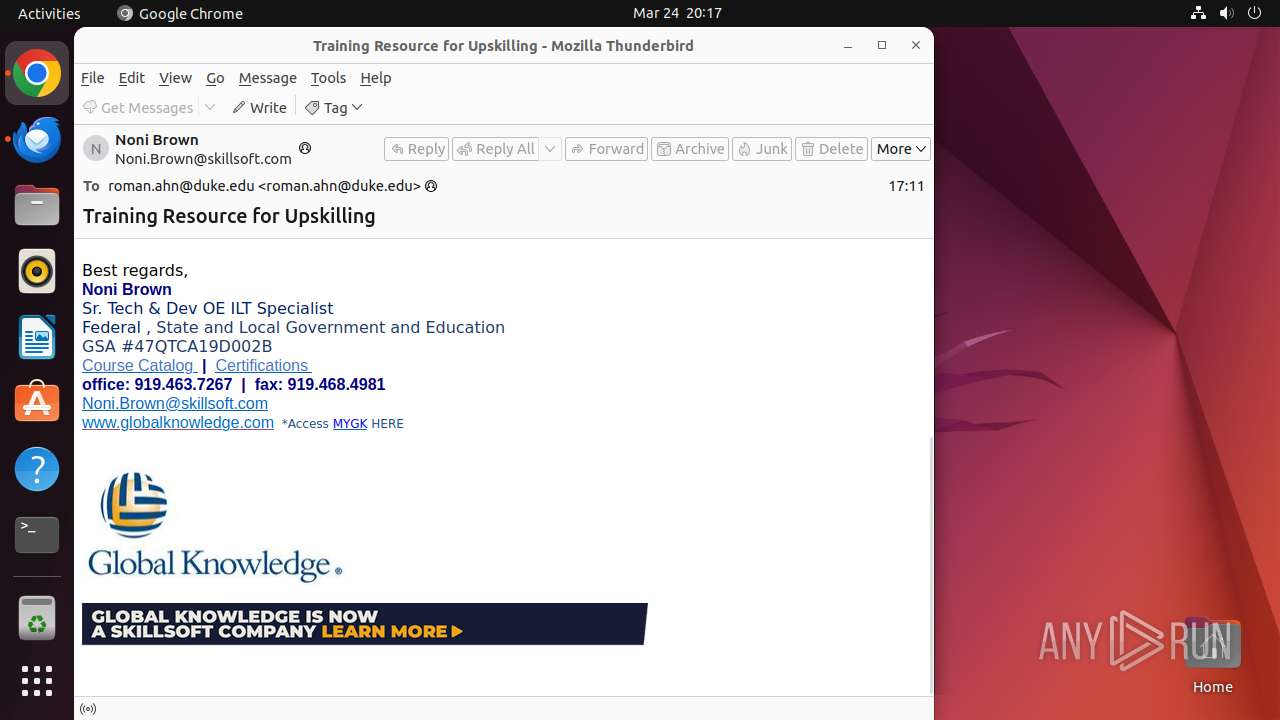
| File name: | email.eml |
| Full analysis: | https://app.any.run/tasks/16119230-bbb6-4ce9-b4ee-2484ab522f96 |
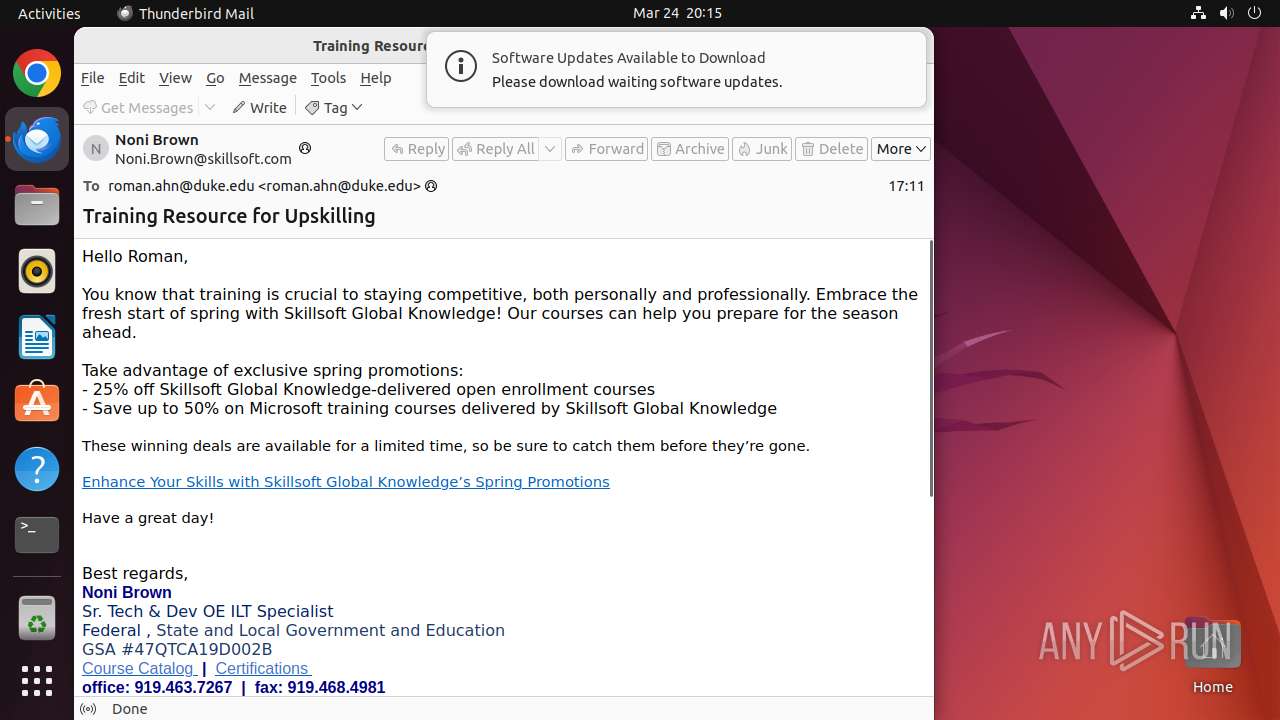
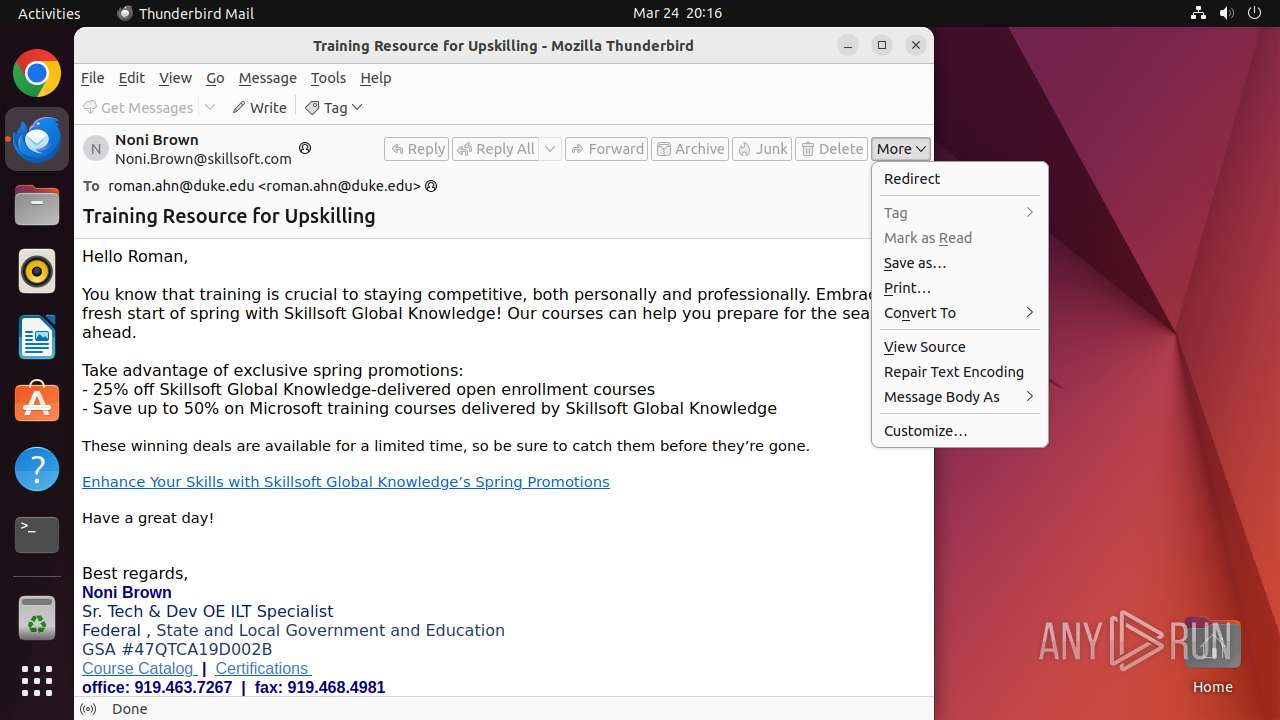
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 20:15:45 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines (347), with CRLF line terminators |
| MD5: | 7E9EE4C46E95C973BC84B2F90B7F3253 |
| SHA1: | EAF6C261018AEC77D0A92E0C000A3154D02A119C |
| SHA256: | C082DD12C4C21D3B6F23D8DC7E52D1A37985D1A9AF3F29F4C7BFBBE978606887 |
| SSDEEP: | 1536:0PPekvJaY6w4o6kbhslzzTqa+0e/owGH80pYCFop9EMSddYS:0PB4o6kEfDe/ozH8xCFWiTn/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads passwd file
- thunderbird (PID: 40656)
- glxtest (PID: 40664)
Creates files in the user directory
- thunderbird (PID: 40656)
- glxtest (PID: 40664)
Check the Environment Variables Related to System Identification (os-release)
- thunderbird (PID: 40656)
- python3.10 (PID: 40682)
Reads profile file
- thunderbird (PID: 40656)
Reads /proc/mounts (likely used to find writable filesystems)
- thunderbird (PID: 40656)
INFO
Checks timezone
- thunderbird (PID: 40656)
- python3.10 (PID: 40682)
- chrome (PID: 41124)
- chrome (PID: 40805)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
393
Monitored processes
171
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 40654 | /bin/sh -c "DISPLAY=:0 sudo -iu user thunderbird /tmp/email\.eml " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 40655 | sudo -iu user thunderbird /tmp/email.eml | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40656 | /usr/lib/thunderbird/thunderbird /tmp/email.eml | /usr/lib/thunderbird/thunderbird | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 40657 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | thunderbird |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40658 | /bin/sh /usr/bin/which /usr/bin/thunderbird | /usr/bin/dash | — | thunderbird |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40659 | /usr/lib/thunderbird/thunderbird /tmp/email.eml | /usr/lib/thunderbird/thunderbird | — | thunderbird |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40664 | /usr/lib/thunderbird/glxtest -f 12 | /usr/lib/thunderbird/glxtest | — | thunderbird |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40682 | /usr/bin/python3 -Es /usr/bin/lsb_release -idrc | /usr/bin/python3.10 | — | thunderbird |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40761 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
2
Suspicious files
468
Text files
28
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40805 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40805 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40805 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 41124 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 41124 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 41124 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40805 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40805 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40805 | chrome | /home/user/.config/google-chrome/Default/Extension State/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40805 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
150
DNS requests
252
Threats
221
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
1178 | snap-store | 195.181.175.41:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
512 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40656 | thunderbird | 3.167.227.56:443 | services.addons.thunderbird.net | — | US | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40850 | chrome | 142.250.184.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
40850 | chrome | 172.217.23.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40850 | chrome | 52.71.28.102:443 | urldefense.com | AMAZON-AES | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
services.addons.thunderbird.net |
| whitelisted |
12.100.168.192.in-addr.arpa |
| unknown |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
urldefense.com |
| whitelisted |
accounts.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40850 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |