| File name: | WinToHDD.exe |
| Full analysis: | https://app.any.run/tasks/08b0c18d-c210-4574-8d33-ff0ef2e87566 |
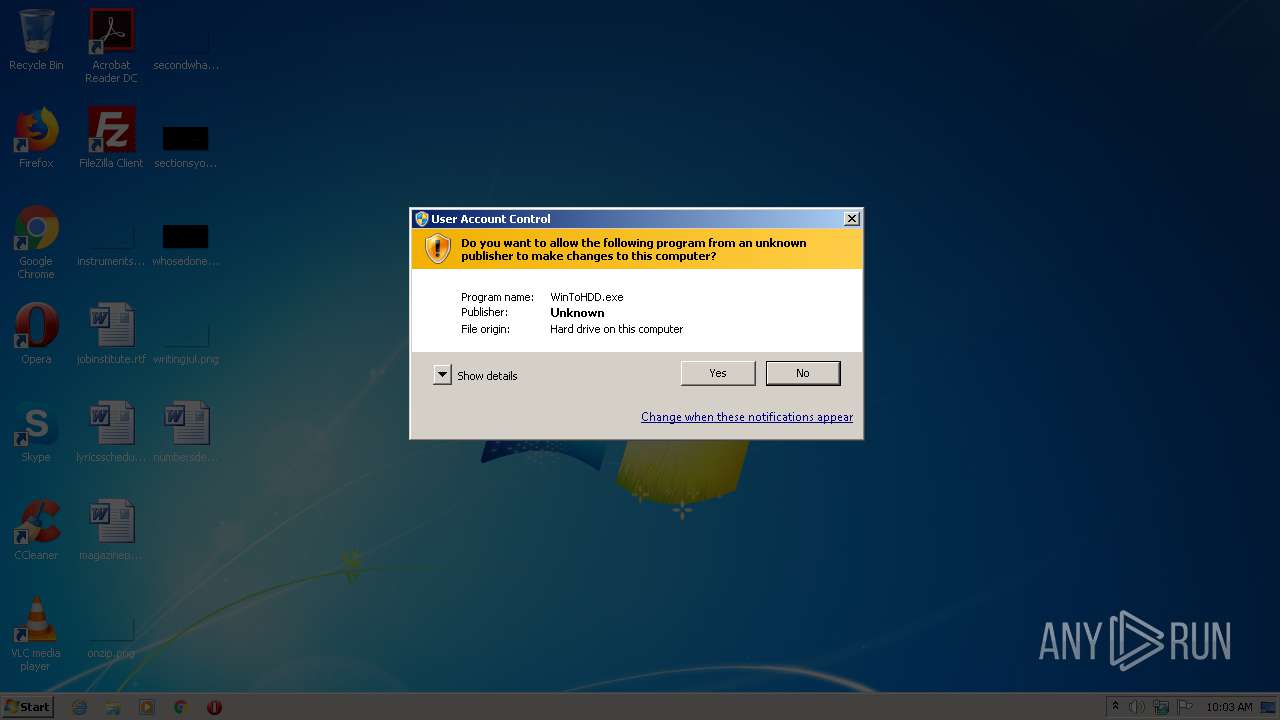
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2020, 09:02:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EFF1998CE5E8F4E29100CB93DC3C8282 |
| SHA1: | 3A150539B63087DCE10411DADA021CEBE1DF5E22 |
| SHA256: | BFECE1557B321DEE5231A65329E6454C938934DF86FCA9400F9EB9B3716B7936 |
| SSDEEP: | 393216:MNtmKLWtHBj/JV45C4jtoHkjzSJs3GuQCkTypngfiMd:lKLkx/JQC4BHjzSOaAy |
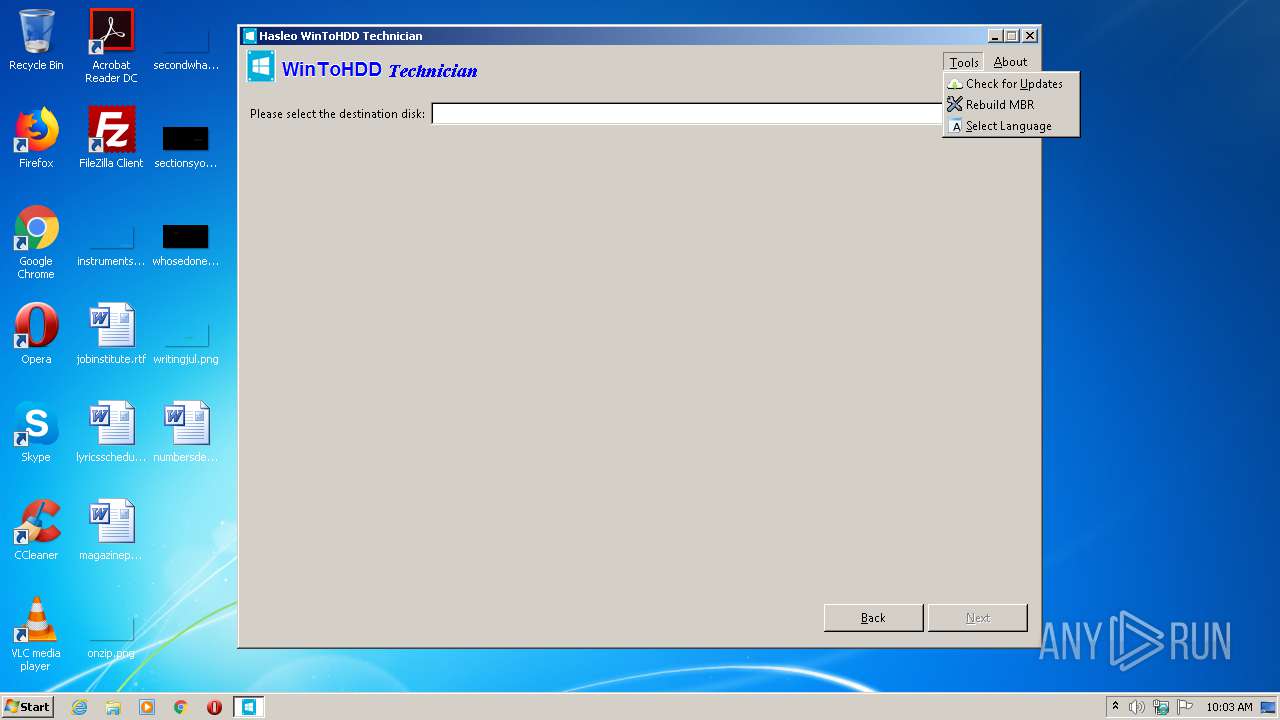
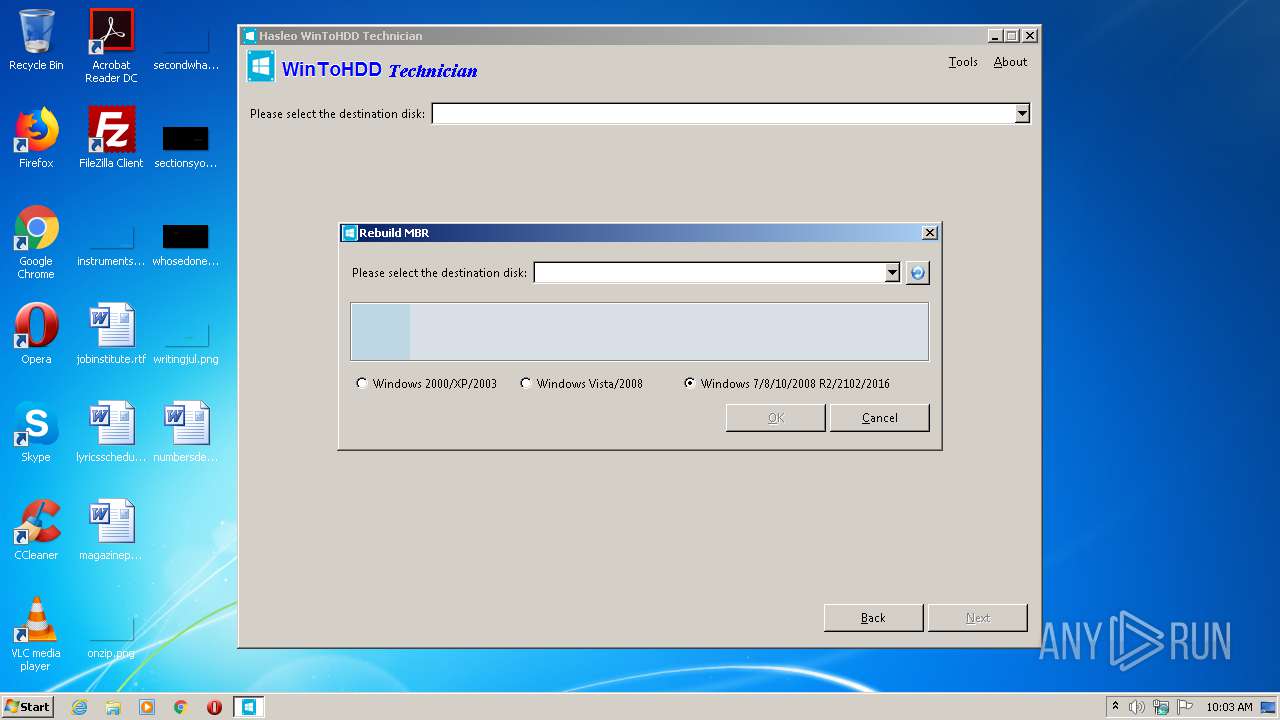
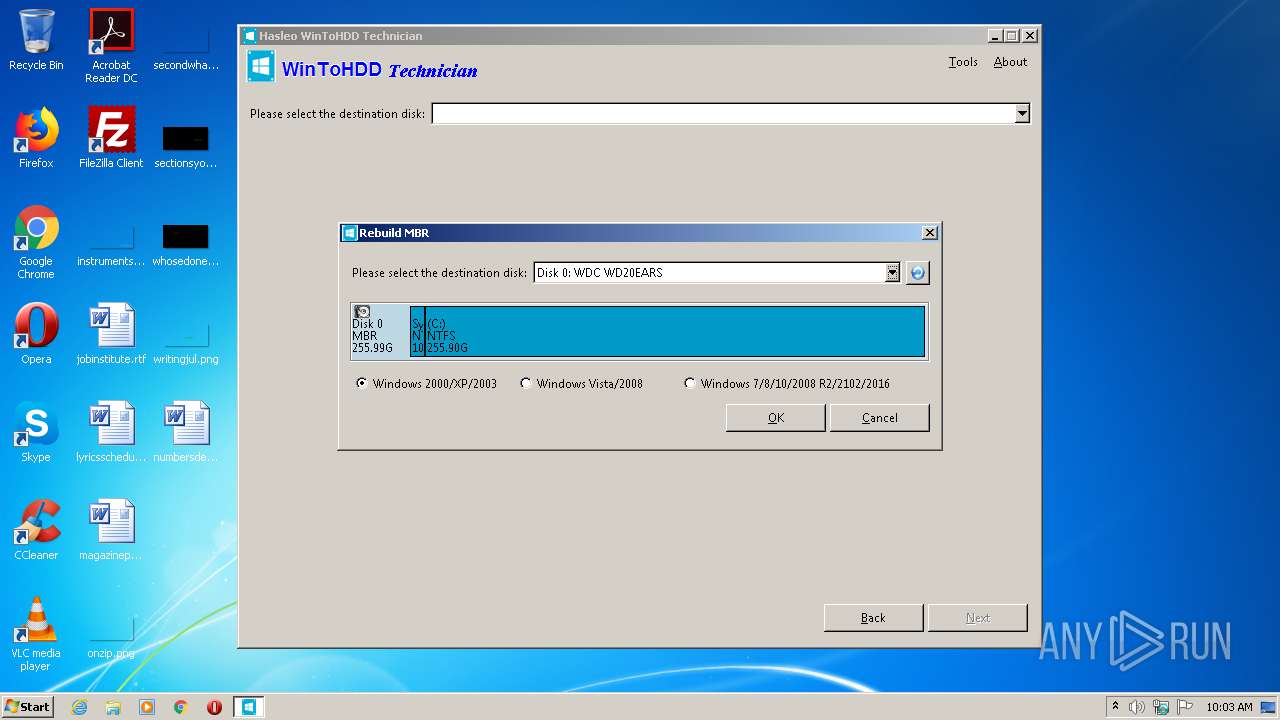
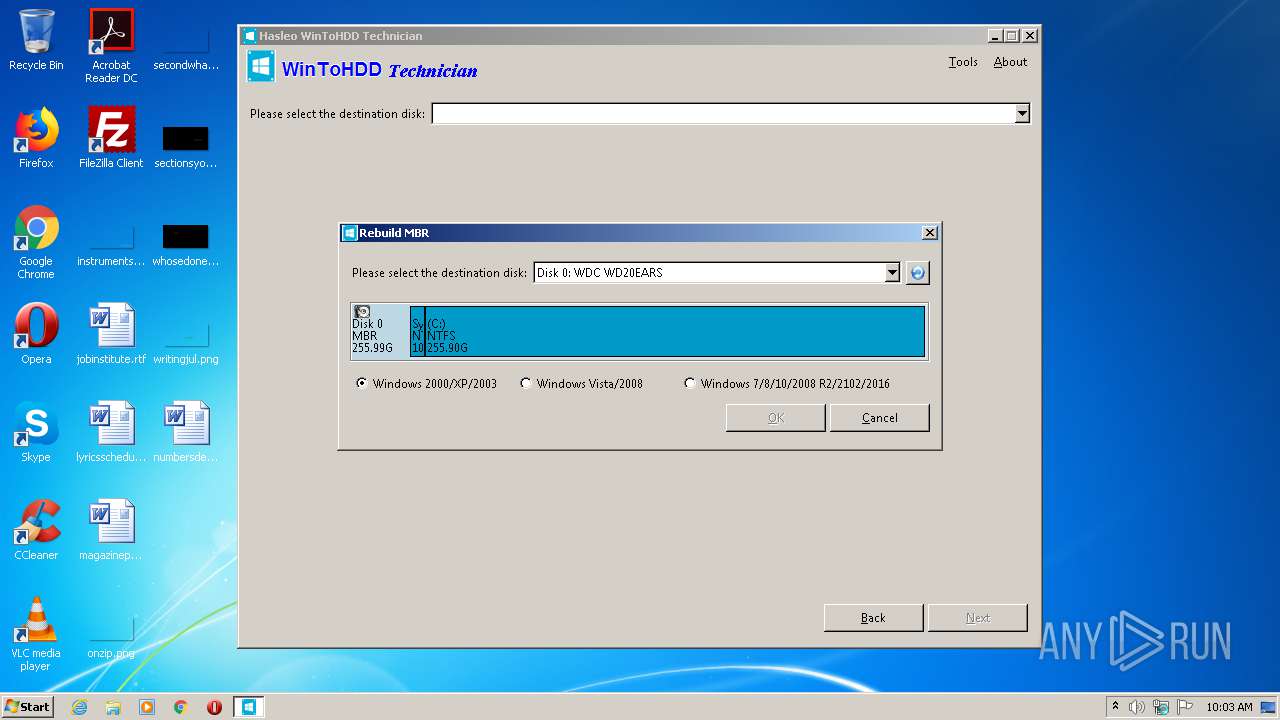
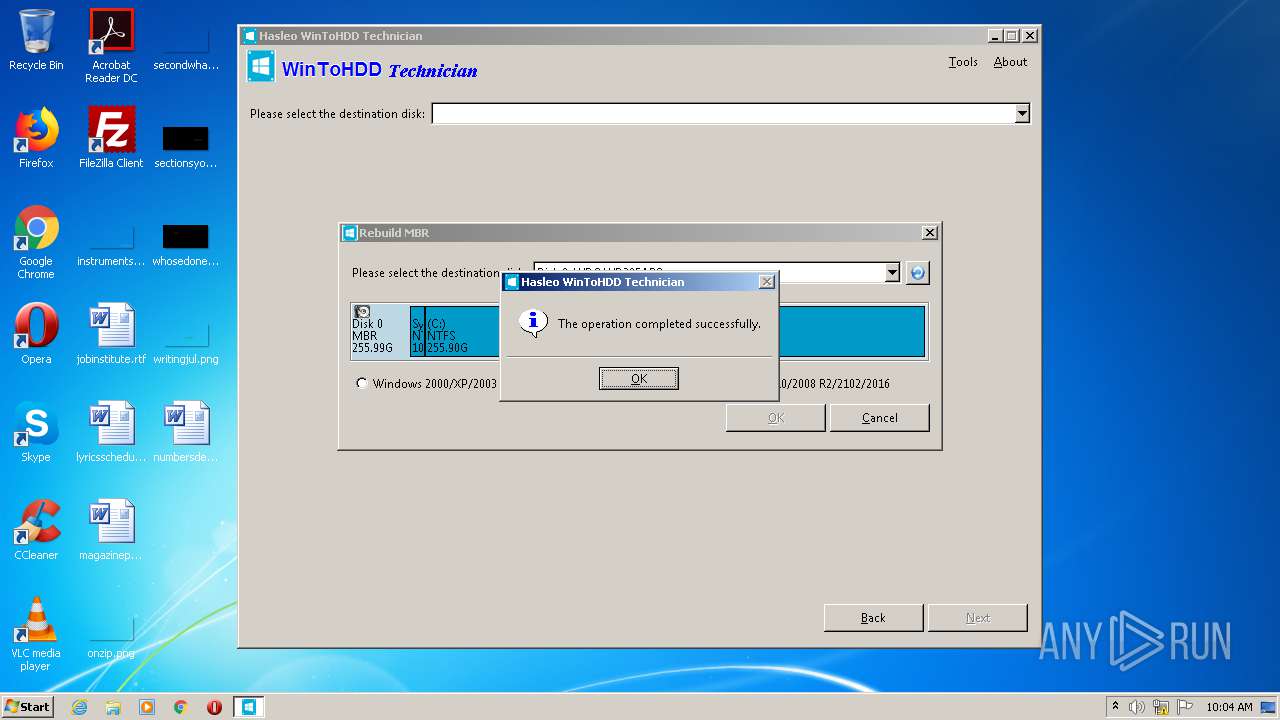
MALICIOUS
Low-level write access rights to disk partition
- WinToHDD.exe (PID: 1832)
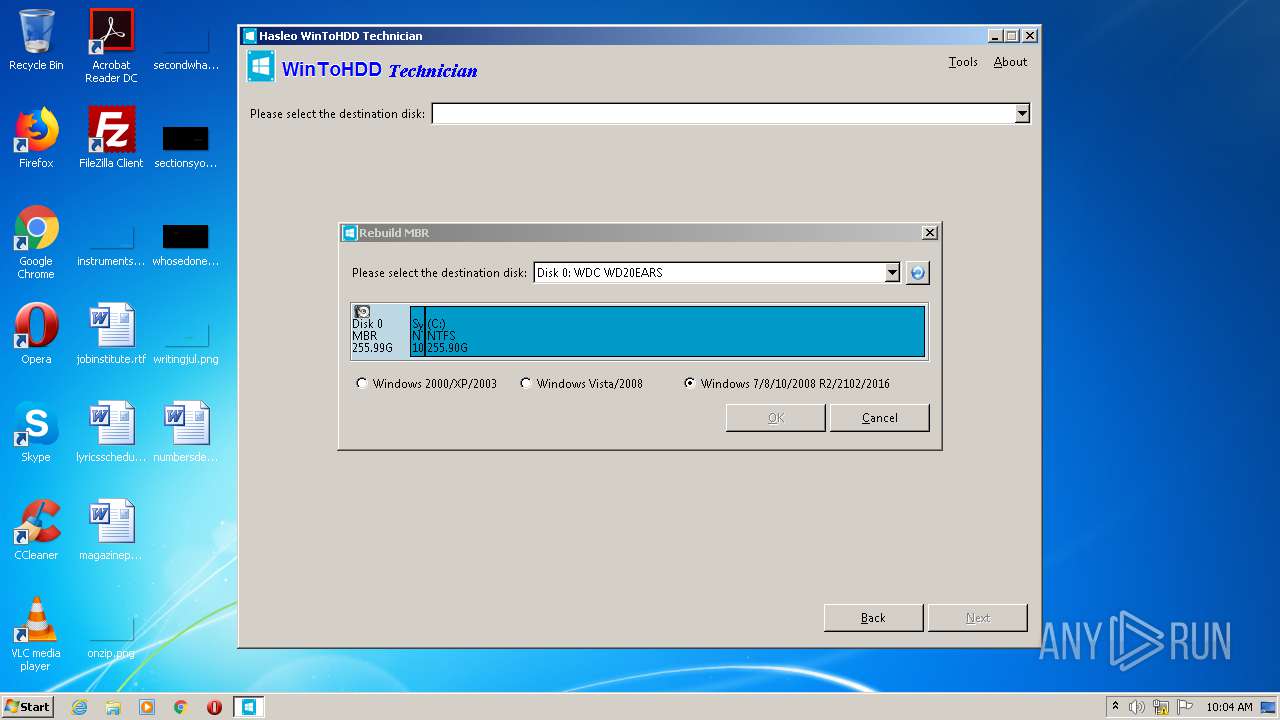
SUSPICIOUS
Low-level read access rights to disk partition
- WinToHDD.exe (PID: 1832)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:26 15:27:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 20480 |
| InitializedDataSize: | 61440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2884 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.0.0 |
| ProductVersionNumber: | 4.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
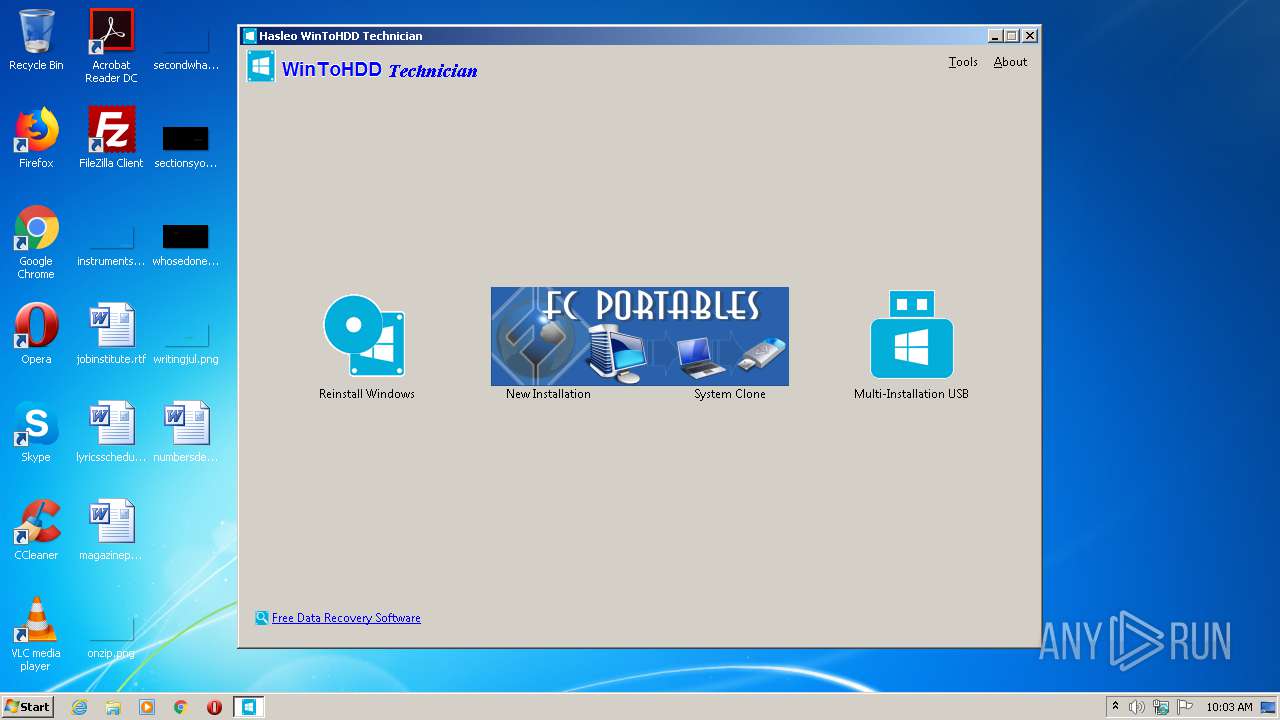
| CompanyName: | fcportables.com |
| FileDescription: | WinToHDD |
| FileVersion: | 4.4.0.0 |
| InternalName: | WinToHDD.exe |
| LegalCopyright: | - |
| OriginalFileName: | WinToHDD.exe |
| ProductName: | WinToHDD |
| ProductVersion: | 4.4.0.0 |
| Packager: | Turbo Studio 20 |
| PackagerVersion: | 20.5.1337 |
| VmVersion: | 20.5.1515.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jun-2020 13:27:54 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 26-Jun-2020 13:27:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000455C | 0x00004600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36314 |
.data | 0x00006000 | 0x00000460 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.xcpad | 0x00007000 | 0x008C1000 | 0x00000000 | 0 | |
.idata | 0x008C8000 | 0x0000034C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.19532 |
.reloc | 0x008C9000 | 0x00000248 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.40249 |
.rsrc | 0x008CA000 | 0x0000C1EC | 0x0000C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.51373 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8195 | 407 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.12796 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.72662 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.55061 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.79947 | 5346 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.79537 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.92446 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 2.27383 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.85546 | 5804 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.01764 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
KERNEL32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
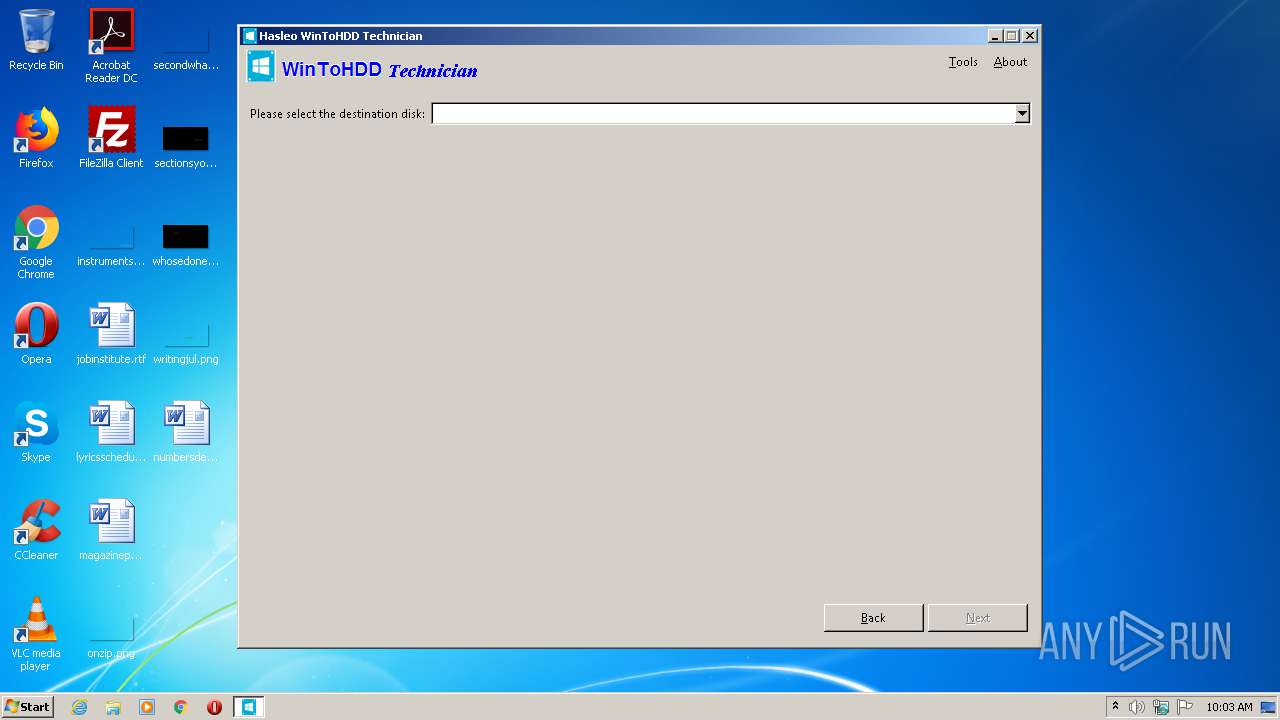
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | "C:\Users\admin\AppData\Local\Temp\WinToHDD.exe" | C:\Users\admin\AppData\Local\Temp\WinToHDD.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Temp\WinToHDD.exe" | C:\Users\admin\AppData\Local\Temp\WinToHDD.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1832 | "C:\Users\admin\AppData\Local\Temp\Data\WinToHDD\local\stubexe\0x755A5BF074B0F051\WinToHDD.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Program Files\Hasleo\WinToHDD\bin\WinToHDD.exe | WinToHDD.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
81
Read events
81
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1288 | WinToHDD.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\Data\WinToHDD\xsandbox.bin | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | C:\Users\admin\AppData\Local\Temp\Data\WinToHDD\xsandbox.bin.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\Data\WinToHDD\local\modified\@PROGRAMFILESX86@\Hasleo\WinToHDD\bin\WinToHDD.exe | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | C:\Users\admin\AppData\Local\Temp\Data\WinToHDD\local\temp\@PROGRAMFILESX86@\Hasleo\WinToHDD\bin\WinToHDD.exe | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\Data\WinToHDD\local\meta\@PROGRAMFILESX86@\Hasleo\WinToHDD\bin\WinToHDD.exe.__meta__ | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | C:\Users\admin\AppData\Local\Temp\Data\WinToHDD\local\meta\@PROGRAMFILESX86@\Hasleo\WinToHDD\bin\WinToHDD.exe.__meta__.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x2BBFA4D84287B120\sxs\AppLoader.exe\AppLoader.exe.manifest | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x2BBFA4D84287B120\sxs\AppLoader.exe\AppLoader.exe.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x2BBFA4D84287B120\sxs\intl.dll\intl.dll.manifest | — | |
MD5:— | SHA256:— | |||
| 1288 | WinToHDD.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x2BBFA4D84287B120\sxs\intl.dll\intl.dll.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report