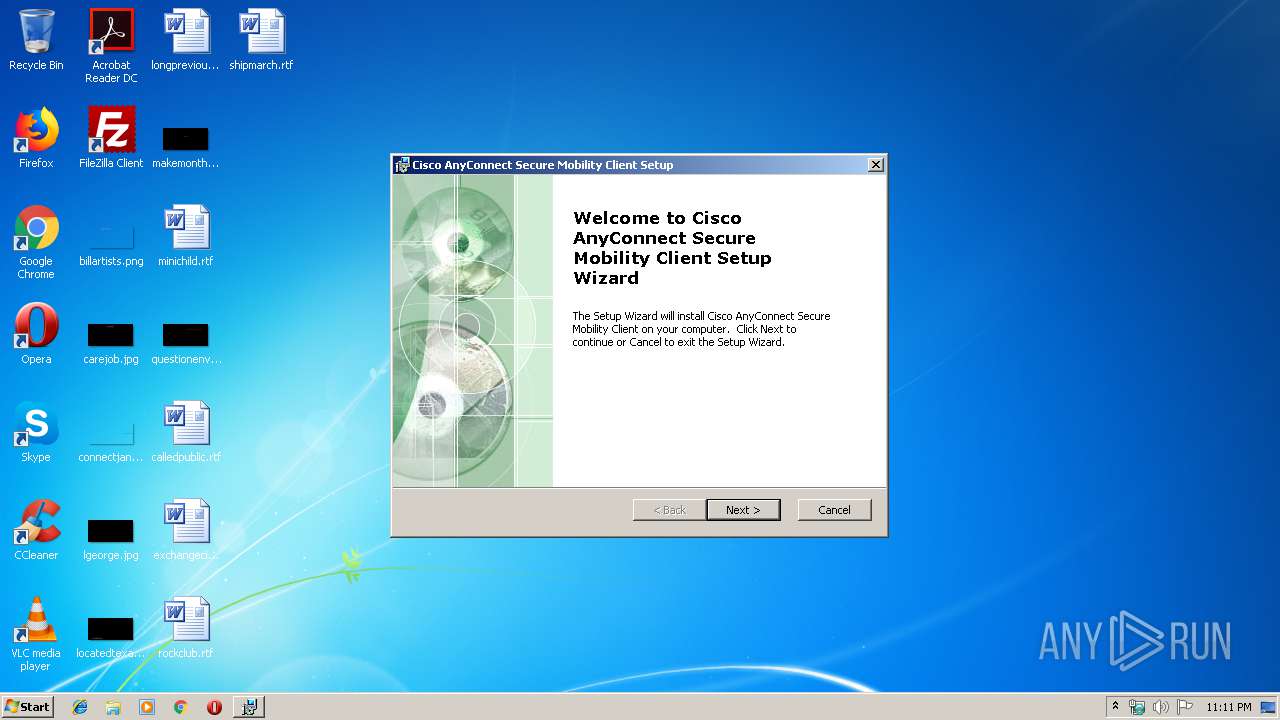
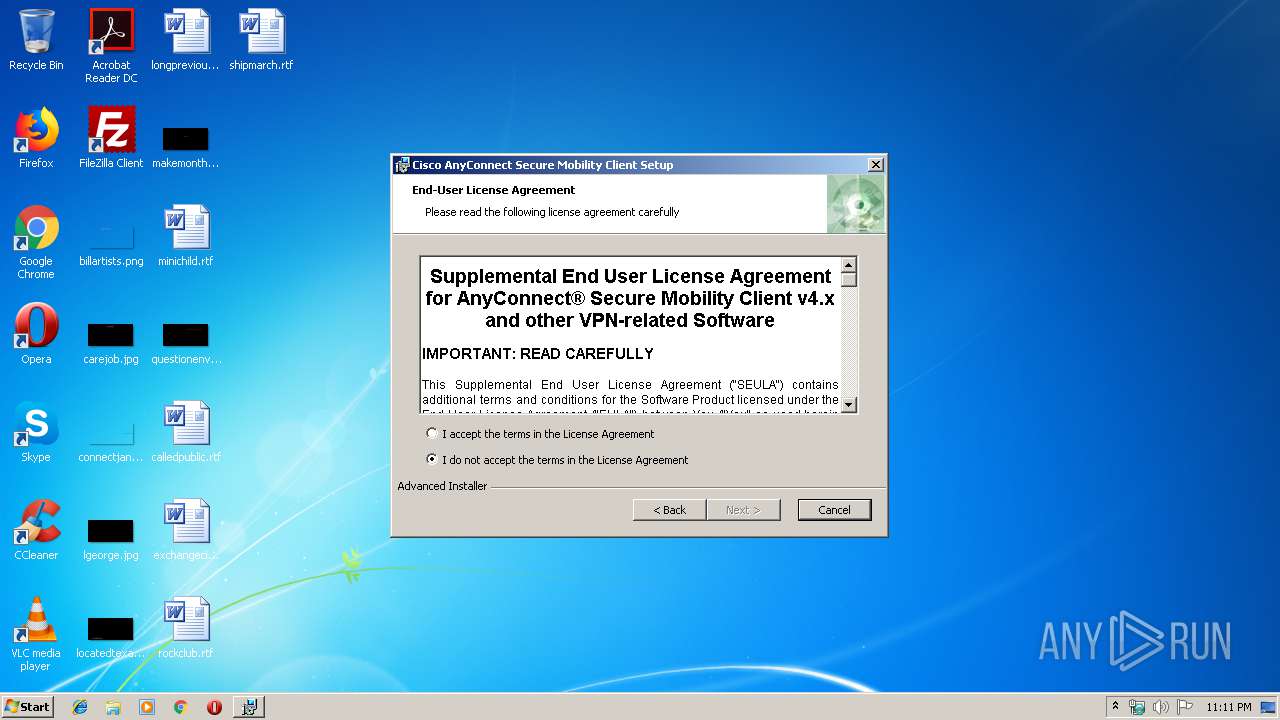
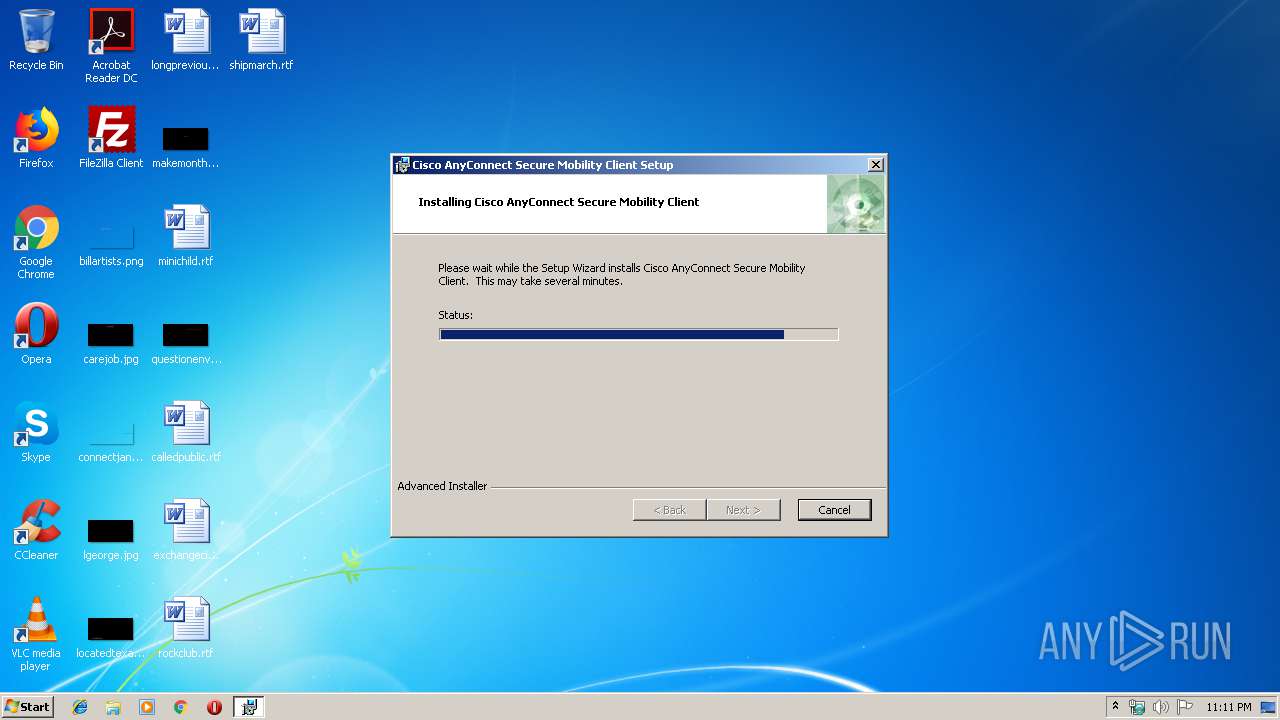
| File name: | anyconnect-win-4.5.04029-core-vpn-webdeploy-k9 (1).exe |
| Full analysis: | https://app.any.run/tasks/c7915b3b-0315-4676-8fda-79fcfee5509d |
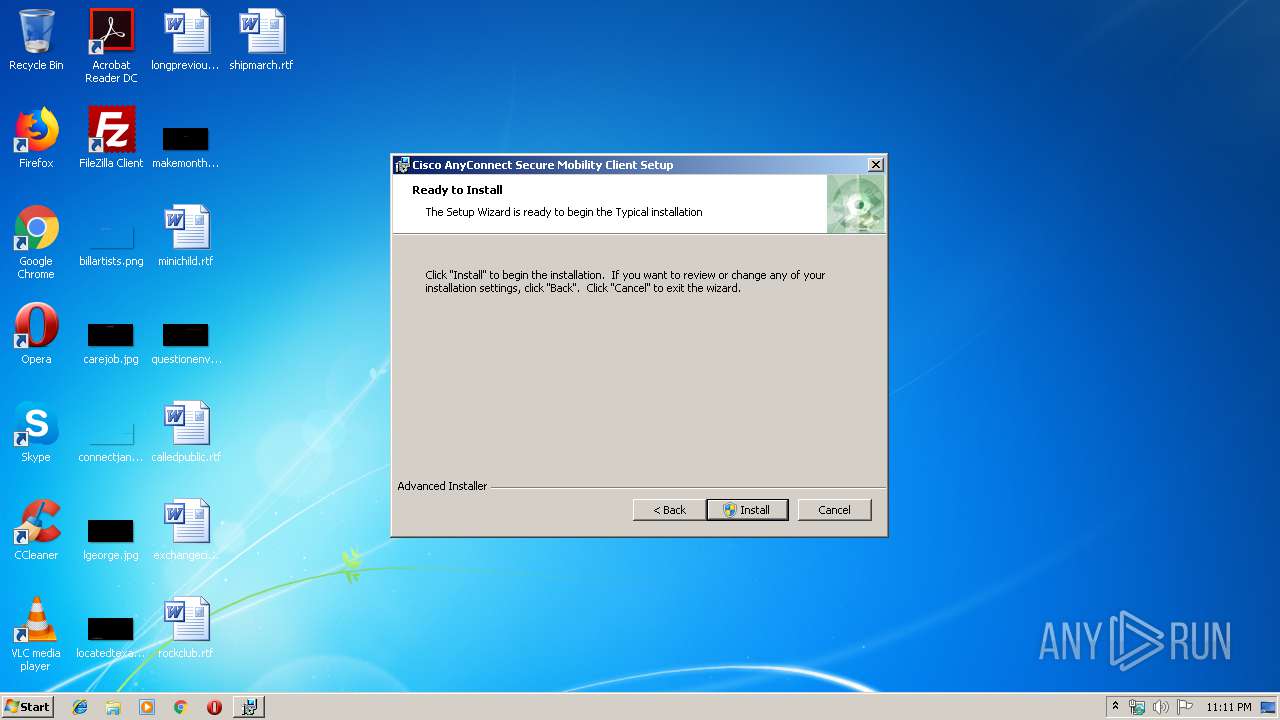
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2019, 22:10:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C89B28B83256CB139A0A3D0BC24DF051 |
| SHA1: | FC99E14C6159DF4FEE9905B4279656CE4998B3E1 |
| SHA256: | BFFFBACC952AE8FFC5C748FE2C0315A3C4119D0127F5E1404AB448A3649DBC25 |
| SSDEEP: | 98304:4cJCfsi0s2R+/nJMYPkjuziheUScKVNUJIRe4mXdUA18Ky5/JAm++/OVSGQn:4cZ3s2R+/nJMYuuzWVSXyIRezlg5RykF |
MALICIOUS
Loads dropped or rewritten executable
- anyconnect-win-4.5.04029-core-vpn-webdeploy-k9 (1).exe (PID: 2956)
- InstallHelper.exe (PID: 3716)
- InstallHelper.exe (PID: 1908)
- InstallHelper.exe (PID: 2108)
- VACon.exe (PID: 2076)
- InstallHelper.exe (PID: 3620)
- InstallHelper.exe (PID: 2168)
- InstallHelper.exe (PID: 328)
- vpnagent.exe (PID: 2548)
- VACon.exe (PID: 1252)
- InstallHelper.exe (PID: 2204)
- InstallHelper.exe (PID: 2924)
Application was dropped or rewritten from another process
- InstallHelper.exe (PID: 2108)
- InstallHelper.exe (PID: 1908)
- InstallHelper.exe (PID: 3716)
- InstallHelper.exe (PID: 3620)
- InstallHelper.exe (PID: 328)
- InstallHelper.exe (PID: 2168)
- VACon.exe (PID: 2076)
- vpnagent.exe (PID: 2548)
- VACon.exe (PID: 1252)
- InstallHelper.exe (PID: 2204)
- InstallHelper.exe (PID: 2924)
- InstallHelper.exe (PID: 2784)
Changes the autorun value in the registry
- VACon.exe (PID: 2076)
- vpnagent.exe (PID: 2548)
Tries to delete the host file
- vpnagent.exe (PID: 2548)
SUSPICIOUS
Executable content was dropped or overwritten
- anyconnect-win-4.5.04029-core-vpn-webdeploy-k9 (1).exe (PID: 2956)
- msiexec.exe (PID: 2392)
- VACon.exe (PID: 2076)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 2056)
Executed as Windows Service
- vssvc.exe (PID: 284)
- vpnagent.exe (PID: 2548)
Creates files in the Windows directory
- msiexec.exe (PID: 2392)
- VACon.exe (PID: 2076)
- vpnagent.exe (PID: 2548)
- DrvInst.exe (PID: 3872)
- DrvInst.exe (PID: 1792)
Changes the autorun value in the registry
- msiexec.exe (PID: 2392)
Creates COM task schedule object
- InstallHelper.exe (PID: 328)
Removes files from Windows directory
- VACon.exe (PID: 2076)
- vpnagent.exe (PID: 2548)
- DrvInst.exe (PID: 3872)
- DrvInst.exe (PID: 1792)
Creates files in the driver directory
- VACon.exe (PID: 2076)
- vpnagent.exe (PID: 2548)
- DrvInst.exe (PID: 3872)
- DrvInst.exe (PID: 1792)
Creates files in the program directory
- InstallHelper.exe (PID: 2204)
Executed via COM
- DrvInst.exe (PID: 3872)
- DrvInst.exe (PID: 1792)
- rundll32.exe (PID: 3172)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 892)
- MsiExec.exe (PID: 3832)
Application launched itself
- msiexec.exe (PID: 2392)
Searches for installed software
- msiexec.exe (PID: 2392)
Low-level read access rights to disk partition
- vssvc.exe (PID: 284)
Dropped object may contain Bitcoin addresses
- anyconnect-win-4.5.04029-core-vpn-webdeploy-k9 (1).exe (PID: 2956)
- msiexec.exe (PID: 2392)
Creates or modifies windows services
- msiexec.exe (PID: 2392)
Creates a software uninstall entry
- msiexec.exe (PID: 2392)
Creates files in the program directory
- msiexec.exe (PID: 2392)
Reads the hosts file
- vpnagent.exe (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:11:15 17:17:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 256000 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x272c9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5.4029.0 |
| ProductVersionNumber: | 4.5.4029.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Cisco Systems, Inc. |
| FileDescription: | A SmartNET contract is required for support - Cisco AnyConnect Secure Mobility Client. |
| FileVersion: | 4.5.04029 |
| InternalName: | WinSetup-Release-web-deploy |
| LegalCopyright: | Copyright (C) 2018 Cisco Systems, Inc. |
| OriginalFileName: | WinSetup-Release-web-deploy.exe |
| ProductName: | Cisco AnyConnect Secure Mobility Client |
| ProductVersion: | 4.5.04029 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2016 16:17:16 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Cisco Systems, Inc. |
| FileDescription: | A SmartNET contract is required for support - Cisco AnyConnect Secure Mobility Client. |
| FileVersion: | 4.5.04029 |
| InternalName: | WinSetup-Release-web-deploy |
| LegalCopyright: | Copyright (C) 2018 Cisco Systems, Inc. |
| OriginalFileName: | WinSetup-Release-web-deploy.exe |
| ProductName: | Cisco AnyConnect Secure Mobility Client |
| ProductVersion: | 4.5.04029 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 15-Nov-2016 16:17:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003E720 | 0x0003E800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62814 |
.rdata | 0x00040000 | 0x00012294 | 0x00012400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67103 |
.data | 0x00053000 | 0x000022A4 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.31769 |
.gfids | 0x00056000 | 0x00000108 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.16534 |
.tls | 0x00057000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00058000 | 0x0000EB9C | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.05774 |
.reloc | 0x00067000 | 0x00003C0C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60409 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.34109 | 1000 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
66
Monitored processes
27
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe" -registerdll "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\vpnapi.dll" | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe | — | msiexec.exe | |||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Install Helper Exit code: 0 Version: 4, 5, 04029 Modules
| |||||||||||||||
| 892 | C:\Windows\system32\MsiExec.exe -Embedding A0E15EC0DBB20512DC1517E960F55932 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | /C "C:\Users\admin\AppData\Local\Temp\{8DE4FAAB-4C4F-4383-8747-4EDB55D9DEAE}.bat" | C:\Windows\system32\cmd.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\VACon.exe" -install "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\vpnva-6.inf" VPNVA | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\VACon.exe | msiexec.exe | ||||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Virtual Adapter Installer Exit code: 0 Version: 4, 5, 04029 Modules
| |||||||||||||||
| 1792 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\Windows\INF\oem4.inf" "vpnva-6.inf:Cisco:Cisco.ndi.NTx86:4.5.4025.0:vpnva" "658dd218b" "000003E4" "000005E0" "000005E4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe" -moveIfExist "C:\Users\admin\AppData\Local\\Cisco\Cisco AnyConnect VPN Client\preferences.xml" "C:\Users\admin\AppData\Local\Cisco\Cisco AnyConnect Secure Mobility Client\\preferences.xml" | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe | — | msiexec.exe | |||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Install Helper Exit code: 0 Version: 4, 5, 04029 Modules
| |||||||||||||||
| 2056 | C:\Windows\system32\MsiExec.exe -Embedding 38FCE9B62E49B7C771D0145C236E31E5 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\VACon.exe" kdf -install "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\\" acsock | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\VACon.exe | msiexec.exe | ||||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Virtual Adapter Installer Exit code: 0 Version: 4, 5, 04029 Modules
| |||||||||||||||
| 2104 | /C "C:\Users\admin\AppData\Local\Temp\{8DE4FAAB-4C4F-4383-8747-4EDB55D9DEAE}.bat" | C:\Windows\system32\cmd.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 755
Read events
899
Write events
811
Delete events
45
Modification events
| (PID) Process: | (2816) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2816) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2816) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2816) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2816) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2816) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000026CE64D63785D50158090000340F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000026CE64D63785D50158090000340F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (284) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008267BFD63785D5011C01000084010000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (284) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008267BFD63785D5011C010000AC0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
164
Suspicious files
13
Text files
187
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | anyconnect-win-4.5.04029-core-vpn-webdeploy-k9 (1).exe | C:\Users\admin\AppData\Local\Temp\Cisco\Installer\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2816 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB1B6.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB254.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB274.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB2D3.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 284 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2392 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF680FF94D137DDDF5.TMP | — | |
MD5:— | SHA256:— | |||
| 2392 | msiexec.exe | C:\Windows\Installer\MSI2C09.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | msiexec.exe | C:\Windows\Installer\MSI2D23.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2548 | vpnagent.exe | GET | — | 72.163.1.80:80 | http://72.163.1.80/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 72.163.1.80:80 | mus.cisco.com | Cisco Systems, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mus.cisco.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MsiExec.exe | DBGHELP: Symbol Search Path: .
|
MsiExec.exe | DBGHELP: Symbol Search Path: C:\Windows\system32
|
MsiExec.exe | DBGHELP: SymSrv load failure: symsrv.dll
|
MsiExec.exe | DBGHELP: C:\Windows\system32\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: C:\Windows\system32\dll\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: C:\Windows\system32\symbols\dll\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: ntdll - export symbols
|
VACon.exe | VACON: -install
|