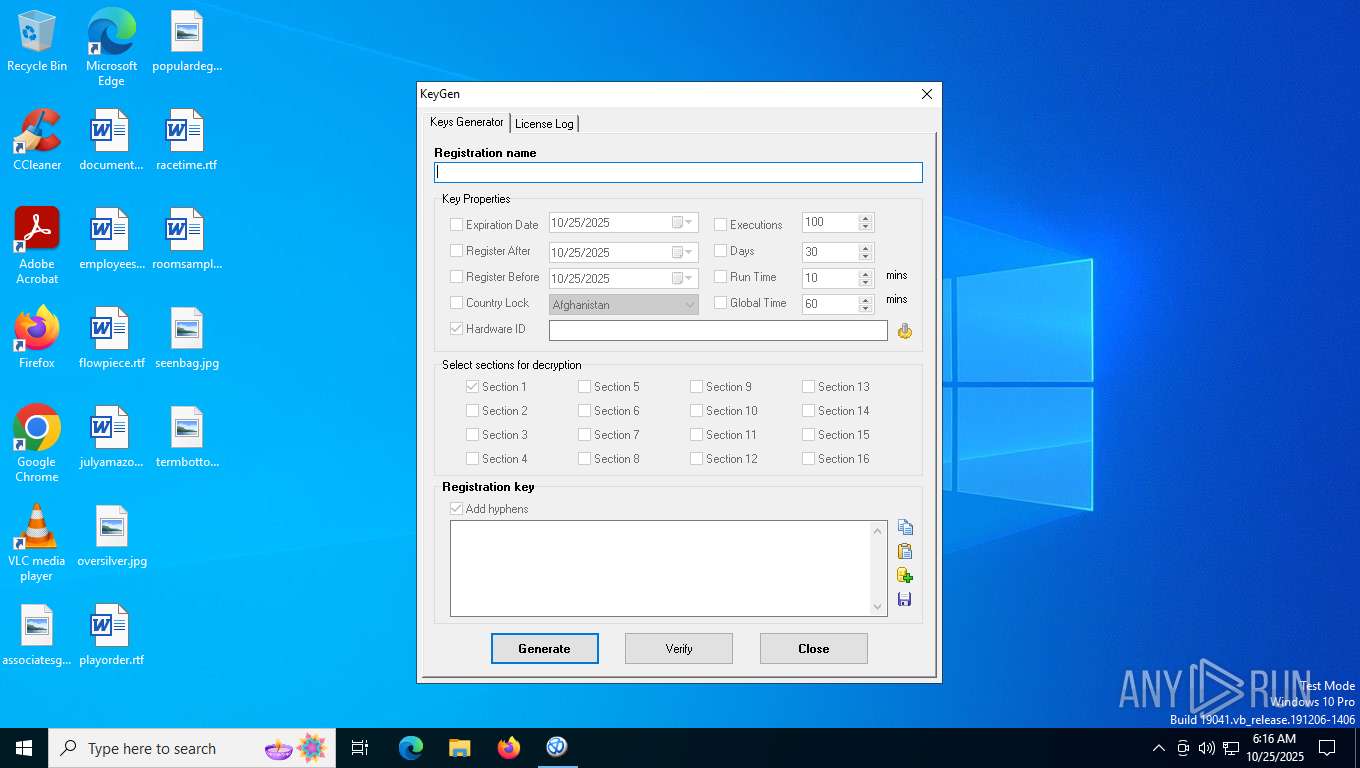
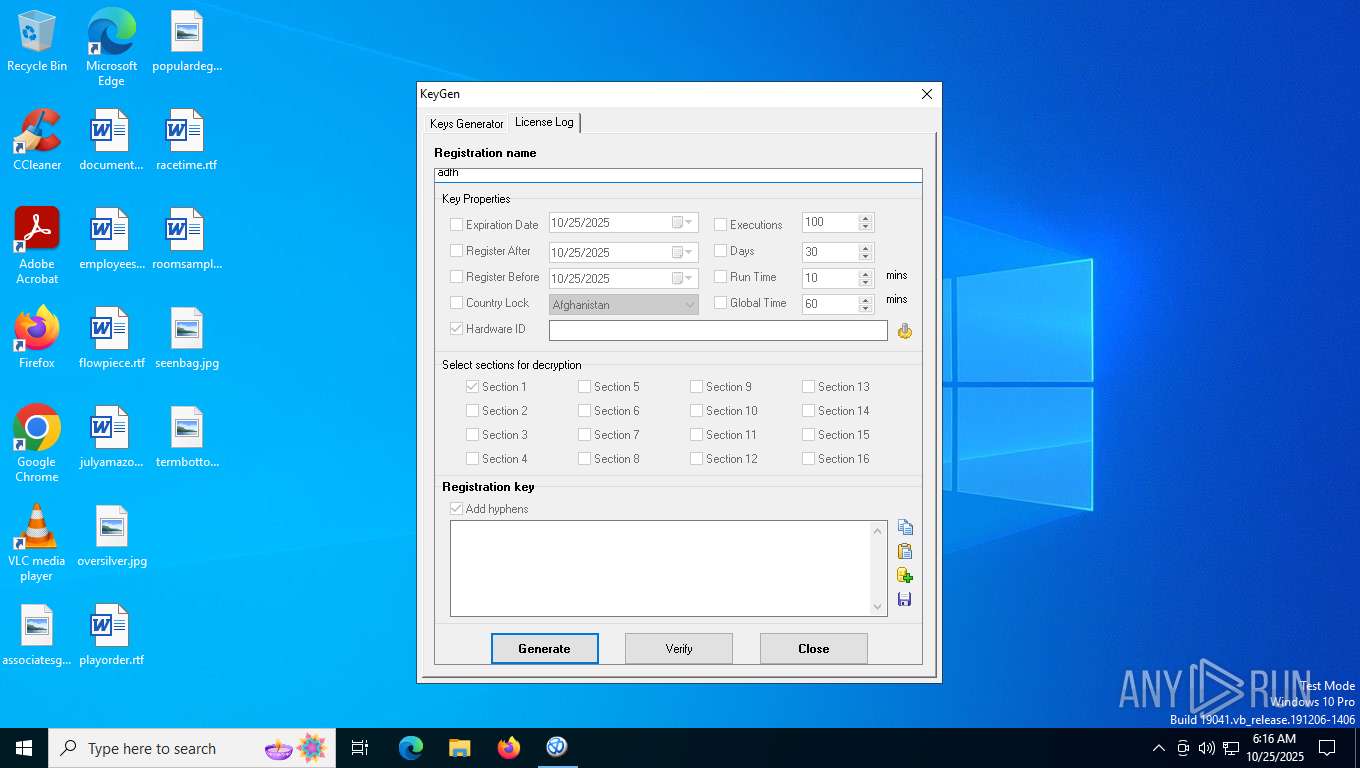
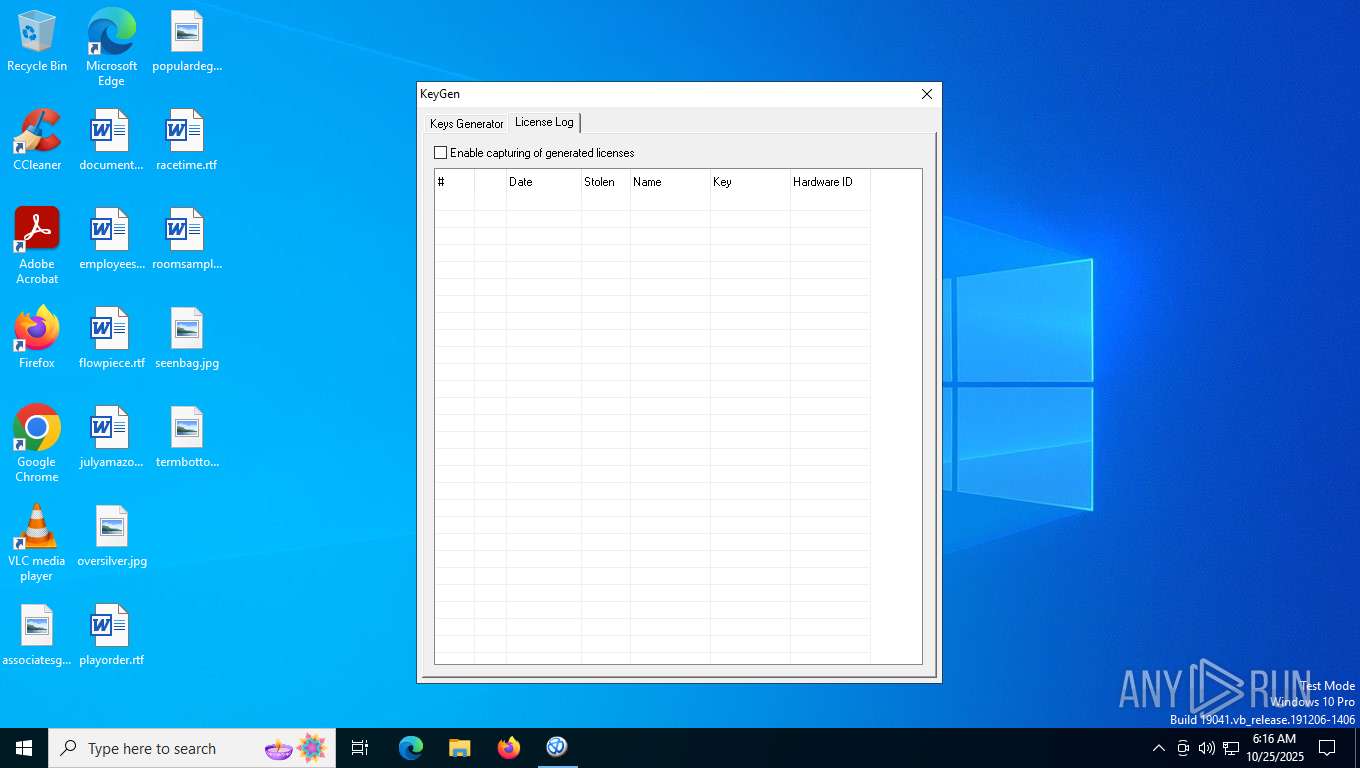
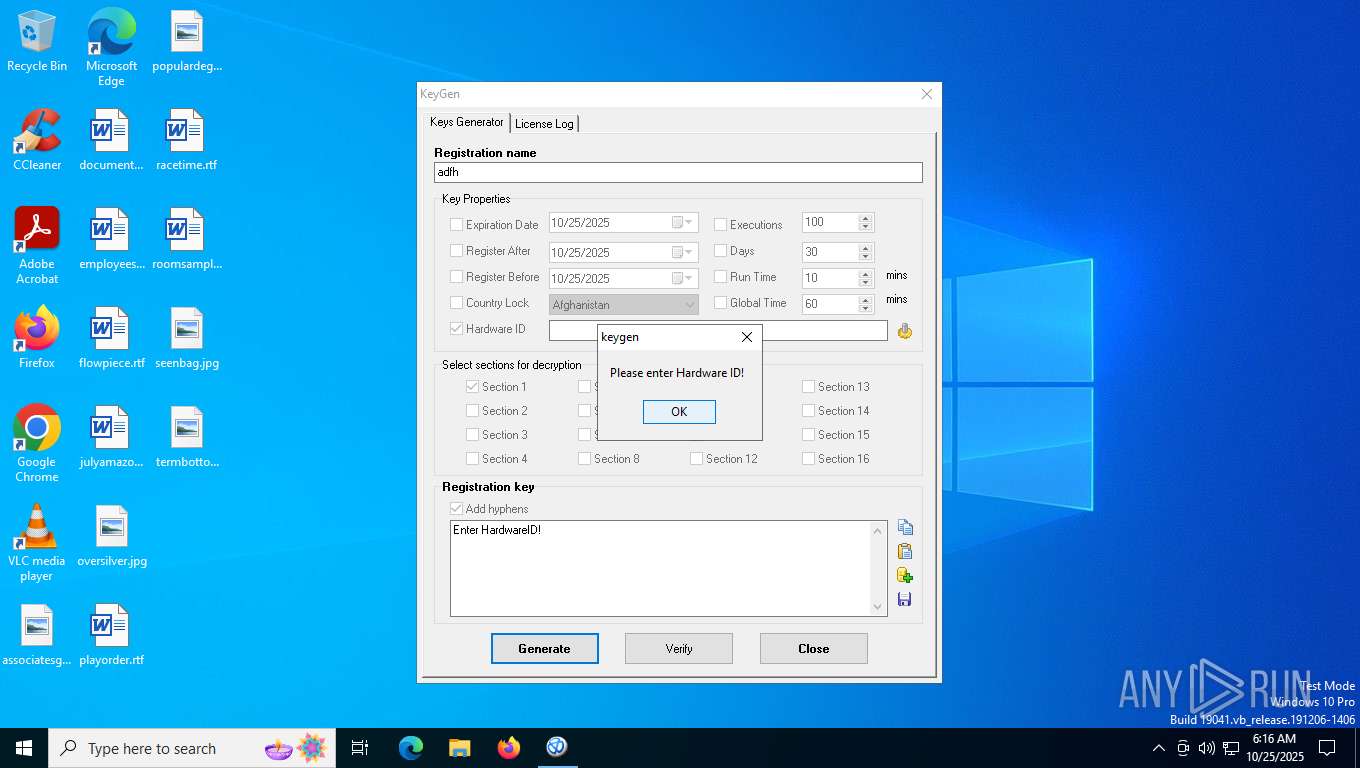
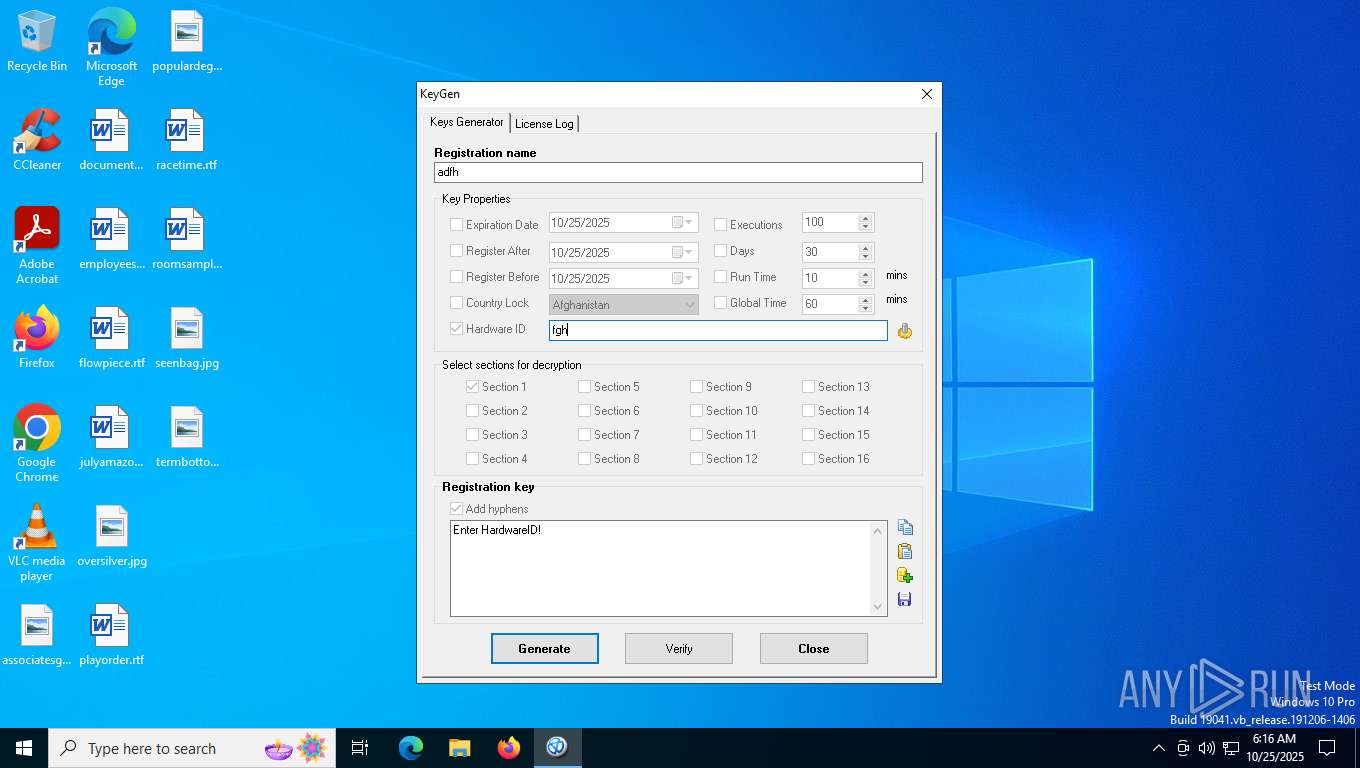
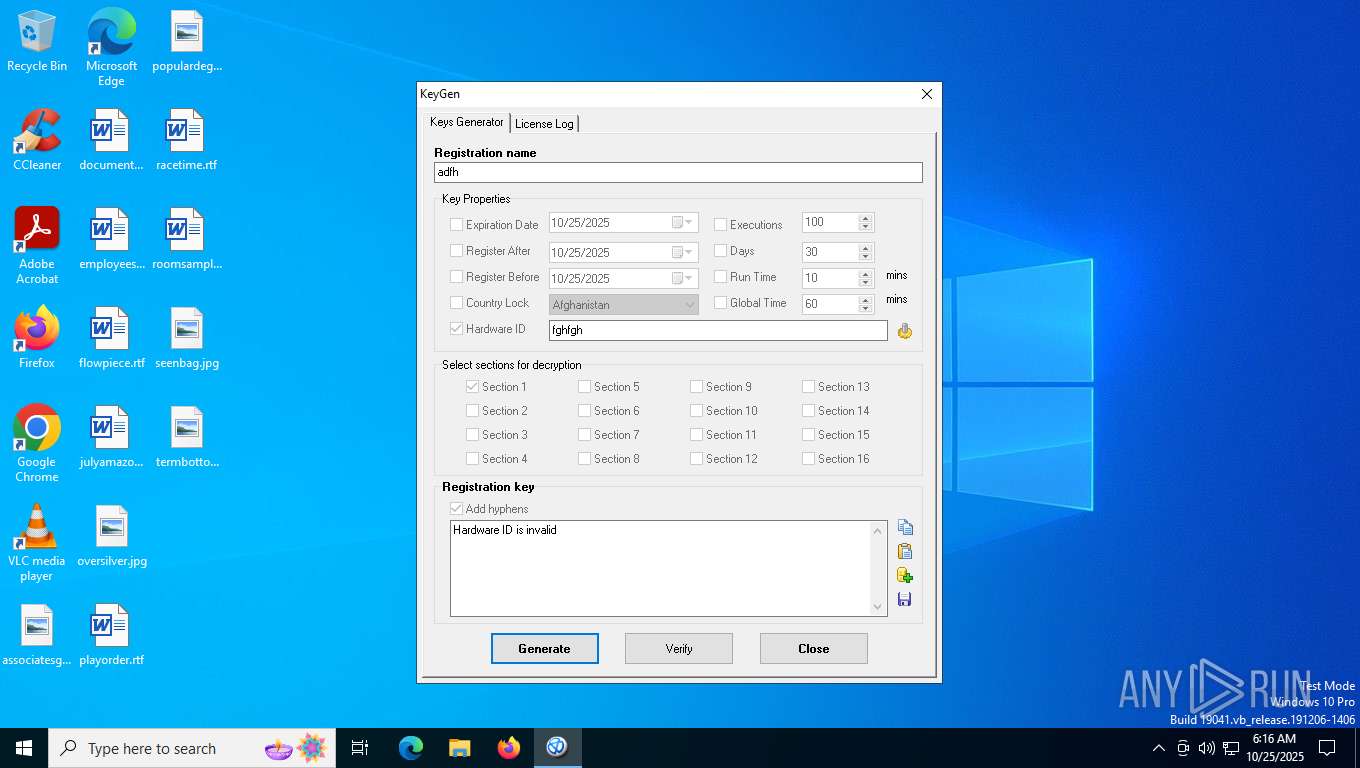
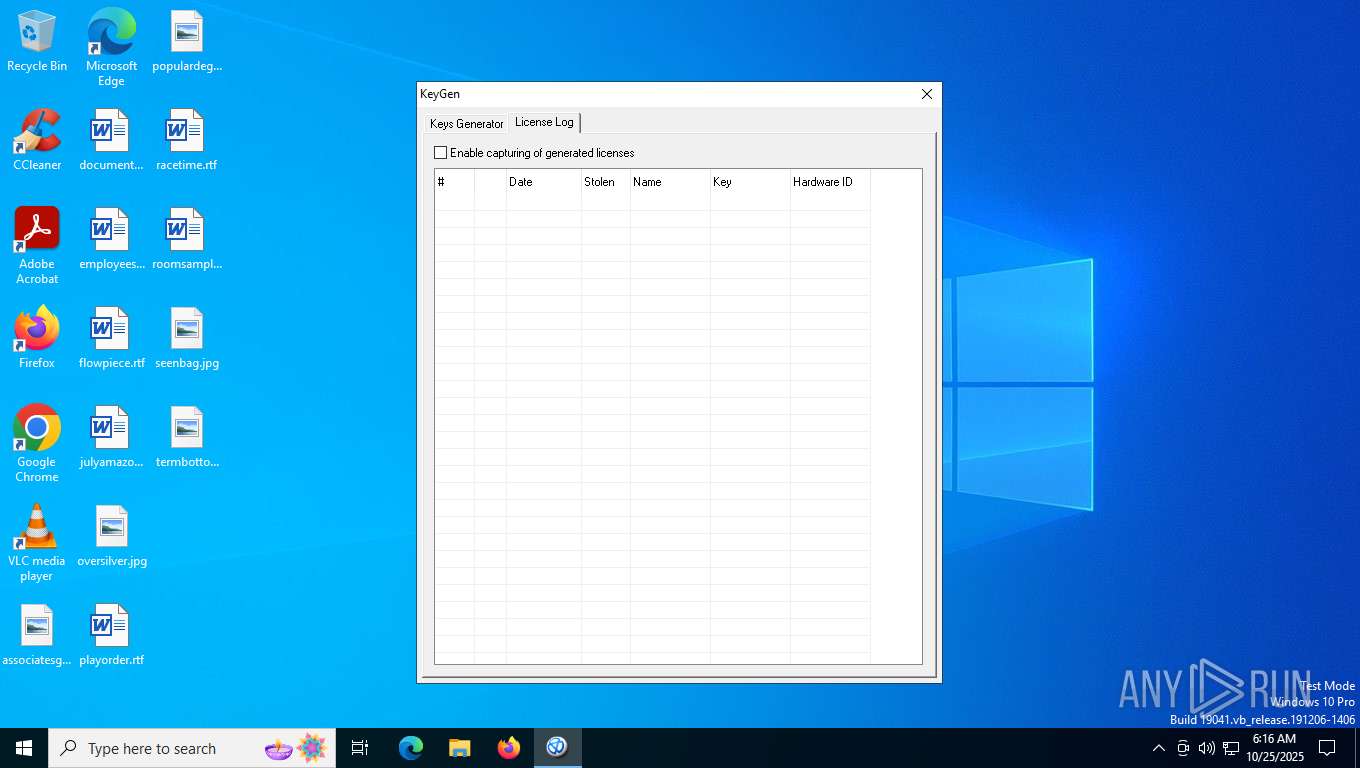
| File name: | KeyGen.exe |
| Full analysis: | https://app.any.run/tasks/70564446-b393-4b62-bff7-33cf6bffe4b1 |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2025, 06:16:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | F5CADD5E2241A19B1EFA23FAD6BF7C5D |
| SHA1: | DFD869121DDEEE8BCC110B32CD803A1EBB4D3C49 |
| SHA256: | BFAAFAD76AB1673719785A80371189355FD9195513945BA9AD29CEF18BD95B95 |
| SSDEEP: | 49152:vcqnMye0exk1AwRX1limiG+3cfEzkkMvVPE5aJK+mW8UCmd8j5+170m85QCf41G:vcvKexk15gp0EiEcJK+mW4SKUG |
MALICIOUS
JEEFO has been detected
- KeyGen.exe (PID: 7916)
SUSPICIOUS
Starts application with an unusual extension
- KeyGen.exe (PID: 7916)
Executable content was dropped or overwritten
- KeyGen.exe (PID: 7916)
There is functionality for VM detection antiVM strings (YARA)
- keygen.exe (PID: 7940)
There is functionality for taking screenshot (YARA)
- keygen.exe (PID: 7940)
INFO
Checks supported languages
- KeyGen.exe (PID: 7916)
- keygen.exe (PID: 7940)
Create files in a temporary directory
- KeyGen.exe (PID: 7916)
Failed to create an executable file in Windows directory
- KeyGen.exe (PID: 7916)
The sample compiled with english language support
- KeyGen.exe (PID: 7916)
Reads the computer name
- keygen.exe (PID: 7940)
Compiled with Borland Delphi (YARA)
- keygen.exe (PID: 7940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (42.6) |
|---|---|---|
| .exe | | | InstallShield setup (22.3) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.2) |
| .exe | | | Win64 Executable (generic) (14.3) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
145
Monitored processes
3
Malicious processes
1
Suspicious processes
0
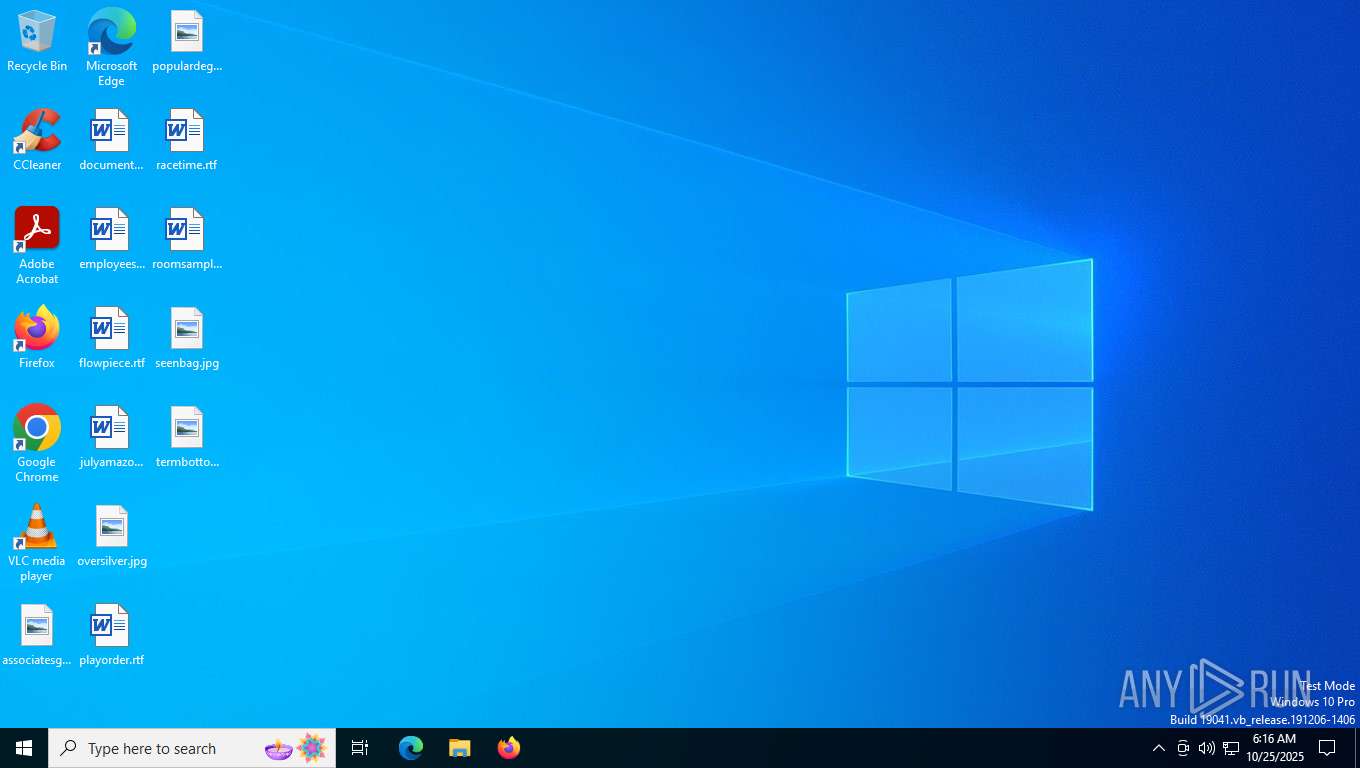
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7584 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7916 | "C:\Users\admin\AppData\Local\Temp\KeyGen.exe" | C:\Users\admin\AppData\Local\Temp\KeyGen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7940 | c:\users\admin\appdata\local\temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | KeyGen.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
360
Read events
358
Write events
2
Delete events
0
Modification events
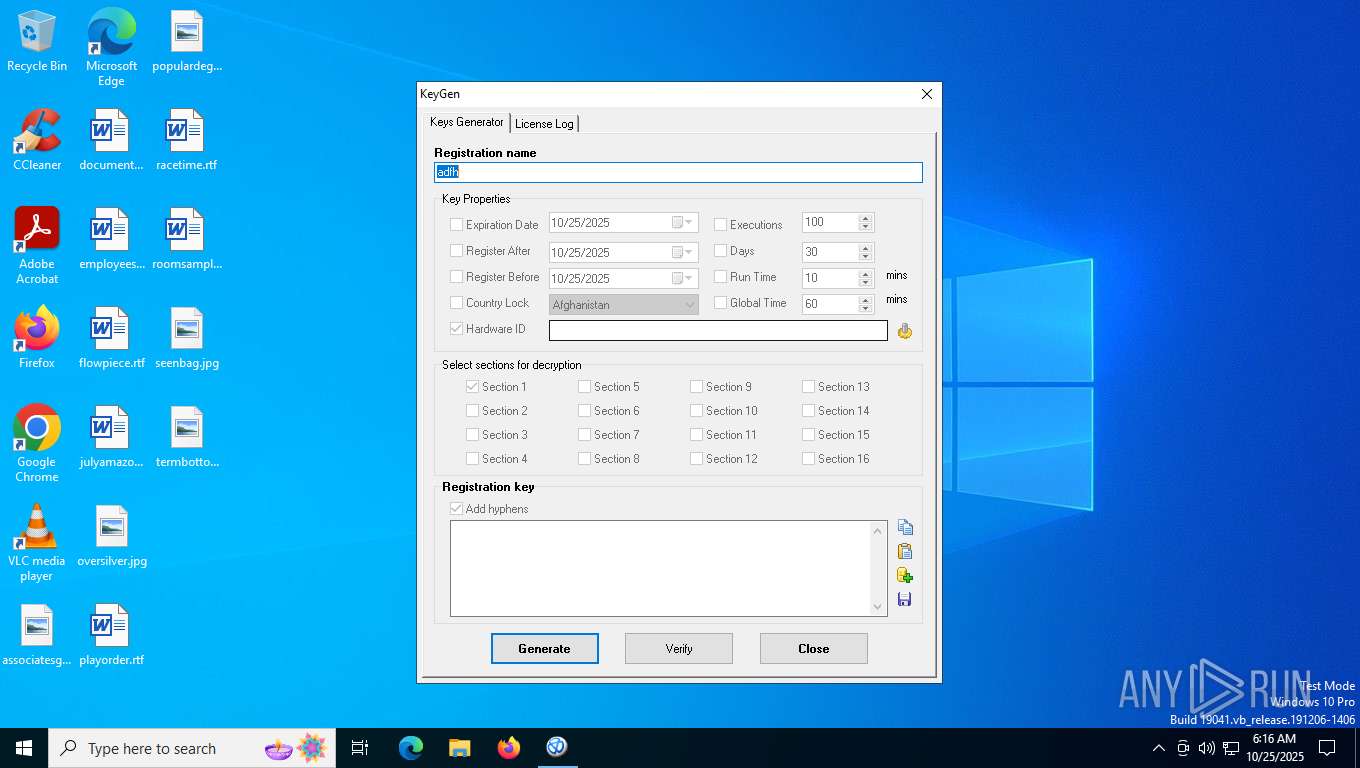
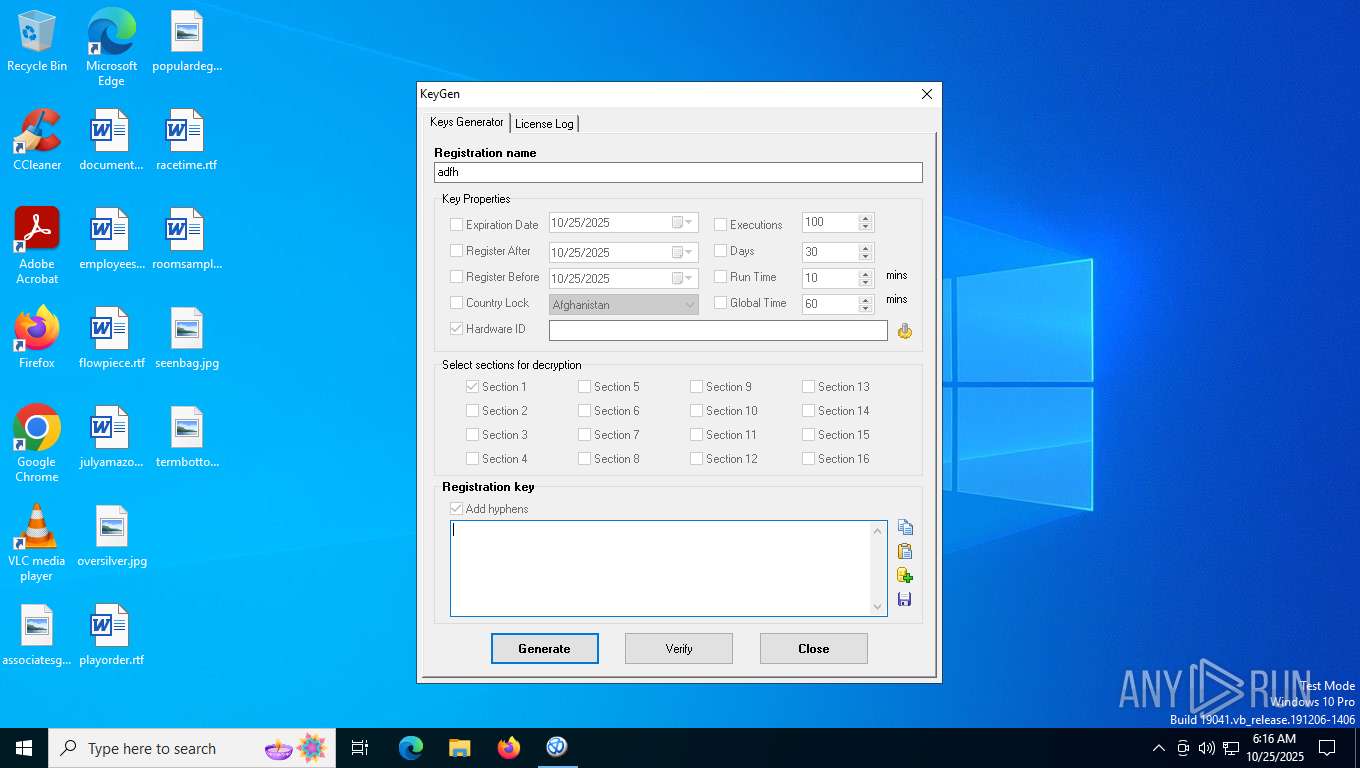
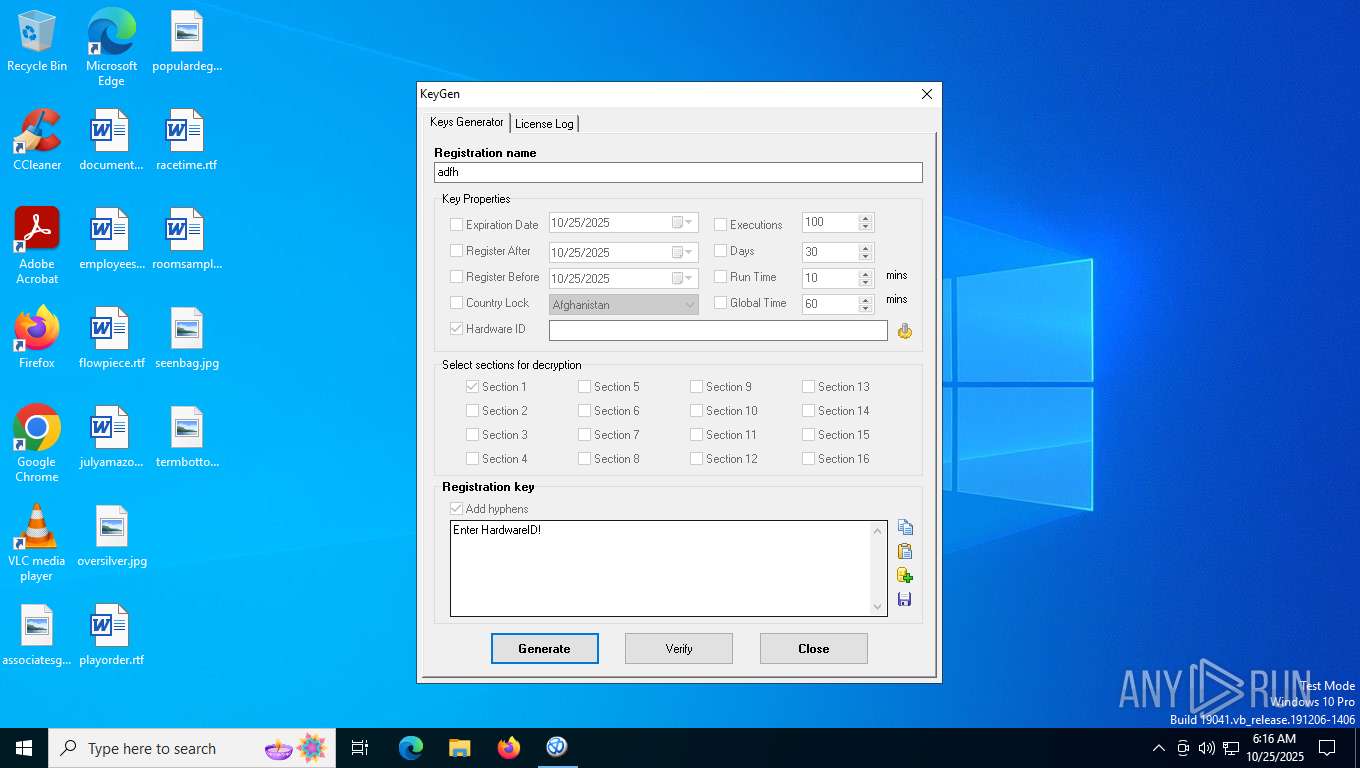
| (PID) Process: | (7916) KeyGen.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7940) keygen.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\TheEnigmaProtector2\Keygen |
| Operation: | write | Name: | Hyphens |
Value: 1 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7916 | KeyGen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:38E4889BE852DE46E60765E052D59A86 | SHA256:99FA861FD7C832F75598D54BB91FB61EE5078E4B89E5DA6A11DB43474E086CD7 | |||
| 7916 | KeyGen.exe | C:\Users\admin\AppData\Local\Temp\~DFD6D757E41EDD45D4.TMP | binary | |
MD5:5404F6F94C4D34D2B2A3DA5785F30B08 | SHA256:3D5C687AB2A9979C39DAEFF47302DC560DCC0B703EB71840BFF547BC4A90FD81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
41
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7460 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6784 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7212 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7212 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5048 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5424 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 95.101.136.194:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7088 | SearchApp.exe | 95.101.136.194:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
3440 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7392 | backgroundTaskHost.exe | 95.101.136.194:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
7460 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |