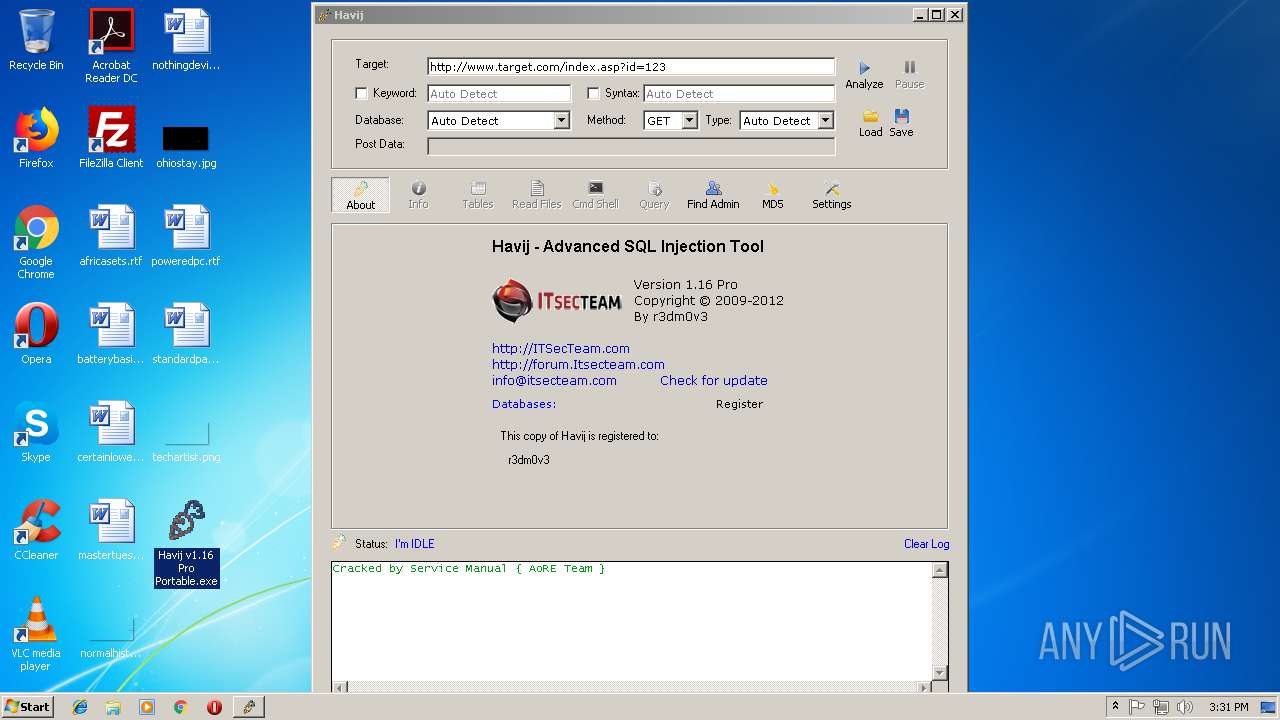
| File name: | Havij v1.16 Pro Portable.exe |
| Full analysis: | https://app.any.run/tasks/92f3ec9b-ff98-49b0-a0fc-5a9383913360 |
| Verdict: | Malicious activity |
| Analysis date: | October 15, 2018, 14:30:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 984E28E70D1000272A2AB61E34D12D6E |
| SHA1: | 35F4FA8D9E8779504300AA449B862FF119CEEE49 |
| SHA256: | BFEA6B1BA80A8B663C54DBA0AA6E45AD3A4E8FF005A82ADFED88AAB78B2FFB85 |
| SSDEEP: | 98304:W8s0qHiN7V6/1IyObD26U/M78DLhJHcMW36wYZjj/Yk/D6IeQBTpUIeUR536uMMc:vs0qHuVSgal/z/hJ8XGjzY+D6IeQppU5 |
MALICIOUS
Loads dropped or rewritten executable
- Havij v1.16 Pro Portable.exe (PID: 2388)
- Havij v1.16 Pro Portable.exe (PID: 2132)
- Havij.exe (PID: 3864)
Application was dropped or rewritten from another process
- Havij_Load.exe (PID: 1576)
- Havij.exe (PID: 3864)
SUSPICIOUS
Executable content was dropped or overwritten
- Havij v1.16 Pro Portable.exe (PID: 2132)
- Havij v1.16 Pro Portable.exe (PID: 2388)
Creates files in the user directory
- Havij.exe (PID: 3864)
Creates files in the Windows directory
- Havij v1.16 Pro Portable.exe (PID: 2132)
Low-level read access rights to disk partition
- Havij.exe (PID: 3864)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:10:06 12:33:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 3 |
| CodeSize: | 2560 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1020 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Oct-1999 10:33:39 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 06-Oct-1999 10:33:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000009F8 | 0x00000A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27597 |
.rdata | 0x00002000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0407808 |
.data | 0x00003000 | 0x0000025C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.15937 |
.idata | 0x00004000 | 0x000002FE | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83057 |
.Shared | 0x00005000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0.0659144 |
.rsrc | 0x00006000 | 0x0000039C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.00314 |
.reloc | 0x00007000 | 0x000001B2 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.36734 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.23396 | 744 | UNKNOWN | English - United States | RT_ICON |
101 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | C:\Windows\system32\HavijPro\Havij_Load.exe | C:\Windows\system32\HavijPro\Havij_Load.exe | — | Havij v1.16 Pro Portable.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\Desktop\Havij v1.16 Pro Portable.exe" | C:\Users\admin\Desktop\Havij v1.16 Pro Portable.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
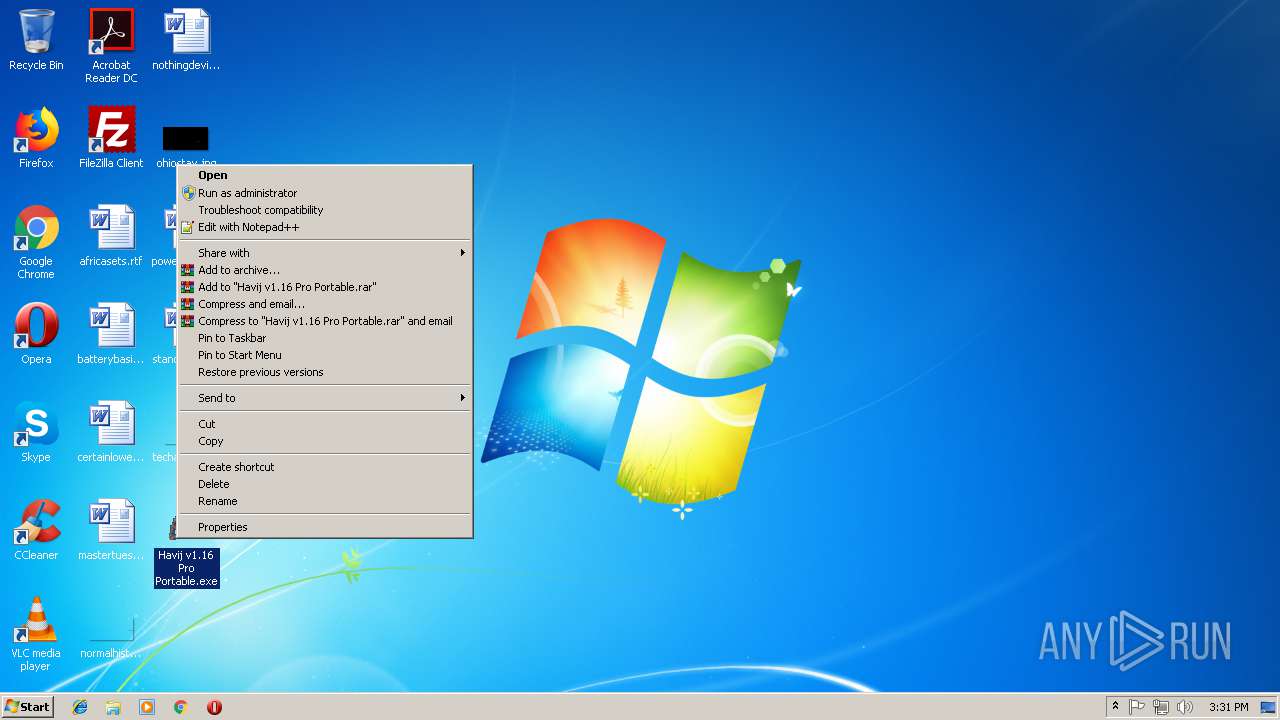
| 2388 | "C:\Users\admin\Desktop\Havij v1.16 Pro Portable.exe" | C:\Users\admin\Desktop\Havij v1.16 Pro Portable.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
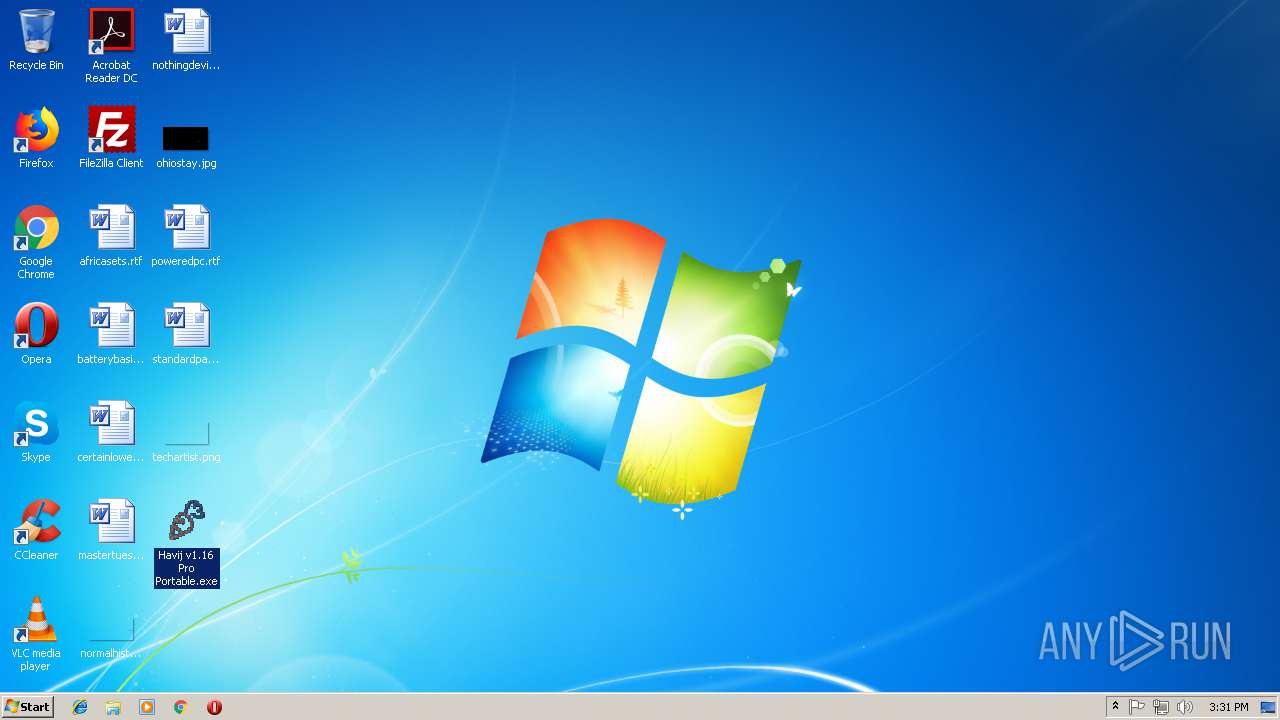
| 3864 | "C:\Windows\system32\HavijPro\Havij.exe" | C:\Windows\system32\HavijPro\Havij.exe | — | Havij_Load.exe | |||||||||||
User: admin Company: ITSecTeam Integrity Level: HIGH Description: Advanced SQL Injection Tool Exit code: 0 Version: 1.16 Modules
| |||||||||||||||
Total events
1 663
Read events
1 060
Write events
530
Delete events
73
Modification events
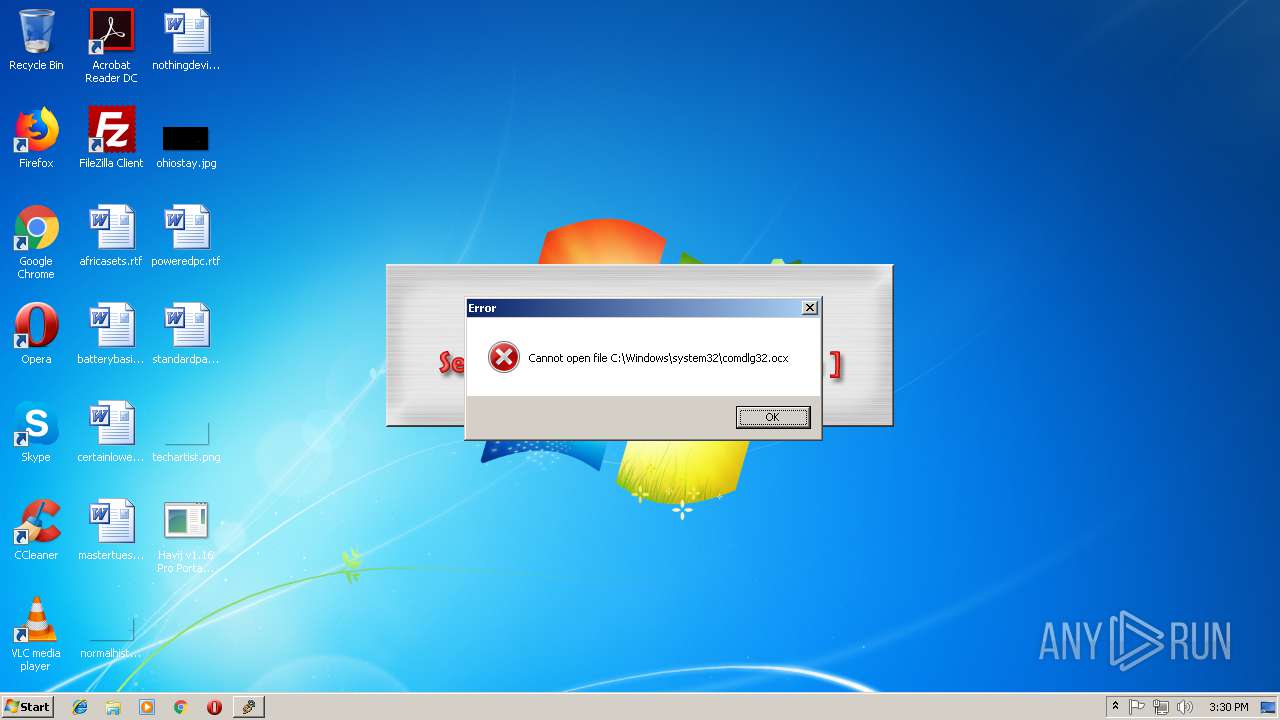
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB} |
| Operation: | write | Name: | |
Value: Microsoft Common Dialog Control, version 6.0 | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\comdlg32.ocx | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog |
| Operation: | write | Name: | |
Value: Microsoft Common Dialog Control, version 6.0 | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog\CLSID |
| Operation: | write | Name: | |
Value: {F9043C85-F6F2-101A-A3C9-08002B2F49FB} | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog\CurVer |
| Operation: | write | Name: | |
Value: MSComDlg.CommonDialog.1 | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog.1 |
| Operation: | write | Name: | |
Value: Microsoft Common Dialog Control, version 6.0 | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog.1\CLSID |
| Operation: | write | Name: | |
Value: {F9043C85-F6F2-101A-A3C9-08002B2F49FB} | |||
| (PID) Process: | (2132) Havij v1.16 Pro Portable.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB}\VersionIndependentProgID |
| Operation: | write | Name: | |
Value: MSComDlg.CommonDialog | |||
Executable files
9
Suspicious files
0
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | Havij v1.16 Pro Portable.exe | C:\Users\admin\AppData\Local\Temp\IRANTK.INFO | executable | |
MD5:0DAB1380431FF8A5BFE52797D4240DA8 | SHA256:9E5453882DF10F54E8E9F8CFDFB99D919654479665D17F589DBC3D8622C0E256 | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Windows\system32\HavijPro\Help.chm | chm | |
MD5:D22FD197CB0F86058A4CC1E7BC712EF1 | SHA256:FD3AFCE9F48E0E18601864F53FE996FA34F1B261E2B0E3B5ED3CCFA78D565F96 | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Windows\system32\comdlg32.ocx | executable | |
MD5:D76F0EAB36F83A31D411AEAF70DA7396 | SHA256:46F4FDB12C30742FF4607876D2F36CF432CDC7EC3D2C99097011448FC57E997C | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Windows\system32\HavijPro\columns.txt | text | |
MD5:D728B72F71468FCC57E3560D74972DFB | SHA256:55589AB69216A8D9A1AA175255EB03BC90B4B8FAFFB469893FBFBA677C06313F | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Windows\system32\HavijPro\Havij_Load.exe | executable | |
MD5:C54226211F2A5C979BA14B7B8D3C6B3A | SHA256:AB1A59FC8991B7A4372B68AF0415D20C27E6A1DE5C15F701D55ADBC8E837B399 | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Windows\system32\HavijPro\Havij.exe | executable | |
MD5:A9985FD7BA9B20F84F65D924656E8D52 | SHA256:E9DDB4F8036A3885A32F7CA720079D038BB97B2FBC30E1CF3E4DFE079FB3D7D3 | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Users\admin\AppData\Local\Temp\IRANTK.INFO | executable | |
MD5:0DAB1380431FF8A5BFE52797D4240DA8 | SHA256:9E5453882DF10F54E8E9F8CFDFB99D919654479665D17F589DBC3D8622C0E256 | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Windows\system32\HavijPro\Read Me.txt | text | |
MD5:11EC6EB7965B25EF6E909FC33B521D8C | SHA256:A85824CF8BF32C3D2440D9F32C8906A7C665FF607F9F227CD5F2D7224FB9ADA2 | |||
| 2132 | Havij v1.16 Pro Portable.exe | C:\Windows\system32\HavijPro\tables.txt | text | |
MD5:C100748489C99F000D7C9D7940C76146 | SHA256:5A4B46FF5AB8018B7560F6D6D79C910F2A97F48178E5995C401C06A5E81E46A2 | |||
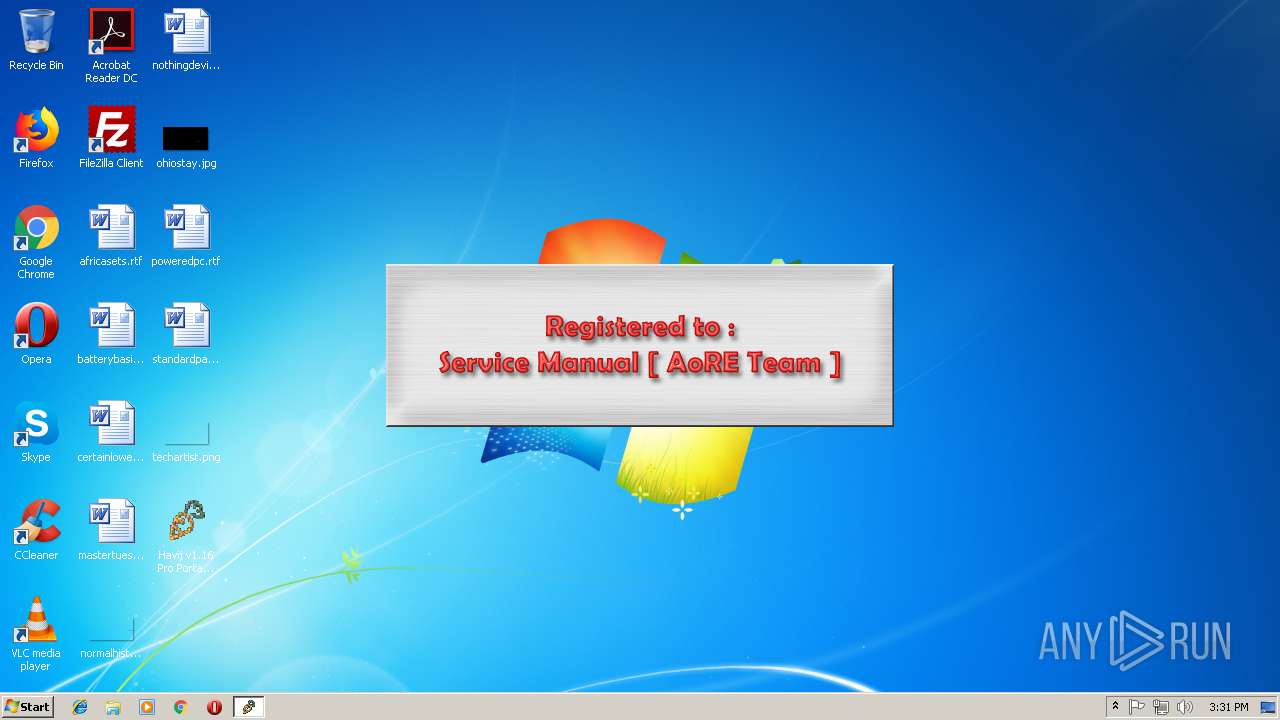
| 2388 | Havij v1.16 Pro Portable.exe | C:\users\admin\appdata\local\temp\REG-SM-AoRE.bmp | image | |
MD5:618EF93D12F1C201313F3E9DF0D34C2C | SHA256:0DE8FBD0686F6434F03DCB7EF2ED622980902D495E7483105F2ABB8318C8303C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report