| File name: | 3ca3579e3a2a66f494bcb72adc576482.bat |
| Full analysis: | https://app.any.run/tasks/549e0ea6-eeb8-43a8-9ada-fb09488bb8a6 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 11:21:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2978B9AF6D7985ECBEEDF8E3CBC5F6F3 |
| SHA1: | 58D74DA45259396B1E43A10B6736C5CA7443ACC4 |
| SHA256: | BFF1B31DF5D7BD5DA7F80E84D094AFC34A4E96BB08DDC5D37483C145700D91C3 |
| SSDEEP: | 12288:/UBgyoyvf7UziRXlQM9nH541EeIccPniD1kR/XlQM9nH541EeIccPniD1kR1:/UXvf7OQVQ4nZaEj+kR/VQ4nZaEj+kR1 |
MALICIOUS
Application was dropped or rewritten from another process
- 1.exe (PID: 3280)
- 2.bat (PID: 3836)
- 2.bat (PID: 2792)
- 1.exe (PID: 2812)
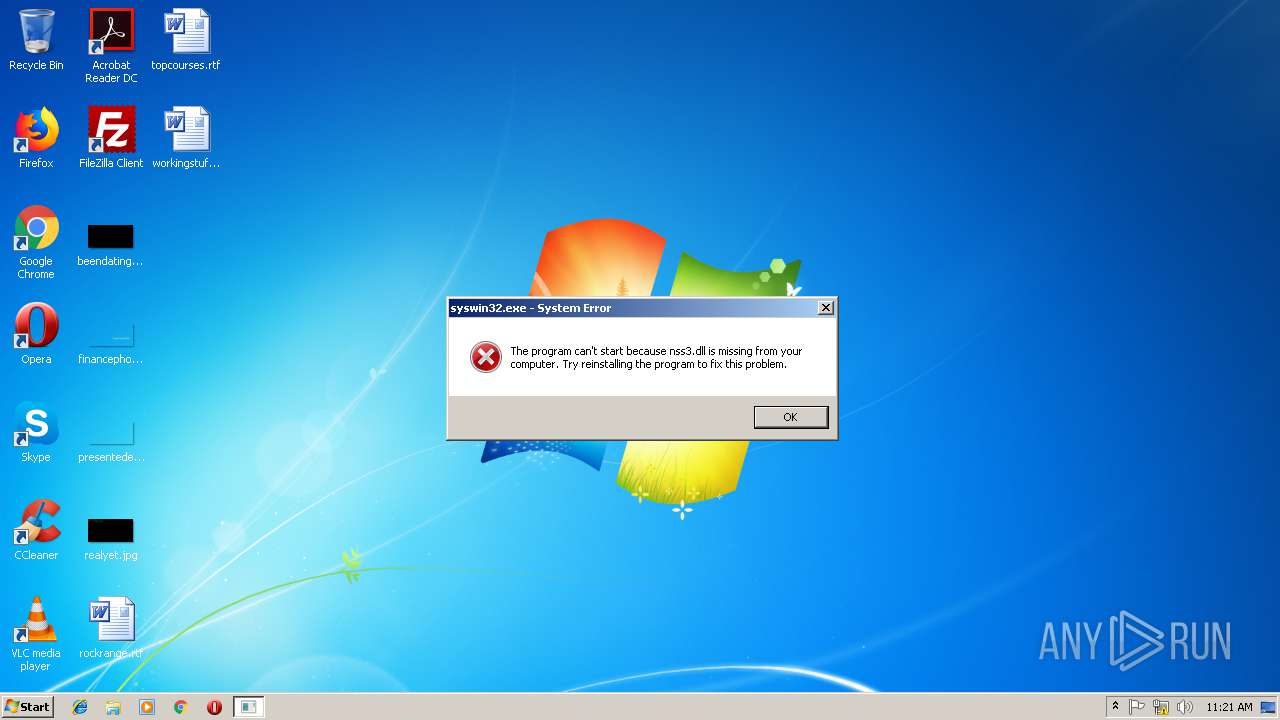
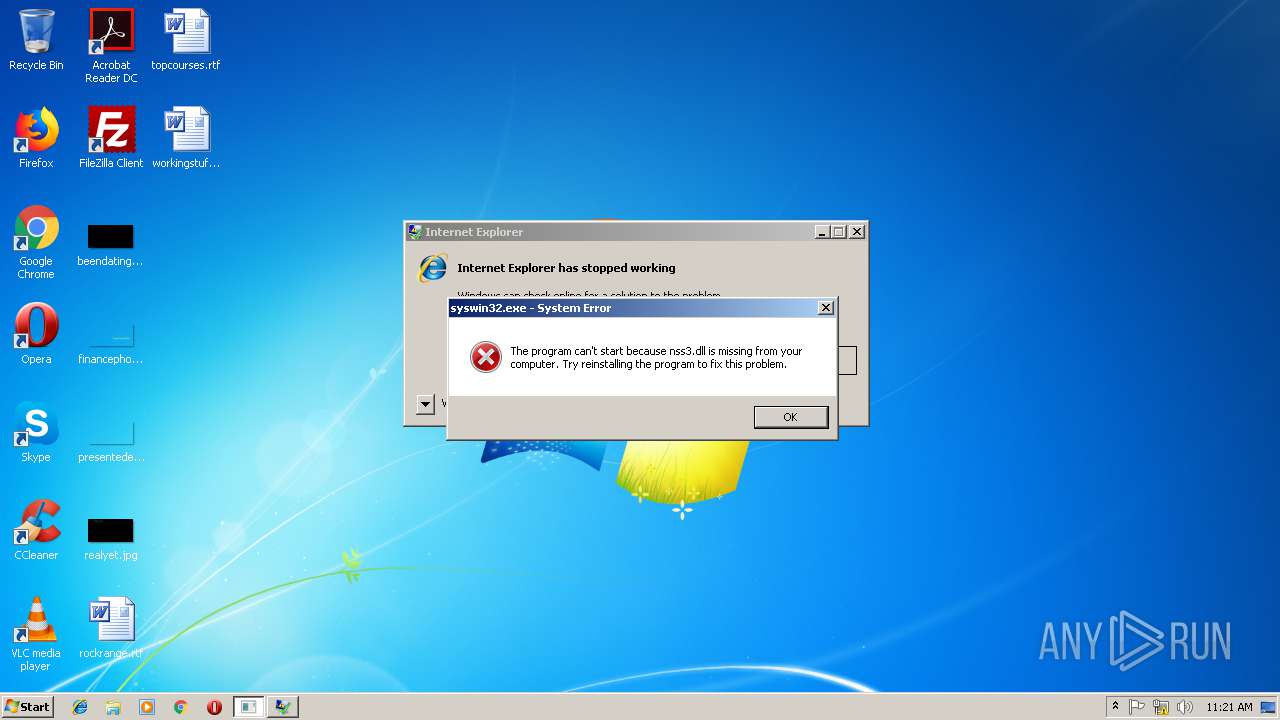
- syswin32.exe (PID: 3824)
- syswin32.exe (PID: 3212)
SUSPICIOUS
Starts application with an unusual extension
- 3ca3579e3a2a66f494bcb72adc576482.bat (PID: 3144)
- 2.bat (PID: 3836)
Executable content was dropped or overwritten
- 3ca3579e3a2a66f494bcb72adc576482.bat (PID: 3144)
- 2.bat (PID: 2792)
Suspicious files were dropped or overwritten
- 3ca3579e3a2a66f494bcb72adc576482.bat (PID: 3144)
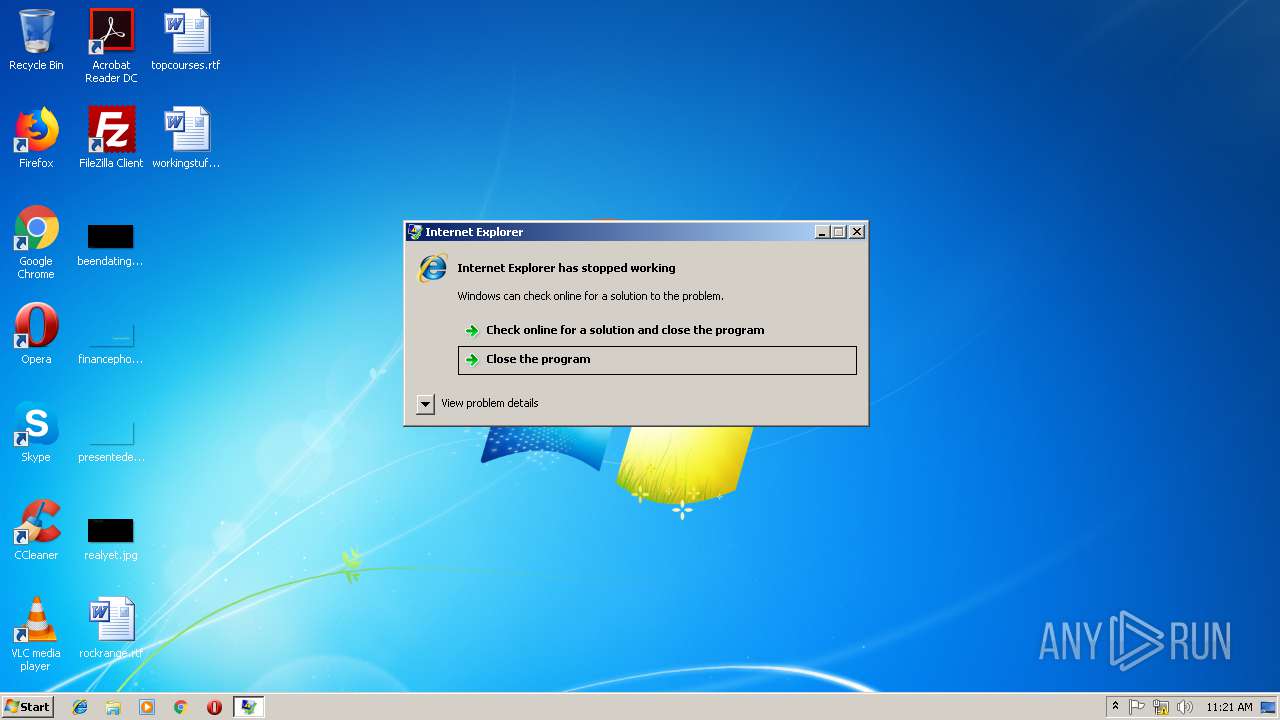
Starts Internet Explorer
- 2.bat (PID: 2792)
- 1.exe (PID: 2812)
Creates files in the user directory
- 2.bat (PID: 2792)
Application launched itself
- syswin32.exe (PID: 3824)
- taskmgr.exe (PID: 3460)
Loads DLL from Mozilla Firefox
- syswin32.exe (PID: 3212)
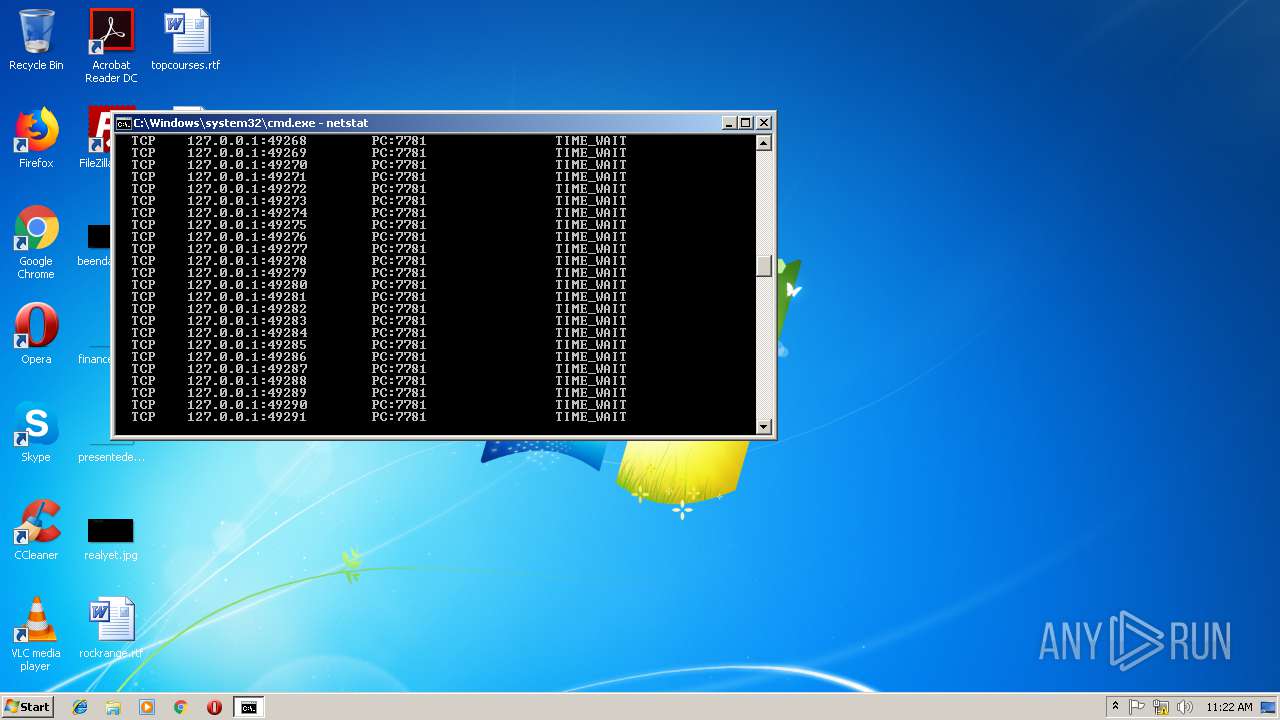
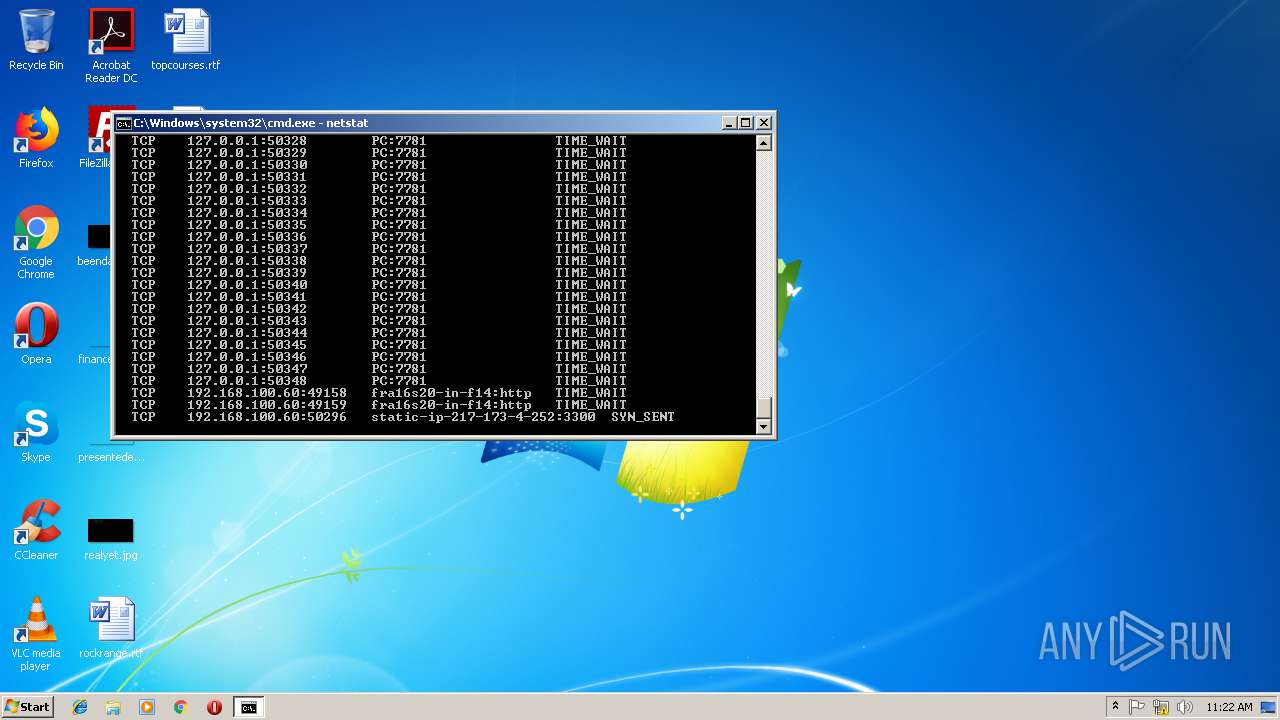
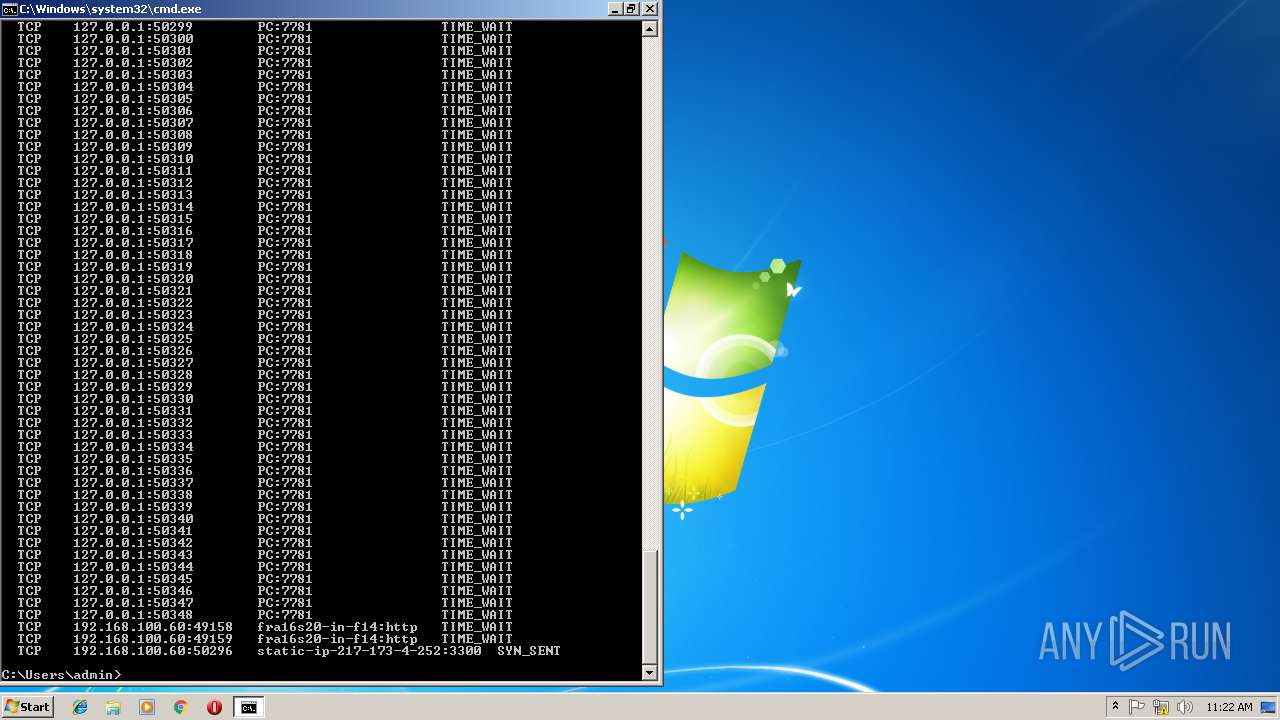
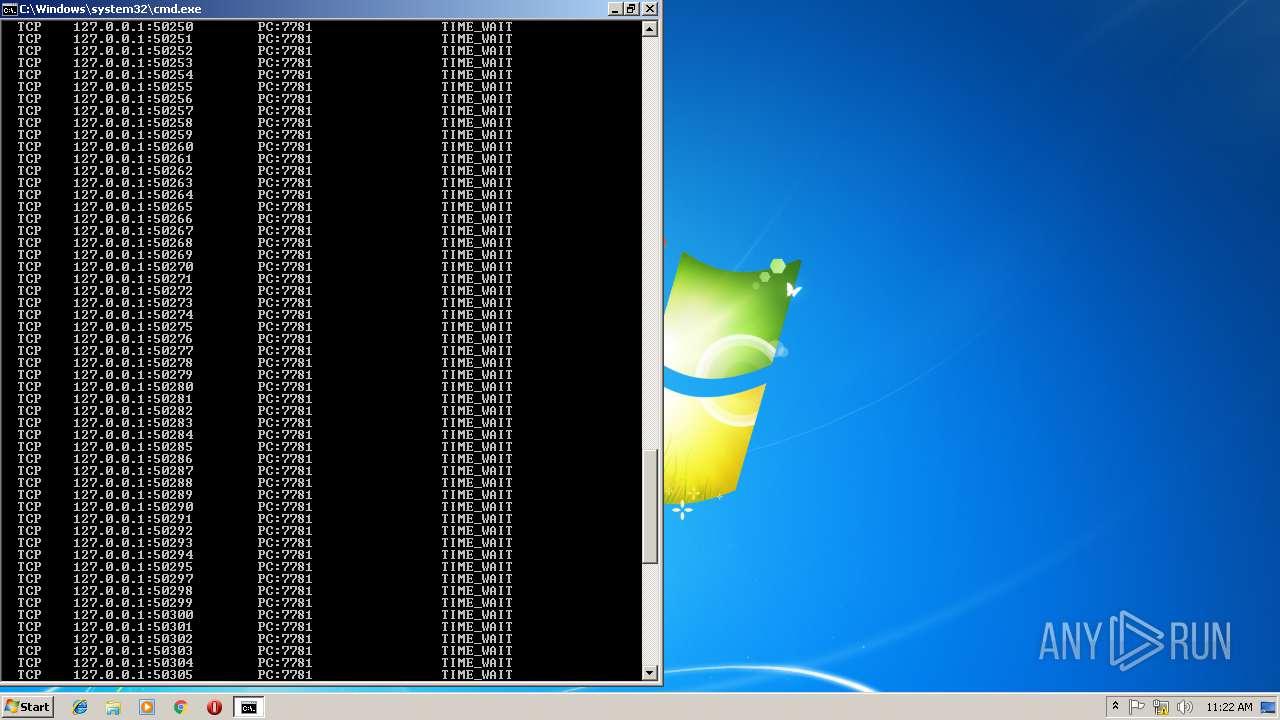
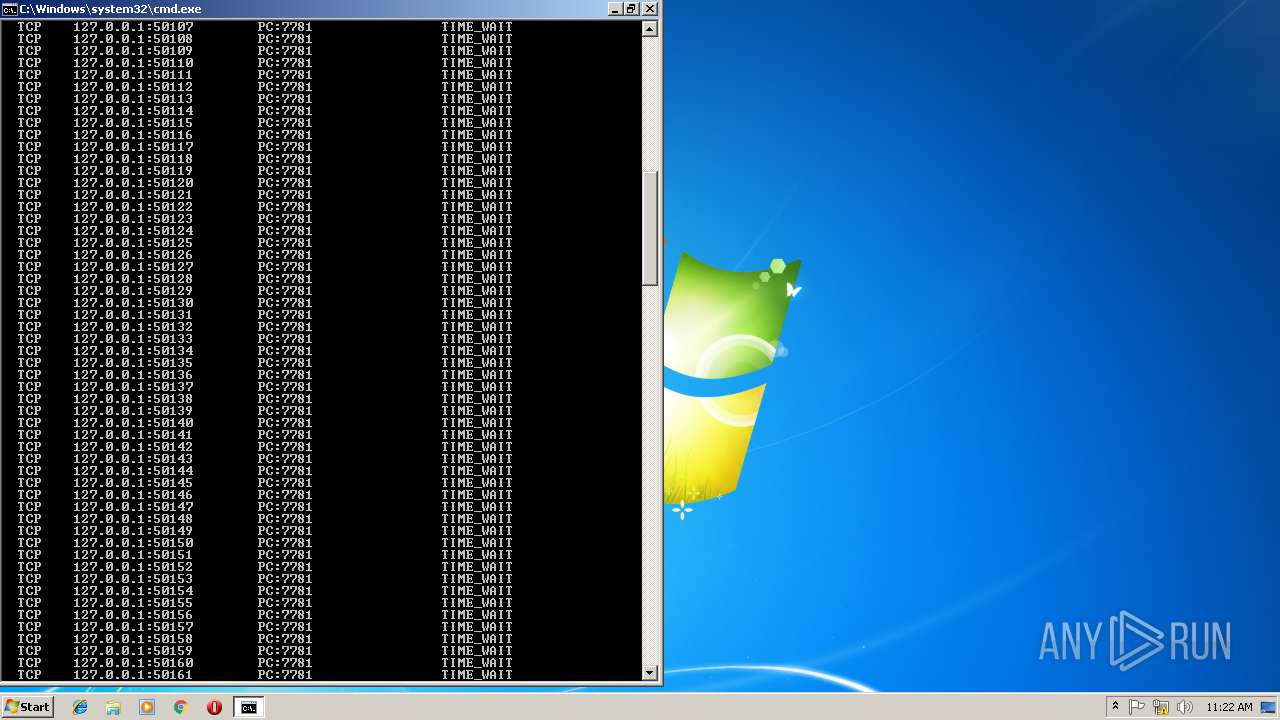
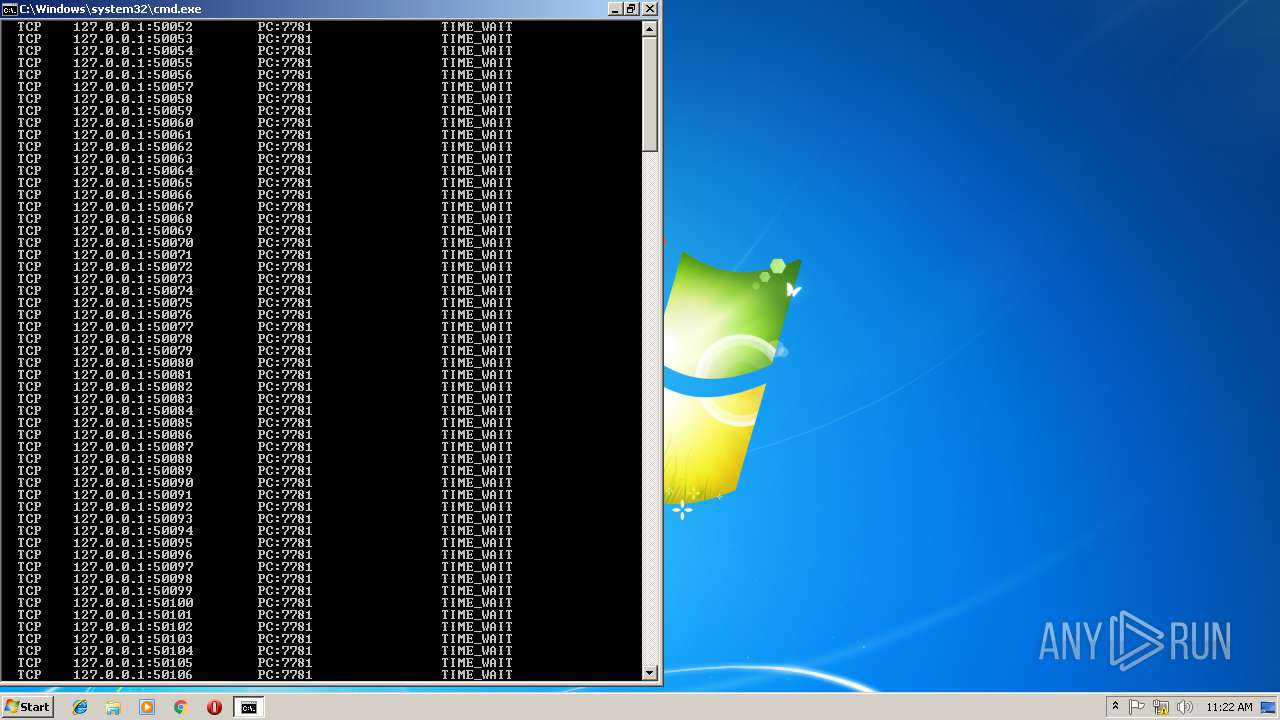
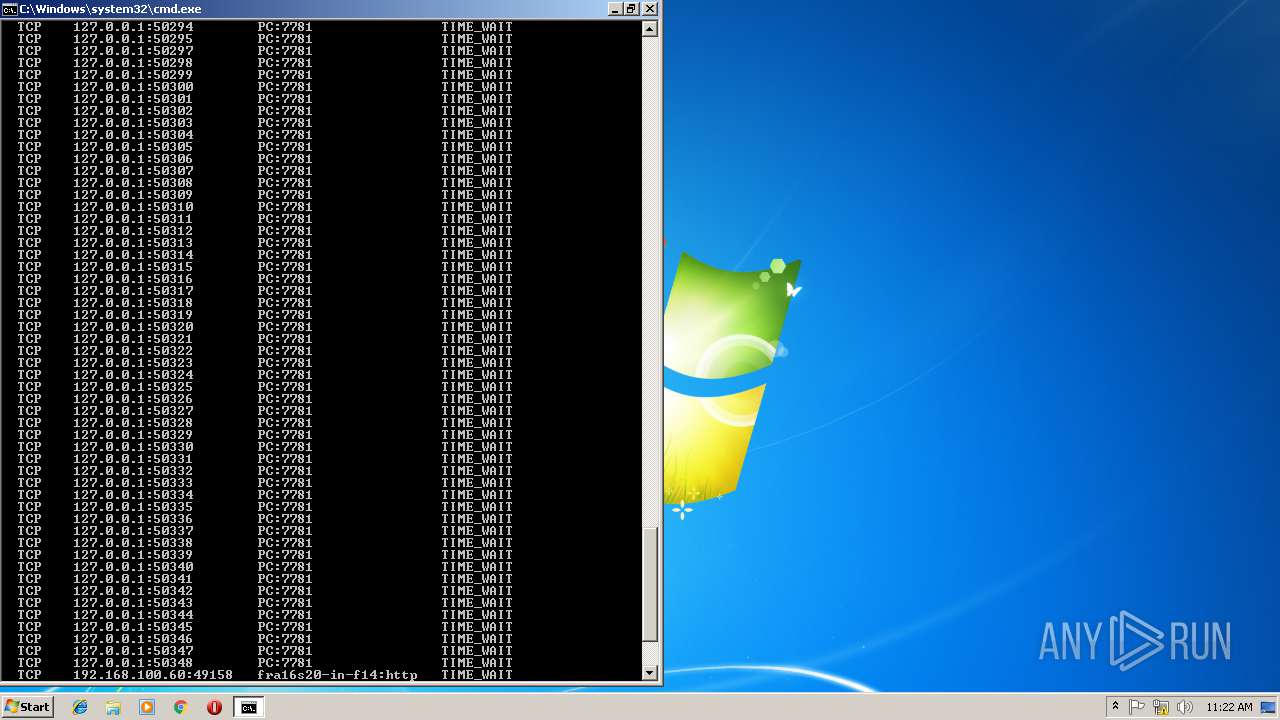
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3384)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2540)
Application was crashed
- iexplore.exe (PID: 2552)
Connects to unusual port
- iexplore.exe (PID: 2540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 135168 |
| InitializedDataSize: | 250880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xfce7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:54 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00020F77 | 0x00021000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62162 |
.rdata | 0x00022000 | 0x00008FD4 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13549 |
.data | 0x0002B000 | 0x0002D370 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.7652 |
.gfids | 0x00059000 | 0x000000FC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.16316 |
.rsrc | 0x0005A000 | 0x0000483D | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.69159 |
.reloc | 0x0005F000 | 0x00002354 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.69514 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28823 | 1873 | UNKNOWN | Polish - Poland | RT_MANIFEST |
7 | 3.41798 | 548 | UNKNOWN | Polish - Poland | RT_STRING |
8 | 3.45553 | 572 | UNKNOWN | Polish - Poland | RT_STRING |
9 | 3.47114 | 492 | UNKNOWN | Polish - Poland | RT_STRING |
10 | 3.40584 | 320 | UNKNOWN | Polish - Poland | RT_STRING |
11 | 3.53928 | 1216 | UNKNOWN | Polish - Poland | RT_STRING |
12 | 3.32935 | 368 | UNKNOWN | Polish - Poland | RT_STRING |
13 | 3.23901 | 300 | UNKNOWN | Polish - Poland | RT_STRING |
14 | 3.15623 | 264 | UNKNOWN | Polish - Poland | RT_STRING |
15 | 3.15753 | 232 | UNKNOWN | Polish - Poland | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
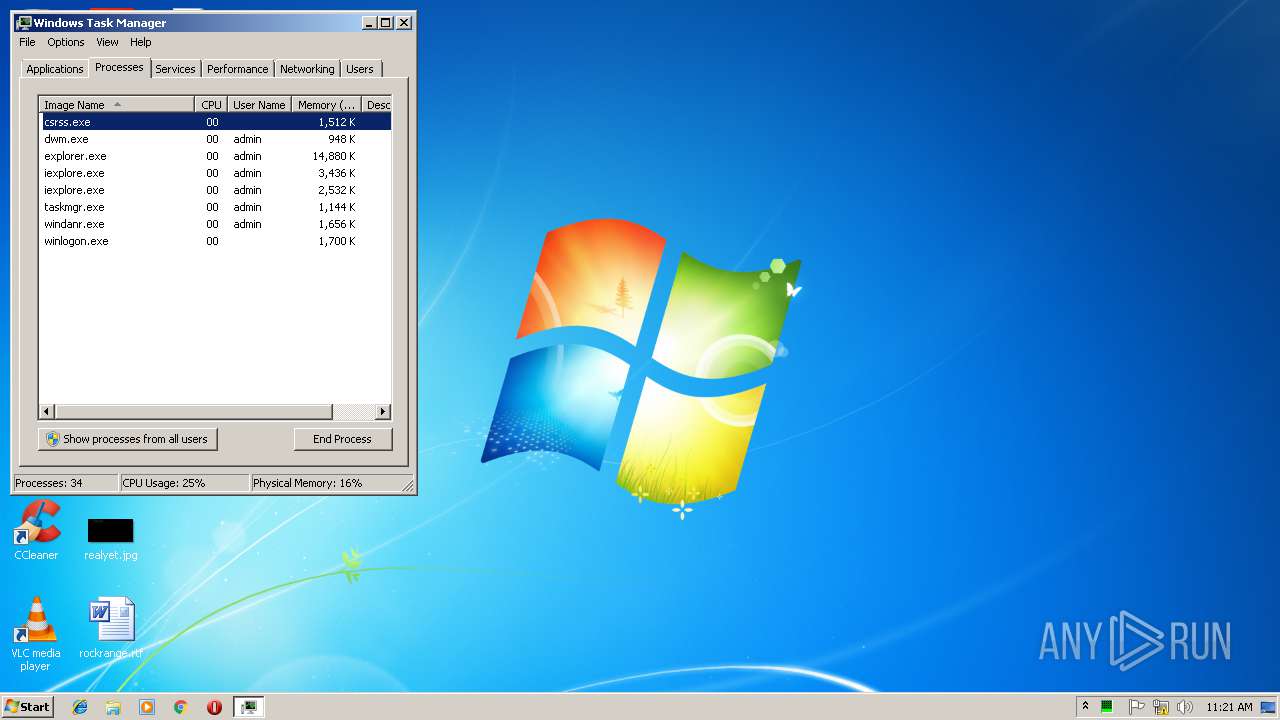
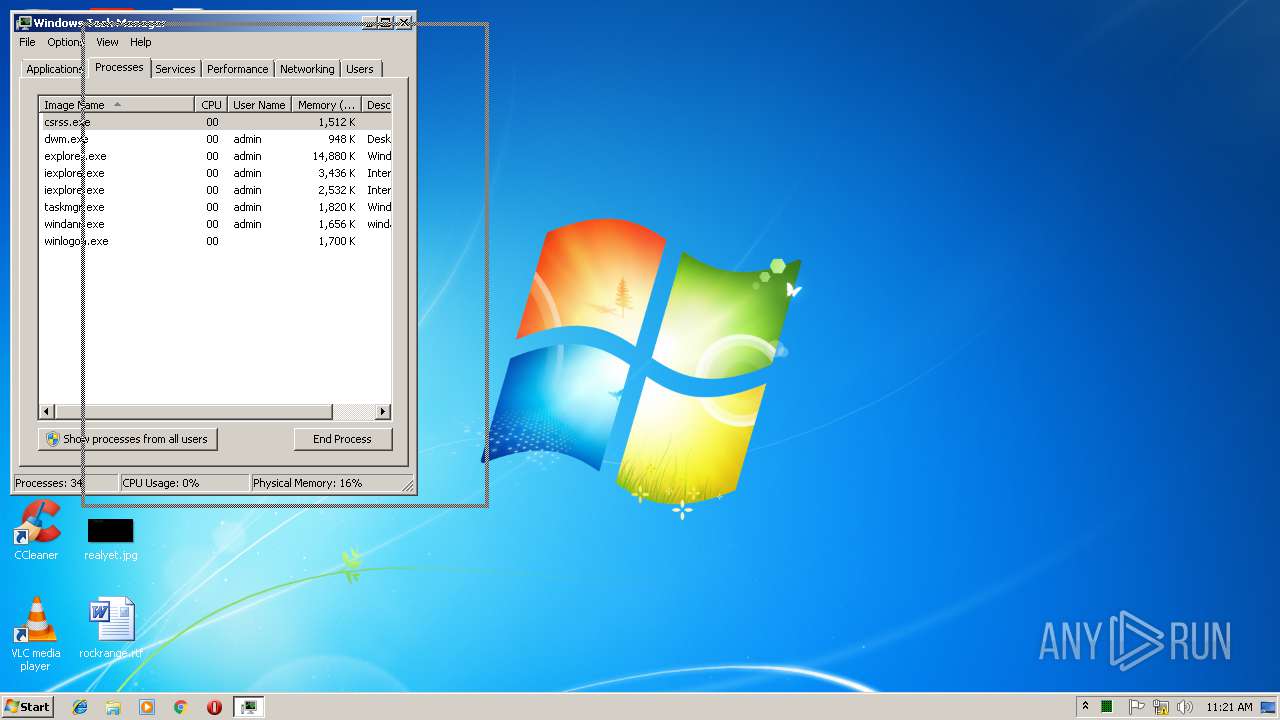
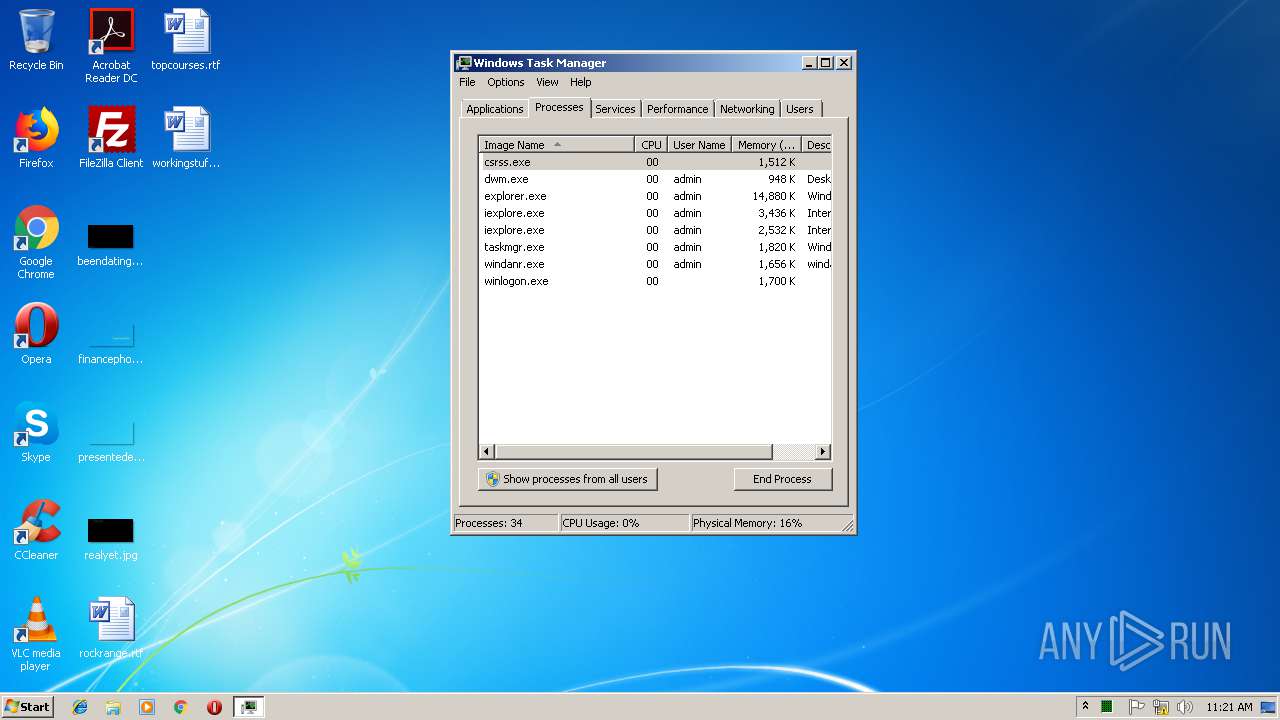
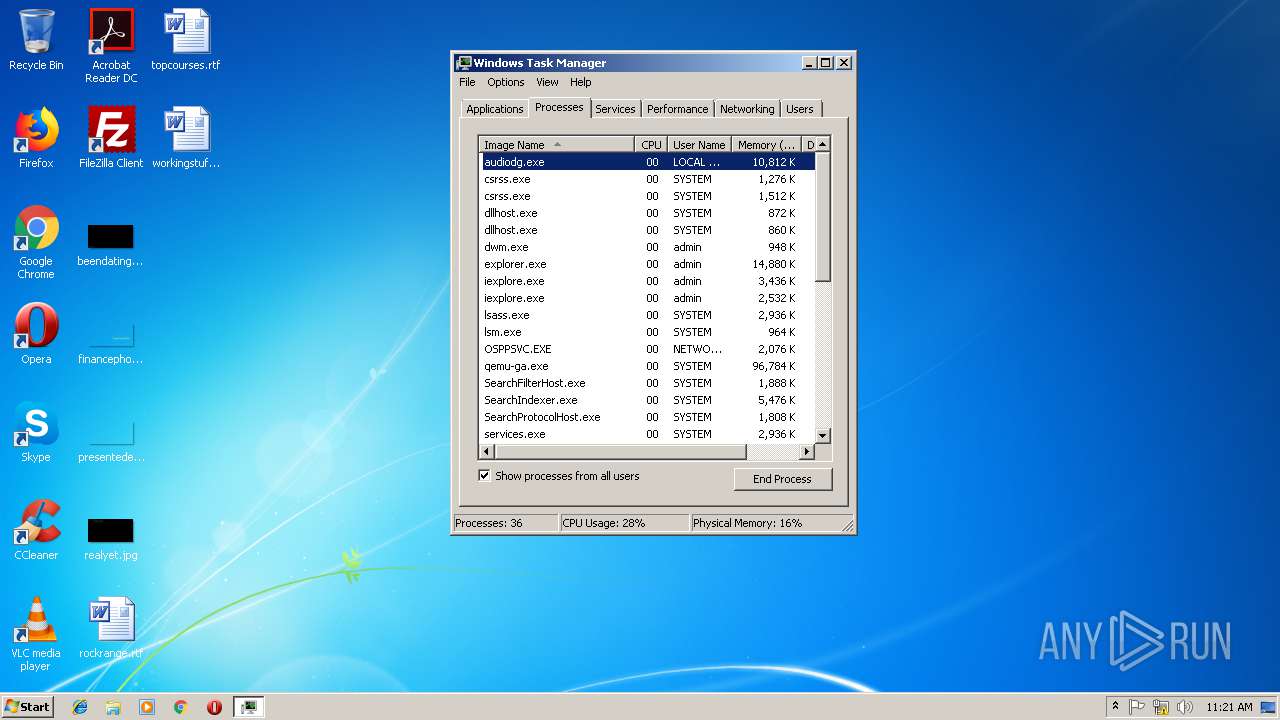
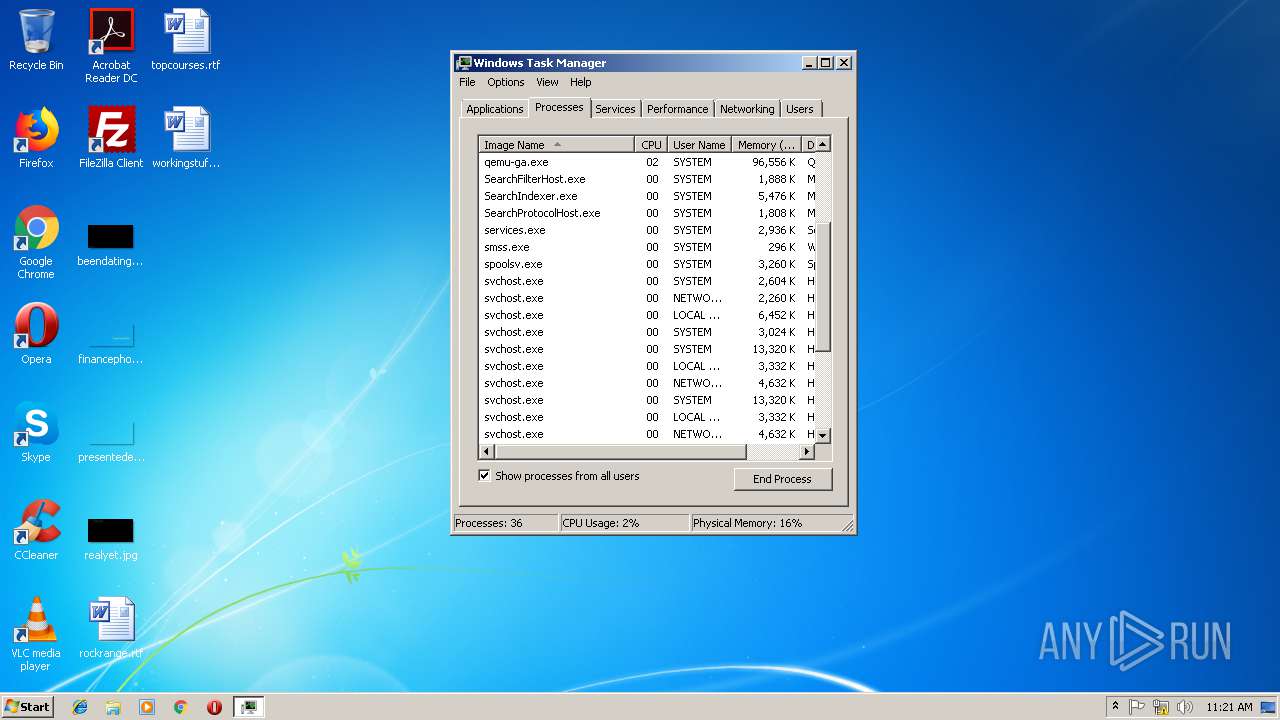
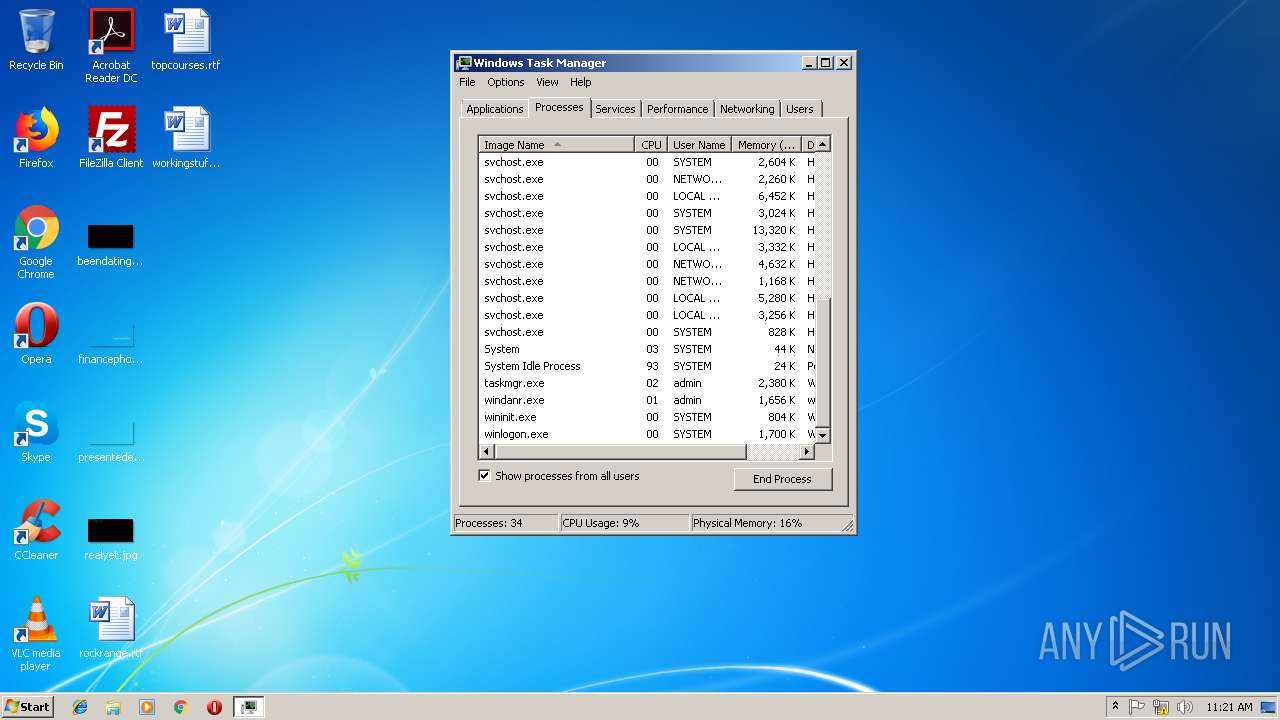
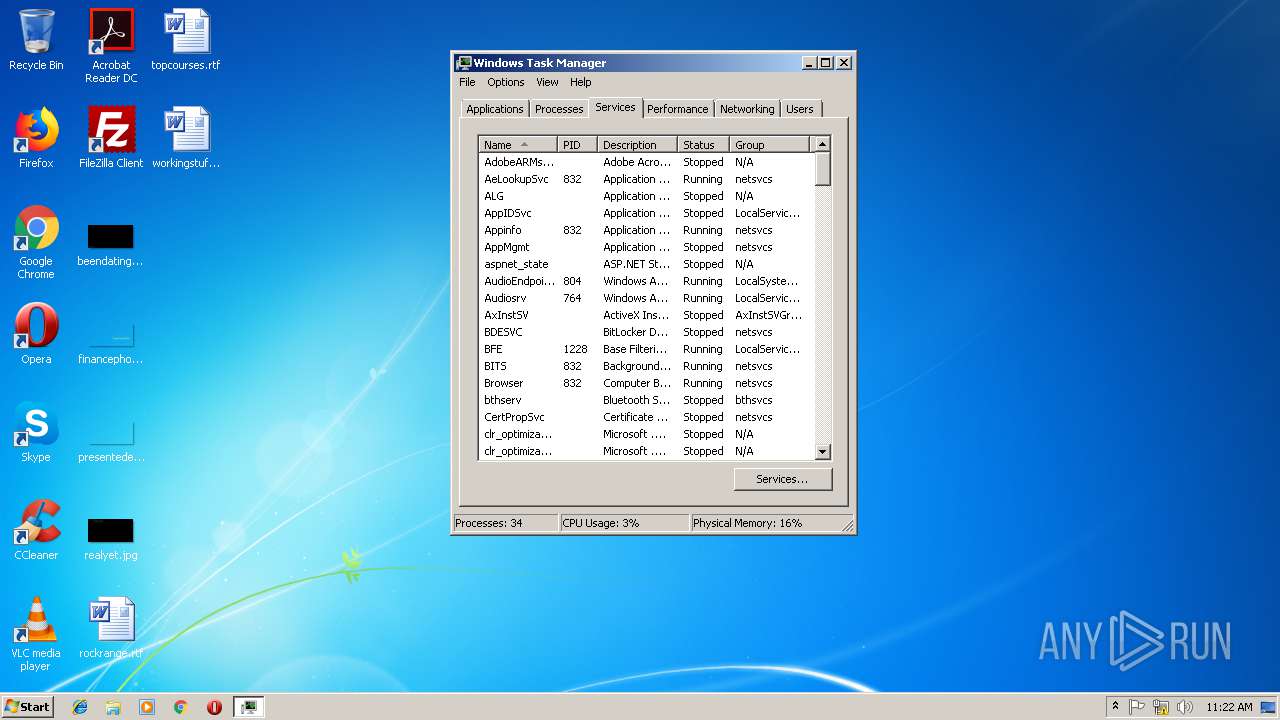
Total processes
50
Monitored processes
13
Malicious processes
2
Suspicious processes
5
Behavior graph
Click at the process to see the details
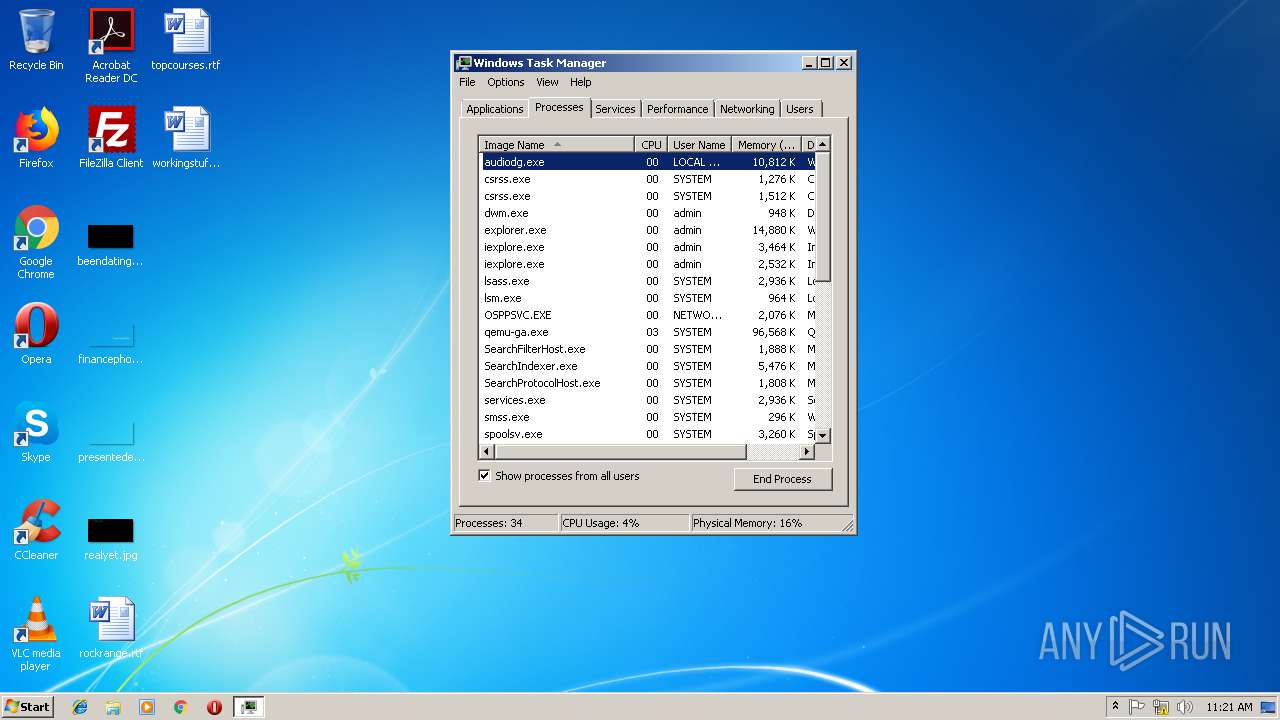
Process information
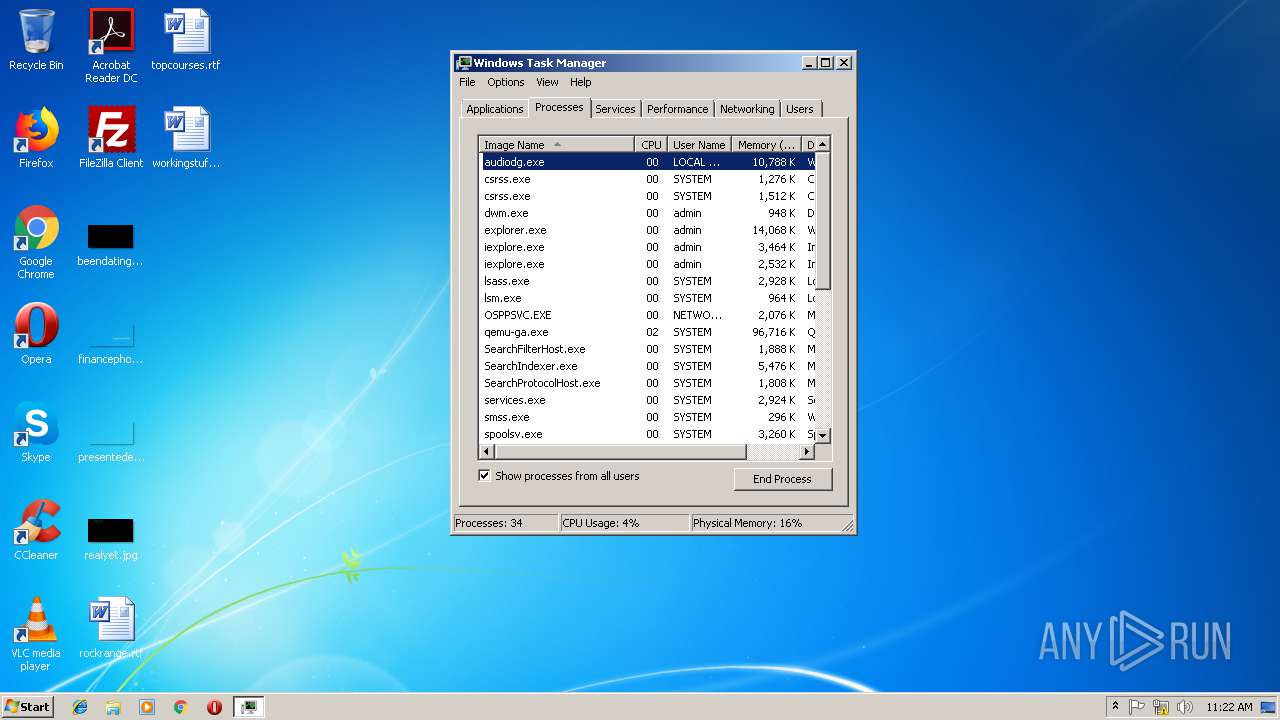
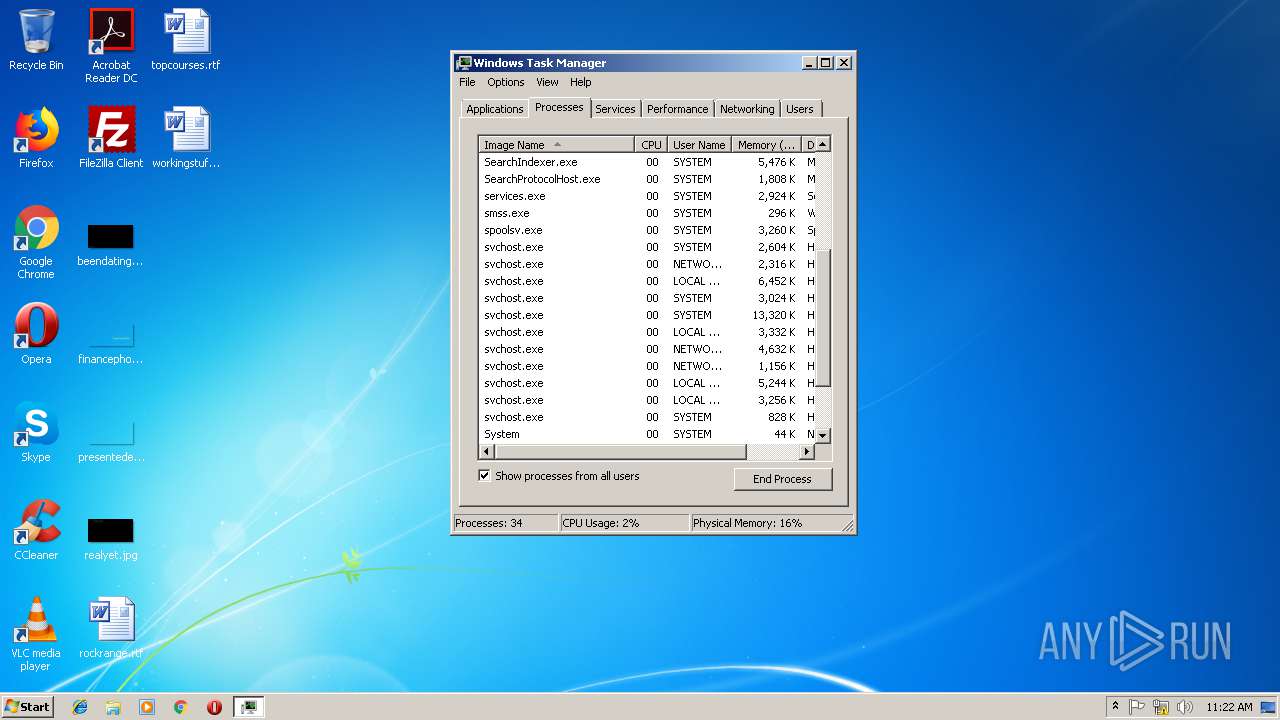
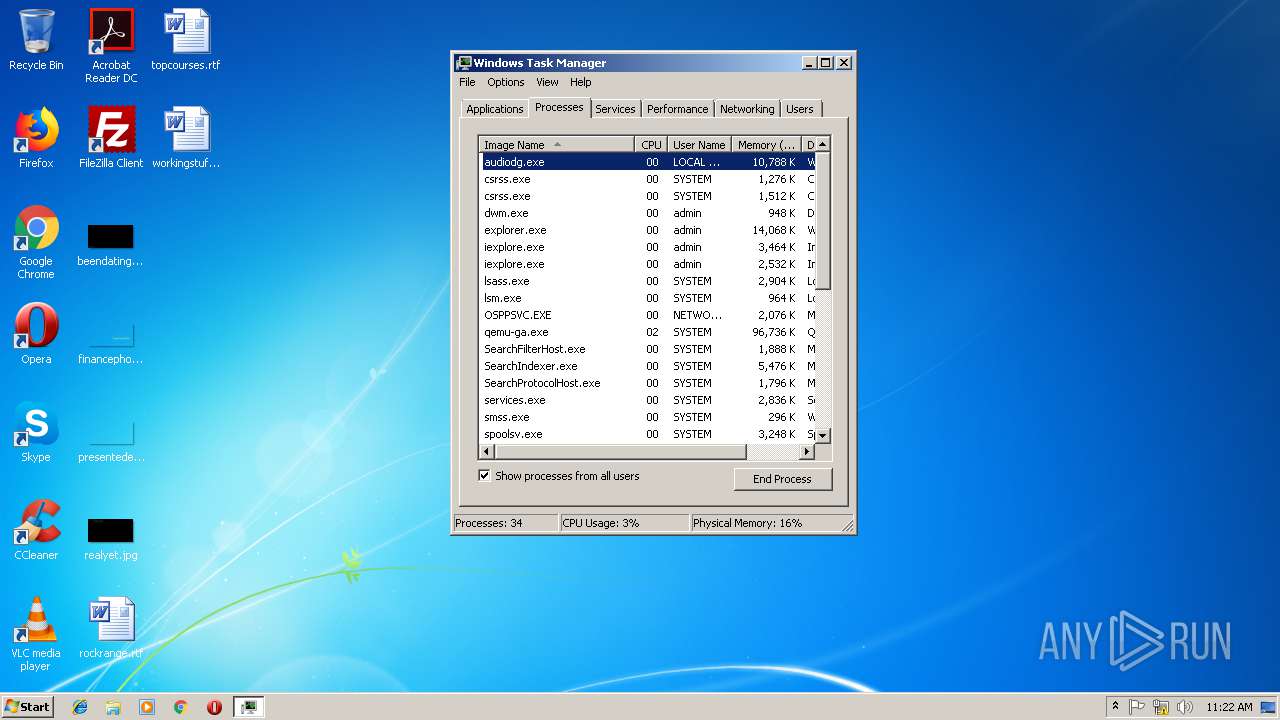
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
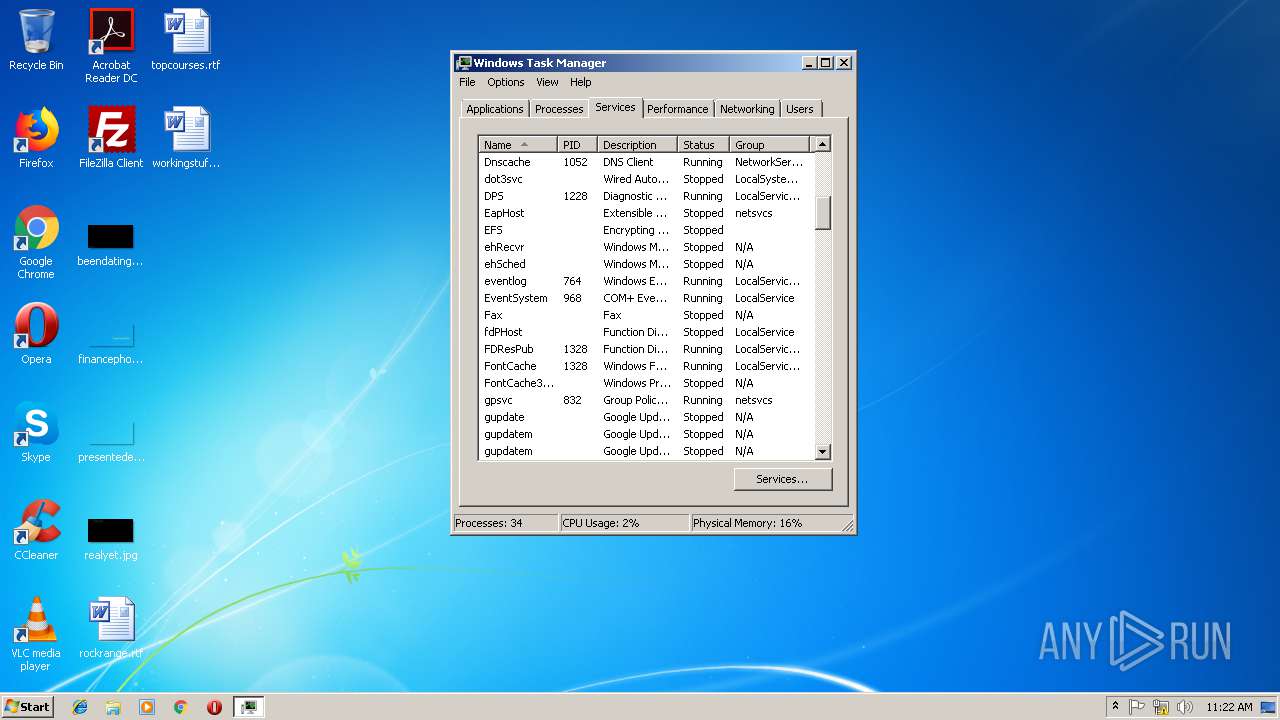
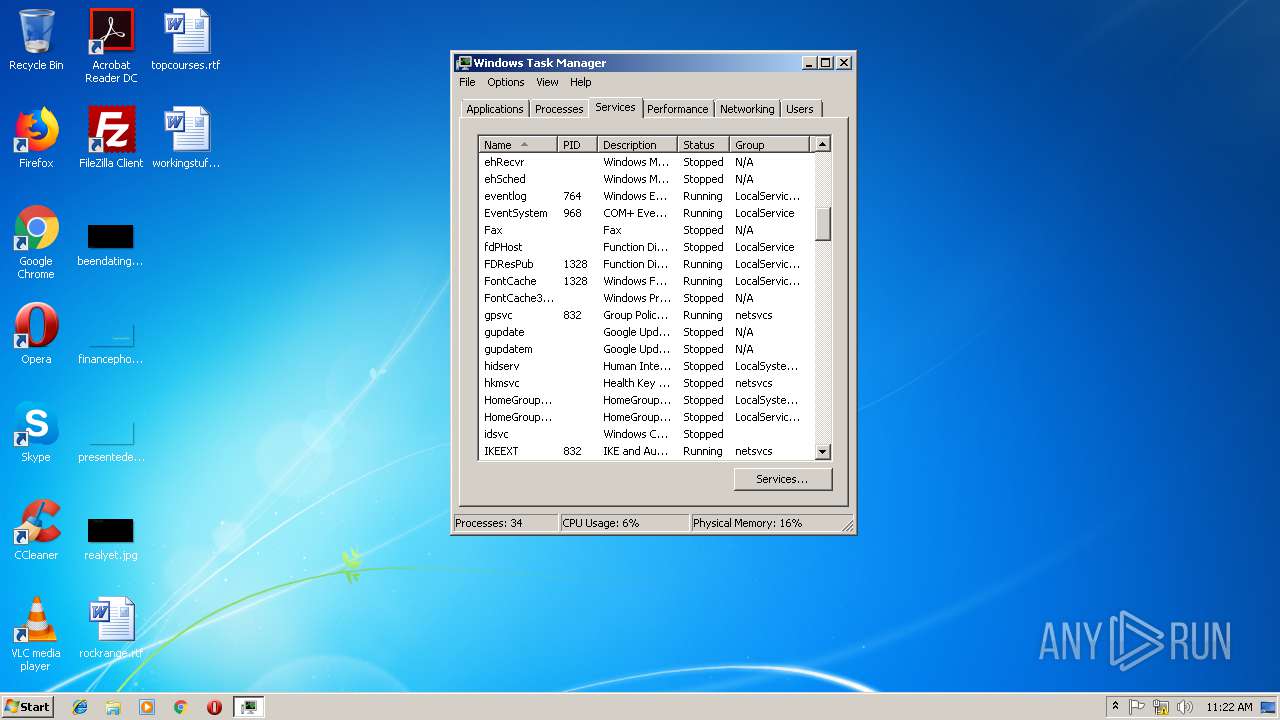
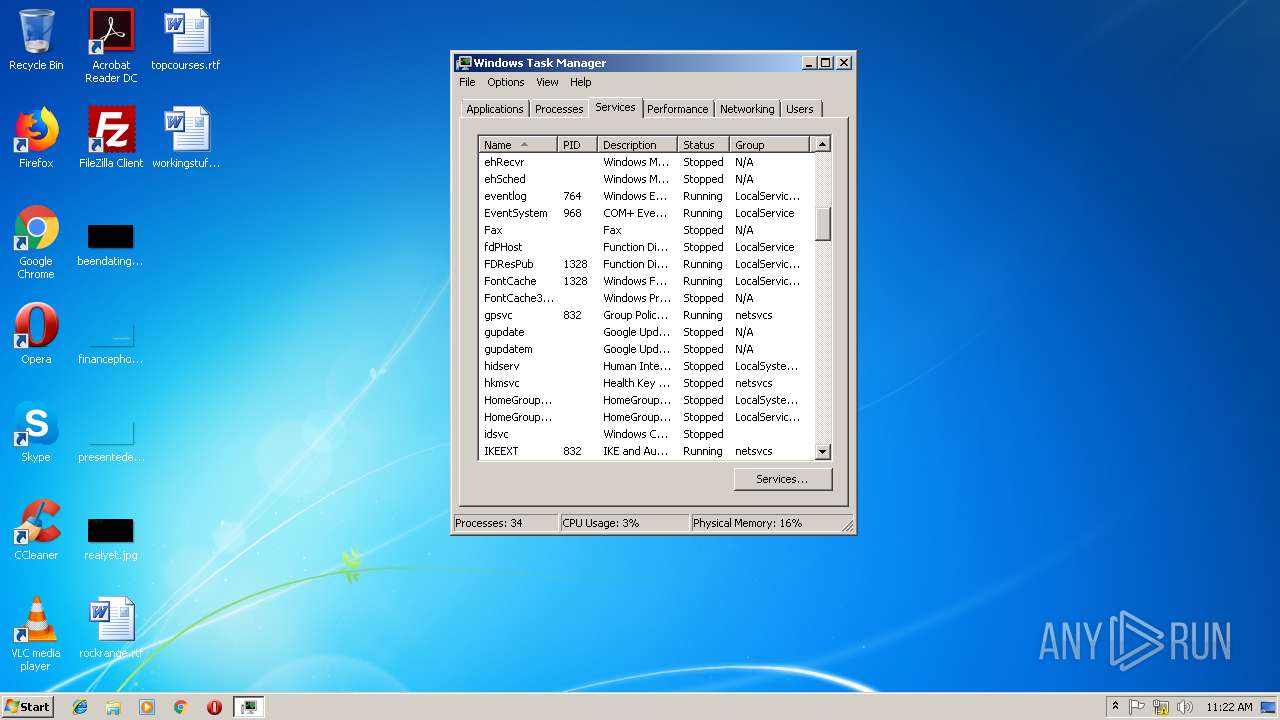
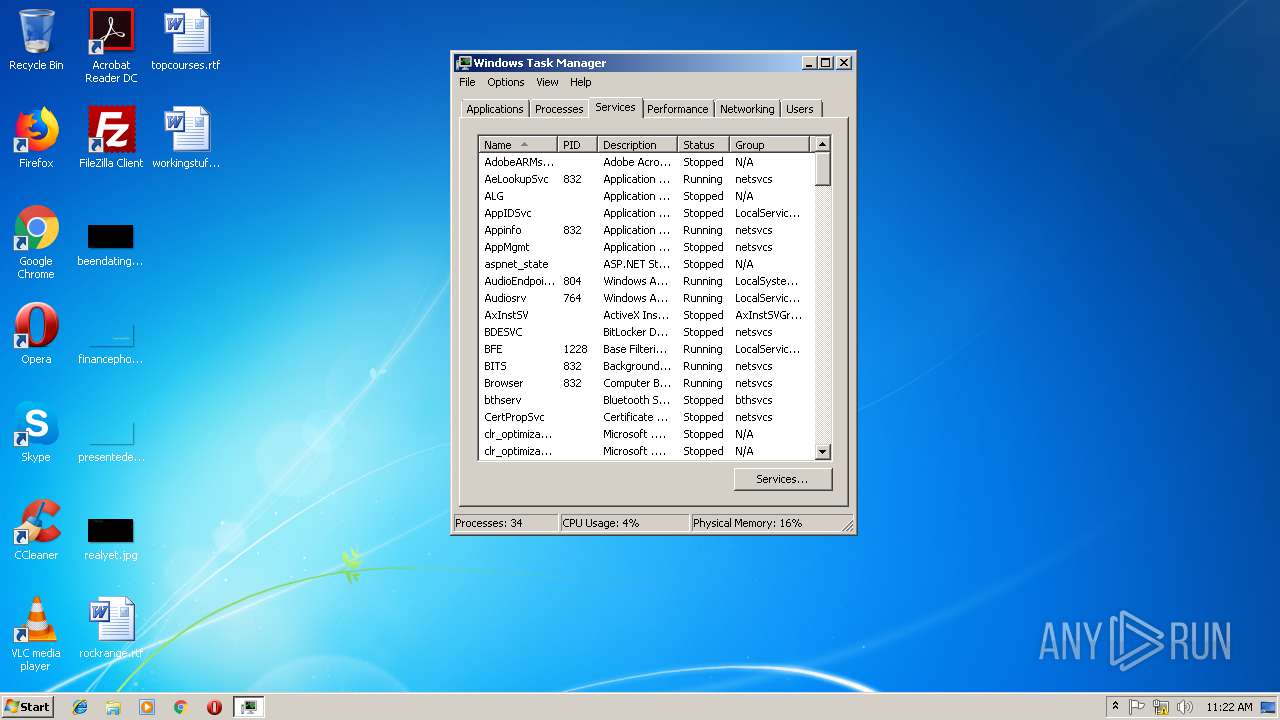
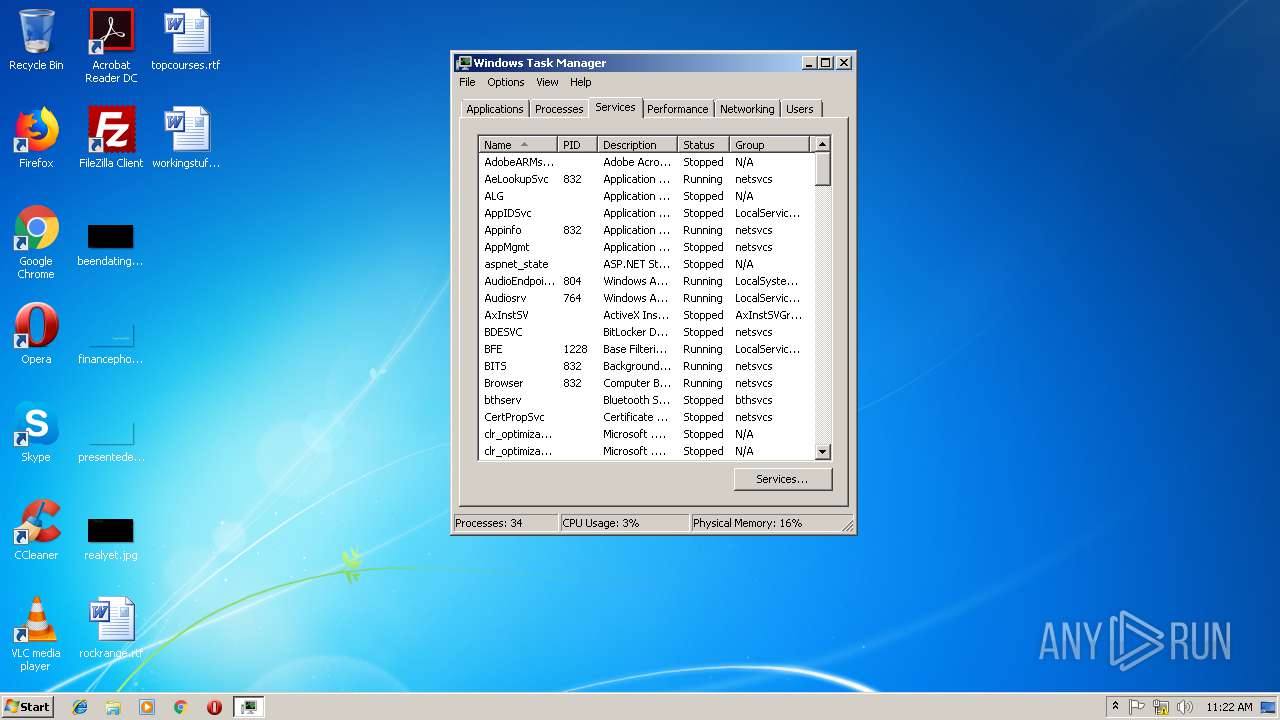
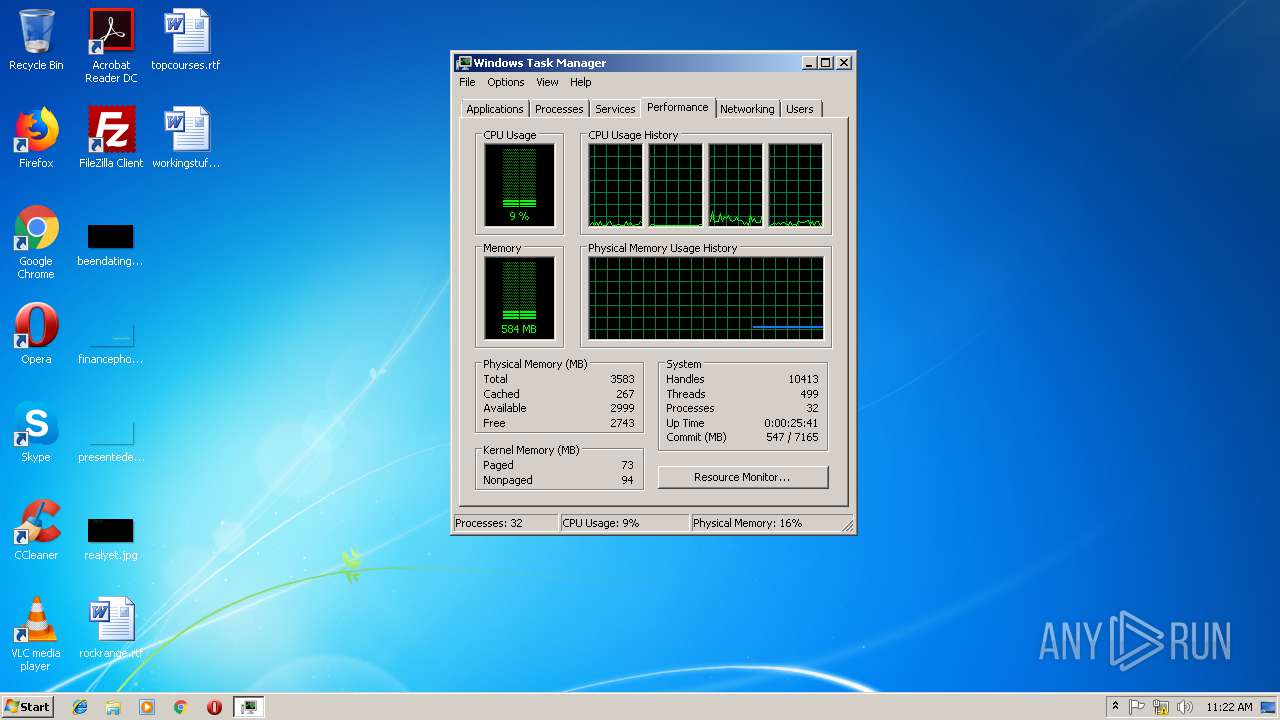
| 2180 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | 1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | 2.bat | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2792 | "C:\Users\admin\AppData\Local\Temp\2.bat" | C:\Users\admin\AppData\Local\Temp\2.bat | 2.bat | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2812 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | — | 1.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2896 | netstat | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\3ca3579e3a2a66f494bcb72adc576482.bat" | C:\Users\admin\AppData\Local\Temp\3ca3579e3a2a66f494bcb72adc576482.bat | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3212 | "C:\Users\admin\AppData\Roaming\install\syswin32.exe" | C:\Users\admin\AppData\Roaming\install\syswin32.exe | — | syswin32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3280 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | — | 3ca3579e3a2a66f494bcb72adc576482.bat | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3384 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 122
Read events
1 095
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3144) 3ca3579e3a2a66f494bcb72adc576482.bat | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3144) 3ca3579e3a2a66f494bcb72adc576482.bat | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\addon |
| Operation: | write | Name: | FirstExecution |
Value: 15/11/2018 -- 11:21 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\addon |
| Operation: | write | Name: | NewIdentification |
Value: addon | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3212) syswin32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\syswin32_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3212) syswin32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\syswin32_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3212) syswin32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\syswin32_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3212) syswin32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\syswin32_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
3
Suspicious files
2
Text files
1 593
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | 3ca3579e3a2a66f494bcb72adc576482.bat | C:\Users\admin\AppData\Local\Temp\2.bat | executable | |
MD5:— | SHA256:— | |||
| 2792 | 2.bat | C:\Users\admin\AppData\Roaming\install\syswin32.exe | executable | |
MD5:— | SHA256:— | |||
| 3144 | 3ca3579e3a2a66f494bcb72adc576482.bat | C:\Users\admin\AppData\Local\Temp\1.exe | executable | |
MD5:— | SHA256:— | |||
| 2792 | 2.bat | C:\Users\admin\AppData\Local\Temp\XX--XX--XX.txt | binary | |
MD5:— | SHA256:— | |||
| 2812 | 1.exe | C:\Users\admin\AppData\Local\Temp\XX--XX--XX.txt | binary | |
MD5:— | SHA256:— | |||
| 2540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\UuU.uUu | text | |
MD5:— | SHA256:— | |||
| 2540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\XxX.xXx | text | |
MD5:— | SHA256:— | |||
| 2540 | iexplore.exe | C:\Users\admin\AppData\Roaming\logs.dat | text | |
MD5:BF3DBA41023802CF6D3F8C5FD683A0C7 | SHA256:4A8E75390856BF822F492F7F605CA0C21F1905172F6D3EF610162533C140507D | |||
| 3212 | syswin32.exe | C:\Users\admin\AppData\Local\Temp\IEWEB.abc | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
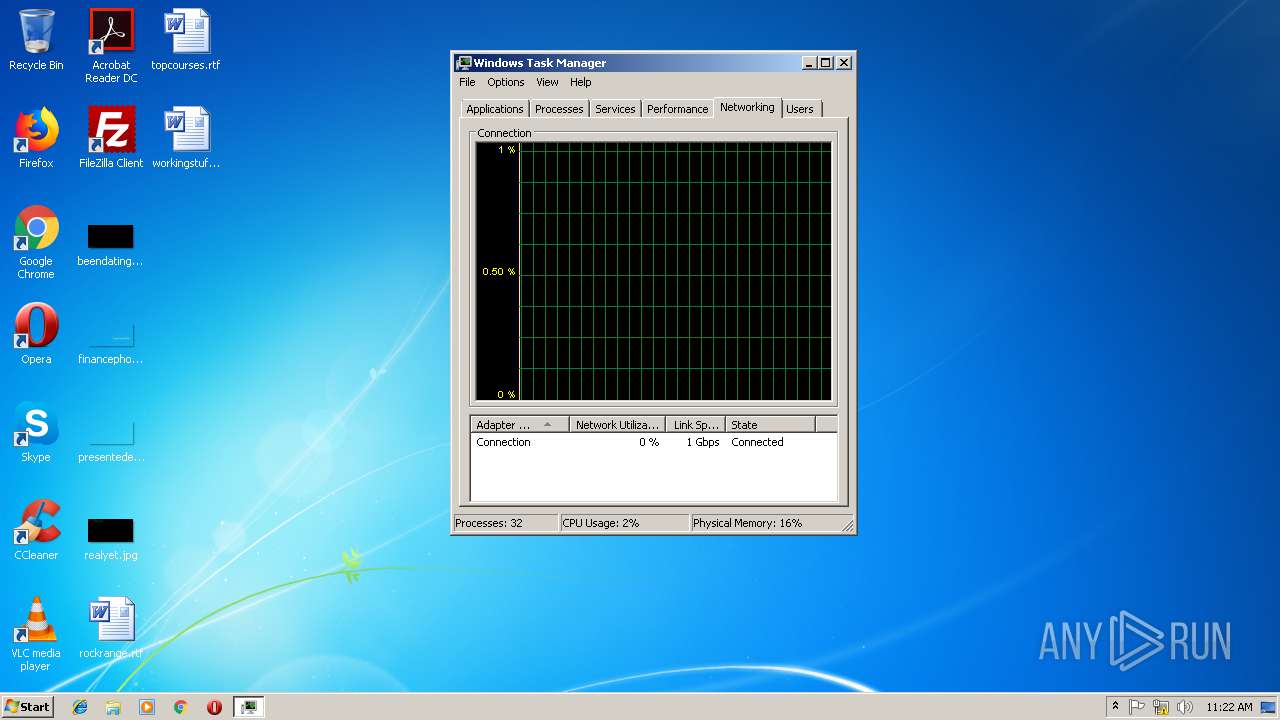
4
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | iexplore.exe | 217.173.4.252:3300 | 123host.zapto.org | Przedsiebiorstwo PROMAX Spolka Jawna Zofia Formanek-Okroj, Wieslaw Okroj | PL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
123host.zapto.org |
| unknown |
dns.msftncsi.com |
| shared |