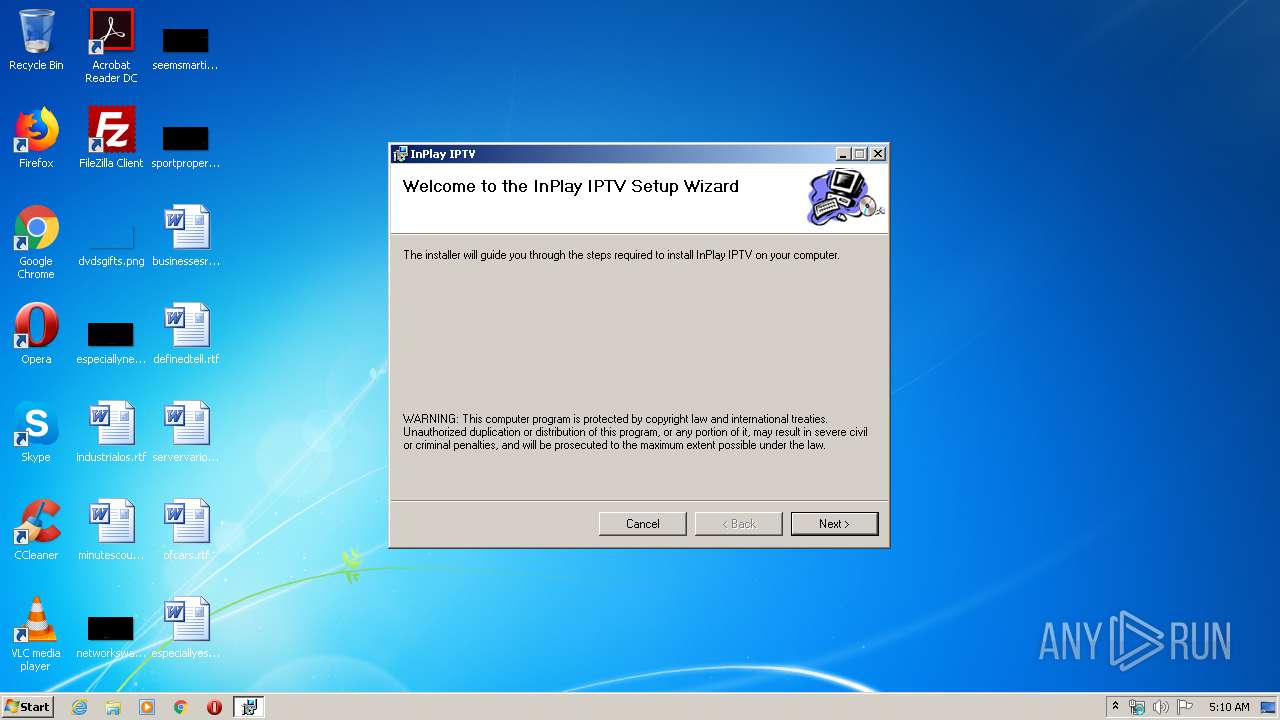
| File name: | http://www.cobainltd.co.uk/inplay/v4/InPlayTV.msi |
| Full analysis: | https://app.any.run/tasks/8fcf79b1-17c1-422e-a65b-1b5d0f1c9df5 |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2020, 05:10:38 |
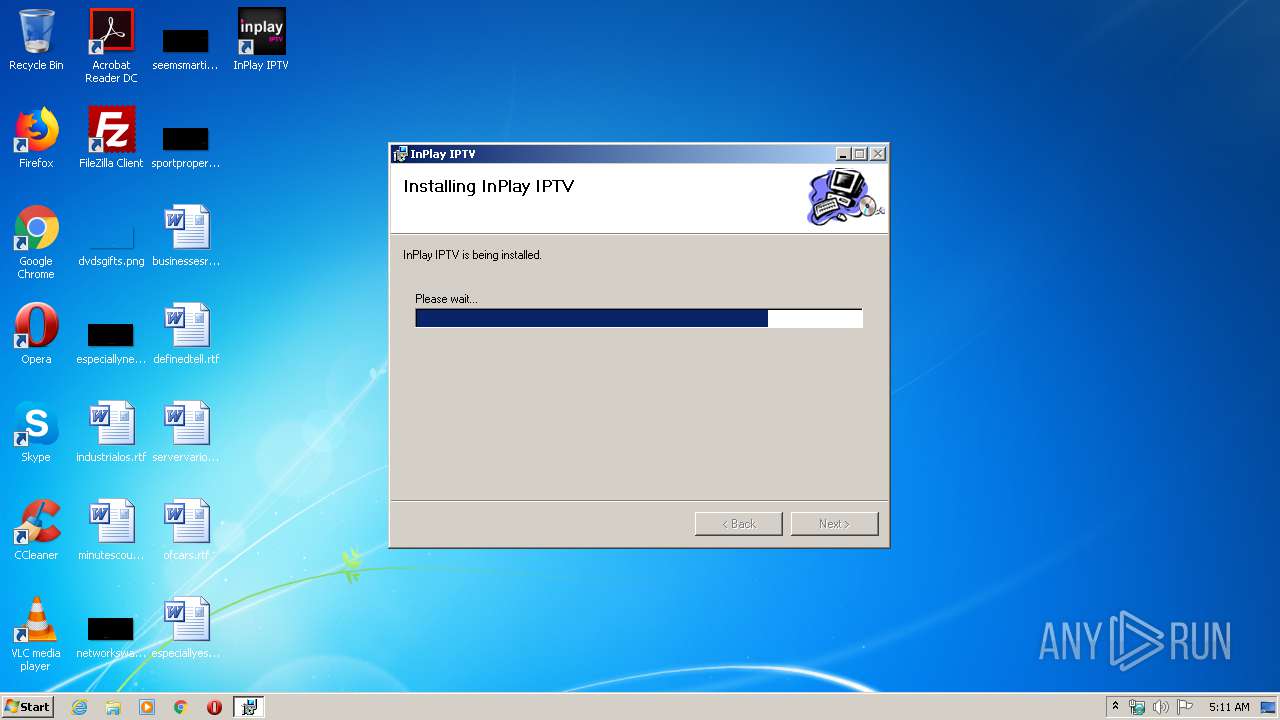
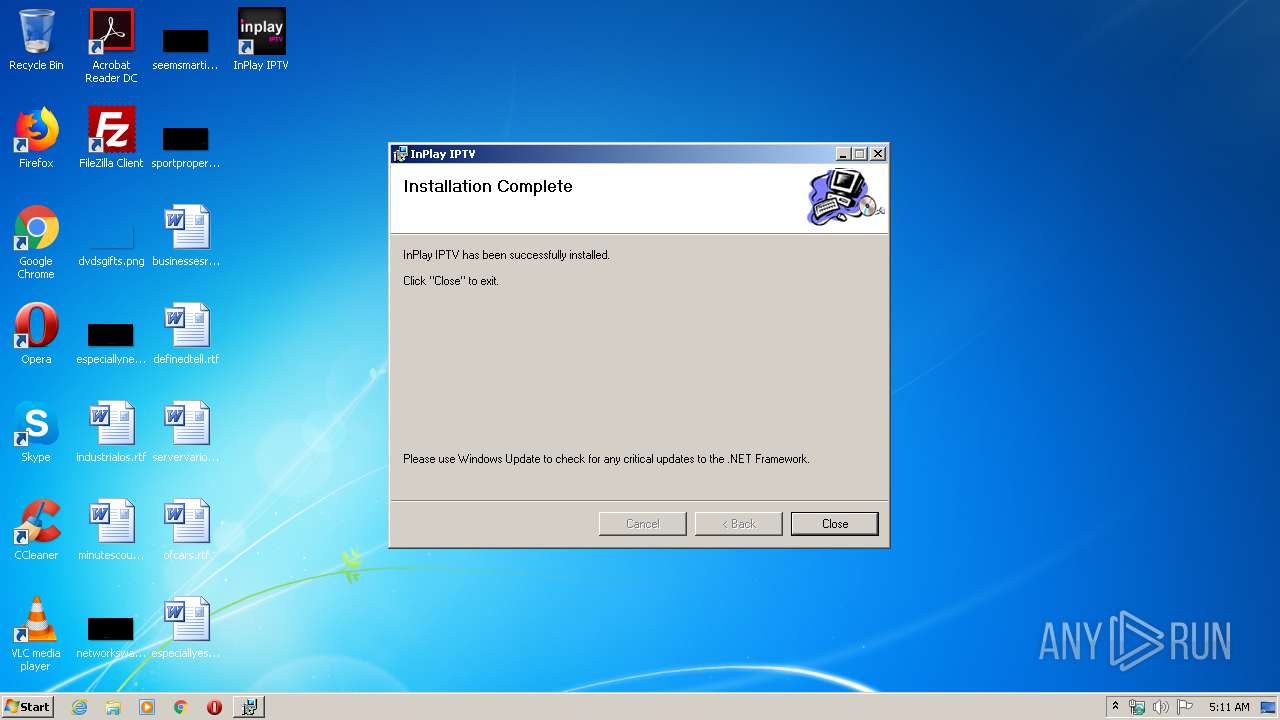
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {6C7090E5-EA88-4B9E-B09B-B2F852EA4B75}, Title: InPlay IPTV, Author: Cobain ltd, Comments: InPlay IPTV, Number of Words: 2, Last Saved Time/Date: Mon Sep 5 14:10:36 2011, Last Printed: Mon Sep 5 14:10:36 2011 |
| MD5: | 9C9FC86AA86C2668D910C6E2A004A515 |
| SHA1: | 05F042C94943266AAC877915BB46CF0EFFB83648 |
| SHA256: | BFBEFBE51570899BEEC0630D73ECC688D76994AD8B68C66469FEB45CA0314845 |
| SSDEEP: | 196608:YRRVDWkSTgY+hRUmTXoI5A02uR9MzV6cHtL:gRVSkS8Y+hRUiXoF02uR9MzV6cN |
MALICIOUS
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3640)
- MsiExec.exe (PID: 2284)
- MsiExec.exe (PID: 3304)
- regsvr32.exe (PID: 3380)
- WTConsole.exe (PID: 3276)
Registers / Runs the DLL via REGSVR32.EXE
- MsiExec.exe (PID: 952)
Application was dropped or rewritten from another process
- WTConsole.exe (PID: 3276)
Starts Visual C# compiler
- WTConsole.exe (PID: 3276)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 2184)
Executable content was dropped or overwritten
- msiexec.exe (PID: 852)
- MsiExec.exe (PID: 952)
Creates COM task schedule object
- MsiExec.exe (PID: 3640)
- regsvr32.exe (PID: 3380)
Creates files in the program directory
- WTConsole.exe (PID: 3276)
INFO
Searches for installed software
- msiexec.exe (PID: 852)
Application launched itself
- msiexec.exe (PID: 852)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 852)
Creates files in the program directory
- msiexec.exe (PID: 852)
- MsiExec.exe (PID: 952)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2184)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 952)
Creates a software uninstall entry
- msiexec.exe (PID: 852)
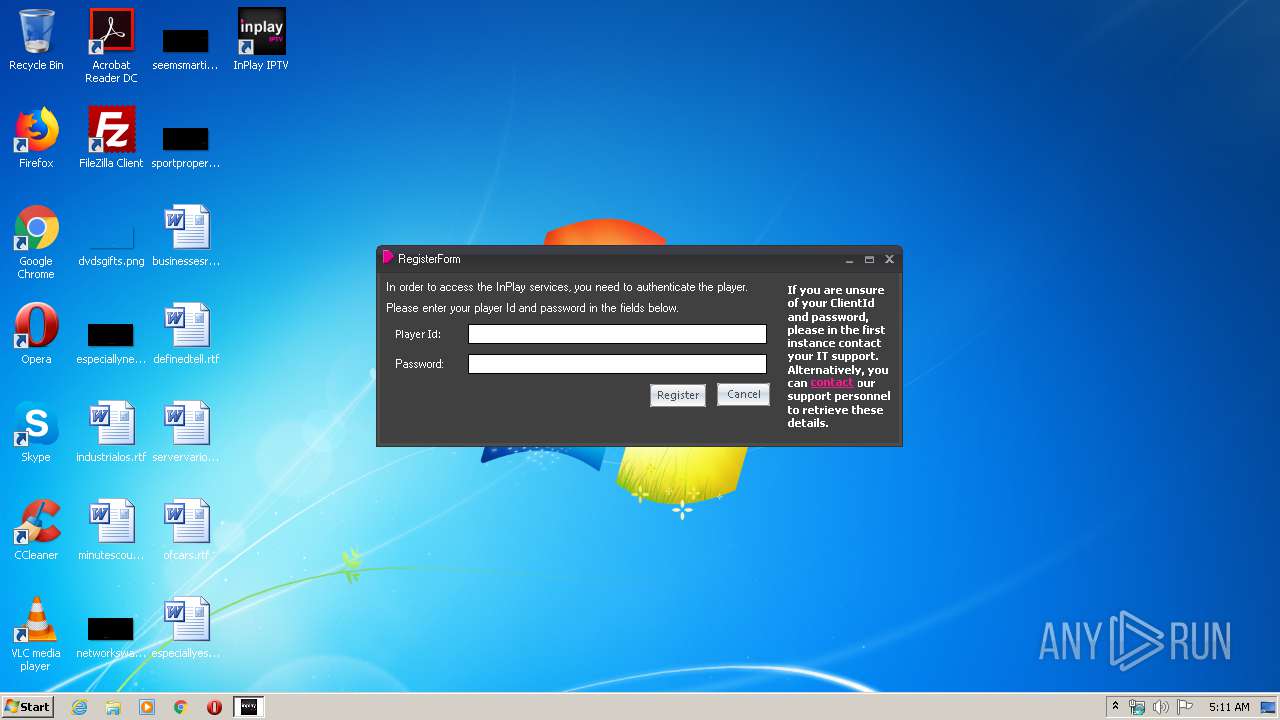
Manual execution by user
- WTConsole.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {6C7090E5-EA88-4B9E-B09B-B2F852EA4B75} |
| Title: | InPlay IPTV |
| Subject: | - |
| Author: | Cobain ltd |
| Keywords: | - |
| Comments: | InPlay IPTV |
| Words: | 2 |
| ModifyDate: | 2011:09:05 13:10:36 |
| LastPrinted: | 2011:09:05 13:10:36 |
Total processes
57
Monitored processes
18
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 852 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | C:\Windows\system32\MsiExec.exe -Embedding E959001F0EDCB64DE97D23F329DD5F5C M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1544 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1B4D.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1B4C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2012 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\icjqncll.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | WTConsole.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2112 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES17B3.tmp" "c:\Users\admin\AppData\Local\Temp\CSC17B2.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2128 | C:\Windows\system32\MsiExec.exe -Embedding 76CEC03285D76347A5B794A74EC11734 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Windows\system32\MsiExec.exe" /Y "C:\Program Files\Cobain ltd\InPlay IPTV\mc_dec_aac_ds.ax" | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\3nb4-qqd.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | WTConsole.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2788 | C:\Windows\system32\MsiExec.exe -Embedding 24C271561EFCA0C7992E57B618536FBB | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
972
Read events
572
Write events
388
Delete events
12
Modification events
| (PID) Process: | (852) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000074E2818062D6D50154030000000B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (852) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000074E2818062D6D50154030000000B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (852) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (852) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000001CB7D78062D6D50154030000000B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (852) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007619DA8062D6D50154030000600A0000E80300000100000000000000000000000A16C92642769342B3940B8233E5C4A10000000000000000 | |||
| (PID) Process: | (2184) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009267E88062D6D50188080000640C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2184) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009267E88062D6D50188080000D80A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2184) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009267E88062D6D501880800007C090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2184) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009267E88062D6D50188080000D40B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2184) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000000818F98062D6D50188080000D80A0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
21
Suspicious files
5
Text files
10
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI7150.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI71CE.tmp | — | |
MD5:— | SHA256:— | |||
| 852 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 852 | msiexec.exe | C:\Windows\Installer\a6b7a0.msi | — | |
MD5:— | SHA256:— | |||
| 852 | msiexec.exe | C:\Windows\Installer\MSIBE76.tmp | — | |
MD5:— | SHA256:— | |||
| 852 | msiexec.exe | C:\Windows\Installer\MSIBF71.tmp | — | |
MD5:— | SHA256:— | |||
| 852 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFB3B20AE4A1B73B28.TMP | — | |
MD5:— | SHA256:— | |||
| 2184 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 852 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 852 | msiexec.exe | C:\Program Files\Cobain ltd\InPlay IPTV\CustomMessages.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
WTConsole.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
WTConsole.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
WTConsole.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
WTConsole.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
WTConsole.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
WTConsole.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
WTConsole.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
WTConsole.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
WTConsole.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
WTConsole.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|