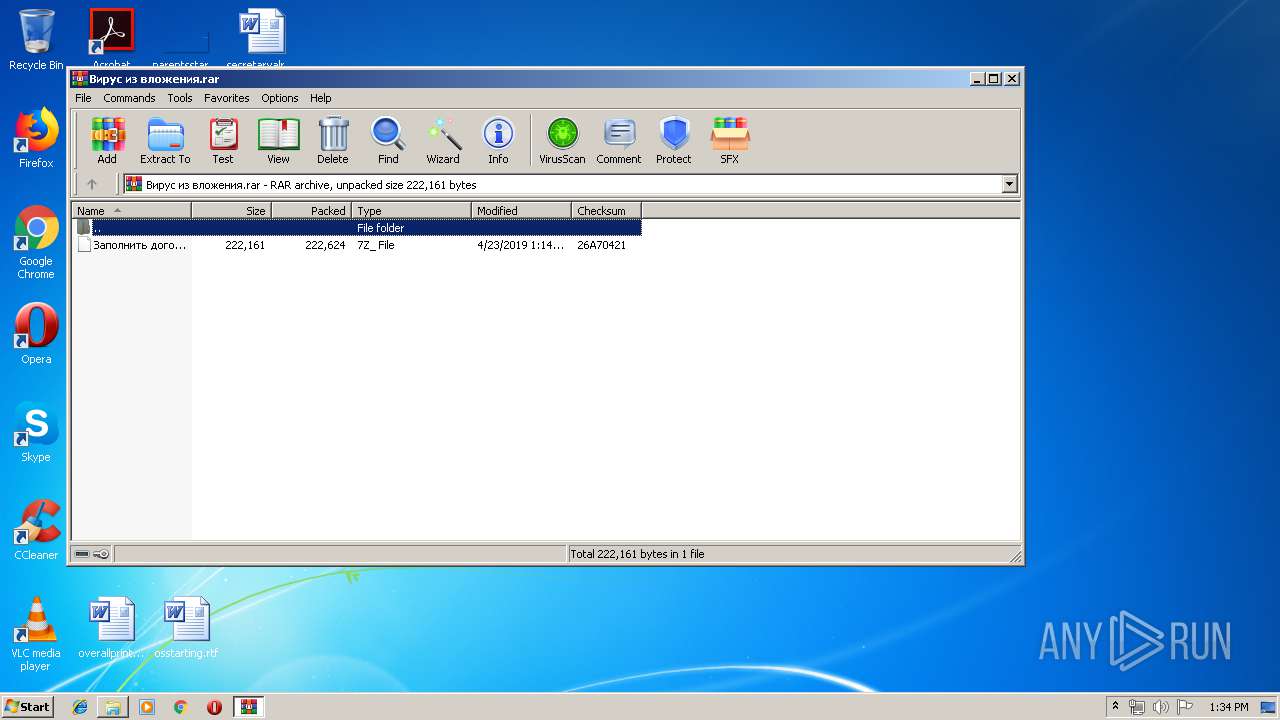
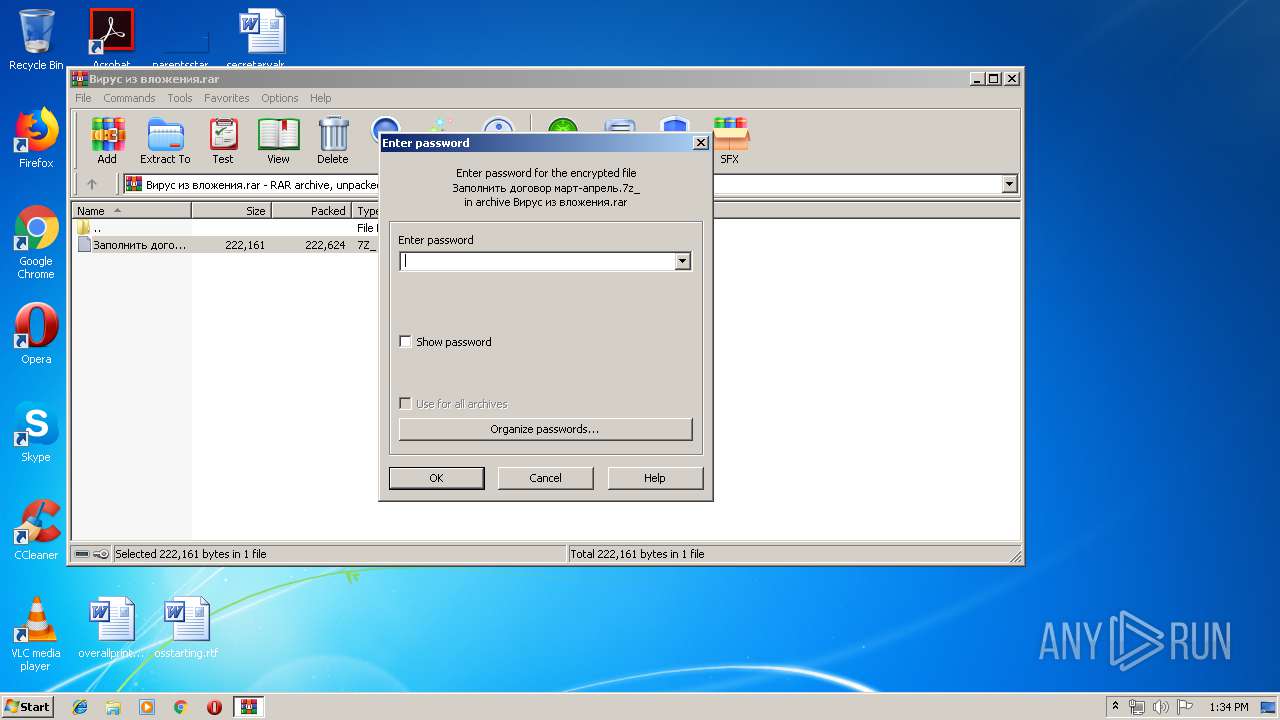
| File name: | Вирус из вложения.rar |
| Full analysis: | https://app.any.run/tasks/b20068db-1e41-4433-b2ce-c9f4c567831b |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:34:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 8948D28CF6D6D9766012BB7A9CD4CD0C |
| SHA1: | F2086A2A206F3EE5D20F44028A4D618EA41686C4 |
| SHA256: | BFB326C7DDE463A98CFD734C7A79D564E66CE93ADFFC2DF908771E696988810E |
| SSDEEP: | 6144:shweYNW1gDlZbpLrAknASoyLhGmjHQWdP4mp:shyNW81LrAYh5Hzwi |
MALICIOUS
Changes the autorun value in the registry
- Заполнить договор март-апрель.exe (PID: 3984)
Application was dropped or rewritten from another process
- Заполнить договор март-апрель.exe (PID: 3984)
Loads dropped or rewritten executable
- rundll32.exe (PID: 1524)
- rundll32.exe (PID: 3608)
- explorer.exe (PID: 2044)
- WinRAR.exe (PID: 2956)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 1524)
Changes settings of System certificates
- rundll32.exe (PID: 3608)
SUSPICIOUS
Executable content was dropped or overwritten
- Заполнить договор март-апрель.exe (PID: 3984)
- WinRAR.exe (PID: 2956)
- rundll32.exe (PID: 1524)
Creates files in the user directory
- explorer.exe (PID: 2044)
Reads Internet Cache Settings
- explorer.exe (PID: 2044)
Uses RUNDLL32.EXE to load library
- Заполнить договор март-апрель.exe (PID: 3984)
Creates files in the program directory
- rundll32.exe (PID: 1524)
Connects to server without host name
- rundll32.exe (PID: 3608)
Adds / modifies Windows certificates
- rundll32.exe (PID: 3608)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
7
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
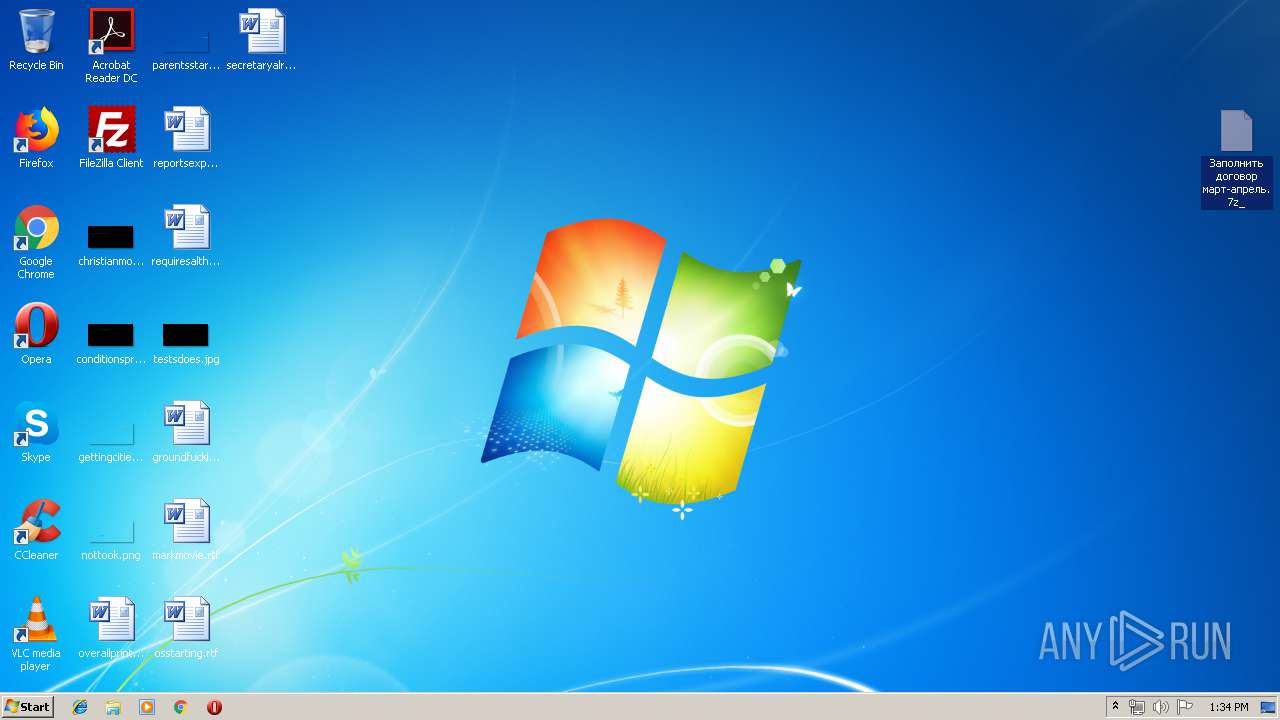
| 916 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Вирус из вложения.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1524 | rundll32.exe v34.dll,DllGetClassObject root 000000000000 Post Install program: <None> | C:\Windows\system32\rundll32.exe | Заполнить договор март-апрель.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
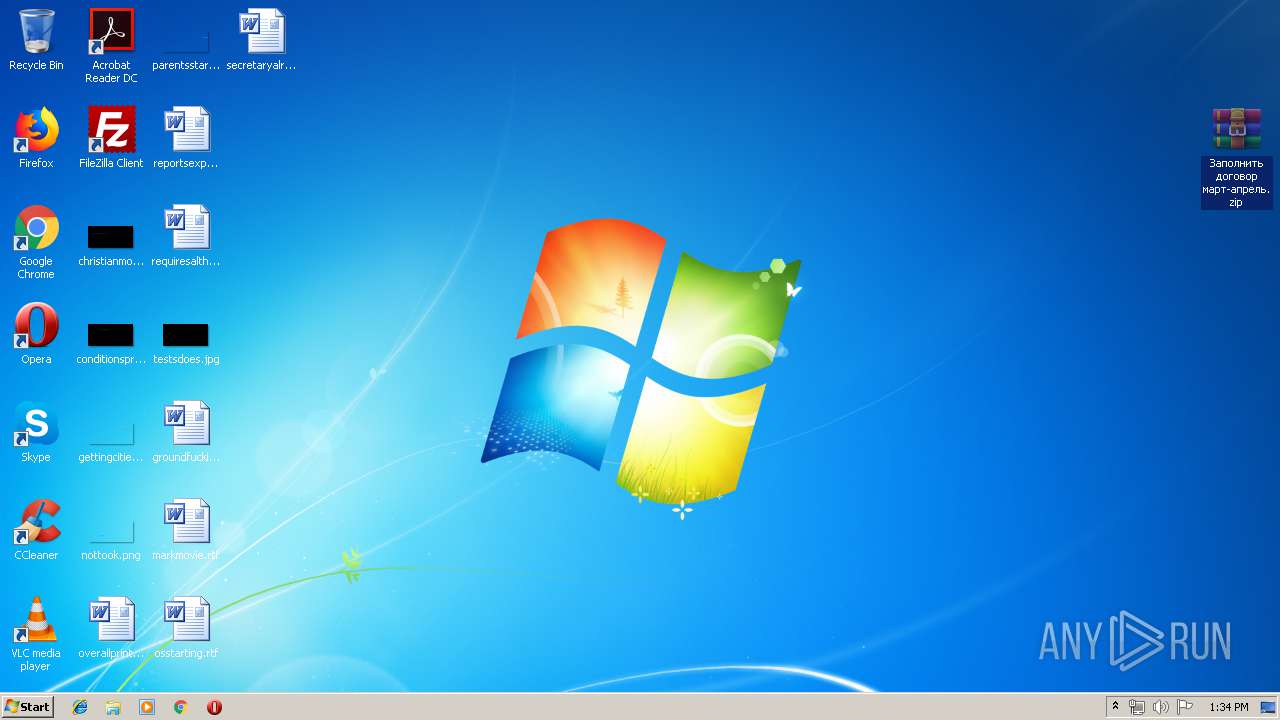
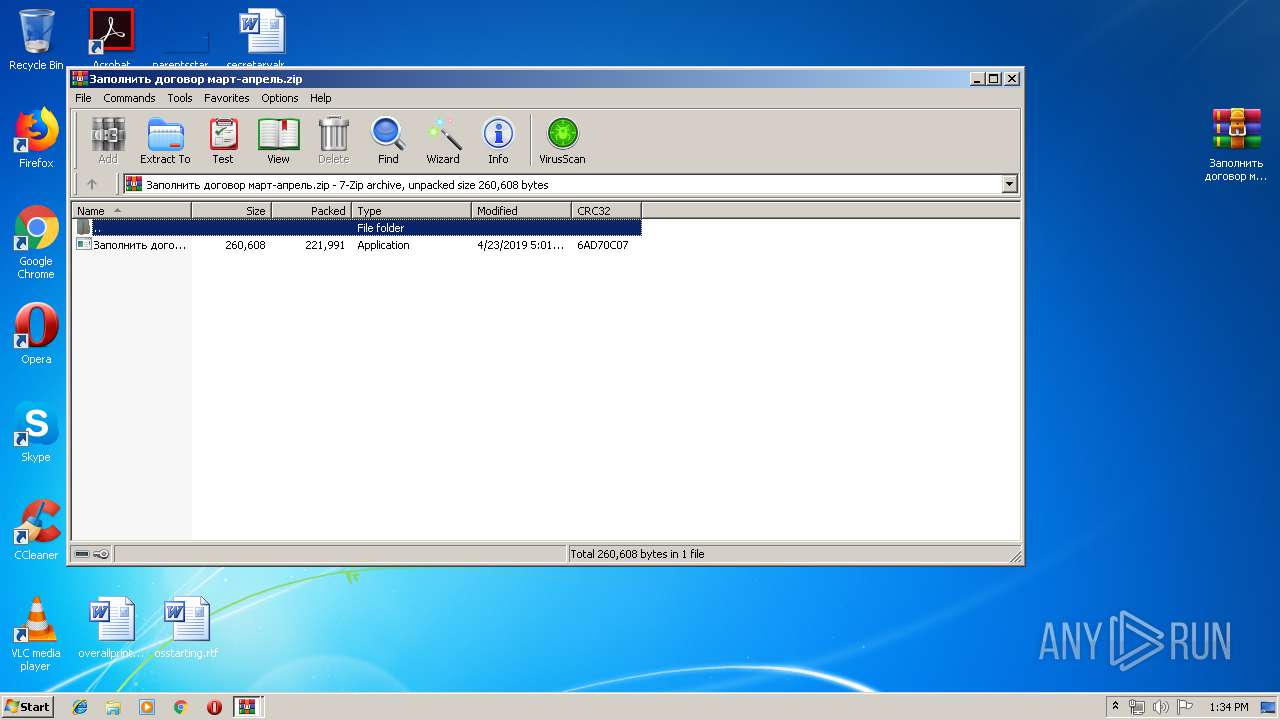
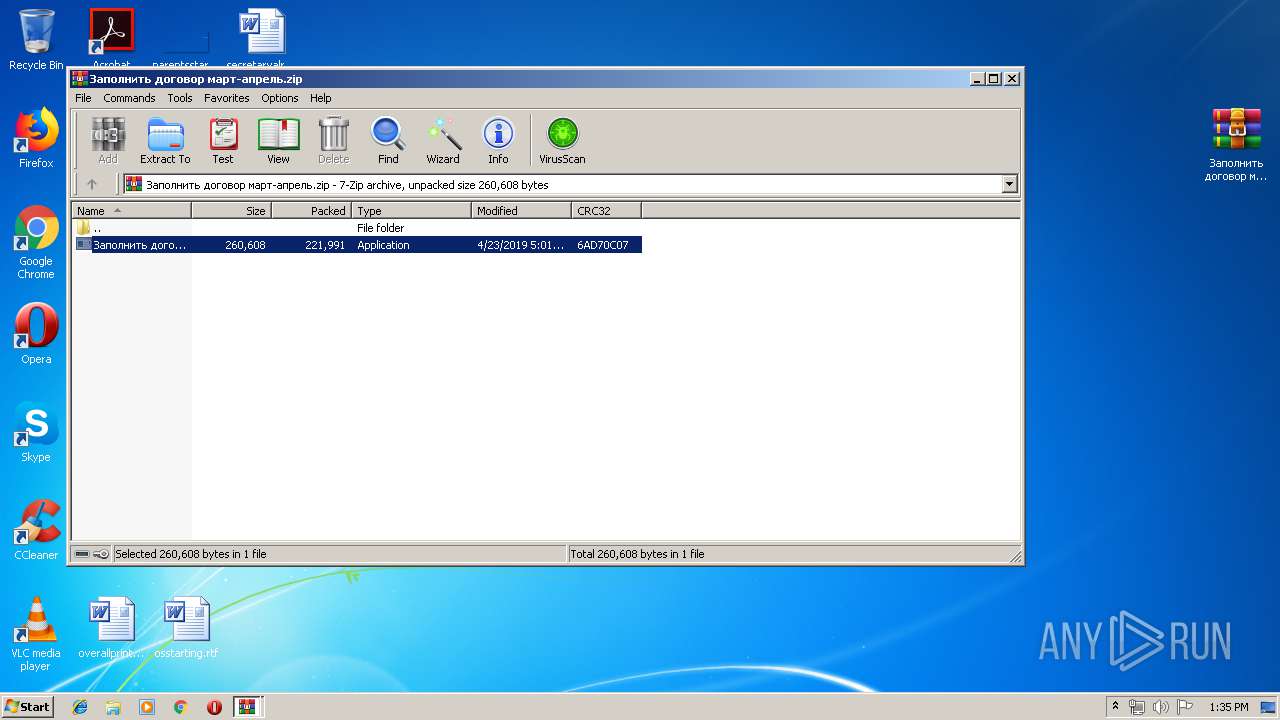
| 1832 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Заполнить договор март-апрель.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Заполнить договор март-апрель.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3608 | rundll32.exe "C:\ProgramData\2401bf603c90\2702bc633f93.dat",DllGetClassObject root | C:\Windows\system32\rundll32.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2956.40472\Заполнить договор март-апрель.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2956.40472\Заполнить договор март-апрель.exe | WinRAR.exe | ||||||||||||
User: admin Company: Корпорация Майкрософт Integrity Level: MEDIUM Description: Самоизвлечение CAB-файлов Win32 Exit code: 0 Version: 6.00.2900.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
Total events
3 021
Read events
2 924
Write events
94
Delete events
3
Modification events
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Вирус из вложения.rar | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
3
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb916.37403\Заполнить договор март-апрель.7z_ | compressed | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Заполнить договор март-апрель.zip.lnk | lnk | |
MD5:— | SHA256:— | |||
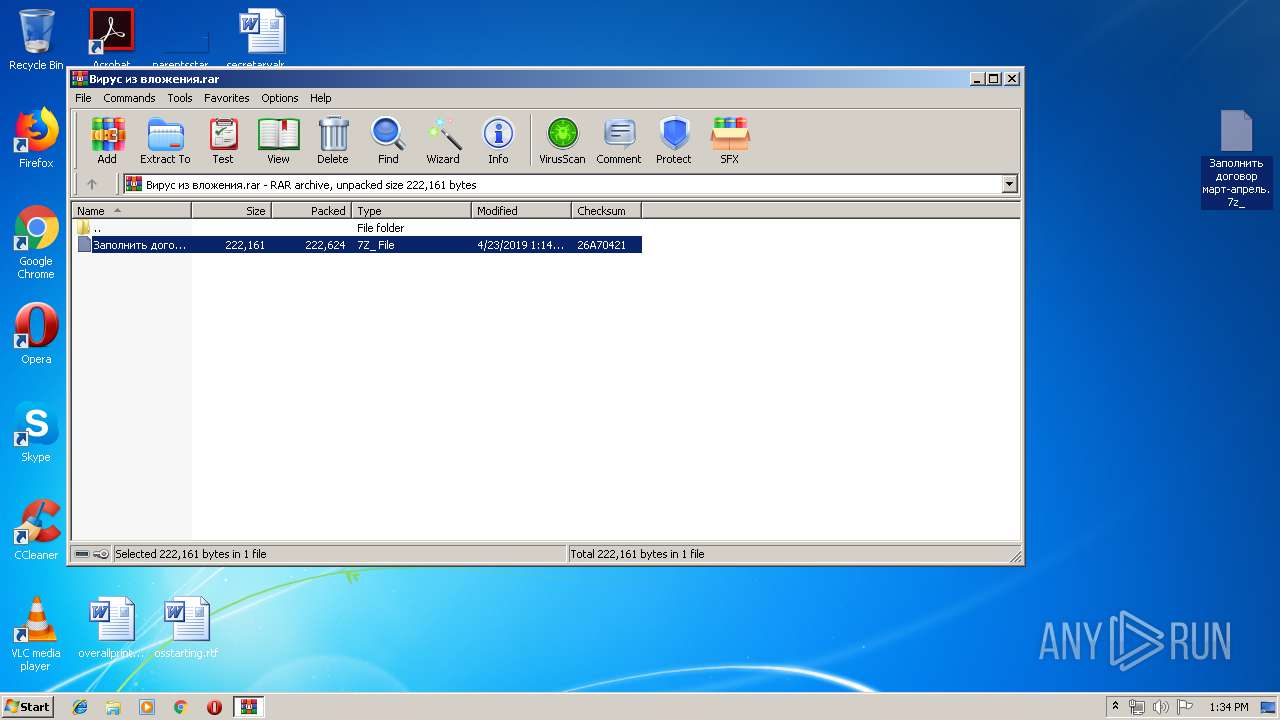
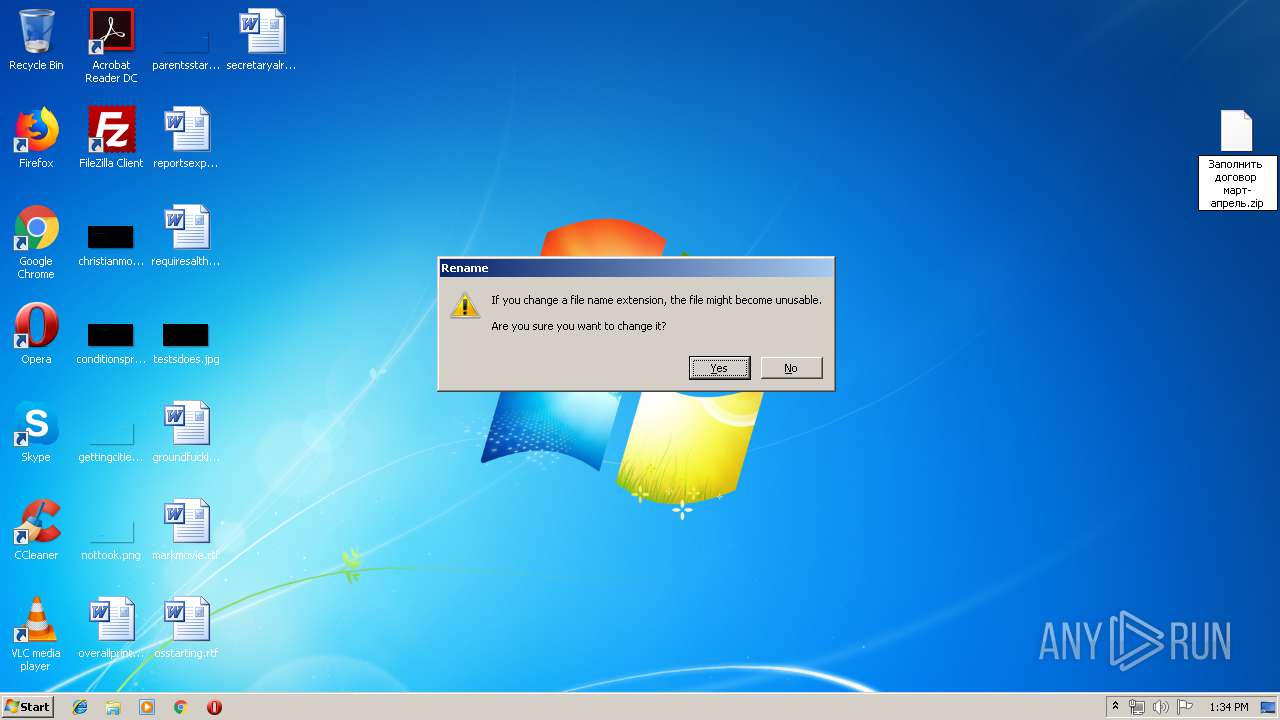
| 2044 | explorer.exe | C:\Users\admin\Desktop\Заполнить договор март-апрель.7z_ | compressed | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019042320190424\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 3984 | Заполнить договор март-апрель.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\v34.dll | executable | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\Desktop\Заполнить договор март-апрель.zip | compressed | |
MD5:— | SHA256:— | |||
| 1524 | rundll32.exe | C:\ProgramData\2401bf603c90\2702bc633f93.dat | executable | |
MD5:— | SHA256:— | |||
| 2956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2956.40472\Заполнить договор март-апрель.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3608 | rundll32.exe | POST | 200 | 195.123.245.202:80 | http://195.123.245.202/index.php | UA | binary | 9 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3608 | rundll32.exe | 52.36.204.116:443 | namecoin.cyphrs.com | Amazon.com, Inc. | US | unknown |
3608 | rundll32.exe | 195.123.245.202:80 | — | — | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
namecoin.cyphrs.com |
| unknown |