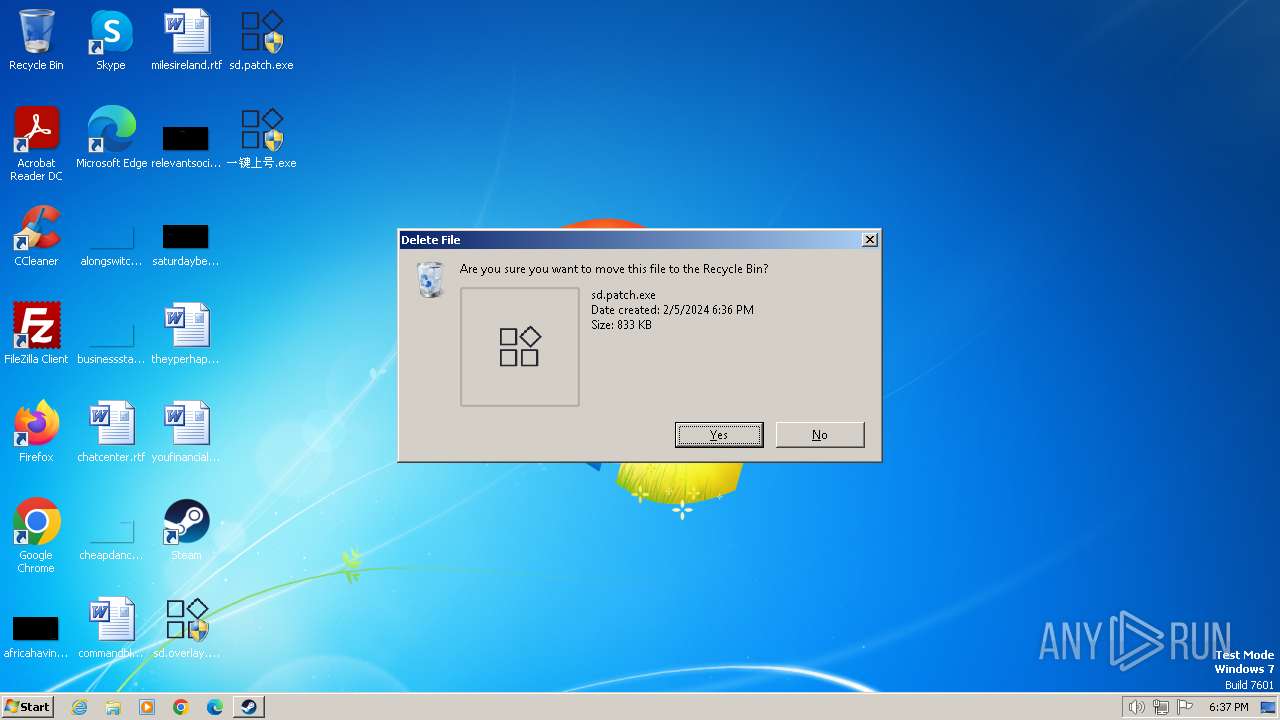
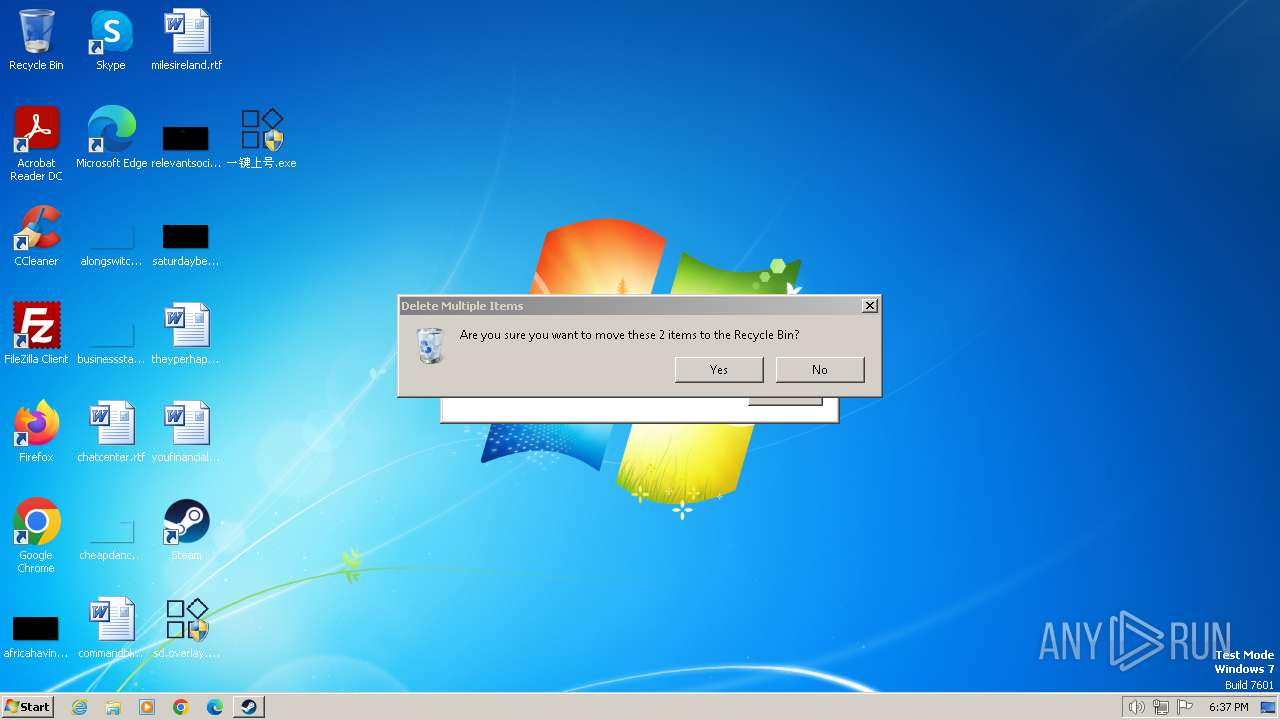
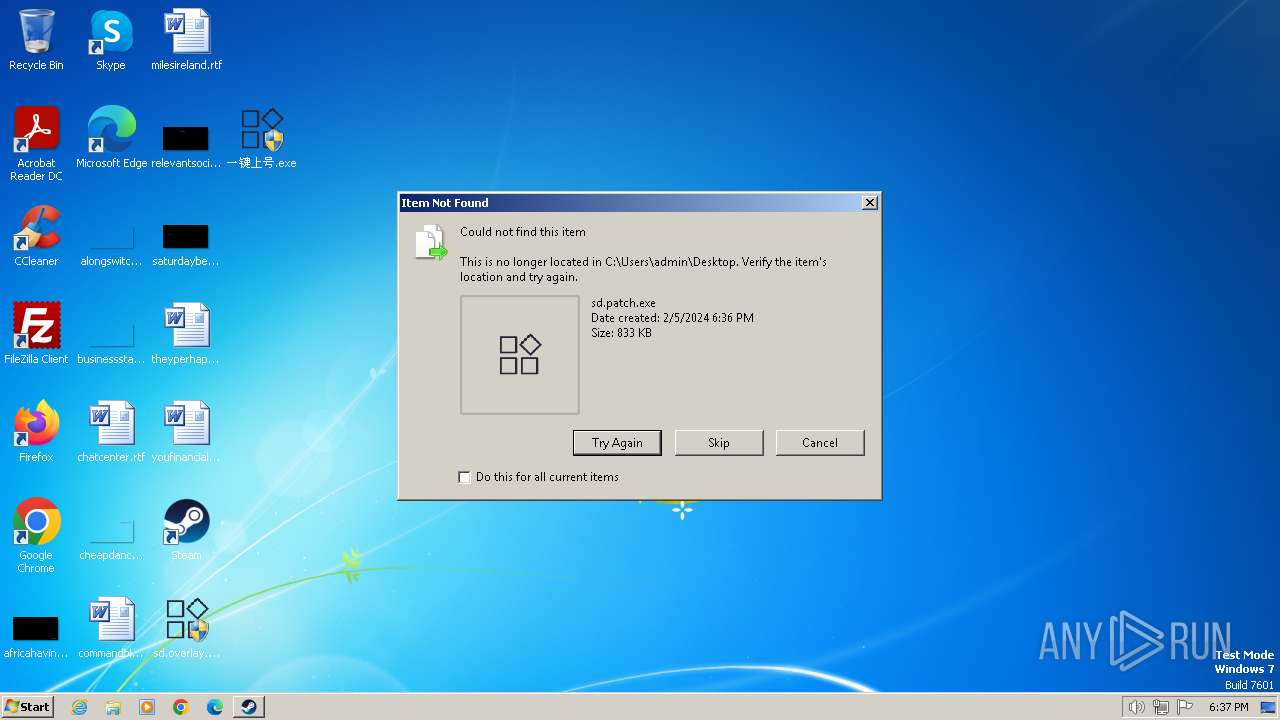
Manual execution by a user
- chrome.exe (PID: 3452)
- Steam.exe (PID: 2068)
- 一键上号.exe (PID: 3344)
- sd.patch.exe (PID: 2452)
- sd.patch.exe (PID: 3404)
- 一键上号.exe (PID: 2324)
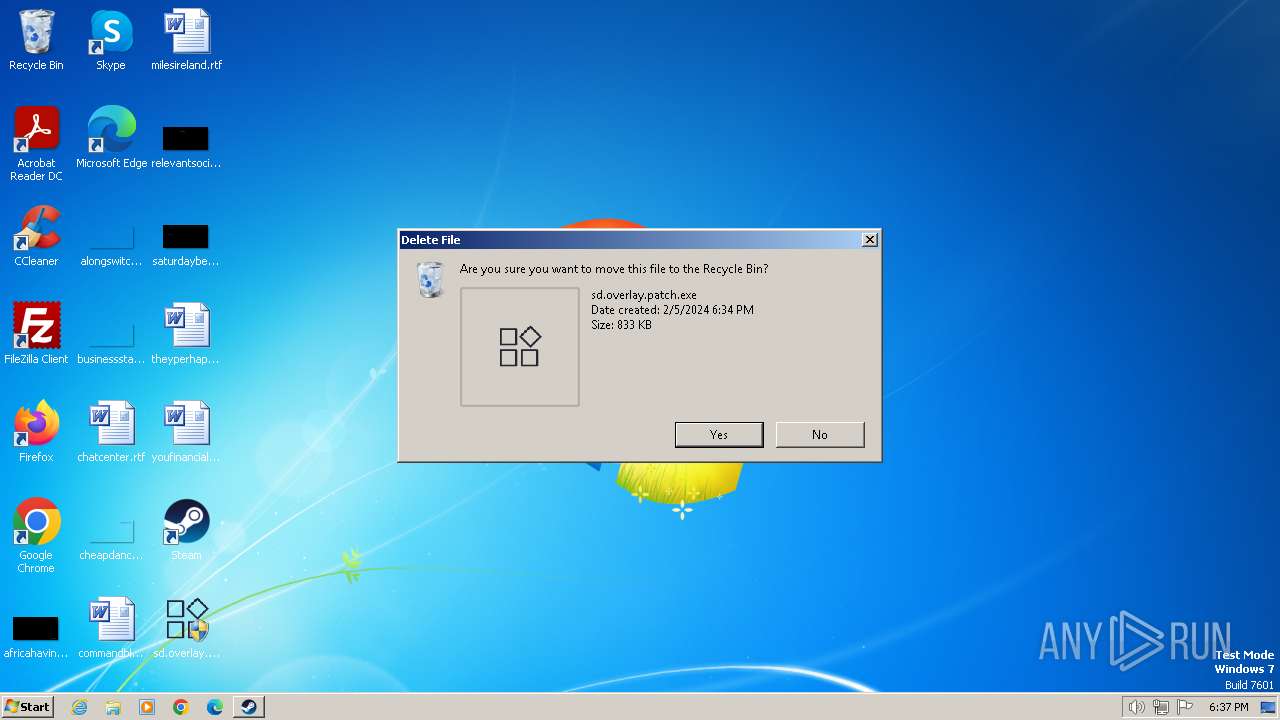
- sd.overlay.patch.exe (PID: 1588)
- sd.overlay.patch.exe (PID: 1876)
- sd.overlay.patch.exe (PID: 1656)
- sd.overlay.patch.exe (PID: 1644)
Create files in a temporary directory
- SteamSetup.exe (PID: 2640)
Creates files in the program directory
- steamservice.exe (PID: 712)
- Steam.exe (PID: 2068)
- SteamSetup.exe (PID: 2640)
Reads the machine GUID from the registry
- SteamSetup.exe (PID: 2640)
Reads CPU info
- Steam.exe (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
33
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | "C:\Program Files\Steam\bin\steamservice.exe" /Install | C:\Program Files\Steam\bin\steamservice.exe | nsCE35.tmp | ||||||||||||
User: admin Company: Valve Corporation Integrity Level: HIGH Description: Steam Client Service Exit code: 0 Version: 07.15.03.72 Modules
| |||||||||||||||
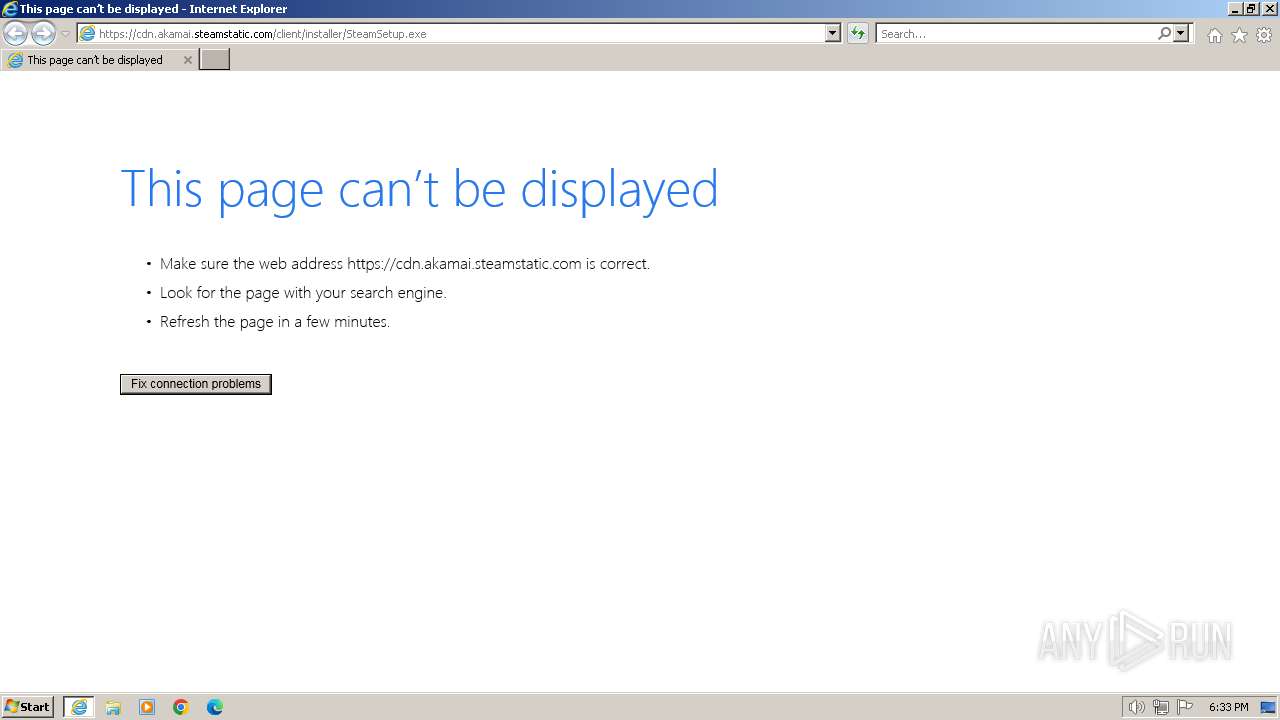
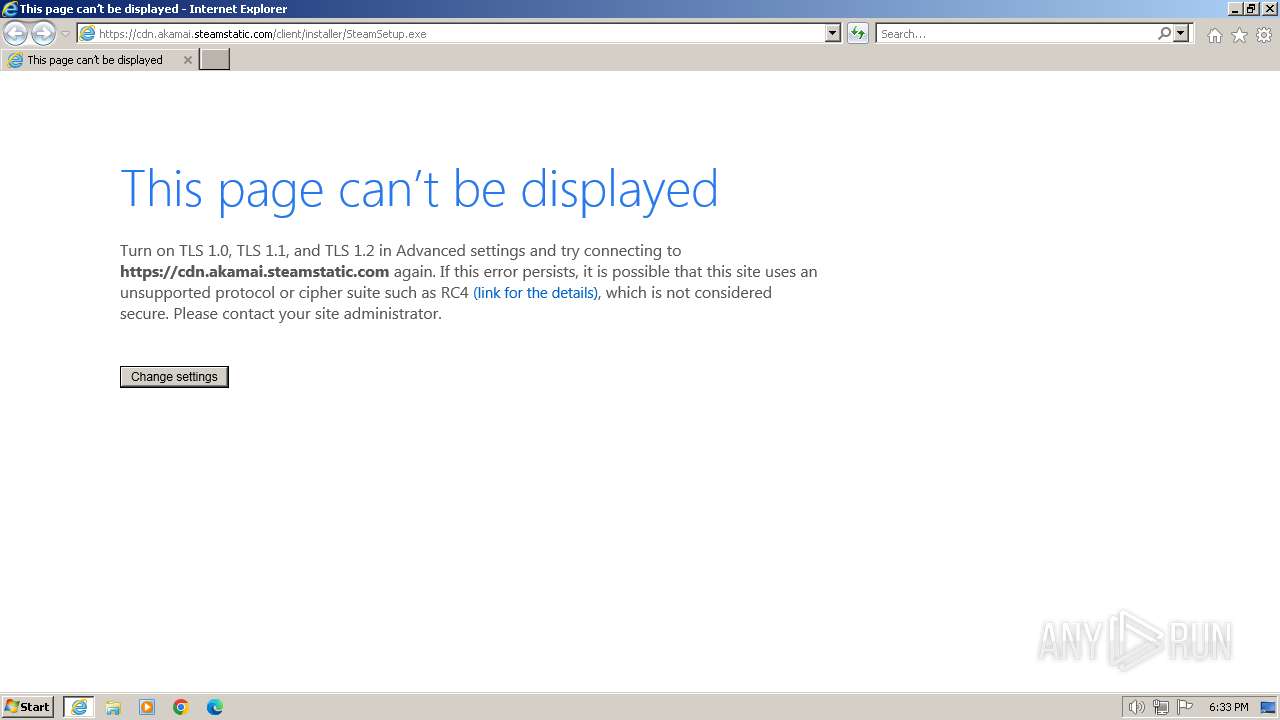
| 752 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cdn.akamai.steamstatic.com/client/installer/SteamSetup.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3420 --field-trial-handle=1164,i,2532196339168984491,11293414647763908868,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4516 --field-trial-handle=1164,i,2532196339168984491,11293414647763908868,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1588 | "C:\Users\admin\Desktop\sd.overlay.patch.exe" | C:\Users\admin\Desktop\sd.overlay.patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\Desktop\sd.overlay.patch.exe" | C:\Users\admin\Desktop\sd.overlay.patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 1656 | "C:\Users\admin\Desktop\sd.overlay.patch.exe" | C:\Users\admin\Desktop\sd.overlay.patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4480 --field-trial-handle=1164,i,2532196339168984491,11293414647763908868,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\Desktop\sd.overlay.patch.exe" | C:\Users\admin\Desktop\sd.overlay.patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4380 --field-trial-handle=1164,i,2532196339168984491,11293414647763908868,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
15 303
Read events
15 126
Write events
170
Delete events
7
Modification events
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
14
Suspicious files
260
Text files
2 390
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF169b1c.TMP | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:A1E0D07666D36FB36727F60DC0B3095C | SHA256:7230890A5BF83B5878B2D9AB6D94A234979D14D8D4F1DC57BB75B6498101D8EC | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:1FC5F643A92316FB87BEE154DC70EFA7 | SHA256:FE7FC83D97379CCE69B26AC4B6F5273515F677DA29AEA65C57691971F4599ECF | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3387B80255650BC9.TMP | binary | |
MD5:8BD8C49138872D1CCE6BE9FDCF1EE56B | SHA256:3681E4D7361B3429815A1FF81C45F88A981046E48E095702CC1D45F6B5820D41 | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF512E359EFE72C2B0.TMP | binary | |
MD5:2DB6477B7C08AE50FE48B43431B52D53 | SHA256:5BA23261EBA1BD050B6D03F9294BDF90CB4735E5F28C853858772CEB87214E18 | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF60F7B81B1289B5AF.TMP | binary | |
MD5:7362BD84D810EE0601E526AD84AEA0B5 | SHA256:D516E4DBBAFD5C7BE0DC2FCC8D769EB6E4FBD03BC6D0D465CF4BB73631AEF4E4 | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:DF27BED4360EBE730C6F726E26DD3B4F | SHA256:92D4499AD3B0029A492DF4D25E78A7AD241BDFB02E4800B6D17A591AE5346915 | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
35
DNS requests
27
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
752 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2f21ede4db813e6d | unknown | — | — | unknown |
752 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4c4bae6a1643aa04 | unknown | — | — | unknown |
752 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
752 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fc91d912a85a08d5 | unknown | compressed | 65.2 Kb | unknown |
1080 | svchost.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1dd404ff67a3d8ee | unknown | compressed | 65.2 Kb | unknown |
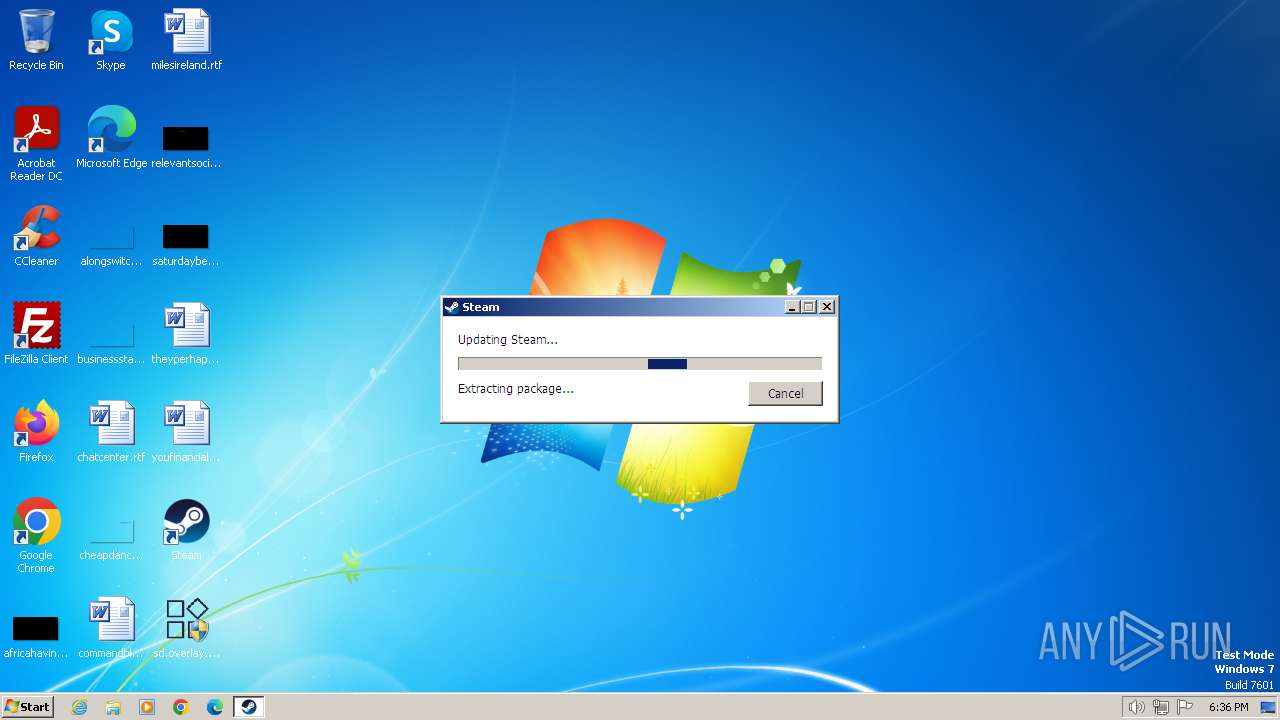
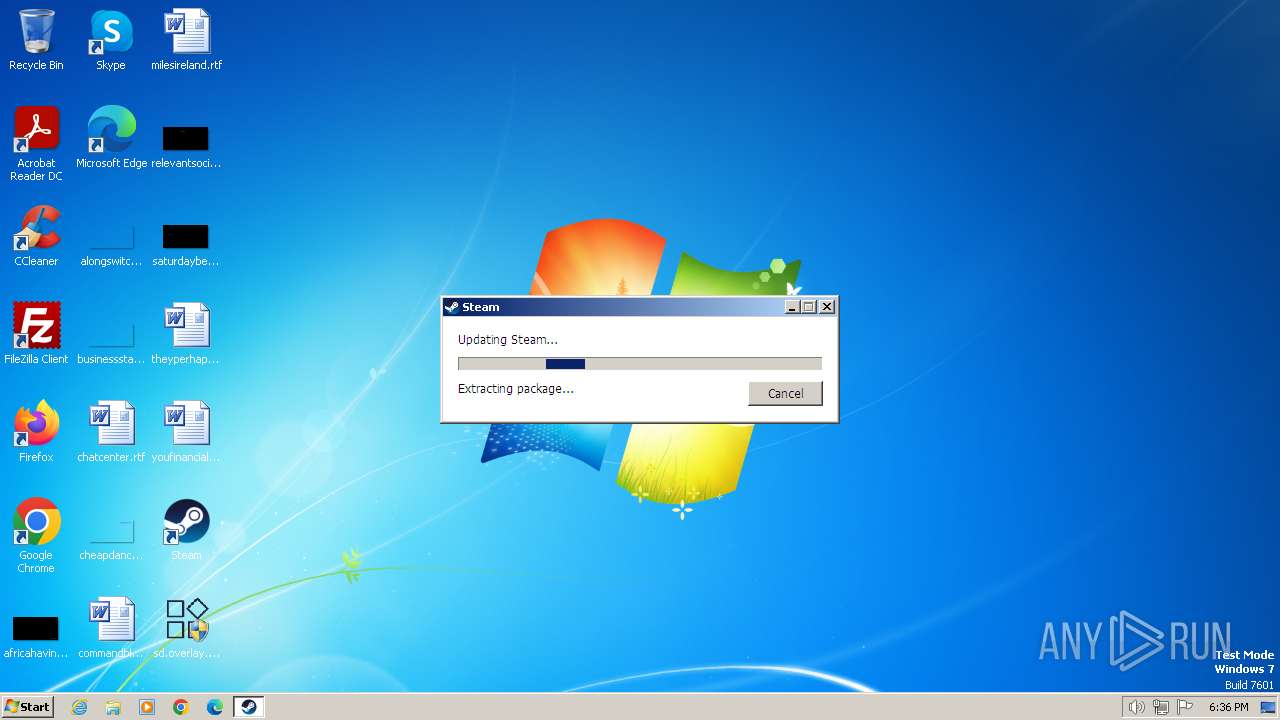
2068 | Steam.exe | GET | 200 | 184.24.77.33:80 | http://media.steampowered.com/client/steam_client_win32 | unknown | text | 3.63 Kb | unknown |
2068 | Steam.exe | GET | 200 | 184.24.77.33:80 | http://media.steampowered.com/client/tenfoot_images_all.zip.vz.193cb8c4eb4446698ea2c0a9e8c4e6b6a623dac7_5572671 | unknown | binary | 5.31 Mb | unknown |
2068 | Steam.exe | GET | 200 | 184.24.77.33:80 | http://media.steampowered.com/client/resources_misc_all.zip.vz.e86a975545f3ab21a77373870cb311ef93934b8c_2224876 | unknown | binary | 2.12 Mb | unknown |
2068 | Steam.exe | GET | 200 | 184.24.77.33:80 | http://media.steampowered.com/client/steamui_websrc_all.zip.vz.83cdfb92d0b35c6f6716c814b4aaf3ce19b8c4a7_23814718 | unknown | binary | 22.7 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3988 | iexplore.exe | 95.101.54.121:443 | cdn.akamai.steamstatic.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
752 | iexplore.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | unknown |
752 | iexplore.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
752 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3820 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3452 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3820 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.akamai.steamstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2068 | Steam.exe | Potential Corporate Privacy Violation | ET USER_AGENTS Steam HTTP Client User-Agent |
17 ETPRO signatures available at the full report