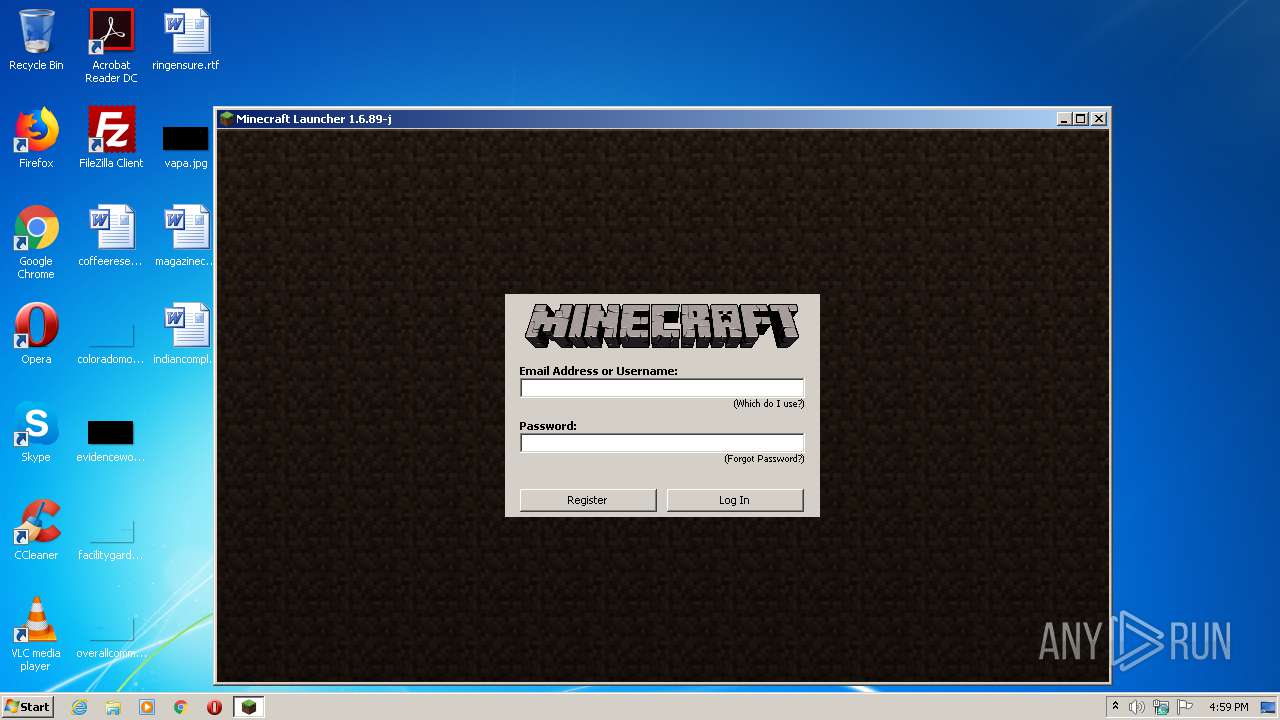
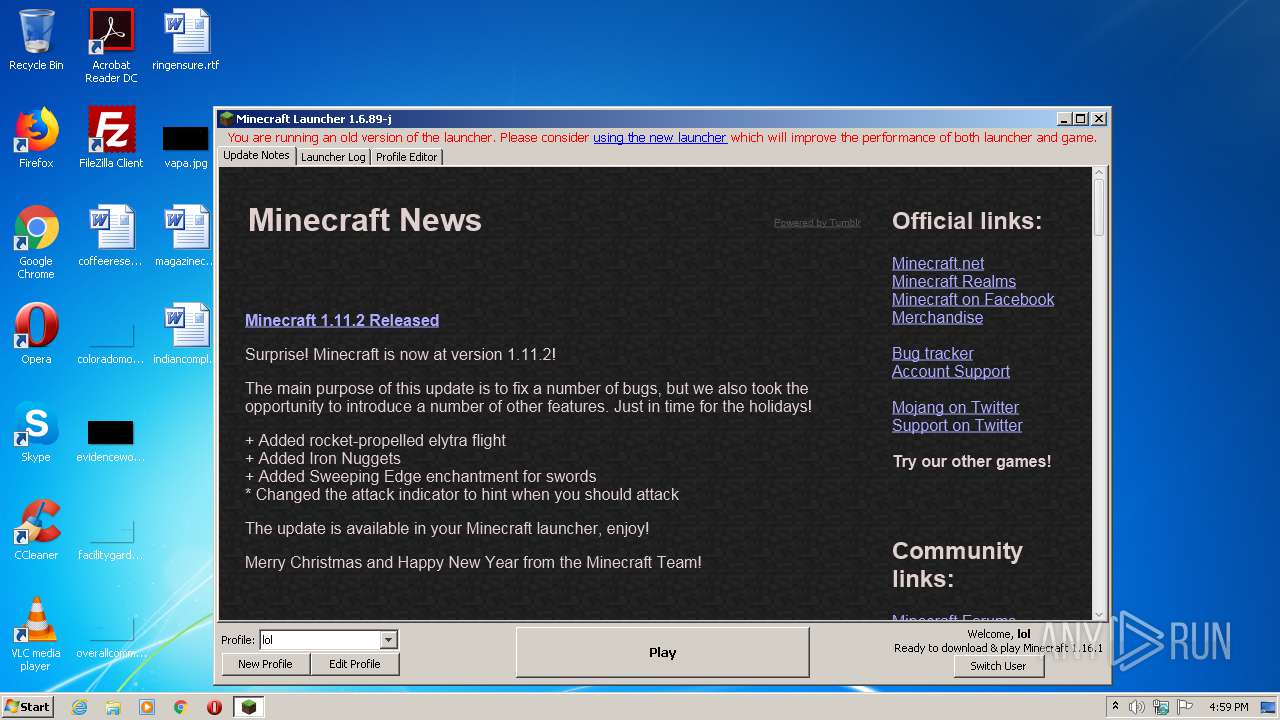
| File name: | Mineshafter-launcher.jar |
| Full analysis: | https://app.any.run/tasks/52095576-e84f-4c6c-8750-153e08c060b8 |
| Verdict: | Malicious activity |
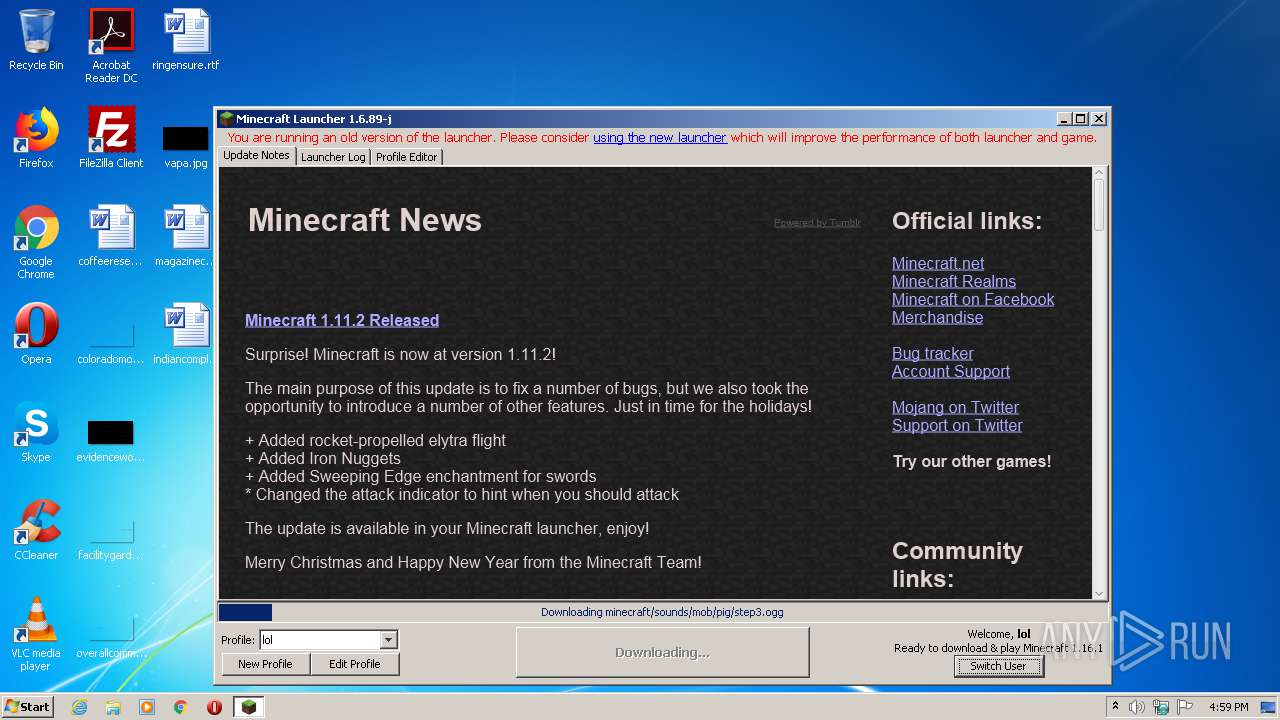
| Analysis date: | July 25, 2020, 15:59:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | F6CD55DE2534393363E1A40E04D71156 |
| SHA1: | 7A8D89DD5548D6BDF8DE77E198AD518300C560CF |
| SHA256: | C03140A4216BD64EE1BF7D5E7416973F1E3F9E60B0513ADA448893DD6952EAD6 |
| SSDEEP: | 3072:hDDxhlswtTmiVBmqt7yANM/+0QGLF0BVHt:JNBtTmCBm07tMpQ4F0/t |
MALICIOUS
No malicious indicators.SUSPICIOUS
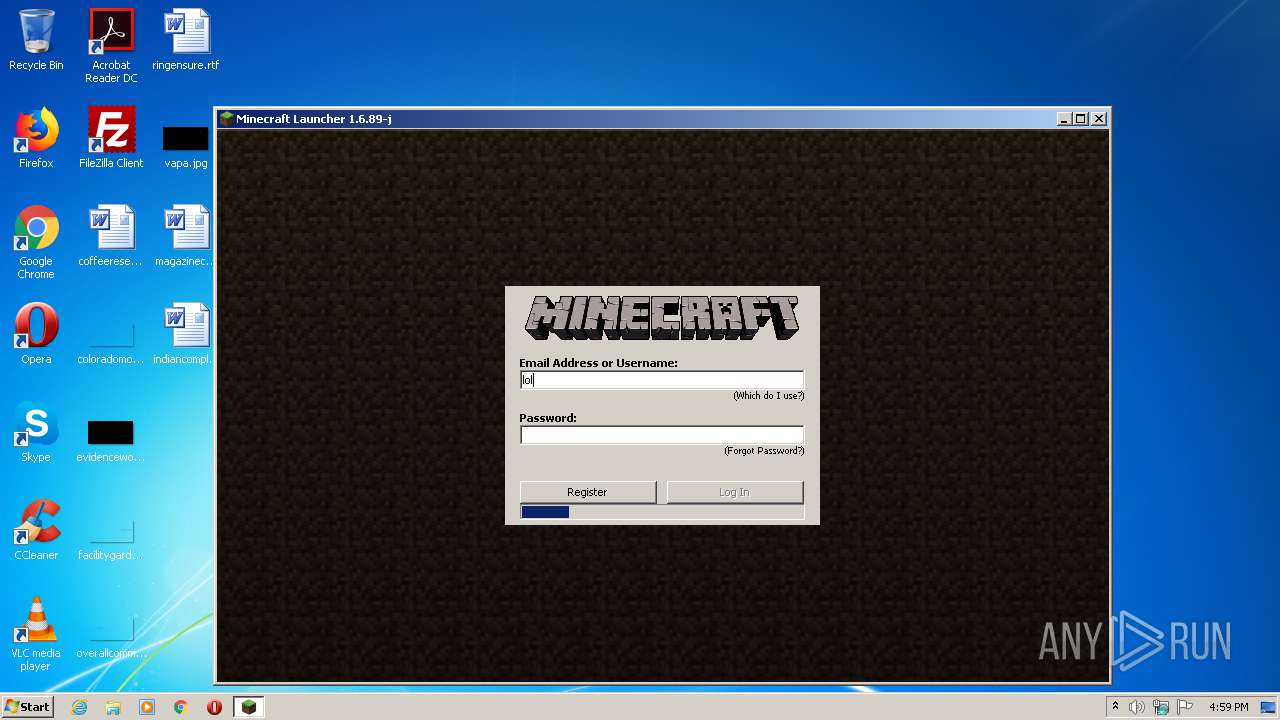
Creates files in the user directory
- javaw.exe (PID: 1736)
INFO
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 1736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:05 23:31:15 |
| ZipCRC: | 0xe40dfb26 |
| ZipCompressedSize: | 67 |
| ZipUncompressedSize: | 65 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
35
Monitored processes
1
Malicious processes
1
Suspicious processes
0
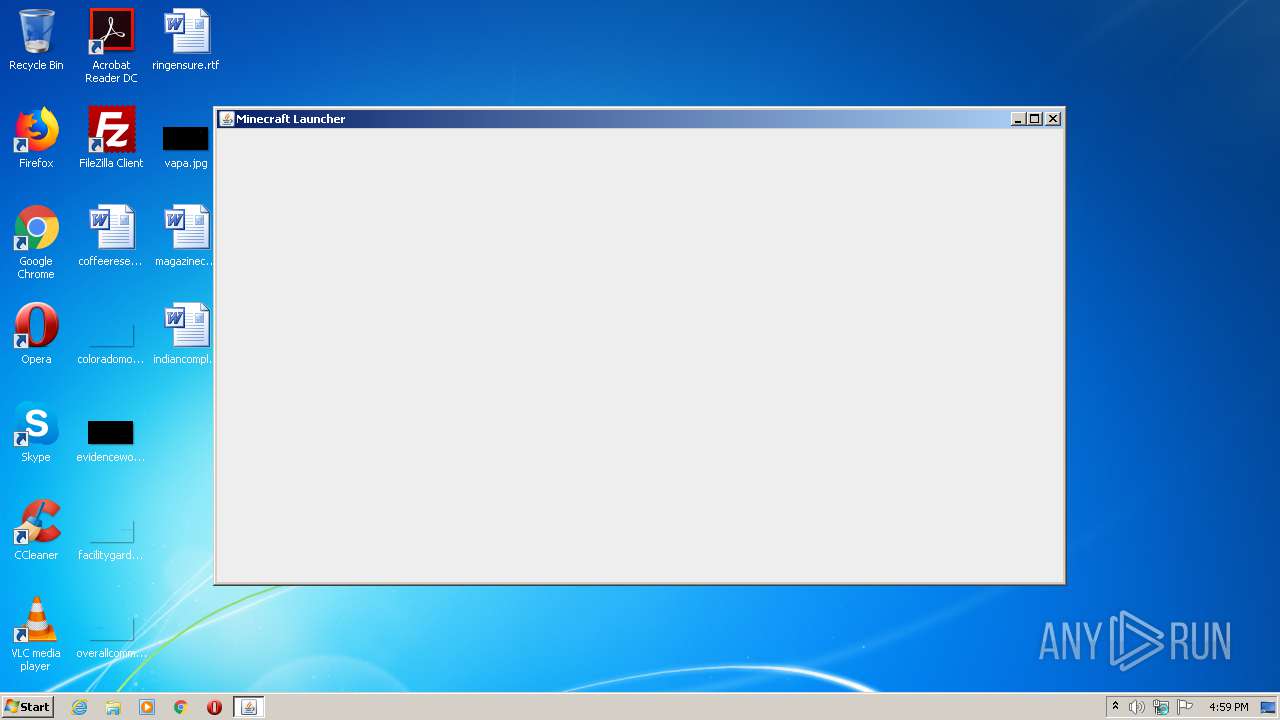
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
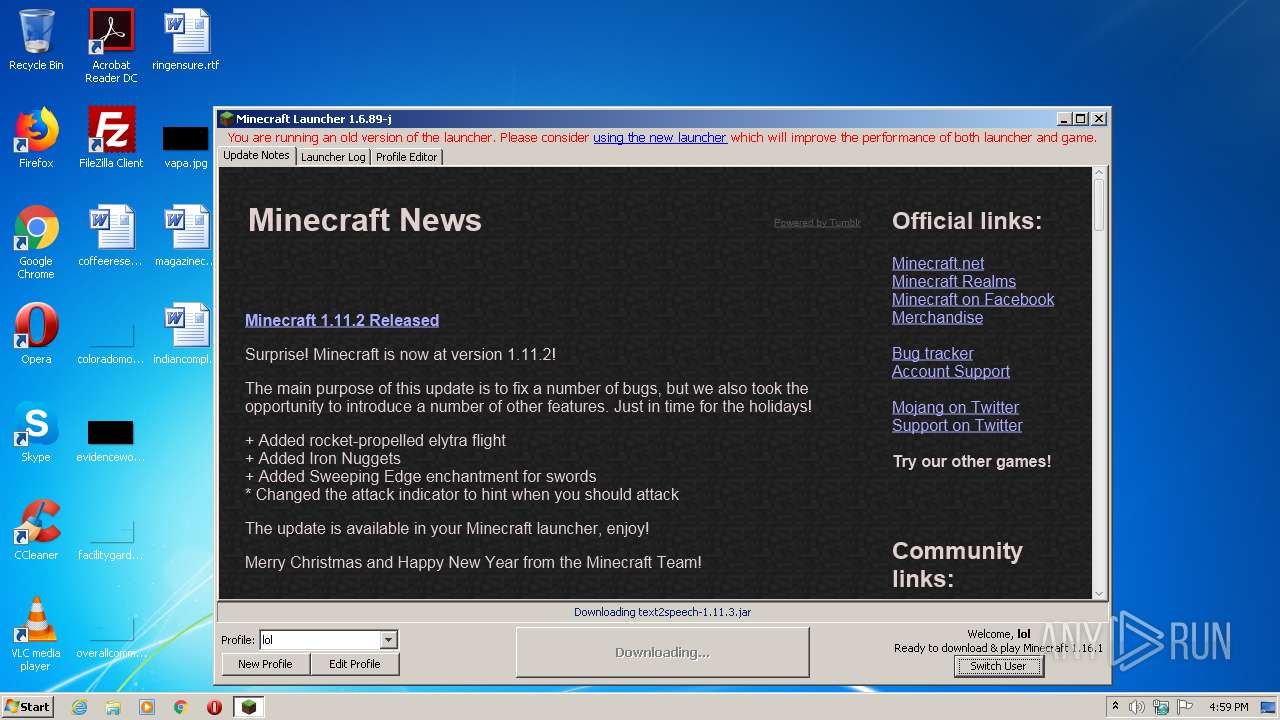
| 1736 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\Mineshafter-launcher.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
25
Read events
23
Write events
2
Delete events
0
Modification events
| (PID) Process: | (1736) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
21
Suspicious files
22
Text files
53
Unknown types
363
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1736 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher.pack.lzma.new | — | |
MD5:— | SHA256:— | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio876637392396950113.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio4841800007240949208.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3666733026011815292.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio1399386609105581584.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher.pack | binary | |
MD5:8F5851921290765F3FC77ED38C9331B3 | SHA256:BF3BD4017B0E6D28D93C3764CDC51C89BF0598DF7EFEA85917C85A4CBCF29D71 | |||
| 1736 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:ACD8E45577CA20928247AACB2B978511 | SHA256:06C6EF45CE65CB40B9B1FB19460E1355BDE84A899C2A56C1A7A740947CEE6848 | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_mcpatched.jar | compressed | |
MD5:CA7DEB1FB5A2E0EDABBC015469A52041 | SHA256:E821E2755707EB3A8532F2DA6D79133097E339158B7F22C20590CB5DCF48954D | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher.pack.lzma | lzma | |
MD5:D3F1E104ED5046CA5AA866D144484E79 | SHA256:CC22979FD70102C7975C2BD7DECE3A5F6B5AE3EC4FE1D39A80816C9D579542CF | |||
| 1736 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\assets\indexes\1.16.json | text | |
MD5:9D62FCCB7C424186D11A91CF12629C18 | SHA256:D3A8C98ACD8E9BE462401DA03241B3E92AAE2A83057176D1D397F04FB37CB0DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
471
TCP/UDP connections
44
DNS requests
11
Threats
0
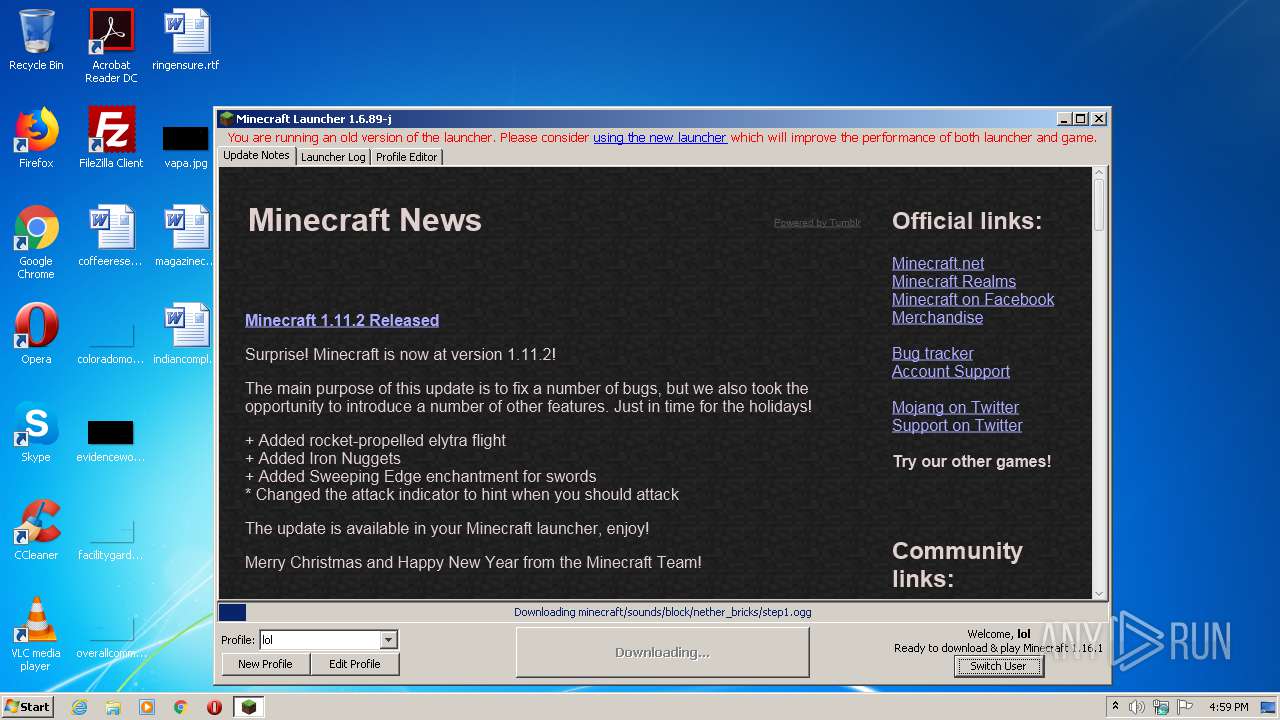
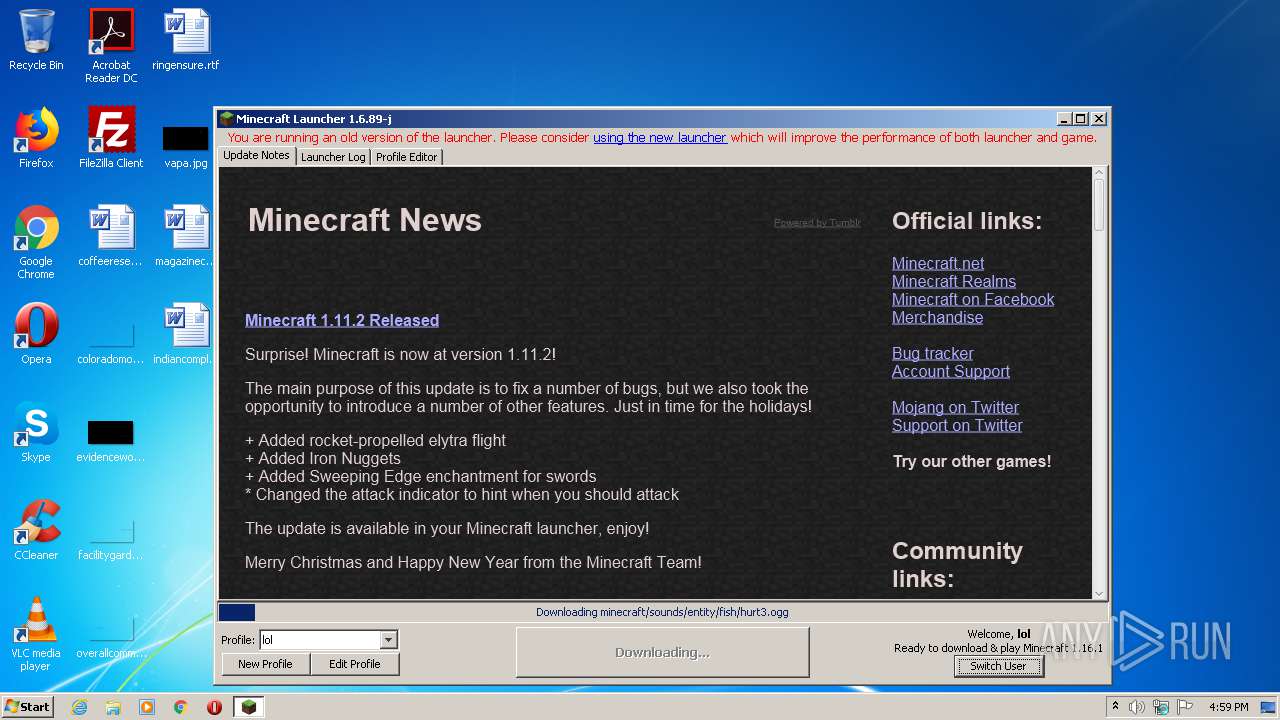
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/16/166af5d48f1f67a4608be9d23fd27f8c16269893 | US | ogg | 11.0 Kb | shared |
1736 | javaw.exe | GET | 302 | 74.114.154.18:80 | http://mcupdate.tumblr.com/ | CA | — | — | suspicious |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/4f/4f3a2c3edf64d8559d3ecd79b0cd14d54ec3d51f | US | ogg | 10.5 Kb | shared |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/da/daa06994b2e42f2264fe061e82eb6c1d5ed8b696 | US | ogg | 34.2 Kb | shared |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/c2/c27a5dfd1f85834d0238273dfc7227b85776afc8 | US | ogg | 23.8 Kb | shared |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/2e/2e5cbdda4af66e8a435c22f822c6b755c2bcc183 | US | ogg | 28.2 Kb | shared |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/c6/c649e60ea9a99c97501a50d2dc4e579343e91ea8 | US | ogg | 16.6 Kb | shared |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/96/9673ae2933b66eada687763cb7f57fa768f30078 | US | ogg | 21.8 Kb | shared |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/ce/ceaaaa1d57dfdfbb0bd4da5ea39628b42897a687 | US | ogg | 1.67 Mb | shared |
1736 | javaw.exe | GET | 200 | 143.204.201.56:80 | http://resources.download.minecraft.net/4d/4da9f12f979eba012c6f62e0820ca58cc49d8834 | US | ogg | 5.85 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1736 | javaw.exe | 185.142.236.247:443 | mineshafter.info | Cogent Communications | NL | unknown |
1736 | javaw.exe | 74.114.154.18:80 | mcupdate.tumblr.com | Automattic, Inc | CA | malicious |
1736 | javaw.exe | 99.86.2.139:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
1736 | javaw.exe | 74.114.154.18:443 | mcupdate.tumblr.com | Automattic, Inc | CA | malicious |
1736 | javaw.exe | 192.0.77.40:443 | assets.tumblr.com | Automattic, Inc | US | suspicious |
1736 | javaw.exe | 192.0.77.3:443 | 64.media.tumblr.com | Automattic, Inc | US | suspicious |
1736 | javaw.exe | 152.199.21.147:443 | px.srvcs.tumblr.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
1736 | javaw.exe | 52.216.17.251:443 | s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
1736 | javaw.exe | 99.86.4.83:443 | libraries.minecraft.net | AT&T Services, Inc. | US | suspicious |
1736 | javaw.exe | 143.204.212.134:443 | launcher.mojang.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mineshafter.info |
| whitelisted |
s3.amazonaws.com |
| shared |
launchermeta.mojang.com |
| whitelisted |
mcupdate.tumblr.com |
| suspicious |
assets.tumblr.com |
| whitelisted |
64.media.tumblr.com |
| suspicious |
px.srvcs.tumblr.com |
| whitelisted |
static.tumblr.com |
| whitelisted |
libraries.minecraft.net |
| shared |
launcher.mojang.com |
| whitelisted |