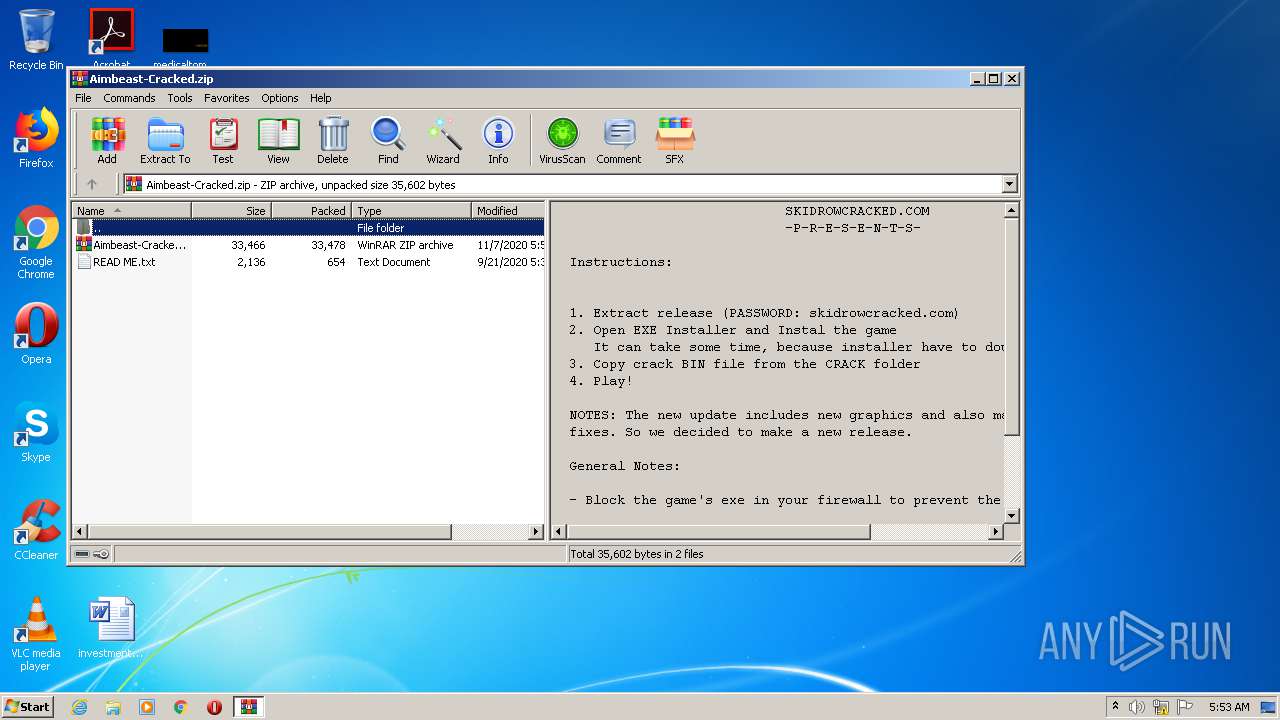
| File name: | Aimbeast-Cracked.zip |
| Full analysis: | https://app.any.run/tasks/5f2296b9-75e5-48eb-a652-a6c985208d90 |
| Verdict: | No threats detected |
| Analysis date: | November 07, 2020, 05:53:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 0F2010E172E972C99E69A2A4AC58A853 |
| SHA1: | FE5F522083C62CC9D35DE2447D59BF457F171321 |
| SHA256: | C0976C3349DB6BD72511B0DF20B6E44D94B5246D6F6BC4676DB71885B51B1532 |
| SSDEEP: | 768:u75XMSuZTlWfPqe83LMpy2NpRV0ajqaB1qrh34lyW4H8UuU:LfZZeijCNpVWaXqrO4hV |
MALICIOUS
Application was dropped or rewritten from another process
- Aimbeast Installer.exe (PID: 1364)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 2384)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2828)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
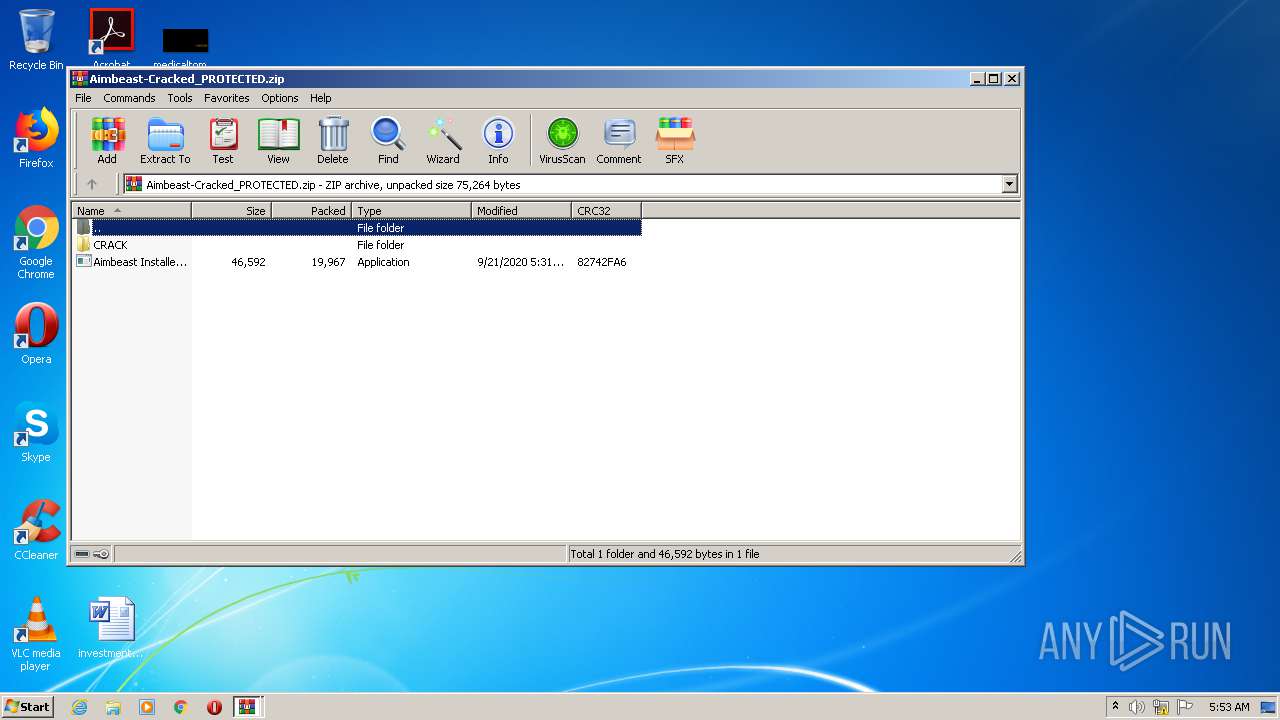
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | None |
| ZipModifyDate: | 2020:11:07 06:51:11 |
| ZipCRC: | 0xea284f1d |
| ZipCompressedSize: | 33478 |
| ZipUncompressedSize: | 33478 |
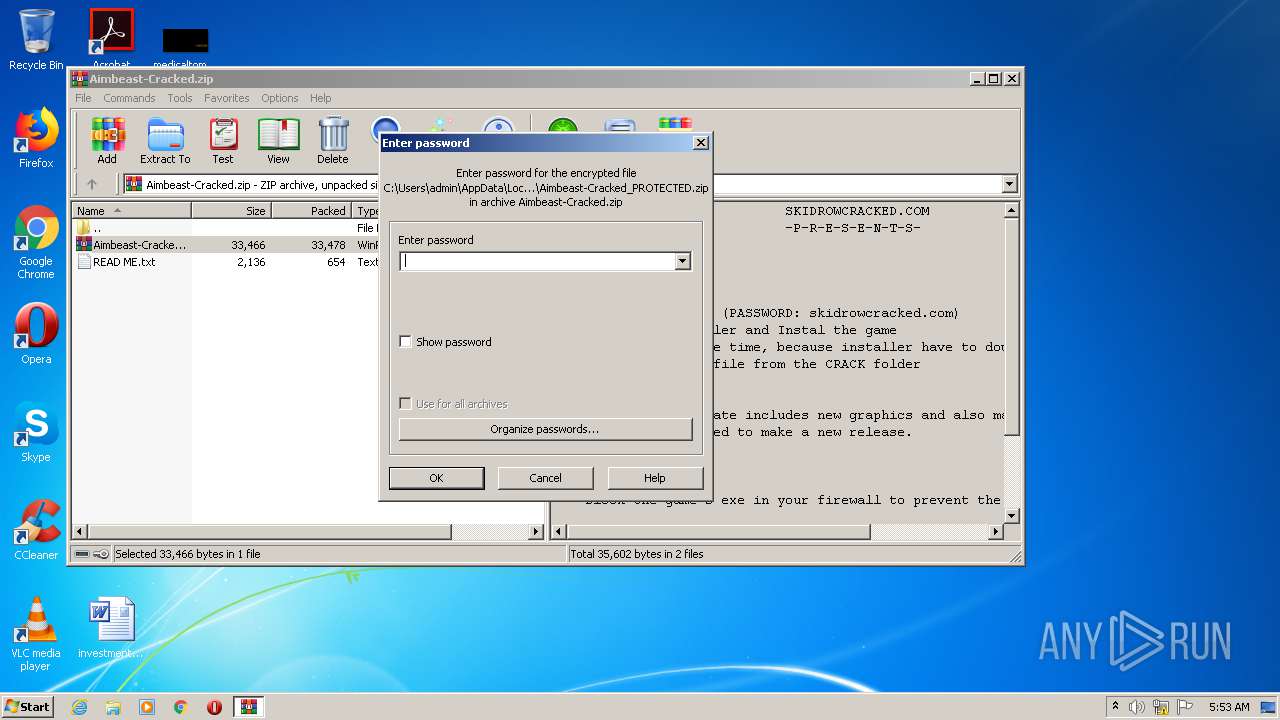
| ZipFileName: | Aimbeast-Cracked_PROTECTED.zip |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
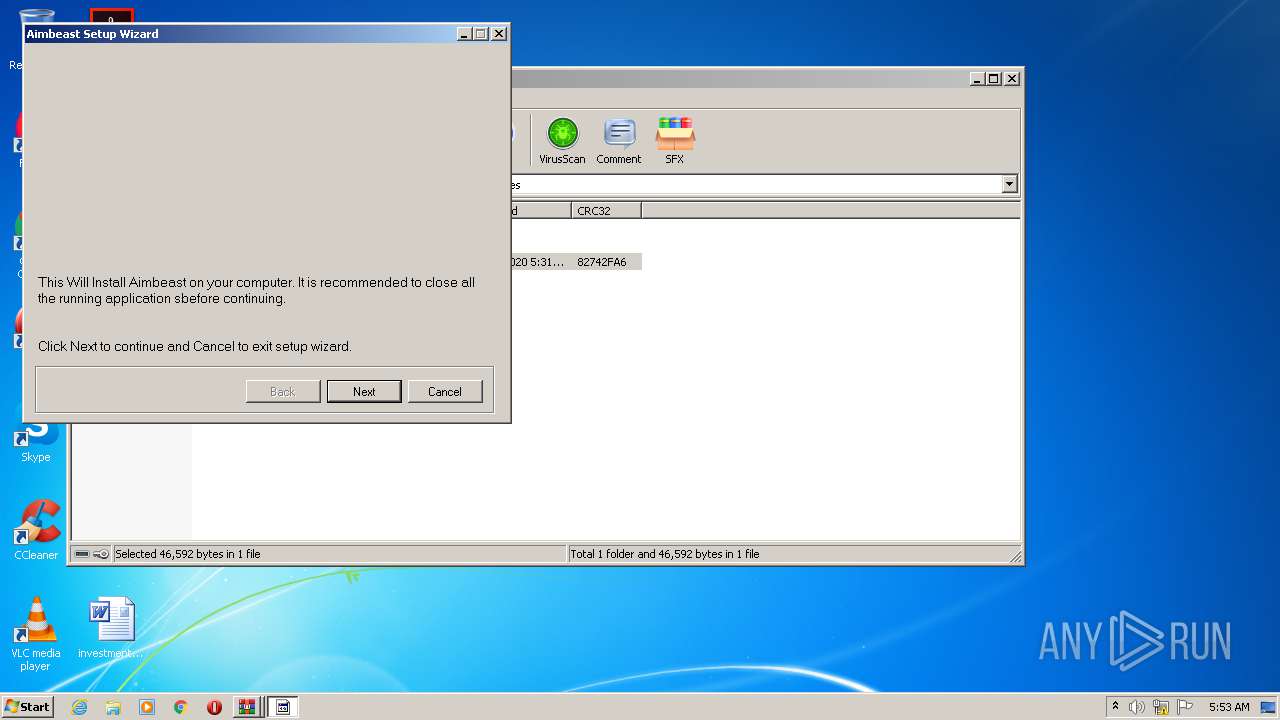
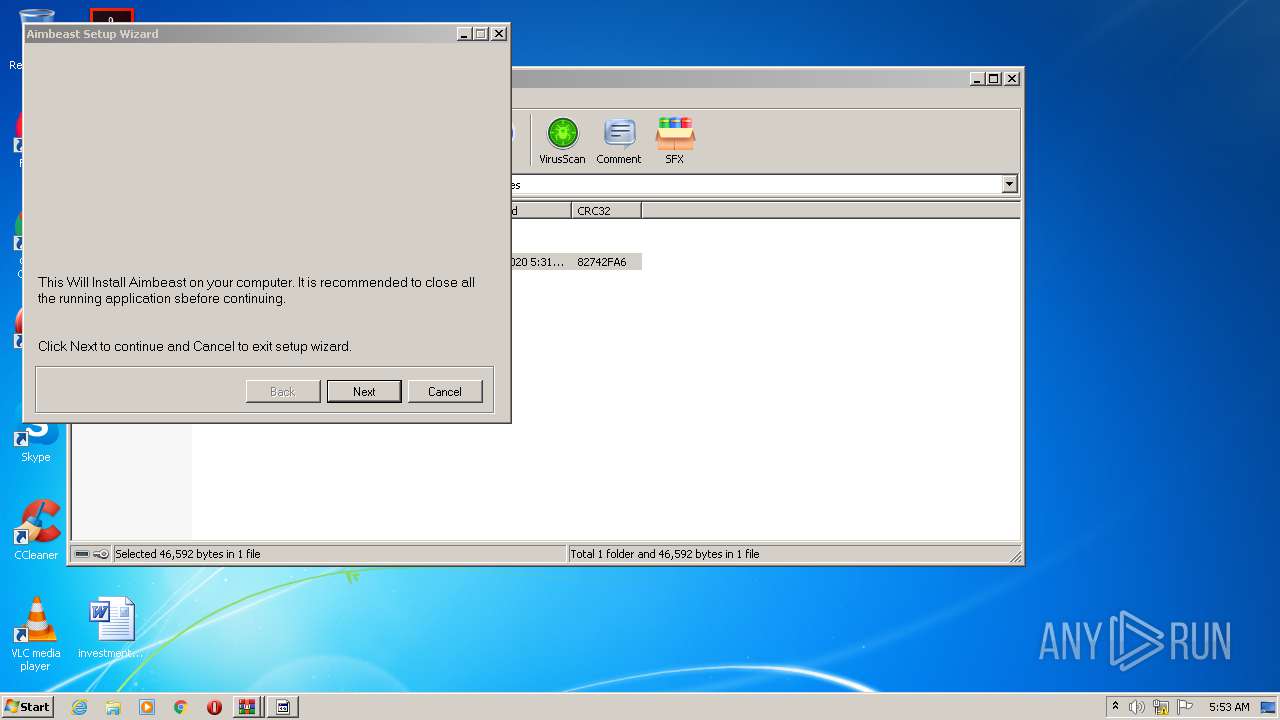
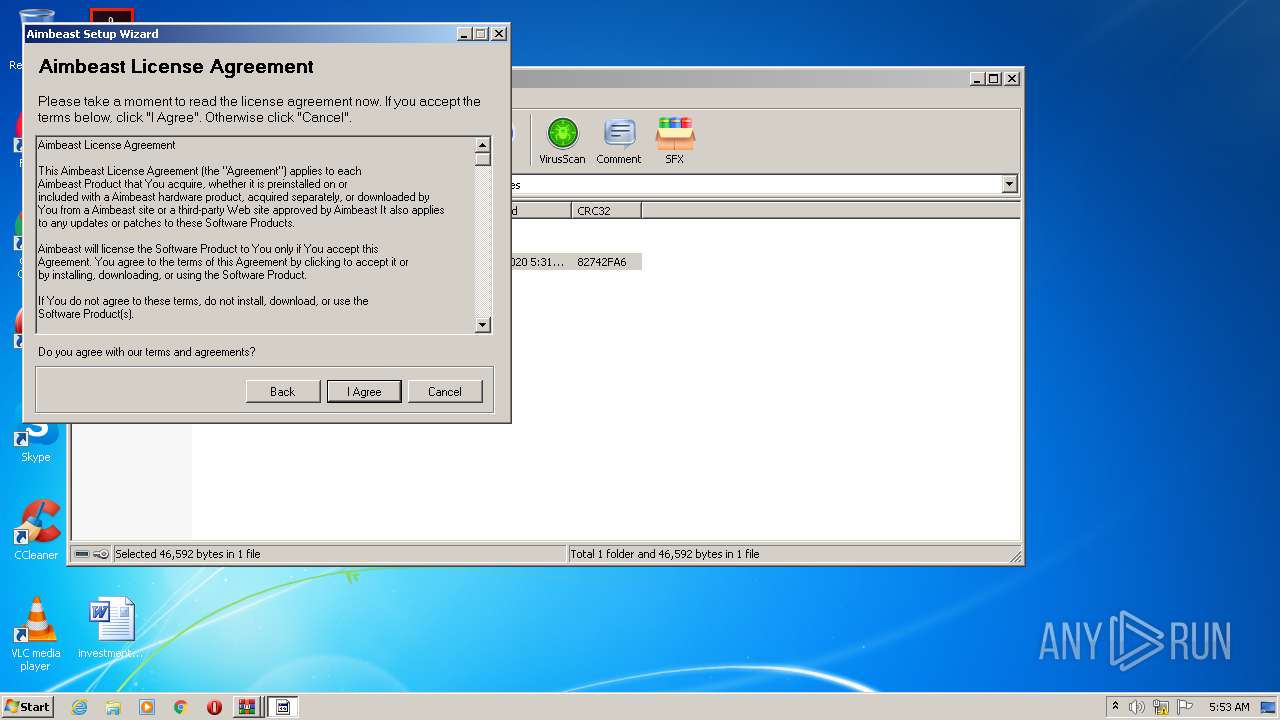
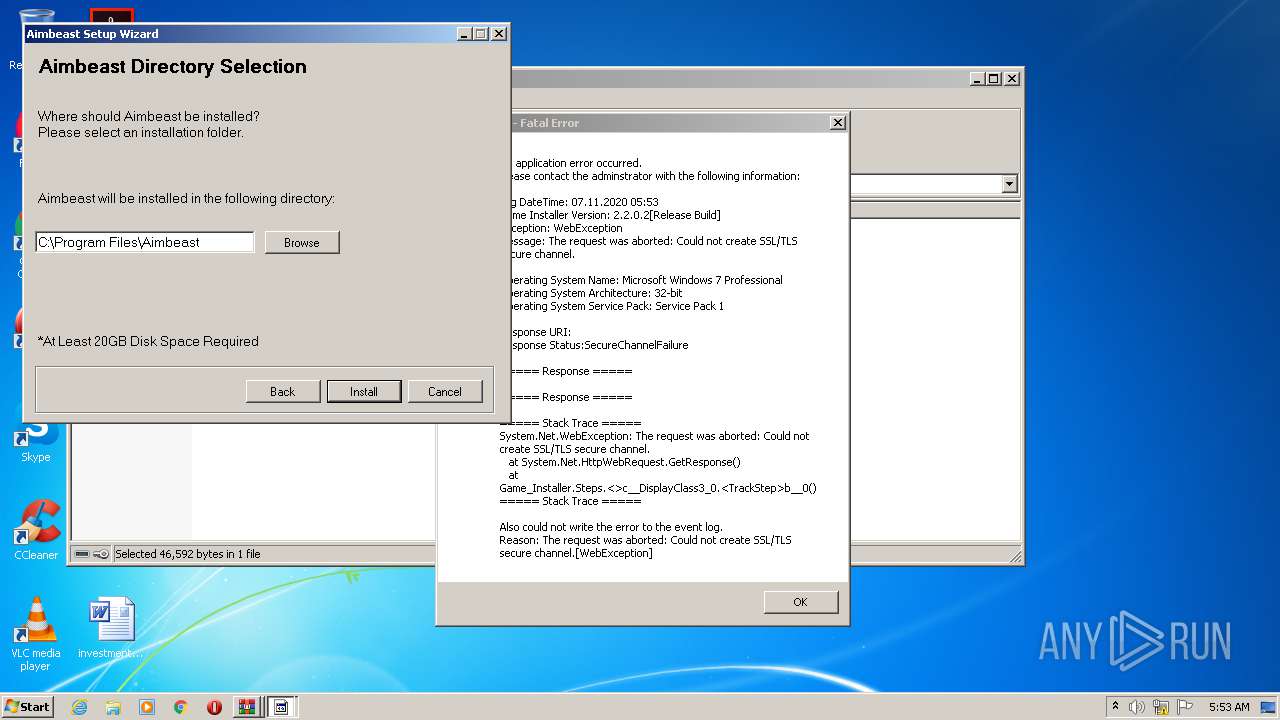
| 1364 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2828.25043\Aimbeast Installer.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2828.25043\Aimbeast Installer.exe | WinRAR.exe | ||||||||||||
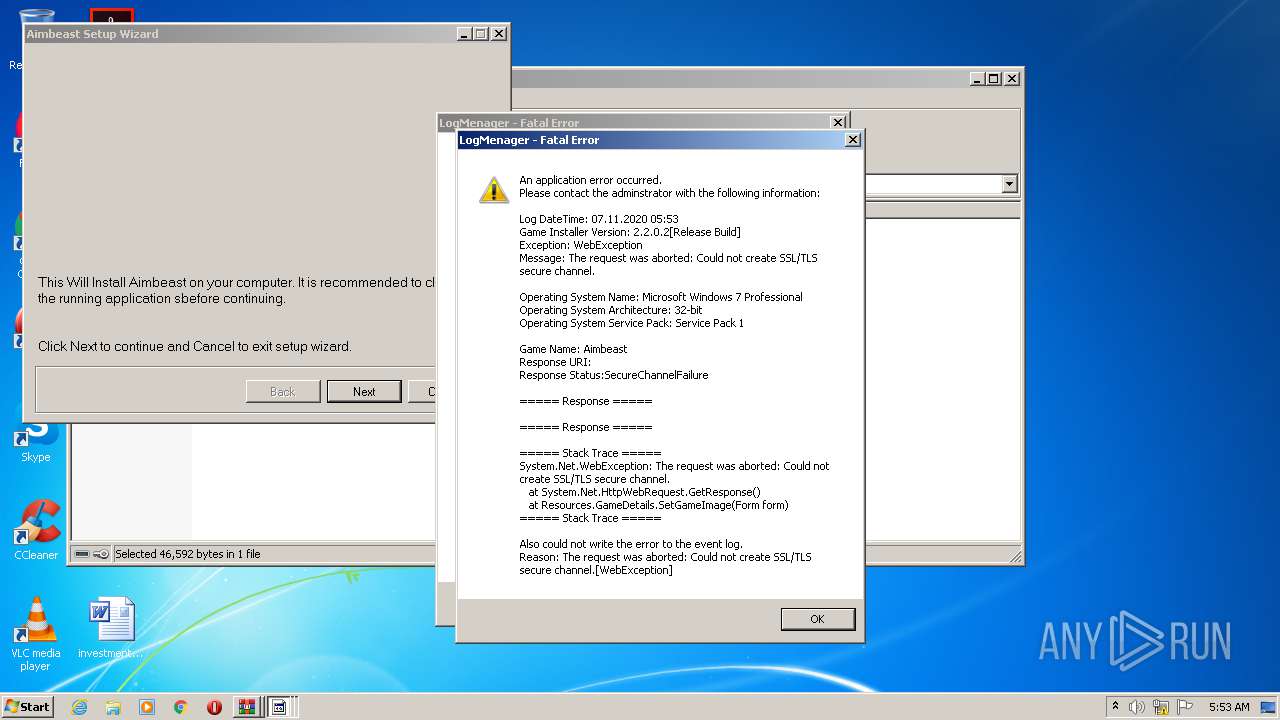
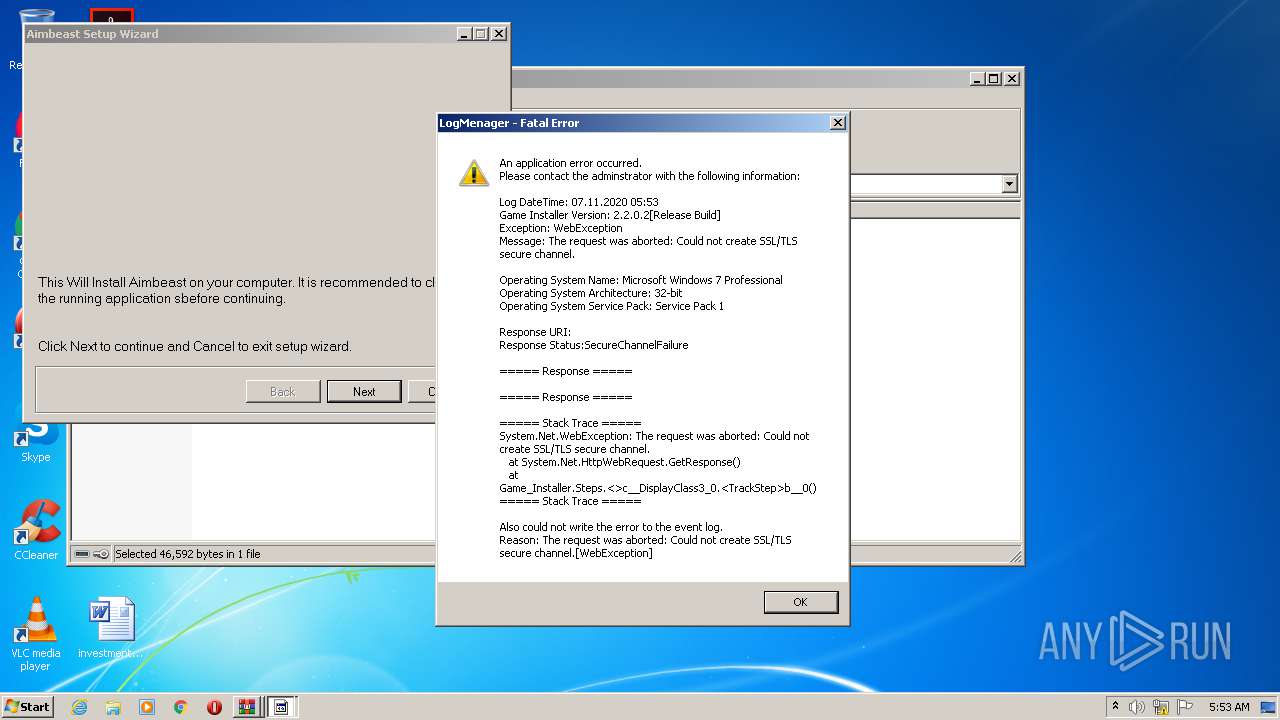
User: admin Integrity Level: MEDIUM Description: Game Installer Exit code: 0 Version: 2.2.0.2 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Aimbeast-Cracked.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb2384.23812\Aimbeast-Cracked_PROTECTED.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
980
Read events
941
Write events
39
Delete events
0
Modification events
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Aimbeast-Cracked.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2828.25043\Aimbeast Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2384.23812\Aimbeast-Cracked_PROTECTED.zip | compressed | |
MD5:— | SHA256:— | |||
| 2828 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2828.25043\CRACK\Aimbeast Crack.exe | executable | |
MD5:00A2F964F71D6F1DD6EEDF62DE0E42BC | SHA256:0919835B7DBA1DFB4152B8E378B93BB514F0D0811C5624872198286018923A2B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
13
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1364 | Aimbeast Installer.exe | GET | 301 | 144.91.64.196:80 | http://sc-contentlocker.com/installer.php?step=Start&game=Aimbeast | US | html | 706 b | malicious |
1364 | Aimbeast Installer.exe | GET | 301 | 144.91.64.196:80 | http://sc-contentlocker.com/installer.php?step=Default&game=Aimbeast | US | html | 706 b | malicious |
1364 | Aimbeast Installer.exe | GET | 301 | 144.91.64.196:80 | http://skidrowcracked.com/post-thumbnail/?password=eo8kcu%3EMk0hN&title=Aimbeast | US | html | 706 b | suspicious |
1364 | Aimbeast Installer.exe | GET | 301 | 144.91.64.196:80 | http://sc-contentlocker.com/installer.php?step=Agreement&game=Aimbeast | US | html | 706 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1364 | Aimbeast Installer.exe | 144.91.64.196:80 | skidrowcracked.com | Mills College | US | suspicious |
— | — | 144.91.64.196:443 | skidrowcracked.com | Mills College | US | suspicious |
1364 | Aimbeast Installer.exe | 144.91.64.196:443 | skidrowcracked.com | Mills College | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
skidrowcracked.com |
| suspicious |
sc-contentlocker.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1364 | Aimbeast Installer.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1364 | Aimbeast Installer.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |