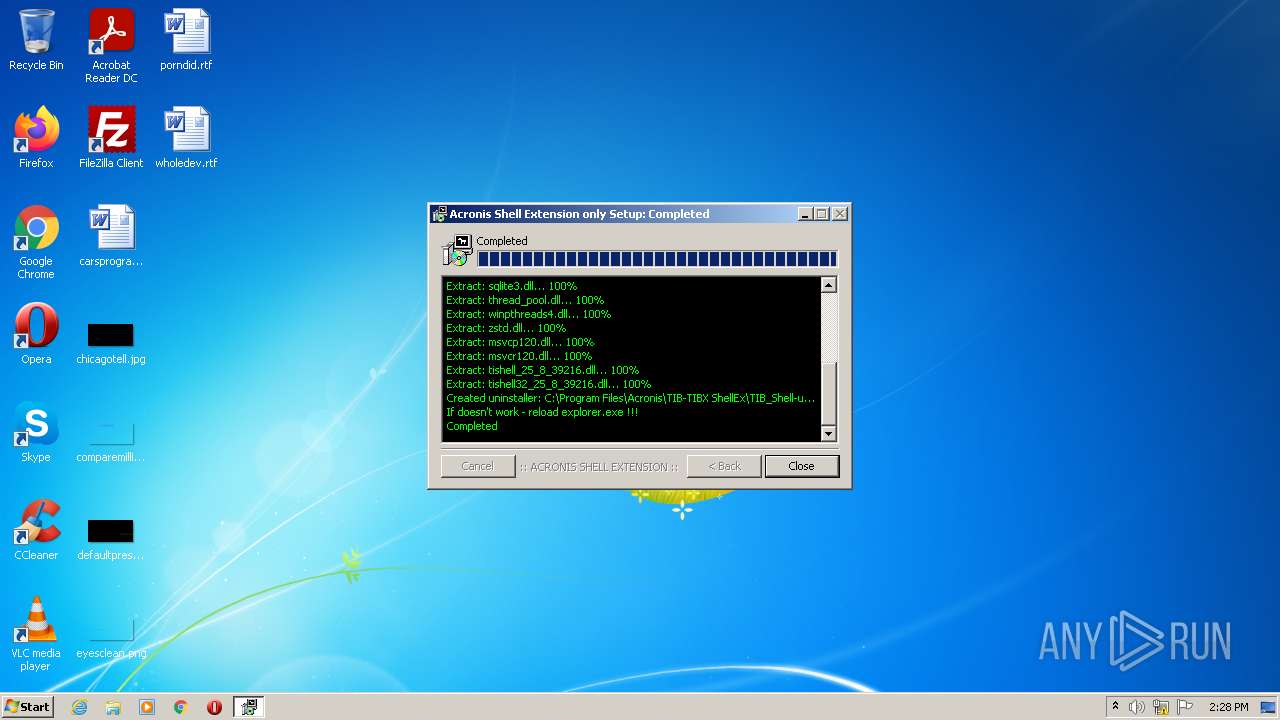
| File name: | TIB,TIBX-ShellEx-25.8.1.39216.exe |
| Full analysis: | https://app.any.run/tasks/485b79af-1171-40f2-9e2a-798a155cb3cd |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2022, 14:28:02 |
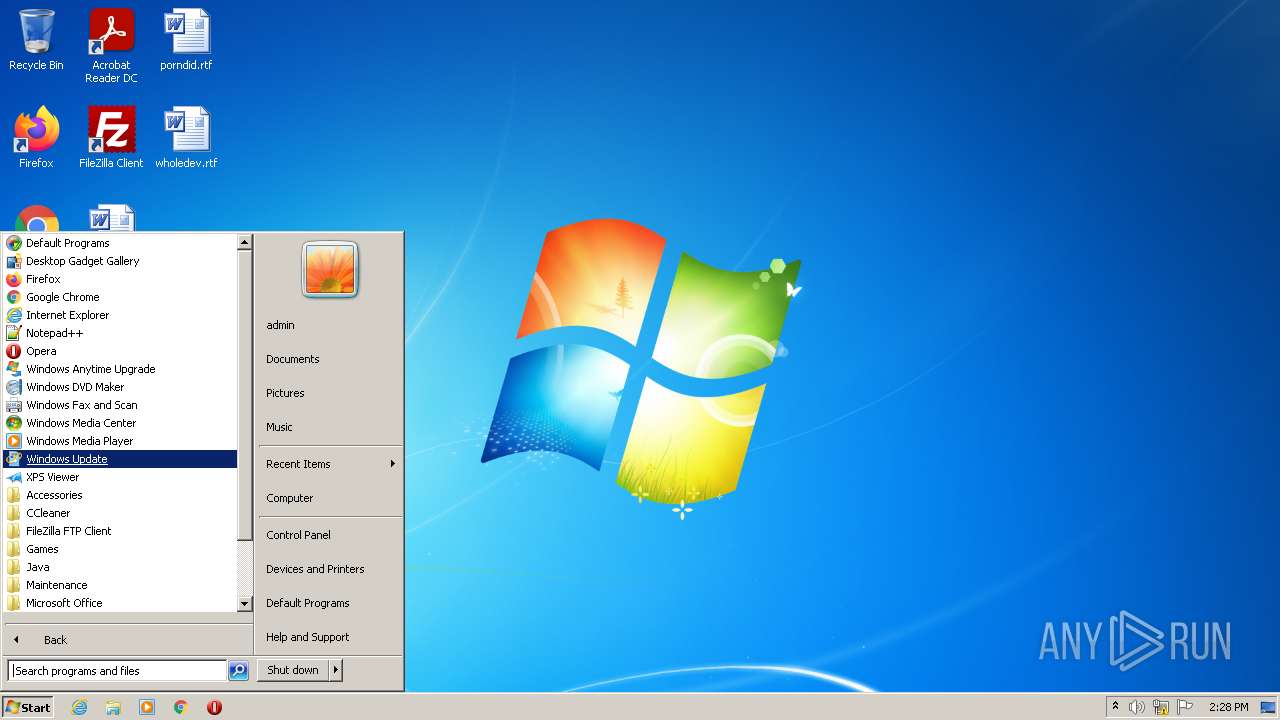
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 029AC5F90BFFEFEE0F0804058BE8B85D |
| SHA1: | 3390FF88FE068DC01B491754F9C37F3C4F71648A |
| SHA256: | C058D7643A6514945716676B2095629B37CA81F8E5A958901085E6EE68B203C7 |
| SSDEEP: | 393216:DzNKqKTtyeu6iX5efOsR1zhpdfuHdHMh3MHl19m4l/9NdM:fof5zoXoOsRPIsMJm4l/FM |
MALICIOUS
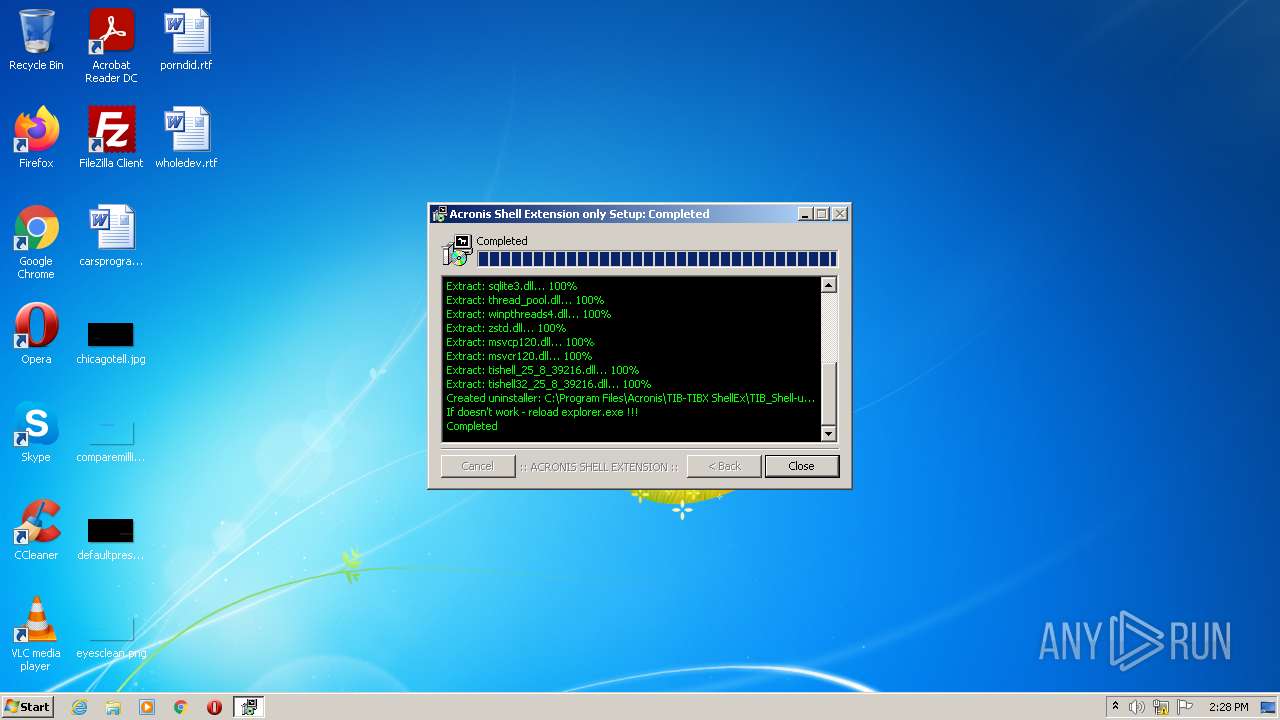
Drops executable file immediately after starts
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
Loads dropped or rewritten executable
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
SUSPICIOUS
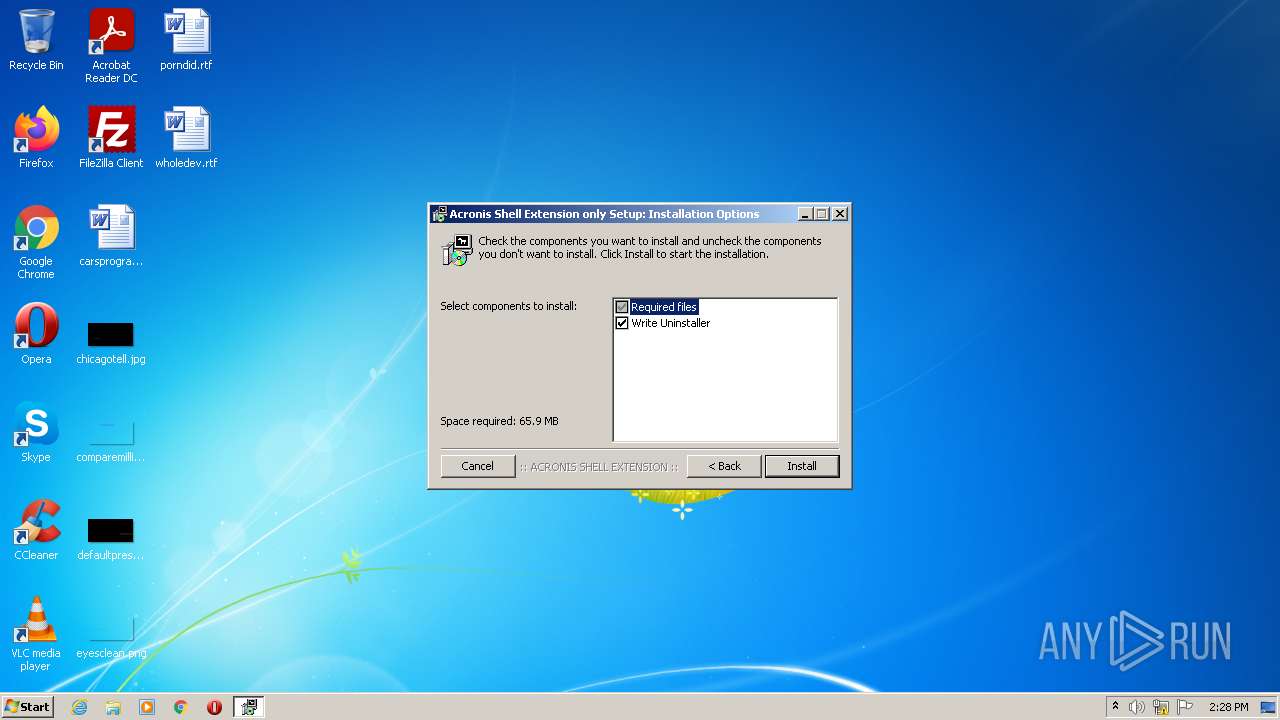
Executable content was dropped or overwritten
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
Reads the computer name
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
Checks supported languages
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
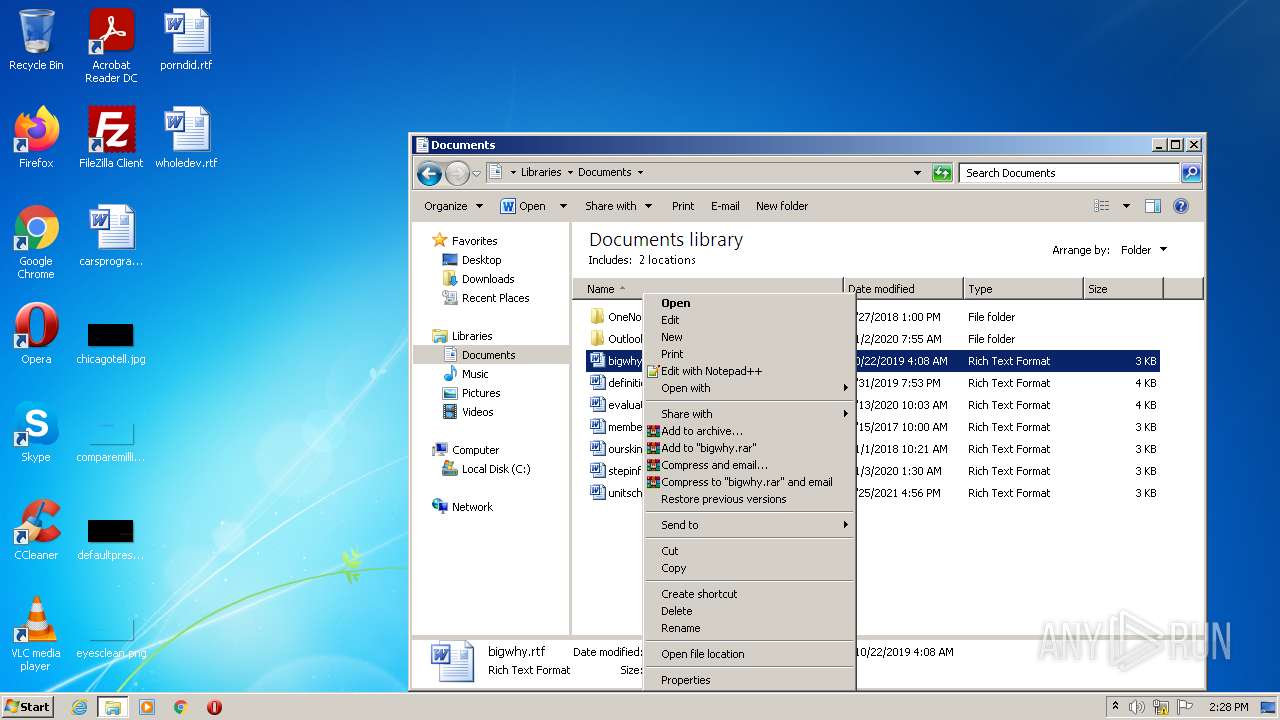
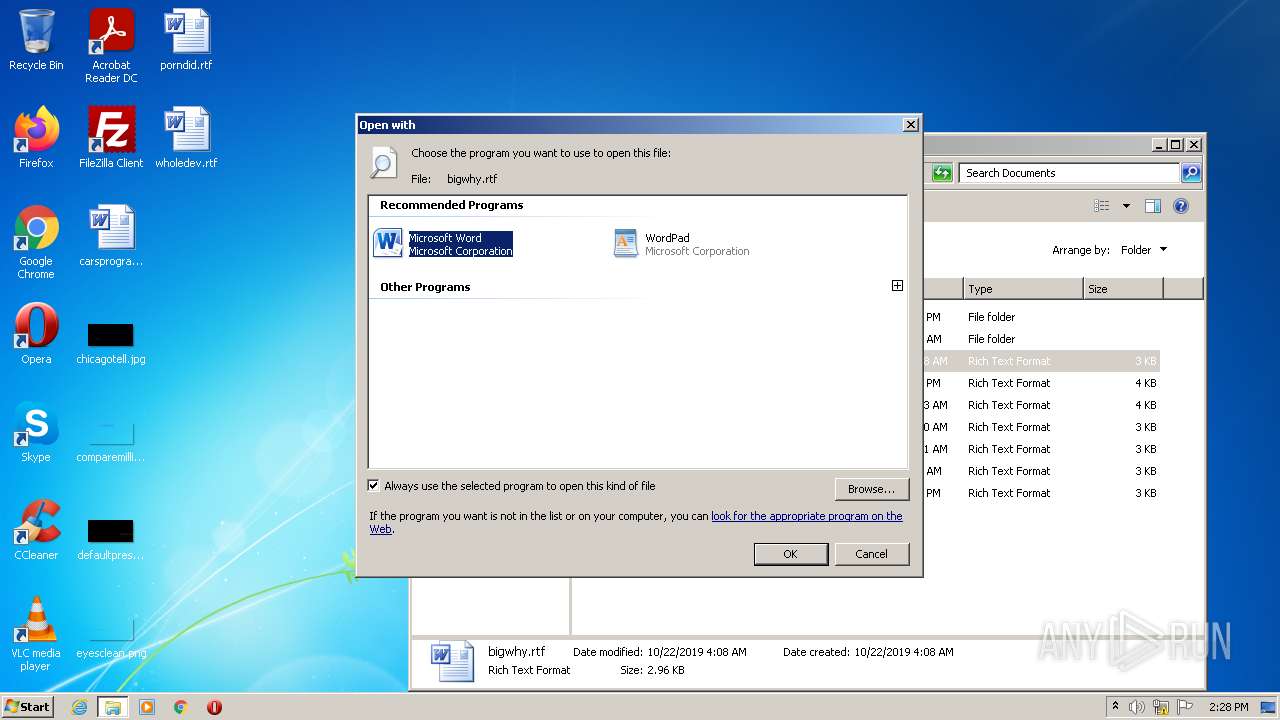
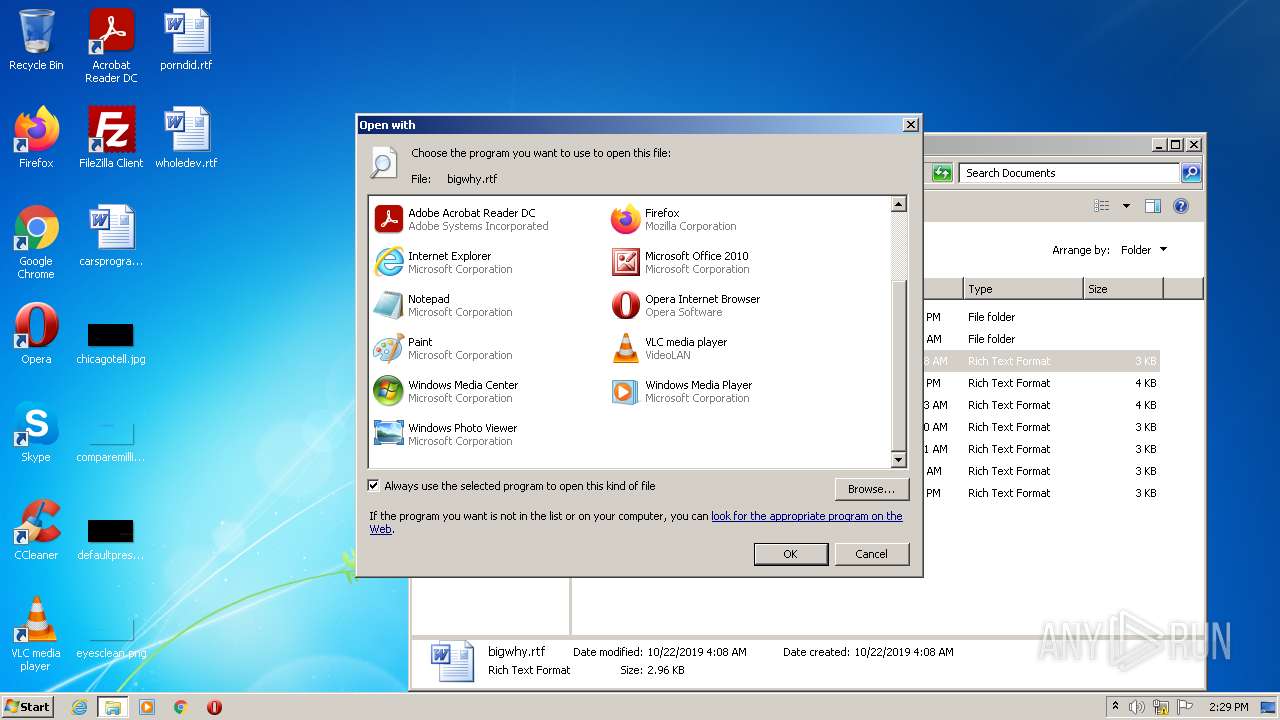
Changes default file association
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
Creates/Modifies COM task schedule object
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
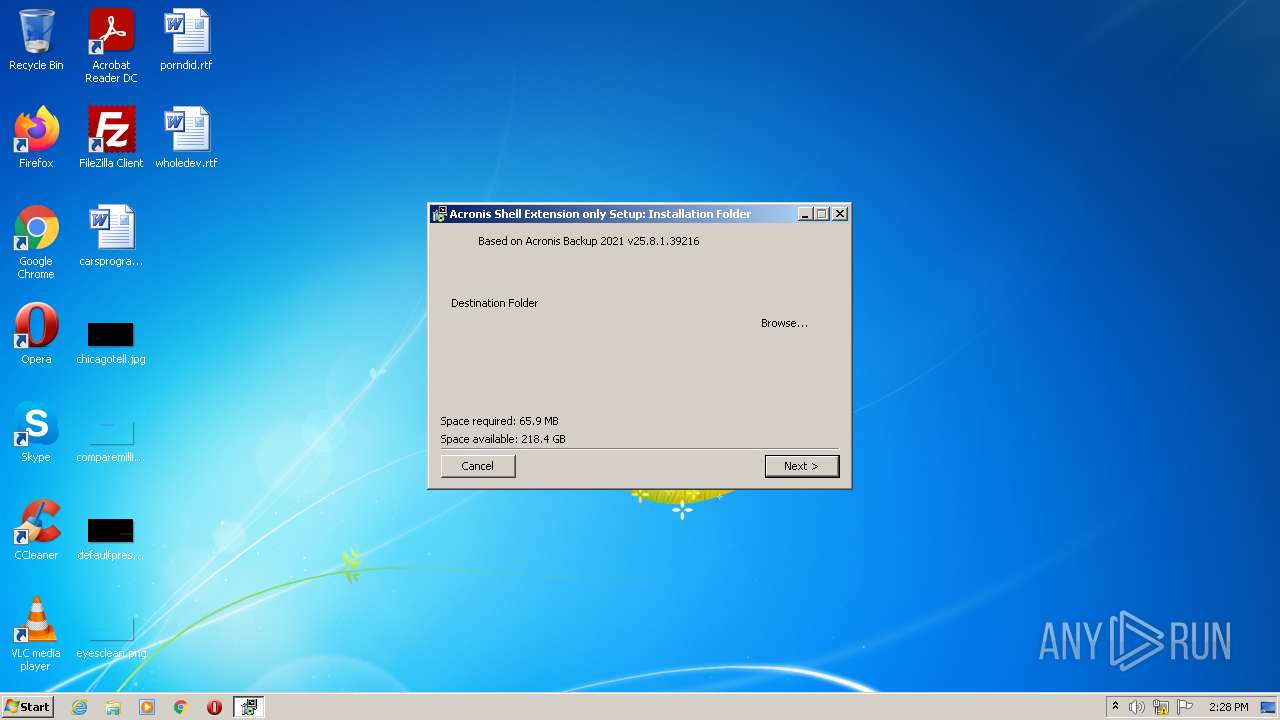
Creates a directory in Program Files
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
Drops a file that was compiled in debug mode
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
Creates a software uninstall entry
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
Creates files in the program directory
- TIB,TIBX-ShellEx-25.8.1.39216.exe (PID: 2712)
INFO
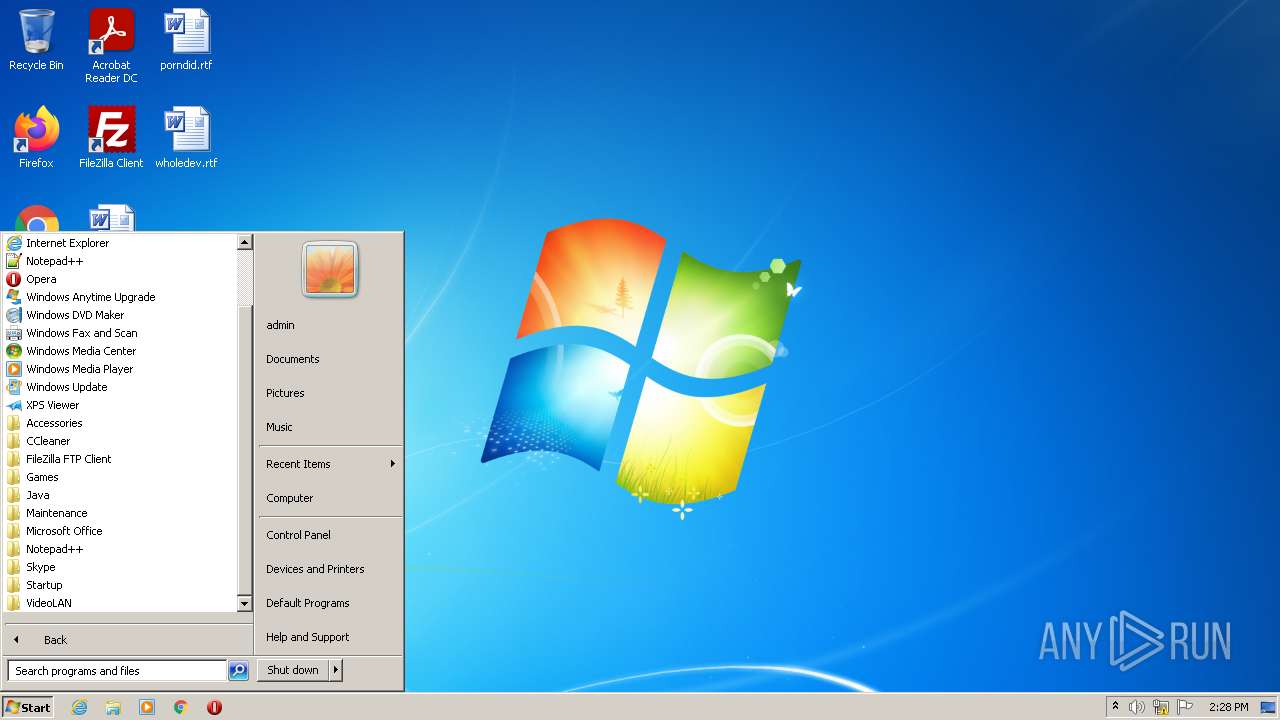
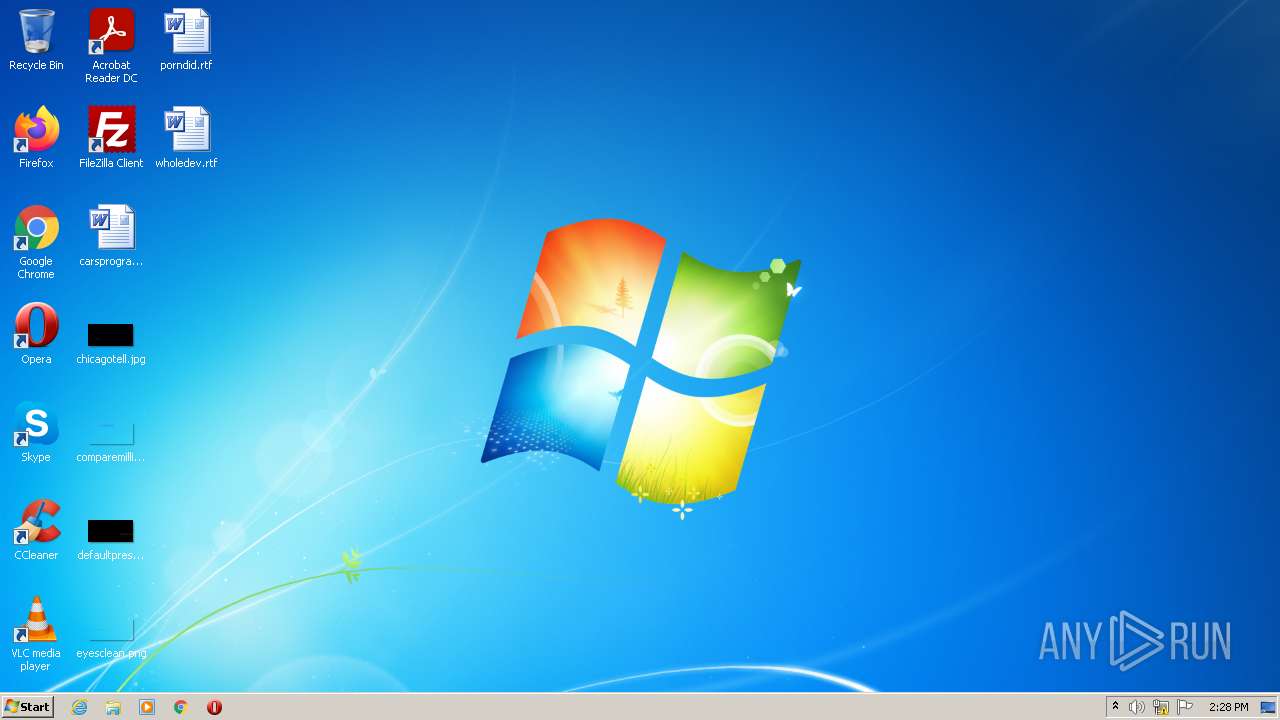
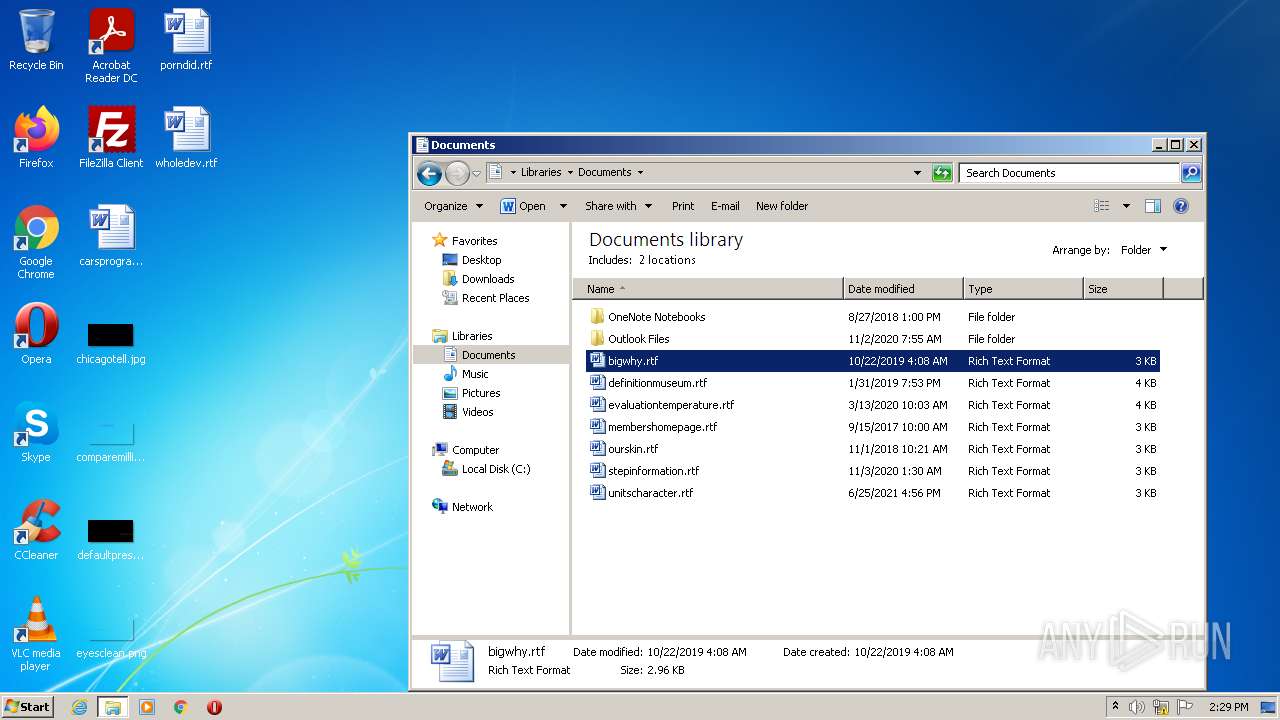
Manual execution by user
- explorer.exe (PID: 1380)
- rundll32.exe (PID: 2604)
Reads the computer name
- explorer.exe (PID: 1380)
- rundll32.exe (PID: 2604)
Checks supported languages
- explorer.exe (PID: 1380)
- rundll32.exe (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3348 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 162816 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2020:08:01 04:44:50+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2020 02:44:50 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2020 02:44:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006457 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43499 |
.rdata | 0x00008000 | 0x00001380 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.261 |
.data | 0x0000A000 | 0x00025538 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13373 |
.ndata | 0x00030000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x000010F8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.38336 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29035 | 843 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1380 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
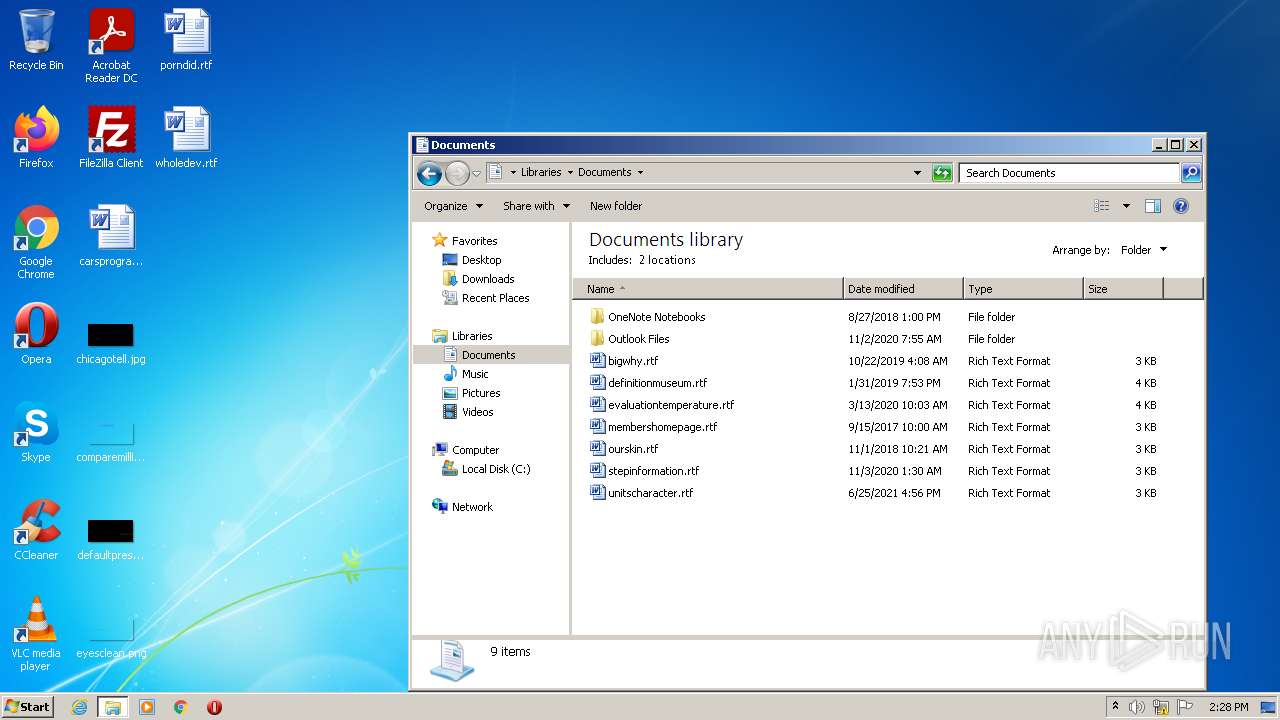
| 2604 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Documents\bigwhy.rtf | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2712 | "C:\Users\admin\AppData\Local\Temp\TIB,TIBX-ShellEx-25.8.1.39216.exe" | C:\Users\admin\AppData\Local\Temp\TIB,TIBX-ShellEx-25.8.1.39216.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4056 | "C:\Users\admin\AppData\Local\Temp\TIB,TIBX-ShellEx-25.8.1.39216.exe" | C:\Users\admin\AppData\Local\Temp\TIB,TIBX-ShellEx-25.8.1.39216.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 044
Read events
951
Write events
93
Delete events
0
Modification events
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.tibx\OpenWithList |
| Operation: | write | Name: | (default) |
Value: | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.tibx\OpenWithProgids |
| Operation: | write | Name: | tibxfile |
Value: | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.tib\OpenWithList |
| Operation: | write | Name: | a |
Value: {1AC14E77-02E7-4E5D-B744-2EB1AE5198B7}\OpenWith.exe | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.tib\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.tib\OpenWithProgids |
| Operation: | write | Name: | tibfile |
Value: | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\tibfile |
| Operation: | write | Name: | (default) |
Value: Acronis True Image backup | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\tibfile\CLSID |
| Operation: | write | Name: | (default) |
Value: {C539A15B-3AF9-4c92-B771-50CB78F5C751} | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\tibfile\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Acronis\TIB-TIBX ShellEx\tishell_25_8_39216.dll,-4 | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\tibfile\Shell\open |
| Operation: | write | Name: | (default) |
Value: | |||
| (PID) Process: | (2712) TIB,TIBX-ShellEx-25.8.1.39216.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\tibfile\Shell\open\command |
| Operation: | write | Name: | (default) |
Value: explorer /idlist,%I,%L | |||
Executable files
20
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\archive3_adapter.dll | executable | |
MD5:B38DC832B4758BF8F571B78340ECAFD0 | SHA256:D912EC5970B6D35953C8791D6E37D032D855206A53F5117FE5EFEFF72210052E | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\icudt38.dll | executable | |
MD5:A7A8139EF4C0DF2E6A797CECD097B60F | SHA256:B320843A62FBBD2DA49D0FEAE8FA13A0BC2C31B12D49F0A1BC5DD465A2128597 | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\libssl10.dll | executable | |
MD5:FD40C4DB1642E69DAE627379EEFF42E7 | SHA256:0329393F556AA2F301FC9243145284B063319041F1A44080F83869217038E5AC | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\pcs_io.dll | executable | |
MD5:6E6F5C7066DA879D3615D378078F96EA | SHA256:D80AB5DA59227A6C4751832688754C998A63EEFBF1C1A4D2A42D0E3E1E3E05A1 | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\sqlite3.dll | executable | |
MD5:FFC43C0D21BB0F253EA07F6DCE757ACF | SHA256:81D635ED978933242A8C3E86237B6821789C86BA946268715F2EF44EB4F9C1FF | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\resource.dll | executable | |
MD5:9B53FE5217C9D61370C849C765C4714E | SHA256:1F9CBC92540CCCB4A0EFCD2DEA3A0D62ACBE56859E626B57AF593BE6E81D6F9D | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\TIB_Shell-uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Users\admin\AppData\Local\Temp\nsy7201.tmp\System.dll | executable | |
MD5:FCCFF8CB7A1067E23FD2E2B63971A8E1 | SHA256:6FCEA34C8666B06368379C6C402B5321202C11B00889401C743FB96C516C679E | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\winpthreads4.dll | executable | |
MD5:73A8D3FC6FEF2EEBB2AE9AE759EB66F5 | SHA256:D8D08FB871EFC60FB085A8AA0D9558741EAD1BB84B8F06558C708DB447B1255B | |||
| 2712 | TIB,TIBX-ShellEx-25.8.1.39216.exe | C:\Program Files\Acronis\TIB-TIBX ShellEx\tishell_25_8_39216.dll | executable | |
MD5:76F9B12FF2C3DCCBC08883F79852388F | SHA256:77E494B25DA0352415F30DF818D091D1AA78E1C8BCDEE988AA6EDEC265C4EEA7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report