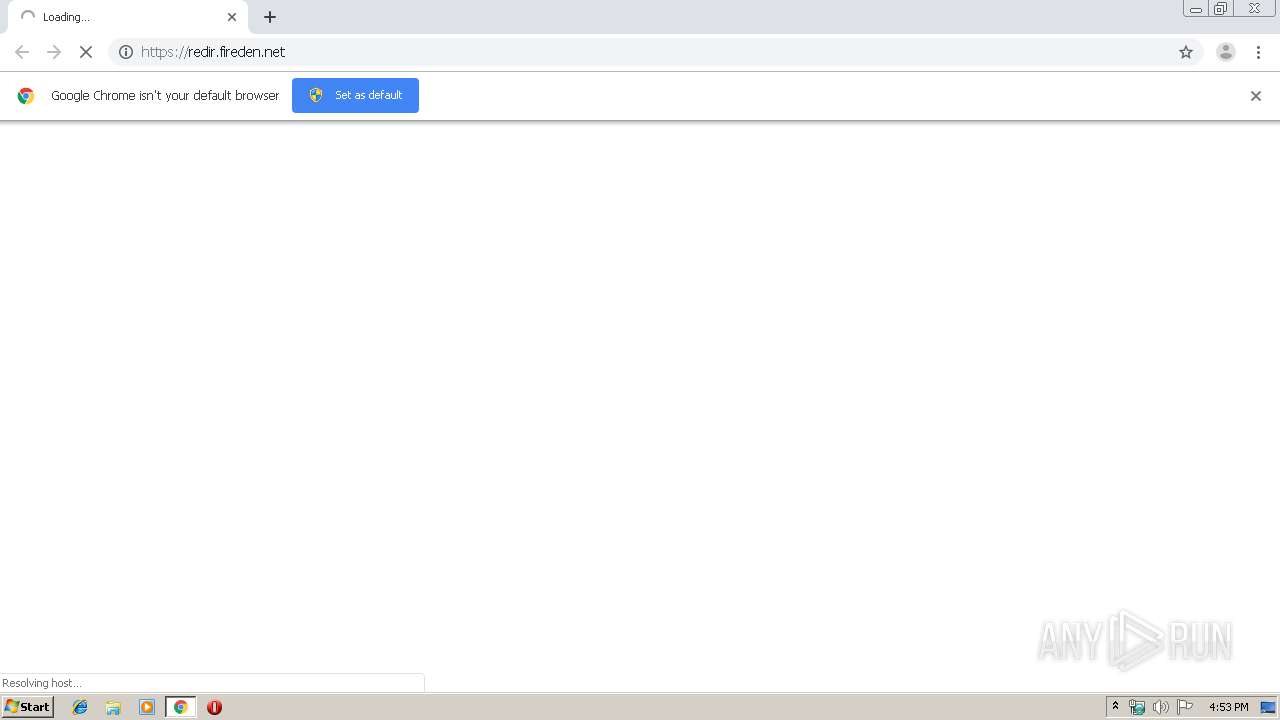
| URL: | https://redir.fireden.net |
| Full analysis: | https://app.any.run/tasks/f72a0b3c-c6c7-4bfc-b4a8-994ca6394316 |
| Verdict: | Malicious activity |
| Analysis date: | October 02, 2019, 15:52:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 44D87EEF6240CA97956F414E832EA9F7 |
| SHA1: | 09F84D73721B1D90157DB881C4F947120FC0E19C |
| SHA256: | C0263889536C9E718409267D642D1D04EE930699B68D4EEC313DA9DCAD4A2768 |
| SSDEEP: | 3:N8/n:2/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3480)
INFO
Application launched itself
- chrome.exe (PID: 3480)
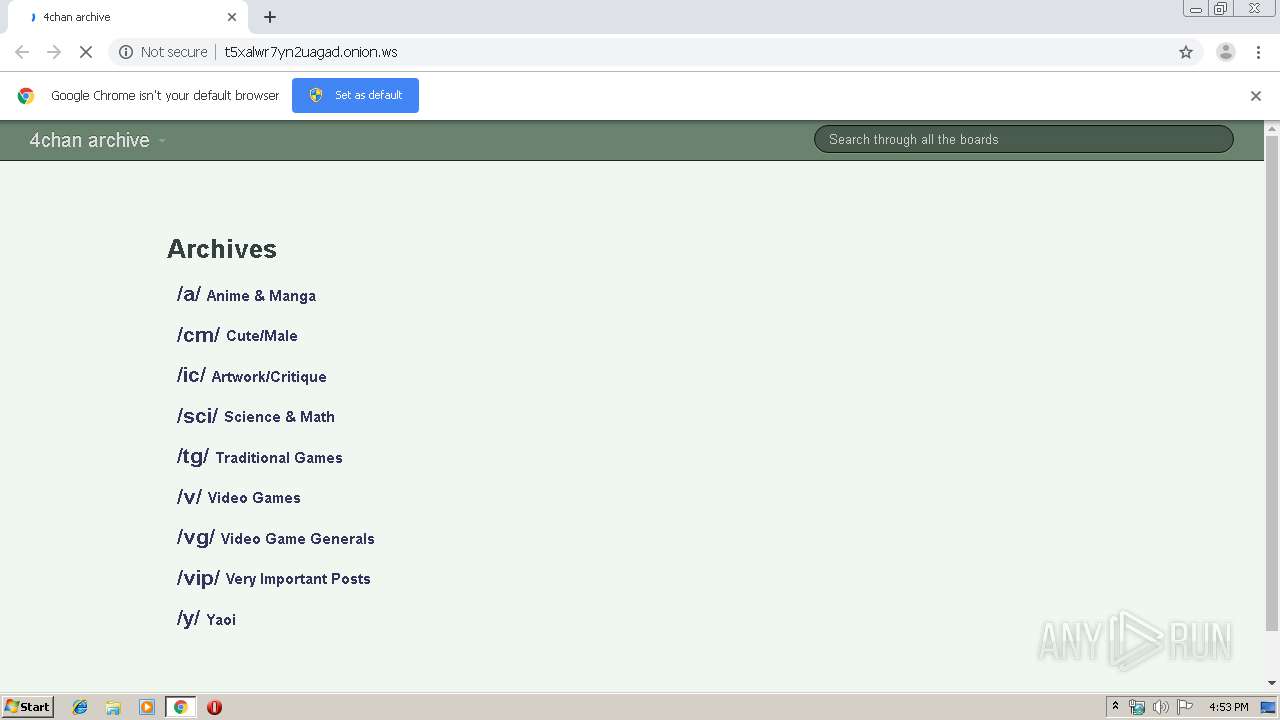
Dropped object may contain TOR URL's
- chrome.exe (PID: 3480)
Reads the hosts file
- chrome.exe (PID: 960)
- chrome.exe (PID: 3480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
22
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x705ba9d0,0x705ba9e0,0x705ba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1763603801080026408 --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12085205722543762678 --mojo-platform-channel-handle=3488 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4874121289059666383 --mojo-platform-channel-handle=3712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14725852492511358209 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12809791077955919883 --mojo-platform-channel-handle=3140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13076980304321591594 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11750222483185468549 --mojo-platform-channel-handle=944 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3890162648707900029 --mojo-platform-channel-handle=1884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14324489660057733236,1502356971391036441,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10971038359154815180 --mojo-platform-channel-handle=3548 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
591
Read events
519
Write events
68
Delete events
4
Modification events
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3480-13214505187842500 |
Value: 259 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3480-13214505187842500 |
Value: 259 | |||
Executable files
0
Suspicious files
57
Text files
138
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\79cee653-57a5-46c1-8e78-ca718c3e7758.tmp | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf44b1.TMP | text | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf44b1.TMP | text | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf44d0.TMP | text | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
32
DNS requests
26
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
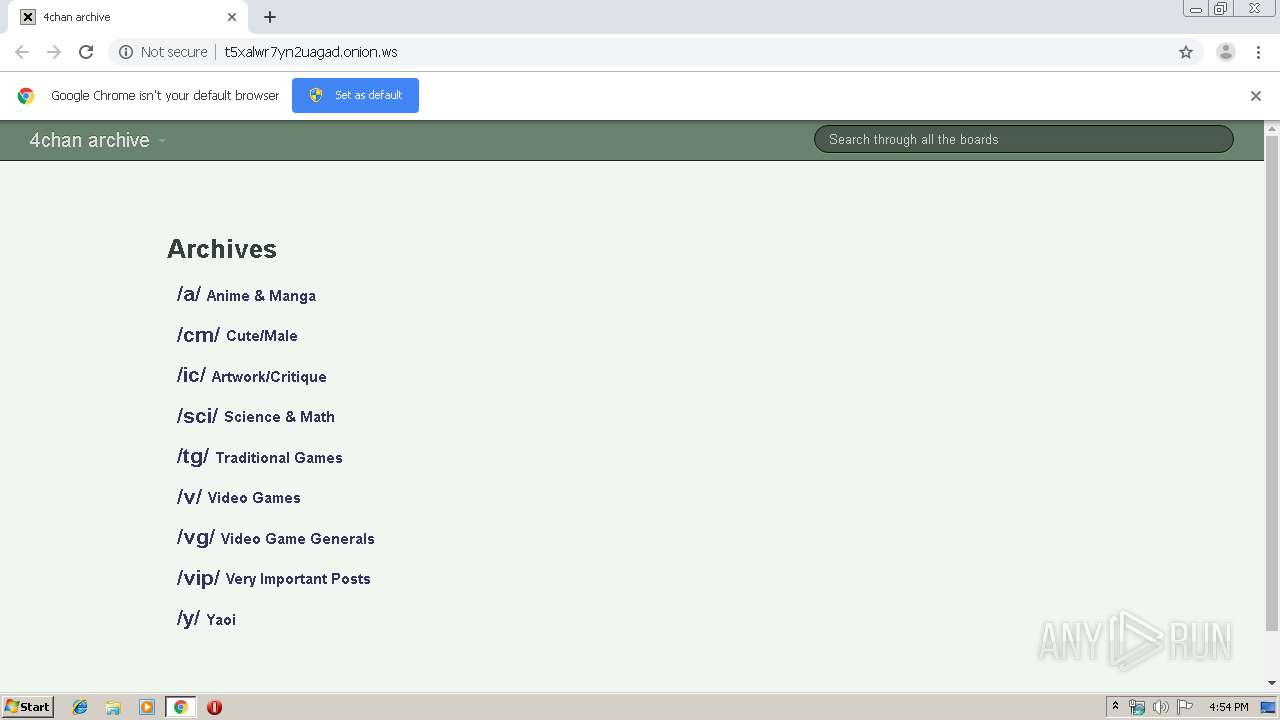
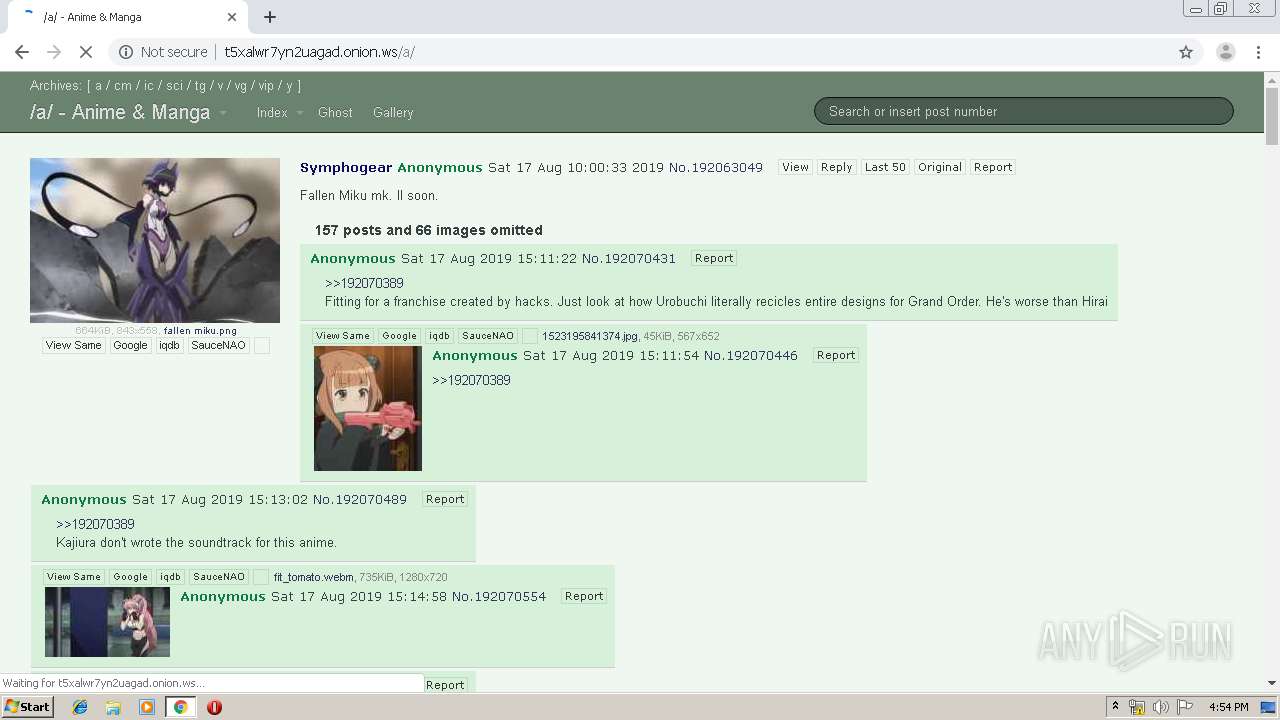
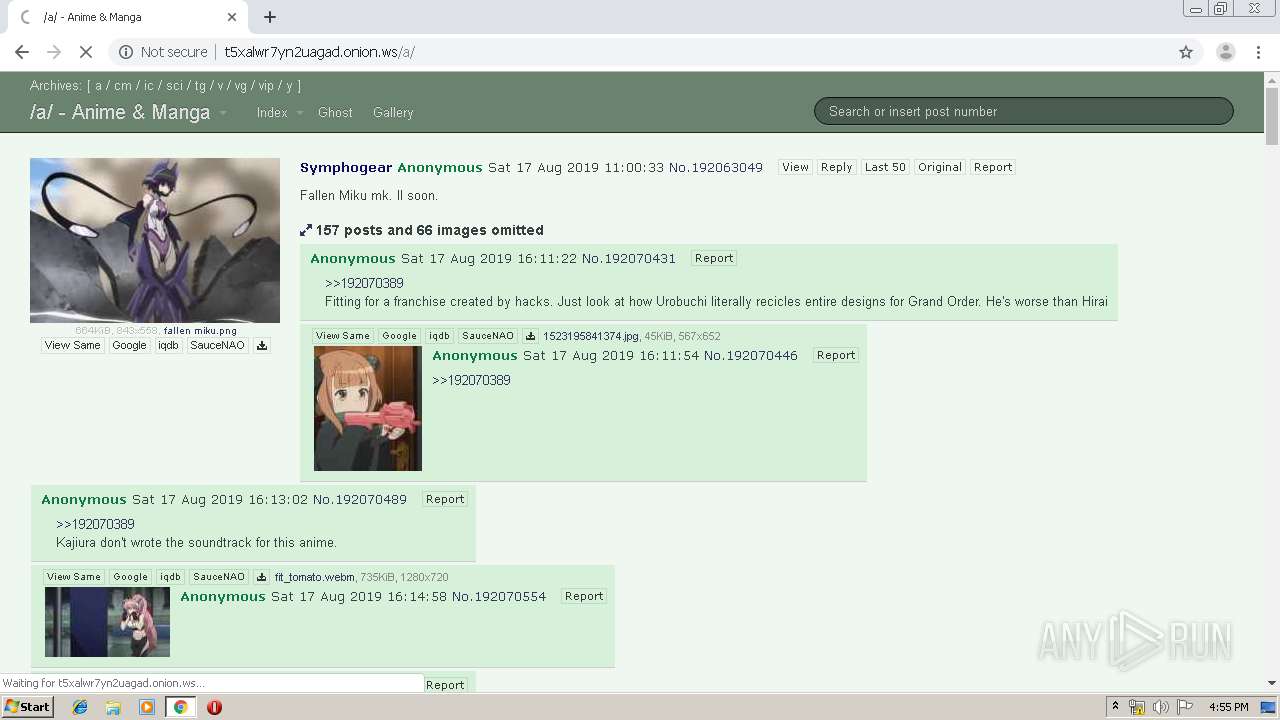
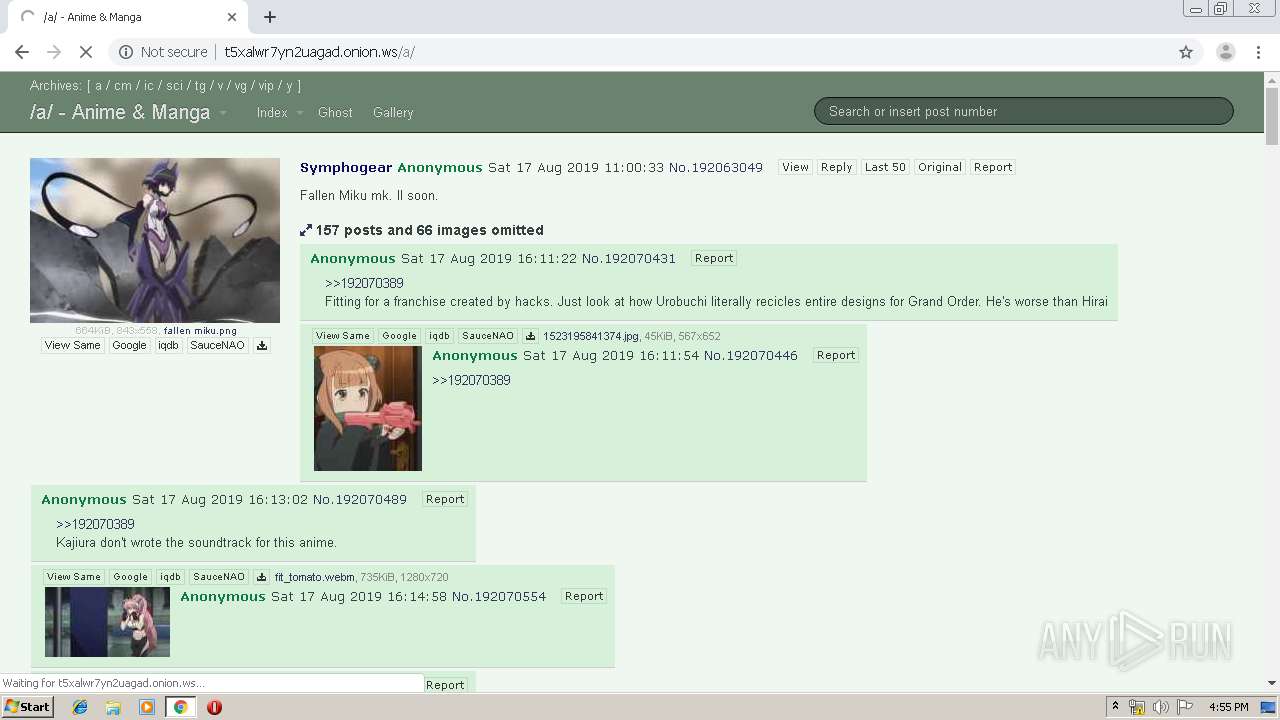
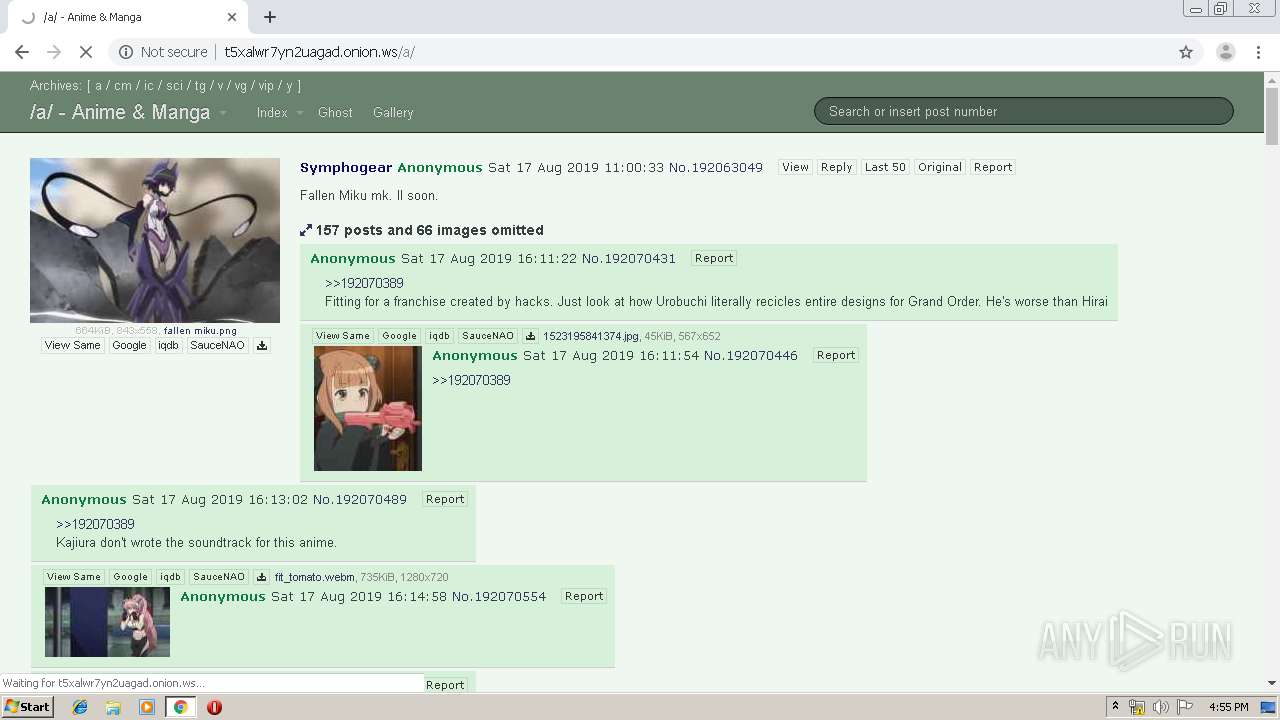
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/ | US | html | 4.90 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/foolz/foolfuuka-theme-foolfuuka/assets-1.1.1/style.css | US | text | 28.3 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/foolz/foolfuuka-theme-foolfuuka/assets-1.1.1/plugins.js | US | text | 36.0 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/foolz/foolfuuka-theme-foolfuuka/assets-1.1.1/flags.css | US | text | 13.4 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/mathjax/mathjax/config/default.js?rev=2.5.1 | US | html | 40.8 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/foolz/foolfuuka-theme-foolfuuka/assets-1.1.1/board.js | US | text | 33.4 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/components/highlightjs/highlight.pack.js | US | kap | 283 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/mathjax/mathjax/jax/output/HTML-CSS/config.js?rev=2.5.1 | US | text | 3.49 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/mathjax/mathjax/extensions/tex2jax.js?rev=2.5.1 | US | text | 6.84 Kb | malicious |
960 | chrome.exe | GET | 200 | 198.251.80.46:80 | http://t5xalwr7yn2uagad.onion.ws/foolfuuka/foolz/foolfuuka-theme-foolfuuka/assets-1.1.1/bootstrap.legacy.css | US | text | 115 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
960 | chrome.exe | 172.217.169.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 104.27.166.102:443 | redir.fireden.net | Cloudflare Inc | US | shared |
960 | chrome.exe | 198.251.80.46:80 | t5xalwr7yn2uagad.onion.ws | FranTech Solutions | US | malicious |
960 | chrome.exe | 216.58.206.173:443 | accounts.google.com | Google Inc. | US | unknown |
960 | chrome.exe | 172.217.169.202:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 216.58.212.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 216.58.206.164:443 | www.google.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 172.217.19.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 172.217.169.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 216.58.208.104:443 | www.googletagmanager.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
redir.fireden.net |
| whitelisted |
accounts.google.com |
| shared |
t5xalwr7yn2uagad.onion.ws |
| malicious |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
archive.foolz.us |
| malicious |
github.com |
| malicious |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy domain (onion .ws) |
960 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
960 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |