| File name: | tsetup-x64.4.12.2.exe |
| Full analysis: | https://app.any.run/tasks/14abd835-786f-434c-a718-add3423142ed |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2024, 12:00:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D3E14A8C3E79990B6BC2FEF46B83FC3C |
| SHA1: | F92FB41169E1A878E73A61593F942EECDF0BC8E6 |
| SHA256: | BFEF099645330CF3428B7A1ED552D2246EFD7087E8724103688B1874A4CE265A |
| SSDEEP: | 6144:B0waXMlrOY8PZ5frVtvhYA4oTDPwZoIRMWmdmWtHXBwtWs+M:0XsEZ5frVtvhYGPPwNRkBcrL |
MALICIOUS
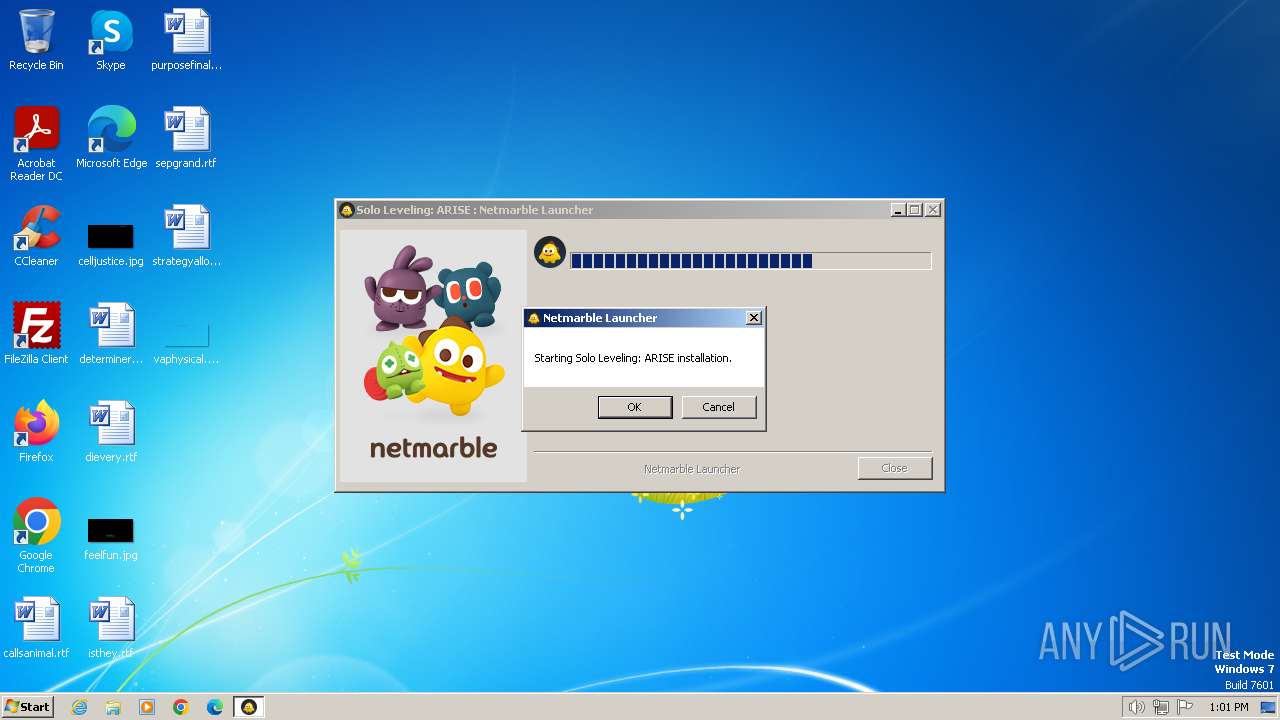
Drops the executable file immediately after the start
- tsetup-x64.4.12.2.exe (PID: 3996)
SUSPICIOUS
Reads security settings of Internet Explorer
- tsetup-x64.4.12.2.exe (PID: 3996)
Reads the Internet Settings
- tsetup-x64.4.12.2.exe (PID: 3996)
Reads settings of System Certificates
- tsetup-x64.4.12.2.exe (PID: 3996)
Checks Windows Trust Settings
- tsetup-x64.4.12.2.exe (PID: 3996)
INFO
Reads the computer name
- tsetup-x64.4.12.2.exe (PID: 3996)
Checks supported languages
- tsetup-x64.4.12.2.exe (PID: 3996)
Checks proxy server information
- tsetup-x64.4.12.2.exe (PID: 3996)
Reads the machine GUID from the registry
- tsetup-x64.4.12.2.exe (PID: 3996)
Reads the software policy settings
- tsetup-x64.4.12.2.exe (PID: 3996)
Create files in a temporary directory
- tsetup-x64.4.12.2.exe (PID: 3996)
Creates files or folders in the user directory
- tsetup-x64.4.12.2.exe (PID: 3996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
41
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3992 | "C:\Users\admin\AppData\Local\Temp\tsetup-x64.4.12.2.exe" | C:\Users\admin\AppData\Local\Temp\tsetup-x64.4.12.2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3996 | "C:\Users\admin\AppData\Local\Temp\tsetup-x64.4.12.2.exe" | C:\Users\admin\AppData\Local\Temp\tsetup-x64.4.12.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
8 652
Read events
8 606
Write events
37
Delete events
9
Modification events
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3996) tsetup-x64.4.12.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\Local\Temp\nsd21DC.tmp\INetC.dll | executable | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
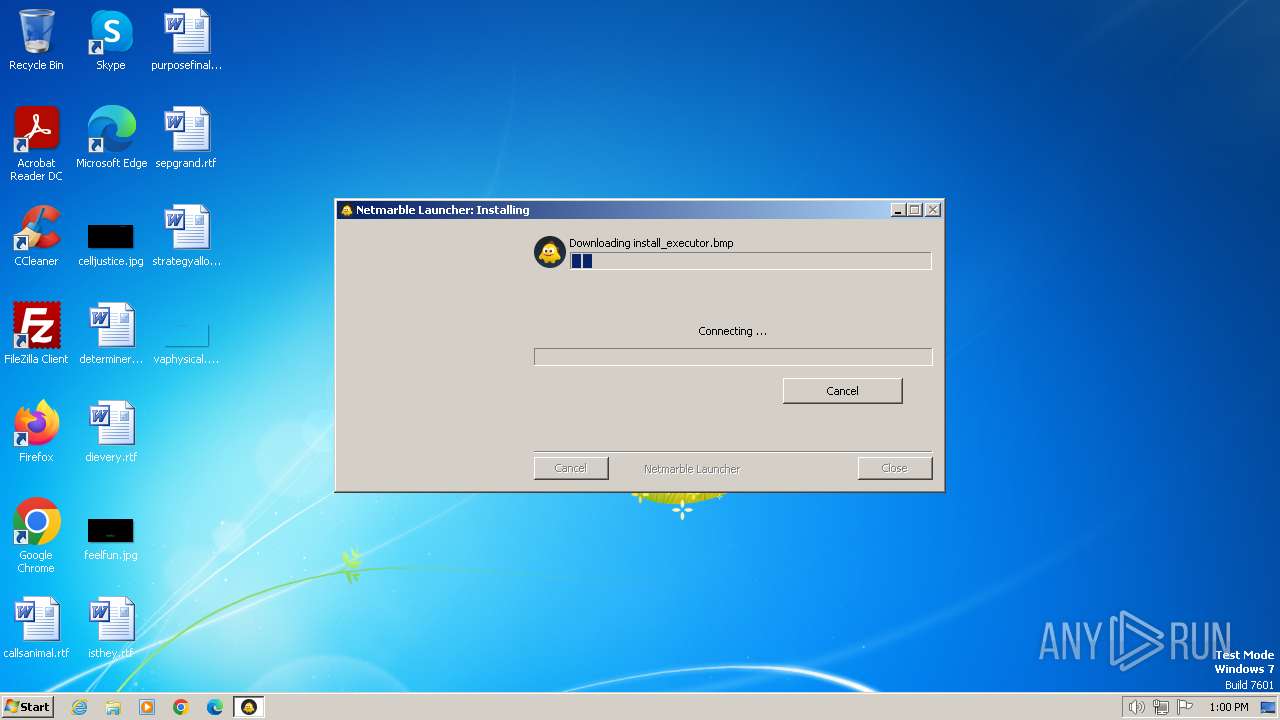
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\install_executor[1].bmp | image | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\Local\Temp\install_executor.bmp | — | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\install_executor_ko[1].bmp | image | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\Local\Temp\install_executor_ko.bmp | — | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\install_executor_cn[1].bmp | image | |
MD5:— | SHA256:— | |||
| 3996 | tsetup-x64.4.12.2.exe | C:\Users\admin\AppData\Local\Temp\install_executor_cn.bmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | tsetup-x64.4.12.2.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 88.221.110.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a414549a770d7263 | unknown | — | — | unknown |
3996 | tsetup-x64.4.12.2.exe | GET | 304 | 95.101.54.131:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?04b2dea8abd60a79 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3996 | tsetup-x64.4.12.2.exe | 95.101.54.99:443 | sgimage.netmarble.com | Akamai International B.V. | DE | unknown |
3996 | tsetup-x64.4.12.2.exe | 95.101.54.131:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3996 | tsetup-x64.4.12.2.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 88.221.110.121:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sgimage.netmarble.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |