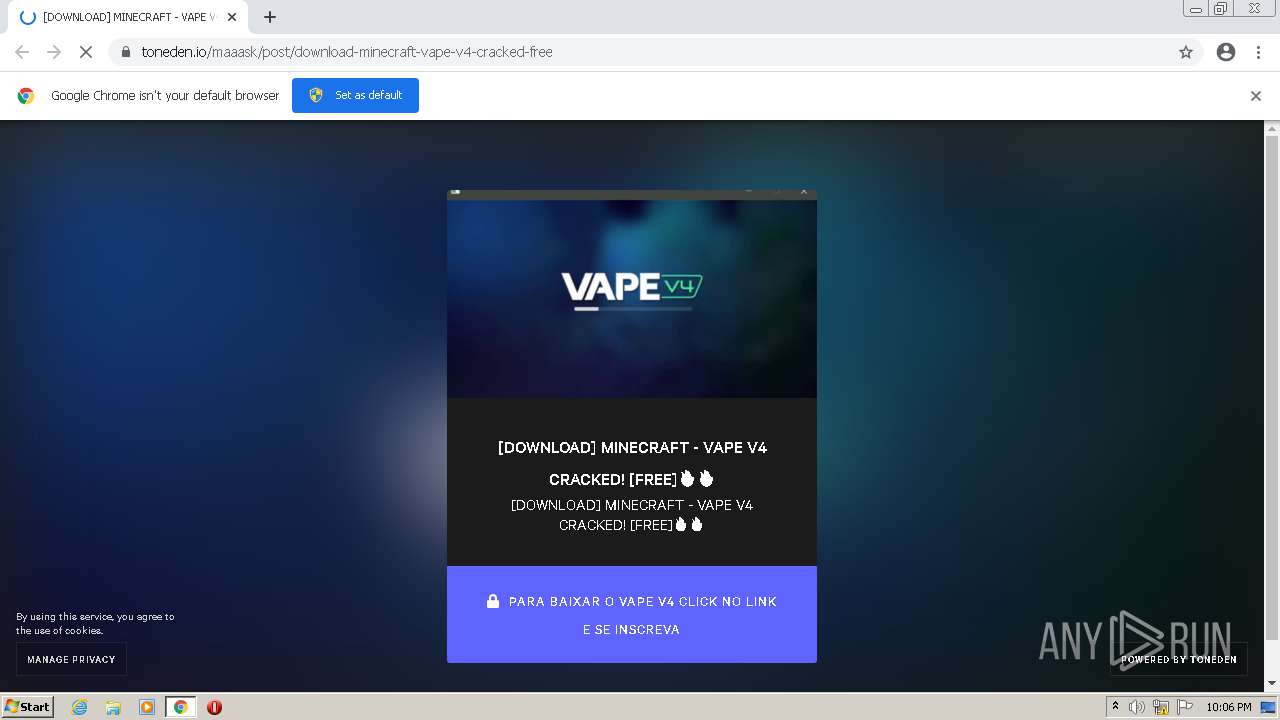
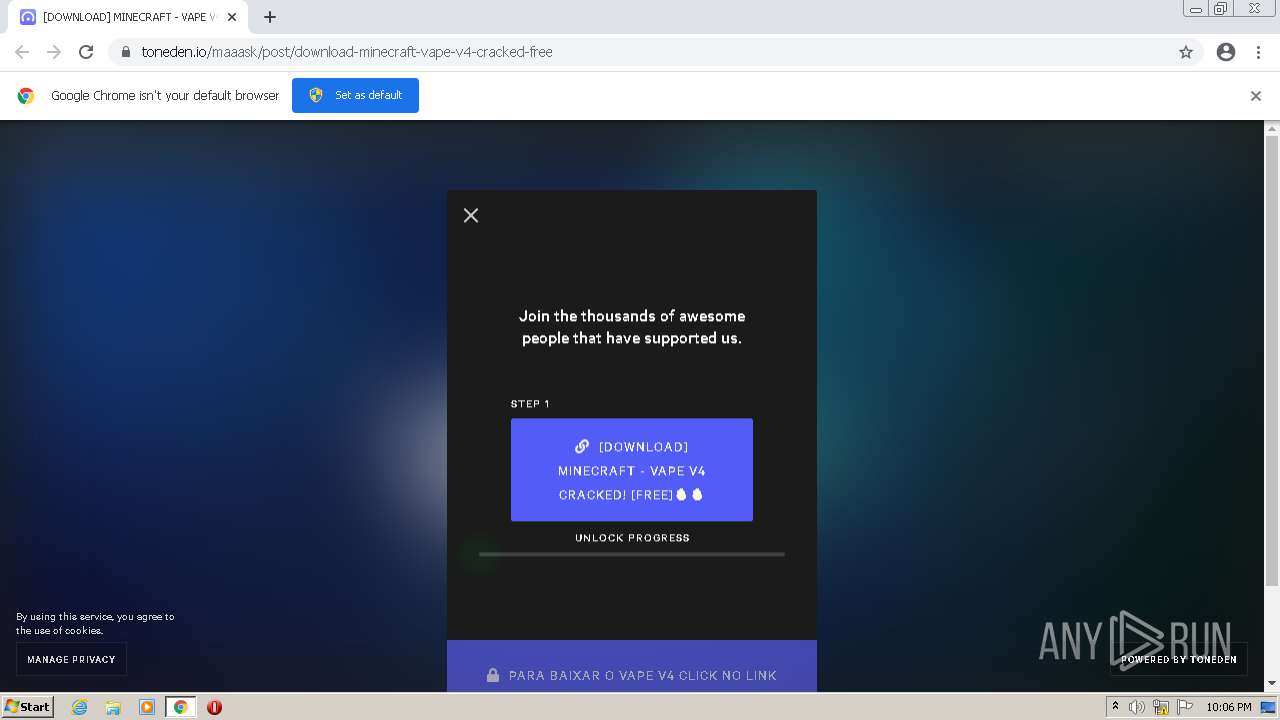
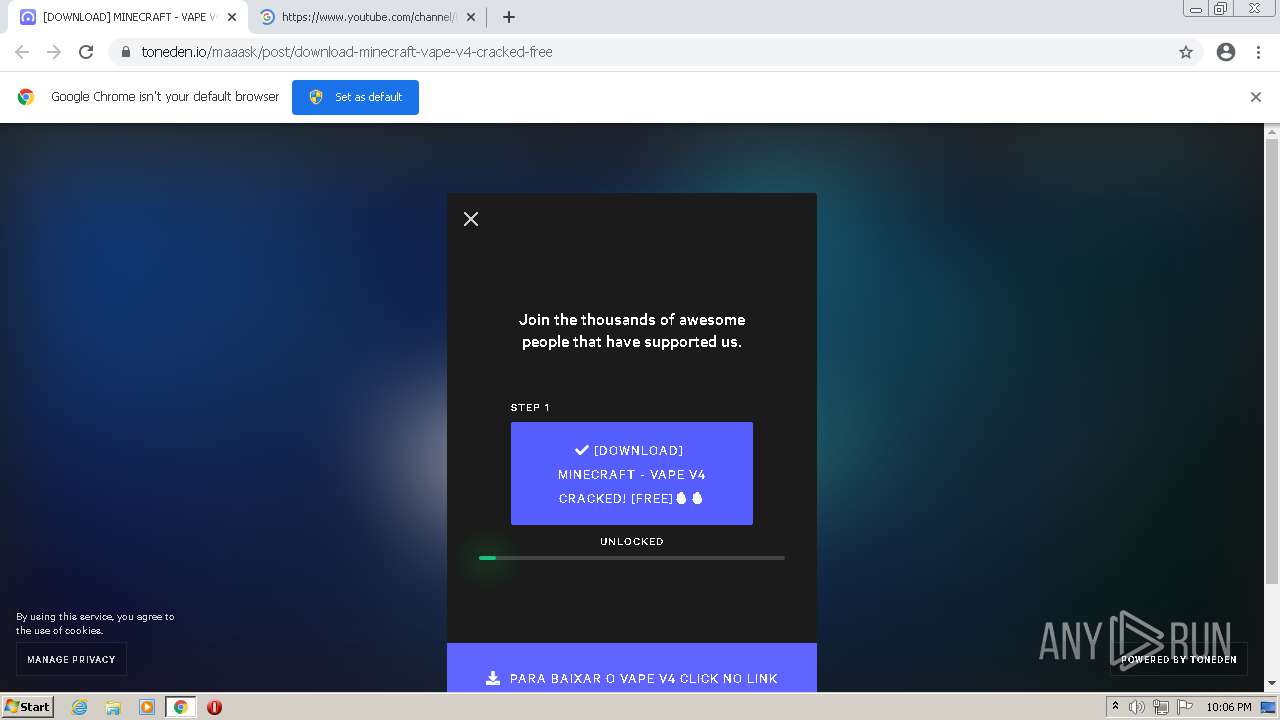
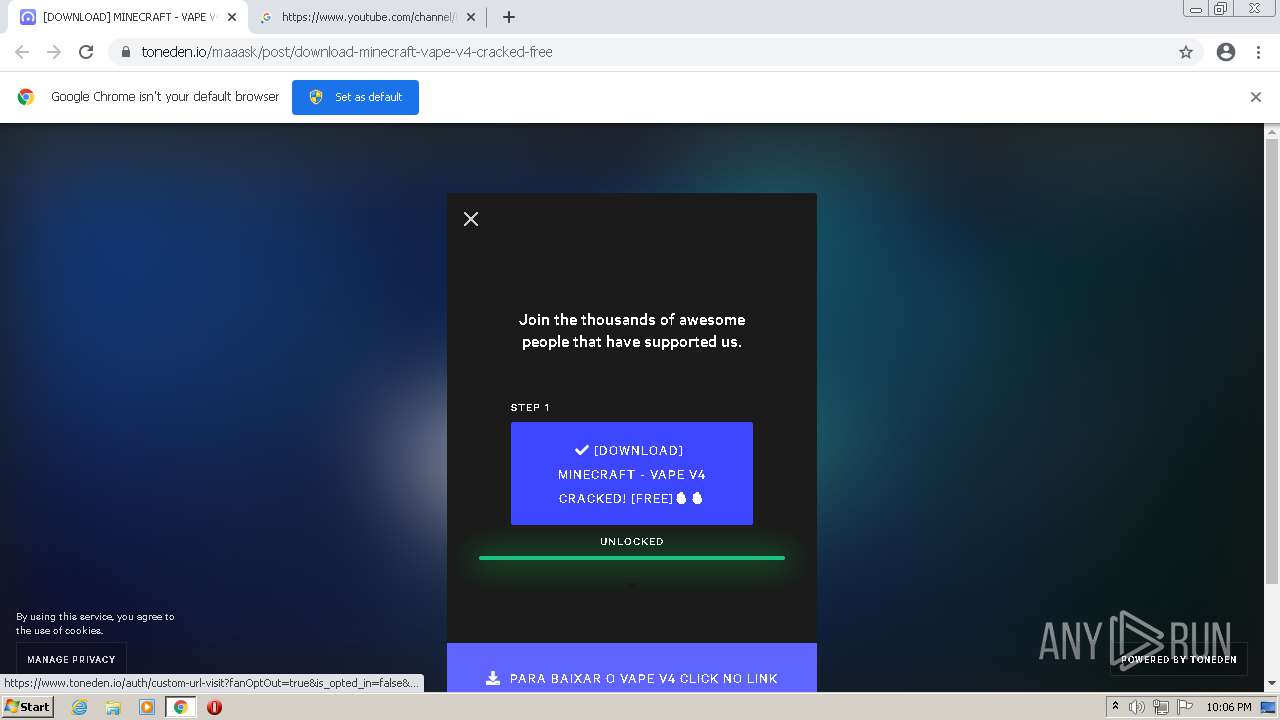
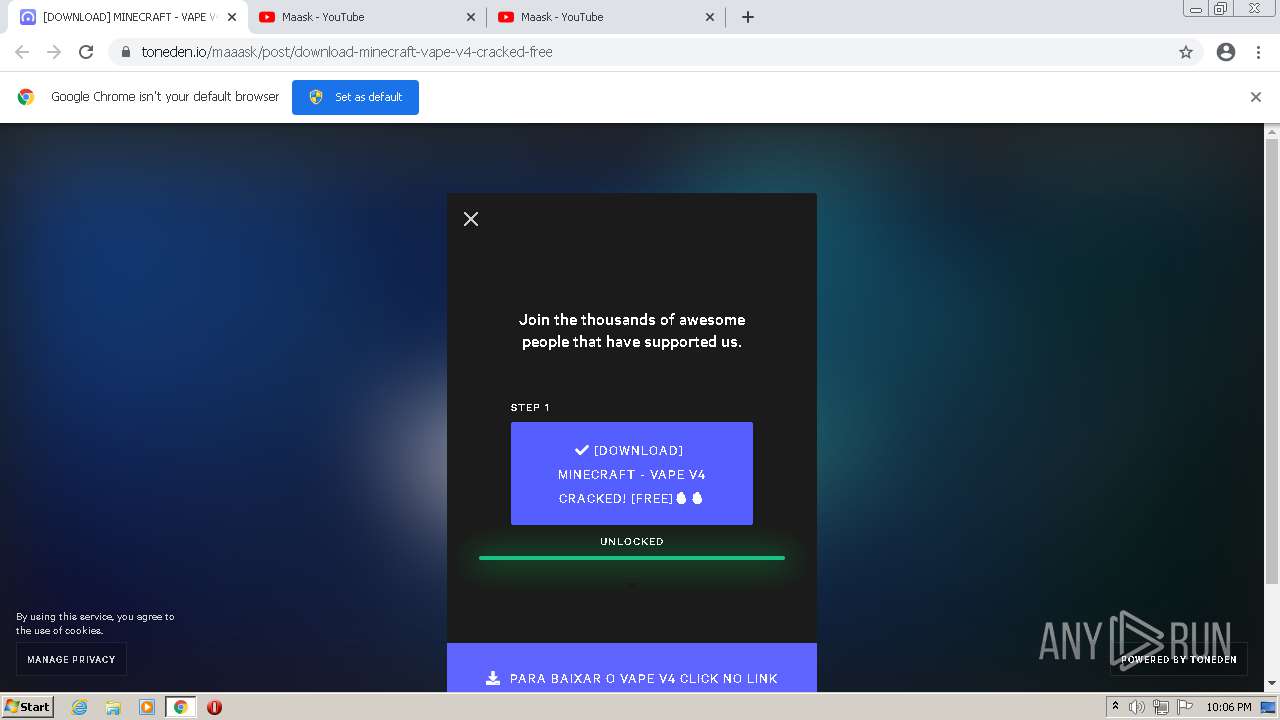
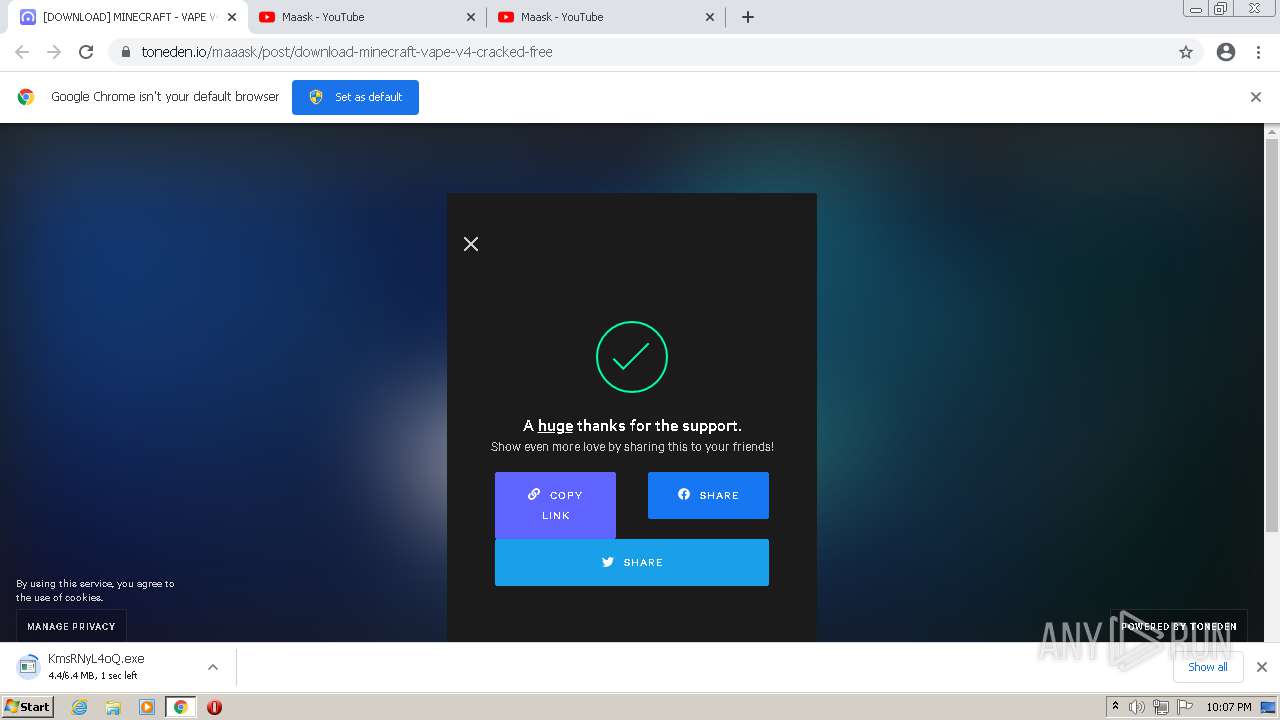
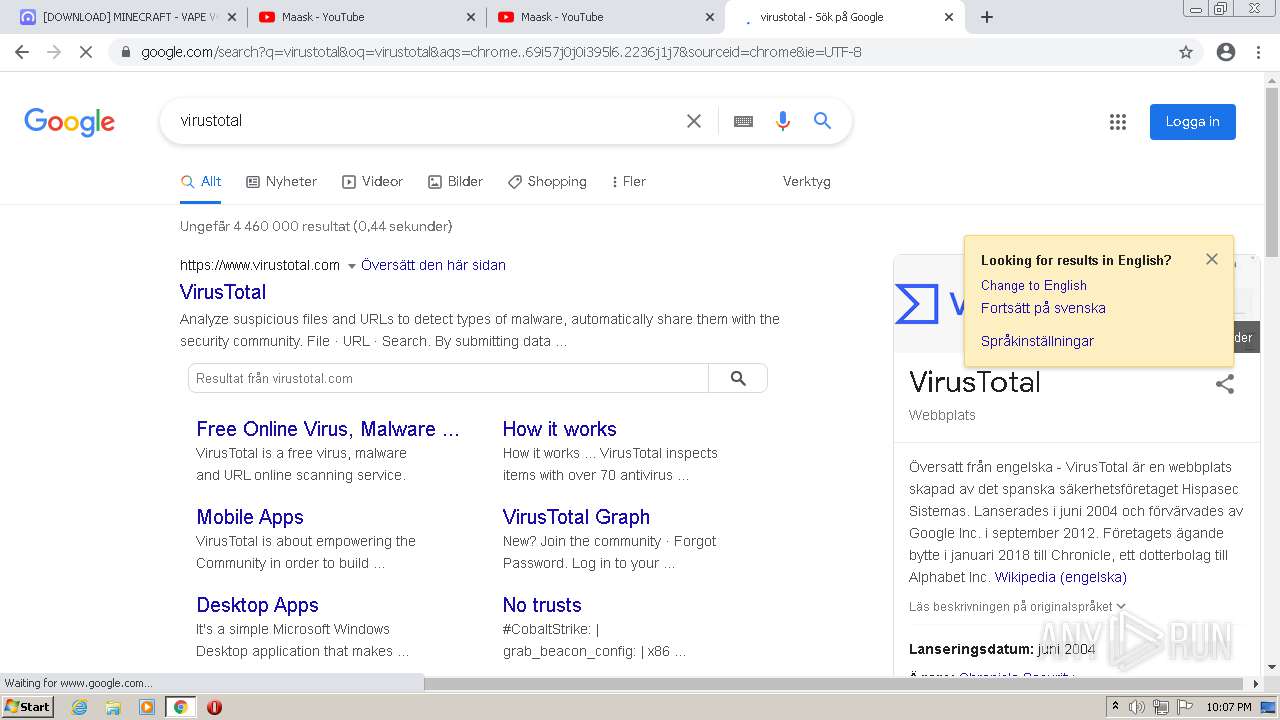
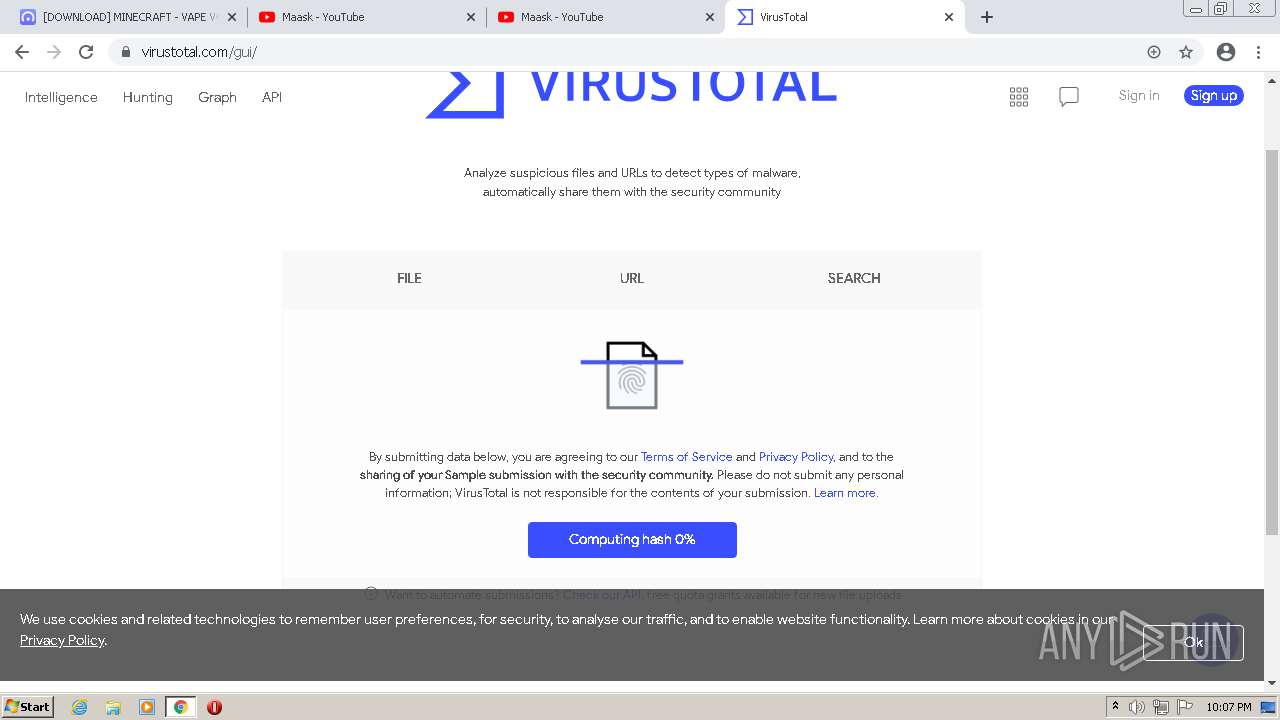
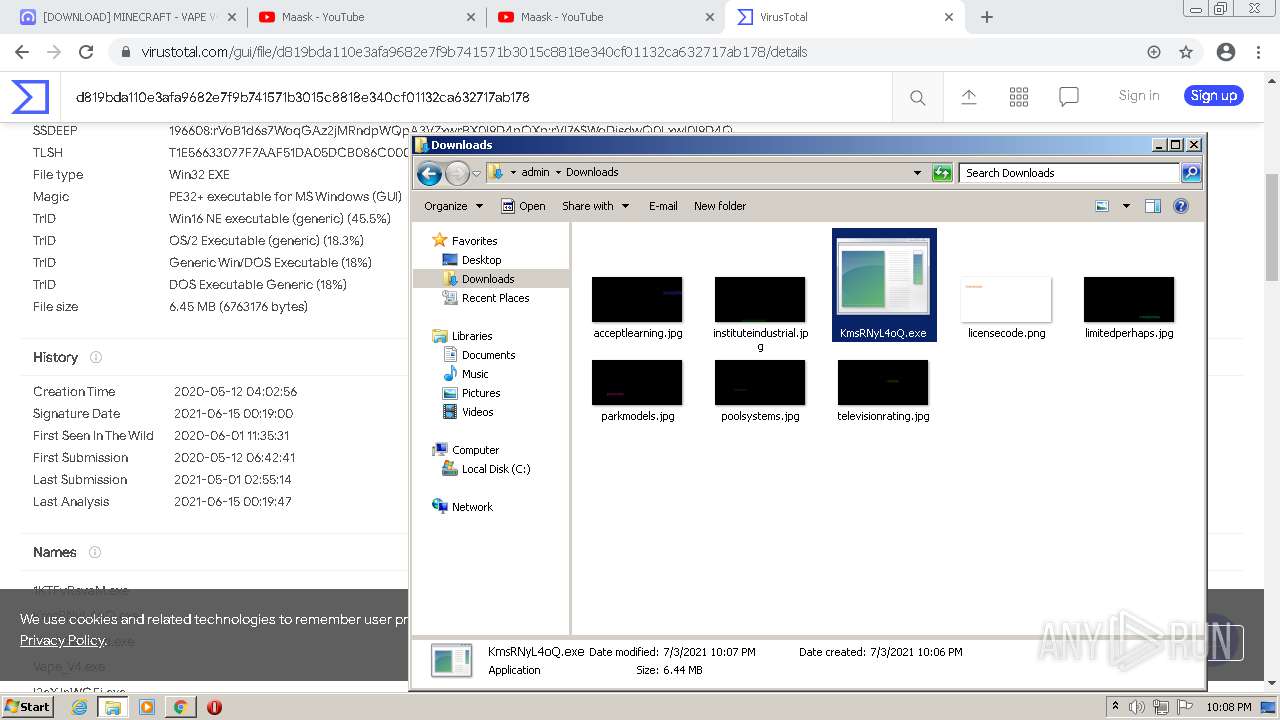
| URL: | https://www.toneden.io/maaask/post/download-minecraft-vape-v4-cracked-free |
| Full analysis: | https://app.any.run/tasks/6310a21a-37f9-4e9b-b743-dc527f914f1f |
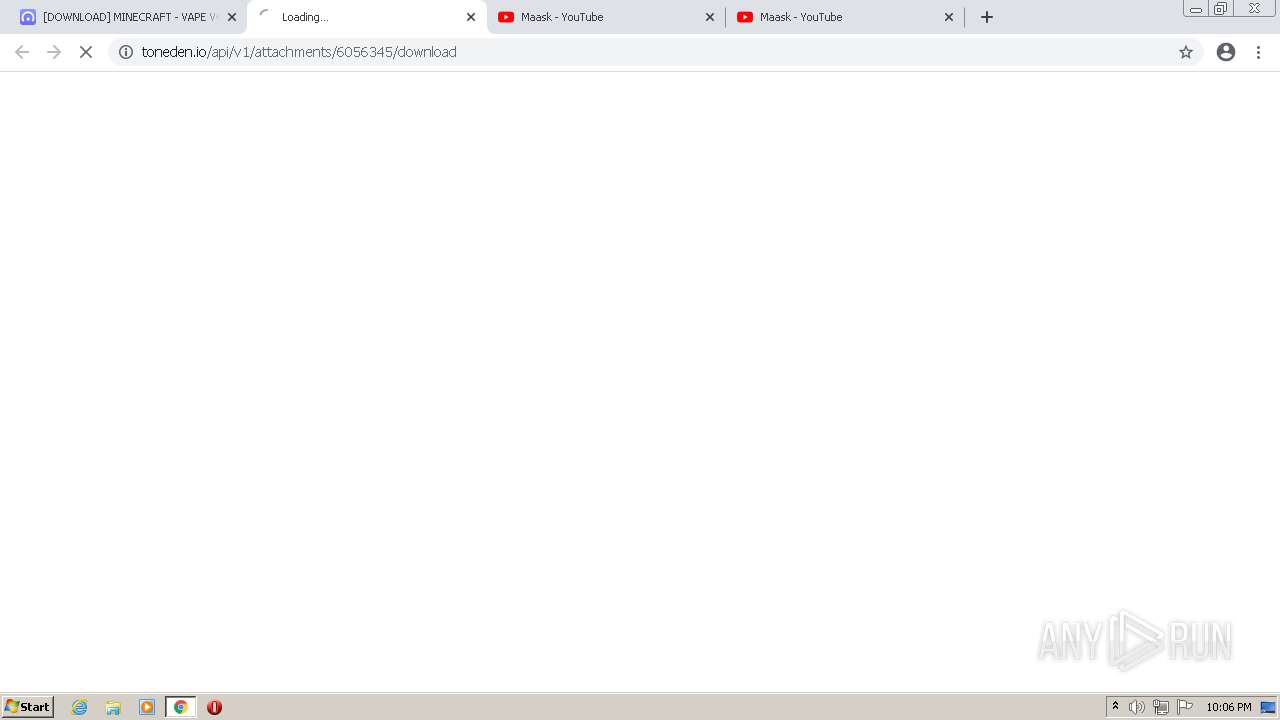
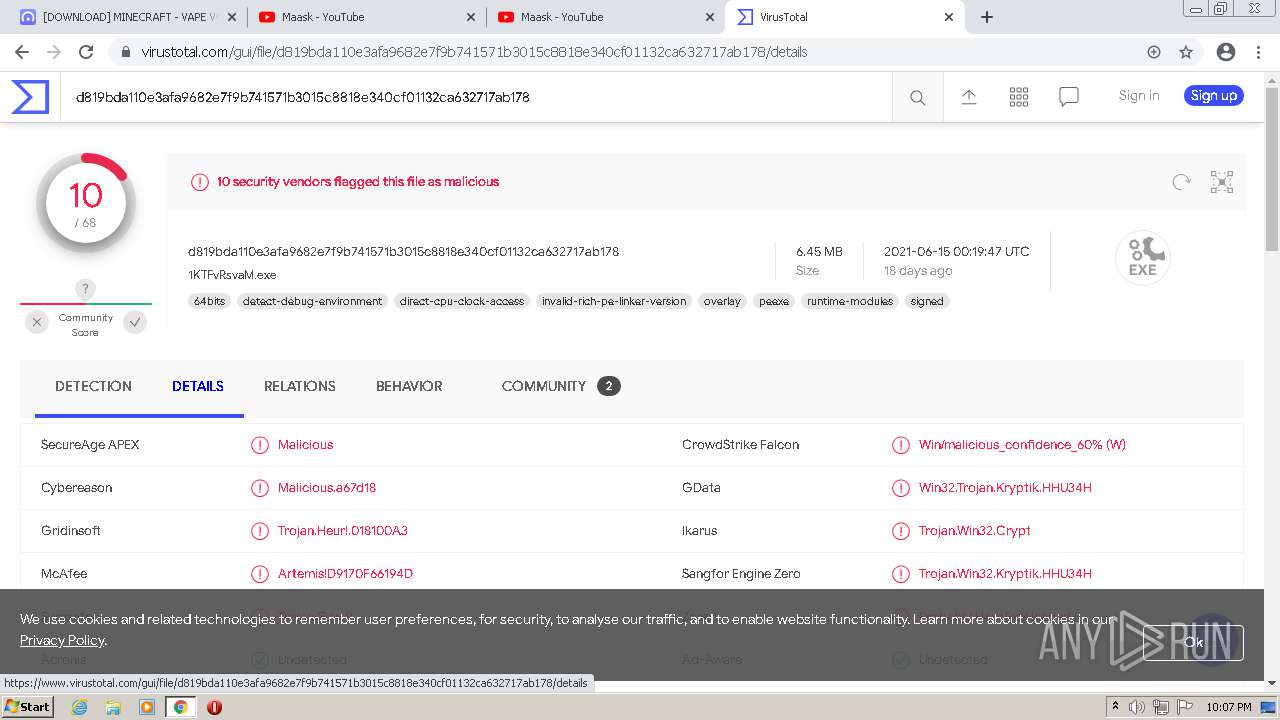
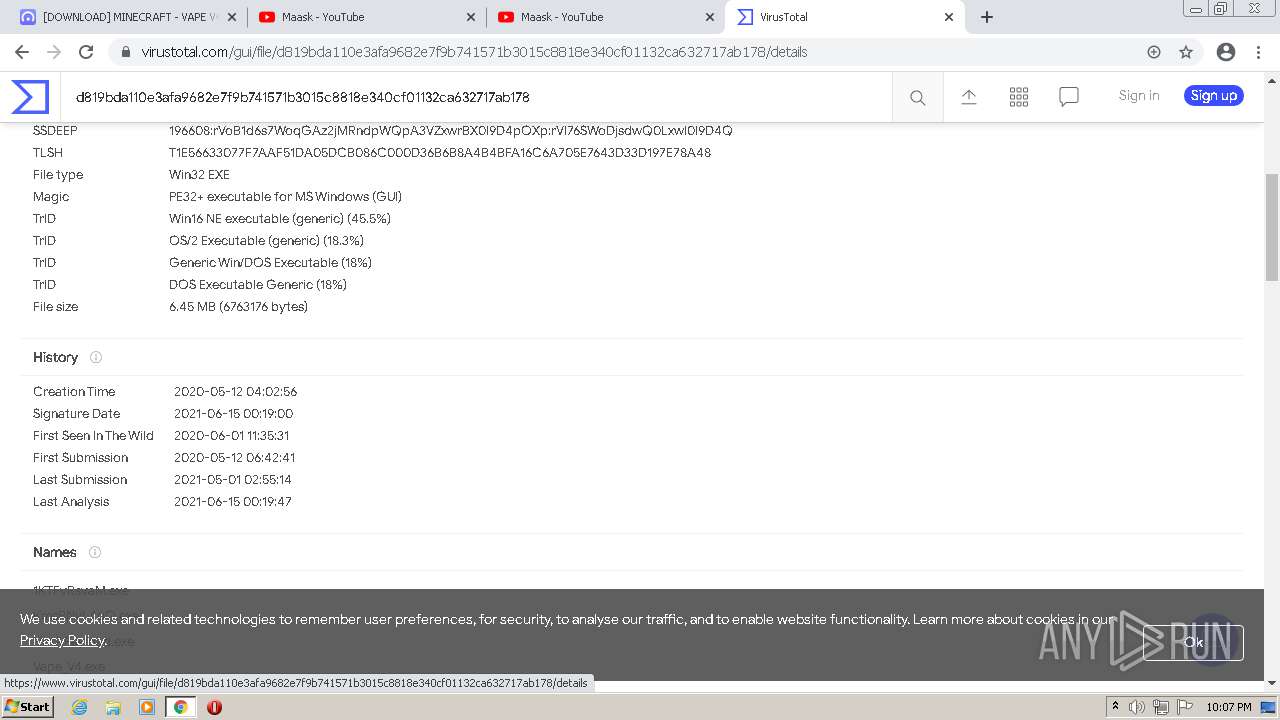
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2021, 21:06:13 |
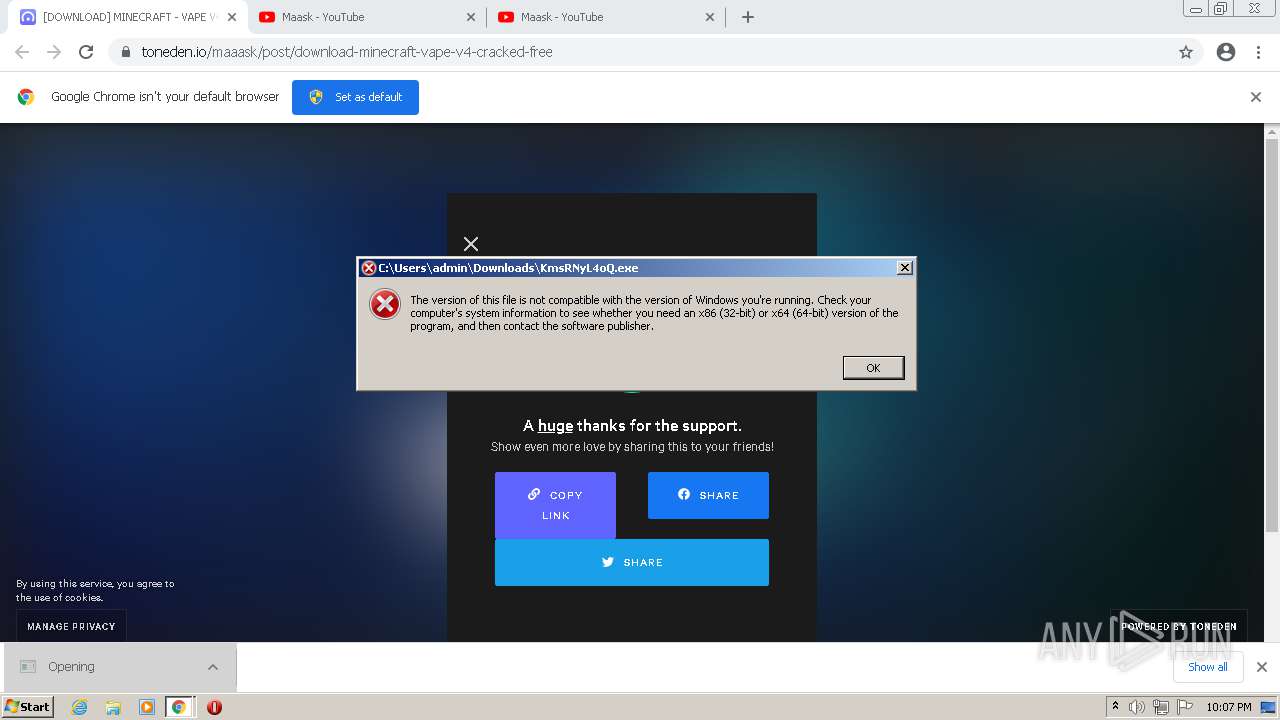
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
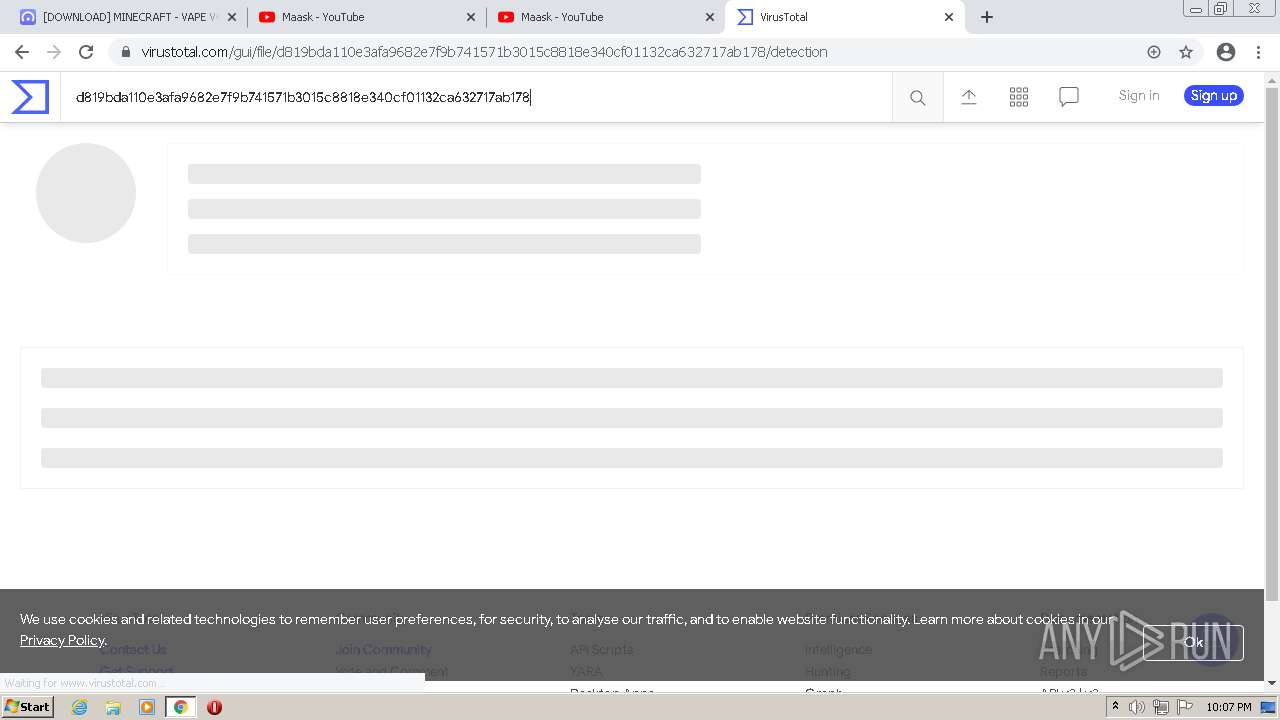
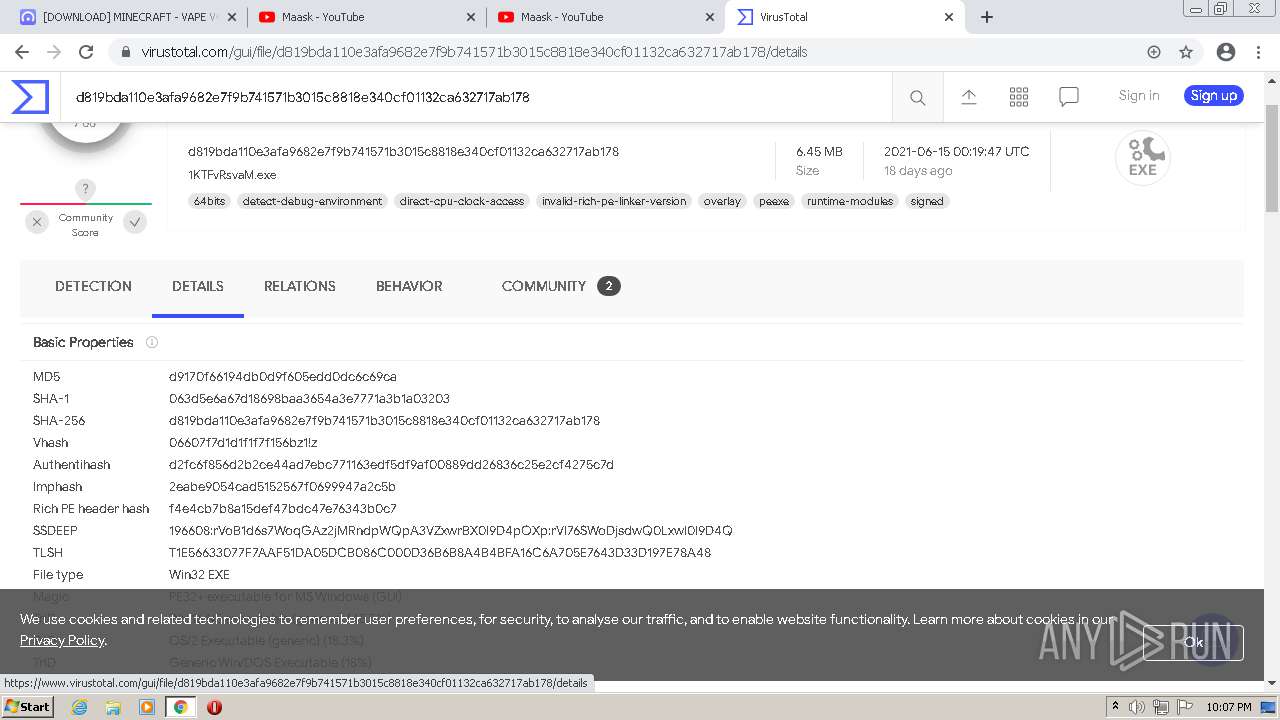
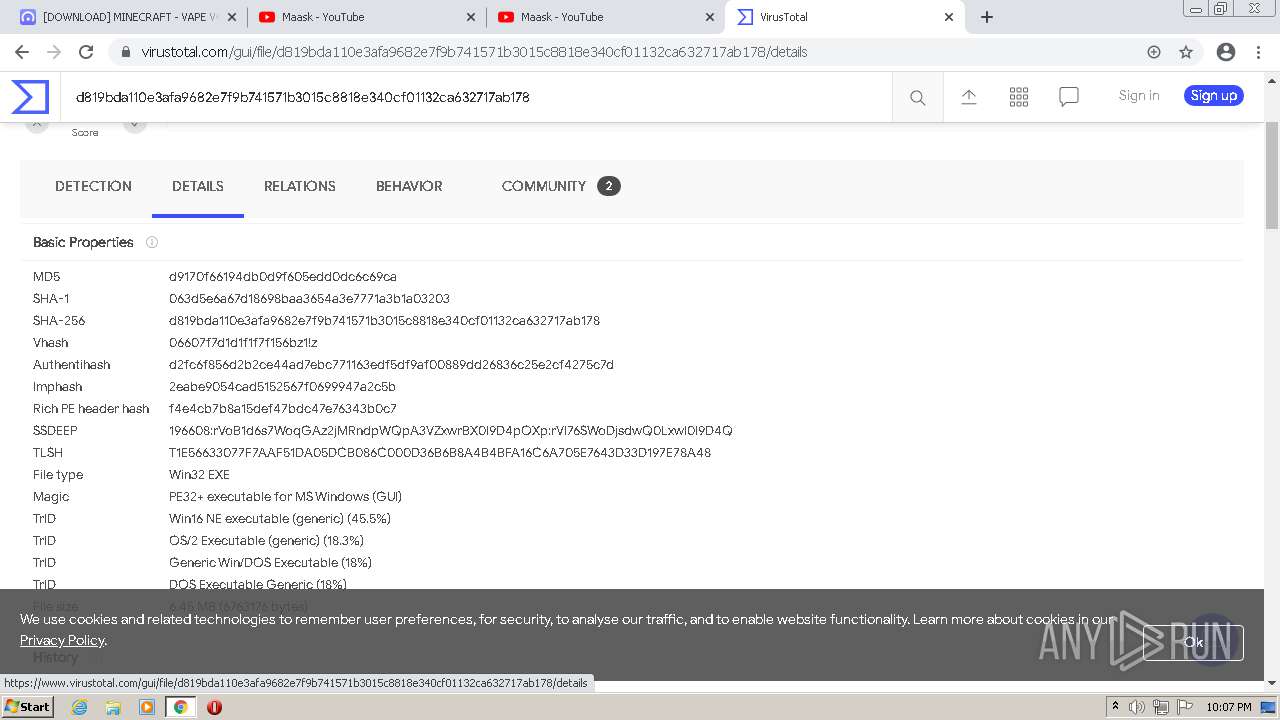
| MD5: | 770FA5BA7C6B2EDBDF27302C215AC989 |
| SHA1: | 70CEDBB6E8A1A78F41523B1EFA827C29B59AAF80 |
| SHA256: | C00DB772EB94450909650E669DB051F5C72AC4884A474F109E22F1344E7C52E5 |
| SSDEEP: | 3:N8DSLqAsLMKKI3TP4kI9p/RIQZdAn:2OLg4RIcB9FtfA |
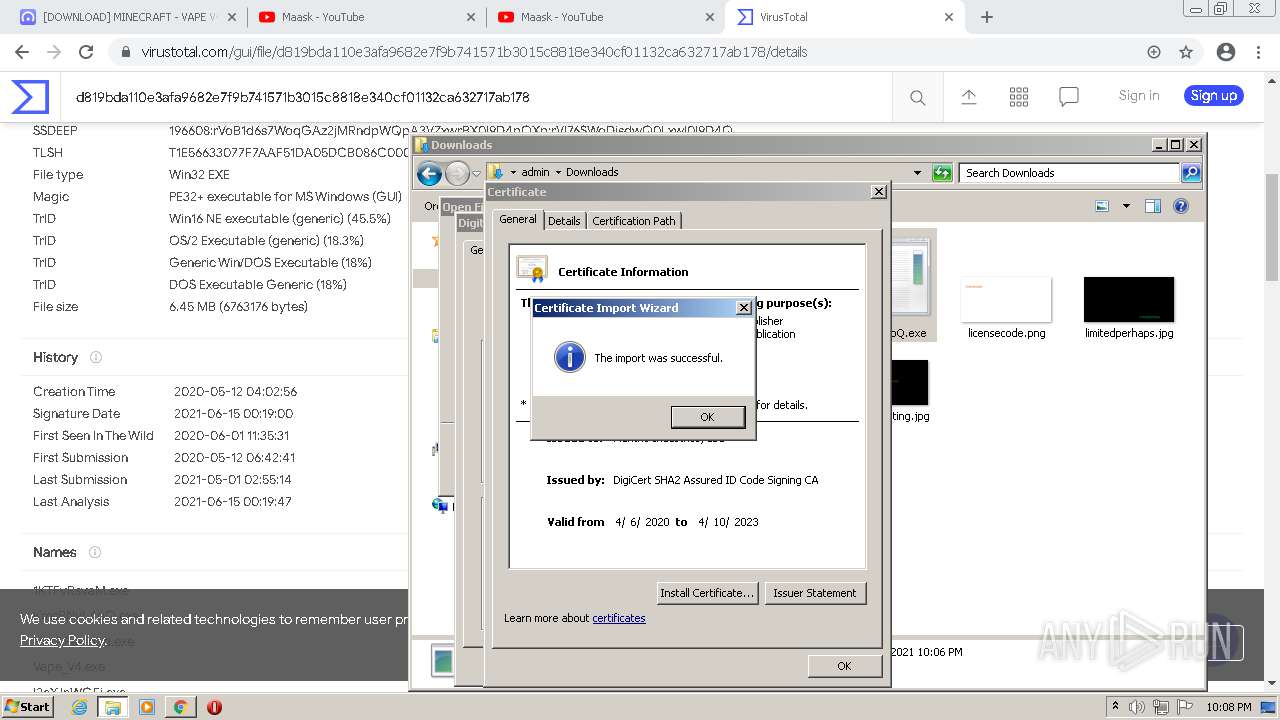
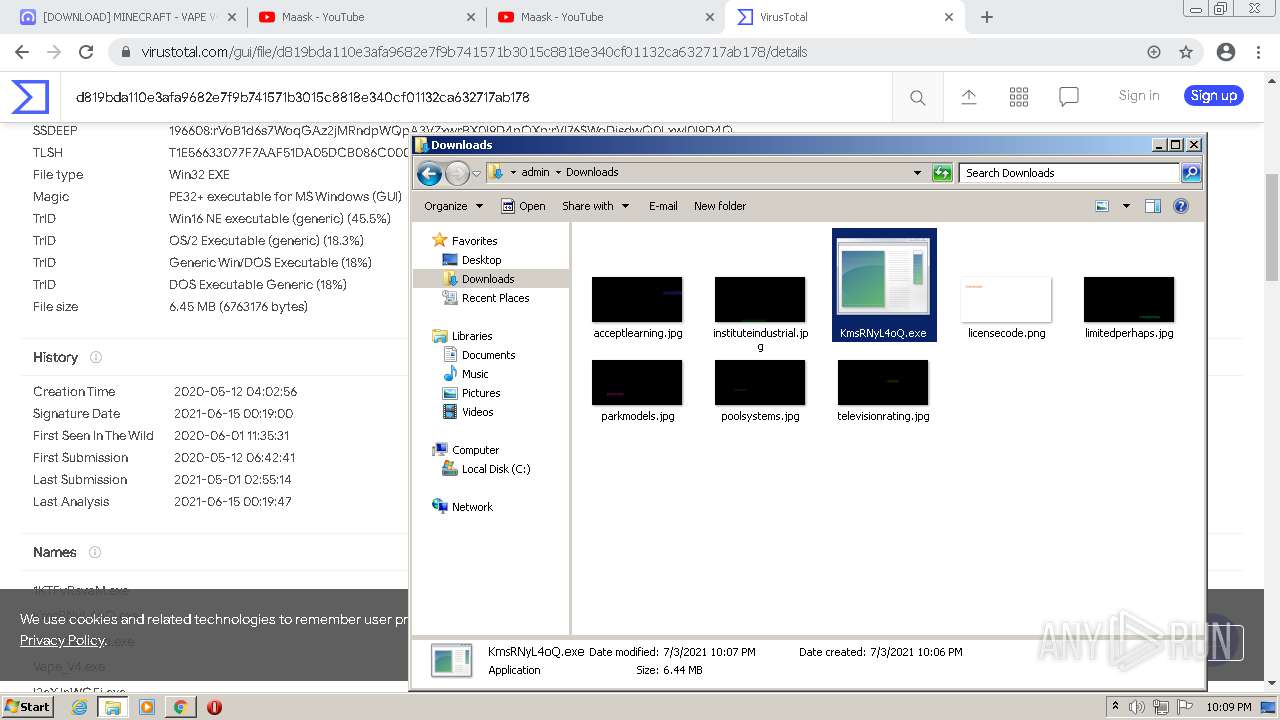
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2420)
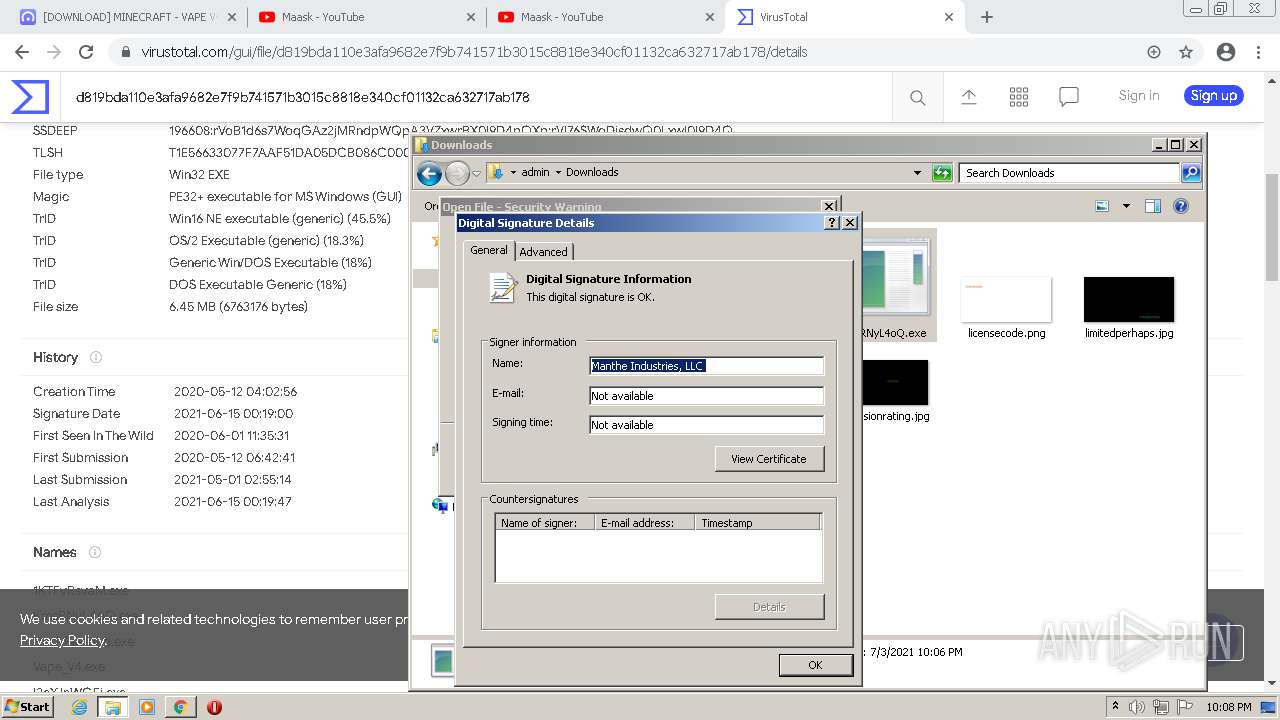
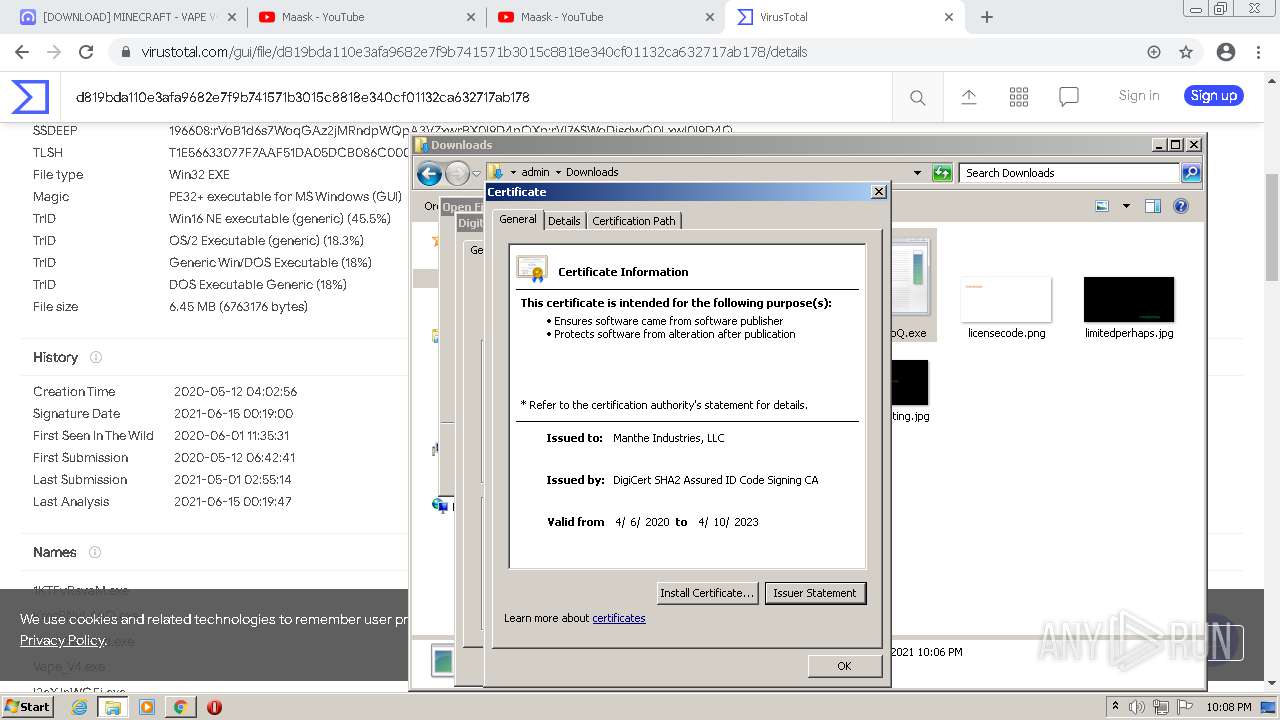
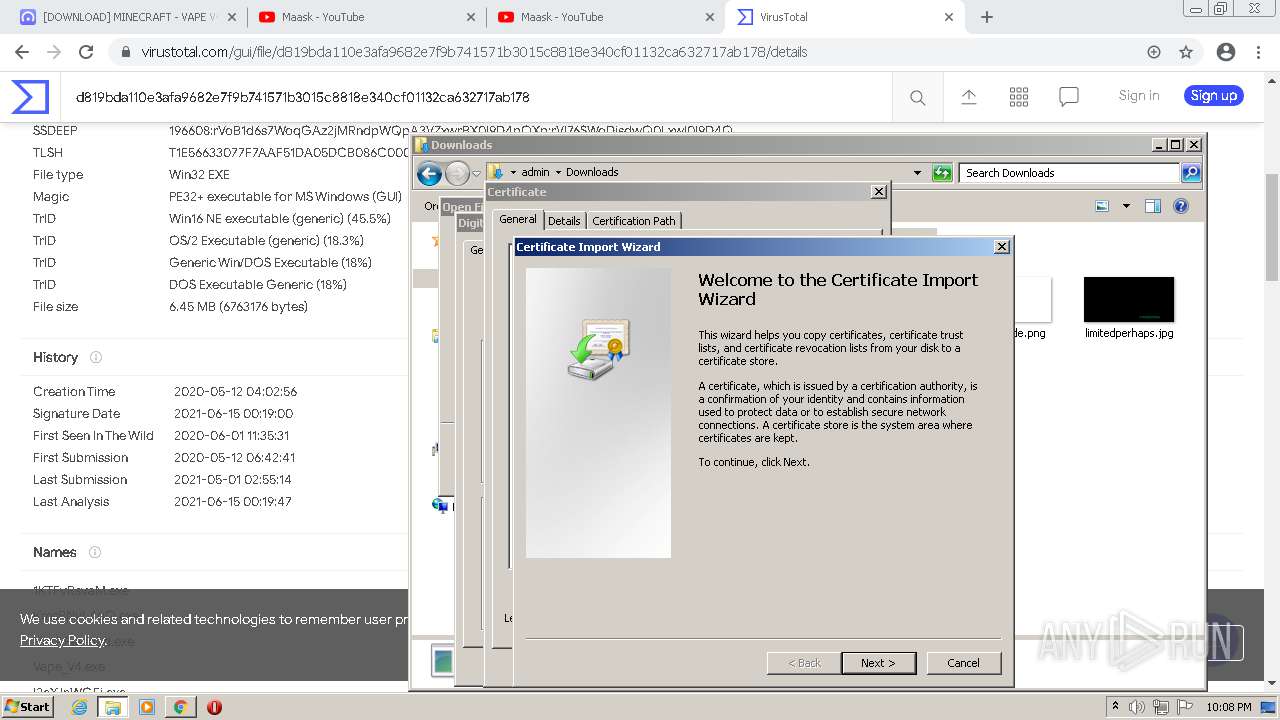
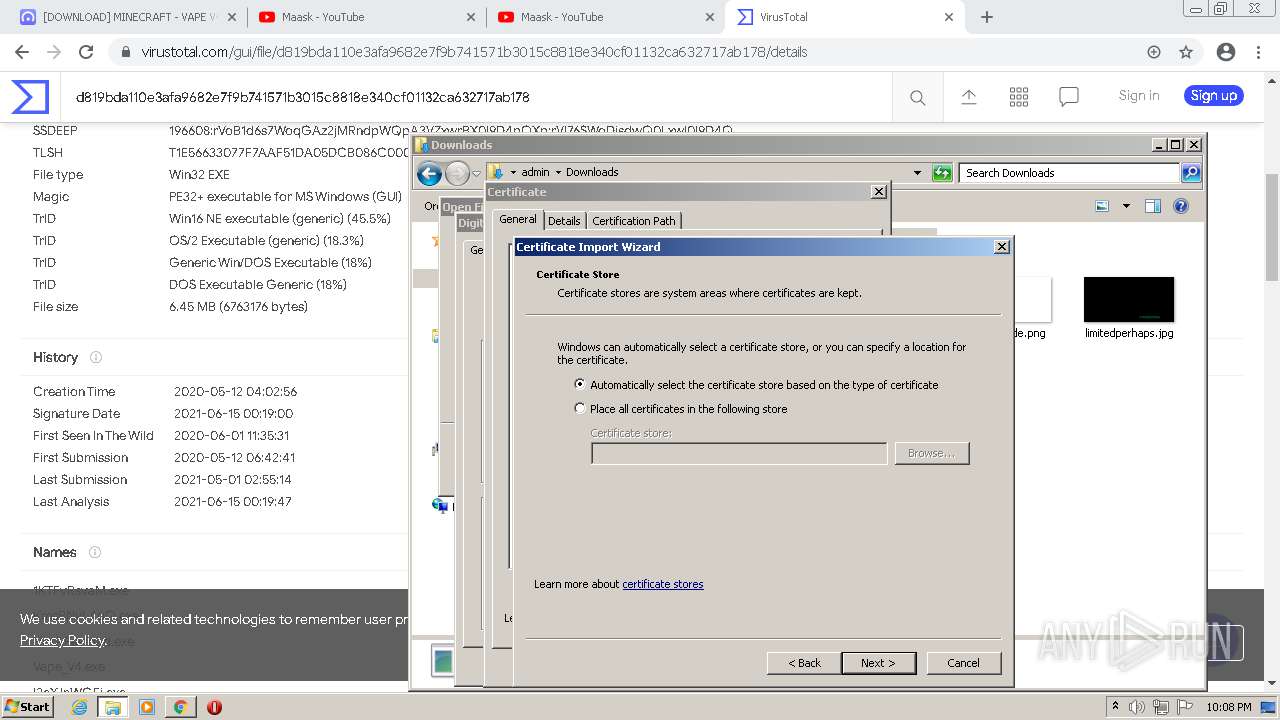
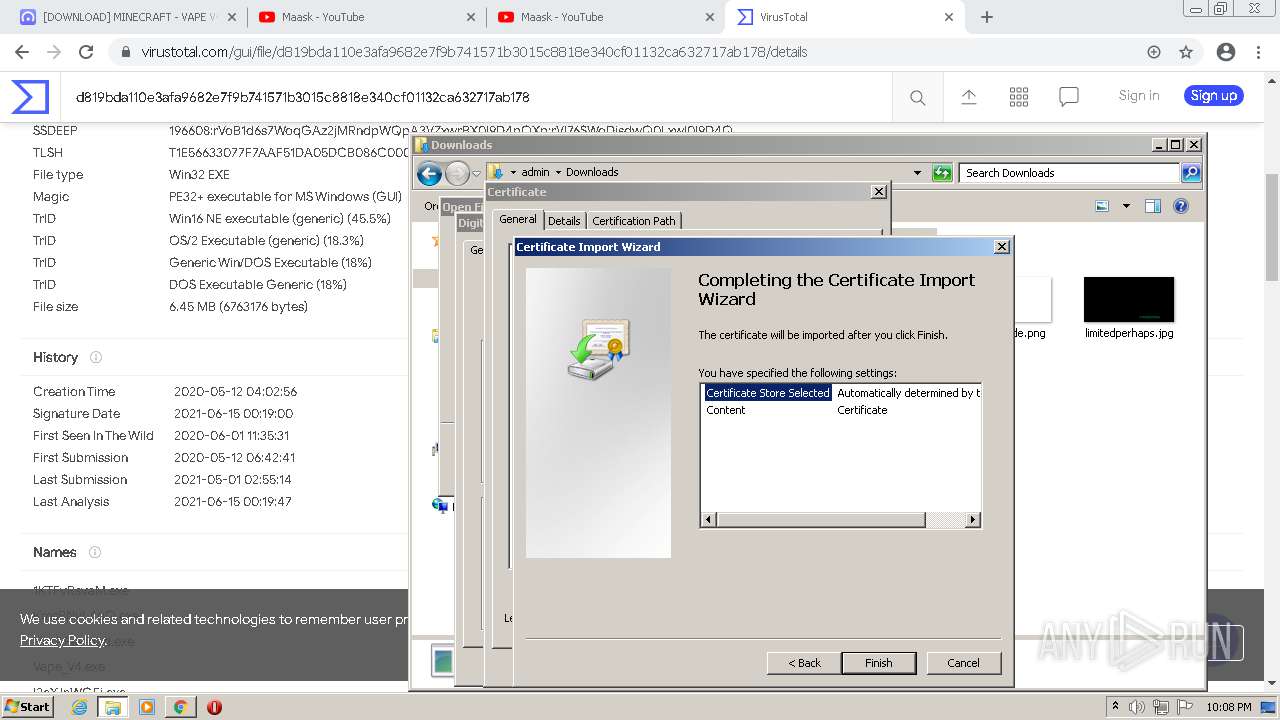
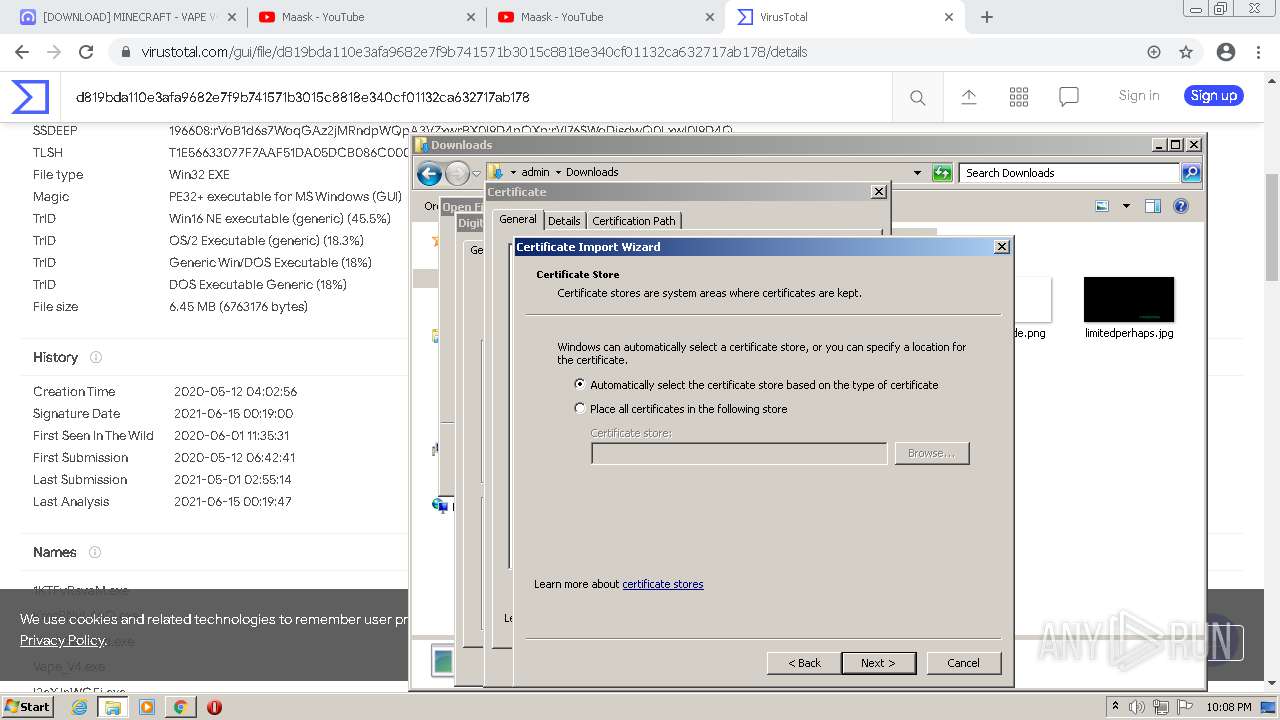
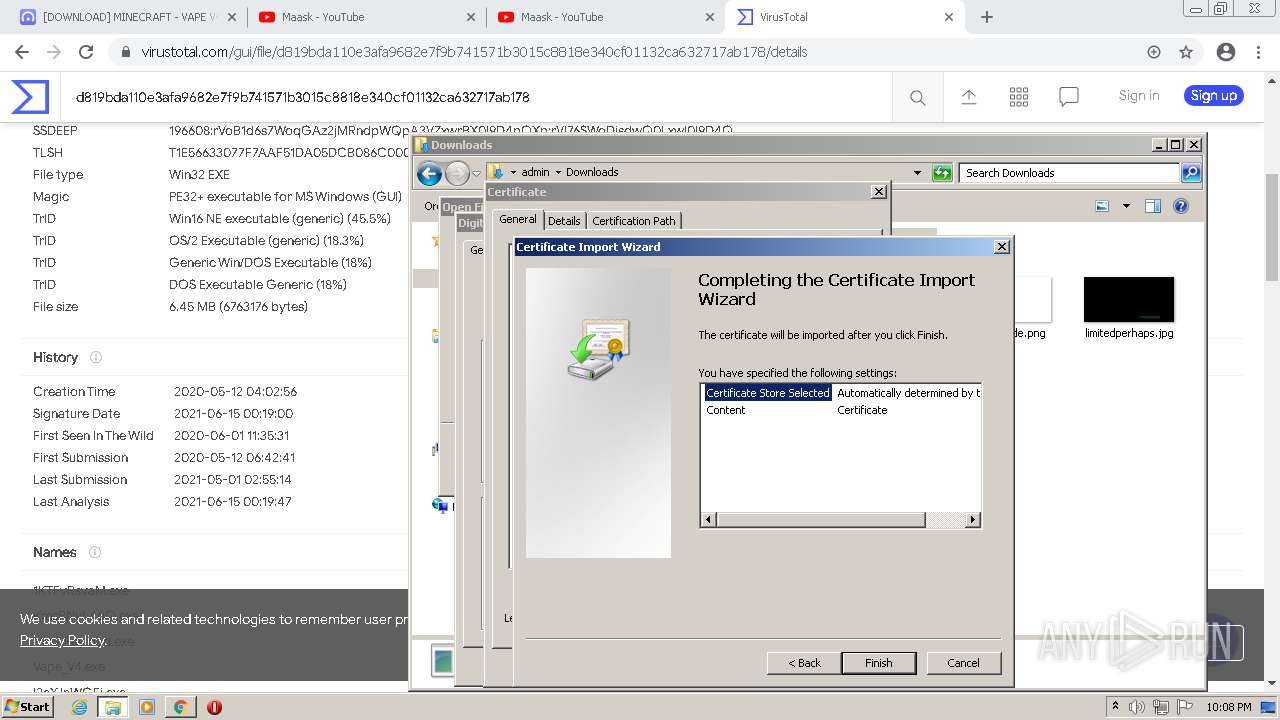
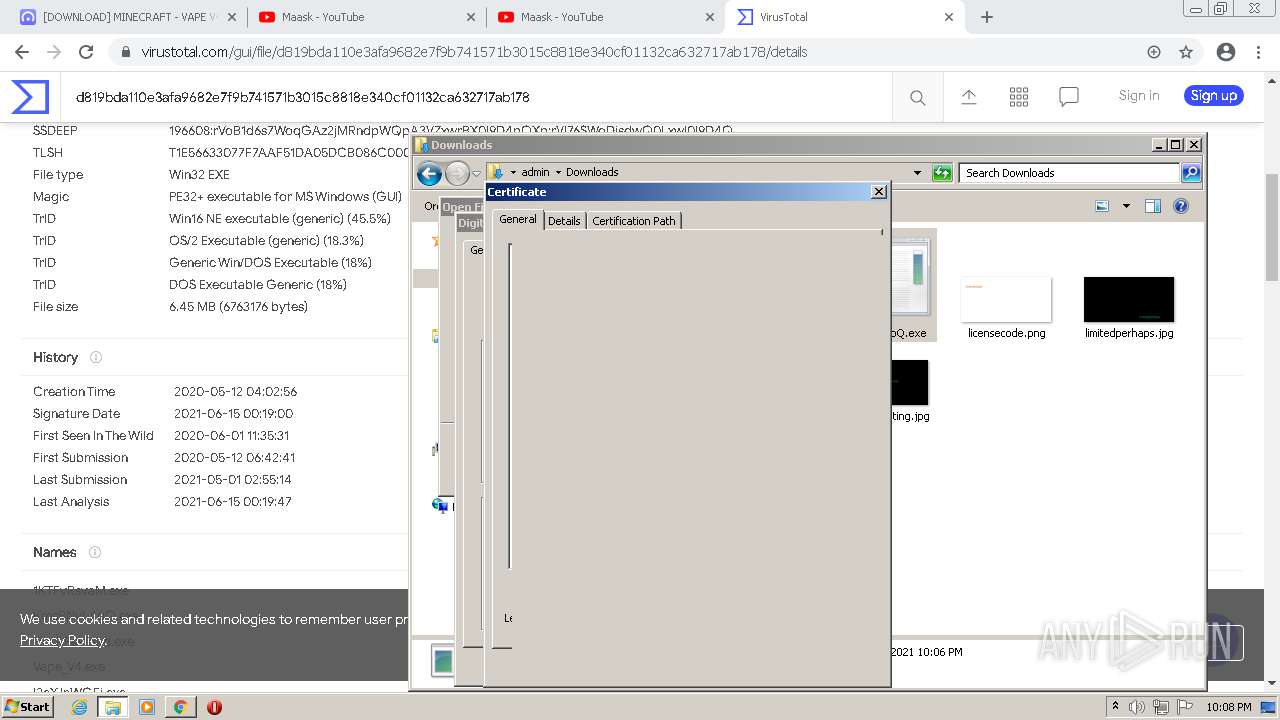
Changes settings of System certificates
- Explorer.EXE (PID: 1384)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1576)
- chrome.exe (PID: 2420)
Reads default file associations for system extensions
- chrome.exe (PID: 1660)
- Explorer.EXE (PID: 1384)
Starts Internet Explorer
- Explorer.EXE (PID: 1384)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2108)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2420)
INFO
Checks supported languages
- chrome.exe (PID: 2324)
- chrome.exe (PID: 2804)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 1576)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 564)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 1656)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 1692)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 1056)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 1660)
- chrome.exe (PID: 2748)
- explorer.exe (PID: 2444)
- chrome.exe (PID: 272)
- chrome.exe (PID: 4052)
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 3472)
- iexplore.exe (PID: 2108)
- chrome.exe (PID: 1176)
- chrome.exe (PID: 1276)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 1132)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 1280)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 2720)
Application launched itself
- chrome.exe (PID: 1576)
- iexplore.exe (PID: 2988)
Reads the hosts file
- chrome.exe (PID: 3044)
- chrome.exe (PID: 1576)
Reads the computer name
- chrome.exe (PID: 1576)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2804)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 1660)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 2840)
- explorer.exe (PID: 2444)
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2108)
Reads settings of System Certificates
- chrome.exe (PID: 3044)
- chrome.exe (PID: 1576)
- Explorer.EXE (PID: 1384)
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 2988)
Checks Windows Trust Settings
- chrome.exe (PID: 1576)
- Explorer.EXE (PID: 1384)
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 2988)
Reads the date of Windows installation
- chrome.exe (PID: 2408)
- iexplore.exe (PID: 2988)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1576)
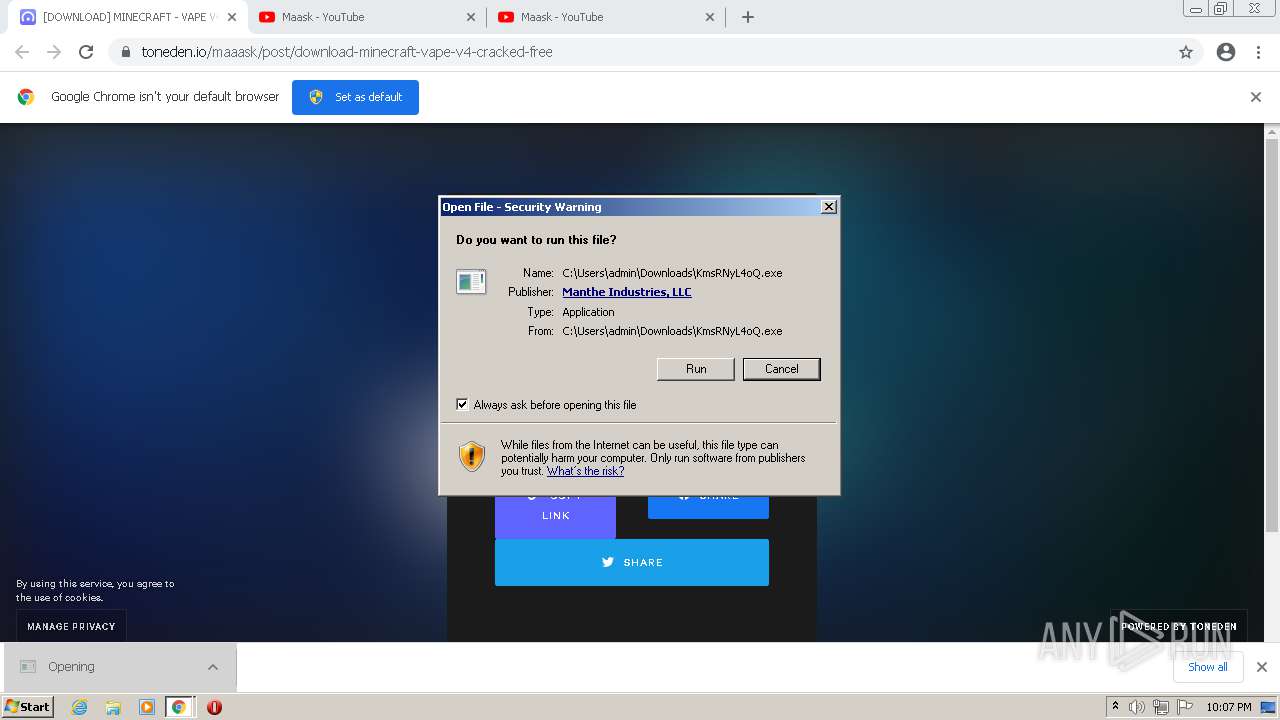
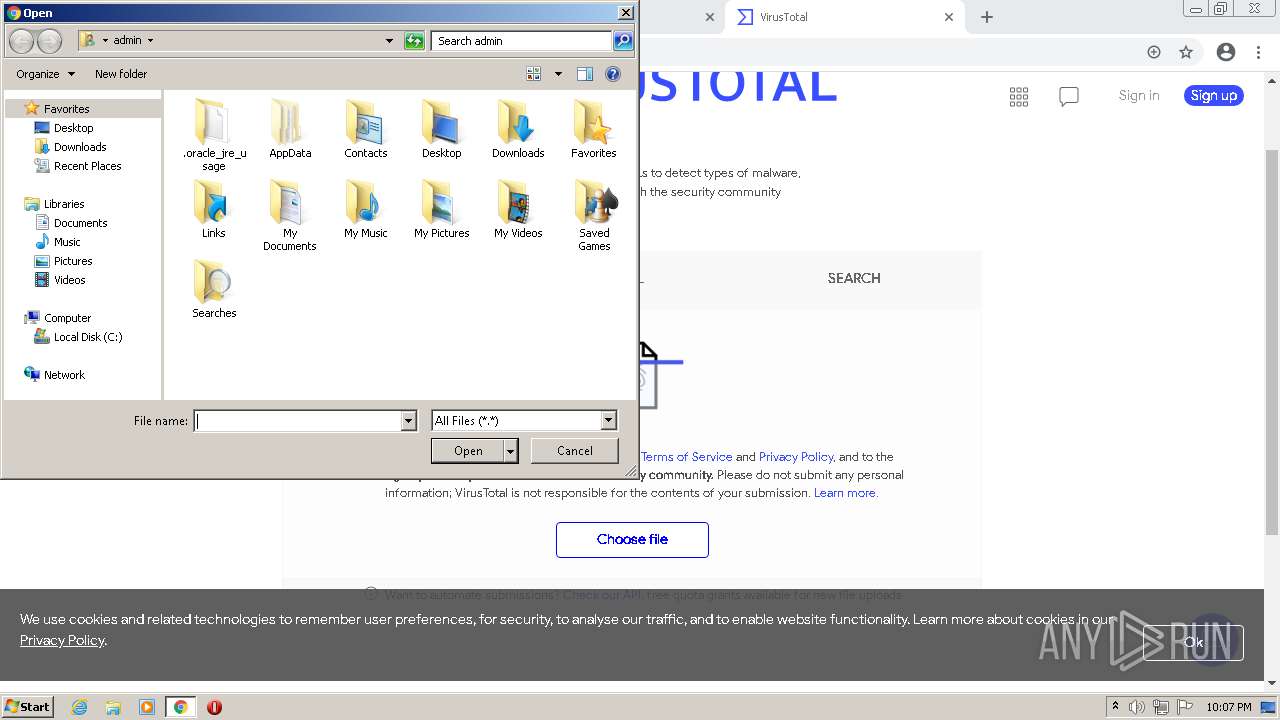
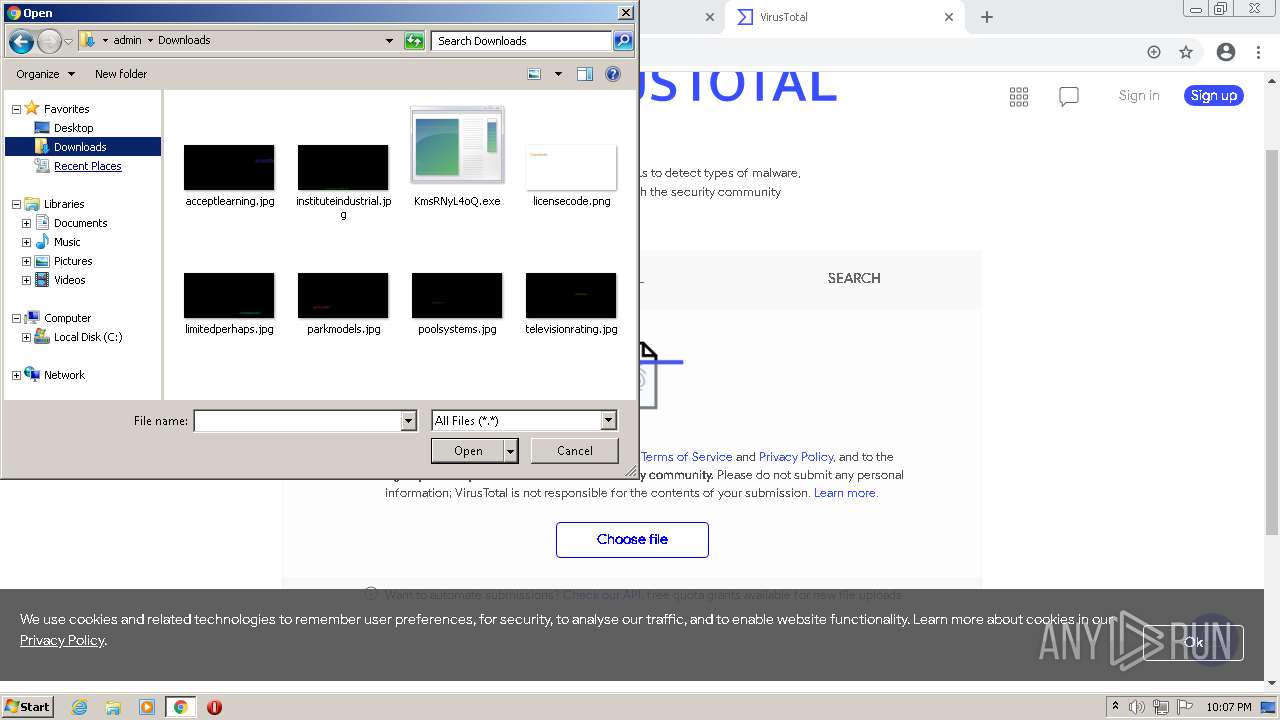
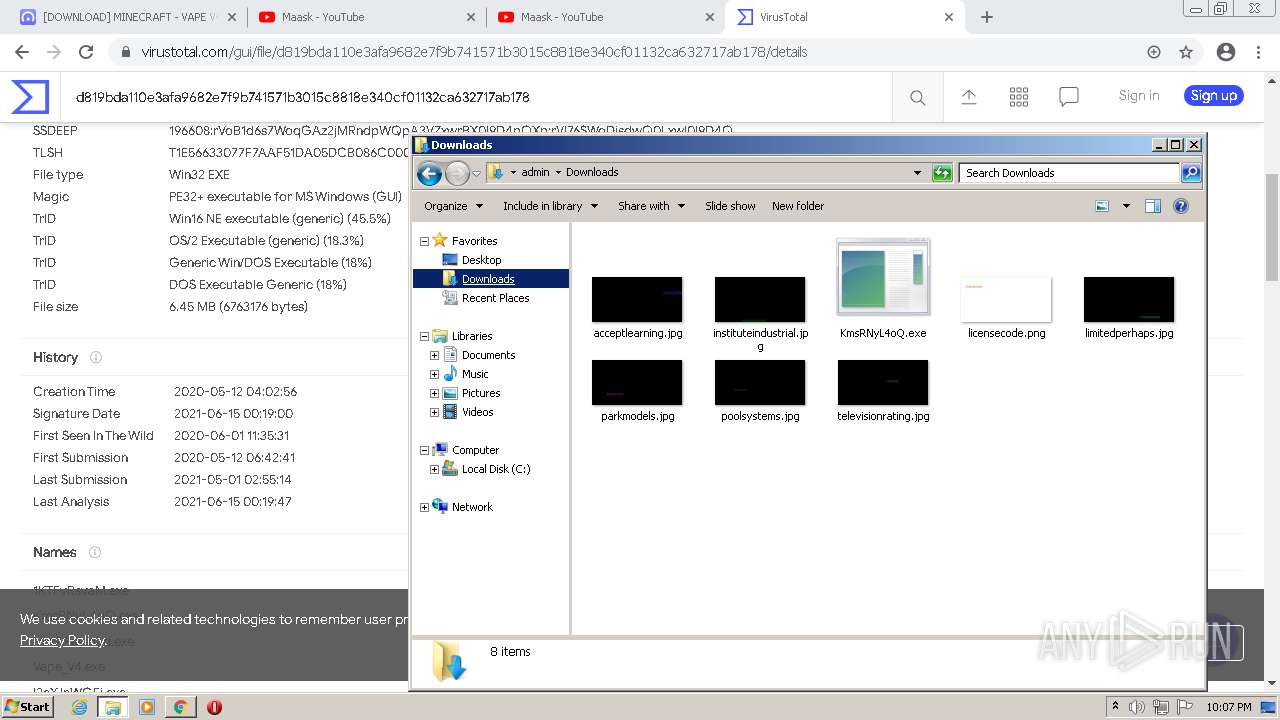
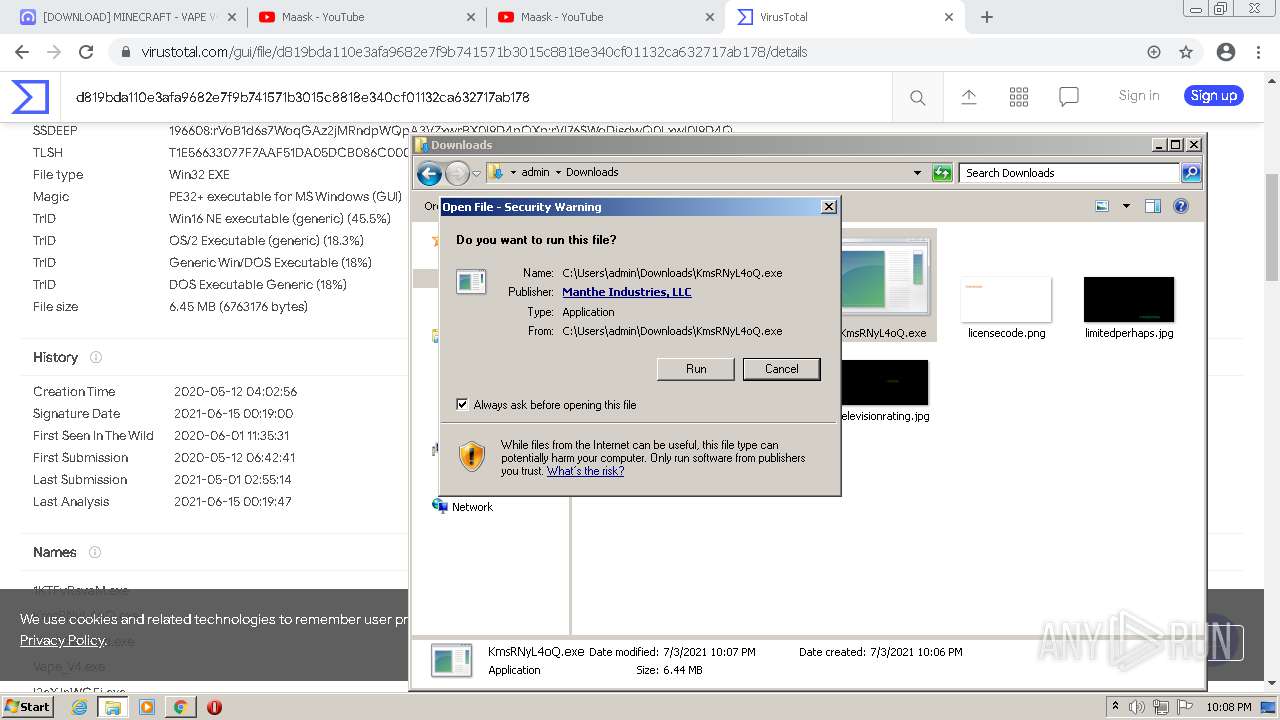
Manual execution by user
- explorer.exe (PID: 2444)
Changes internet zones settings
- iexplore.exe (PID: 2988)
Reads internet explorer settings
- iexplore.exe (PID: 2108)
Creates files in the user directory
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
56
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3040 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4696 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4356 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1384 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://www.toneden.io/maaask/post/download-minecraft-vape-v4-cracked-free" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
50 094
Read events
49 530
Write events
555
Delete events
9
Modification events
| (PID) Process: | (1384) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB0100000036BA507BB2276043AA81AC8F7B4BEB52000000000200000000001066000000010000200000008D4C6A99DCEFA5A6367E0A9FBA5B51F78C4D0206BB406D23E8681293BB2F51DC000000000E8000000002000020000000EBBE9A1E38728444992DEA3303B62631F3CAC9B04F6F760721B537FE618C20C630000000CF9FBA91EFAF0EB3703C3CF2D473BEF9421B73AADF1B77D94A1E39B21E8F6D23760ED5C05DF77EB6D4BCBA8A79F93CDF4000000067C0042031D699A49FD6D138D3A48AADA7B8A8C337FAF496EFFA18E6B09BAC87008AADE467793C3D7D4D6C988A44F04A688B40015BAEEA7ACE7165056332B5E2 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
4
Suspicious files
162
Text files
270
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60E0D157-628.pma | — | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\303ebacf-1c80-414b-b38b-8ced4fa03c97.tmp | text | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF2b3ead.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF2b44d7.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2b3ead.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF2b411e.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
100
TCP/UDP connections
167
DNS requests
126
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
— | — | HEAD | 200 | 74.125.110.136:80 | http://r3---sn-5goeen7y.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=Yu&mip=157.97.120.6&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1625346015&mv=m&mvi=3&pl=25&shardbypass=yes&smhost=r3---sn-5go7yne6.gvt1.com | US | — | — | whitelisted |
— | — | HEAD | 200 | 173.194.150.168:80 | http://r2---sn-5goeen76.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=157.97.120.6&mm=28&mn=sn-5goeen76&ms=nvh&mt=1625346255&mv=m&mvi=2&pl=25&rmhost=r1---sn-5goeen76.gvt1.com&shardbypass=yes&smhost=r1---sn-5go7yner.gvt1.com | US | — | — | whitelisted |
3044 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3044 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAcXeREAXSJn9oiS9o%2BLUFg%3D | US | der | 471 b | whitelisted |
— | — | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | html | 555 b | whitelisted |
— | — | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 540 b | whitelisted |
— | — | GET | 206 | 173.194.150.168:80 | http://r2---sn-5goeen76.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=157.97.120.6&mm=28&mn=sn-5goeen76&ms=nvh&mt=1625346015&mv=m&mvi=2&pl=25&rmhost=r1---sn-5goeen76.gvt1.com&shardbypass=yes&smhost=r1---sn-5go7yner.gvt1.com | US | binary | 7.53 Kb | whitelisted |
— | — | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 540 b | whitelisted |
— | — | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 540 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3044 | chrome.exe | 142.250.185.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3044 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3044 | chrome.exe | 52.53.92.3:443 | www.toneden.io | Amazon.com, Inc. | US | unknown |
3044 | chrome.exe | 151.101.2.110:443 | cdn.evbstatic.com | Fastly | US | suspicious |
3044 | chrome.exe | 151.101.2.132:443 | st.toneden.io | Fastly | US | malicious |
3044 | chrome.exe | 104.18.22.52:443 | kit.fontawesome.com | Cloudflare Inc | US | unknown |
3044 | chrome.exe | 2.16.186.25:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3044 | chrome.exe | 34.107.143.101:443 | dcinfos-cache.abtasty.com | — | US | suspicious |
— | — | 34.102.161.46:443 | ariane.abtasty.com | — | US | suspicious |
3044 | chrome.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.toneden.io |
| suspicious |
platform.twitter.com |
| whitelisted |
st.toneden.io |
| whitelisted |
kit.fontawesome.com |
| whitelisted |
cdn.evbstatic.com |
| whitelisted |
try.abtasty.com |
| shared |
static.ads-twitter.com |
| whitelisted |
ka-p.fontawesome.com |
| whitelisted |