| File name: | e____________3.0.bat |
| Full analysis: | https://app.any.run/tasks/b275d256-46cc-4400-827f-db9dcef3b38b |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2022, 05:42:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | E42984663E34E437169110537D13DACA |
| SHA1: | 73F7D7EEAE5F3D4AA4EF8C0DE3272E5D294811CB |
| SHA256: | BFE0814ED8B93B3188AF739BFBD61C4E285C02EF90B4BD974BD1287076E7704C |
| SSDEEP: | 96:i8/oR7c4g+ywYJWzMzTBViB2rRq+CnLSj4:i8/oR7ZrKKB2rM+CnL24 |
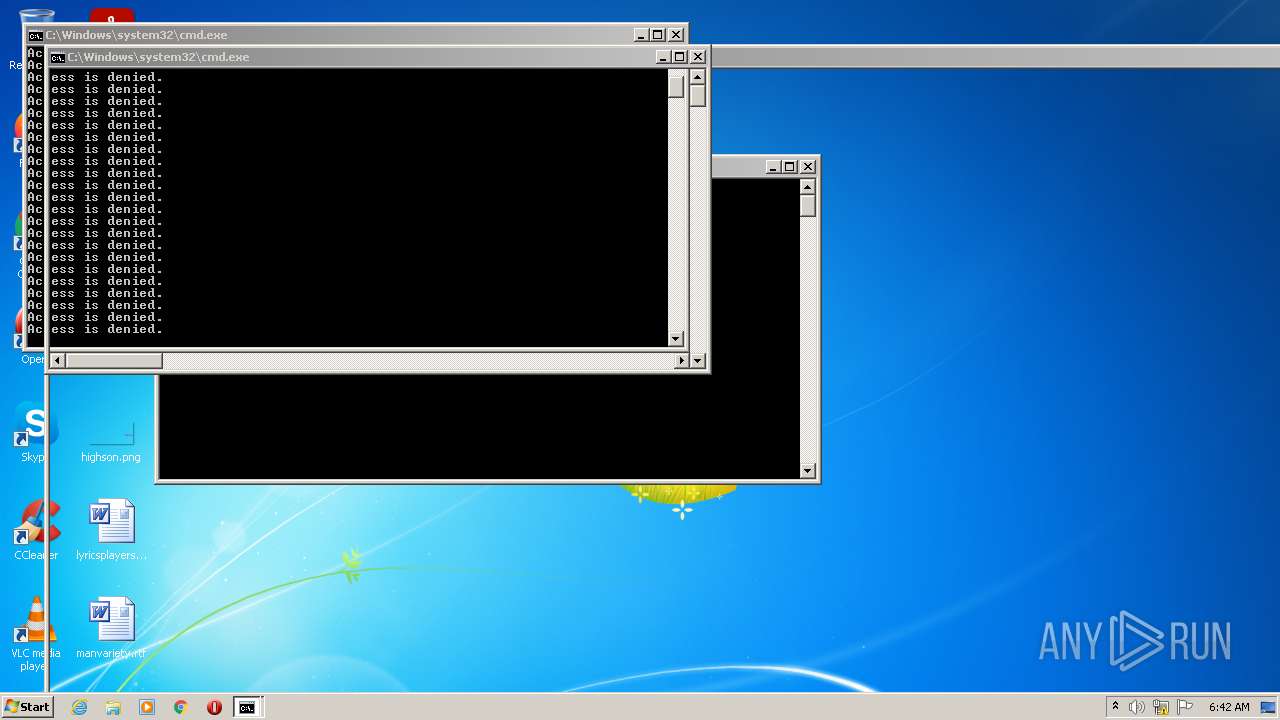
MALICIOUS
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 4052)
Writes to a start menu file
- cmd.exe (PID: 3372)
UAC/LUA settings modification
- reg.exe (PID: 2392)
SUSPICIOUS
Reads the computer name
- cscript.exe (PID: 3536)
- WMIC.exe (PID: 2564)
- WMIC.exe (PID: 2820)
Checks supported languages
- cmd.exe (PID: 3104)
- cmd.exe (PID: 3372)
- cscript.exe (PID: 3536)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 2840)
- WMIC.exe (PID: 2820)
- WMIC.exe (PID: 2564)
- cmd.exe (PID: 2036)
- mode.com (PID: 3904)
- cmd.exe (PID: 1608)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 2932)
- cmd.exe (PID: 2172)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 1292)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 2072)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 2028)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 1320)
- cmd.exe (PID: 3720)
- cmd.exe (PID: 2212)
- cmd.exe (PID: 400)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 1192)
Application launched itself
- cmd.exe (PID: 3372)
Reads Environment values
- netsh.exe (PID: 3660)
Creates files in the program directory
- cmd.exe (PID: 3372)
Checks for external IP
- nslookup.exe (PID: 932)
Executed as Windows Service
- fxssvc.exe (PID: 2800)
- fxssvc.exe (PID: 3864)
INFO
Checks supported languages
- reg.exe (PID: 1276)
- rundll32.exe (PID: 3748)
- reg.exe (PID: 2824)
- net1.exe (PID: 908)
- bcdedit.exe (PID: 3240)
- net.exe (PID: 2072)
- net.exe (PID: 3576)
- net1.exe (PID: 664)
- net.exe (PID: 3672)
- net1.exe (PID: 1888)
- reg.exe (PID: 4052)
- reg.exe (PID: 2392)
- rundll32.exe (PID: 2632)
- reg.exe (PID: 1368)
- netsh.exe (PID: 3660)
- nslookup.exe (PID: 932)
- reg.exe (PID: 3308)
- reg.exe (PID: 860)
- reg.exe (PID: 2472)
- find.exe (PID: 2396)
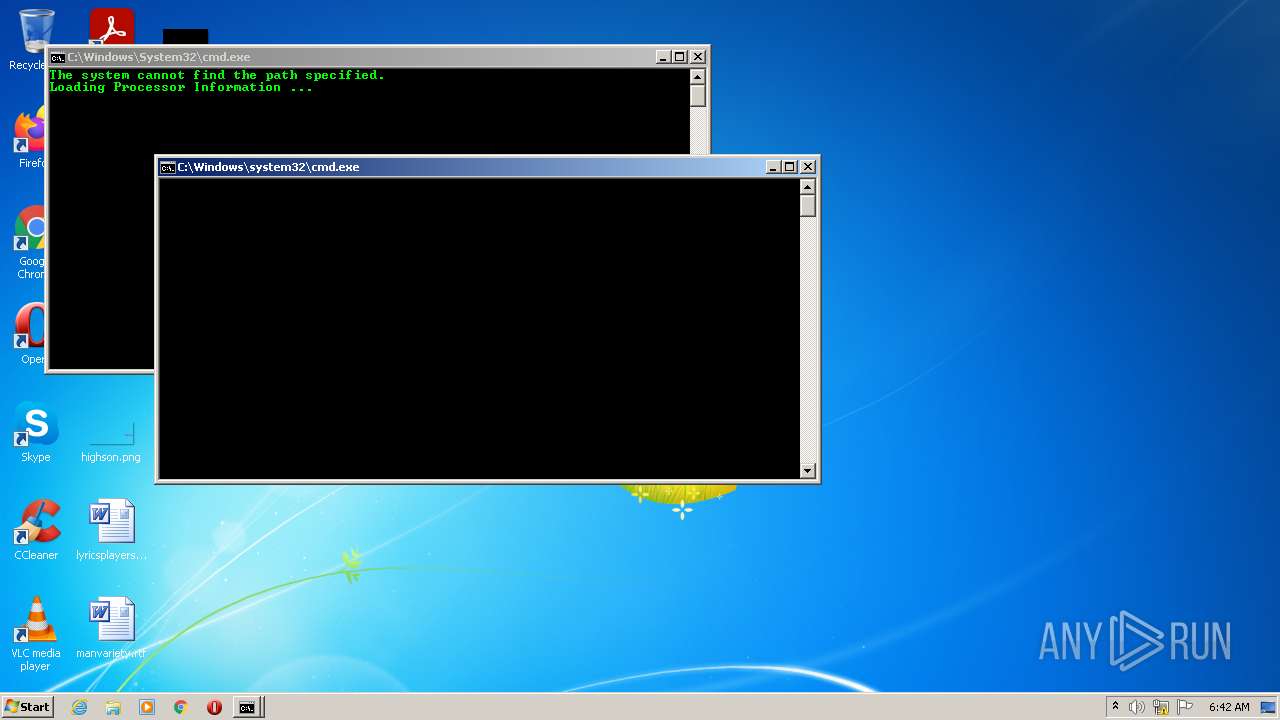
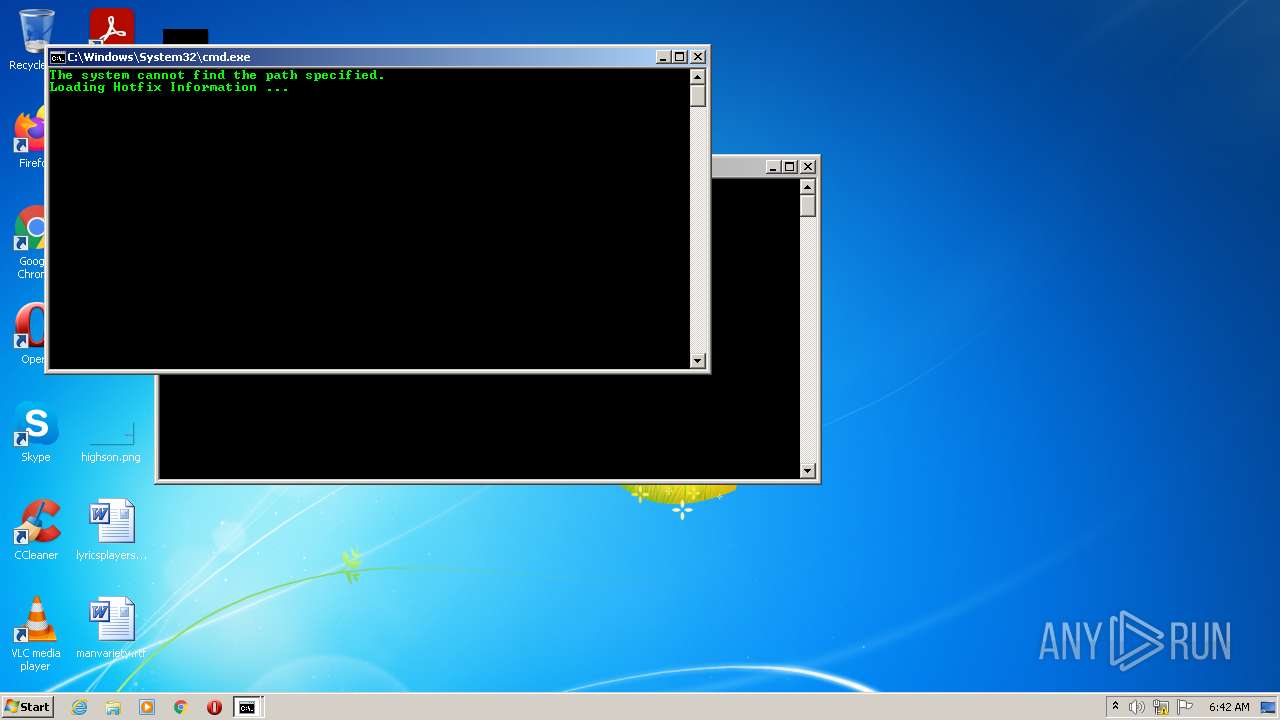
- systeminfo.exe (PID: 3256)
- fxssvc.exe (PID: 2800)
- netsh.exe (PID: 1588)
- netsh.exe (PID: 3700)
- ipconfig.exe (PID: 1404)
- ipconfig.exe (PID: 3824)
- netsh.exe (PID: 3332)
- netsh.exe (PID: 1196)
- fxssvc.exe (PID: 3864)
- netsh.exe (PID: 2904)
- netsh.exe (PID: 3016)
- netsh.exe (PID: 3224)
- netsh.exe (PID: 1712)
- netsh.exe (PID: 2072)
- reg.exe (PID: 188)
- reg.exe (PID: 3580)
- reg.exe (PID: 3036)
- reg.exe (PID: 1992)
- reg.exe (PID: 3476)
Reads the computer name
- net1.exe (PID: 908)
- nslookup.exe (PID: 932)
- netsh.exe (PID: 3660)
- systeminfo.exe (PID: 3256)
- fxssvc.exe (PID: 2800)
- ipconfig.exe (PID: 1404)
- ipconfig.exe (PID: 3824)
- fxssvc.exe (PID: 3864)
Checks Windows Trust Settings
- cscript.exe (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
76
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | reg delete "HKLM" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 400 | cmd /c REN *.ini *.3KM1 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 664 | C:\Windows\system32\net1 user /add e________ fucked your PC | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 860 | reg delete "HKLM\SOFTWARE" /v {Default} /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | C:\Windows\system32\net1 user /del admin | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 932 | nslookup myip.opendns.com resolver1.opendns.com | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | cmd /c REN *.cmd *.sI09 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1192 | cmd /c reg delete "HKLM" /f | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1196 | netsh advfirewall set privateprofile state off | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
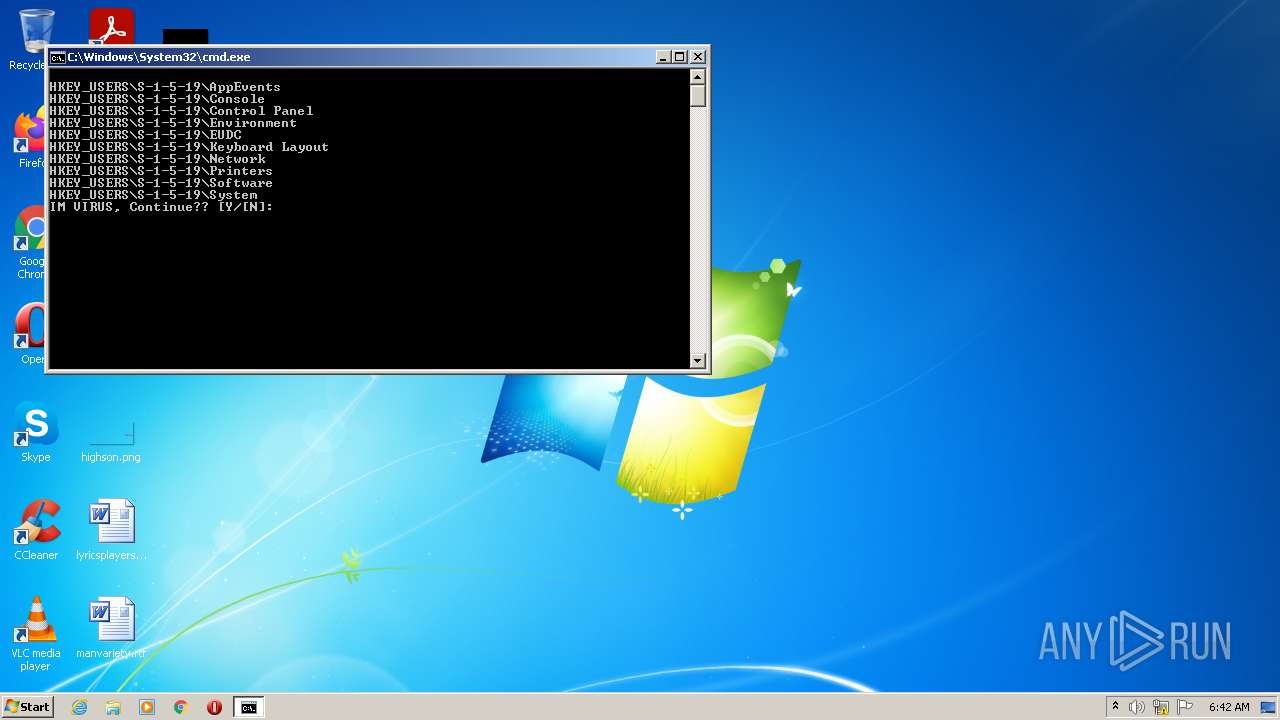
| 1276 | reg query HKU\S-1-5-19 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
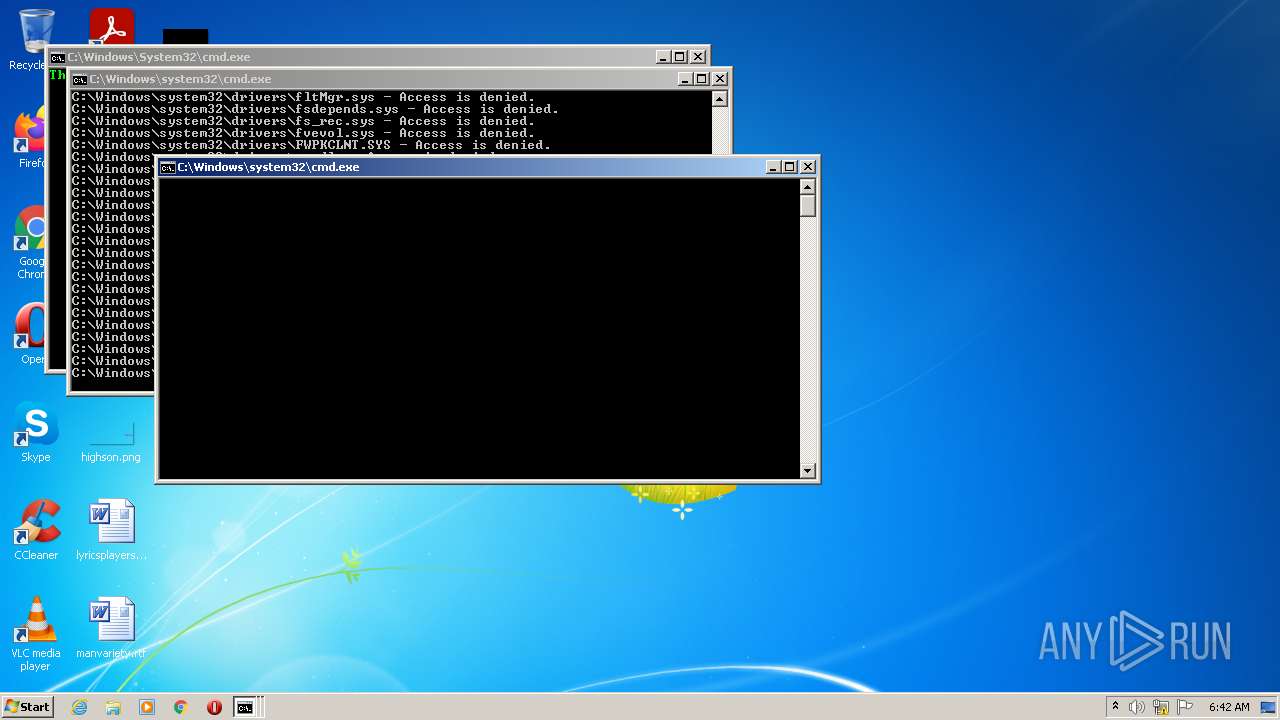
Total events
94 752
Read events
2 624
Write events
75
Delete events
92 053
Modification events
| (PID) Process: | (3536) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3536) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3536) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3536) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3240) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Description |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3240) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3240) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3240) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\12000004 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3240) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\12000005 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3240) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\12000030 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | cmd.exe | C:\Windows\setuperr.439a | — | |
MD5:— | SHA256:— | |||
| 1608 | cmd.exe | C:\Windows\System32\MRT-KB890830.1Je9 | — | |
MD5:— | SHA256:— | |||
| 1608 | cmd.exe | C:\Windows\System32\MRT.1Je9 | — | |
MD5:— | SHA256:— | |||
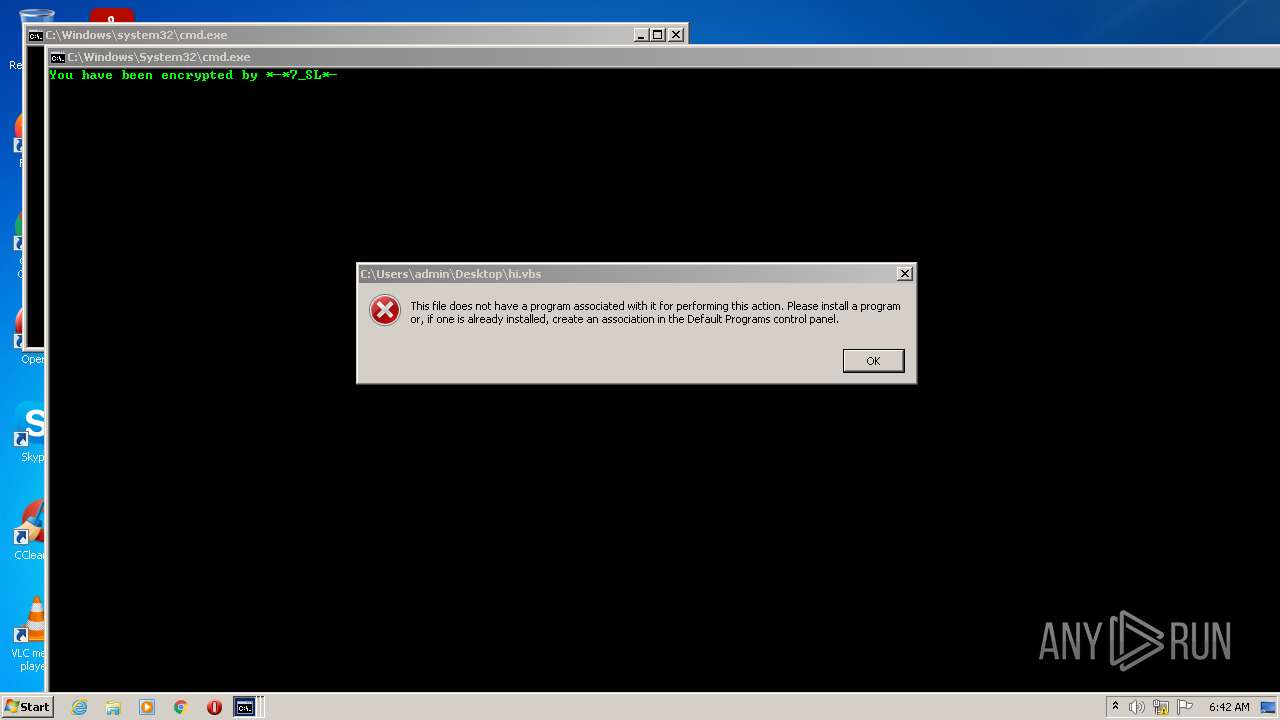
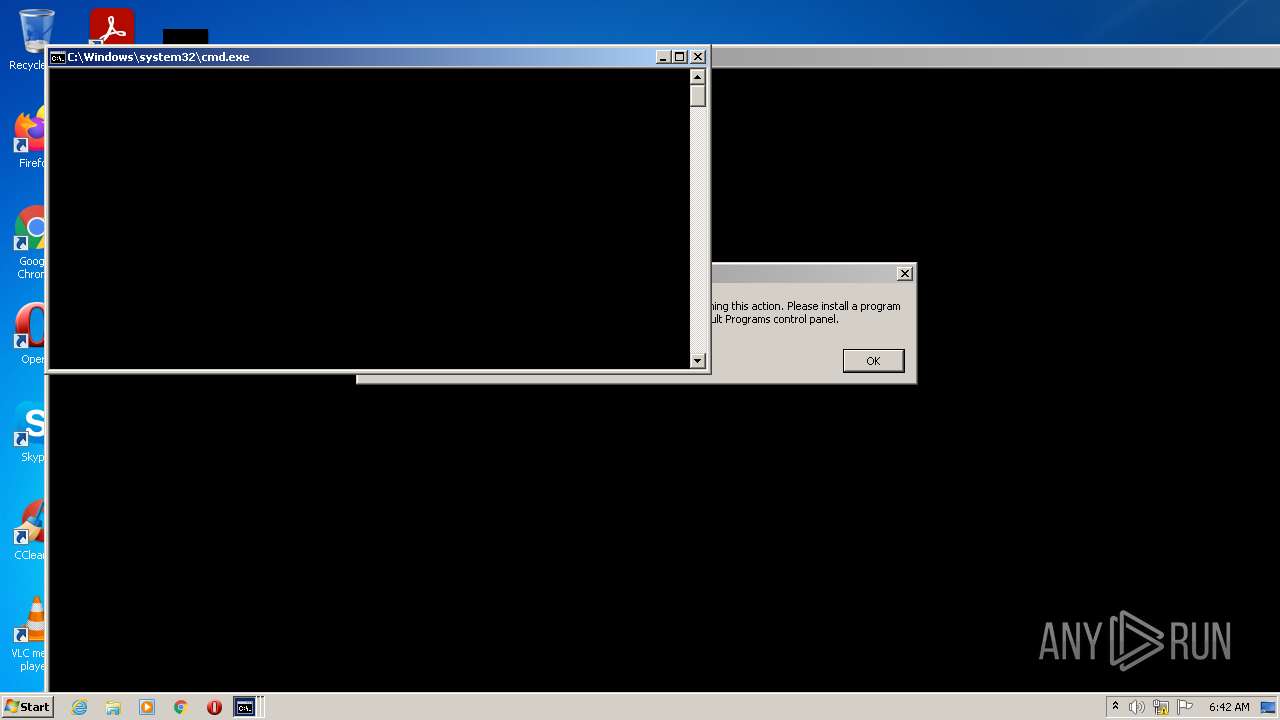
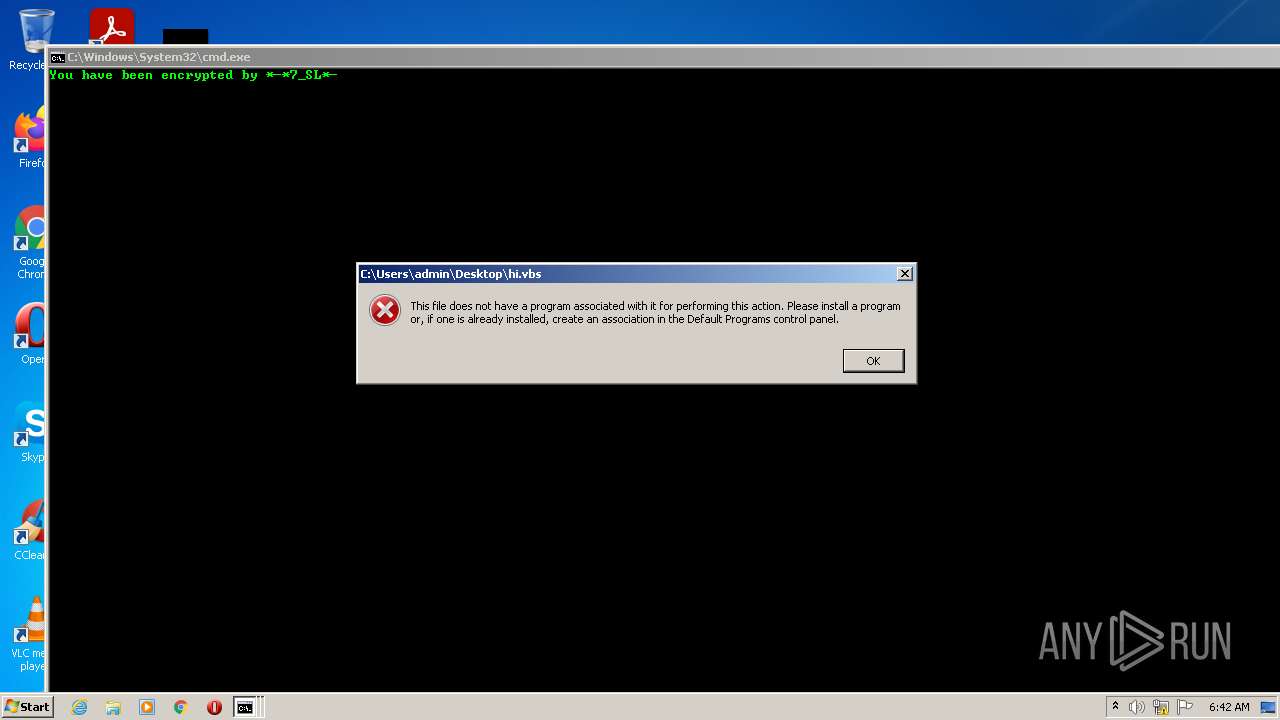
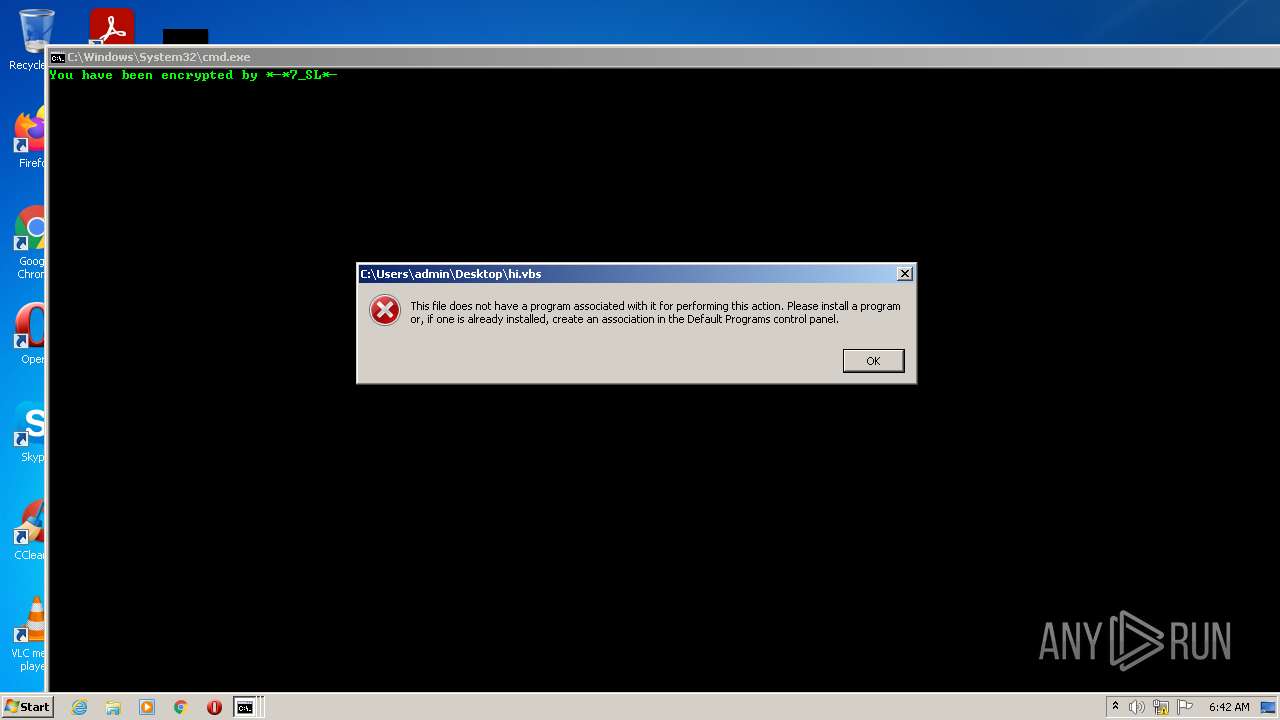
| 3372 | cmd.exe | C:\Users\admin\Desktop\hi.vbs | text | |
MD5:— | SHA256:— | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\admin.vbs | text | |
MD5:BE2433EC5B1B72B231CF97C8B0C96145 | SHA256:5A178D8B067815E23AE858D55A15894CD2E95ED8259FB69A97997DD38E4E61D9 | |||
| 3372 | cmd.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\19836.bat | text | |
MD5:— | SHA256:— | |||
| 3372 | cmd.exe | C:\Windows\system32\9K21JM10B.log | text | |
MD5:A1CA054A2E7FC91F32C820D90EA1C29D | SHA256:1013CD76DA0F74FC9BA2A5AEC5D408DBA4133DF7649E3E937C639289520B6733 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
6
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
resolver1.opendns.com |
| shared |
222.222.67.208.in-addr.arpa |
| unknown |
myip.opendns.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
932 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip .opendns .com in DNS lookup) |
932 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip .opendns .com in DNS lookup) |
932 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip .opendns .com in DNS lookup) |
932 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip .opendns .com in DNS lookup) |