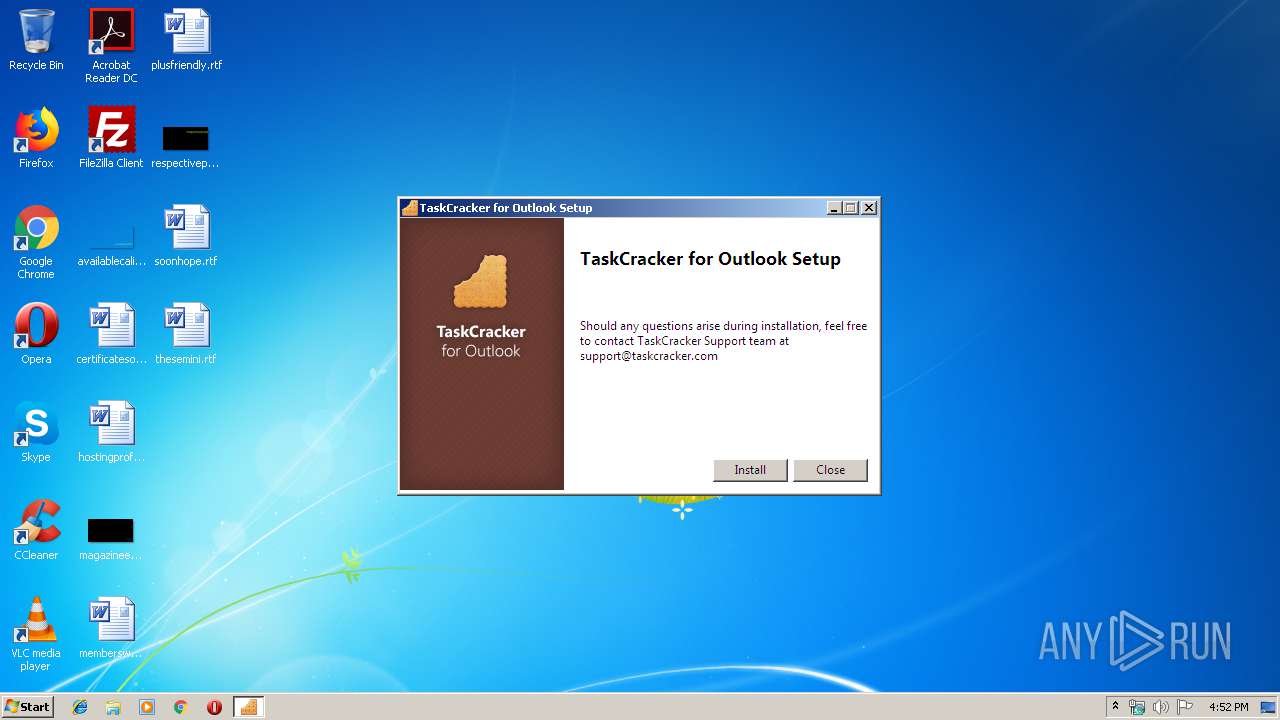
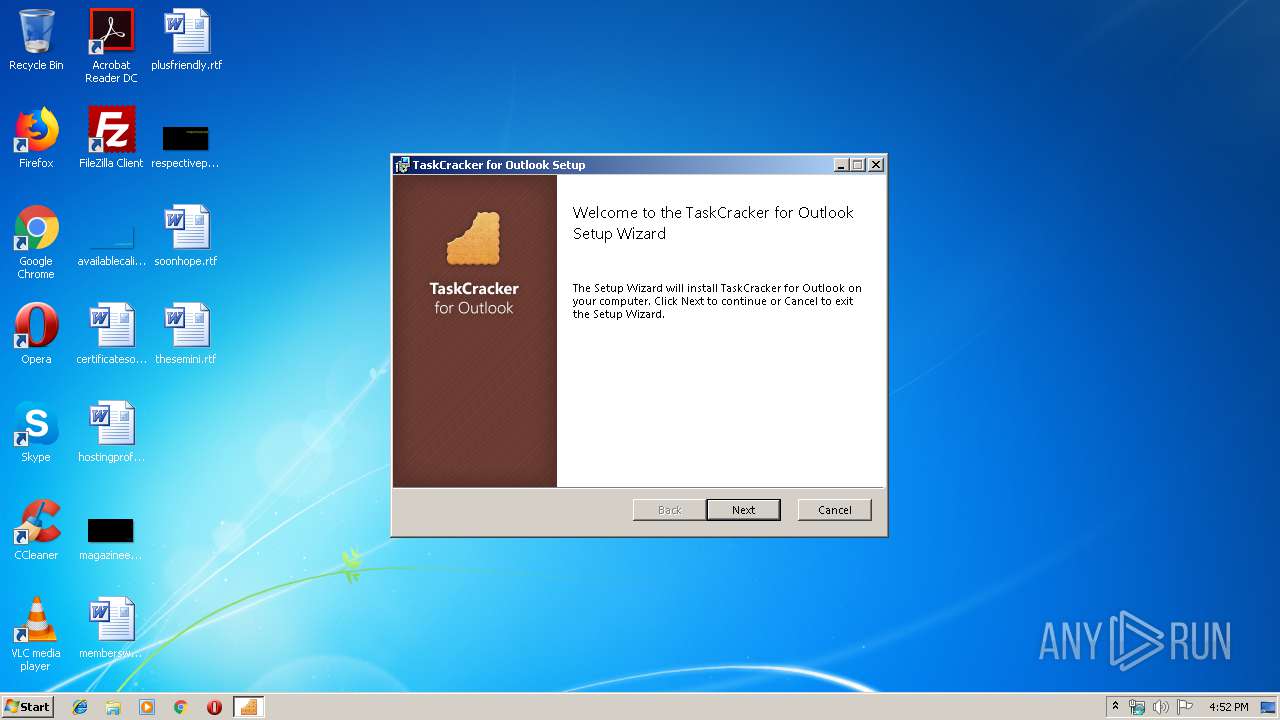
| download: | TaskCrackerForOutlook.exe |
| Full analysis: | https://app.any.run/tasks/38fd4b93-4eeb-482e-87d1-e065e43d55df |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 15:51:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 265F9941050BA6EB8DFBC83E5059040C |
| SHA1: | AEF78BBEBB80A1828D8A73D465F7C4D52C7DE76D |
| SHA256: | C00321608ED18683E03E305B3F001A98D642B8F2A7E61929843E9F63C0FD2896 |
| SSDEEP: | 98304:QgH0nAk/rZaH7vvNkP4uJYnyBf0IBLQy8qD8gZIjgCf:QgUnhVq7vvNkPVB87h/jH |
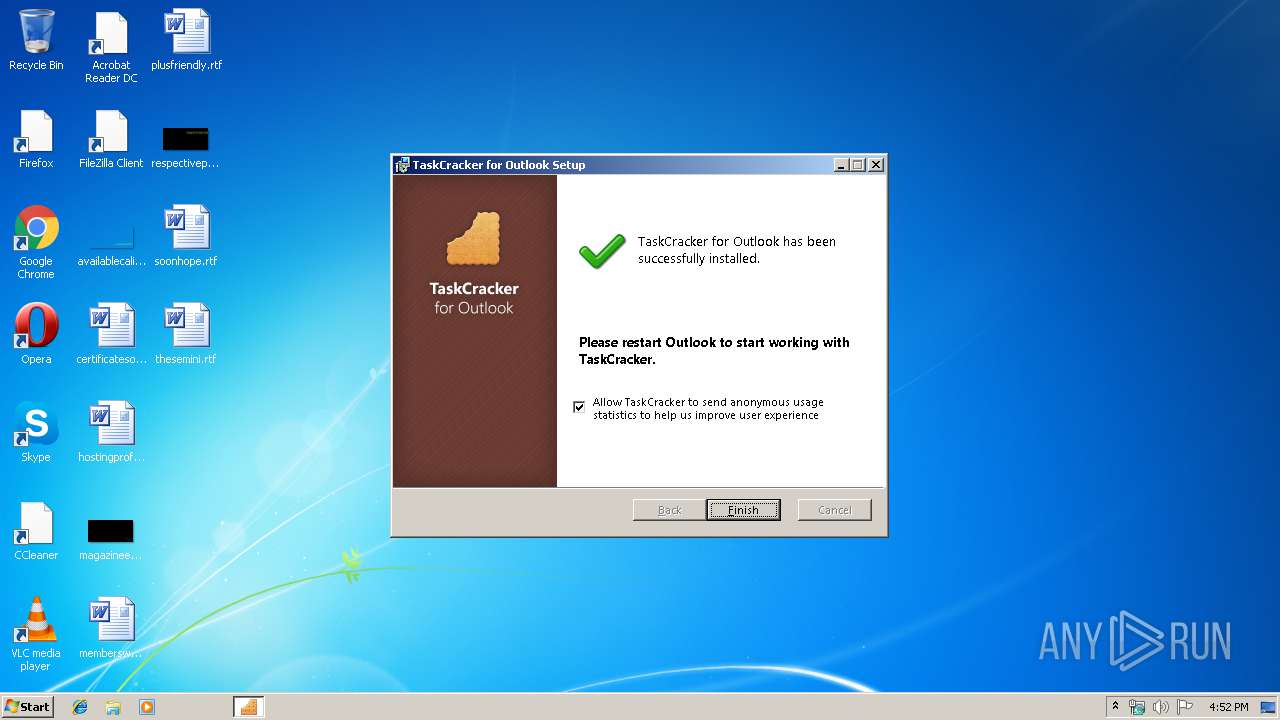
MALICIOUS
Loads dropped or rewritten executable
- TaskCrackerForOutlook.exe (PID: 4076)
Application was dropped or rewritten from another process
- TaskCrackerForOutlook.exe (PID: 4076)
Changes the autorun value in the registry
- TaskCrackerForOutlook.exe (PID: 4076)
SUSPICIOUS
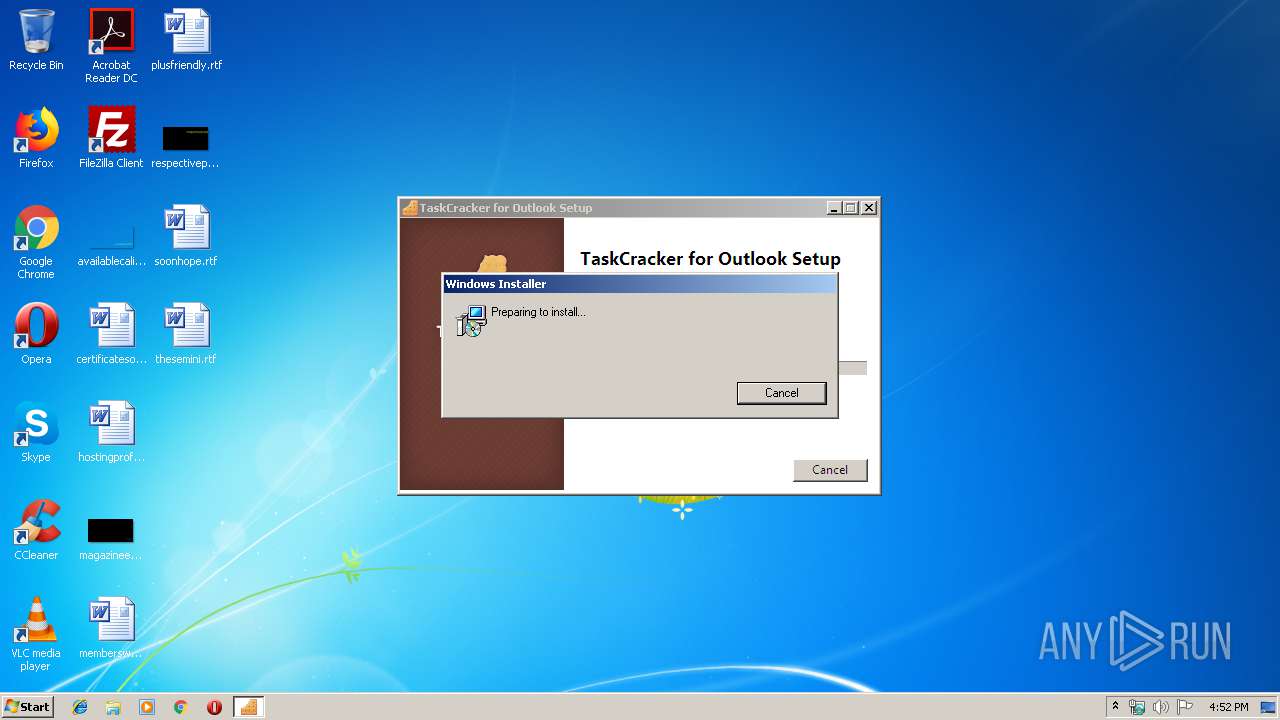
Executable content was dropped or overwritten
- TaskCrackerForOutlook.exe (PID: 3156)
- TaskCrackerForOutlook.exe (PID: 4076)
- msiexec.exe (PID: 2328)
Creates a software uninstall entry
- TaskCrackerForOutlook.exe (PID: 4076)
Creates files in the user directory
- msiexec.exe (PID: 2328)
Creates COM task schedule object
- MSI9094.tmp (PID: 3312)
Starts application with an unusual extension
- TaskCrackerForOutlook.exe (PID: 4076)
Modifies files in Chrome extension folder
- chrome.exe (PID: 456)
INFO
Application launched itself
- msiexec.exe (PID: 2328)
- chrome.exe (PID: 456)
Starts application with an unusual extension
- msiexec.exe (PID: 2328)
Application was dropped or rewritten from another process
- MSI8AA7.tmp (PID: 3816)
- MSI9094.tmp (PID: 3312)
Loads dropped or rewritten executable
- MSI9094.tmp (PID: 3312)
Reads Microsoft Office registry keys
- MSI9094.tmp (PID: 3312)
Manual execution by user
- chrome.exe (PID: 456)
Creates a software uninstall entry
- msiexec.exe (PID: 2328)
Reads settings of System Certificates
- chrome.exe (PID: 3812)
Dropped object may contain TOR URL's
- chrome.exe (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:01 16:33:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.1 |
| CodeSize: | 302080 |
| InitializedDataSize: | 342528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e1fd |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | TaskCracker |
| FileDescription: | TaskCracker for Outlook |
| FileVersion: | 2.2 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) TaskCracker. All rights reserved. |
| OriginalFileName: | TaskCrackerForOutlook.exe |
| ProductName: | TaskCracker for Outlook |
| ProductVersion: | 2.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-May-2017 14:33:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | TaskCracker |
| FileDescription: | TaskCracker for Outlook |
| FileVersion: | 2.2 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) TaskCracker. All rights reserved. |
| OriginalFilename: | TaskCrackerForOutlook.exe |
| ProductName: | TaskCracker for Outlook |
| ProductVersion: | 2.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 01-May-2017 14:33:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049A67 | 0x00049C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56282 |
.rdata | 0x0004B000 | 0x0001EC60 | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10841 |
.data | 0x0006A000 | 0x00001730 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15458 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.739068 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006E000 | 0x0002FE54 | 0x00030000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.17351 |
.reloc | 0x0009E000 | 0x00003DEC | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.79026 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.97589 | 23851 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.83849 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.85174 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.72034 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.48811 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.74599 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.68831 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
85
Monitored processes
50
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12104411717114758771 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16062747478991276503 --mojo-platform-channel-handle=2136 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8770857425326004674 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11793477563337149993 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16562728107289269932 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10632689633433311263 --mojo-platform-channel-handle=3004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10031222792492795572 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16518742659682591938 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14720694170474934525,13758086467037176973,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13984246559085296419 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 722
Read events
1 066
Write events
636
Delete events
20
Modification events
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\Users\admin\AppData\Local\Package Cache\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67}\TaskCrackerForOutlook.exe | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {ED055948-6161-41E7-BCFC-72688790E112} | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundleVersion |
Value: 2.2.0.0 | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | VersionMajor |
Value: 2 | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | VersionMinor |
Value: 2 | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundleProviderKey |
Value: {5a67a3d3-fe1c-4050-9a04-53a4eb778d67} | |||
| (PID) Process: | (4076) TaskCrackerForOutlook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{5a67a3d3-fe1c-4050-9a04-53a4eb778d67} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
36
Suspicious files
75
Text files
234
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4076 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Temp\{796341CA-87C8-425A-9E86-03C1CB2F0053}\OutlookTaskCrackerSetup.msi | — | |
MD5:— | SHA256:— | |||
| 4076 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Package Cache\.unverified\OutlookTaskCrackerSetup.msi | — | |
MD5:— | SHA256:— | |||
| 4076 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Package Cache\{C5514F3C-211B-4814-905F-0A646483E794}v2.2\OutlookTaskCrackerSetup.msi | — | |
MD5:— | SHA256:— | |||
| 4076 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Temp\MSI7DA5.tmp | — | |
MD5:— | SHA256:— | |||
| 2328 | msiexec.exe | C:\Windows\Installer\158892.msi | — | |
MD5:— | SHA256:— | |||
| 2328 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF6E0137F50A8A8AAA.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Temp\{A92525B3-BE9A-47D4-B260-FA91B32C816D}\.cr\TaskCrackerForOutlook.exe | executable | |
MD5:— | SHA256:— | |||
| 4076 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Temp\{796341CA-87C8-425A-9E86-03C1CB2F0053}\.ba\BootstrapperApplicationData.xml | xml | |
MD5:— | SHA256:— | |||
| 4076 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Temp\{796341CA-87C8-425A-9E86-03C1CB2F0053}\.be\TaskCrackerForOutlook.exe | executable | |
MD5:— | SHA256:— | |||
| 4076 | TaskCrackerForOutlook.exe | C:\Users\admin\AppData\Local\Temp\{796341CA-87C8-425A-9E86-03C1CB2F0053}\.ba\thm.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
51
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
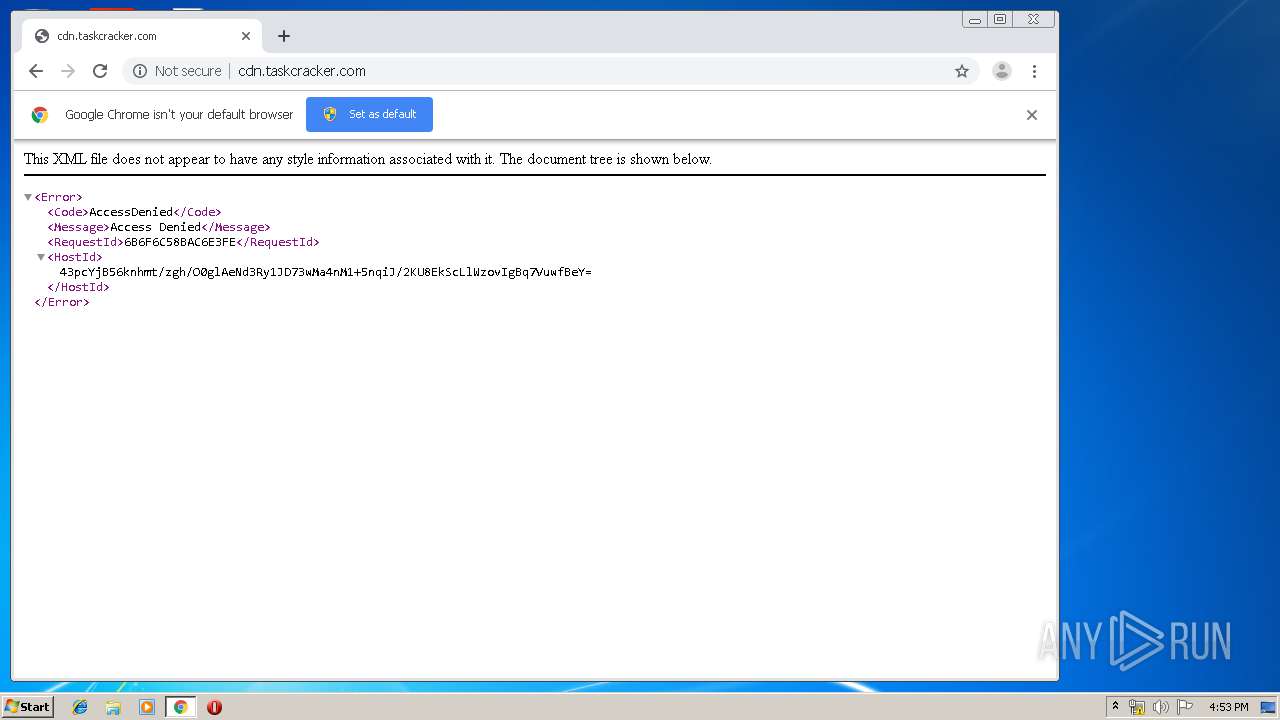
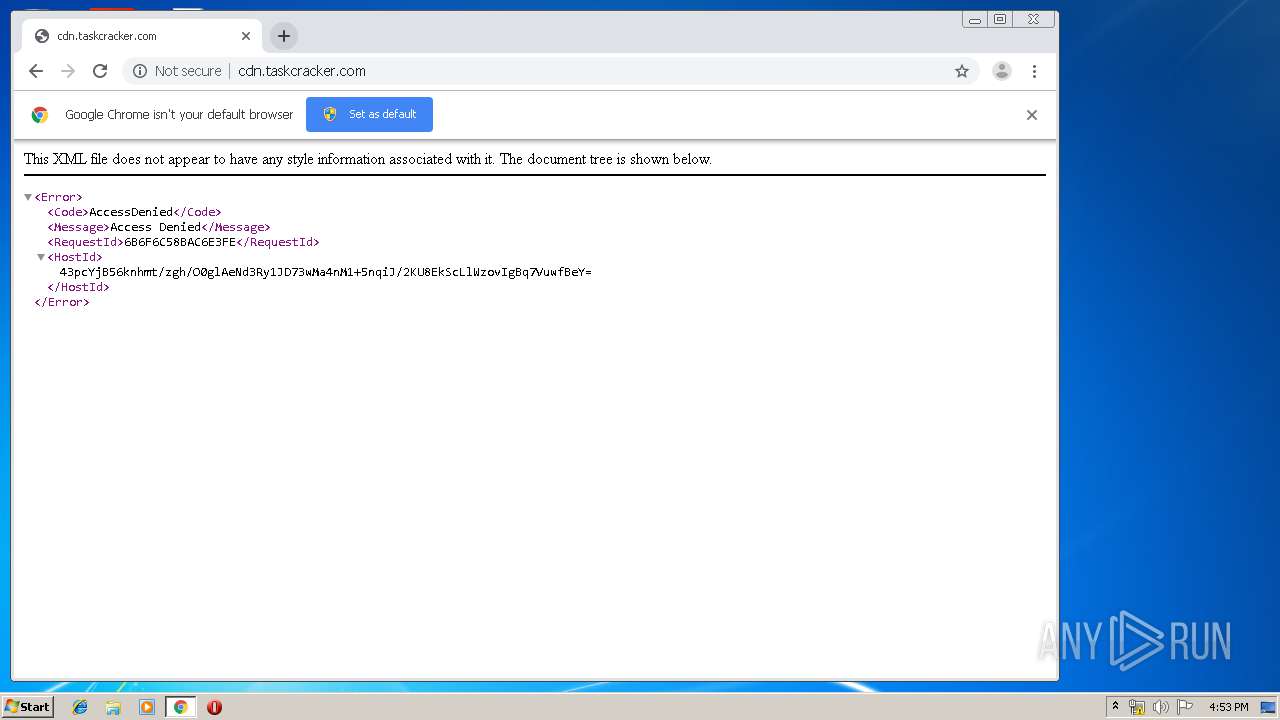
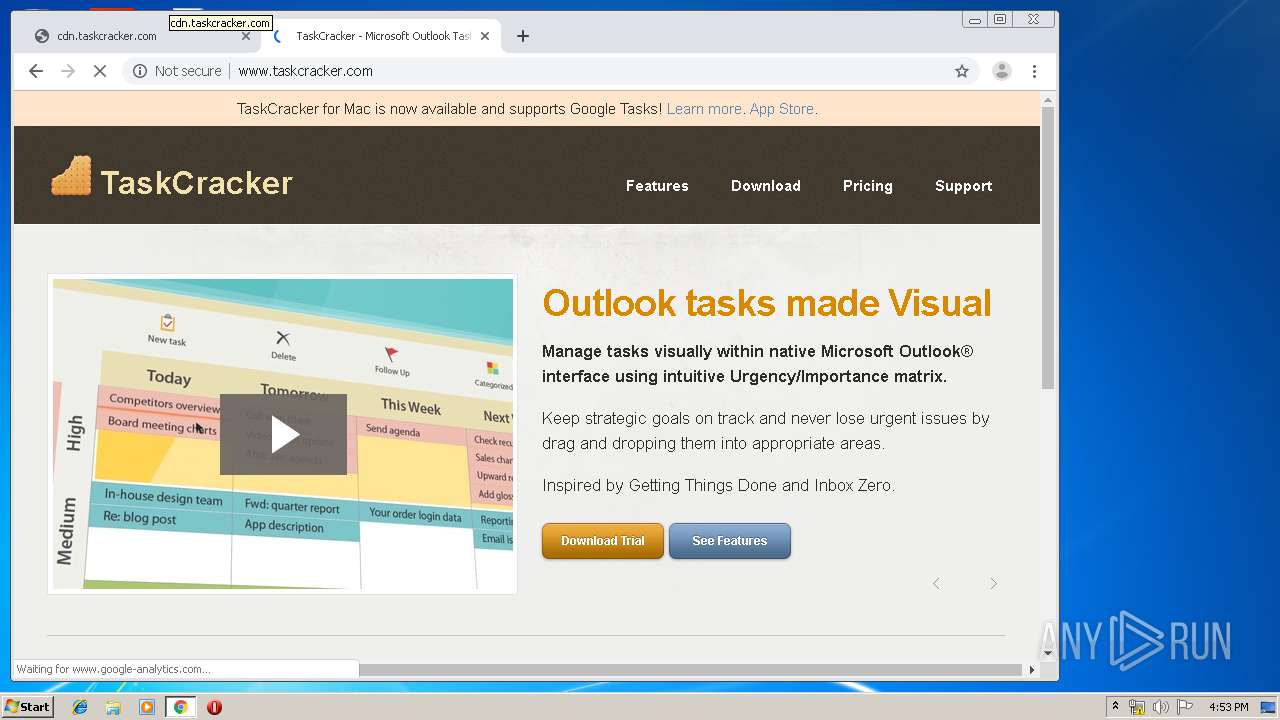
3812 | chrome.exe | GET | 200 | 54.192.185.46:80 | http://cdn.taskcracker.com/favicon.ico | US | xml | 243 b | whitelisted |
3812 | chrome.exe | GET | 200 | 50.63.99.1:80 | http://www.taskcracker.com/?w3tc_minify=64ba5.js | US | text | 15.1 Kb | malicious |
3812 | chrome.exe | GET | 200 | 54.192.185.46:80 | http://cdn.taskcracker.com/wp-content/uploads/getthingsdone.png | US | image | 11.3 Kb | whitelisted |
3812 | chrome.exe | GET | 200 | 93.184.221.133:80 | http://embed-0.wistia.com/deliveries/a2295bdf0bb939cb5d272bb29cc879f68e7e86c3.jpg?image_play_button=true&image_crop_resized=460x310 | US | image | 29.5 Kb | malicious |
3812 | chrome.exe | GET | 200 | 50.63.99.1:80 | http://www.taskcracker.com/ | US | html | 5.83 Kb | malicious |
3812 | chrome.exe | GET | 200 | 50.63.99.1:80 | http://www.taskcracker.com/?w3tc_minify=14e10.css | US | text | 6.89 Kb | malicious |
3812 | chrome.exe | GET | 200 | 151.101.2.110:80 | http://fast.wistia.com/static/popover-v1.js | US | text | 64.2 Kb | whitelisted |
3812 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
3812 | chrome.exe | GET | 200 | 50.63.99.1:80 | http://www.taskcracker.com/?w3tc_minify=64ba5.js | US | text | 15.1 Kb | malicious |
3812 | chrome.exe | GET | 200 | 54.192.185.46:80 | http://cdn.taskcracker.com/wp-content/themes/leverage/images/main_nav_list_divider.png | US | image | 119 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3812 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.18.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3812 | chrome.exe | 173.194.7.89:80 | r3---sn-p5qs7n7e.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
cdn.taskcracker.com |
| whitelisted |
clients2.google.com |
| whitelisted |