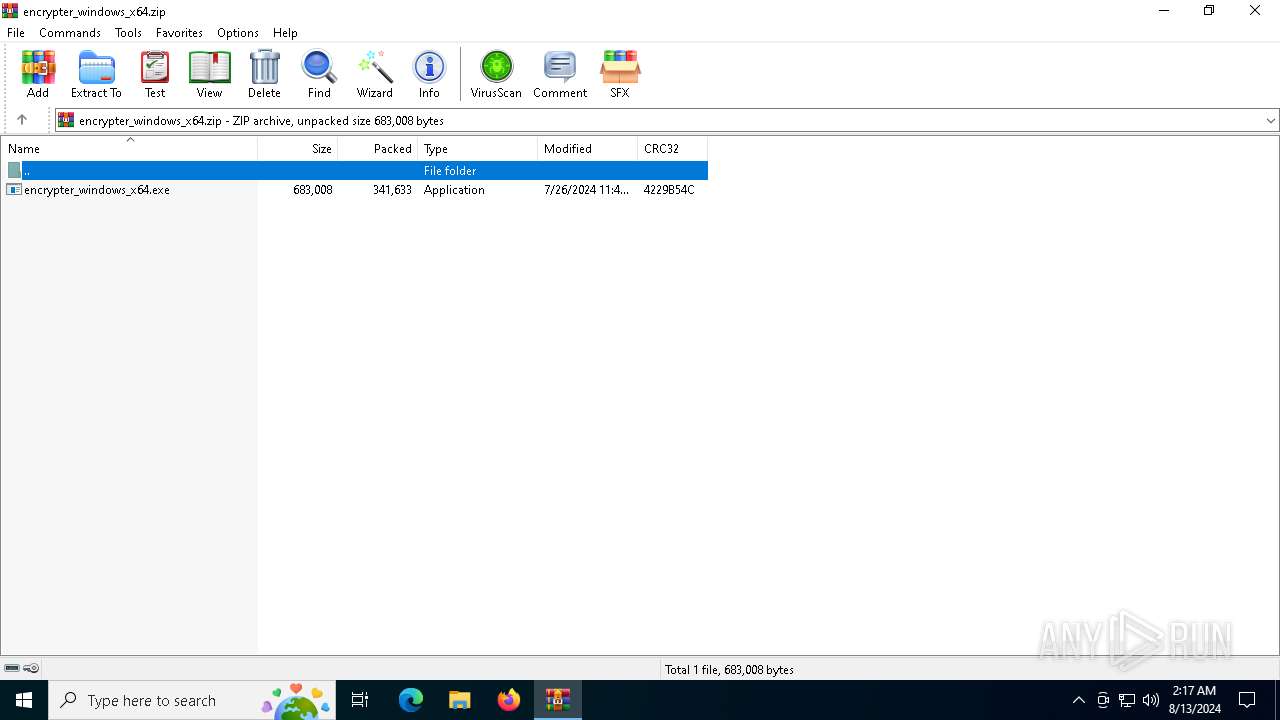
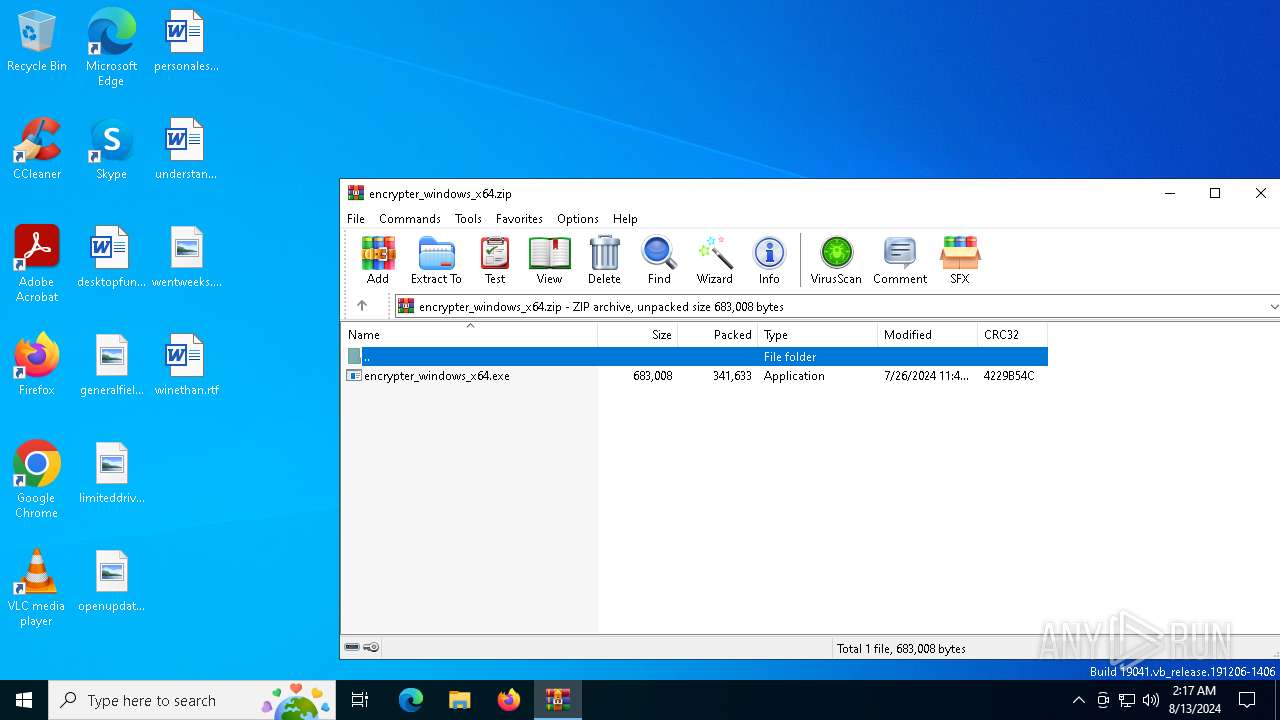
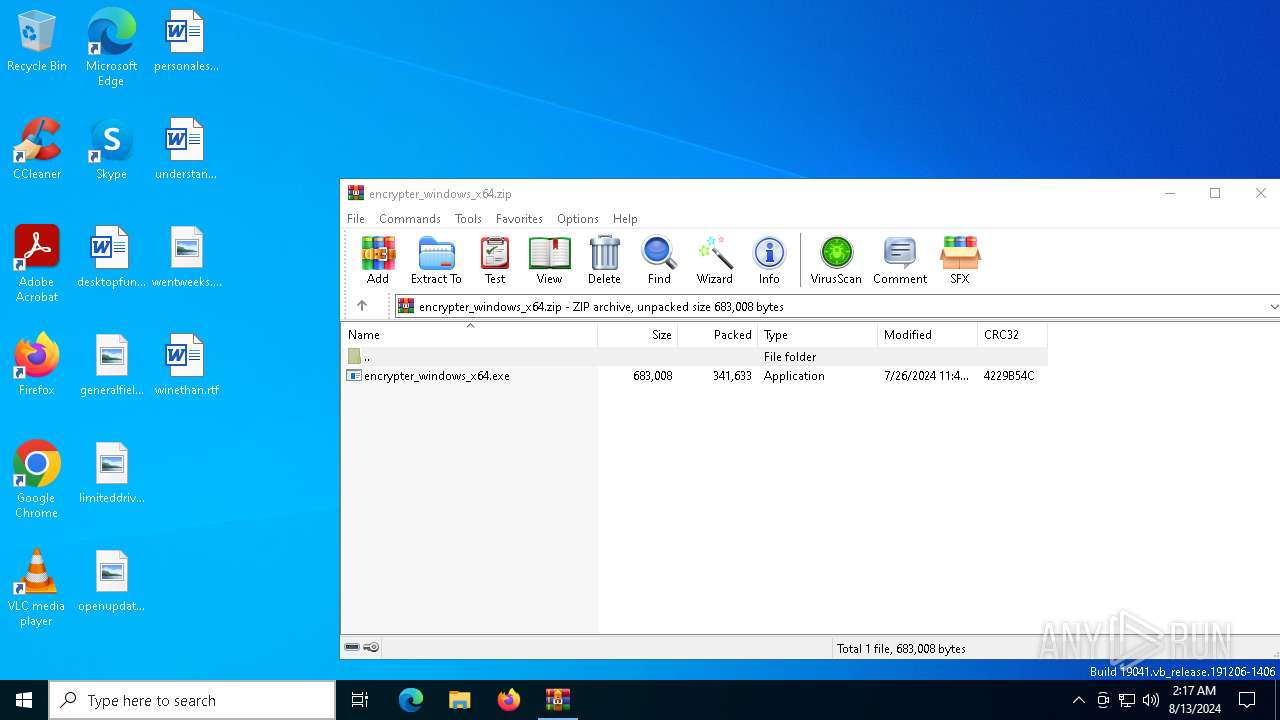
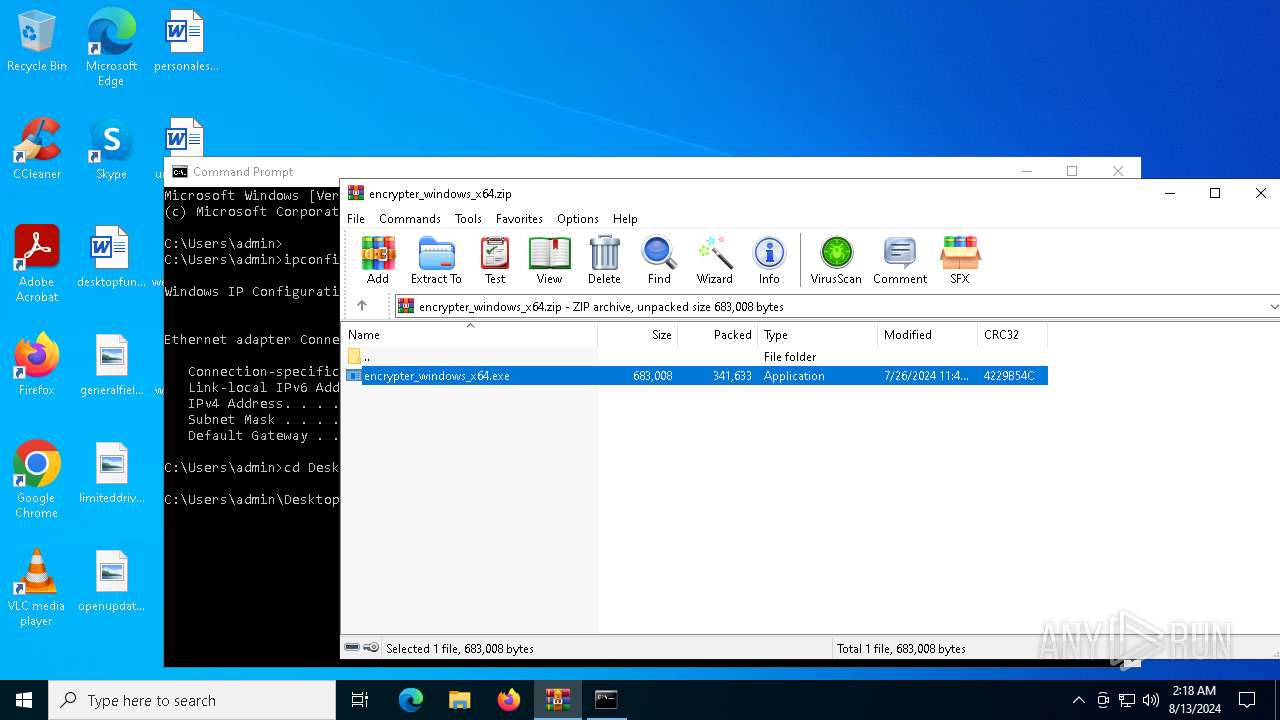
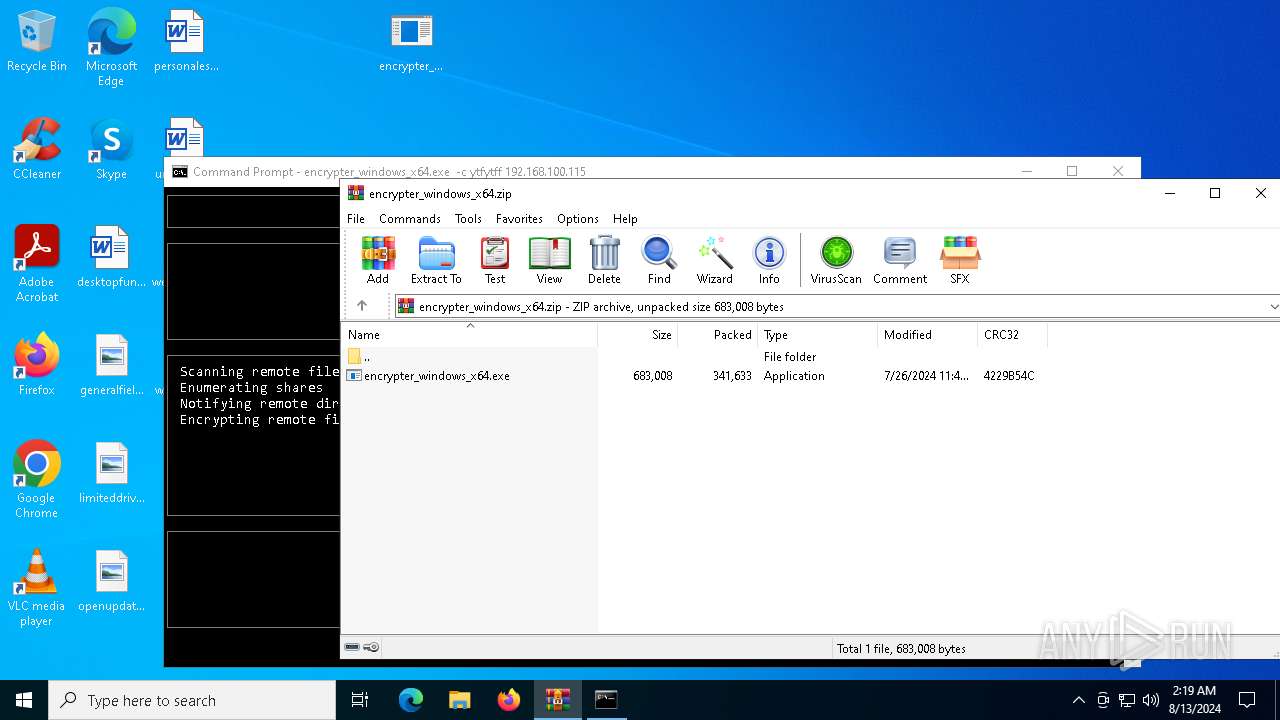
| File name: | encrypter_windows_x64.zip |
| Full analysis: | https://app.any.run/tasks/65517c5a-e197-4459-ac00-fba35fecf08c |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2024, 02:17:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | EC6F21D027BC7E4779ECE75F26B180A0 |
| SHA1: | 4ED3C9CD0CFCFB19E692C726D25A47E727C8625A |
| SHA256: | C0346CB424EF7CB09471F0C8EAB4A59B9235FB8990B4D38AB1E9263EB6D540C9 |
| SSDEEP: | 12288:pcV1Oid/NmXv185fqM1AnZS4Gc+iR8/a58YsG5JBRJXONz9a+b:OVsid/NSt85fxAnZShc+iq/a58YsG5f6 |
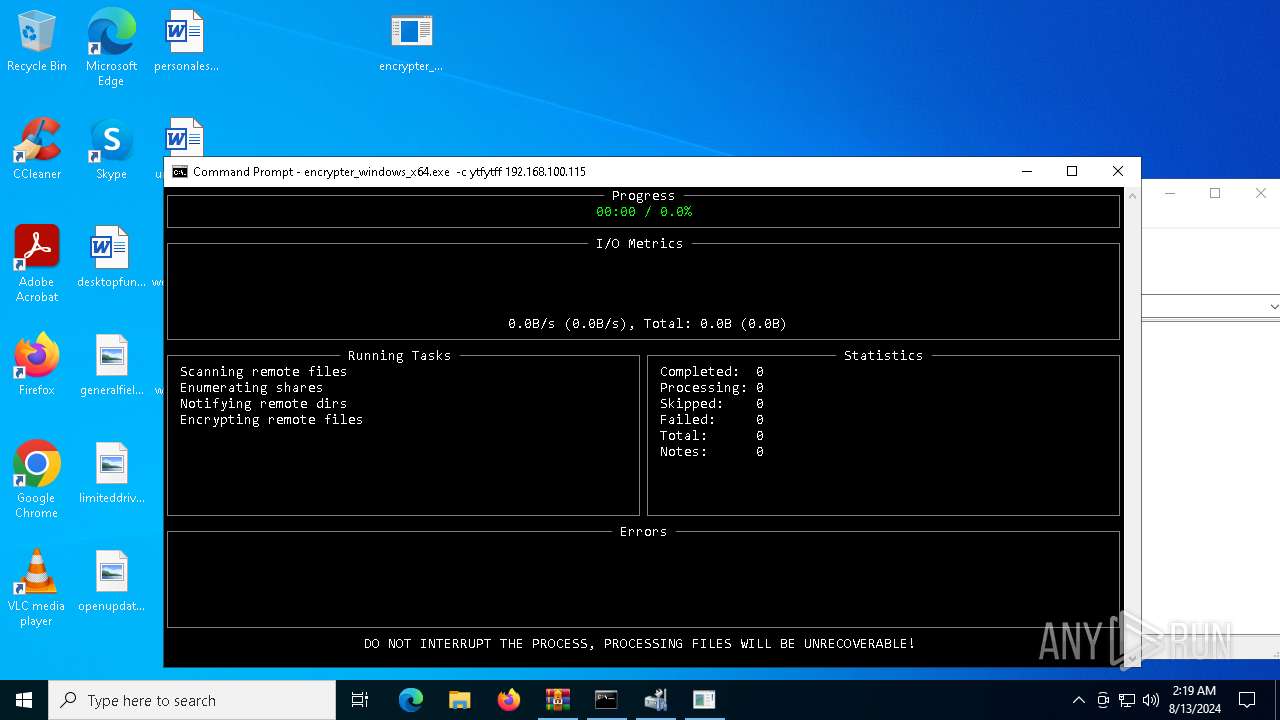
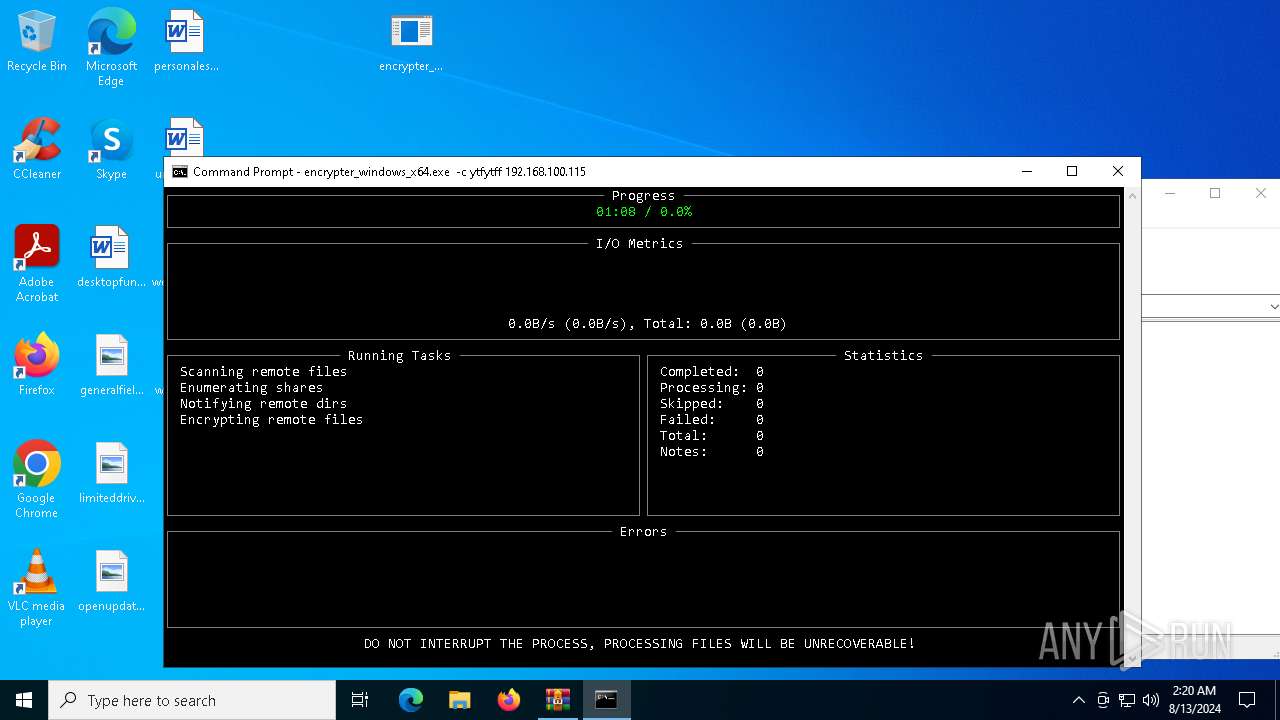
MALICIOUS
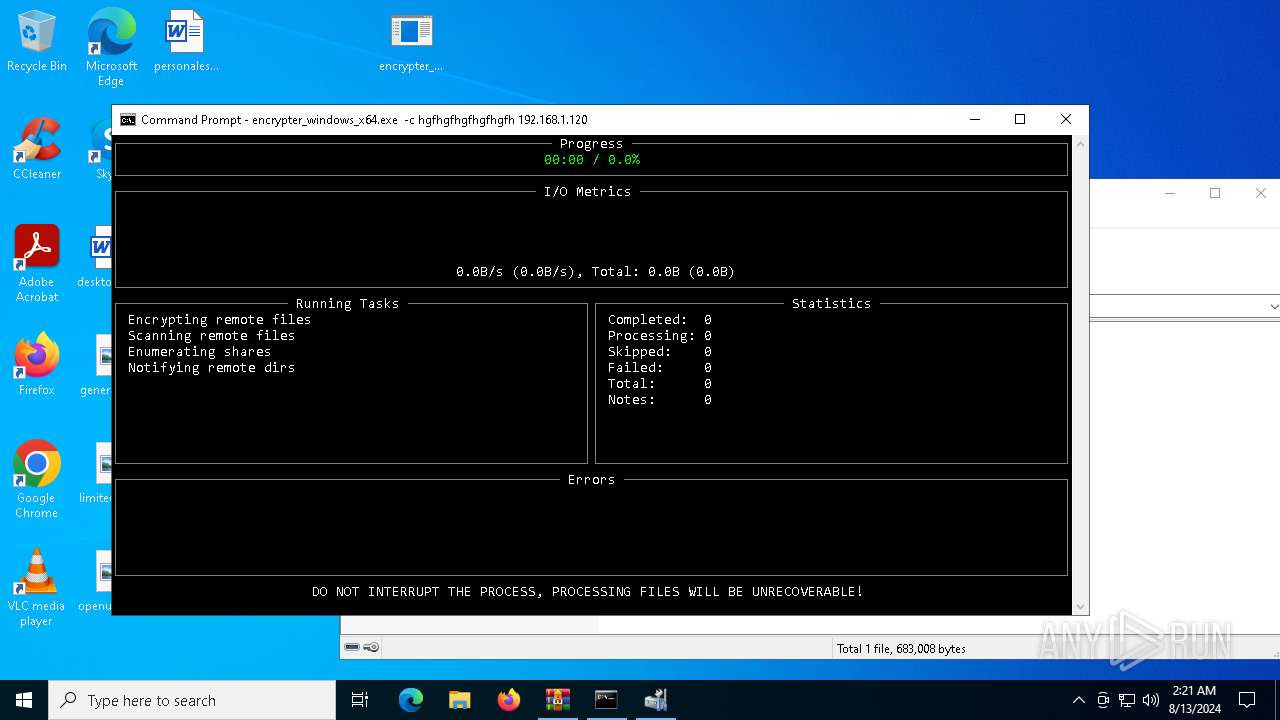
Deletes shadow copies
- encrypter_windows_x64.exe (PID: 6740)
- encrypter_windows_x64.exe (PID: 1860)
Using BCDEDIT.EXE to modify recovery options
- encrypter_windows_x64.exe (PID: 6740)
- encrypter_windows_x64.exe (PID: 1860)
SUSPICIOUS
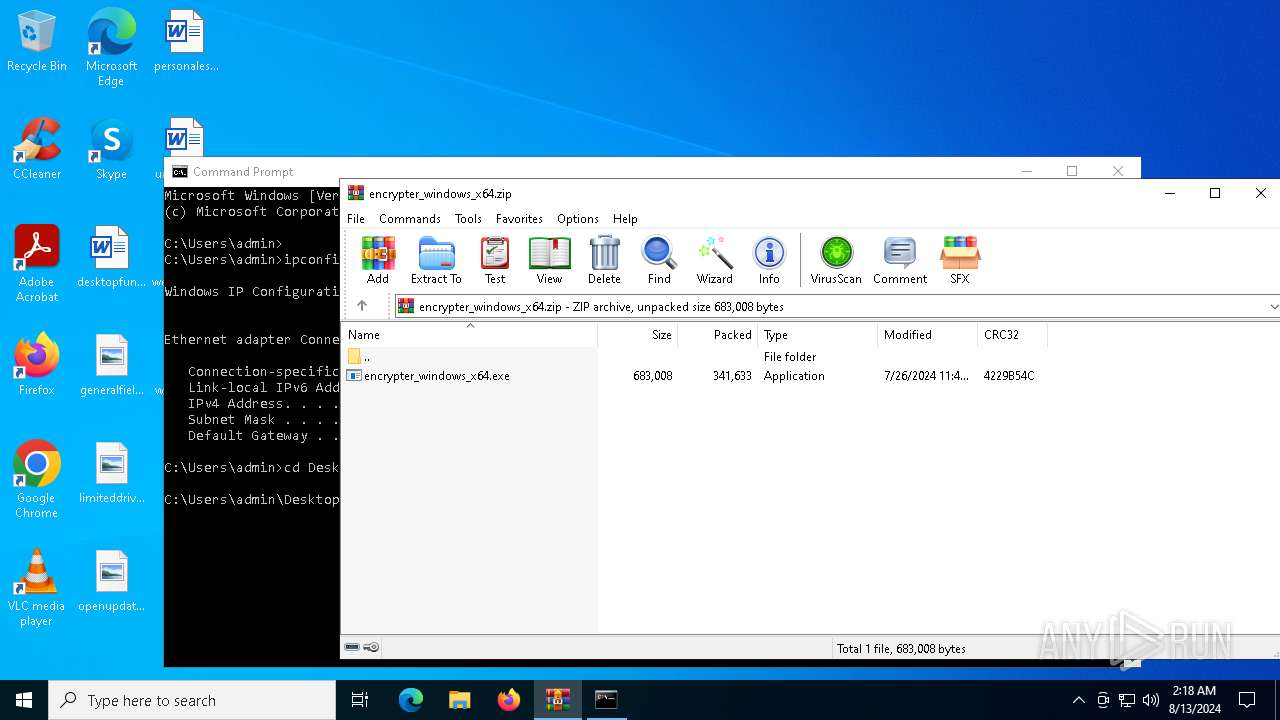
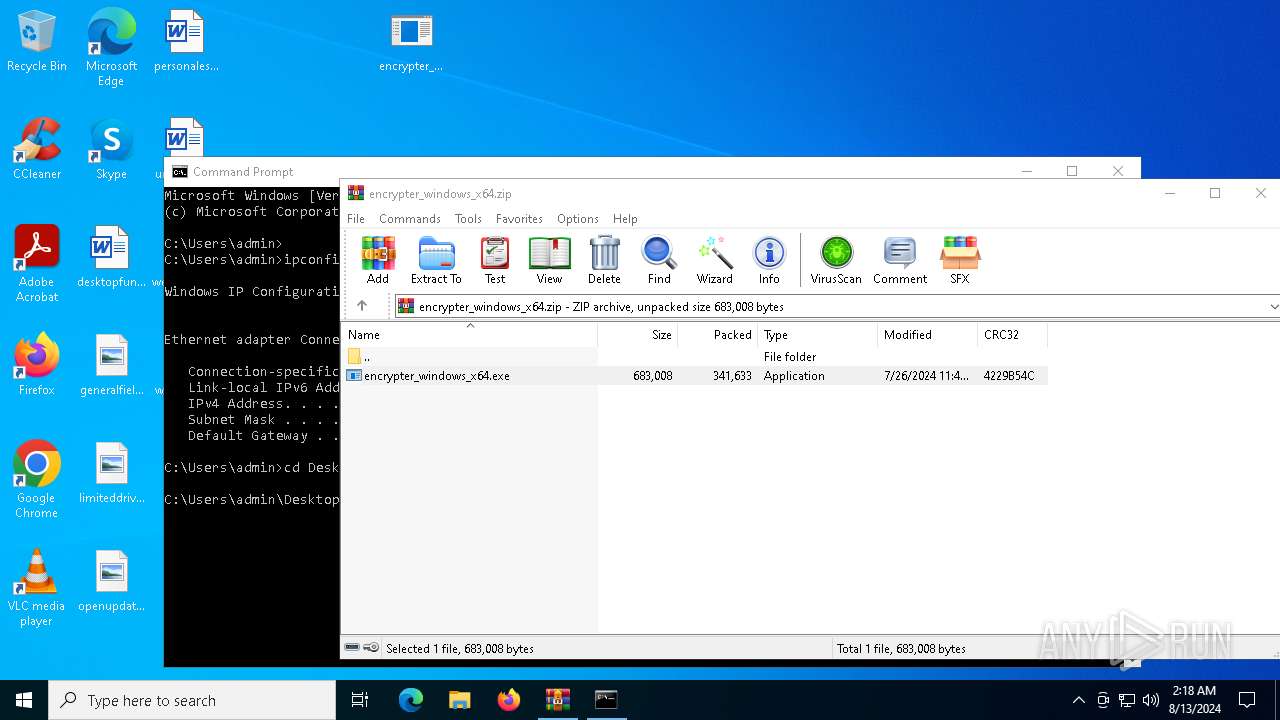
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6480)
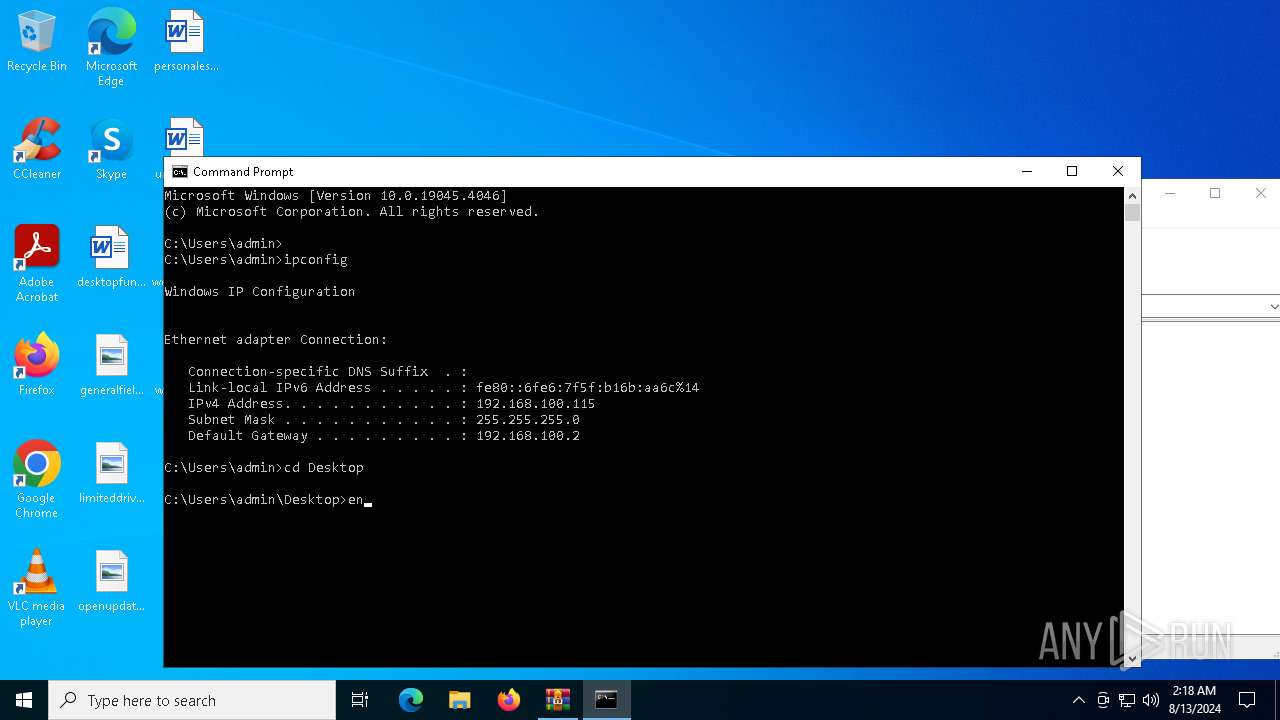
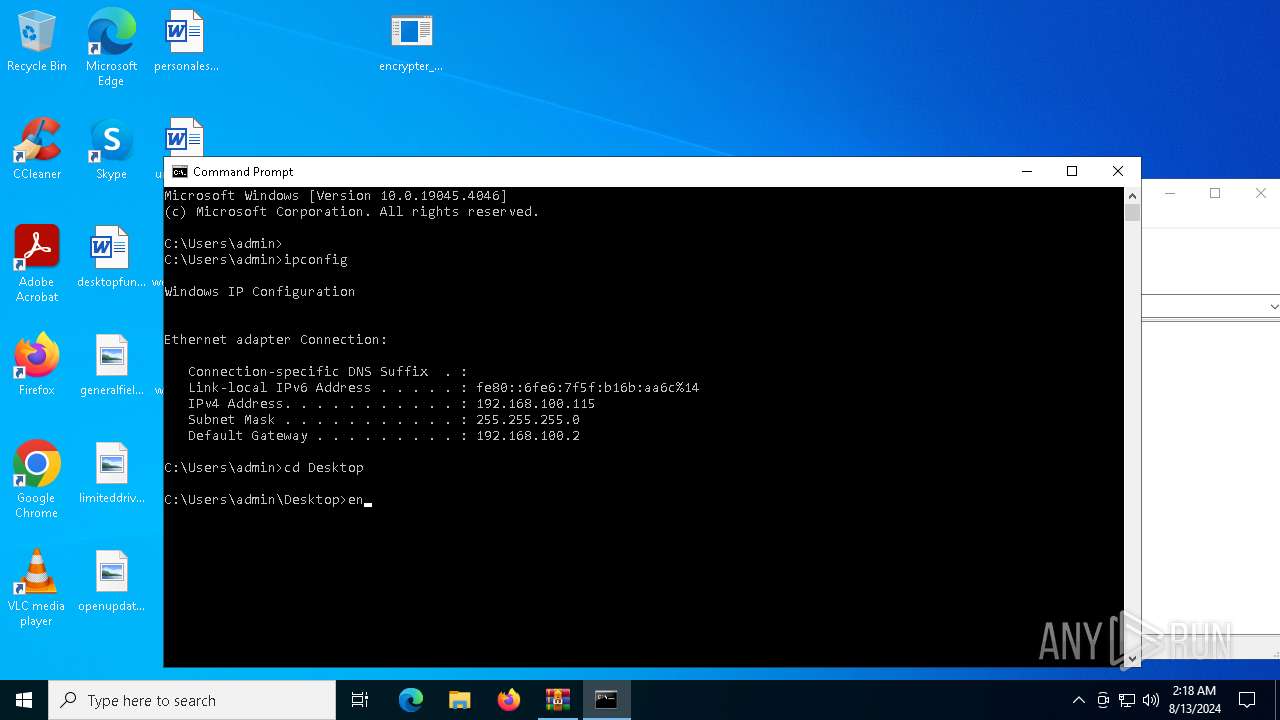
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 5656)
Reads security settings of Internet Explorer
- encrypter_windows_x64.exe (PID: 6740)
- encrypter_windows_x64.exe (PID: 1860)
Reads the date of Windows installation
- encrypter_windows_x64.exe (PID: 6740)
- encrypter_windows_x64.exe (PID: 1860)
Uses pipe srvsvc via SMB (transferring data)
- encrypter_windows_x64.exe (PID: 6740)
INFO
Checks supported languages
- TextInputHost.exe (PID: 7136)
- encrypter_windows_x64.exe (PID: 6740)
- encrypter_windows_x64.exe (PID: 1860)
Reads the computer name
- TextInputHost.exe (PID: 7136)
- encrypter_windows_x64.exe (PID: 6740)
- encrypter_windows_x64.exe (PID: 1860)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6480)
Process checks computer location settings
- encrypter_windows_x64.exe (PID: 6740)
- encrypter_windows_x64.exe (PID: 1860)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5408)
- WMIC.exe (PID: 5988)
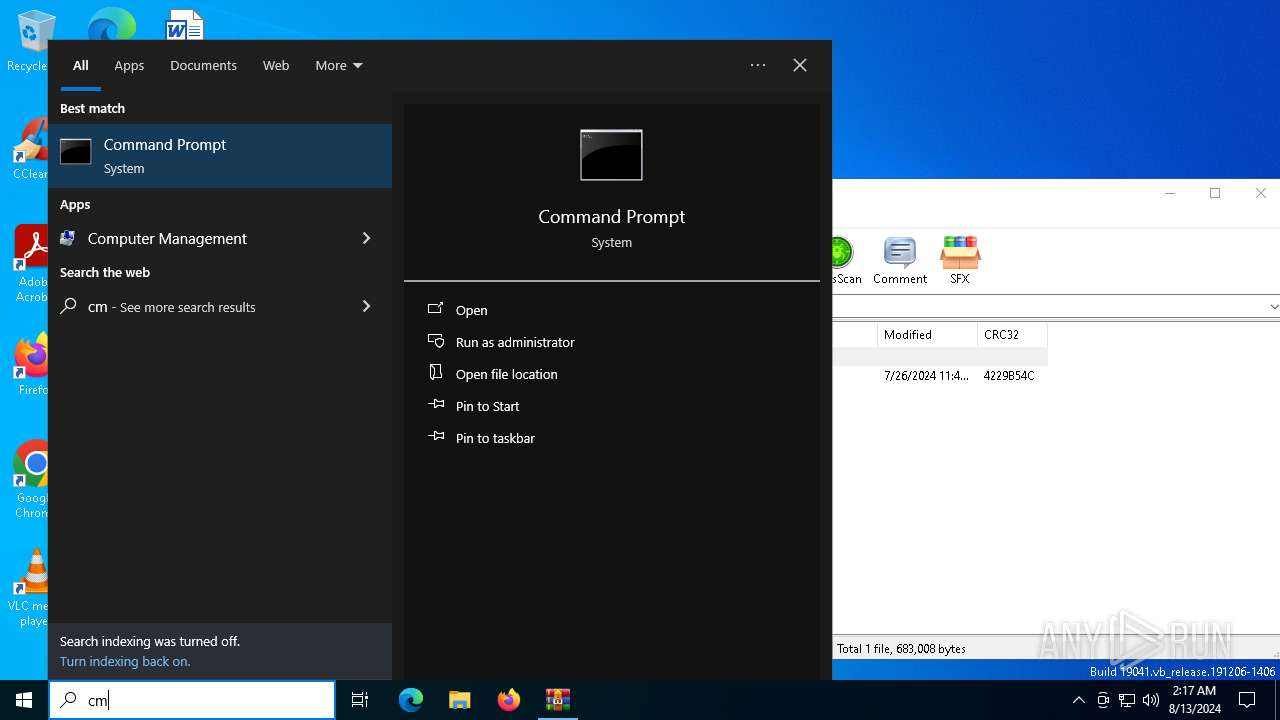
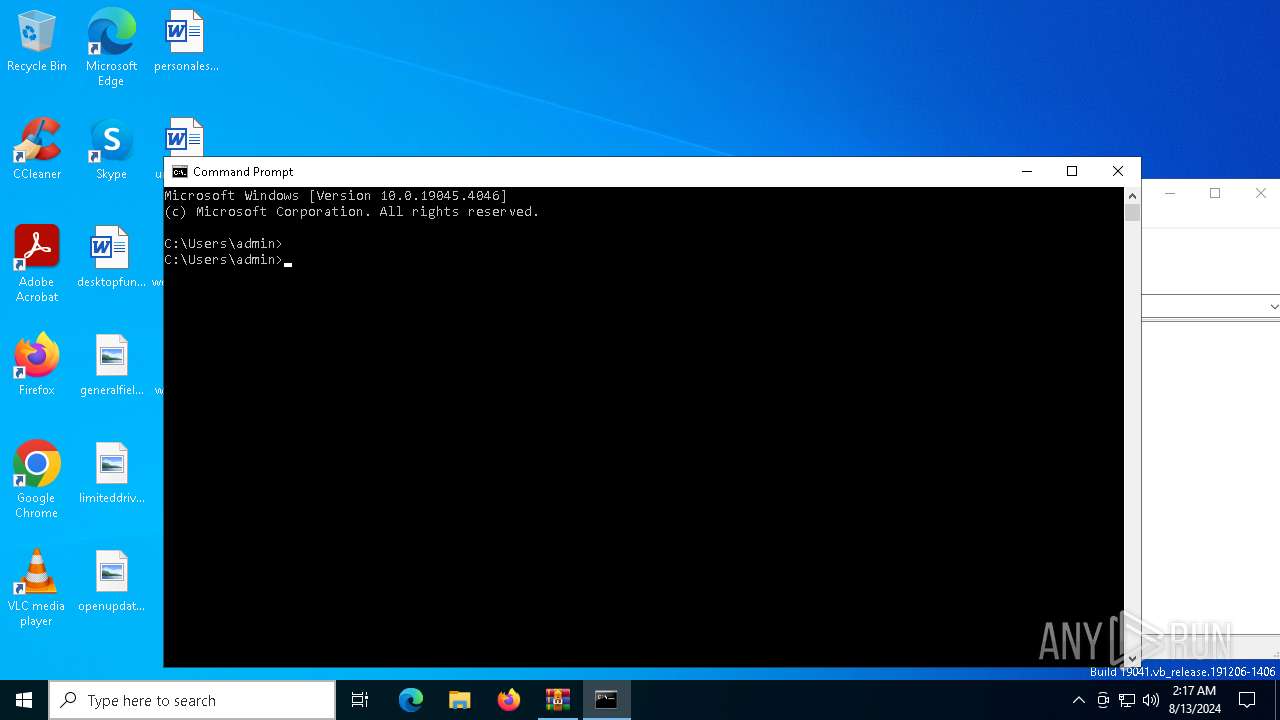
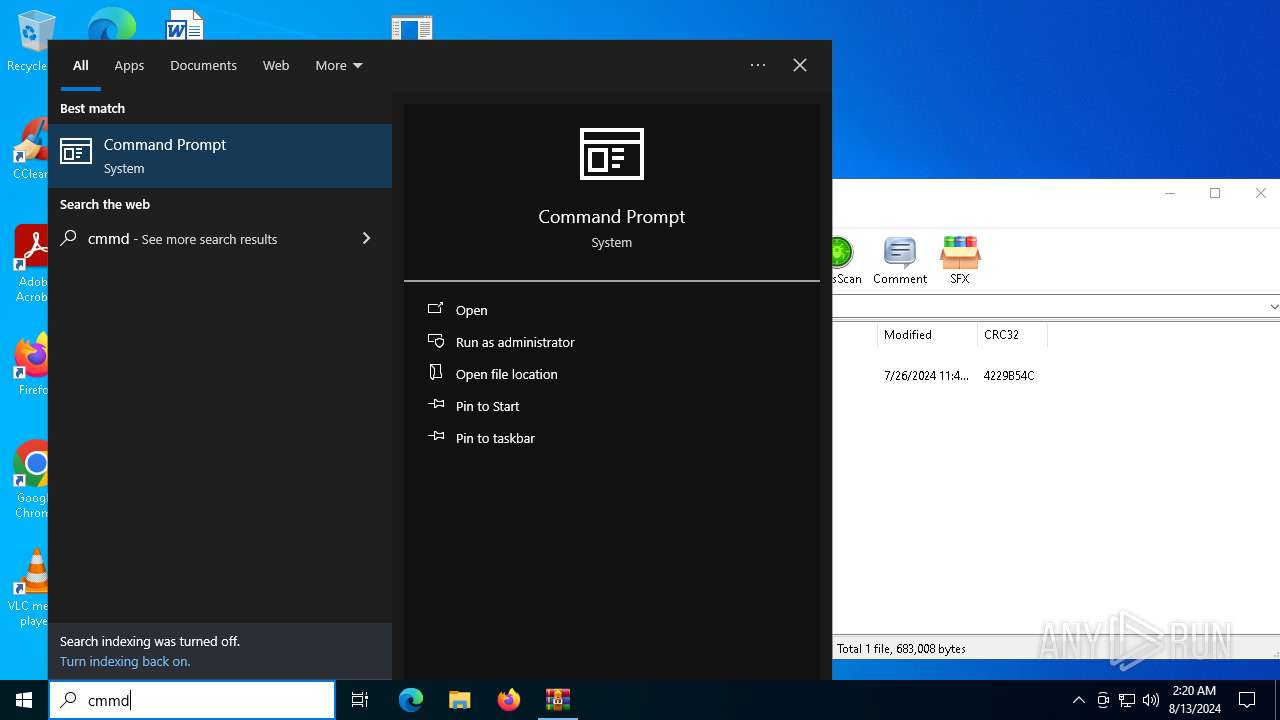
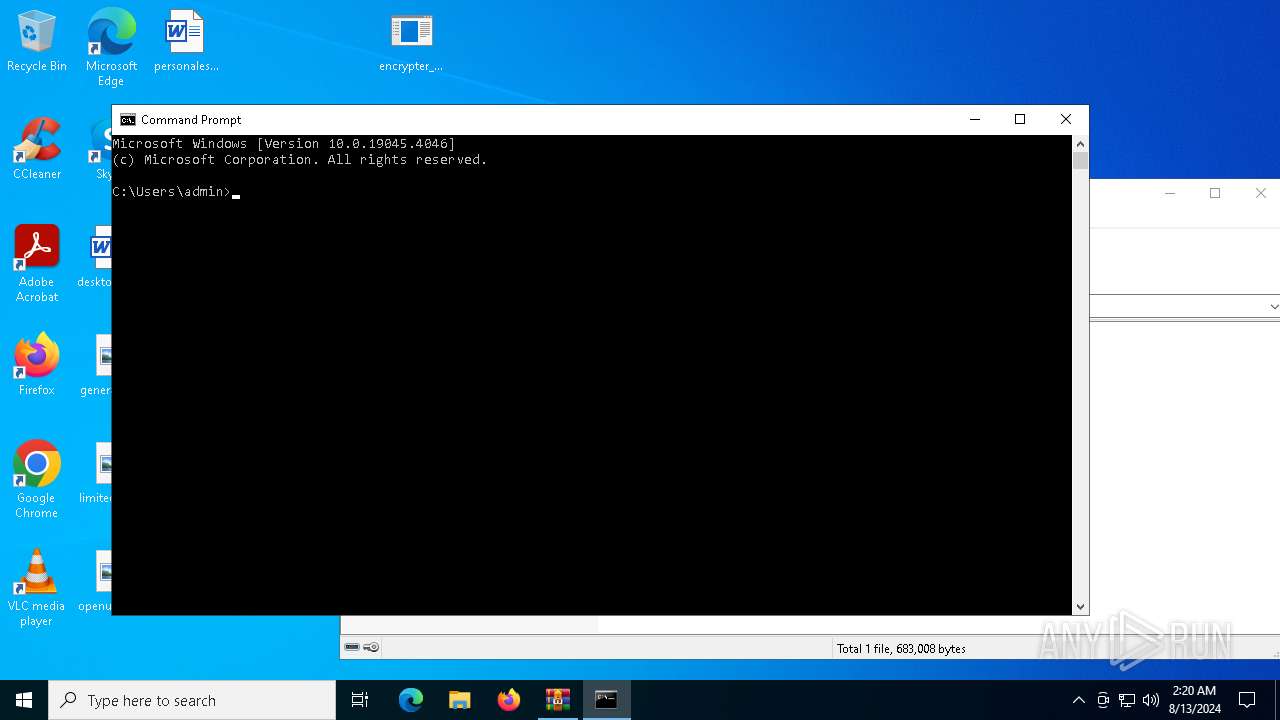
Manual execution by a user
- cmd.exe (PID: 1116)
- cmd.exe (PID: 5656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:07:26 11:46:26 |
| ZipCRC: | 0x4229b54c |
| ZipCompressedSize: | 341633 |
| ZipUncompressedSize: | 683008 |
| ZipFileName: | encrypter_windows_x64.exe |
Total processes
160
Monitored processes
37
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1248 | "C:\Windows\System32\wbadmin.exe" delete systemstatebackup -keepVersions:3 | C:\Windows\System32\wbadmin.exe | encrypter_windows_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vssadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1860 | encrypter_windows_x64.exe -c hgfhgfhgfhgfhgfh 192.168.1.120 | C:\Users\admin\Desktop\encrypter_windows_x64.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2272 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wbadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2476 | "C:\Windows\System32\wbadmin.exe" delete systemstatebackup | C:\Windows\System32\wbadmin.exe | encrypter_windows_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | "C:\Windows\System32\vssadmin.exe" delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | encrypter_windows_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3276 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 245
Read events
18 221
Write events
24
Delete events
0
Modification events
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\encrypter_windows_x64.zip | |||
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6740) encrypter_windows_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6740) encrypter_windows_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
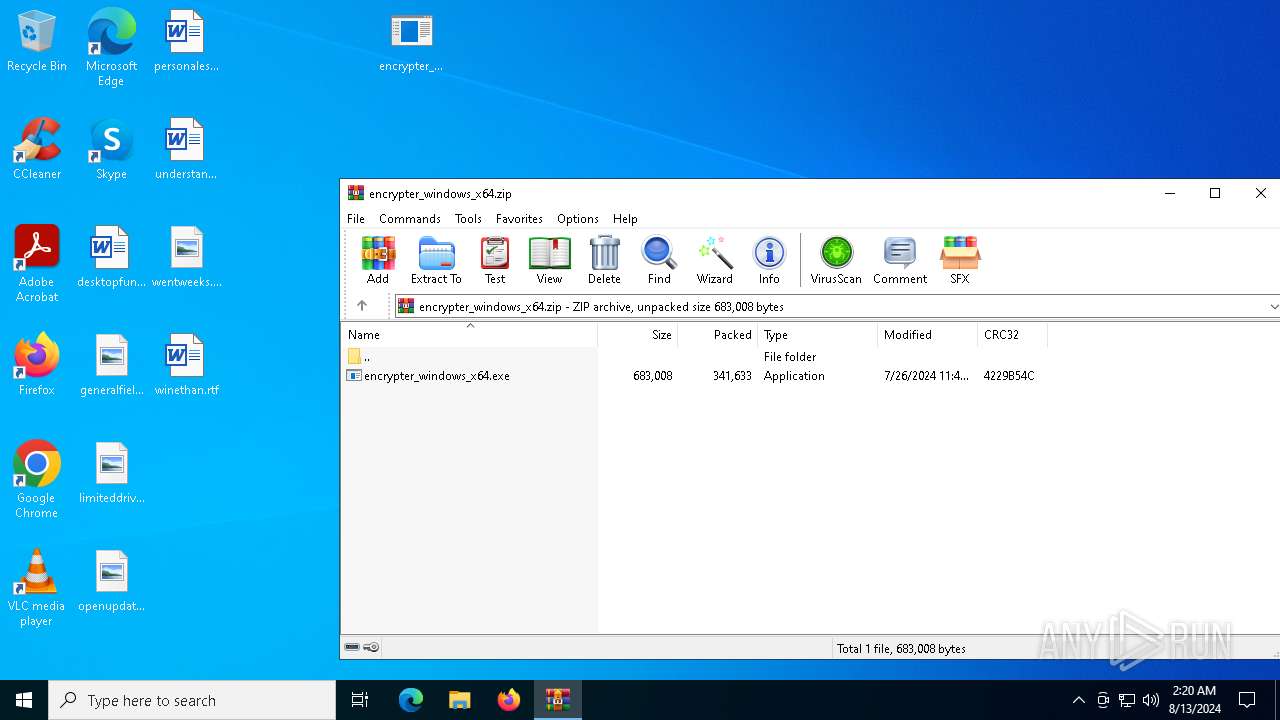
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6740 | encrypter_windows_x64.exe | \Device\Mup:\192.168.100.115\PIPE\srvsvc | — | |
MD5:— | SHA256:— | |||
| 6480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6480.32734\encrypter_windows_x64.exe | executable | |
MD5:A7E363A5767C1C5EDDD8AF3C89C7F1A6 | SHA256:861D1F84A99049948C9F936B6EE8C9A126B8CE03526412AAAC8A70647FA24F77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
43
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4576 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4576 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 104.126.37.170:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 13.89.179.9:443 | browser.pipe.aria.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|