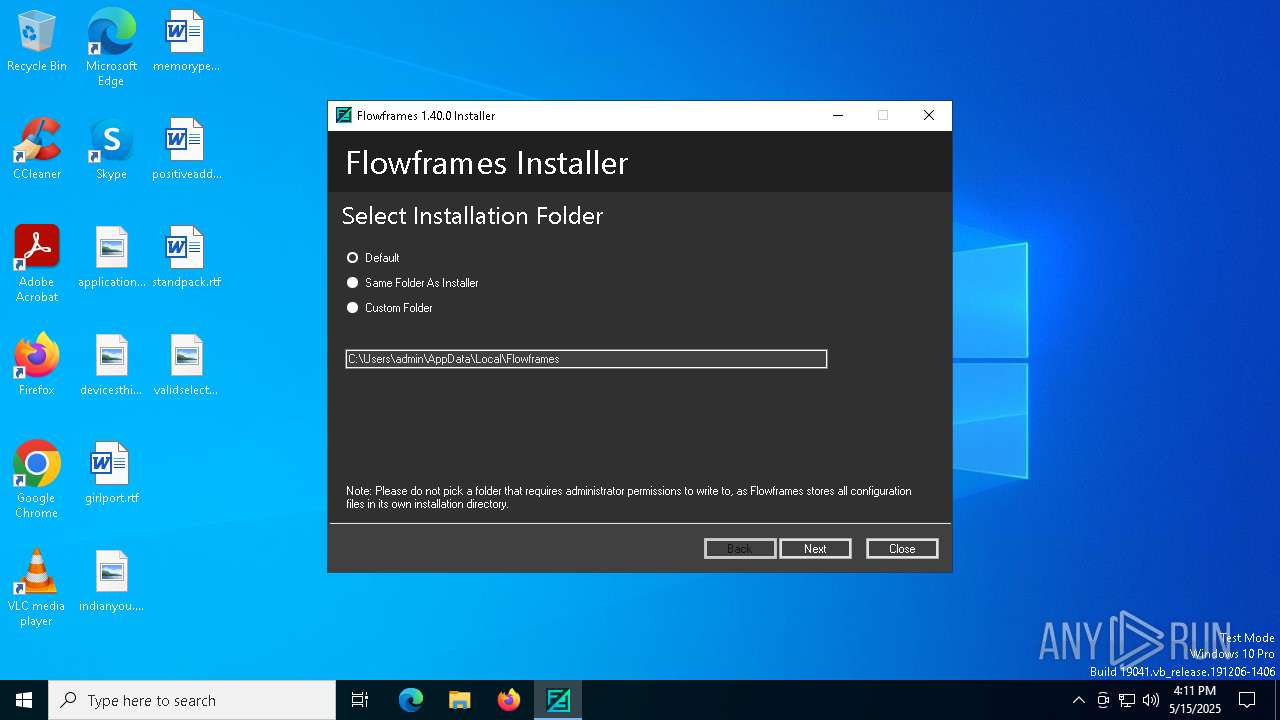
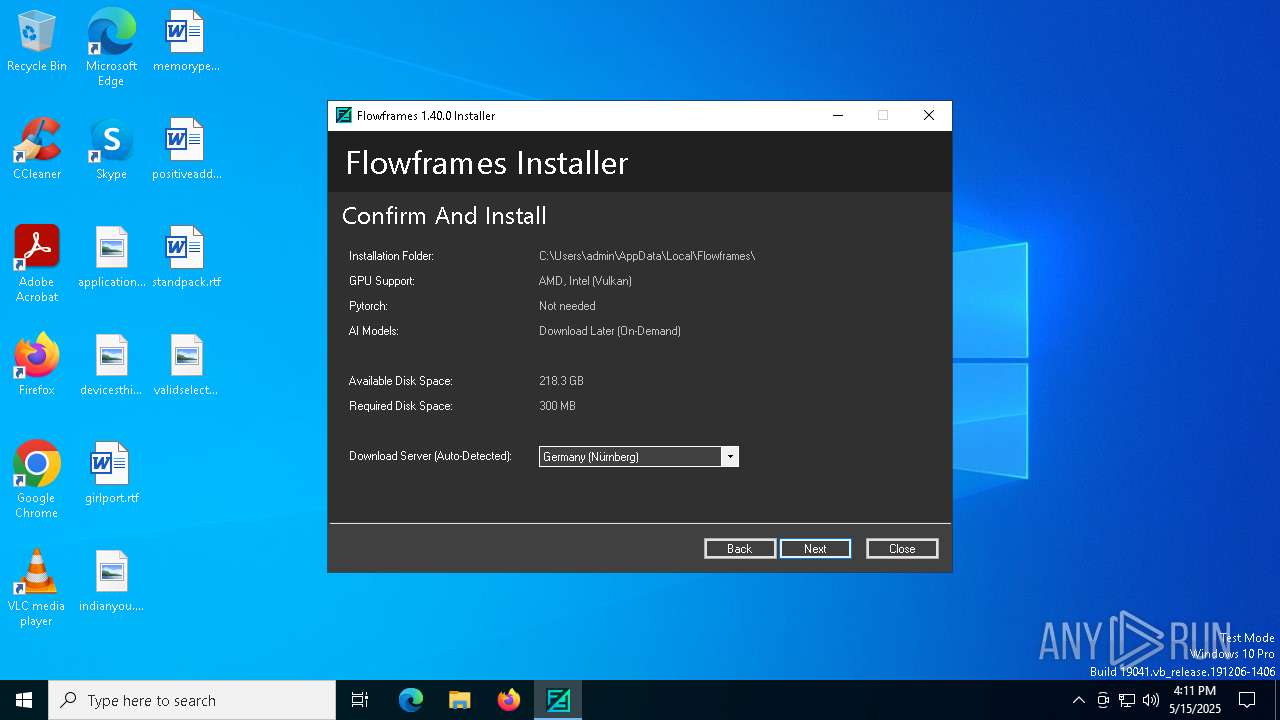
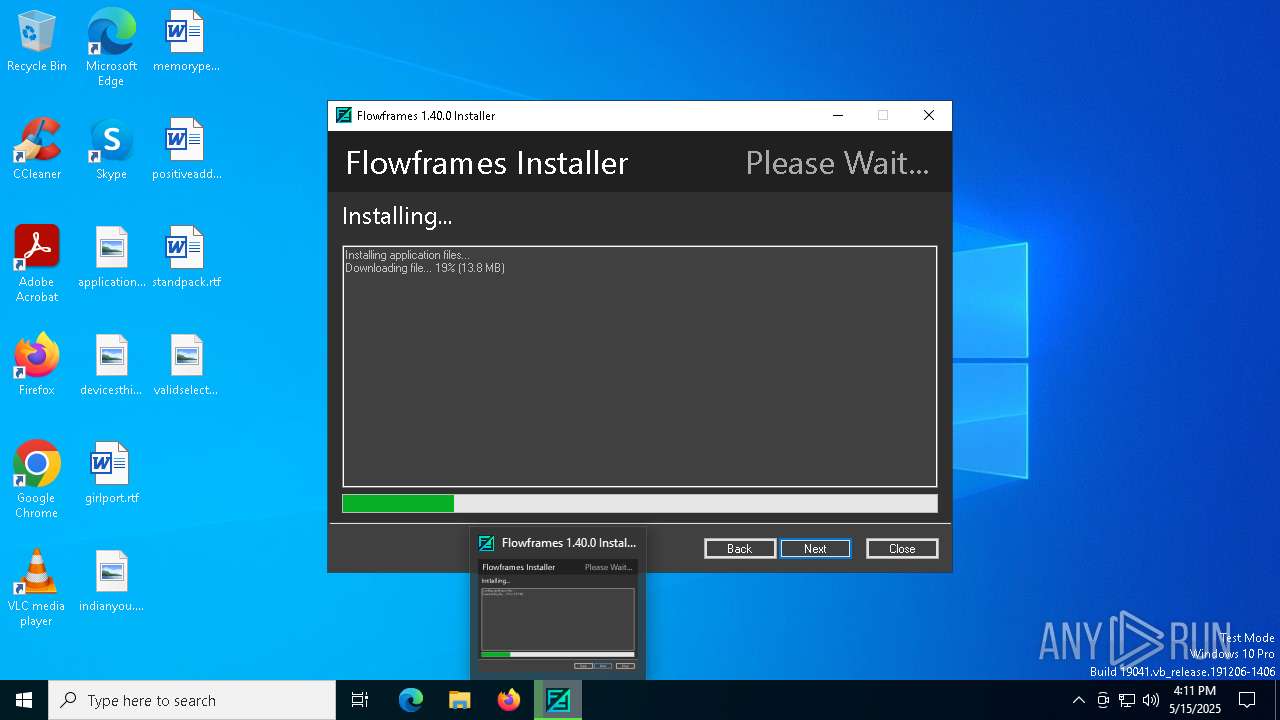
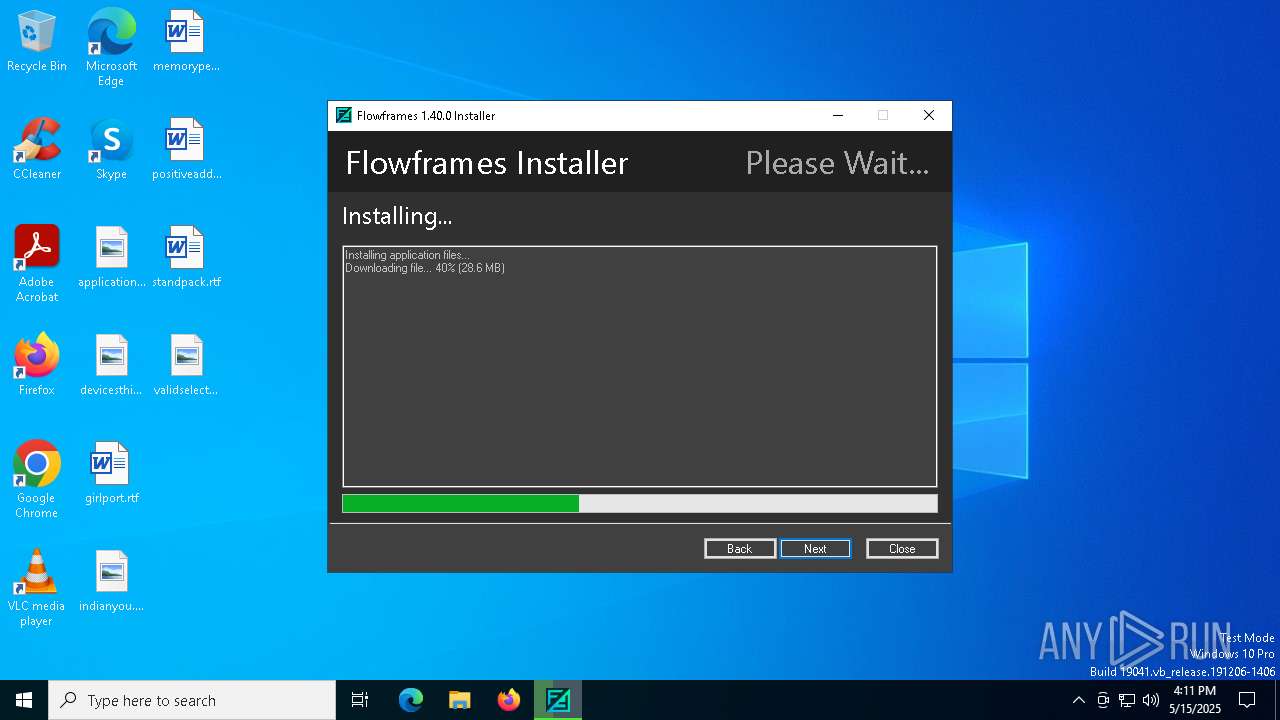
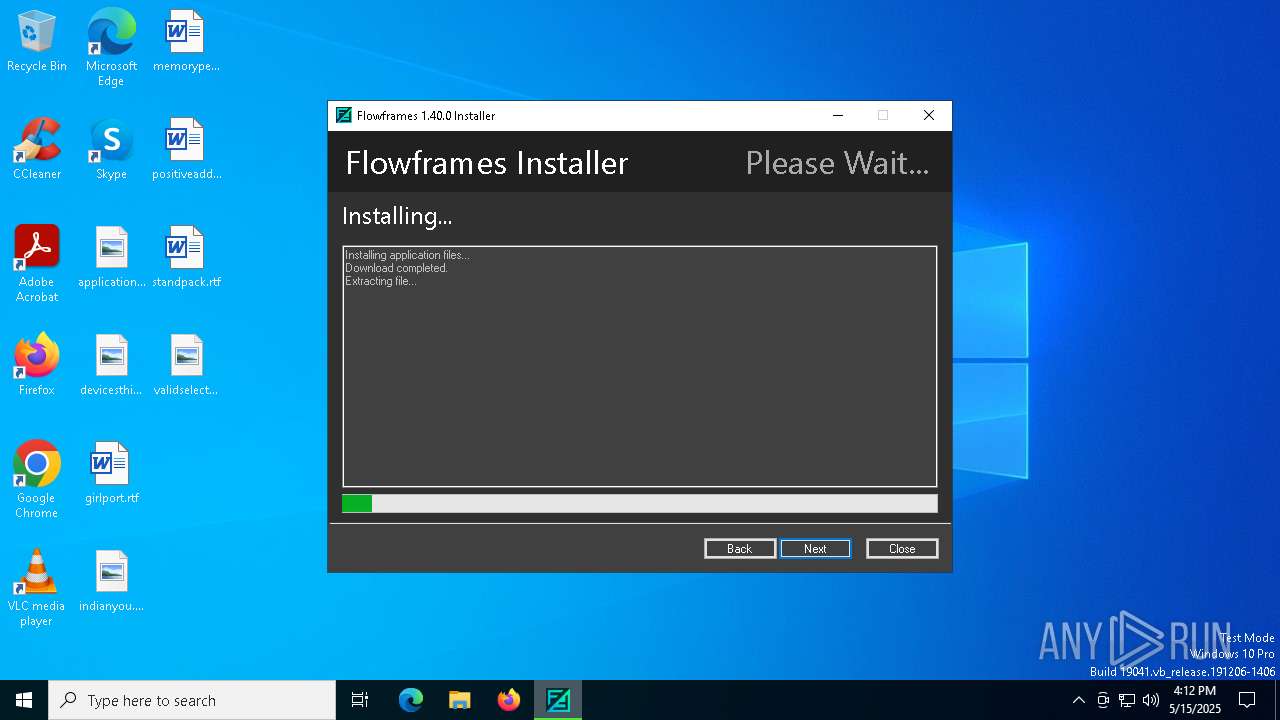
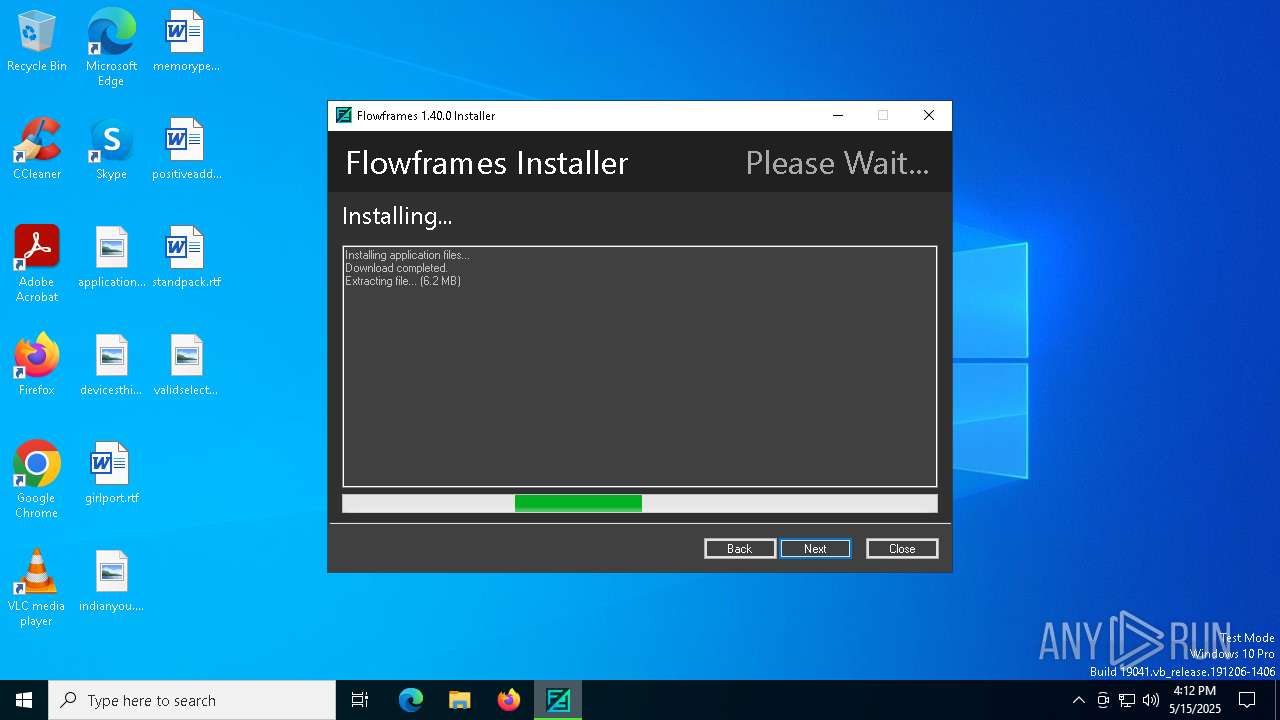
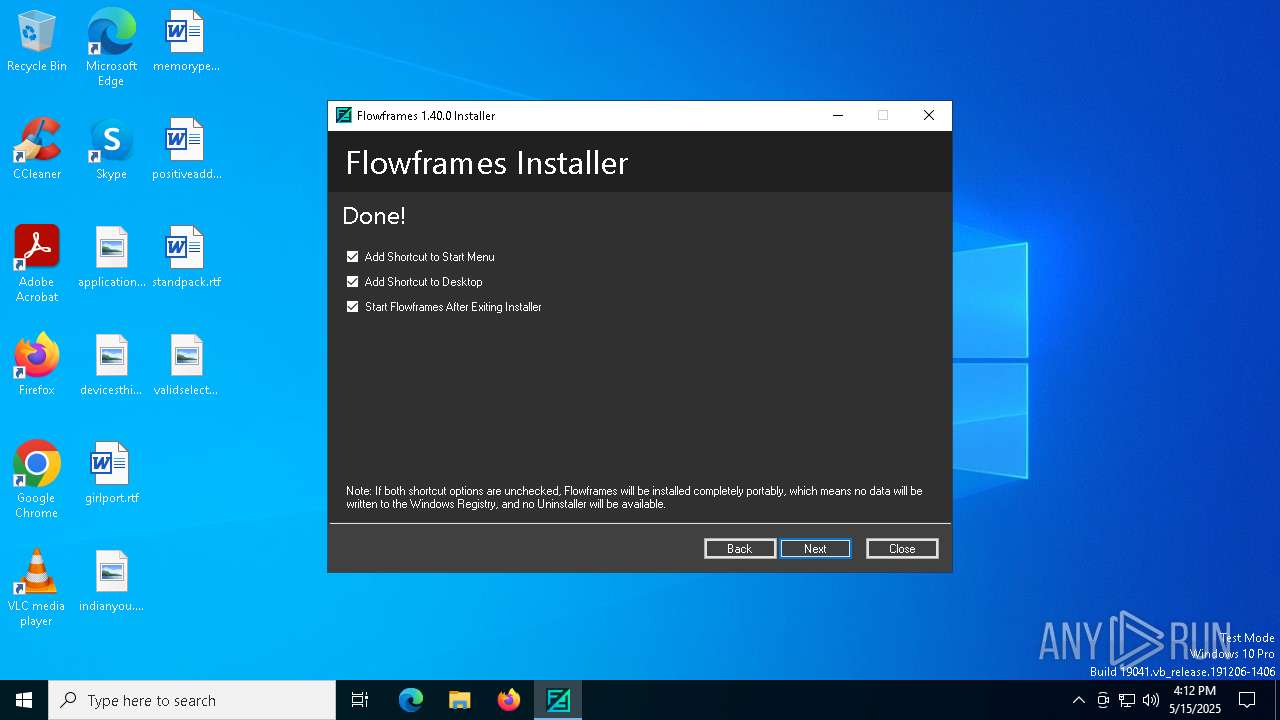
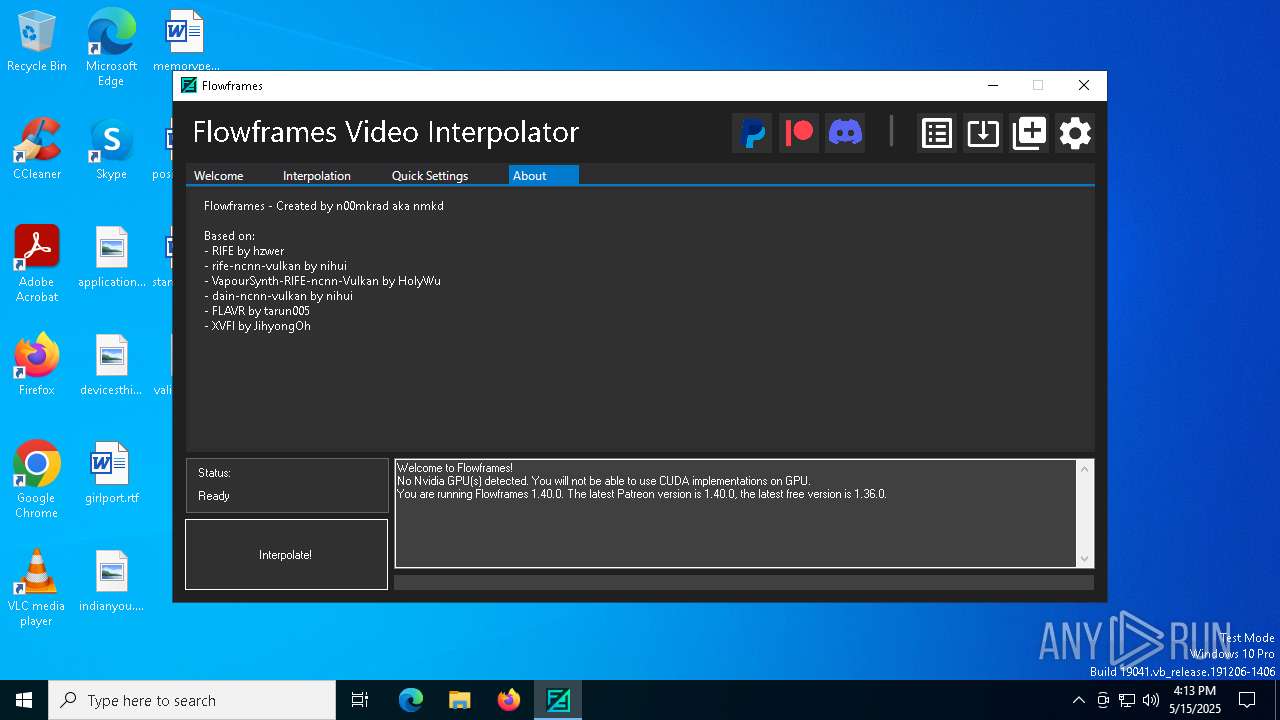
| File name: | FlowframesInstaller1.40.0.exe |
| Full analysis: | https://app.any.run/tasks/af16871c-5a26-424f-a25a-69e0c4d1e7be |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 16:10:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 6068259C7562439A27A7D67A5FDE907A |
| SHA1: | 559FE102D725912C24D9EA8D7C56CE0F744B015C |
| SHA256: | BFABB3F049126A57AA081460F029237D12BEC81EF490842441AB92D1F61F4C69 |
| SSDEEP: | 98304:DpWvloWpUdnGq6A6IF9/L/EUuKJQczHjVI7jFdefYHyQZoiJGrndFF7zs1d9xEbS:MPcvW |
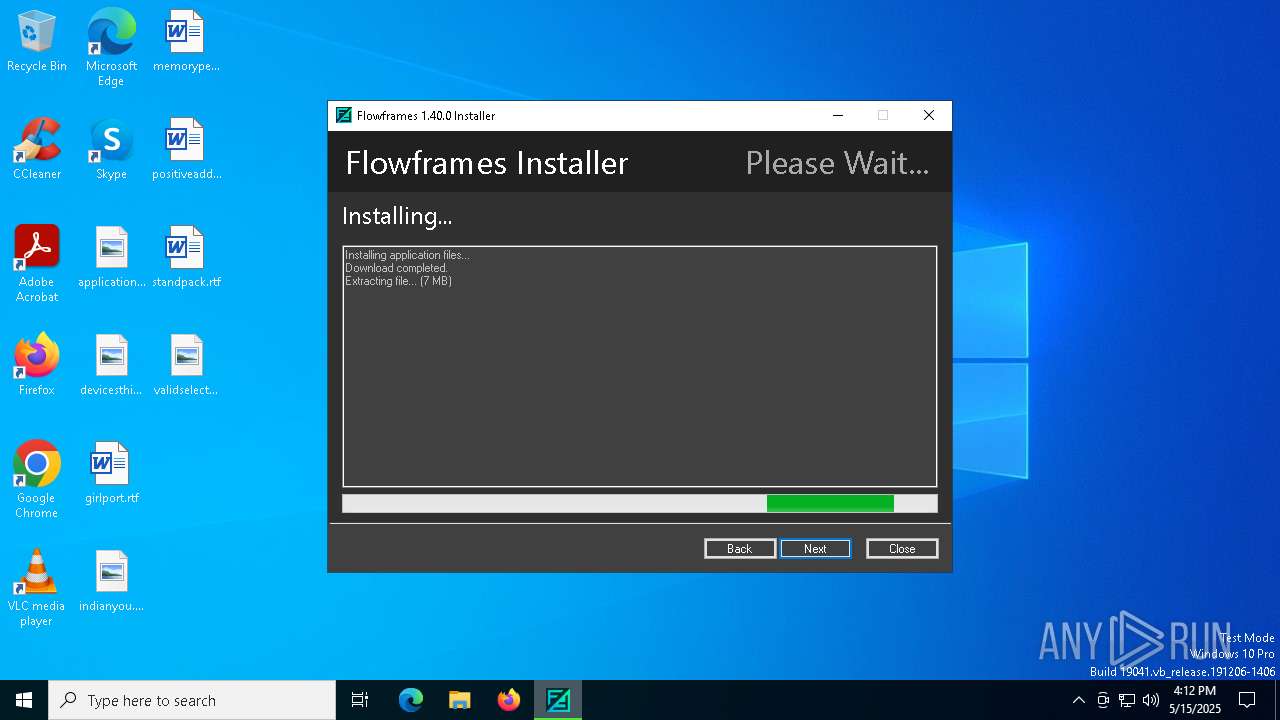
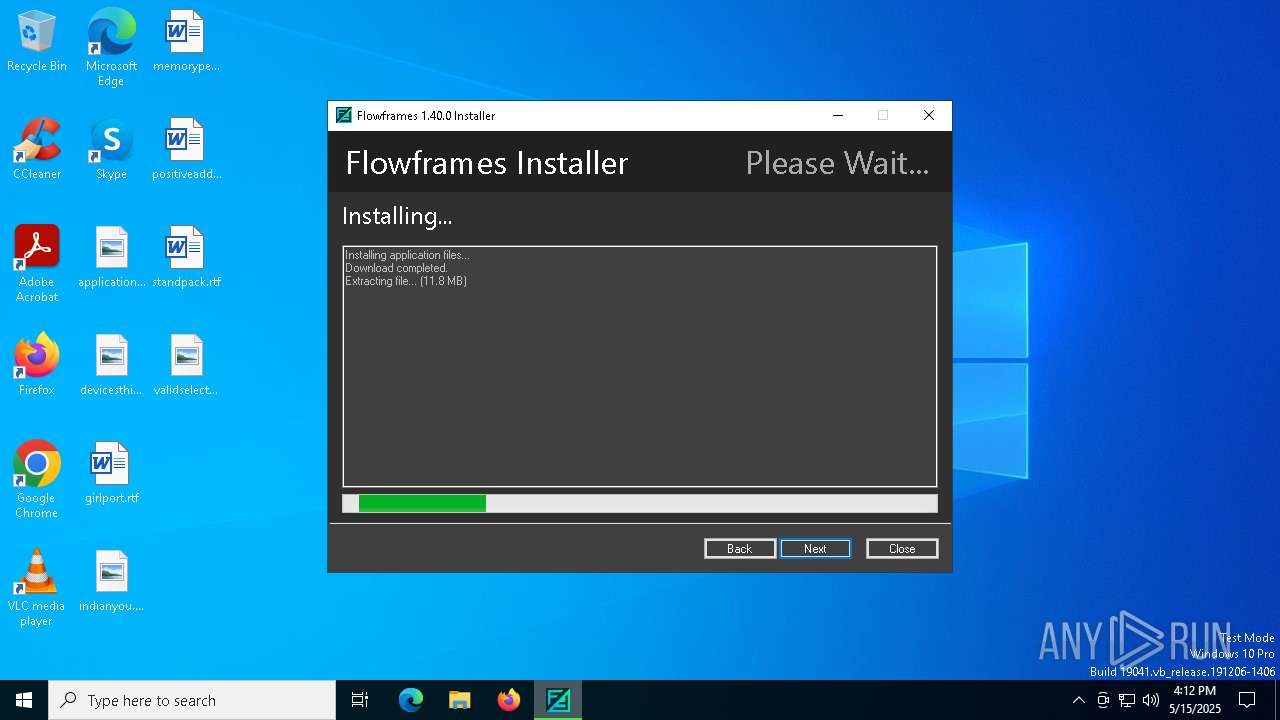
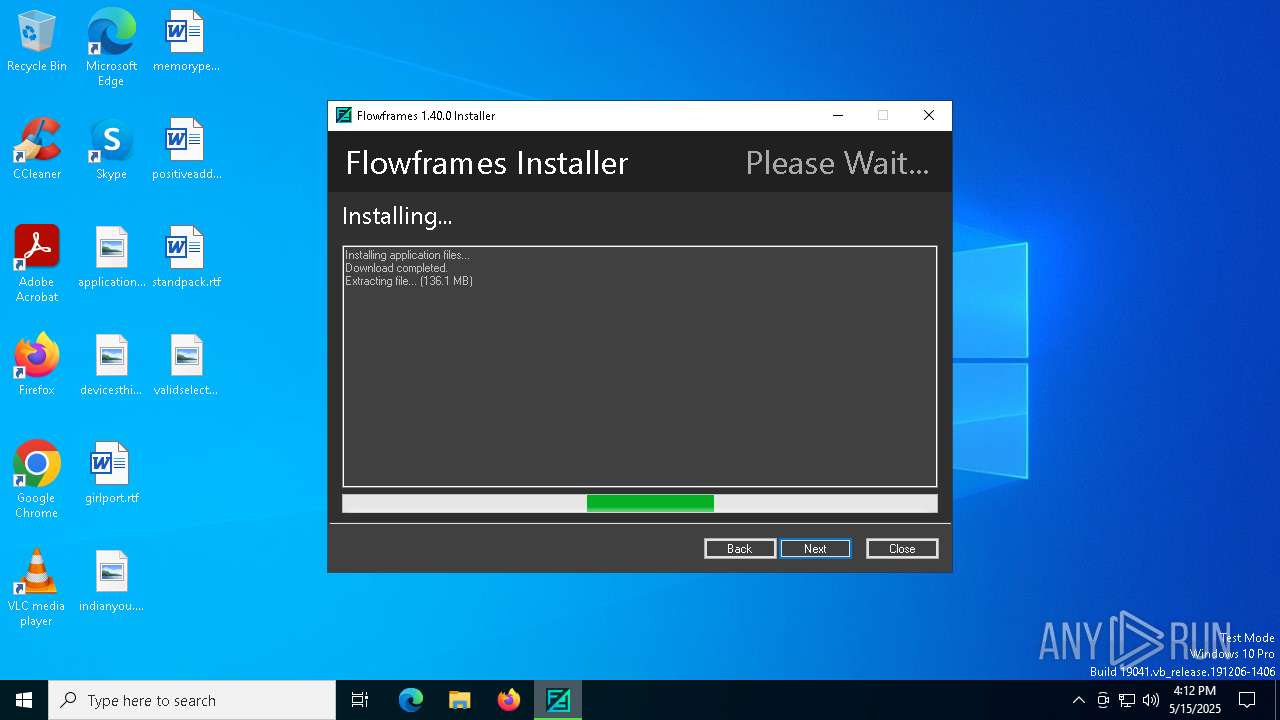
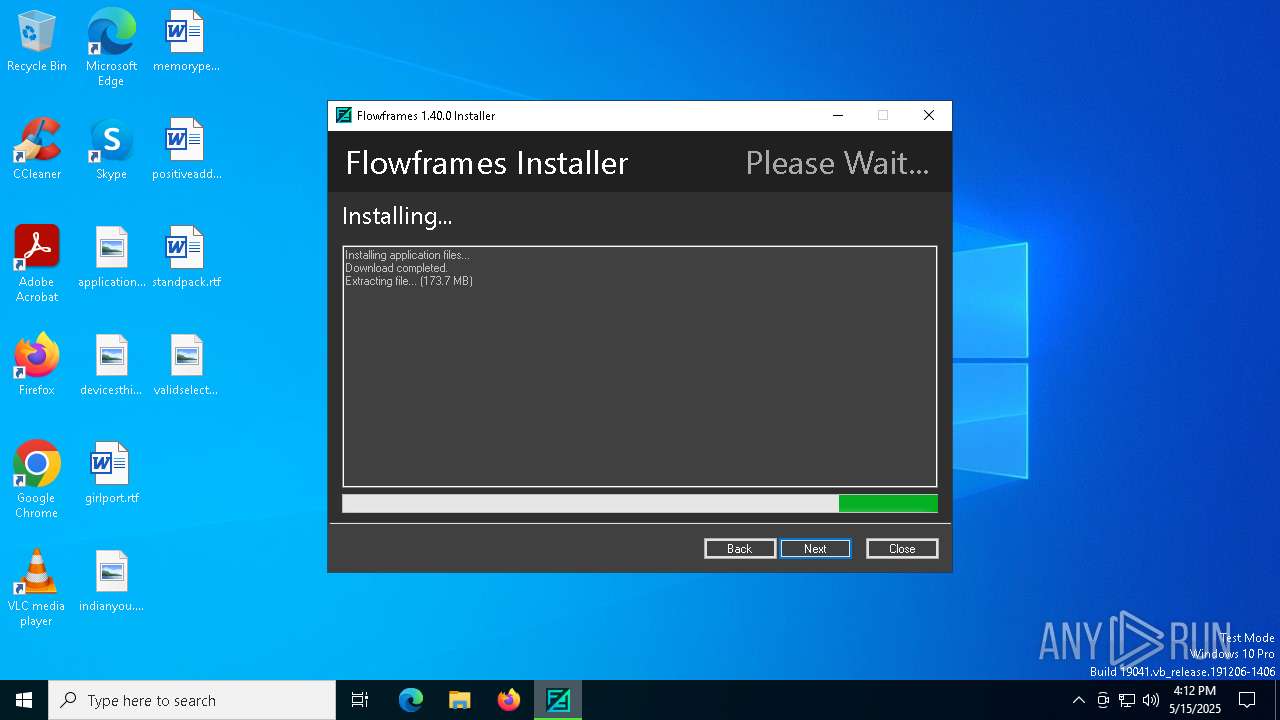
MALICIOUS
No malicious indicators.SUSPICIOUS
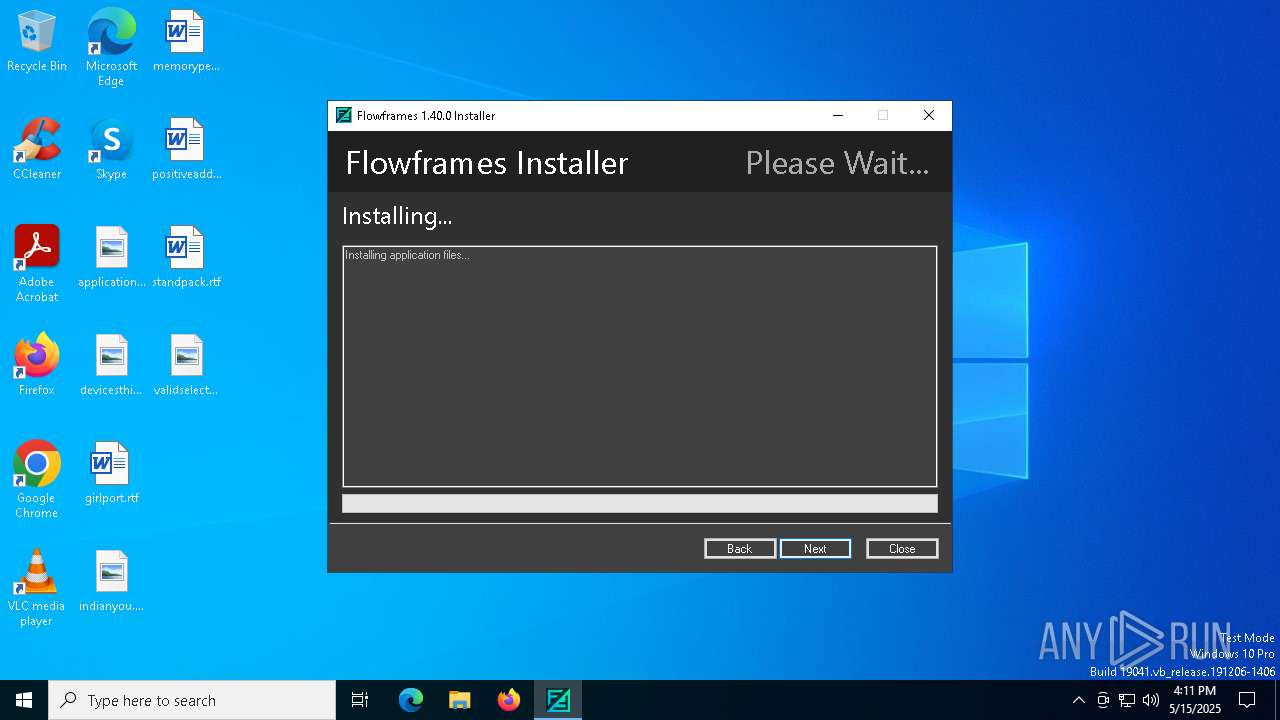
Executable content was dropped or overwritten
- FlowframesInstaller1.40.0.exe (PID: 6044)
- 7za.exe (PID: 3332)
Drops 7-zip archiver for unpacking
- FlowframesInstaller1.40.0.exe (PID: 6044)
- 7za.exe (PID: 3332)
Process drops python dynamic module
- 7za.exe (PID: 3332)
Process drops legitimate windows executable
- 7za.exe (PID: 3332)
Reads security settings of Internet Explorer
- FlowframesInstaller1.40.0.exe (PID: 6044)
The process drops C-runtime libraries
- 7za.exe (PID: 3332)
Reads the date of Windows installation
- FlowframesInstaller1.40.0.exe (PID: 6044)
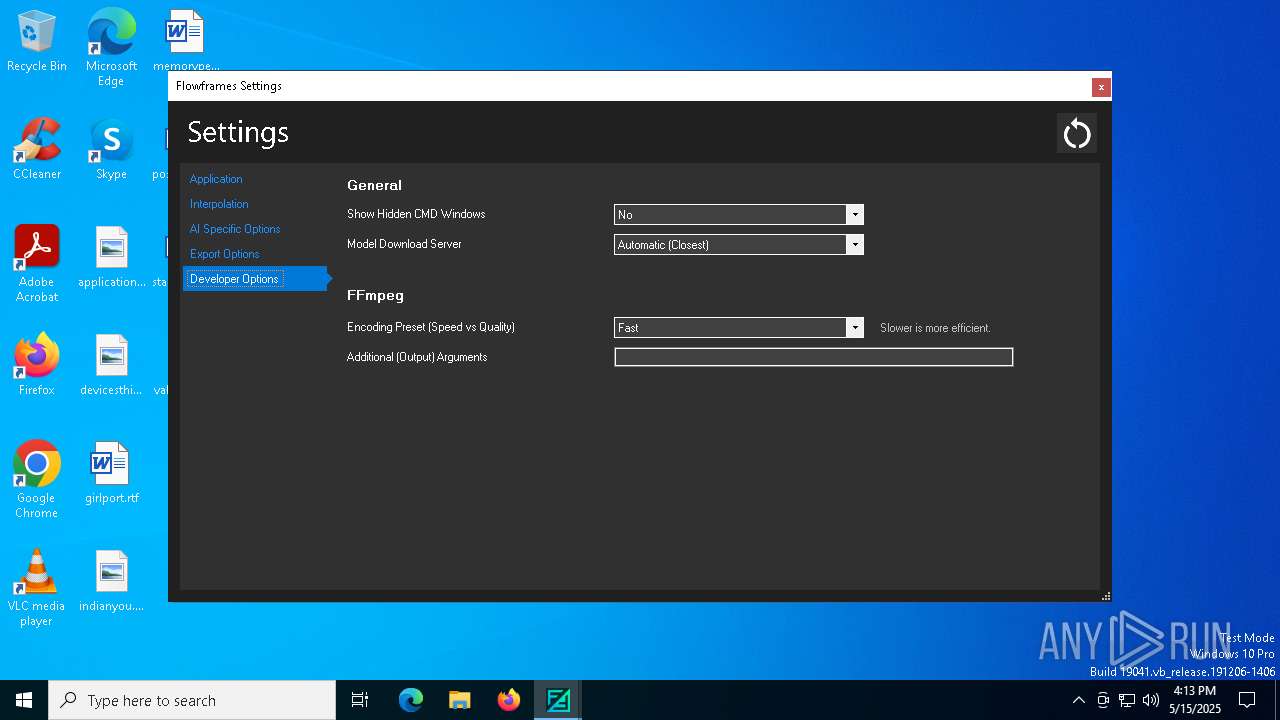
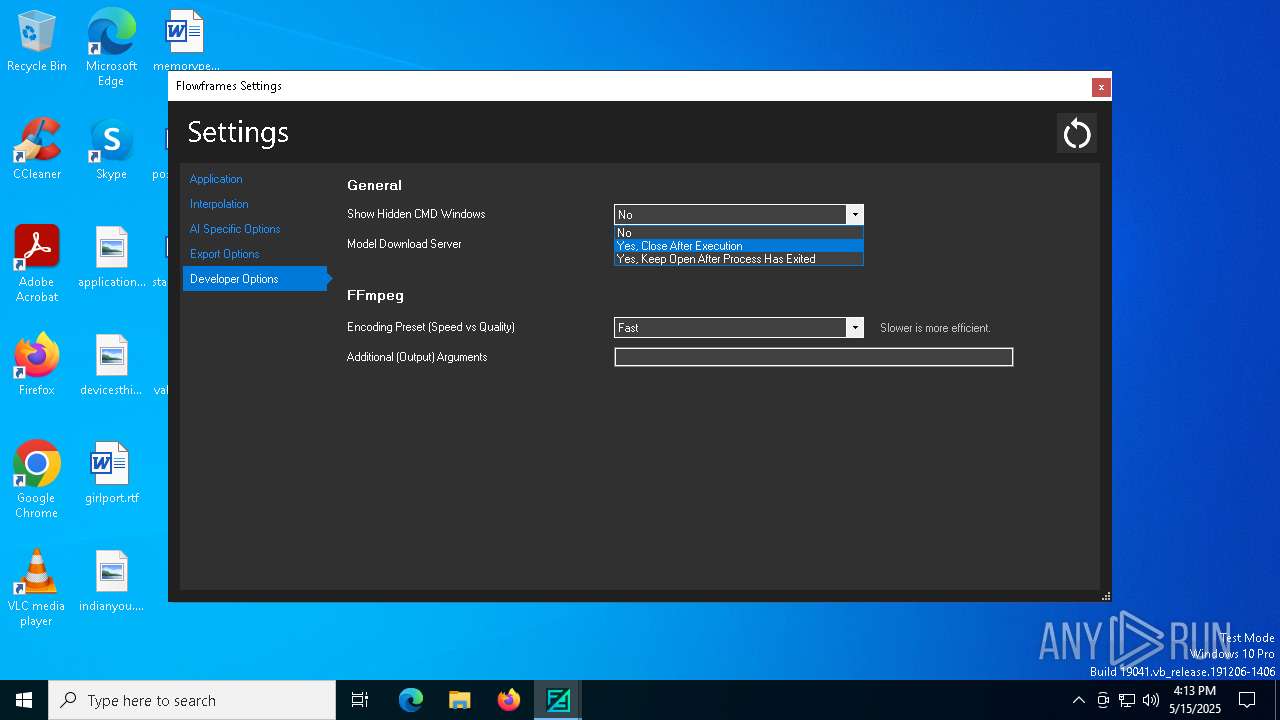
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6644)
Executing commands from a ".bat" file
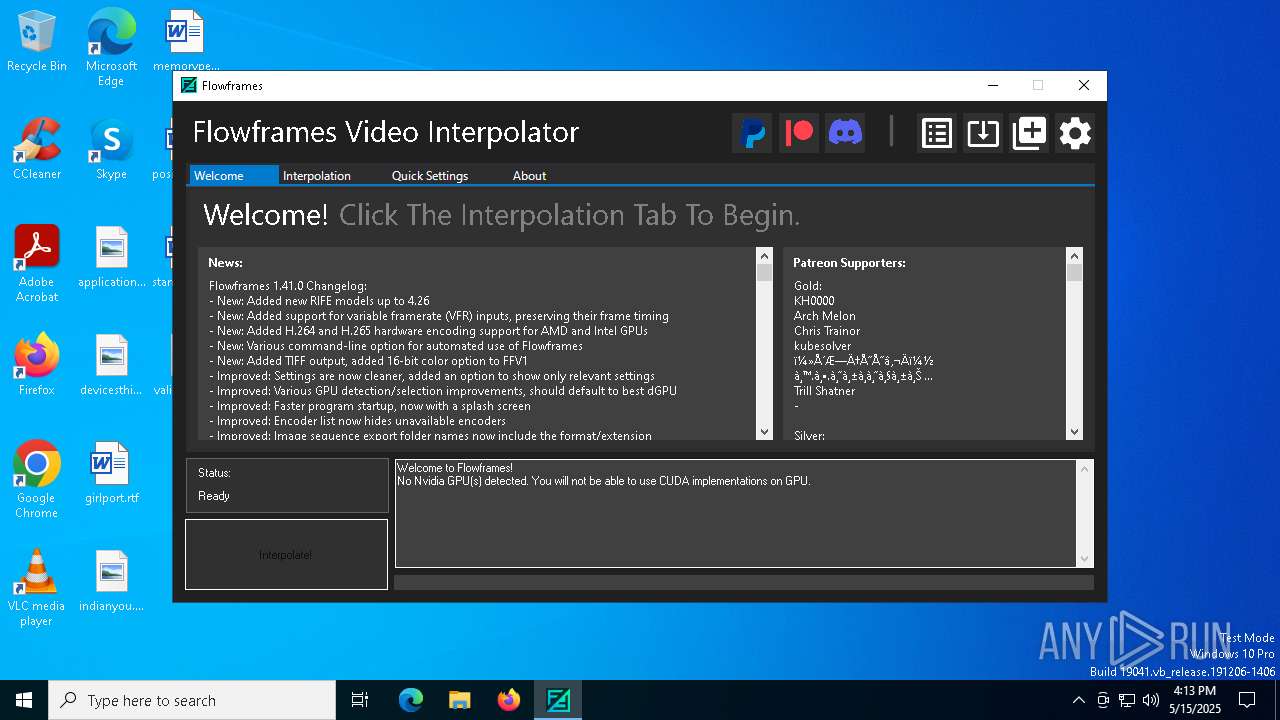
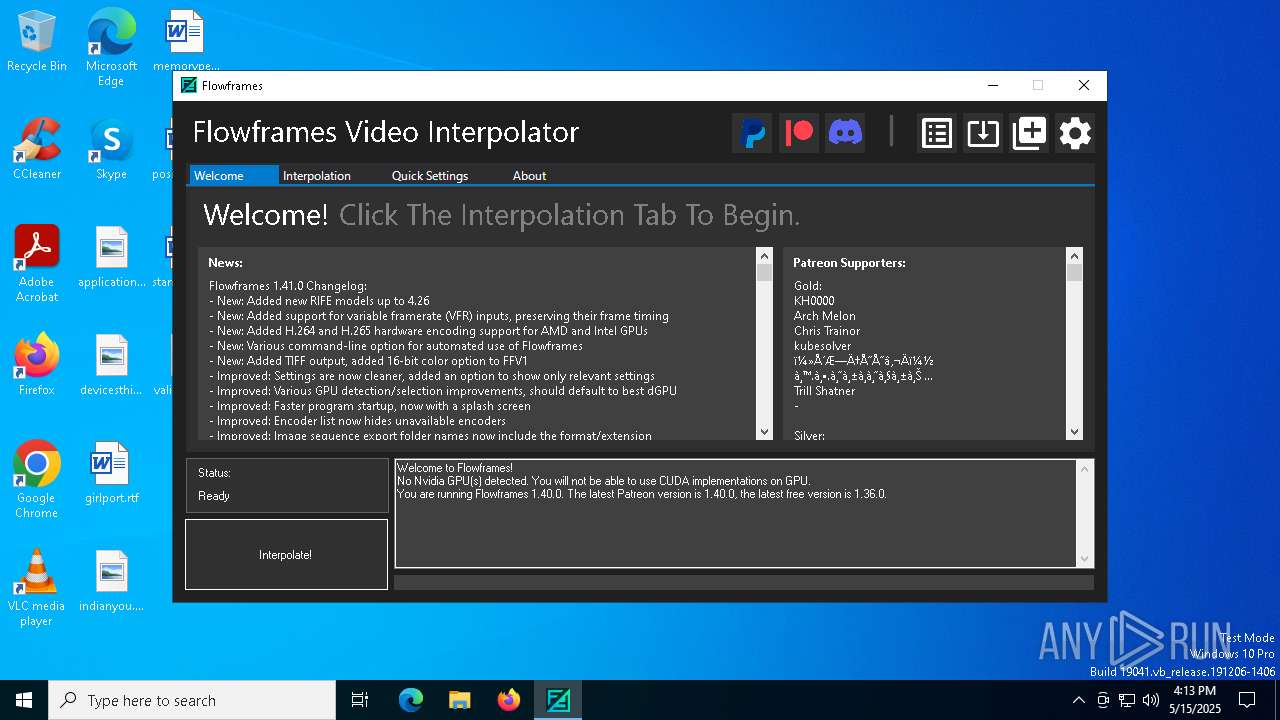
- Flowframes.exe (PID: 208)
- powershell.exe (PID: 4008)
Starts CMD.EXE for commands execution
- Flowframes.exe (PID: 208)
- powershell.exe (PID: 4008)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2064)
INFO
Checks supported languages
- FlowframesInstaller1.40.0.exe (PID: 6044)
- 7za.exe (PID: 3332)
- Flowframes.exe (PID: 208)
Reads the computer name
- FlowframesInstaller1.40.0.exe (PID: 6044)
- 7za.exe (PID: 3332)
- Flowframes.exe (PID: 208)
Reads the machine GUID from the registry
- FlowframesInstaller1.40.0.exe (PID: 6044)
- Flowframes.exe (PID: 208)
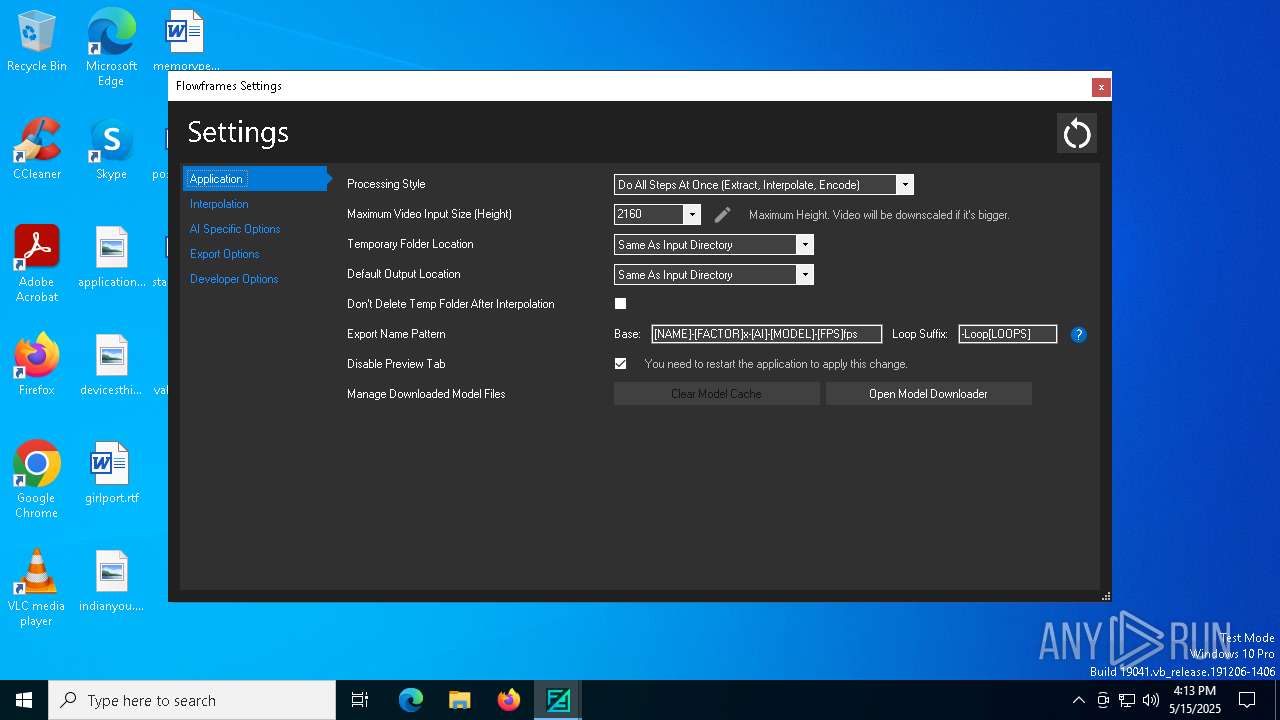
Creates files or folders in the user directory
- FlowframesInstaller1.40.0.exe (PID: 6044)
- 7za.exe (PID: 3332)
- Flowframes.exe (PID: 208)
Disables trace logs
- FlowframesInstaller1.40.0.exe (PID: 6044)
- Flowframes.exe (PID: 208)
Reads the software policy settings
- FlowframesInstaller1.40.0.exe (PID: 6044)
- slui.exe (PID: 6652)
- Flowframes.exe (PID: 208)
- slui.exe (PID: 1272)
Checks proxy server information
- FlowframesInstaller1.40.0.exe (PID: 6044)
- Flowframes.exe (PID: 208)
- slui.exe (PID: 1272)
Reads Environment values
- FlowframesInstaller1.40.0.exe (PID: 6044)
- Flowframes.exe (PID: 208)
The sample compiled with english language support
- FlowframesInstaller1.40.0.exe (PID: 6044)
- 7za.exe (PID: 3332)
Process checks computer location settings
- FlowframesInstaller1.40.0.exe (PID: 6044)
Creates files in the program directory
- Flowframes.exe (PID: 208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2093:08:15 20:38:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 2410496 |
| InitializedDataSize: | 185856 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | FlowframesInstaller |
| FileVersion: | 1.0.0.0 |
| InternalName: | FlowframesInstaller.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFileName: | FlowframesInstaller.exe |
| ProductName: | FlowframesInstaller |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
147
Monitored processes
17
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\AppData\Local\Flowframes\Flowframes.exe" | C:\Users\admin\AppData\Local\Flowframes\Flowframes.exe | FlowframesInstaller1.40.0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Flowframes Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 812 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\AppModelUnlock" /t REG_DWORD /f /v "AllowDevelopmentWithoutDevLicense" /d "1" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Flowframes\FlowframesData\devmode.bat" am_admin | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Local\FlowframesInstallerTemp\7za.exe" x "C:\Users\admin\AppData\Local\FlowframesInstallerTemp\dl\base.7z" -o"C:\Users\admin\AppData\Local\Flowframes\" -aoa -bsp1 | C:\Users\admin\AppData\Local\FlowframesInstallerTemp\7za.exe | FlowframesInstaller1.40.0.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 15.14 Modules
| |||||||||||||||
| 4008 | powershell start -verb runas 'C:\Users\admin\AppData\Local\Flowframes\FlowframesData\devmode.bat' am_admin | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5036 | "cmd.exe" "/C" -c "import torch; print(torch.__version__)" | C:\Windows\System32\cmd.exe | — | Flowframes.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5624 | "cmd.exe" /C python -V | C:\Windows\System32\cmd.exe | — | Flowframes.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 640
Read events
7 610
Write events
30
Delete events
0
Modification events
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6044) FlowframesInstaller1.40.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FlowframesInstaller1_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
87
Suspicious files
24
Text files
686
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6044 | FlowframesInstaller1.40.0.exe | C:\Users\admin\AppData\Local\FlowframesInstallerTemp\dl\base.7z | — | |
MD5:— | SHA256:— | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\dain-ncnn\LICENSE | text | |
MD5:E6428A7BAE5F05E70A71D3EE70840842 | SHA256:DE18CBEDB0C3B0D1EEB9CCAC3988CDF69C21FA89039CD97DD8846CB68F661F81 | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\flavr.py | text | |
MD5:D3947A6DE3205A421A432DB8CF00F88E | SHA256:89FFA4B873C8F94CA6ADC35B0FD990948361ECDB5A4FC6BC8EF4794302574FE0 | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\models.json | text | |
MD5:6ED4577C435B005A5C3D2AD2215D8380 | SHA256:1FE15EE0156021CF874F617ADEA3FB37EF24D665592D853E23502DE025A14C77 | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\model\resnet_3D.py | text | |
MD5:93C6479A8C7CC22FD904426487835E59 | SHA256:C67387D619F7D6E4949CB47E1C61594C142DC1DD6AEEAF569F0A21BFEE1A5DF4 | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\dataset\__pycache__\transforms.cpython-38.pyc | binary | |
MD5:1B5BD3946FBDC4D3B5E06C15A4449228 | SHA256:7E1BD5D6414C118224E3E6A5CC278CB8B3E9F55070D6BFDBE626D4F4DF86CBBE | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\dataset\transforms.py | text | |
MD5:5000AF77B0CD2990BBE6613A55CCBB99 | SHA256:BA7F8578903B62F27FDC79893ABB12E4513D5BD5AC0F4A1E2037670FD11ED65F | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\model\__pycache__\resnet_3D.cpython-38.pyc | binary | |
MD5:13511299C9295CBCB1A4C2021C1FDB7D | SHA256:935BC5877F8D9A62711EECDF66EBB17BB23E44F84F418F485A092E9F418B6B30 | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\model\__pycache__\FLAVR_arch.cpython-38.pyc | binary | |
MD5:A1E9D4E05D918C62FF0D61663FADFEF8 | SHA256:D8602541ECEA9EB67F5CC351BF63C59623092895012FED833E06910F8C8C46BE | |||
| 3332 | 7za.exe | C:\Users\admin\AppData\Local\Flowframes\FlowframesData\pkgs\flavr-cuda\dataset\vimeo90k_septuplet.py | text | |
MD5:A9DAACD9E4B8114522BB0BF05765C267 | SHA256:C1D999B6FFE83710297ED42EB0D80747A604DF8556736CFD25AB89A389D499E4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.160:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5608 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5608 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.160:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6044 | FlowframesInstaller1.40.0.exe | 162.55.177.242:443 | nmkd-hz.de | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
nmkd-hz.de |
| unknown |
nmkd-cb.de |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dl.nmkd-hz.de |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |