| File name: | Release (1).rar |
| Full analysis: | https://app.any.run/tasks/72b07b25-0979-4764-a0bd-f956ca1a8fbf |
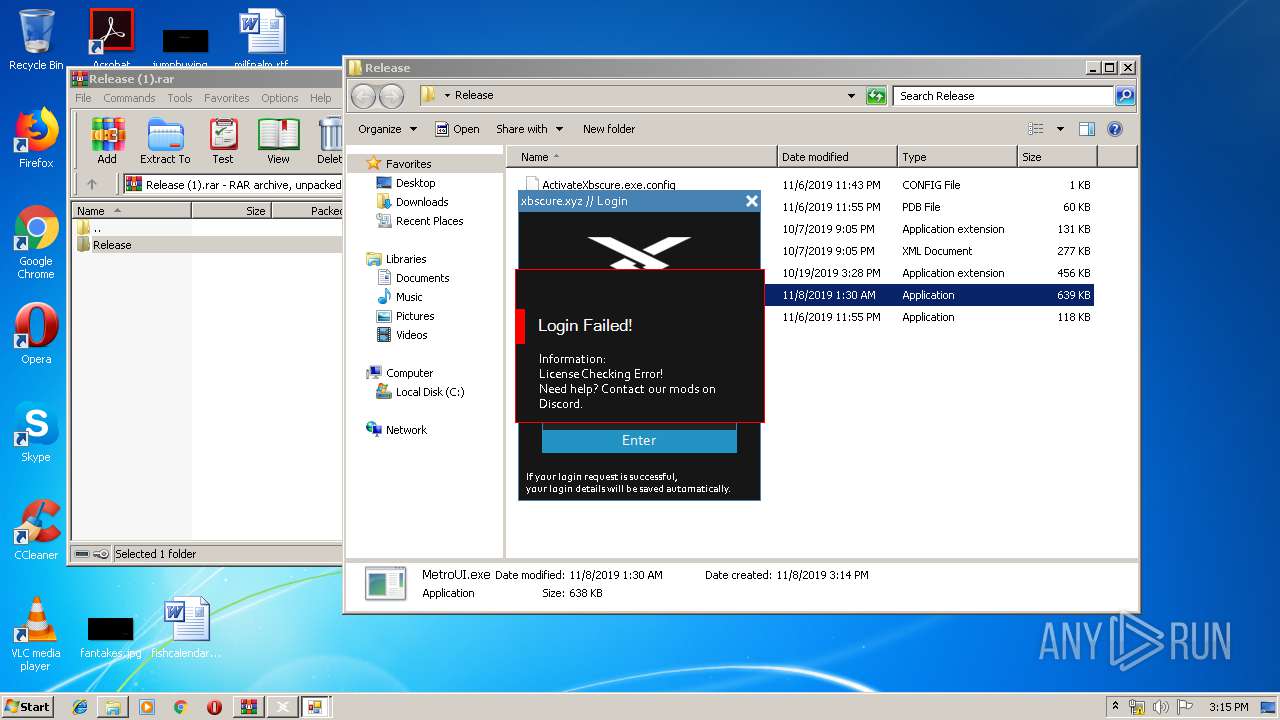
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 15:14:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F78A8471EF0A5094B30C0B0C4A685A72 |
| SHA1: | 0DFC1D692F9B4D1D9BFC8718941B898426918967 |
| SHA256: | BFC16BA7918BE216172DFACB78697F7AE5C529D631A7701EAAD889FDEFC4DD6E |
| SSDEEP: | 24576:ZbdSIKFuBK3lGeVBa122IPAqzy+1qGkEA:ZbdShuylGsBA38ASr1LbA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Environment values
- MetroUI.exe (PID: 2004)
INFO
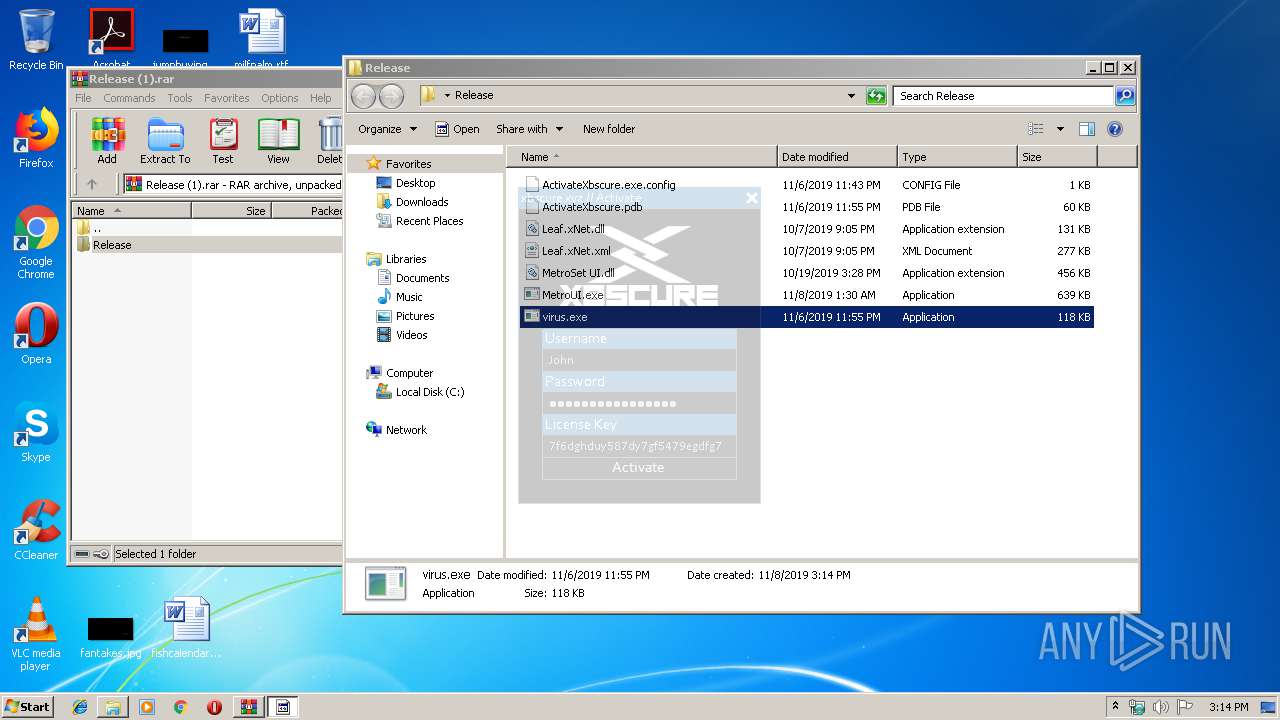
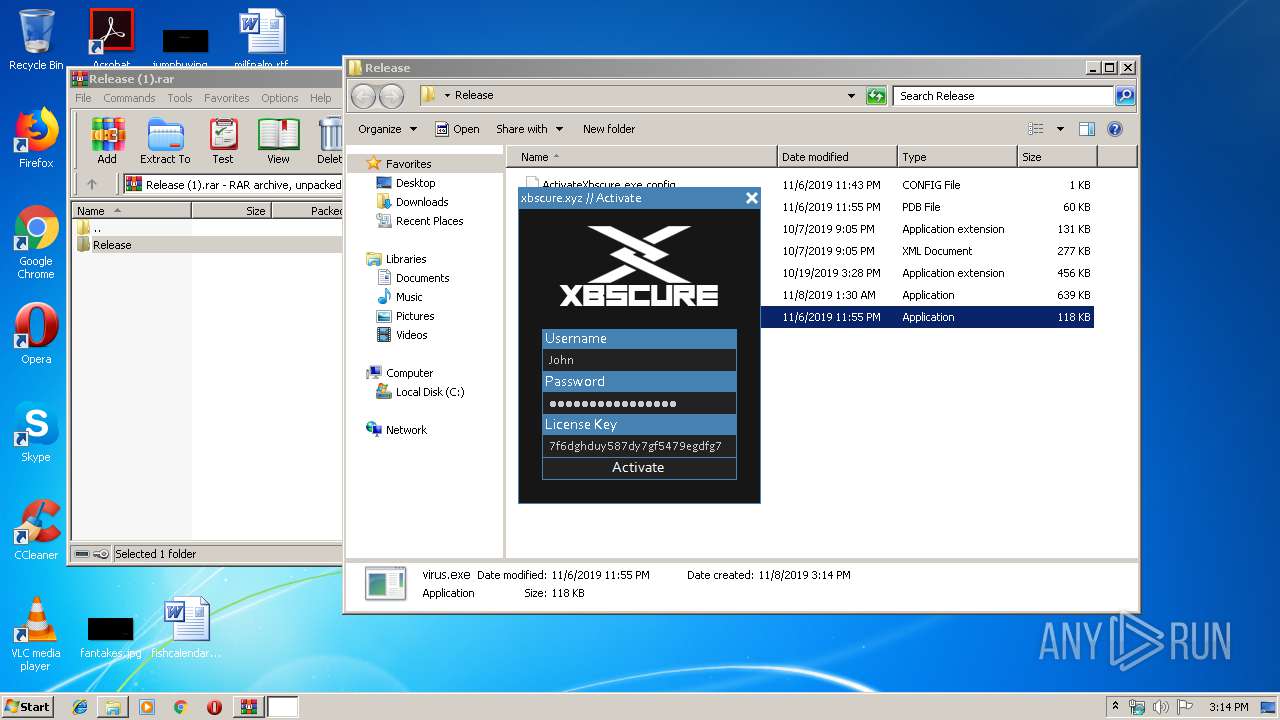
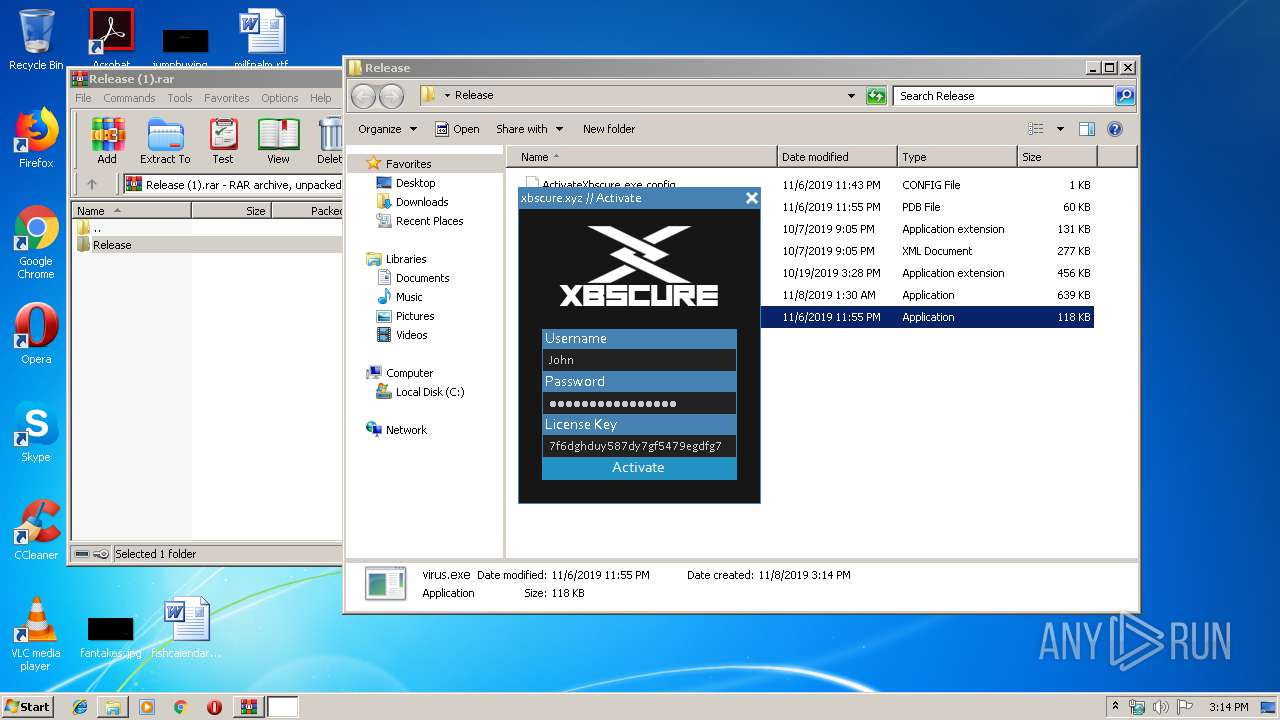
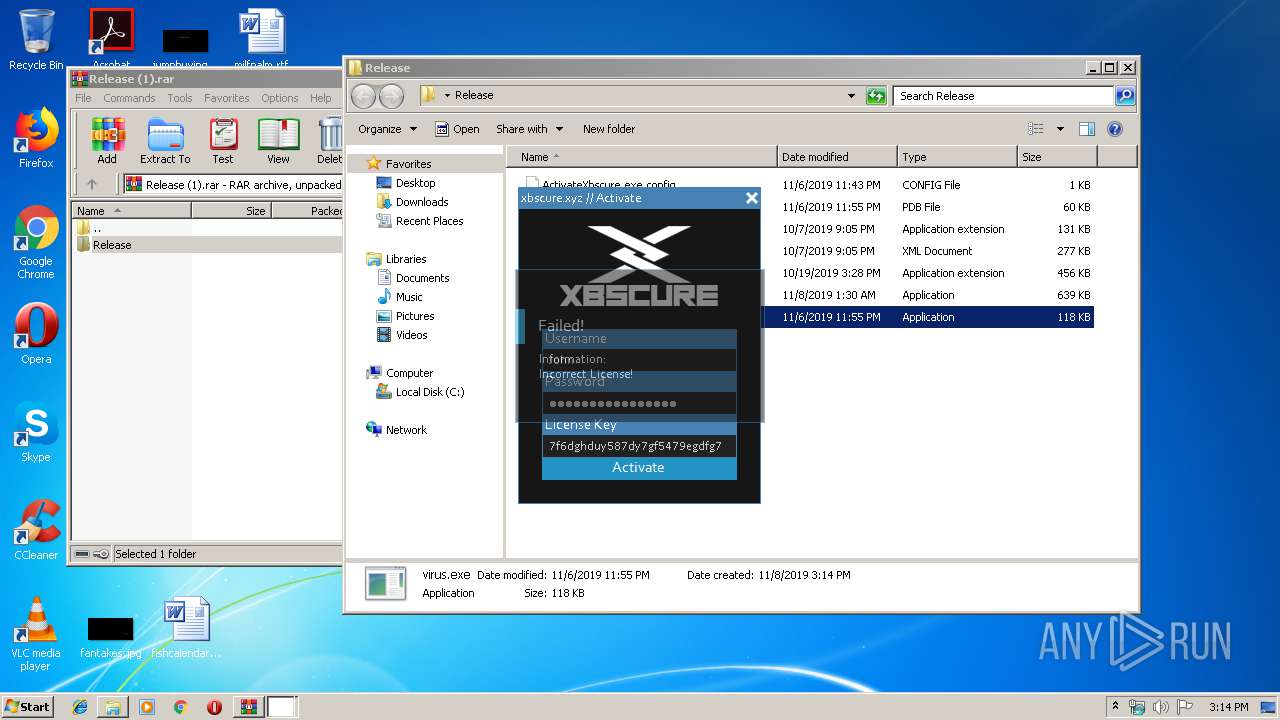
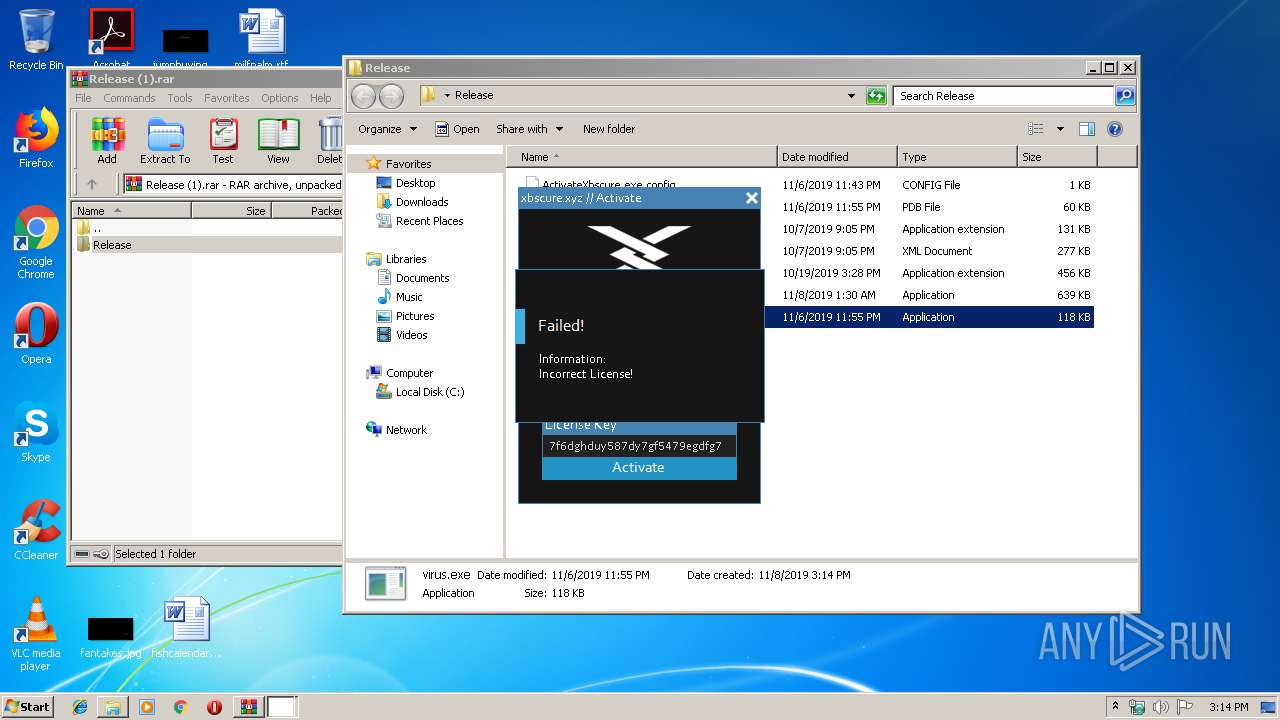
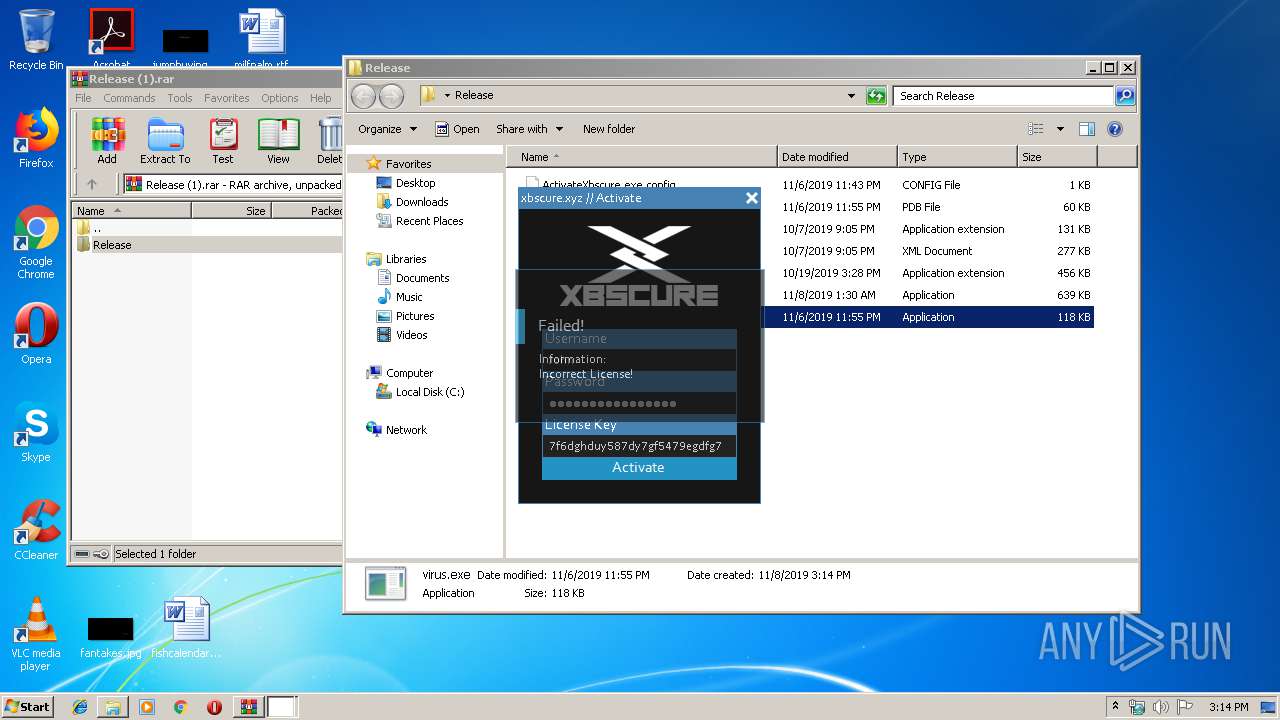
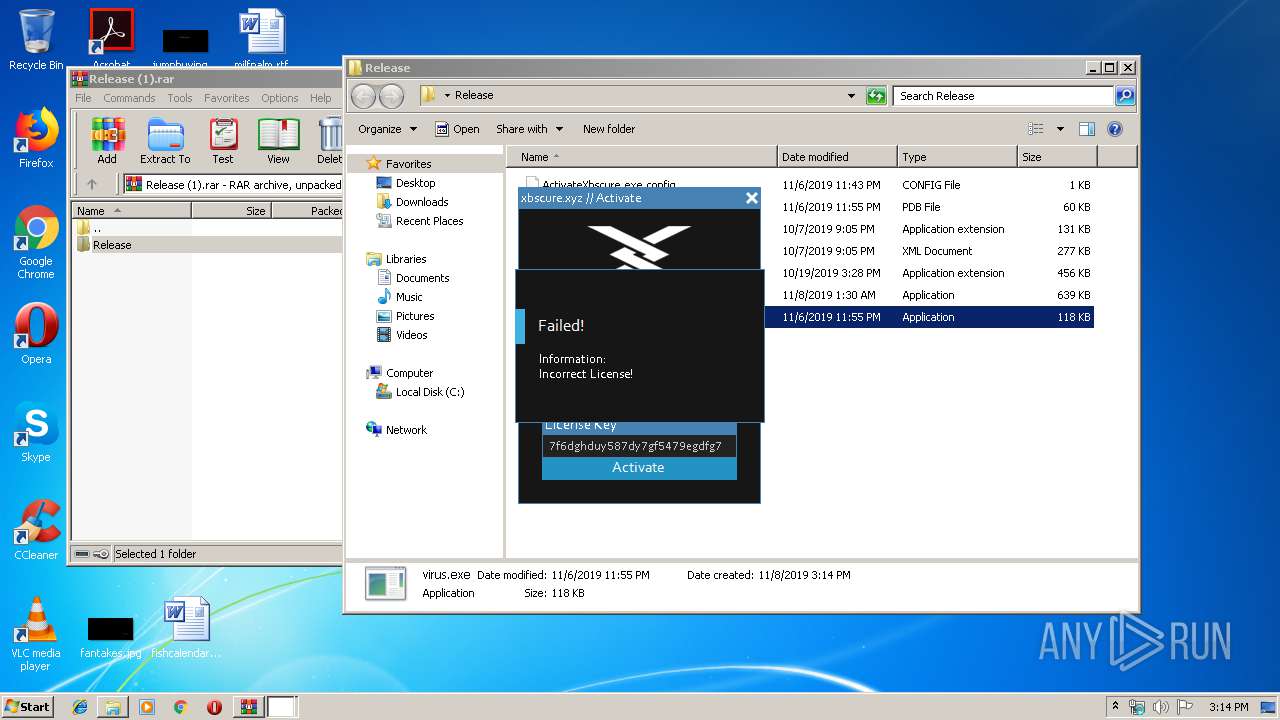
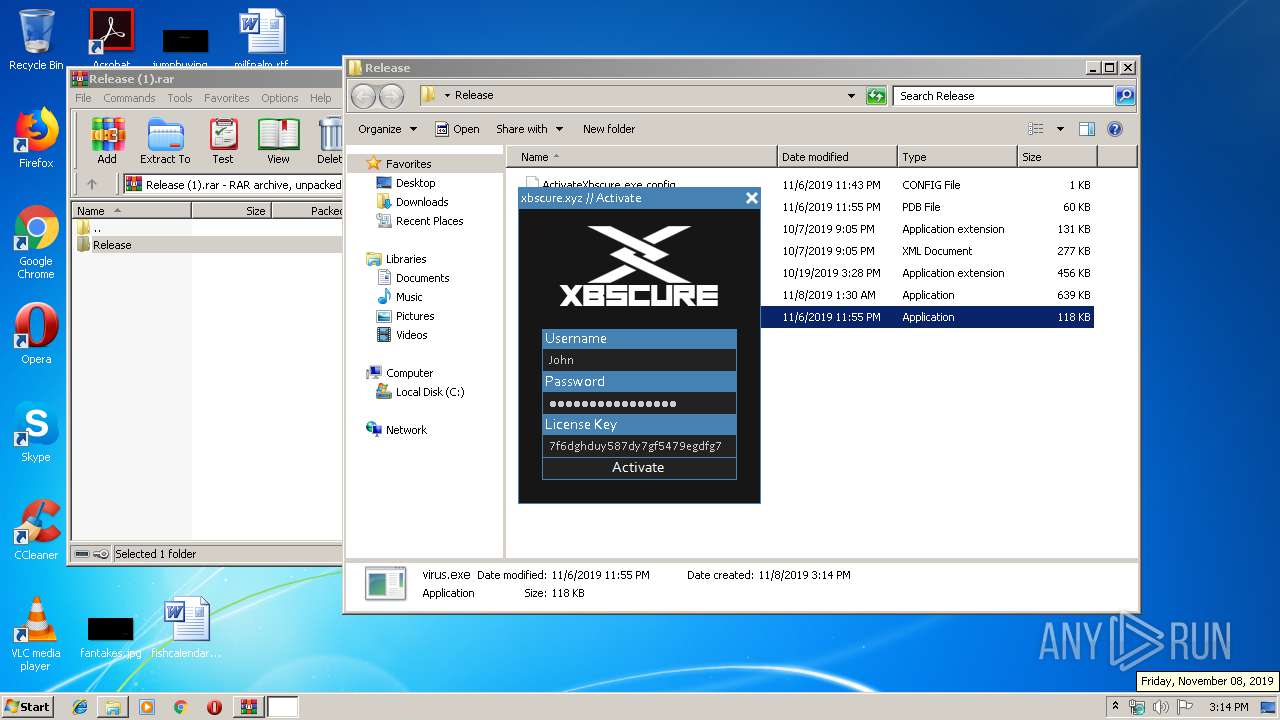
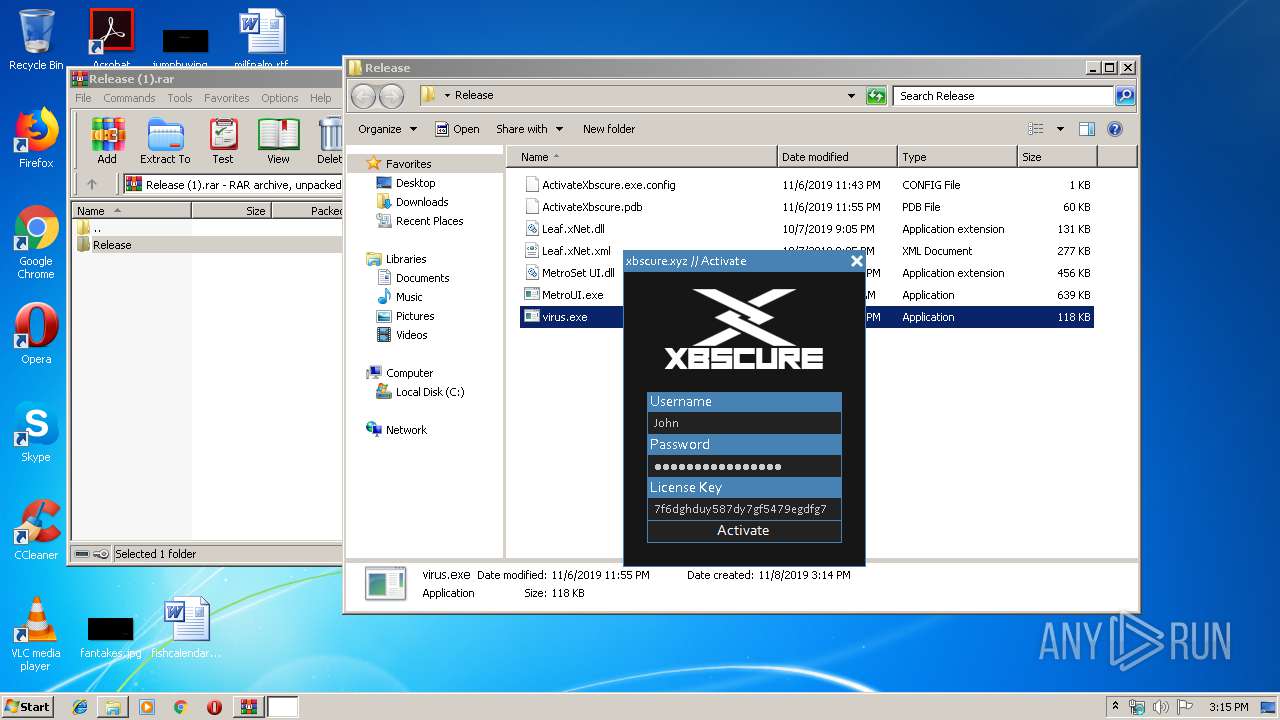
Manual execution by user
- virus.exe (PID: 2476)
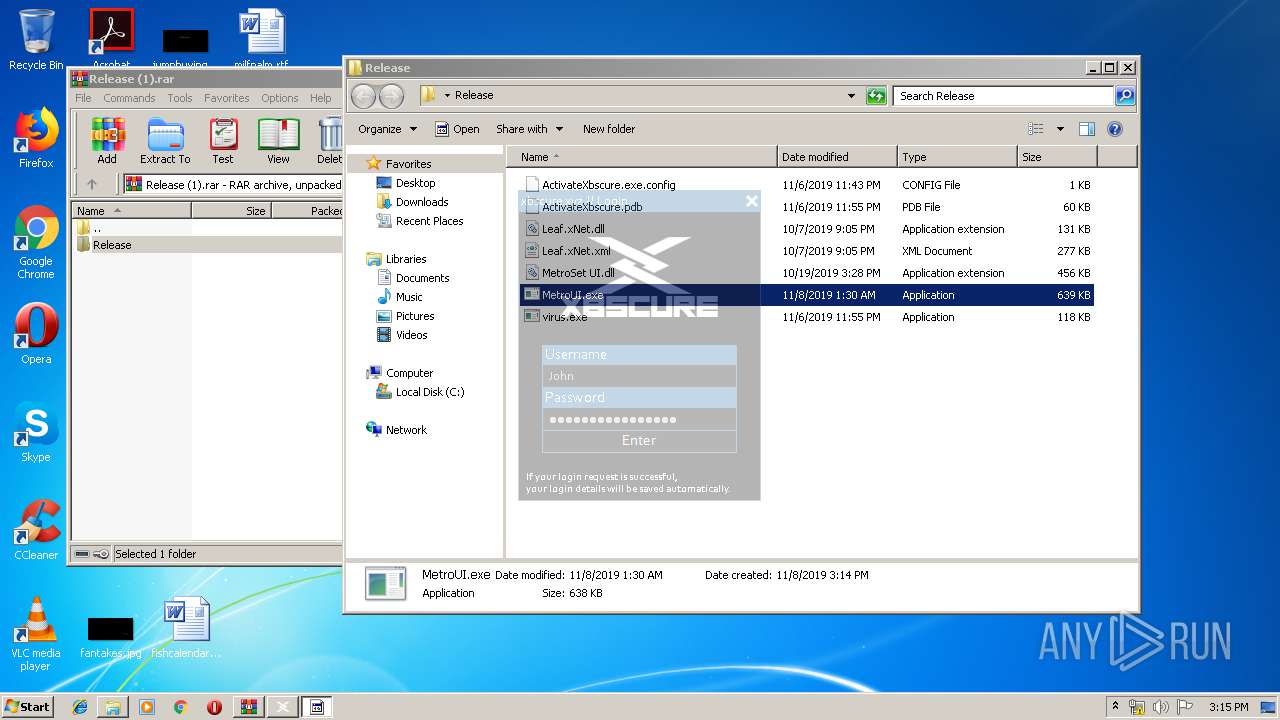
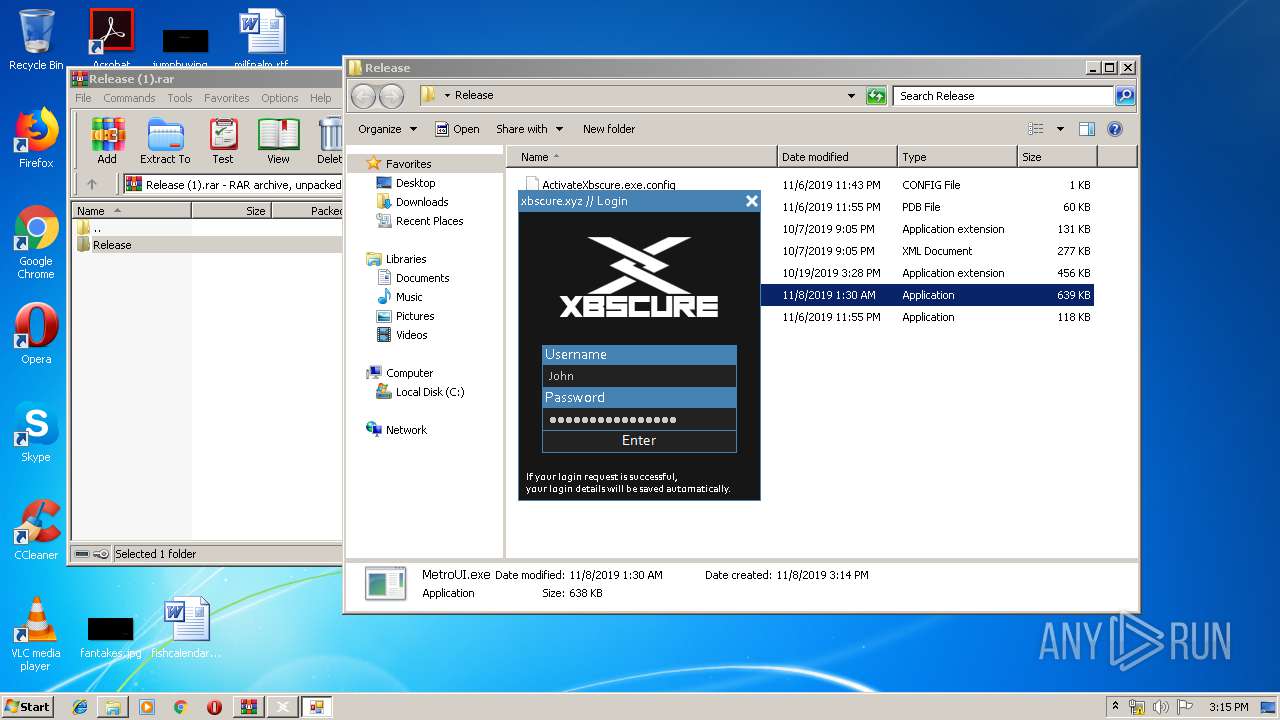
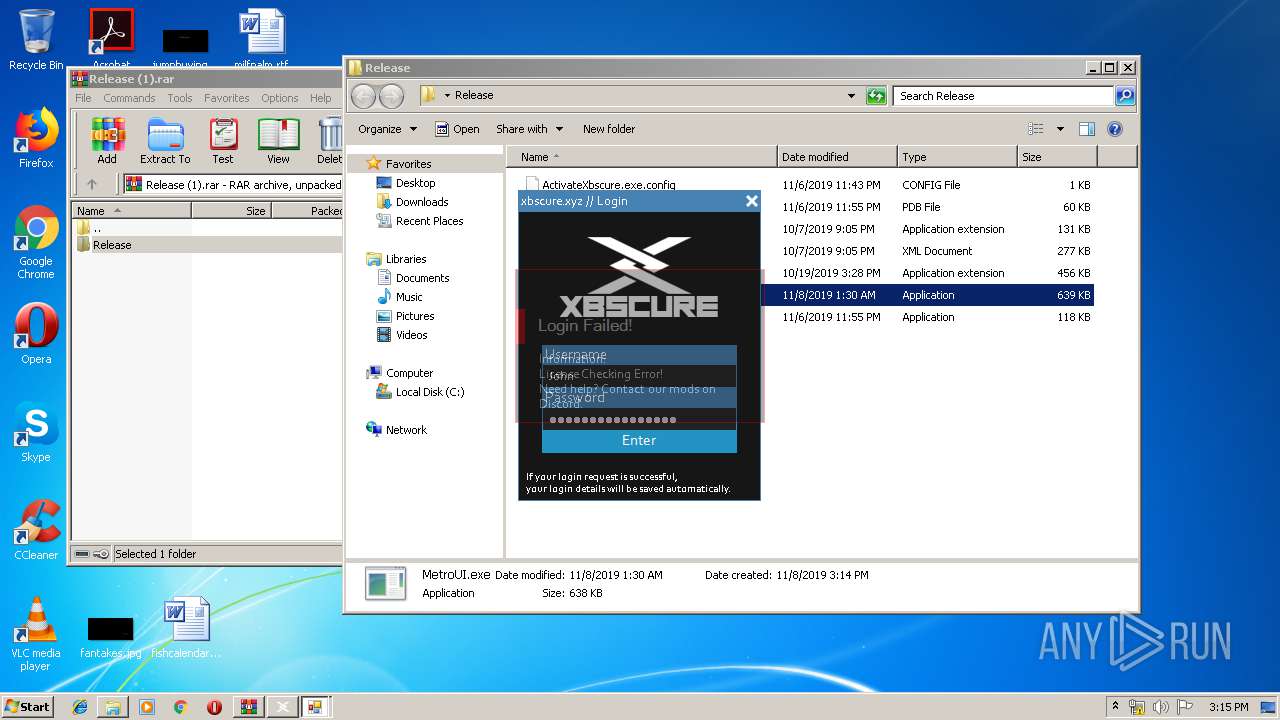
- MetroUI.exe (PID: 2004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
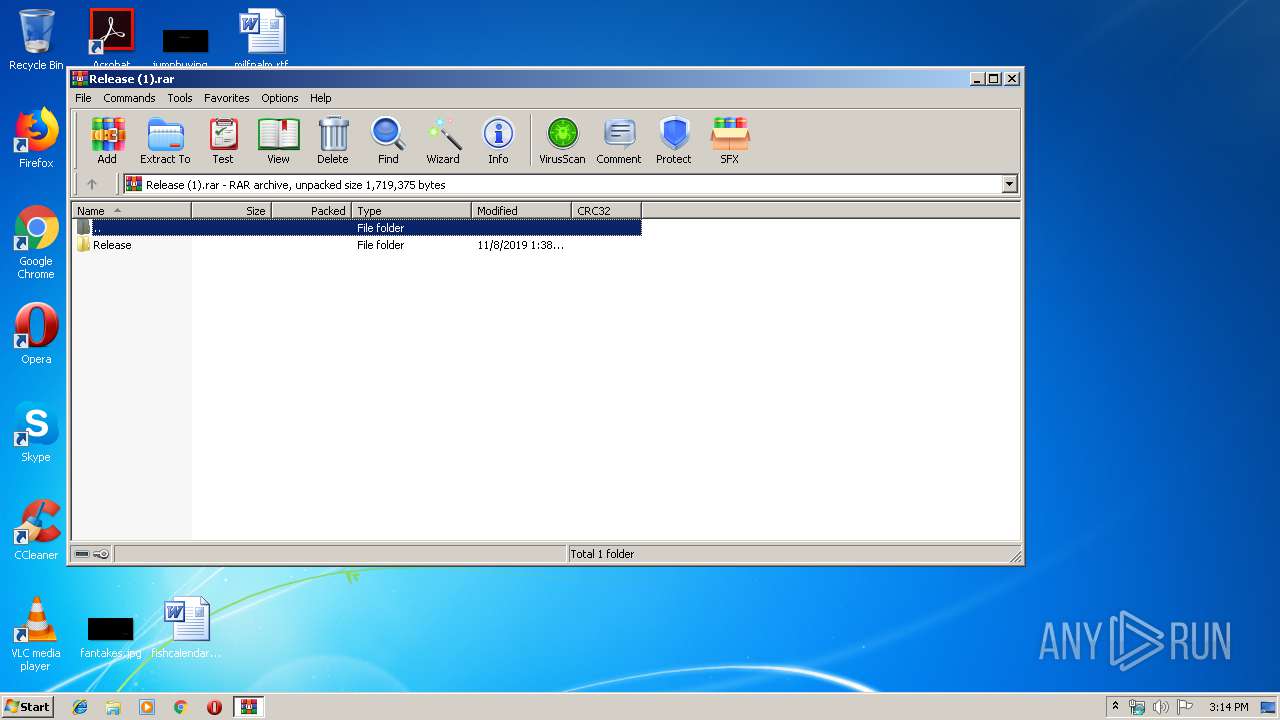
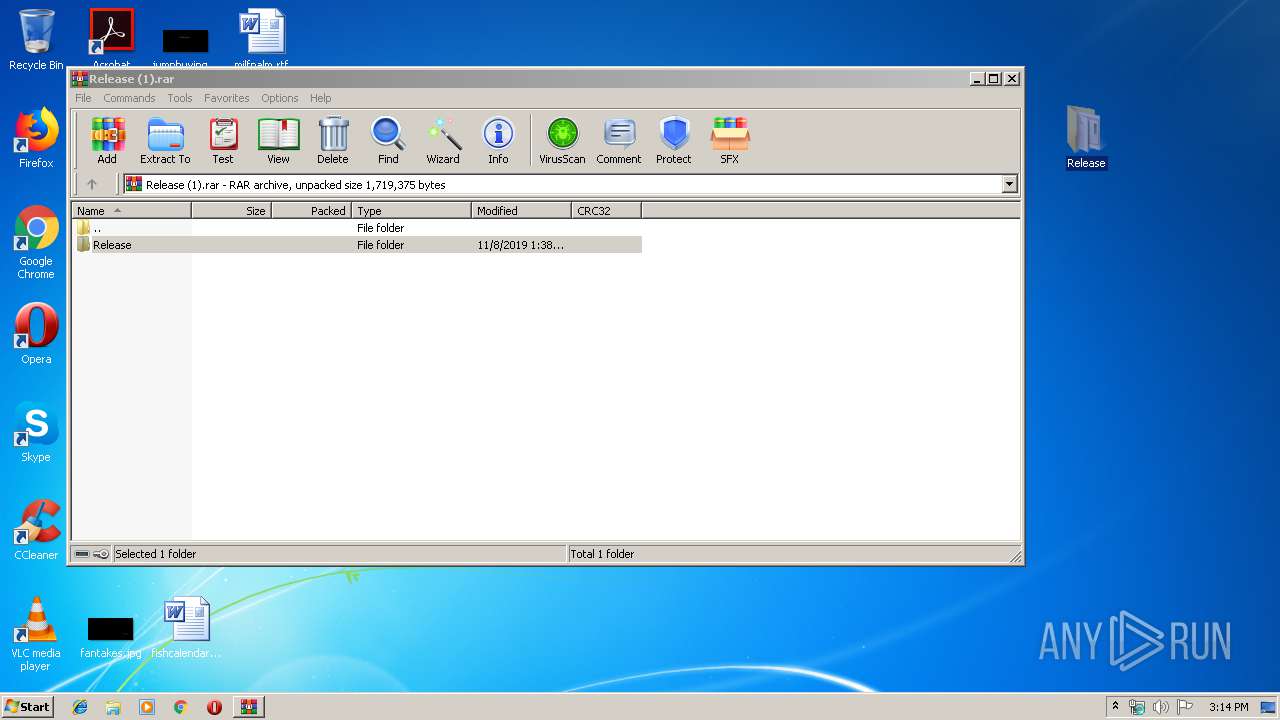
| 1880 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Release (1).rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
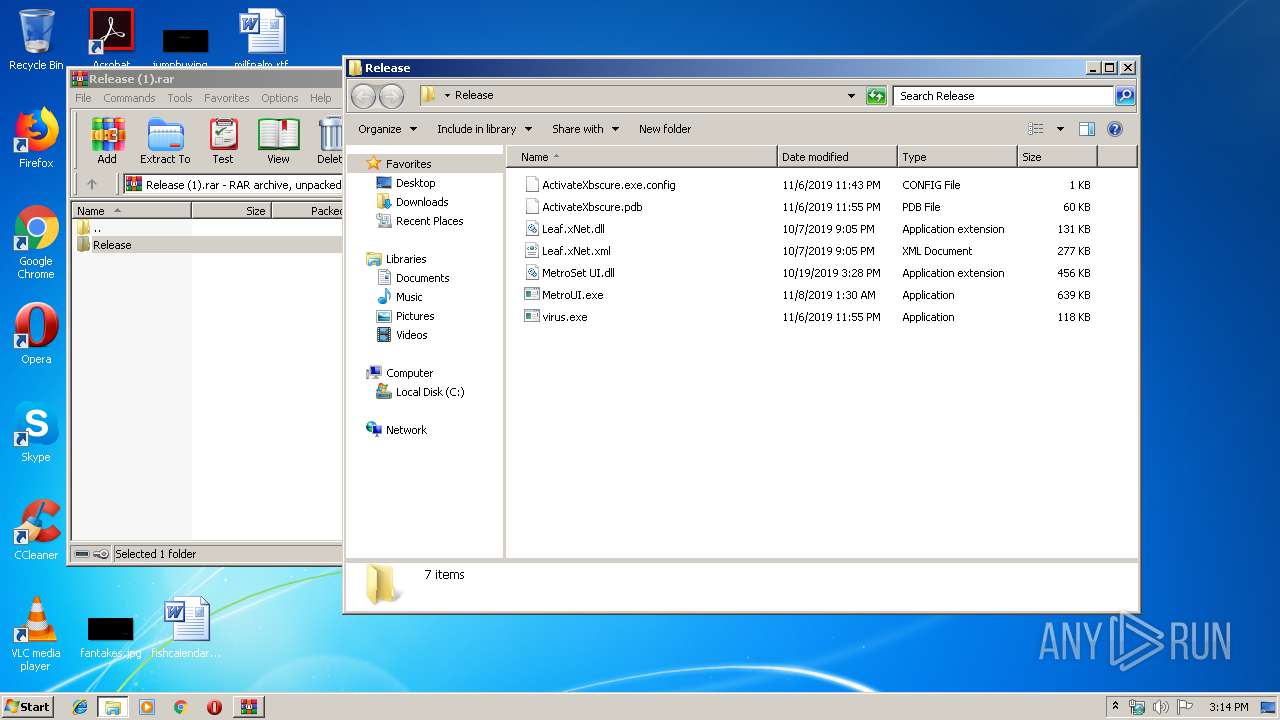
| 2004 | "C:\Users\admin\Desktop\Release\MetroUI.exe" | C:\Users\admin\Desktop\Release\MetroUI.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MetroUI Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2476 | "C:\Users\admin\Desktop\Release\virus.exe" | C:\Users\admin\Desktop\Release\virus.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ActivateXbscure Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
552
Read events
501
Write events
51
Delete events
0
Modification events
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Release (1).rar | |||
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2476) virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\virus_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2476) virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\virus_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1880.6680\Release\ActivateXbscure.exe.config | — | |
MD5:— | SHA256:— | |||
| 1880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1880.6680\Release\ActivateXbscure.pdb | — | |
MD5:— | SHA256:— | |||
| 1880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1880.6680\Release\Leaf.xNet.dll | — | |
MD5:— | SHA256:— | |||
| 1880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1880.6680\Release\Leaf.xNet.xml | — | |
MD5:— | SHA256:— | |||
| 1880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1880.6680\Release\MetroSet UI.dll | — | |
MD5:— | SHA256:— | |||
| 1880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1880.6680\Release\MetroUI.exe | — | |
MD5:— | SHA256:— | |||
| 1880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1880.6680\Release\virus.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2476 | virus.exe | GET | 404 | 37.48.70.196:80 | http://5h6j2ijgr32i4325h4u5kjh2ji3234i635tojgk45h43.cba.pl/fdryrWDTUYRSGHDSA56EWT4363/WR324IJIJRIJOIOTJ4OIU5OJ4T3I545JNOII4HTURFRG.html | NL | html | 2.05 Kb | malicious |
2004 | MetroUI.exe | GET | 404 | 37.48.70.196:80 | http://5h6j2ijgr32i4325h4u5kjh2ji3234i635tojgk45h43.cba.pl/fdryrWDTUYRSGHDSA56EWT4363/WR324IJIJRIJOIOTJ4OIU5OJ4T3I545JNOII4HTURFRG.html | NL | html | 2.05 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2476 | virus.exe | 37.48.70.196:80 | 5h6j2ijgr32i4325h4u5kjh2ji3234i635tojgk45h43.cba.pl | LeaseWeb Netherlands B.V. | NL | malicious |
— | — | 37.48.70.196:80 | 5h6j2ijgr32i4325h4u5kjh2ji3234i635tojgk45h43.cba.pl | LeaseWeb Netherlands B.V. | NL | malicious |
2476 | virus.exe | 145.14.144.179:443 | exceptional-schedul.000webhostapp.com | Hostinger International Limited | US | shared |
2004 | MetroUI.exe | 145.14.144.179:443 | exceptional-schedul.000webhostapp.com | Hostinger International Limited | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
5h6j2ijgr32i4325h4u5kjh2ji3234i635tojgk45h43.cba.pl |
| malicious |
exceptional-schedul.000webhostapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2476 | virus.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
2476 | virus.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |