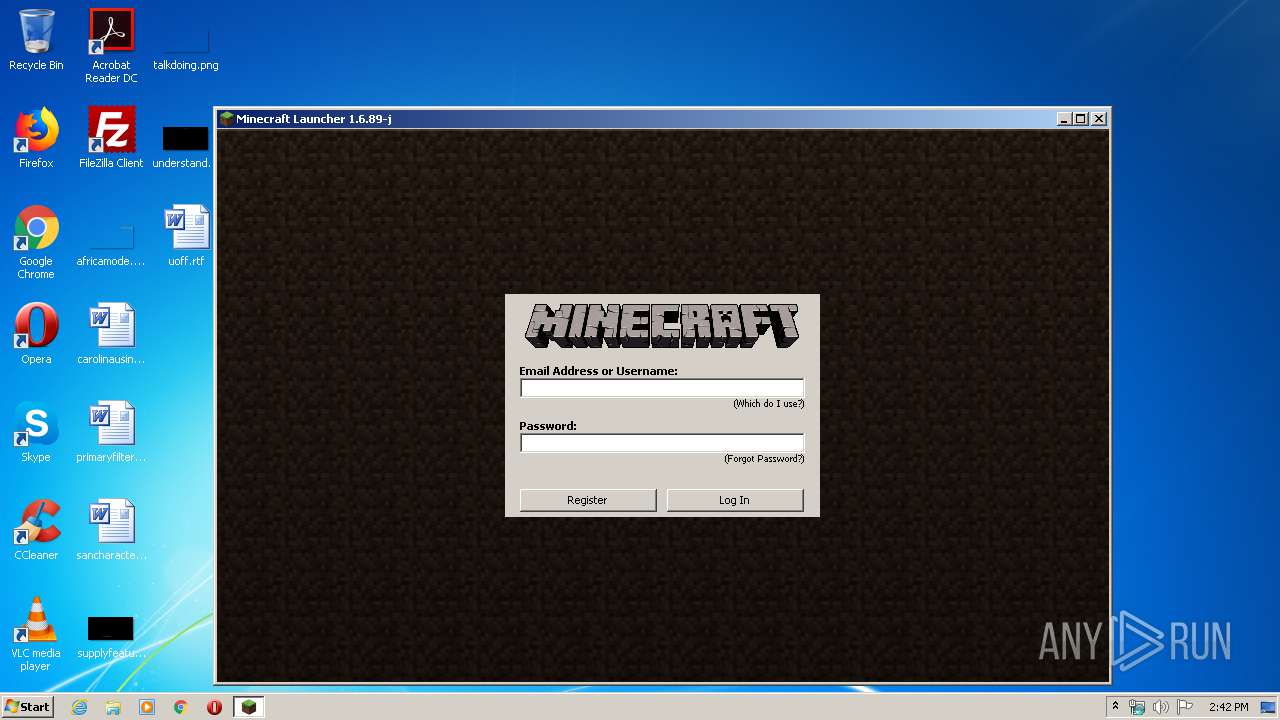
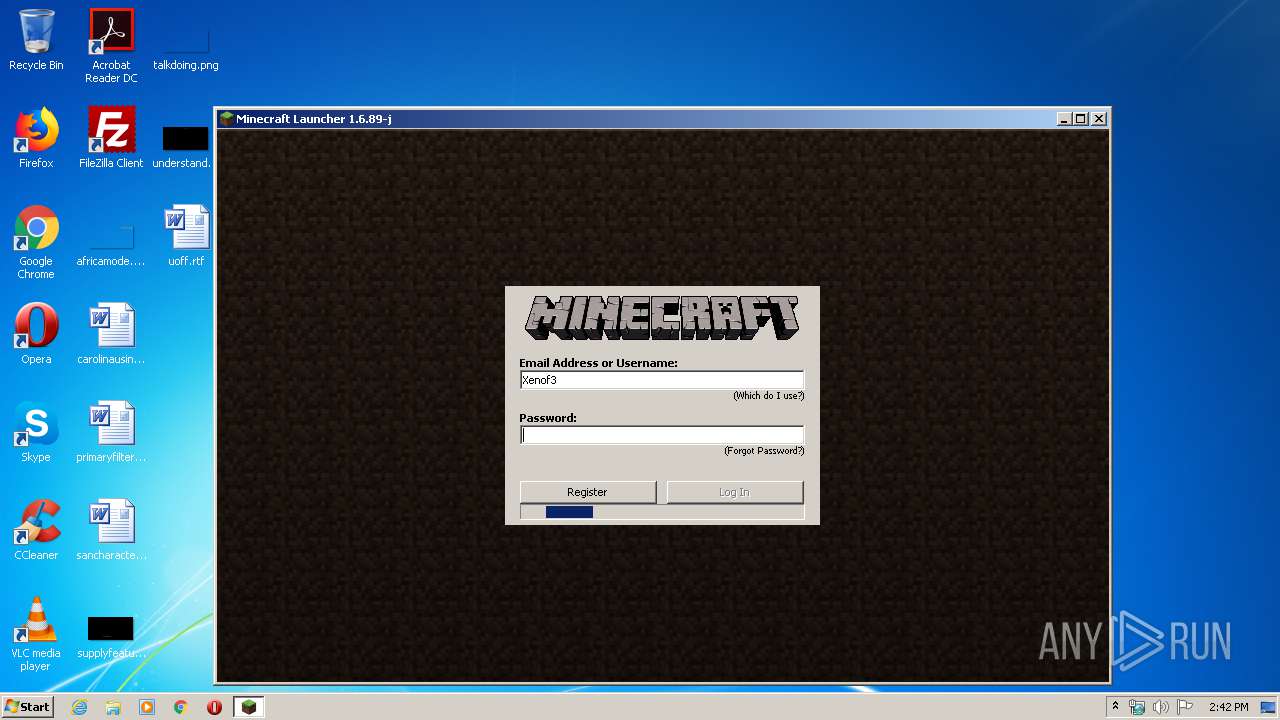
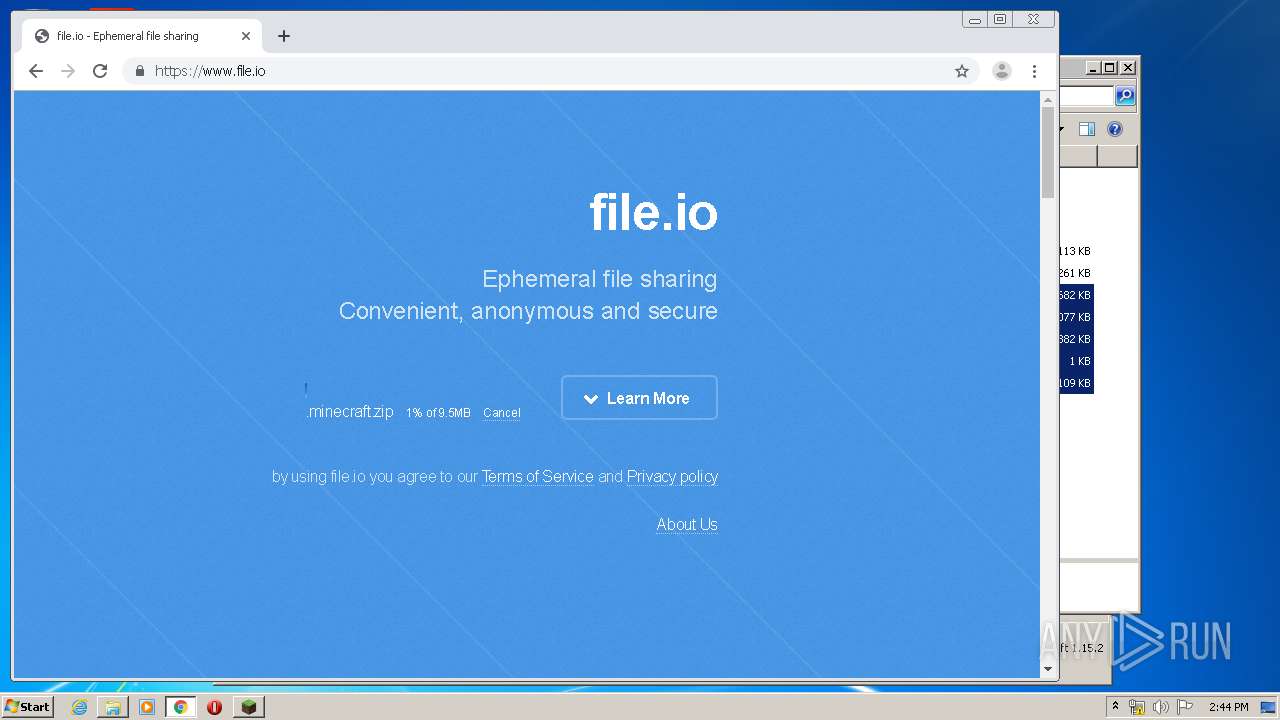
| File name: | Mineshafter-launcher.jar |
| Full analysis: | https://app.any.run/tasks/dc61c101-d5b8-43e4-82c2-d453d912aad0 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2020, 13:41:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | F6CD55DE2534393363E1A40E04D71156 |
| SHA1: | 7A8D89DD5548D6BDF8DE77E198AD518300C560CF |
| SHA256: | C03140A4216BD64EE1BF7D5E7416973F1E3F9E60B0513ADA448893DD6952EAD6 |
| SSDEEP: | 3072:hDDxhlswtTmiVBmqt7yANM/+0QGLF0BVHt:JNBtTmCBm07tMpQ4F0/t |
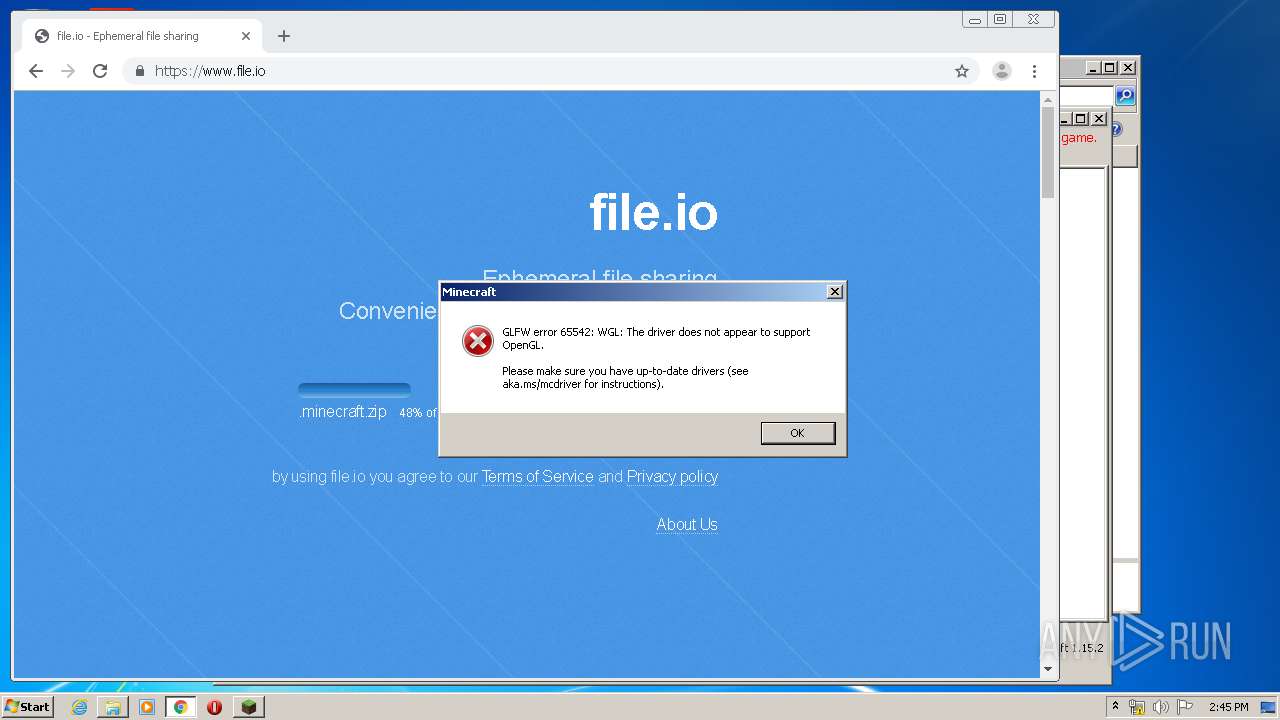
MALICIOUS
Loads dropped or rewritten executable
- javaw.exe (PID: 1172)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3732)
Application launched itself
- javaw.exe (PID: 348)
Executable content was dropped or overwritten
- javaw.exe (PID: 348)
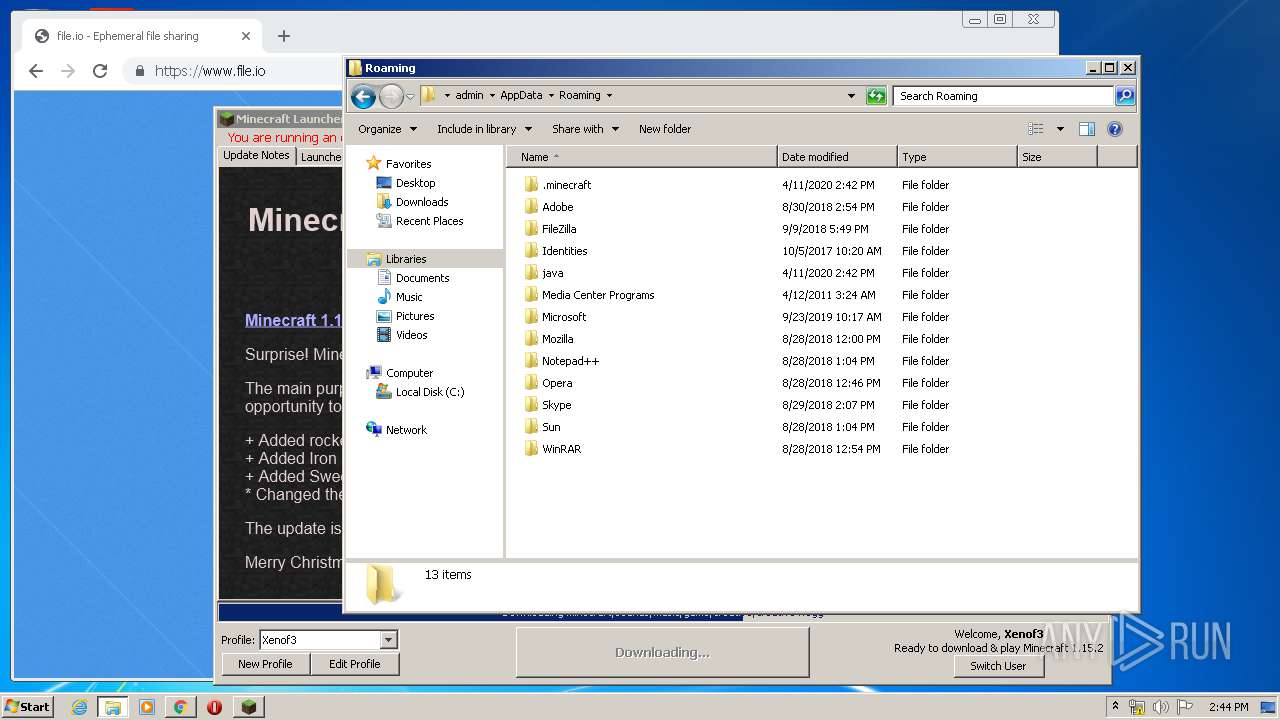
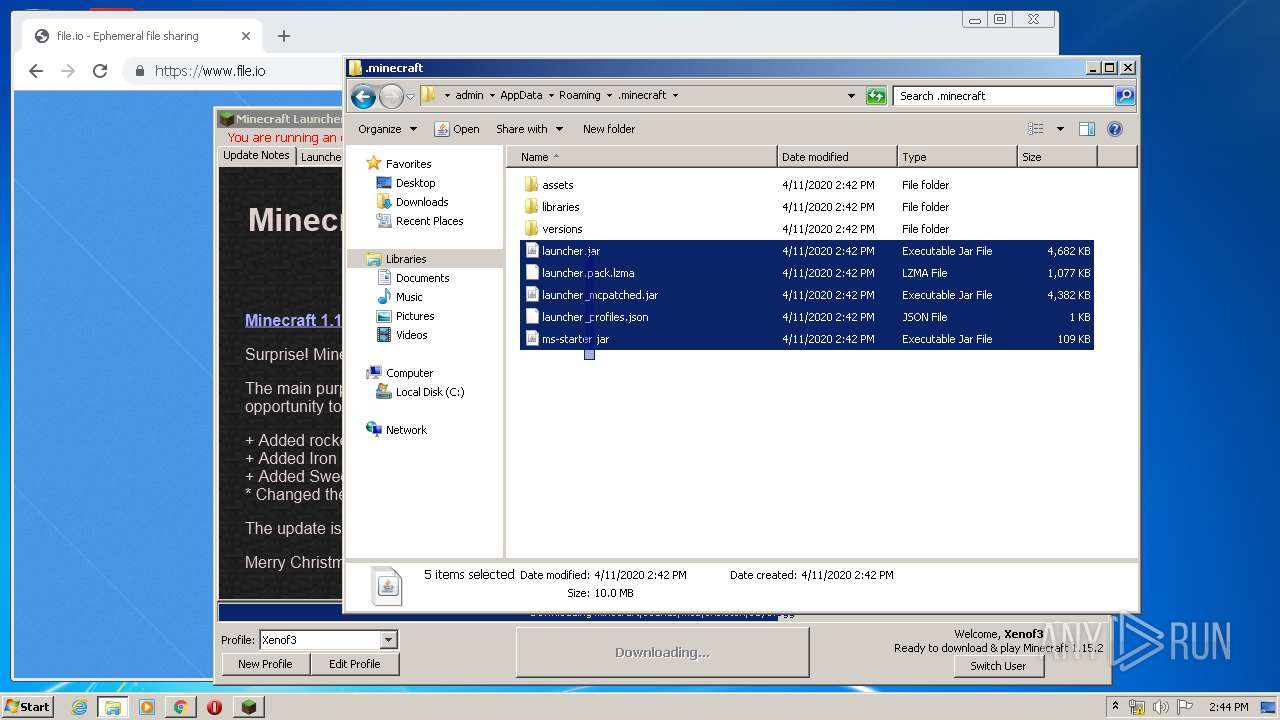
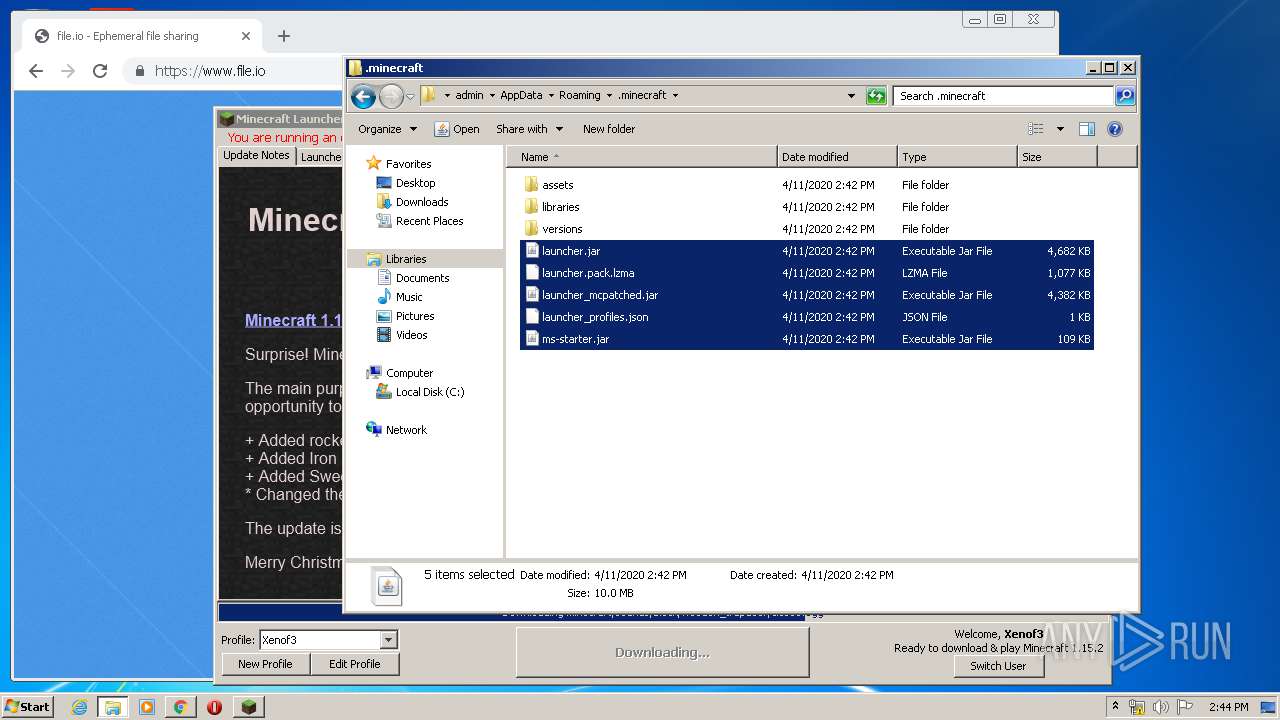
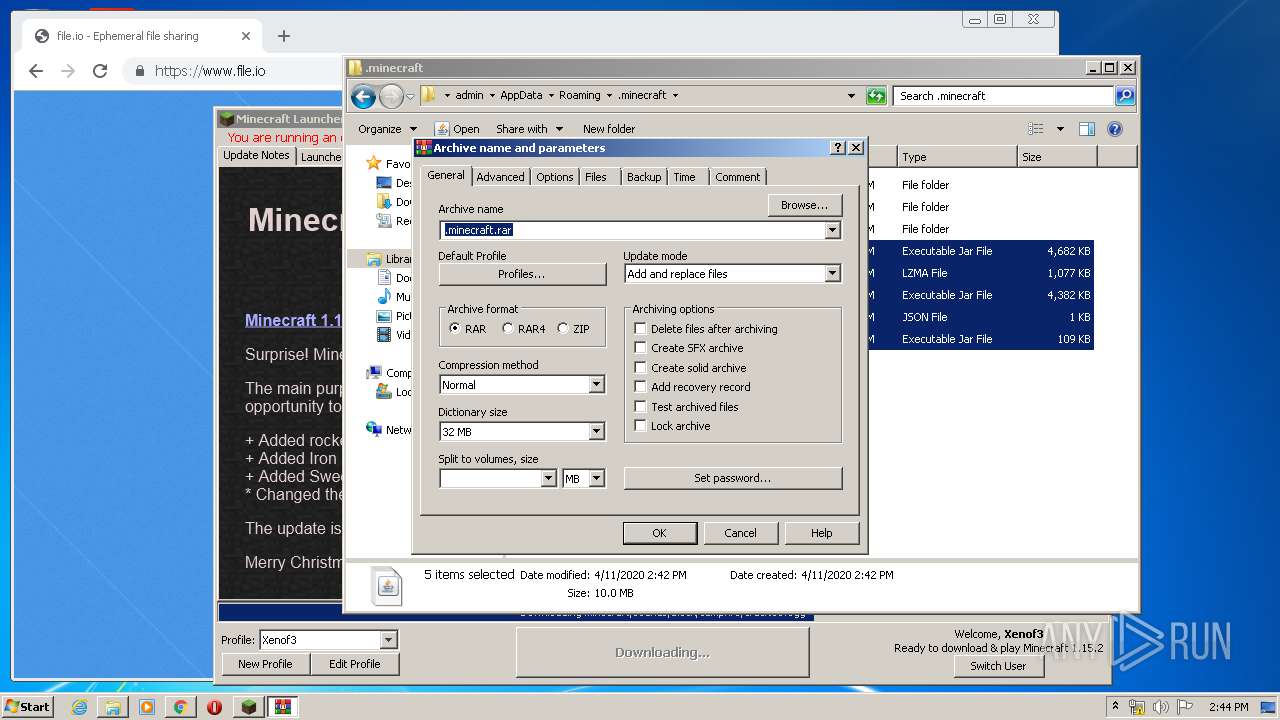
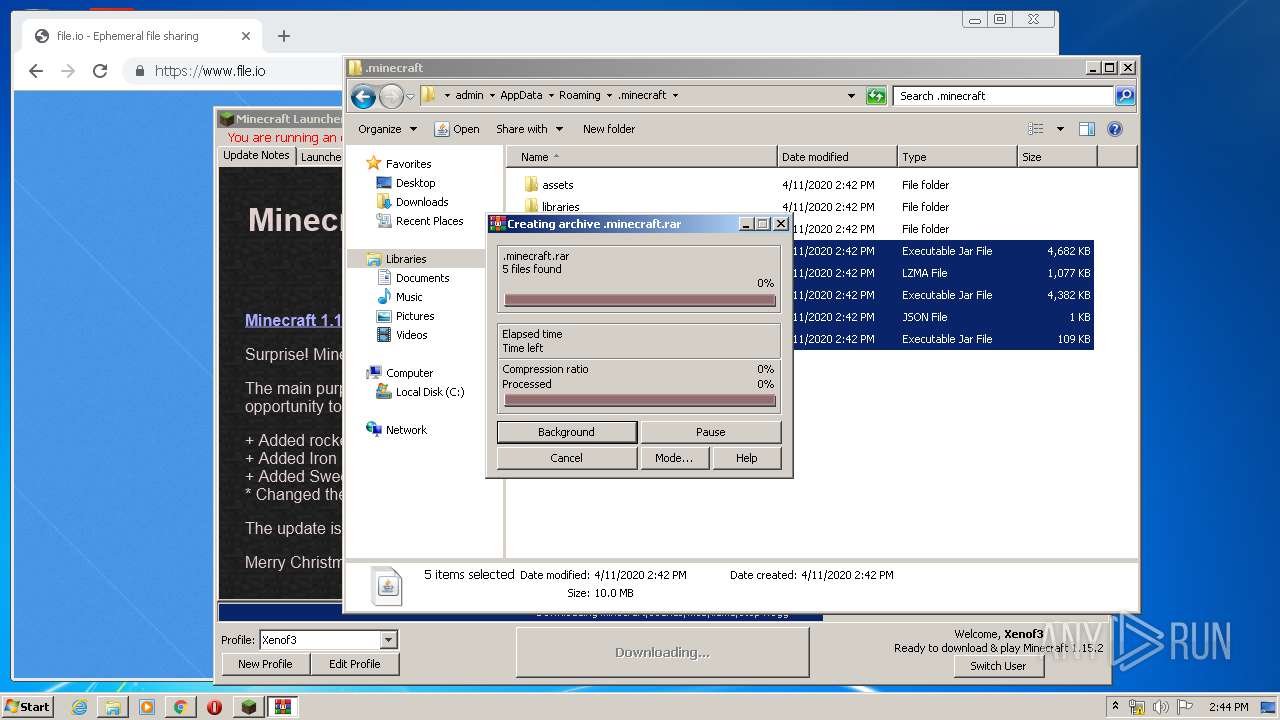
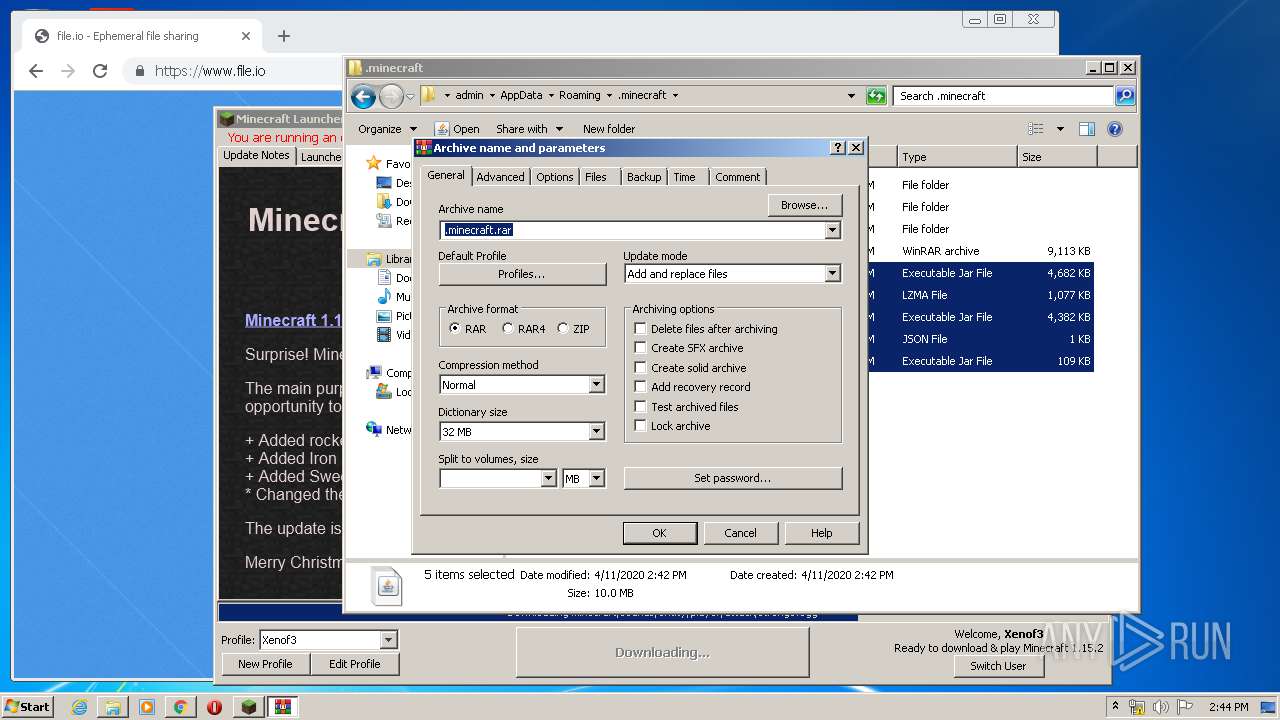
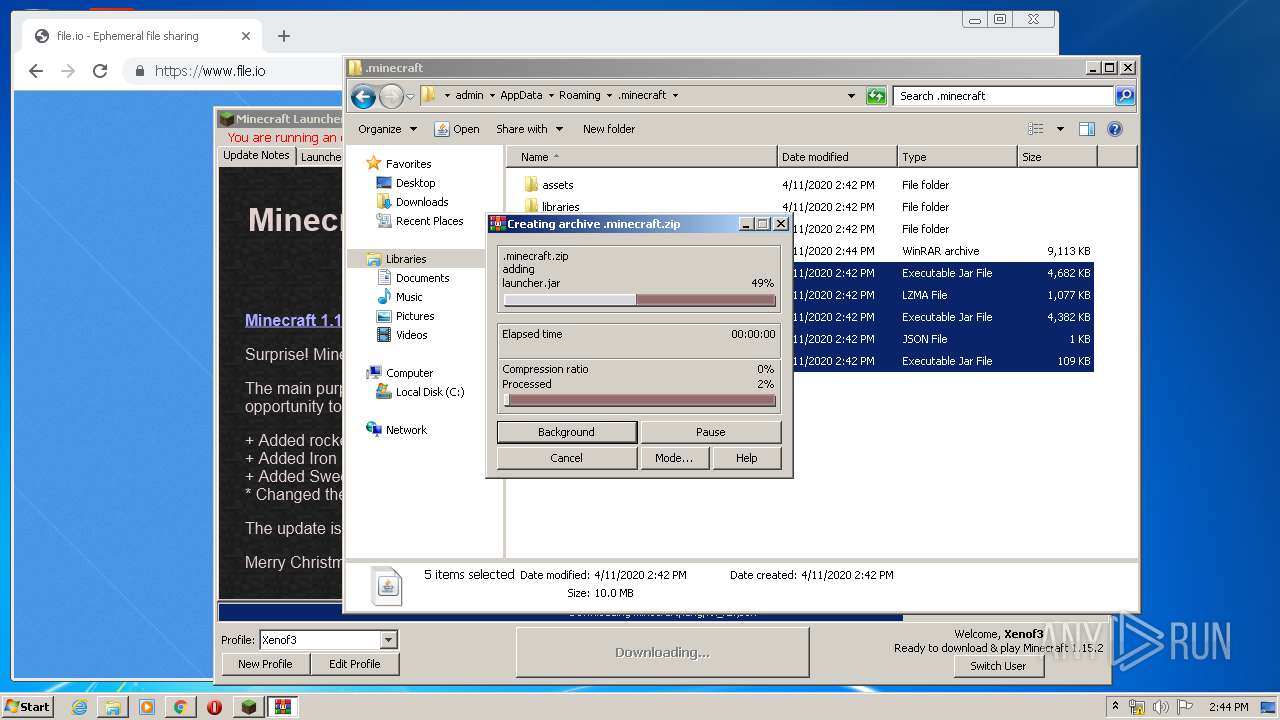
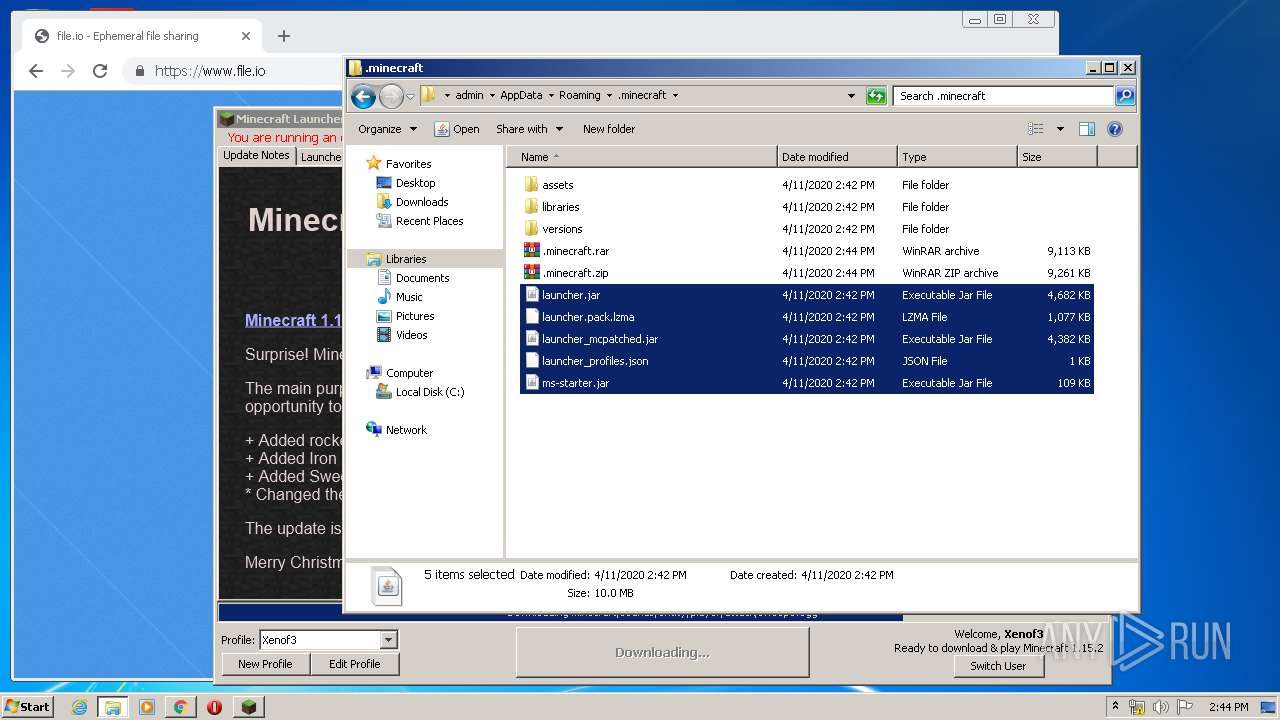
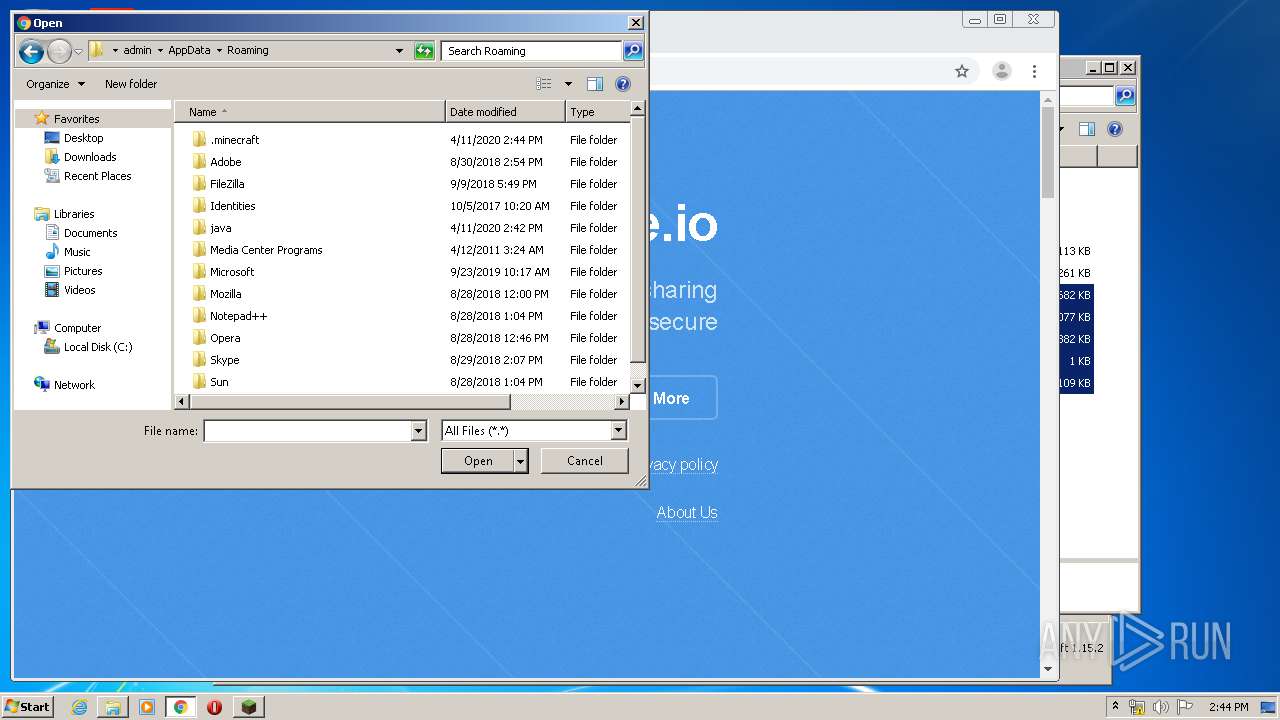
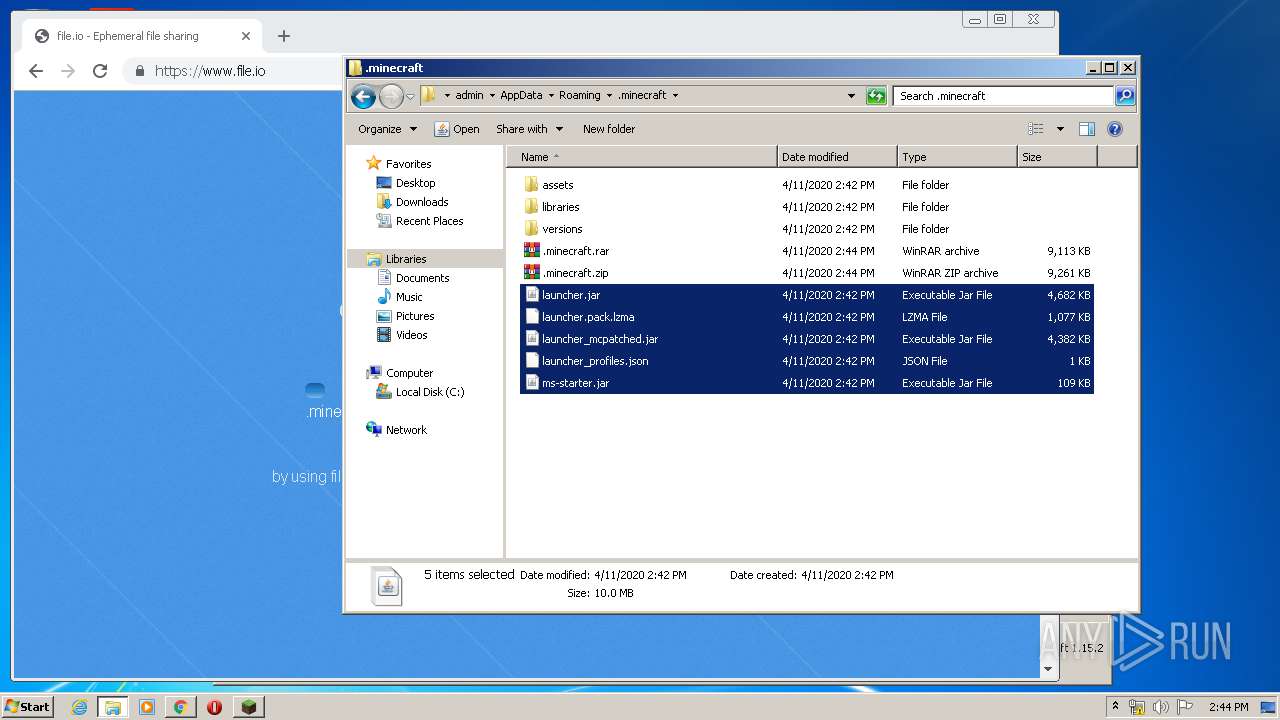
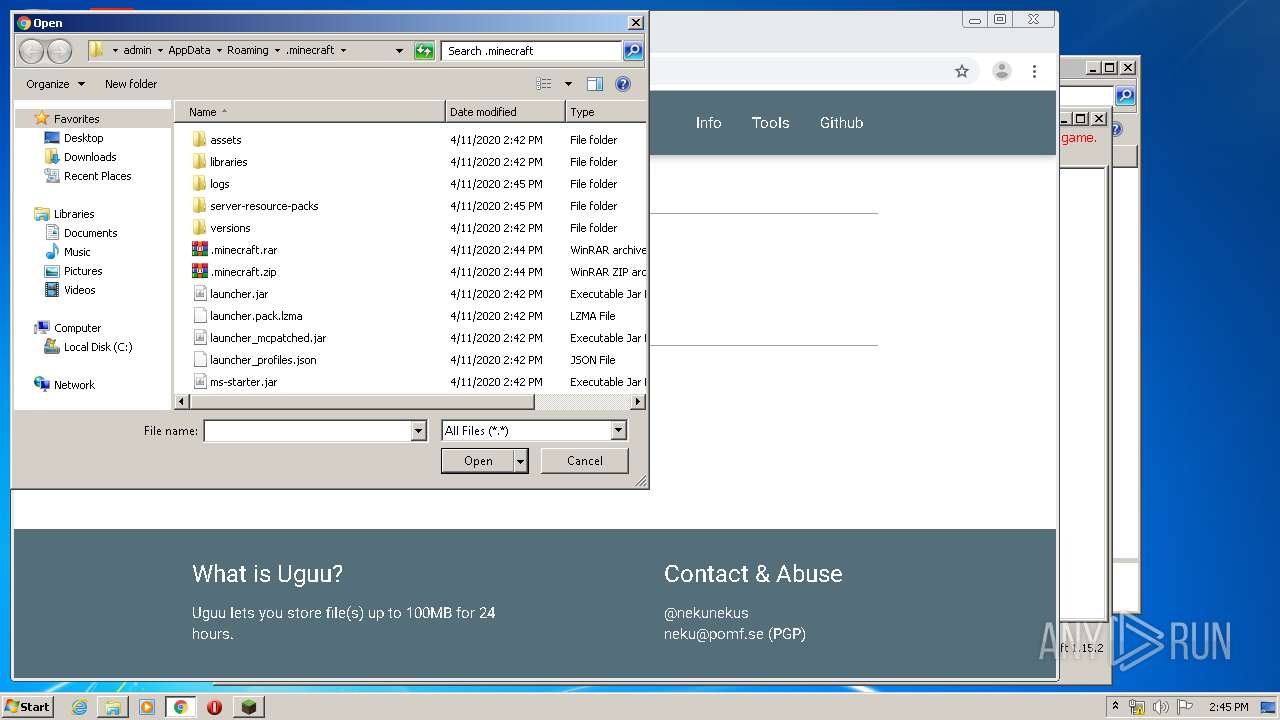
Creates files in the user directory
- javaw.exe (PID: 1172)
- WinRAR.exe (PID: 3776)
- WinRAR.exe (PID: 3380)
- javaw.exe (PID: 348)
Executes JAVA applets
- javaw.exe (PID: 348)
INFO
Reads the hosts file
- chrome.exe (PID: 3732)
- chrome.exe (PID: 1948)
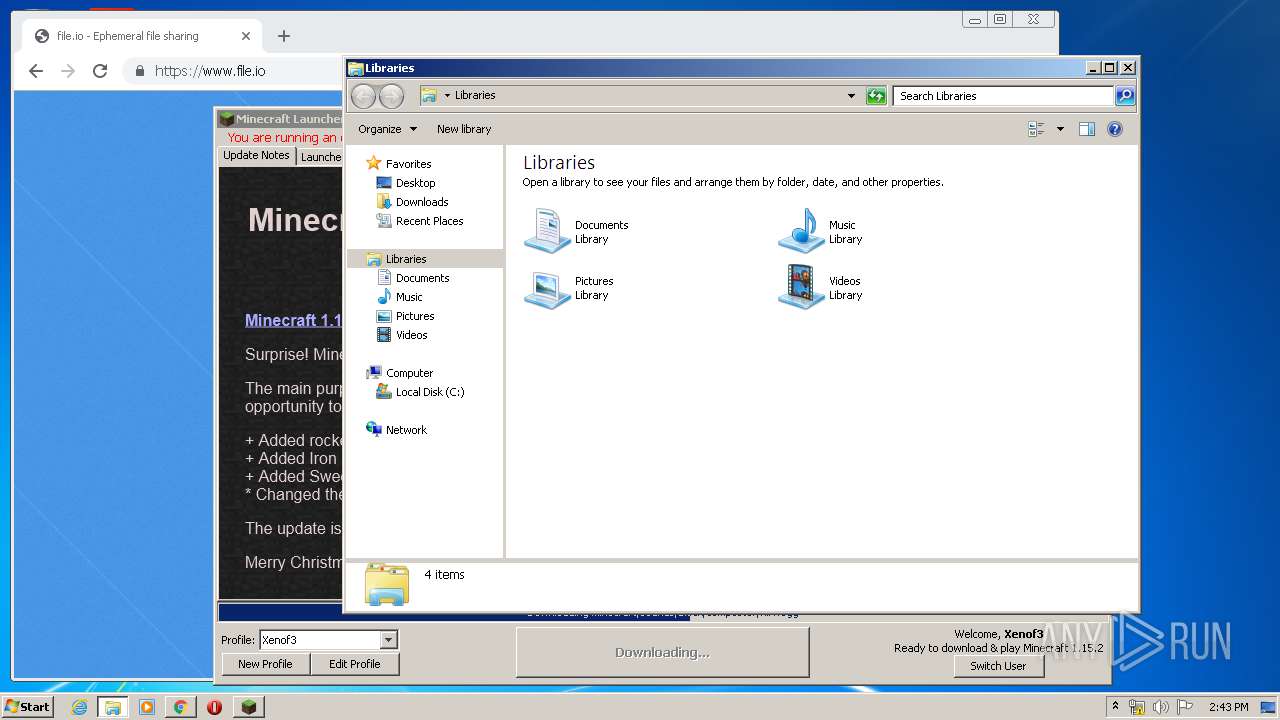
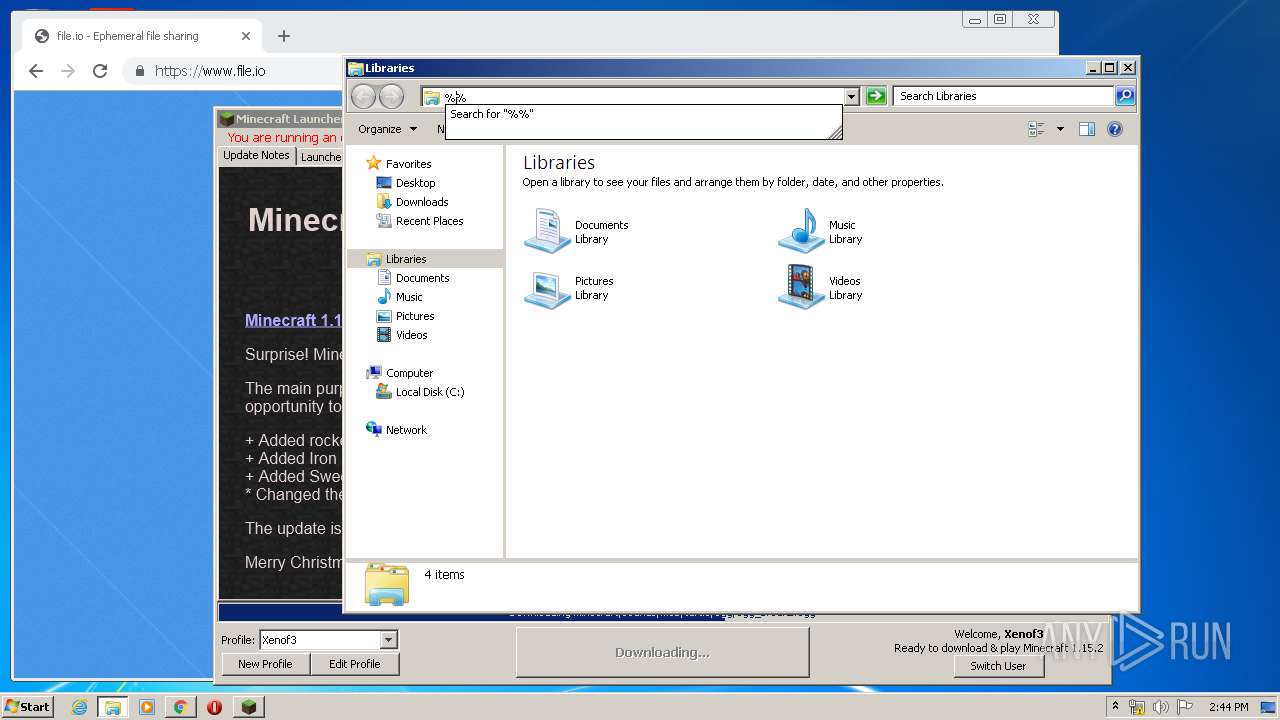
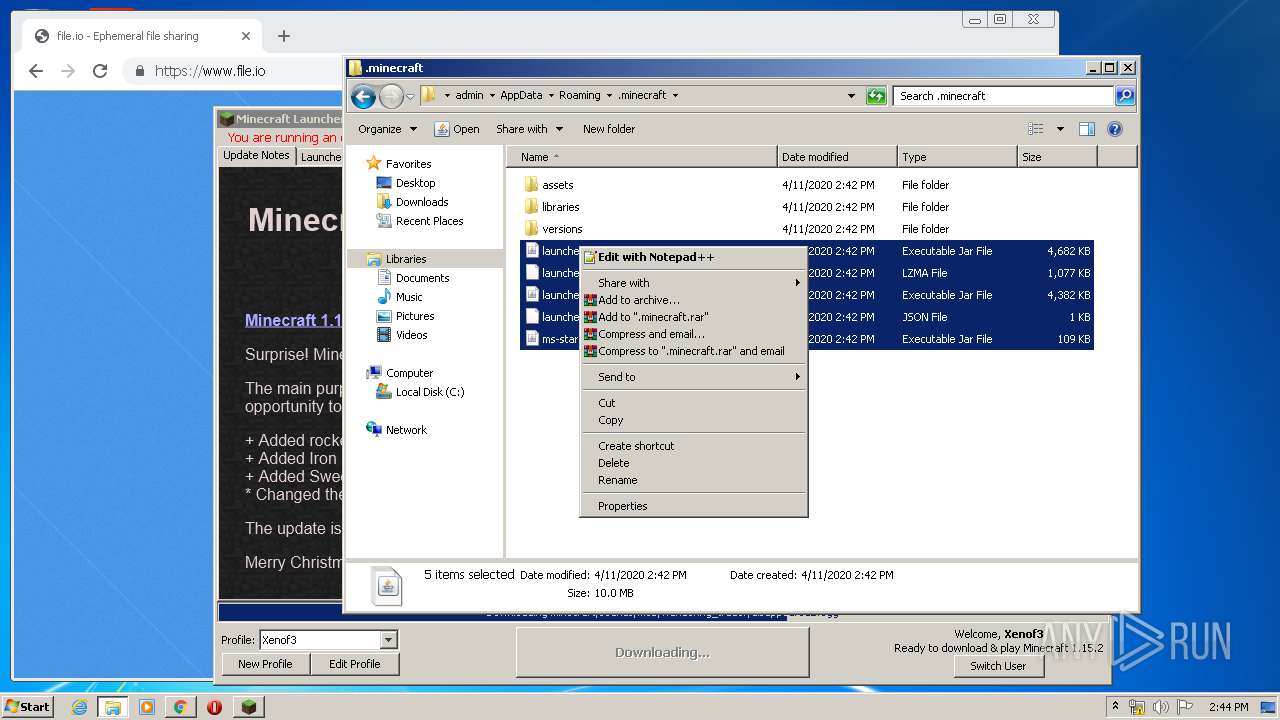
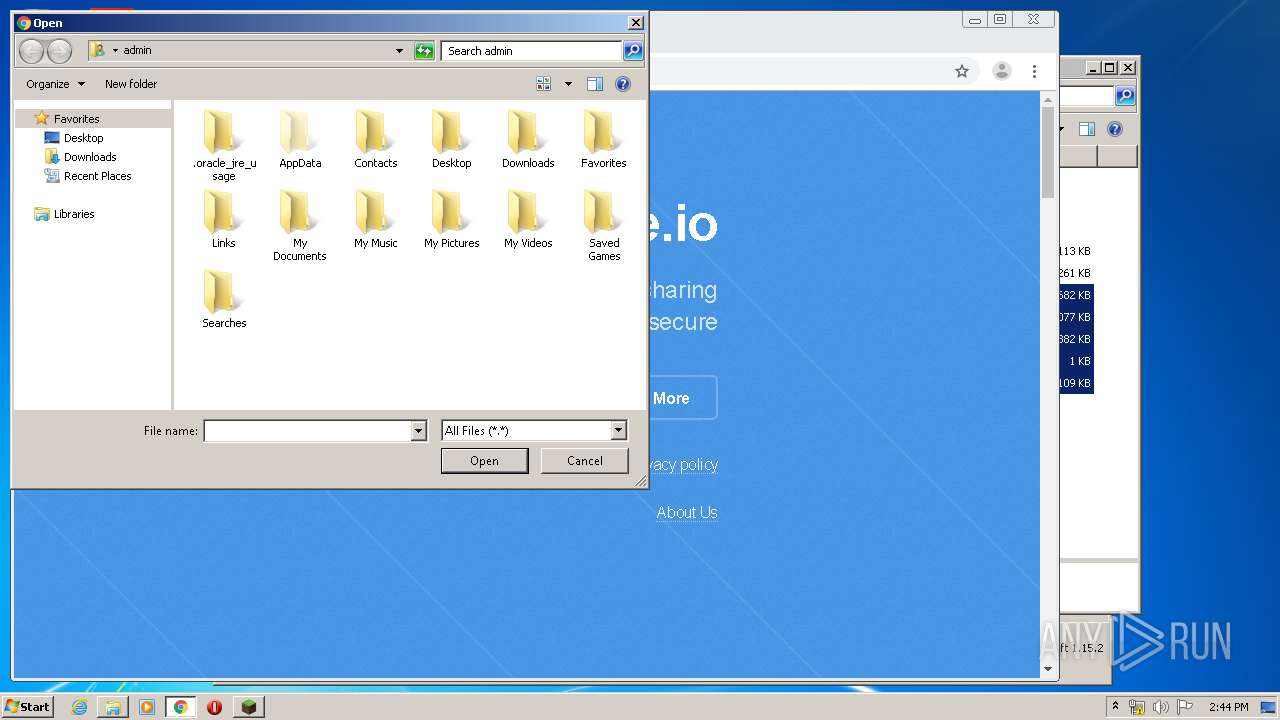
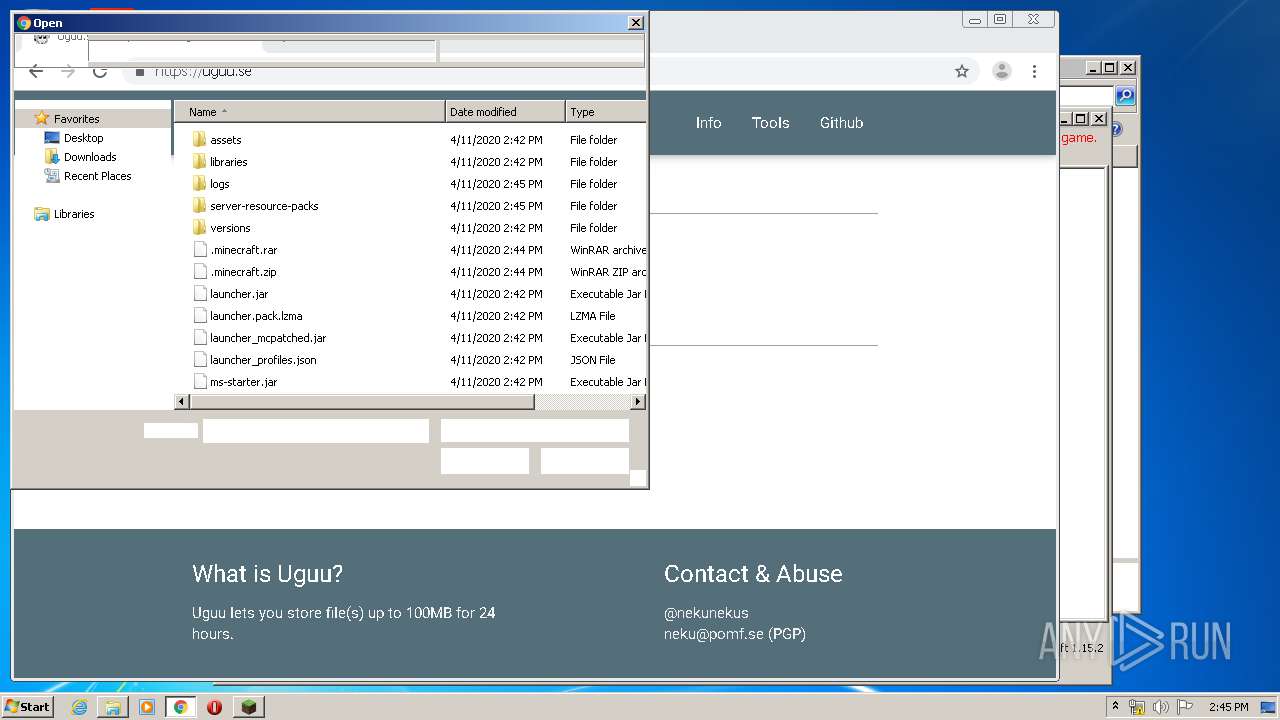
Manual execution by user
- explorer.exe (PID: 1248)
- chrome.exe (PID: 3732)
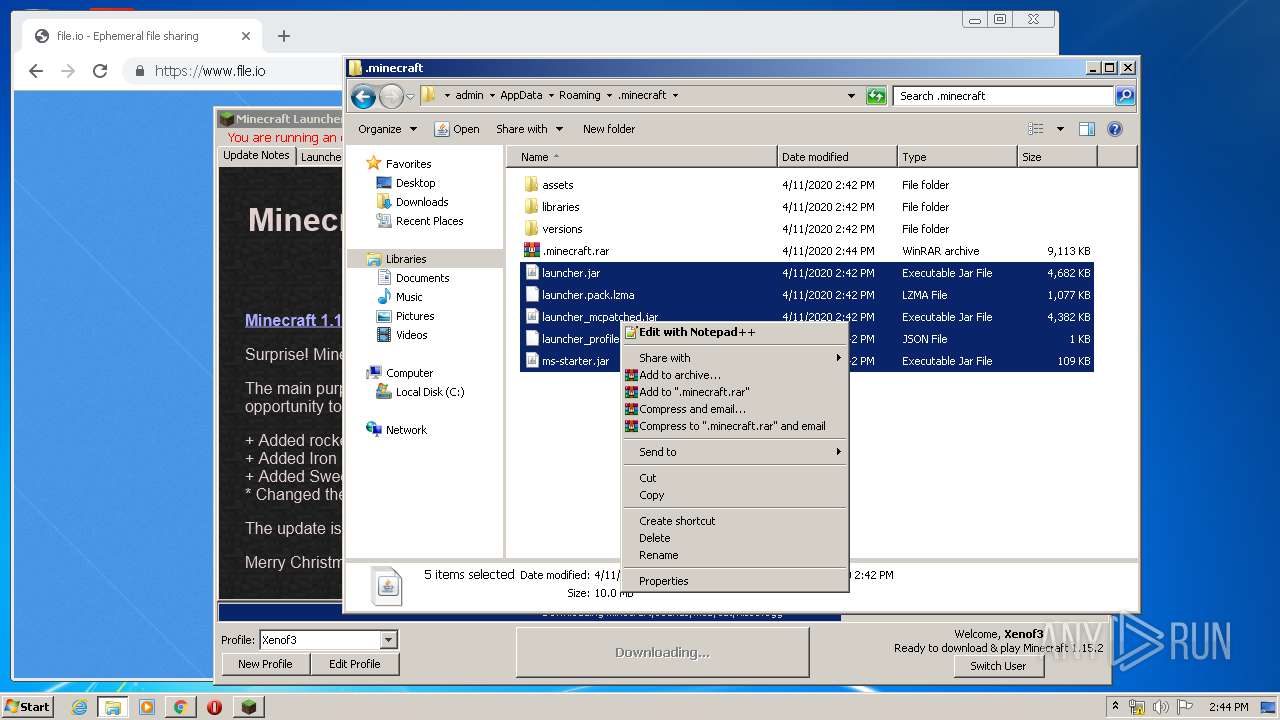
- WinRAR.exe (PID: 3776)
- WinRAR.exe (PID: 3380)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3732)
- javaw.exe (PID: 348)
Application launched itself
- chrome.exe (PID: 3732)
Reads settings of System Certificates
- chrome.exe (PID: 1948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:05 23:31:15 |
| ZipCRC: | 0xe40dfb26 |
| ZipCompressedSize: | 67 |
| ZipUncompressedSize: | 65 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
97
Monitored processes
56
Malicious processes
1
Suspicious processes
1
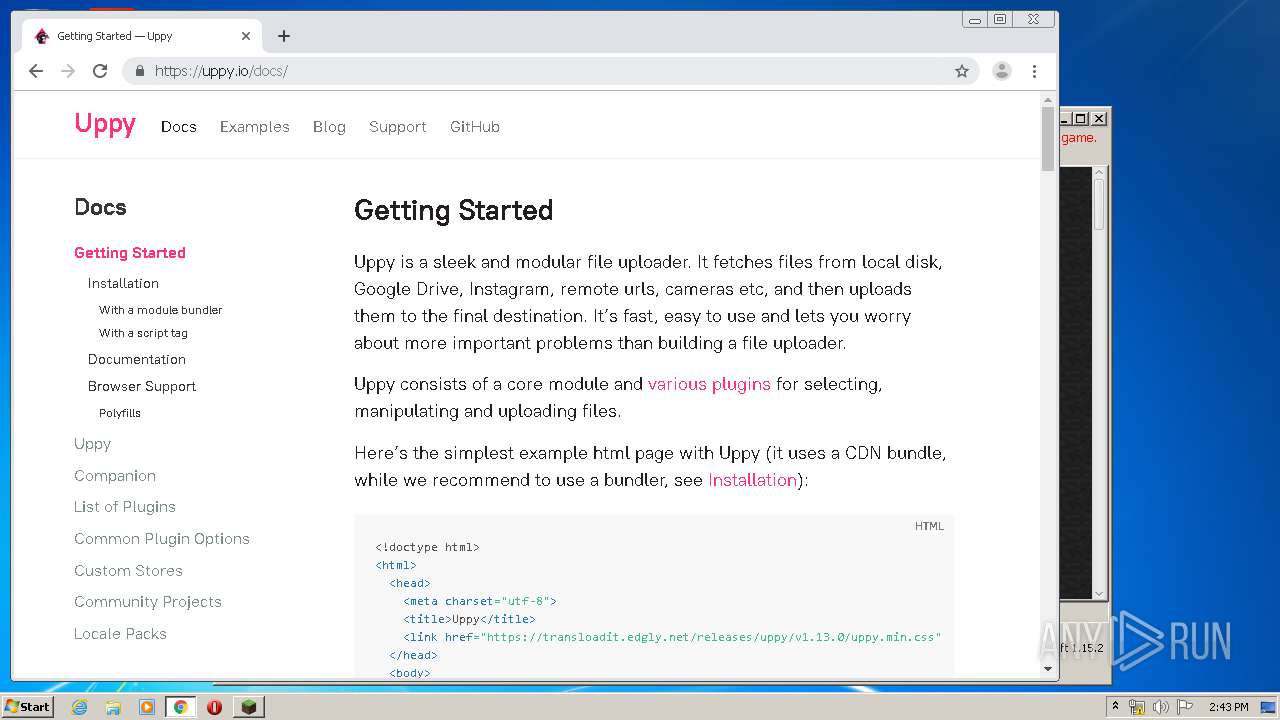
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1972444611341080477,13257624025593577149,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9714530113363067309 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1972444611341080477,13257624025593577149,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13454232469207688184 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
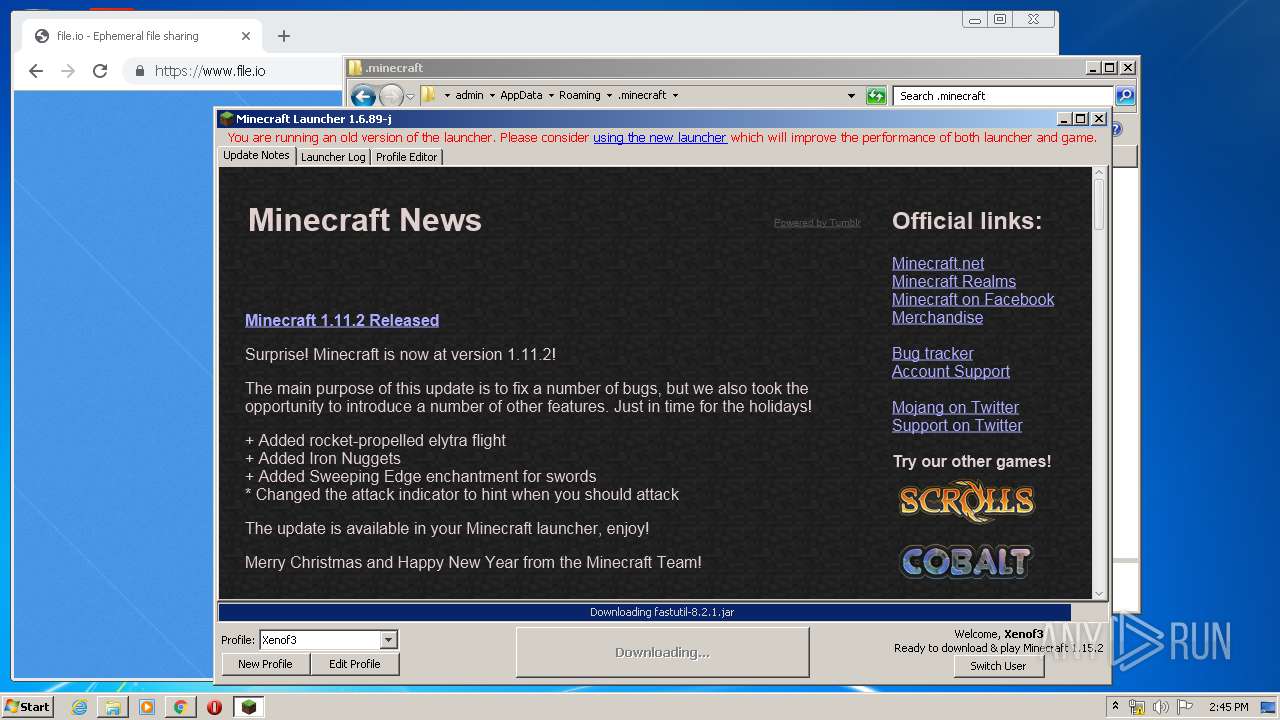
| 348 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\Mineshafter-launcher.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1972444611341080477,13257624025593577149,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8319342761614406858 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1972444611341080477,13257624025593577149,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1352343597292959348 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1972444611341080477,13257624025593577149,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2266522485363112874 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1972444611341080477,13257624025593577149,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17624112901296518737 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
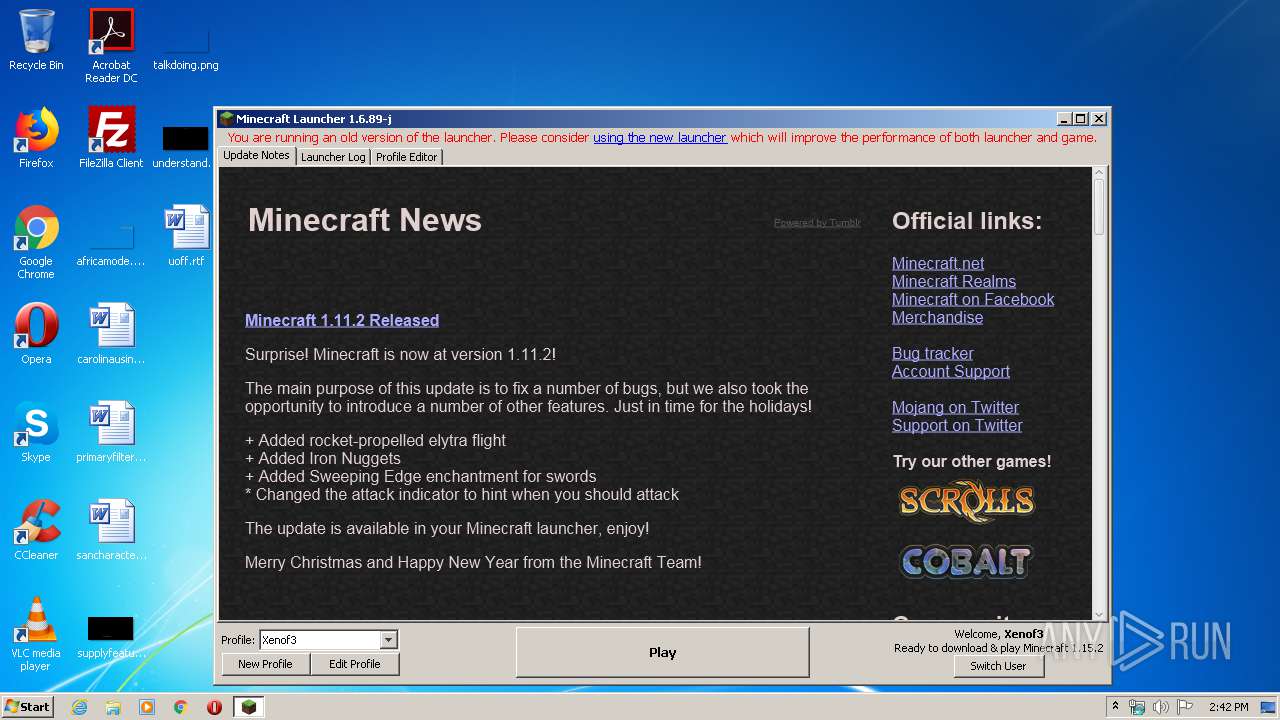
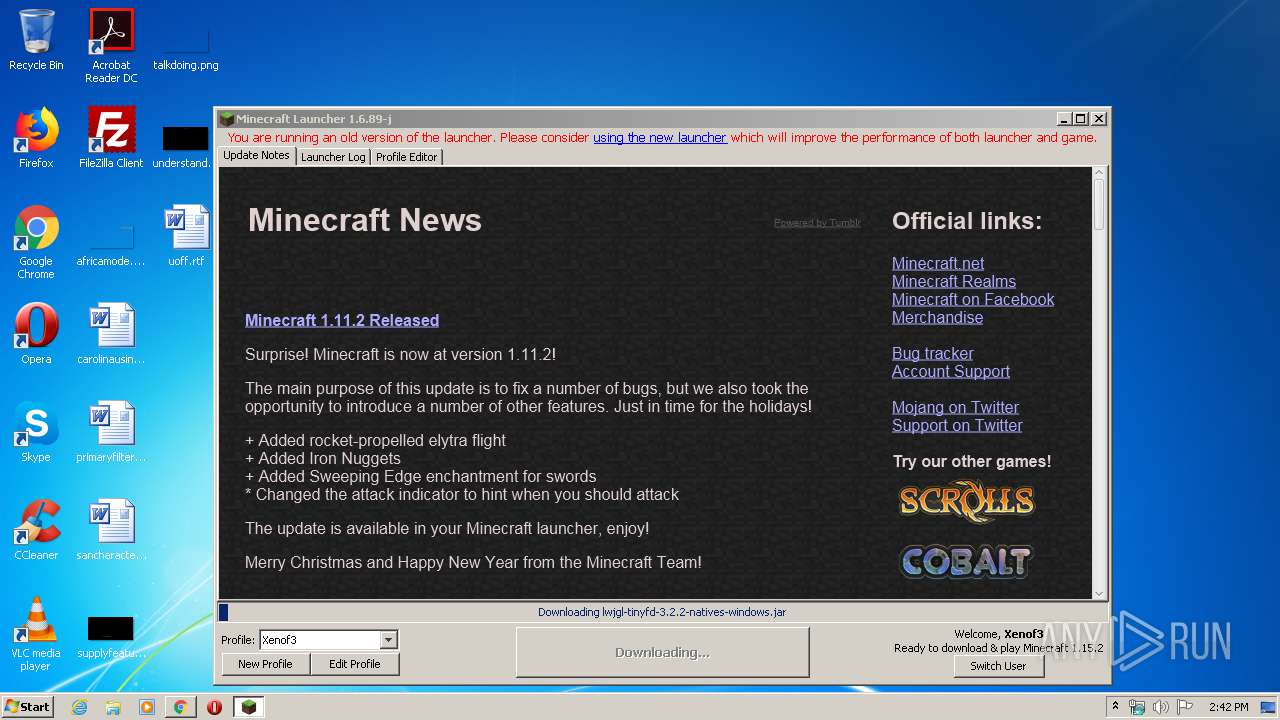
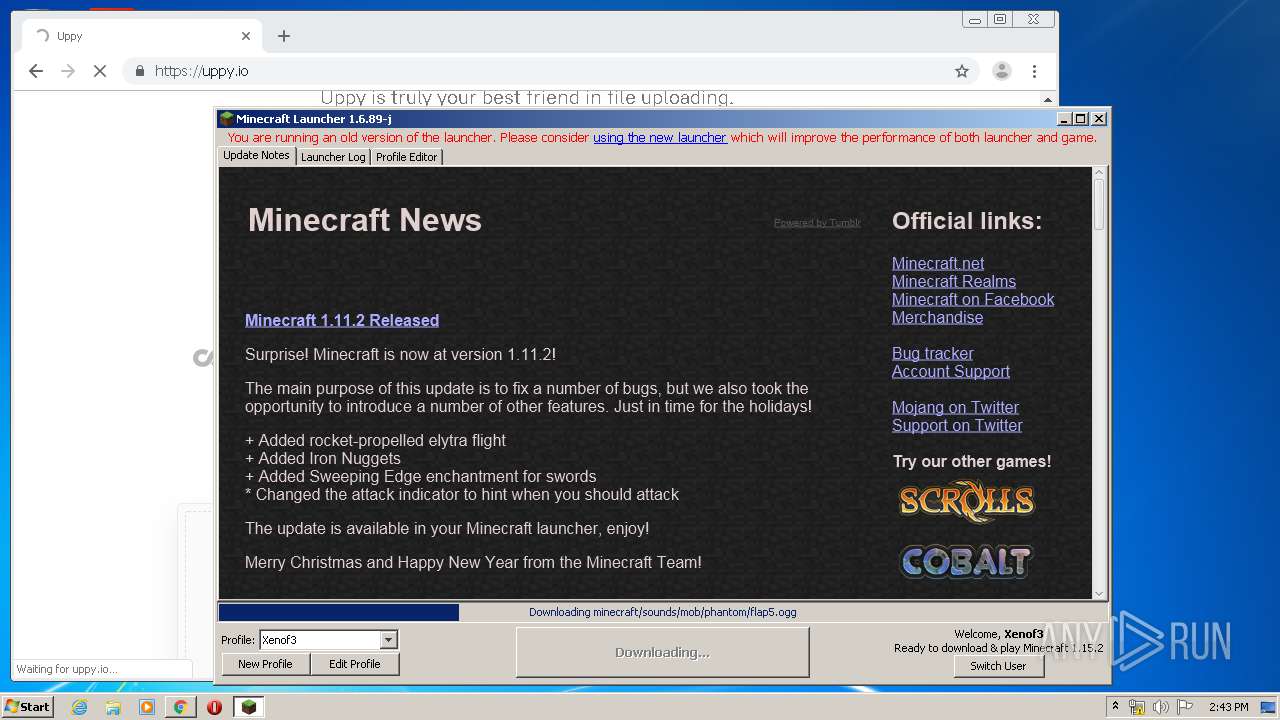
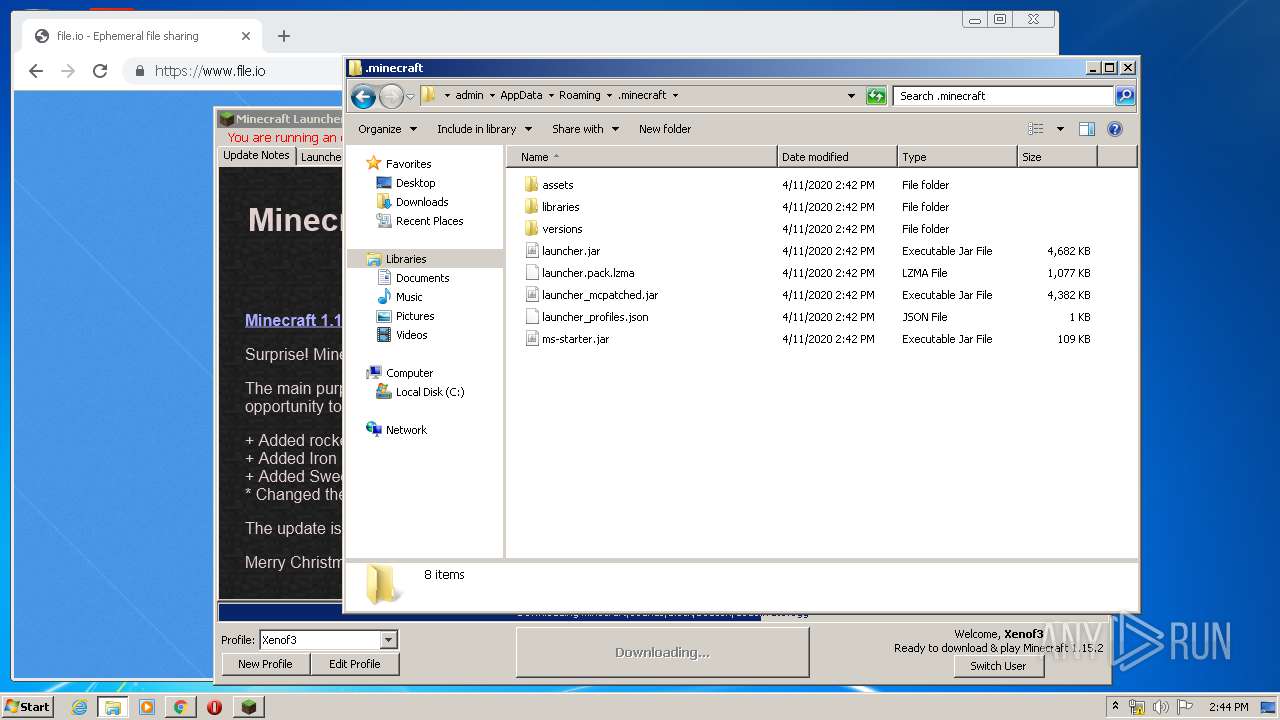
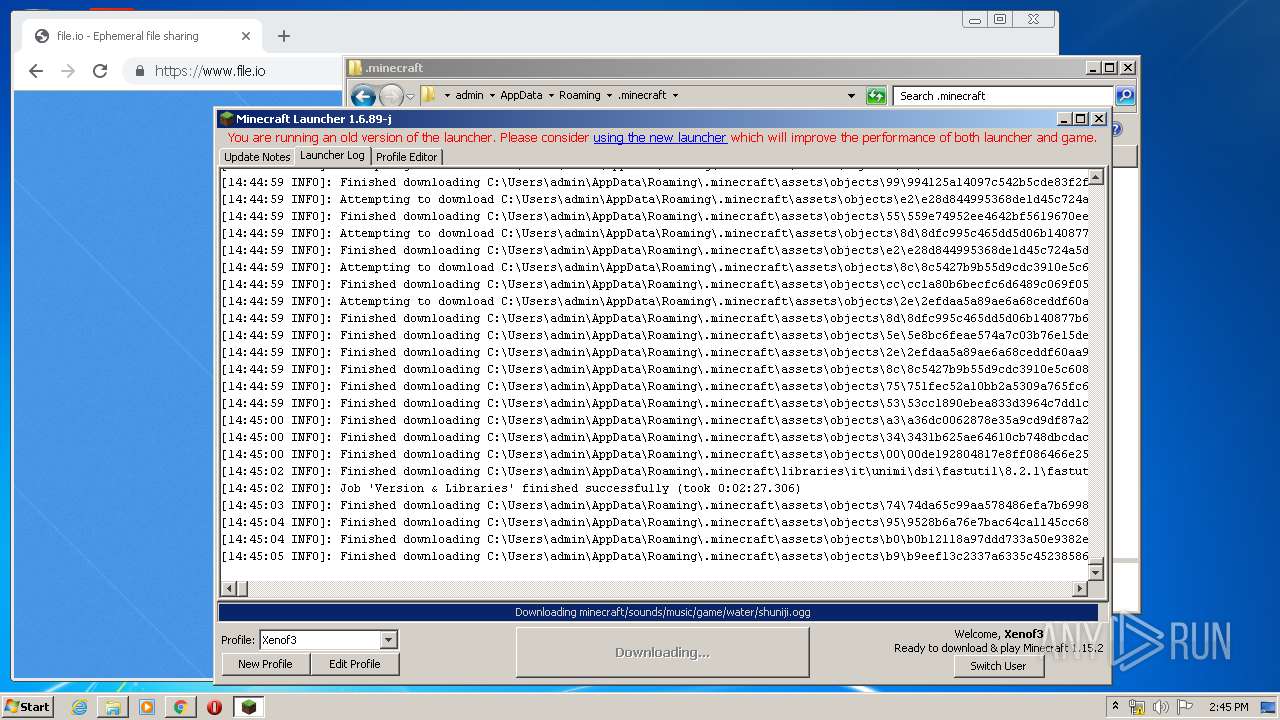
| 1172 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Xmx512M -XX:+UseConcMarkSweepGC -XX:+CMSIncrementalMode -XX:-UseAdaptiveSizePolicy -Xmn128M -XX:HeapDumpPath=MojangTricksIntelDriversForPerformance_javaw.exe_minecraft.exe.heapdump -Xss1M -Djava.library.path=C:\Users\admin\AppData\Roaming\.minecraft\versions\1.15.2\1.15.2-natives-11110717650177 -Dminecraft.launcher.brand=java-minecraft-launcher -Dminecraft.launcher.version=1.6.89-j -cp C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\patchy\1.1\patchy-1.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\oshi-project\oshi-core\1.1\oshi-core-1.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\dev\jna\jna\4.4.0\jna-4.4.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\dev\jna\platform\3.4.0\platform-3.4.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\ibm\icu\icu4j-core-mojang\51.2\icu4j-core-mojang-51.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\javabridge\1.0.22\javabridge-1.0.22.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\sf\jopt-simple\jopt-simple\5.0.3\jopt-simple-5.0.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\io\netty\netty-all\4.1.25.Final\netty-all-4.1.25.Final.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\google\guava\guava\21.0\guava-21.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\commons\commons-lang3\3.5\commons-lang3-3.5.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-io\commons-io\2.5\commons-io-2.5.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-codec\commons-codec\1.10\commons-codec-1.10.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\jinput\jinput\2.0.5\jinput-2.0.5.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\jutils\jutils\1.0.0\jutils-1.0.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\brigadier\1.0.17\brigadier-1.0.17.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\datafixerupper\2.0.24\datafixerupper-2.0.24.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\google\code\gson\gson\2.8.0\gson-2.8.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\authlib\1.5.25\authlib-1.5.25.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\commons\commons-compress\1.8.1\commons-compress-1.8.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\httpcomponents\httpclient\4.3.3\httpclient-4.3.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-logging\commons-logging\1.1.3\commons-logging-1.1.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\httpcomponents\httpcore\4.3.2\httpcore-4.3.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\it\unimi\dsi\fastutil\8.2.1\fastutil-8.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\logging\log4j\log4j-api\2.8.1\log4j-api-2.8.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\logging\log4j\log4j-core\2.8.1\log4j-core-2.8.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl\3.2.2\lwjgl-3.2.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-jemalloc\3.2.2\lwjgl-jemalloc-3.2.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-openal\3.2.2\lwjgl-openal-3.2.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-opengl\3.2.2\lwjgl-opengl-3.2.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-glfw\3.2.2\lwjgl-glfw-3.2.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-stb\3.2.2\lwjgl-stb-3.2.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-tinyfd\3.2.2\lwjgl-tinyfd-3.2.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\text2speech\1.11.3\text2speech-1.11.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\versions\1.15.2\1.15.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\ms-starter.jar info.mineshafter.GameStarter net.minecraft.client.main.Main --username Xenof3 --version 1.15.2 --gameDir C:\Users\admin\AppData\Roaming\.minecraft --assetsDir C:\Users\admin\AppData\Roaming\.minecraft\assets --assetIndex 1.15 --uuid d41d8cd98f00b204e9800998ecf8427e --accessToken d26f1d82-3376-847f-93d1-10ac52265d21 --userType mojang --versionType release | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1248 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1972444611341080477,13257624025593577149,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17782309115350559663 --mojo-platform-channel-handle=3196 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 201
Read events
2 841
Write events
348
Delete events
12
Modification events
| (PID) Process: | (348) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3732-13231086157687890 |
Value: 259 | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
Executable files
38
Suspicious files
211
Text files
619
Unknown types
1 830
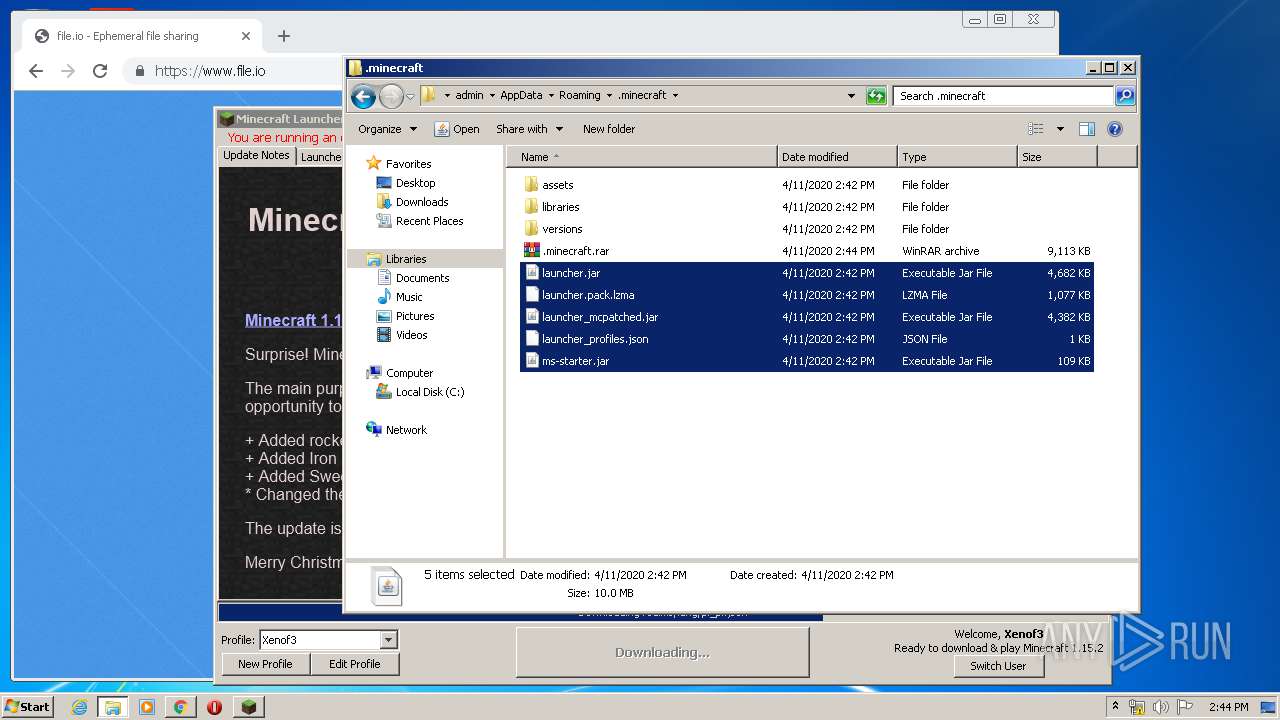
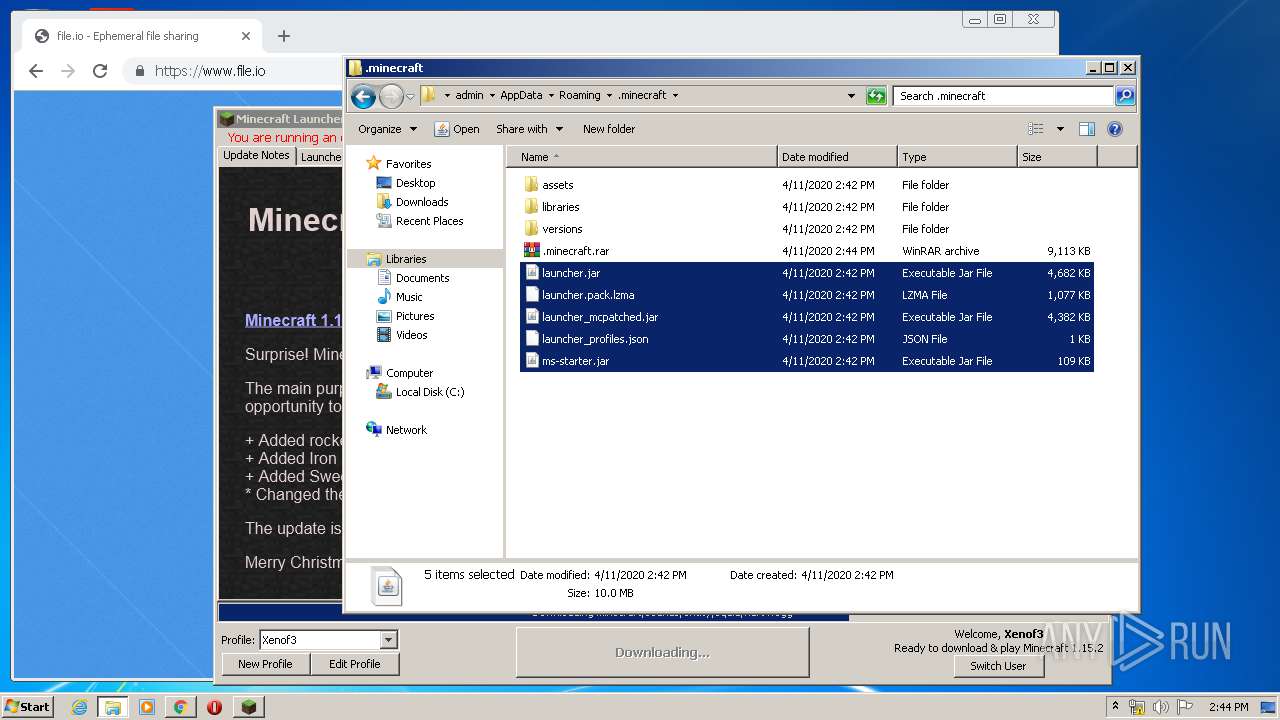
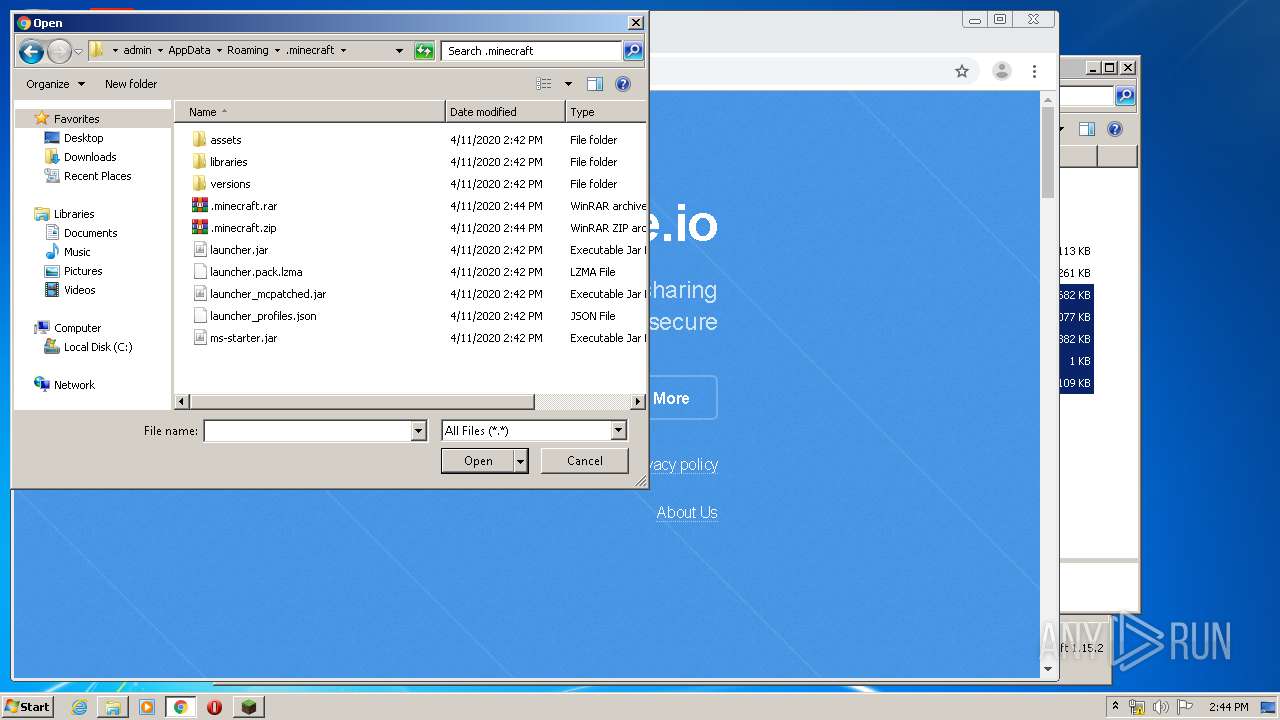
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 348 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher.pack.lzma.new | — | |
MD5:— | SHA256:— | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8295219411454621765.tmp | — | |
MD5:— | SHA256:— | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio593381742561035436.tmp | — | |
MD5:— | SHA256:— | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8504632022432487163.tmp | — | |
MD5:— | SHA256:— | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2643312977206785157.tmp | — | |
MD5:— | SHA256:— | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher.pack | binary | |
MD5:8F5851921290765F3FC77ED38C9331B3 | SHA256:BF3BD4017B0E6D28D93C3764CDC51C89BF0598DF7EFEA85917C85A4CBCF29D71 | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher.jar | java | |
MD5:83D14C2ABBF3097132C8CF0015A614A2 | SHA256:D020678C4C1B6E95D707B9D4ACF075139AB20C8223D8F612CAB62A2E331BDA03 | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | text | |
MD5:55D4DB4BB753087492464E2AD0D91B6B | SHA256:4C8EC859055594A9670E8EC1FC6E224CED0B3948E27582F6CE25A8A96798C80A | |||
| 348 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:2BC5C9670254DD47109402B8B2F27C33 | SHA256:A49D49A1C4480B3FBF1225BEEBD8F9AFD9F8A0CE2E1B13435212789C7E5C6B55 | |||
| 348 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\versions\1.15.2\1.15.2.json | text | |
MD5:97A767BDD838F766BC9A21D57CF03AF0 | SHA256:CBB72030ABDC309507188B8C869DF8A3AB32AA9F7124F2A8CC96808A460D48BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
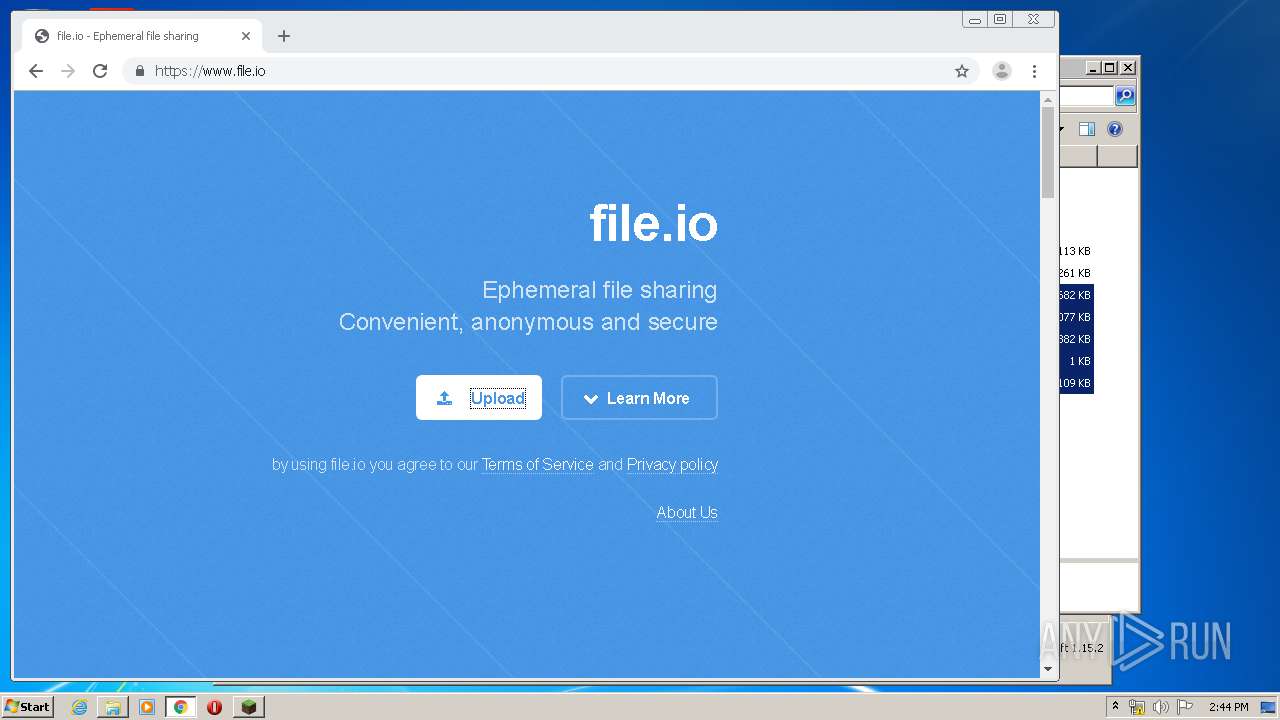
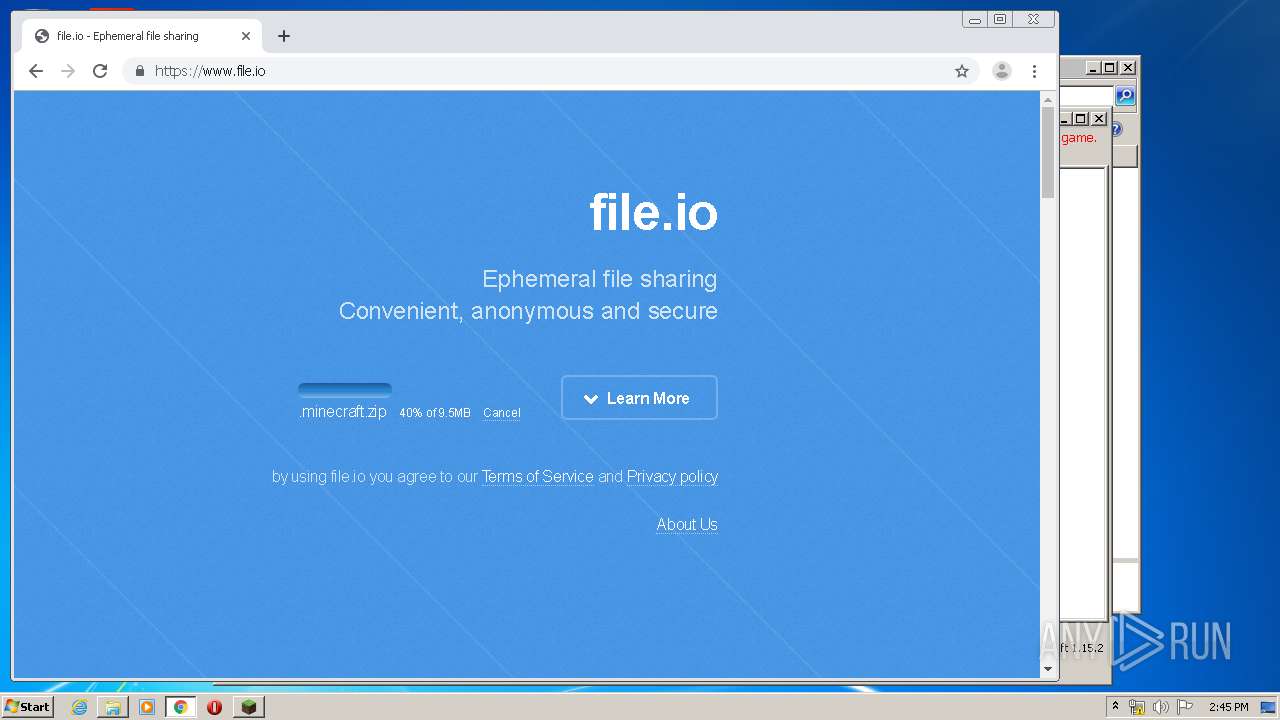
HTTP(S) requests
1 931
TCP/UDP connections
148
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
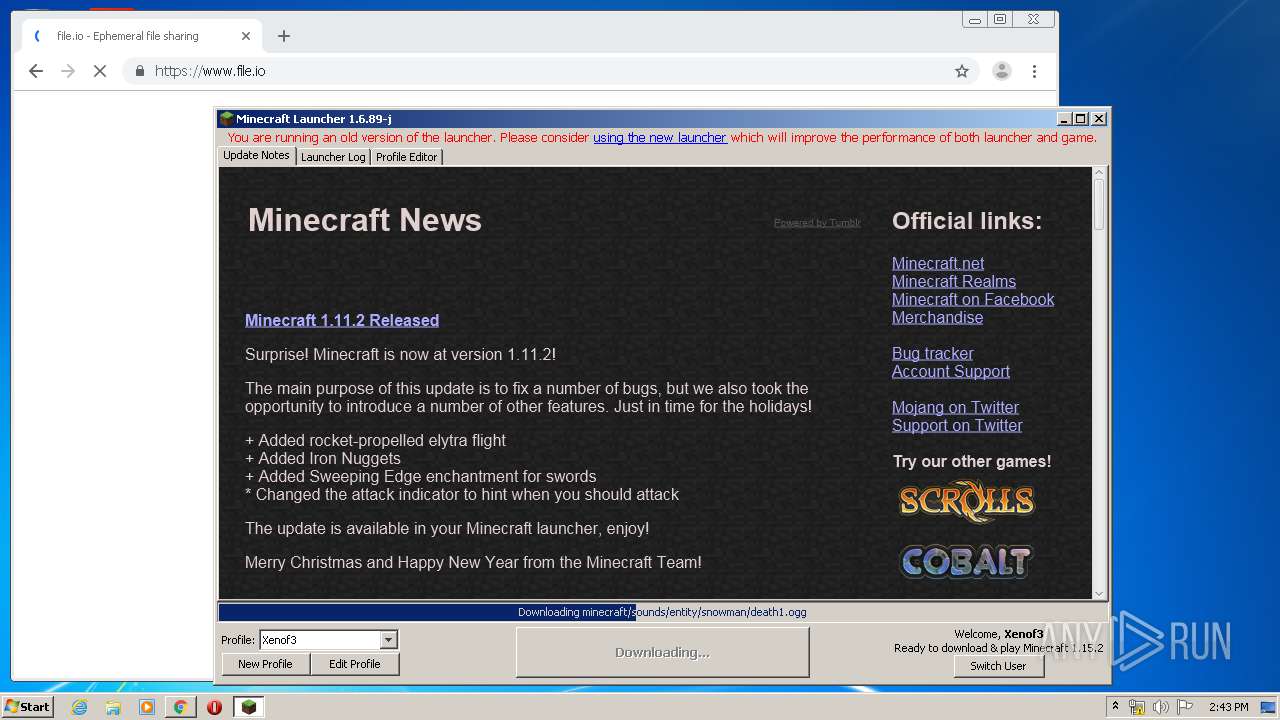
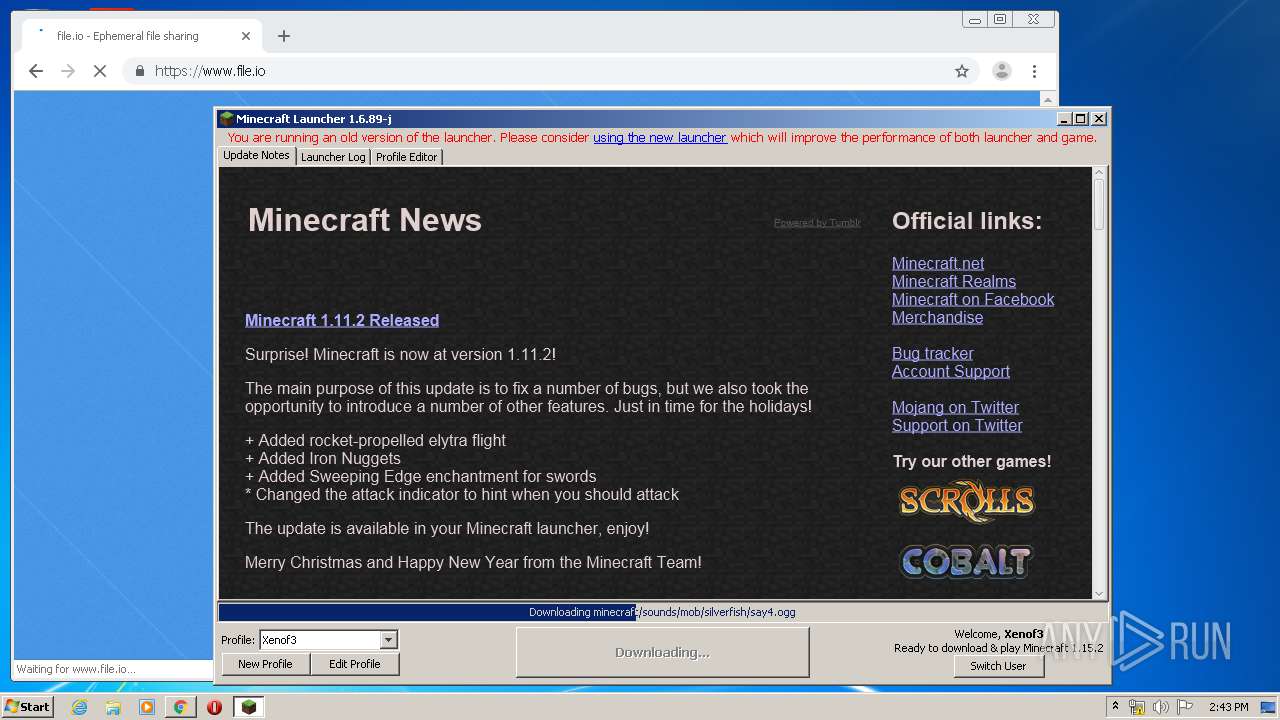
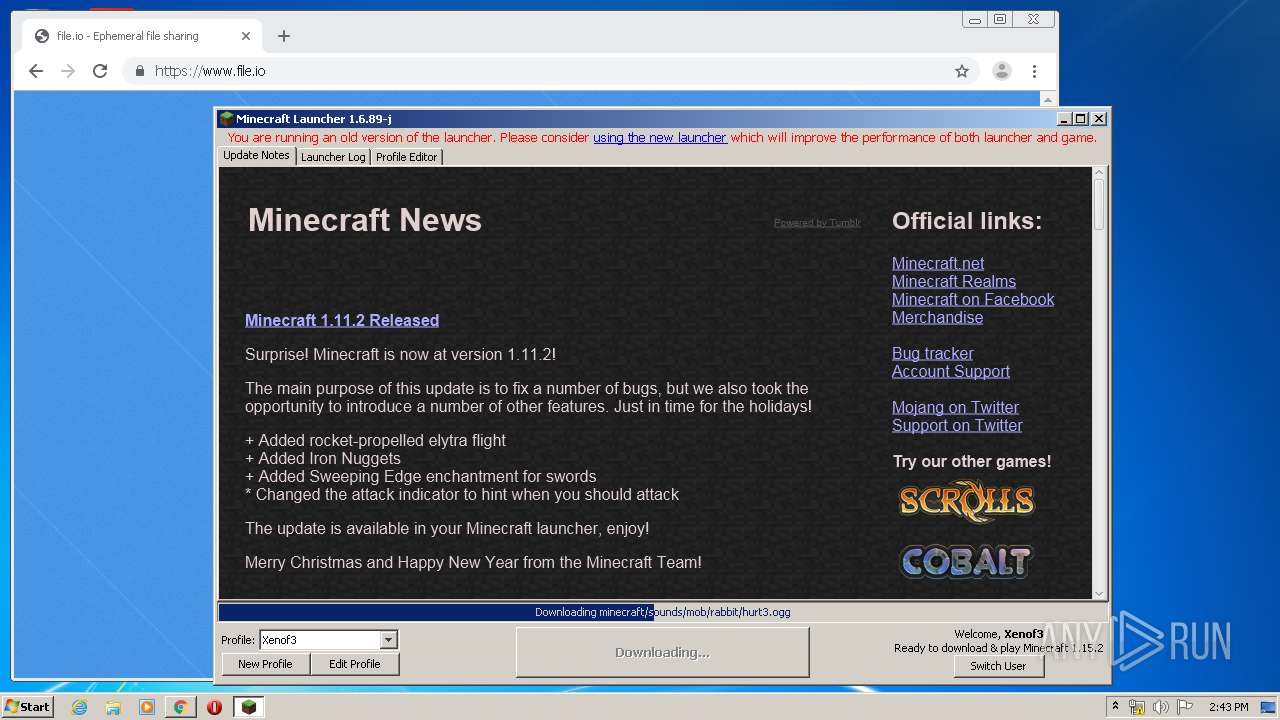
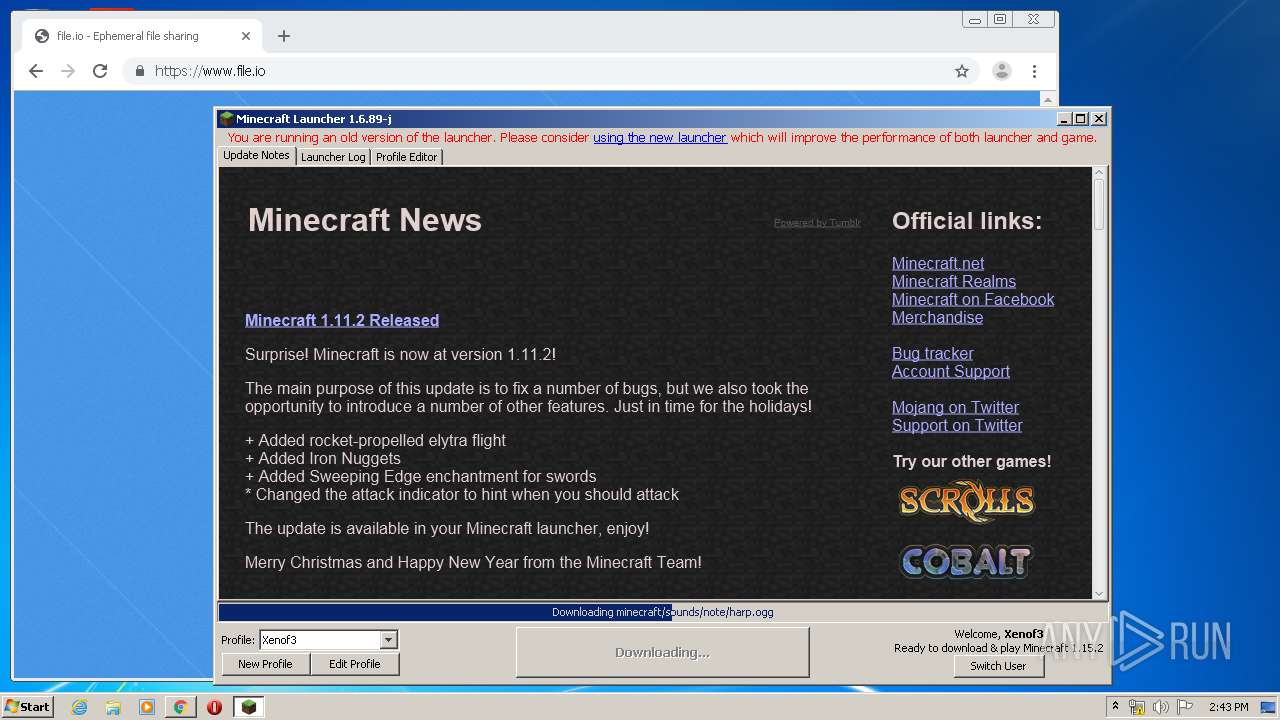
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/44/443a6c542e6cb96d8d7d6e185623266ce0c3af69 | US | ogg | 11.1 Kb | shared |
348 | javaw.exe | GET | 200 | 52.216.88.221:80 | http://assets.mojang.com/cobalt/cobalt_logo_150.PNG | US | image | 14.3 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/52/520aa25be86567d4b6f22aebd2a6add3aad7943d | US | ogg | 26.4 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/e5/e555fcece121879fe0becbada9d01dea27ab153d | US | ogg | 5.25 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/ed/edb8625e330ee1ee8ceeb2540cd083360e9daf65 | US | ogg | 4.87 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/7b/7b19c3abdf4a3ba1cd50947b87a097b40d9d8204 | US | ogg | 21.5 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/d9/d9485749329fba15803faa23dfadd05c5b294f91 | US | ogg | 21.2 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/f9/f9f79162efa6667b753c1fbb46ff9888e8ce5f32 | US | ogg | 7.53 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/f6/f6cf4a1595b52797b24f7bb7b3672564a64488c8 | US | ogg | 35.2 Kb | shared |
348 | javaw.exe | GET | 200 | 13.225.73.50:80 | http://resources.download.minecraft.net/db/dbb3a9ac12c4f888c3f94e8d60b6eb81c4204518 | US | text | 623 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
348 | javaw.exe | 152.199.19.43:443 | 66.media.tumblr.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
348 | javaw.exe | 52.216.88.221:80 | assets.mojang.com | Amazon.com, Inc. | US | unknown |
348 | javaw.exe | 13.224.189.128:443 | launcher.mojang.com | — | US | unknown |
348 | javaw.exe | 13.225.86.78:443 | libraries.minecraft.net | — | US | unknown |
1948 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
348 | javaw.exe | 13.225.73.50:80 | resources.download.minecraft.net | — | US | unknown |
1948 | chrome.exe | 216.58.210.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
348 | javaw.exe | 52.217.38.190:443 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
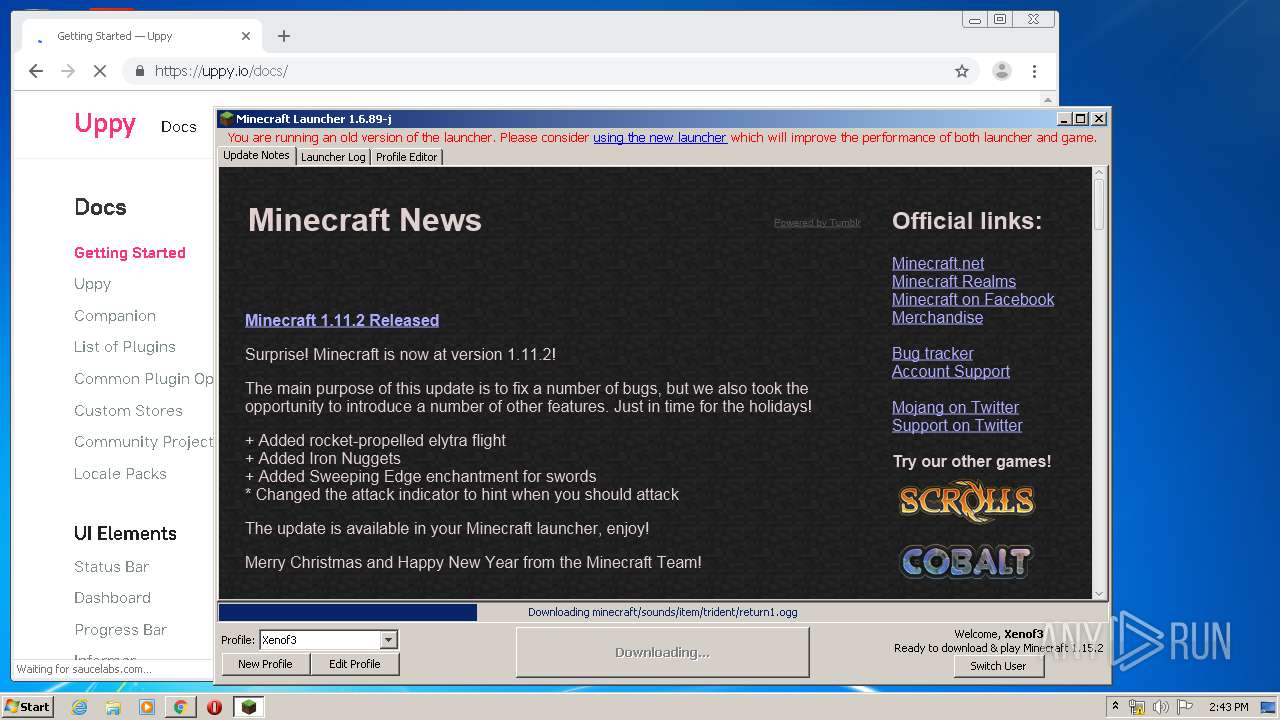
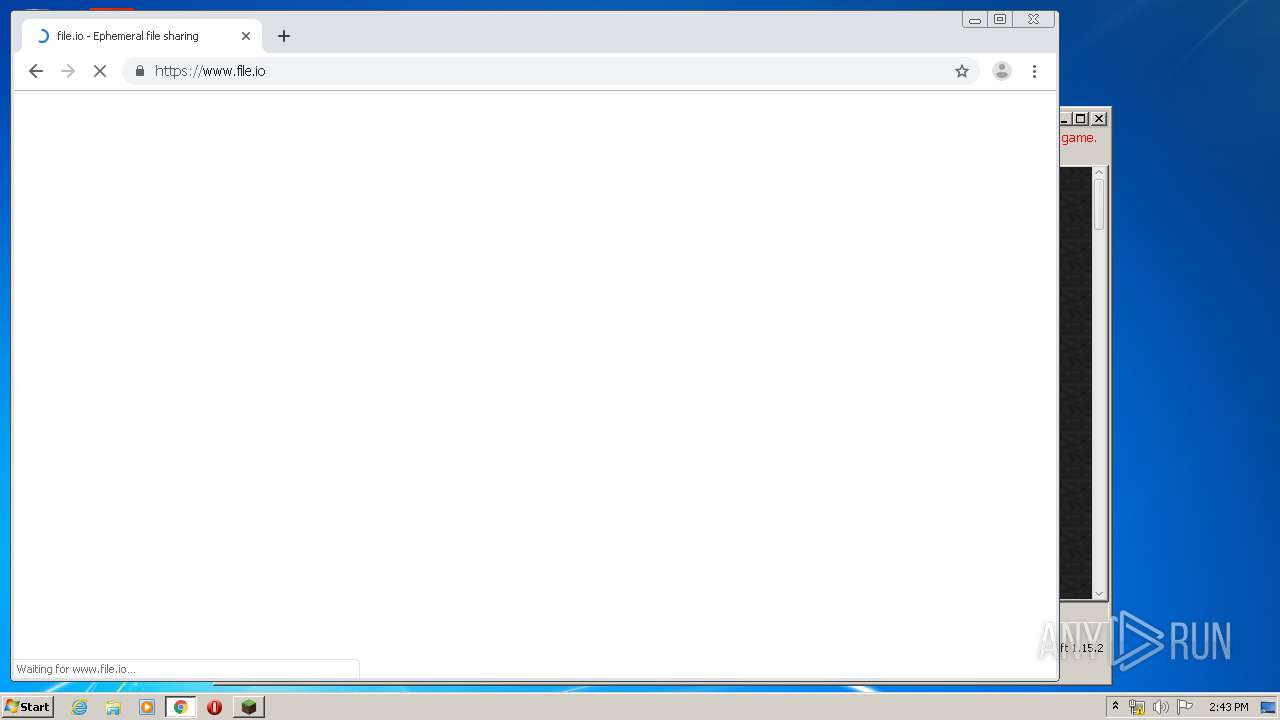
348 | javaw.exe | 74.114.154.18:80 | mcupdate.tumblr.com | Automattic, Inc | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
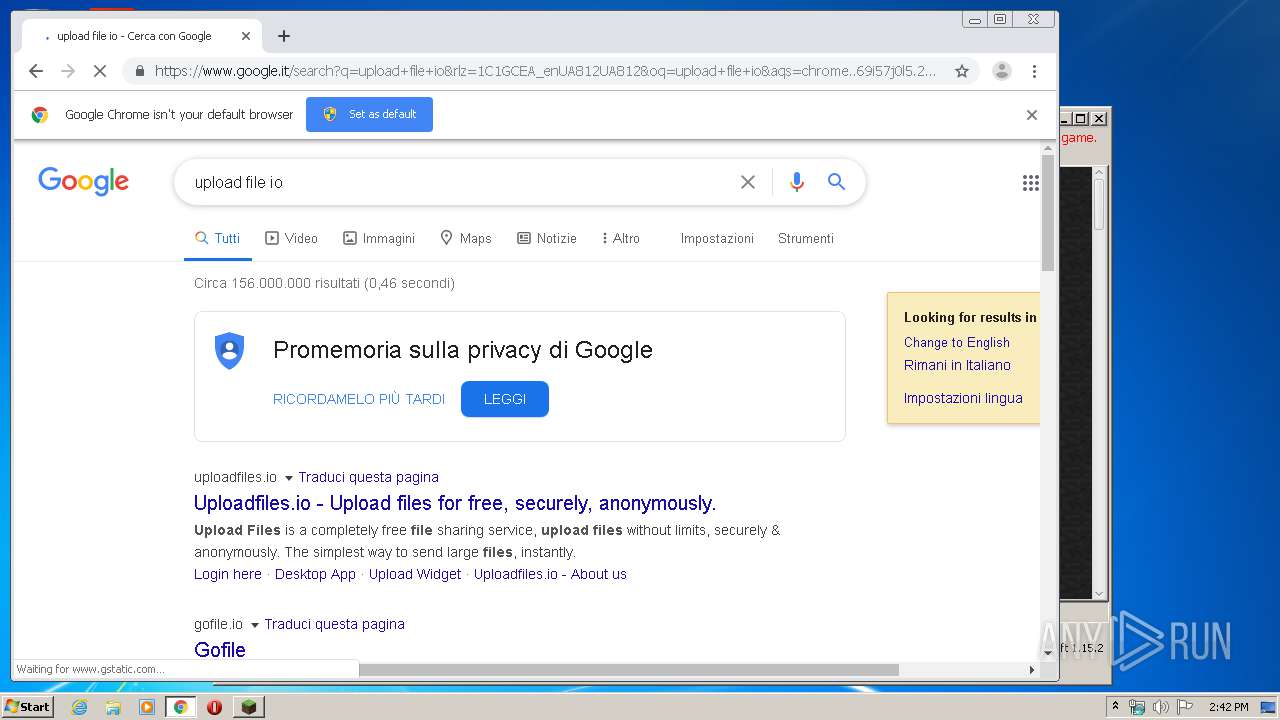
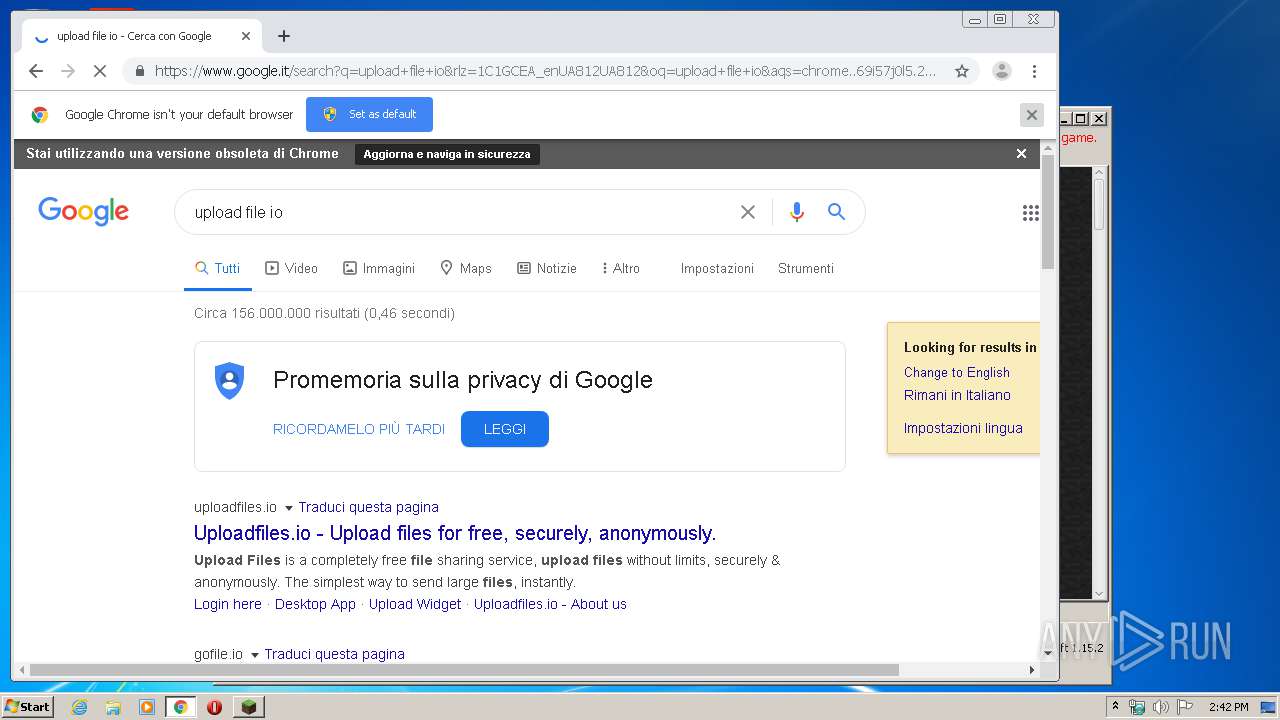
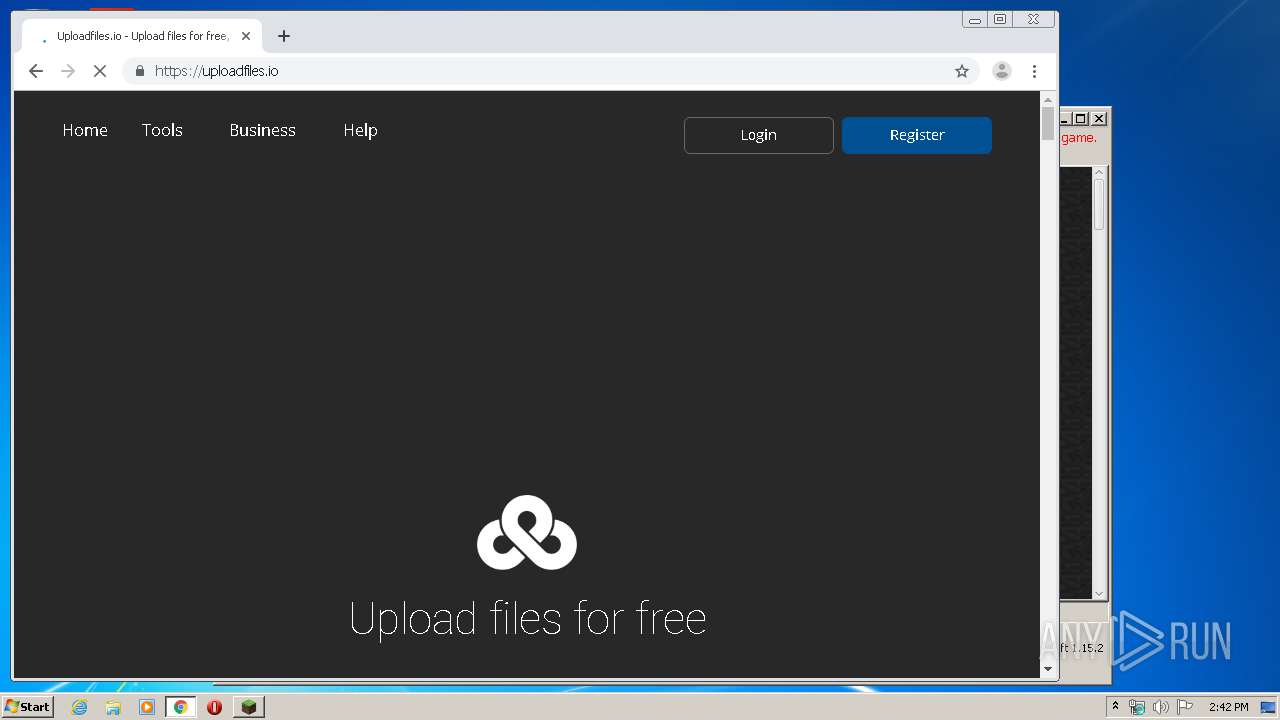
mineshafter.info |
| whitelisted |
s3.amazonaws.com |
| shared |
launchermeta.mojang.com |
| whitelisted |
mcupdate.tumblr.com |
| suspicious |
assets.tumblr.com |
| whitelisted |
66.media.tumblr.com |
| suspicious |
assets.mojang.com |
| shared |
px.srvcs.tumblr.com |
| whitelisted |
static.tumblr.com |
| whitelisted |
libraries.minecraft.net |
| shared |