| download: | Loader.rar |
| Full analysis: | https://app.any.run/tasks/2c339638-f113-4c28-a0cf-24cda5a7cda6 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 18:15:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
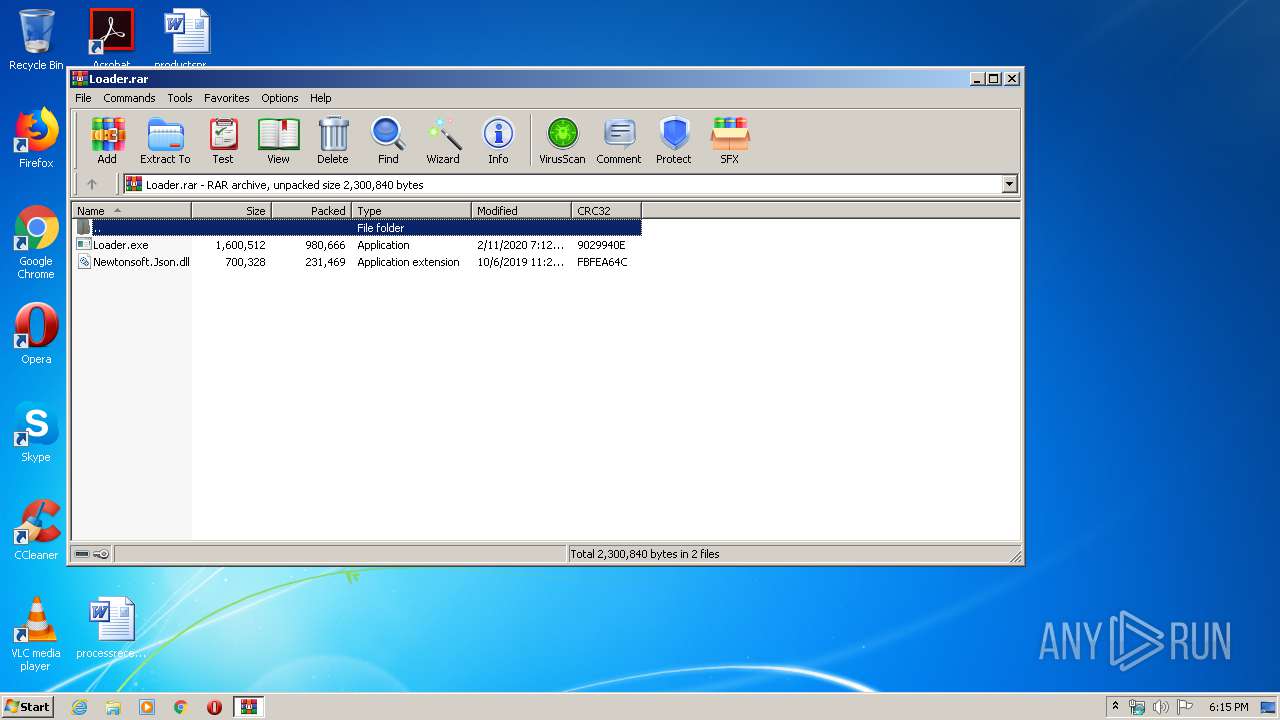
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5275EF55E09A50C5A9848A663751317A |
| SHA1: | 83691F5ECB4C1BDFFA726E8DD249B19E2E6CEB1E |
| SHA256: | BFA208385133F7FF4F72F3F372A0F73EAF0C5F294495925BEE121B5527D3B552 |
| SSDEEP: | 24576:KV3ChKZBiJ3lLeH7YcCGILPl8NZT1lhcVKdhHkyWhSk/TKss/ZH2PhQlWIK7L:KhidOCGyPwB1lhwKdC/SxssBH2PylWpf |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3548)
- Loader.exe (PID: 3120)
- Loader.exe (PID: 2960)
- Loader.exe (PID: 2312)
Application was dropped or rewritten from another process
- Loader.exe (PID: 2400)
- Loader.exe (PID: 3120)
- Loader.exe (PID: 2668)
- Loader.exe (PID: 2960)
- Loader.exe (PID: 2312)
- Loader.exe (PID: 1468)
Changes settings of System certificates
- Loader.exe (PID: 3120)
SUSPICIOUS
Executable content was dropped or overwritten
- Loader.exe (PID: 3120)
- Loader.exe (PID: 2960)
- Loader.exe (PID: 2312)
Adds / modifies Windows certificates
- Loader.exe (PID: 3120)
INFO
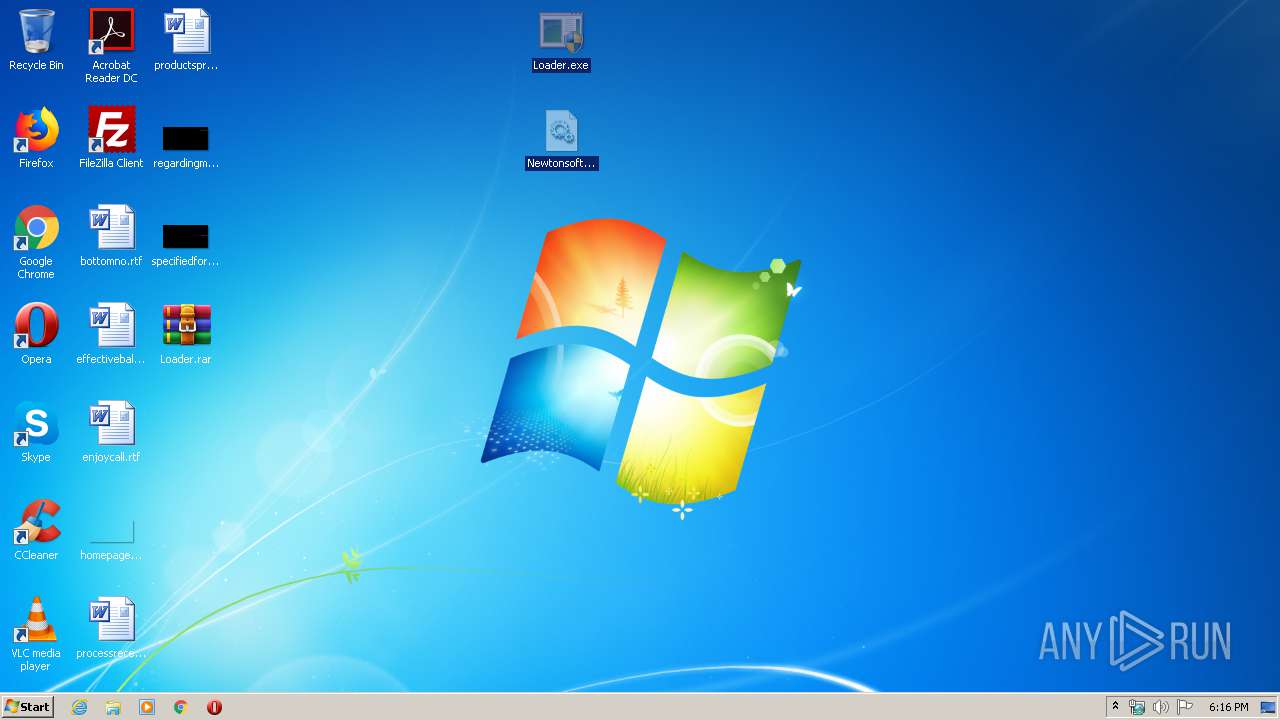
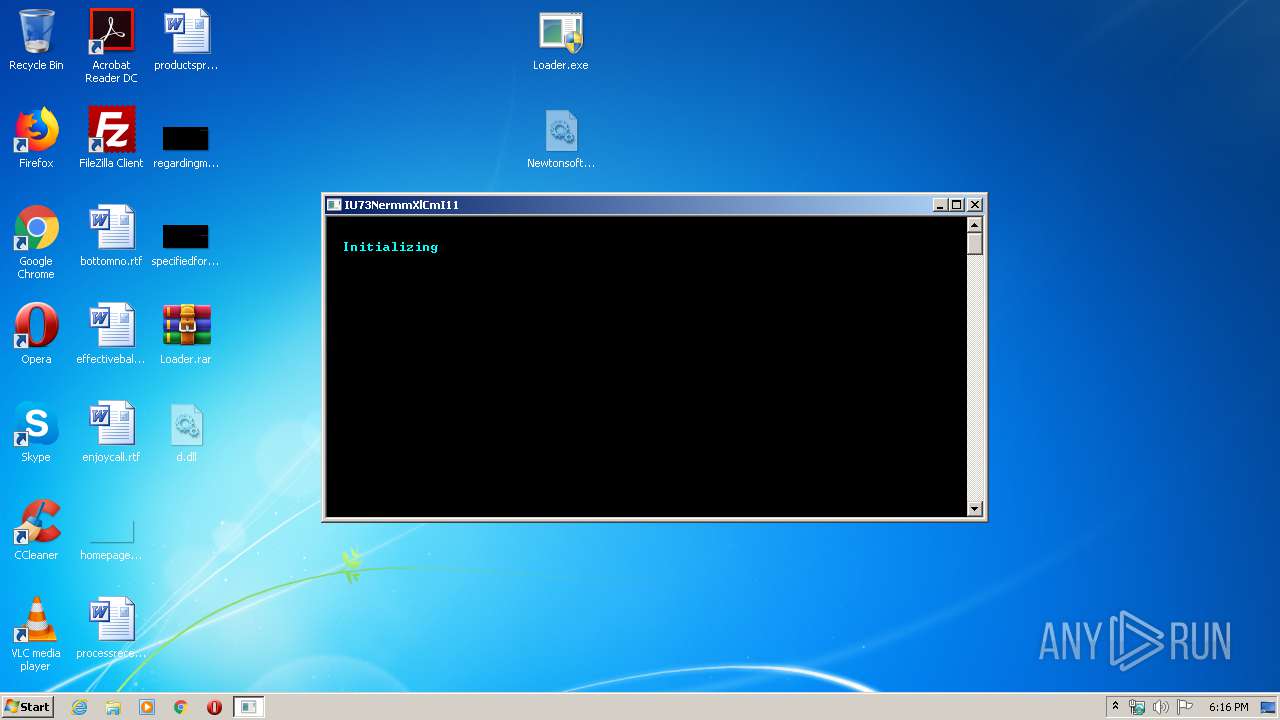
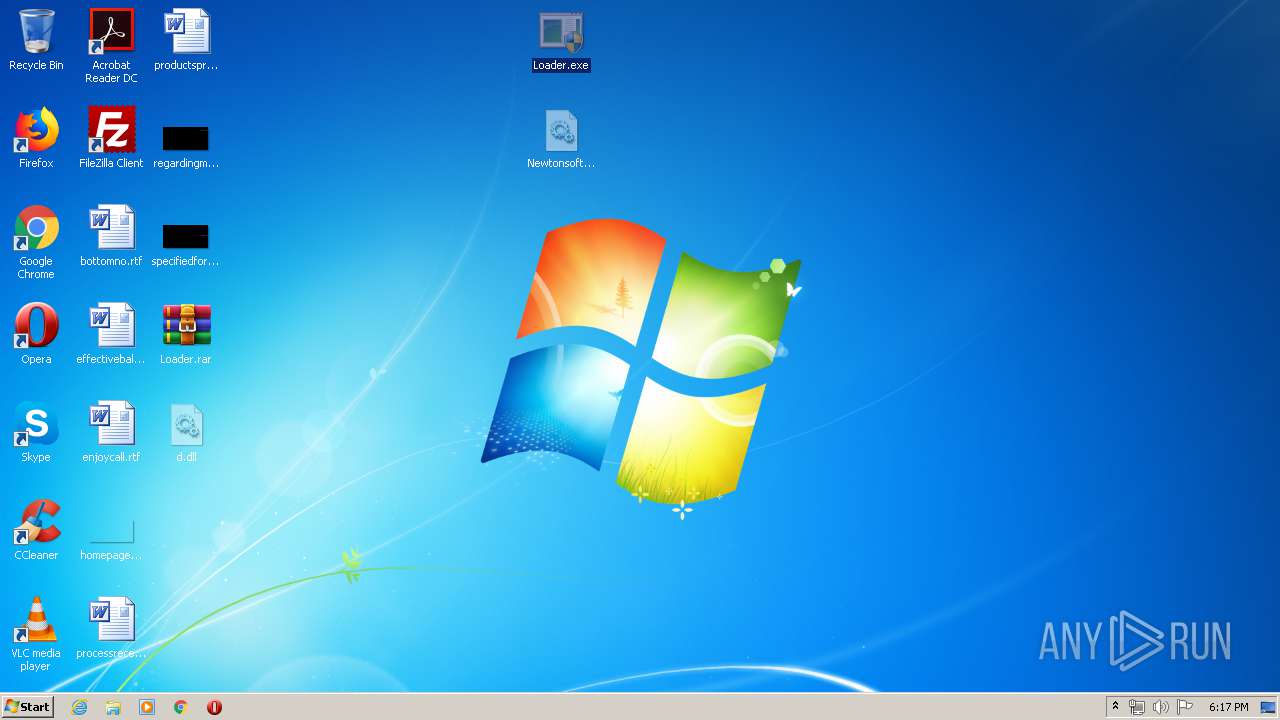
Manual execution by user
- Loader.exe (PID: 2400)
- Loader.exe (PID: 3120)
- Loader.exe (PID: 2960)
- Loader.exe (PID: 2668)
- Loader.exe (PID: 1468)
- Loader.exe (PID: 2312)
Reads settings of System Certificates
- Loader.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
59
Monitored processes
8
Malicious processes
4
Suspicious processes
0
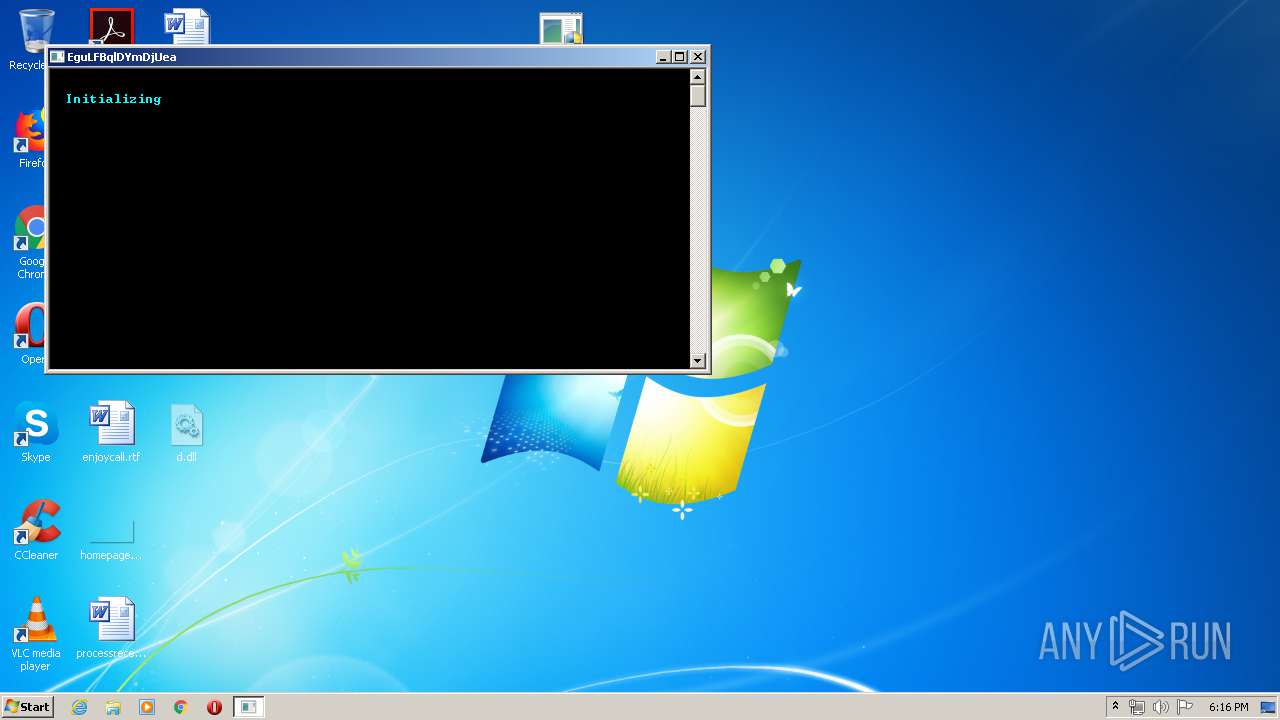
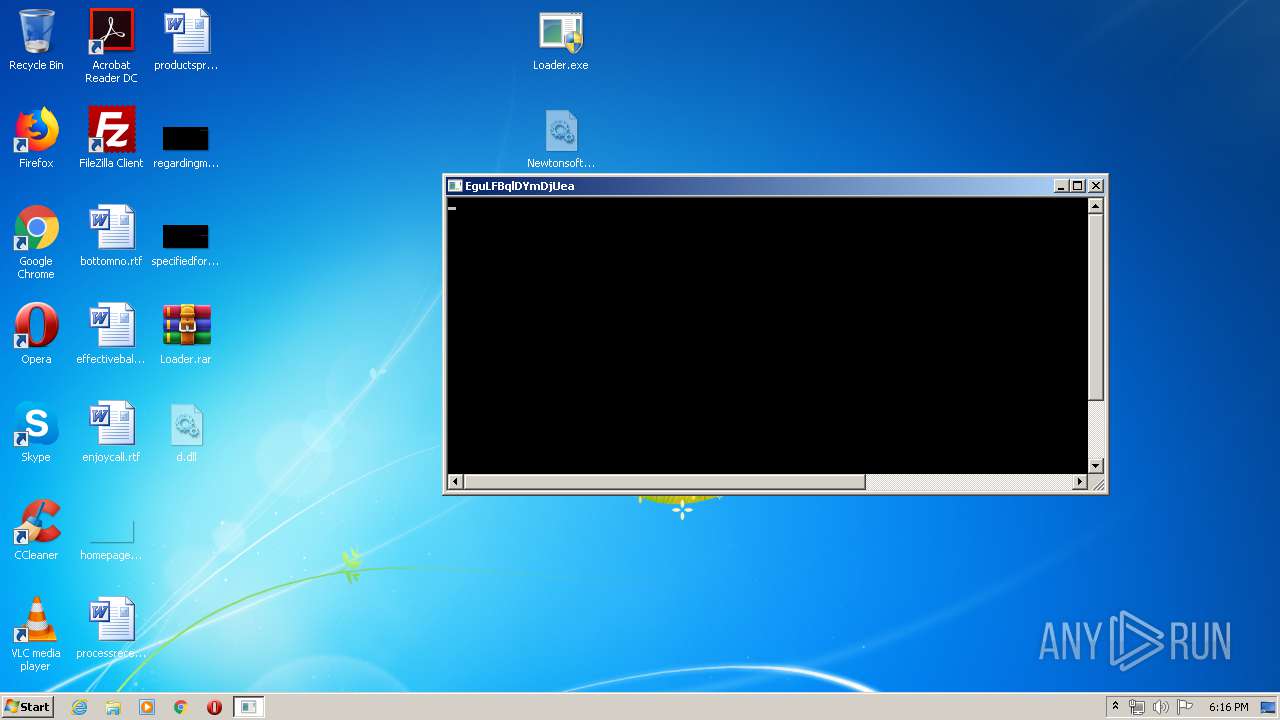
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
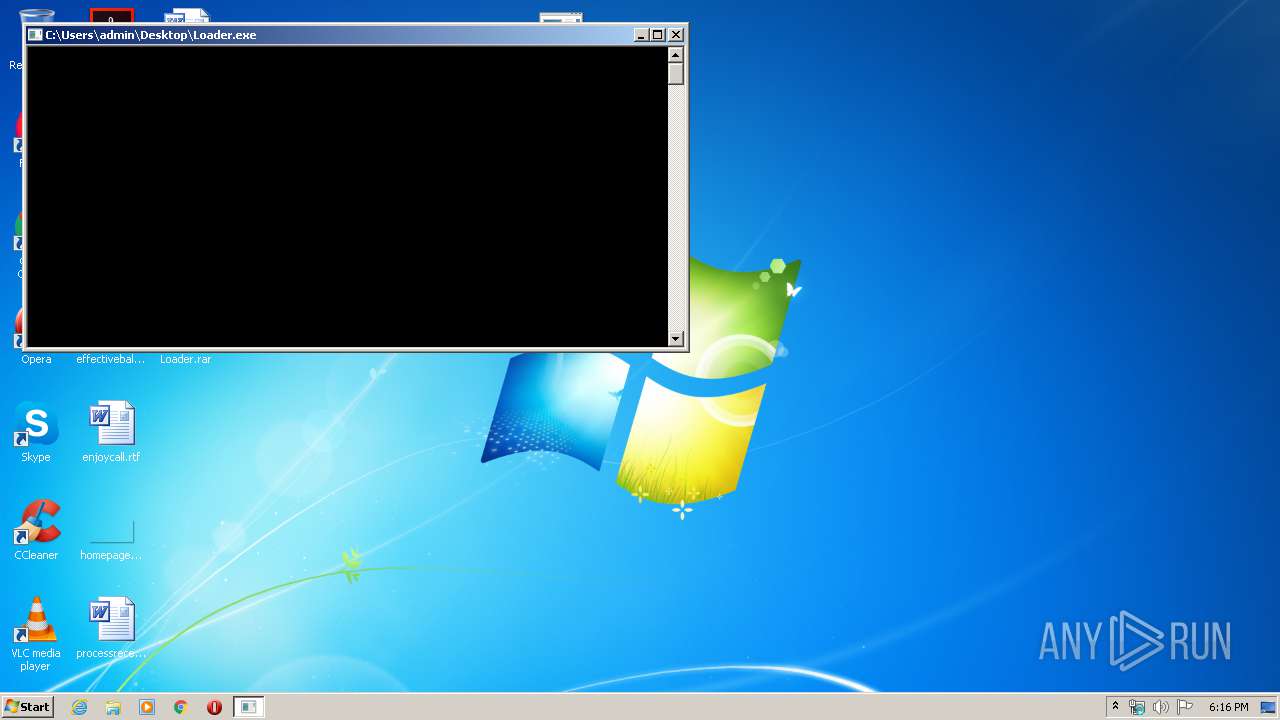
| 1468 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Pear Loader Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
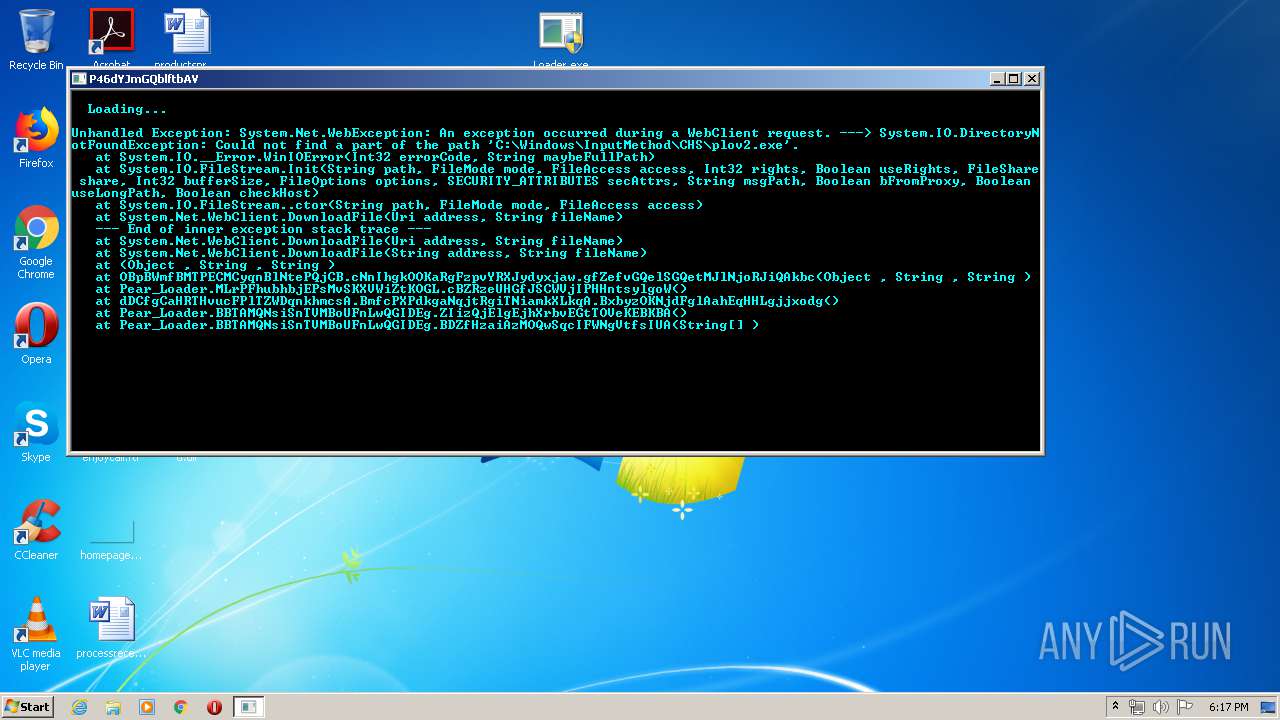
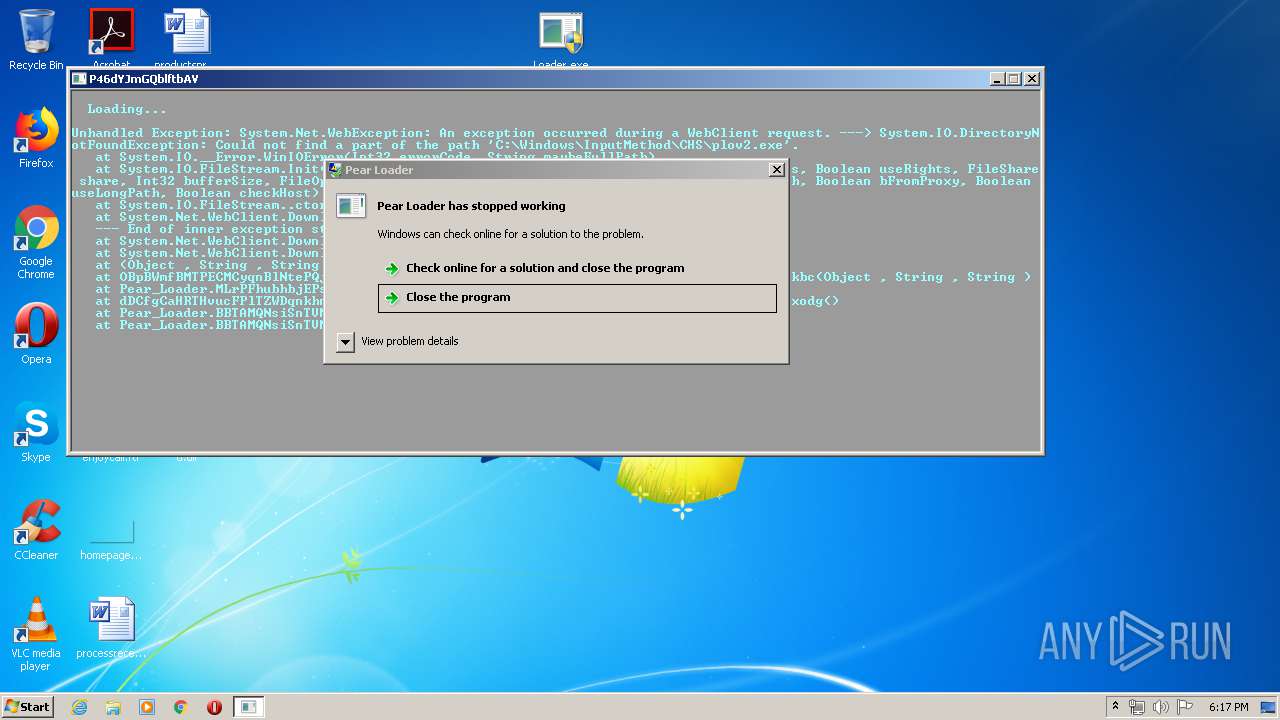
| 2312 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Pear Loader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Pear Loader Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Loader.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Pear Loader Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Pear Loader Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Pear Loader Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 665
Read events
431
Write events
1 234
Delete events
0
Modification events
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Loader.rar | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
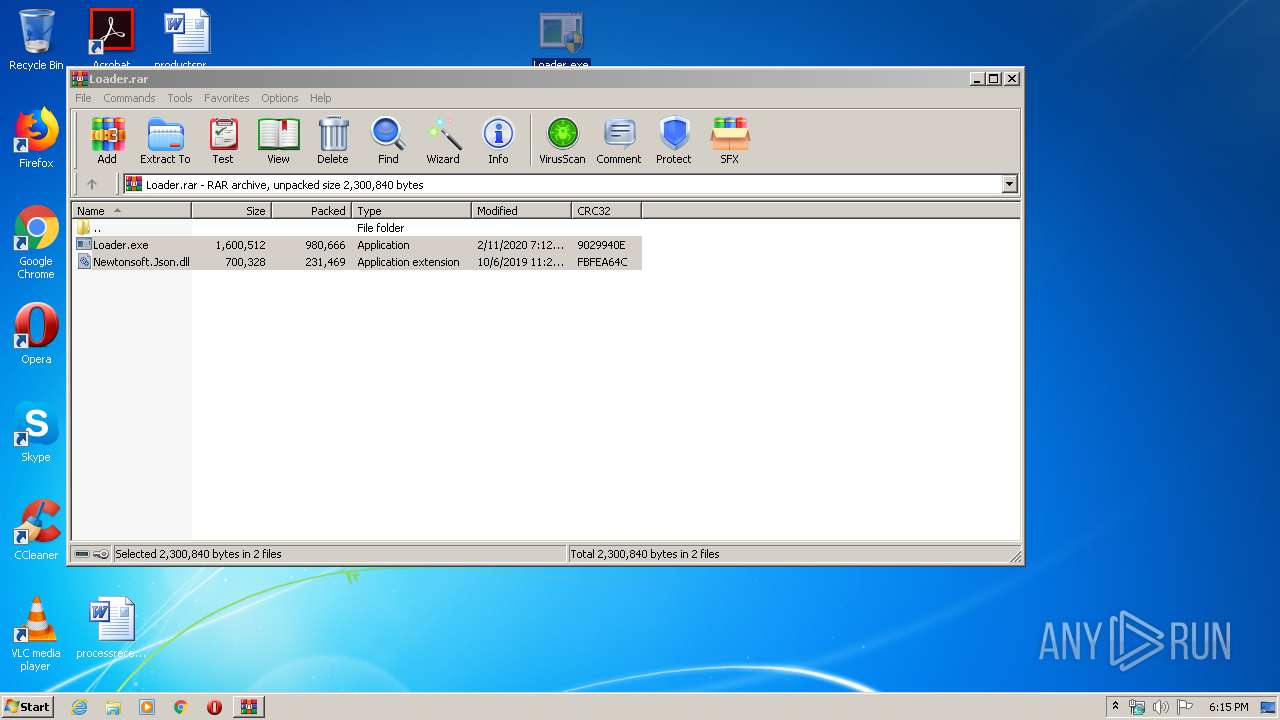
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.45965\Loader.exe | — | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.45965\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 2312 | Loader.exe | C:\Users\admin\Desktop\d.dll | executable | |
MD5:25C0AD929078001A9ABCE07D5636E4B0 | SHA256:58D9B84F39DB8E009D347B360B0165DB1CEF8F75AB56A82084487864791ED9CB | |||
| 3120 | Loader.exe | C:\Users\admin\Desktop\d.dll | executable | |
MD5:25C0AD929078001A9ABCE07D5636E4B0 | SHA256:58D9B84F39DB8E009D347B360B0165DB1CEF8F75AB56A82084487864791ED9CB | |||
| 2960 | Loader.exe | C:\Users\admin\Desktop\d.dll | executable | |
MD5:25C0AD929078001A9ABCE07D5636E4B0 | SHA256:58D9B84F39DB8E009D347B360B0165DB1CEF8F75AB56A82084487864791ED9CB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
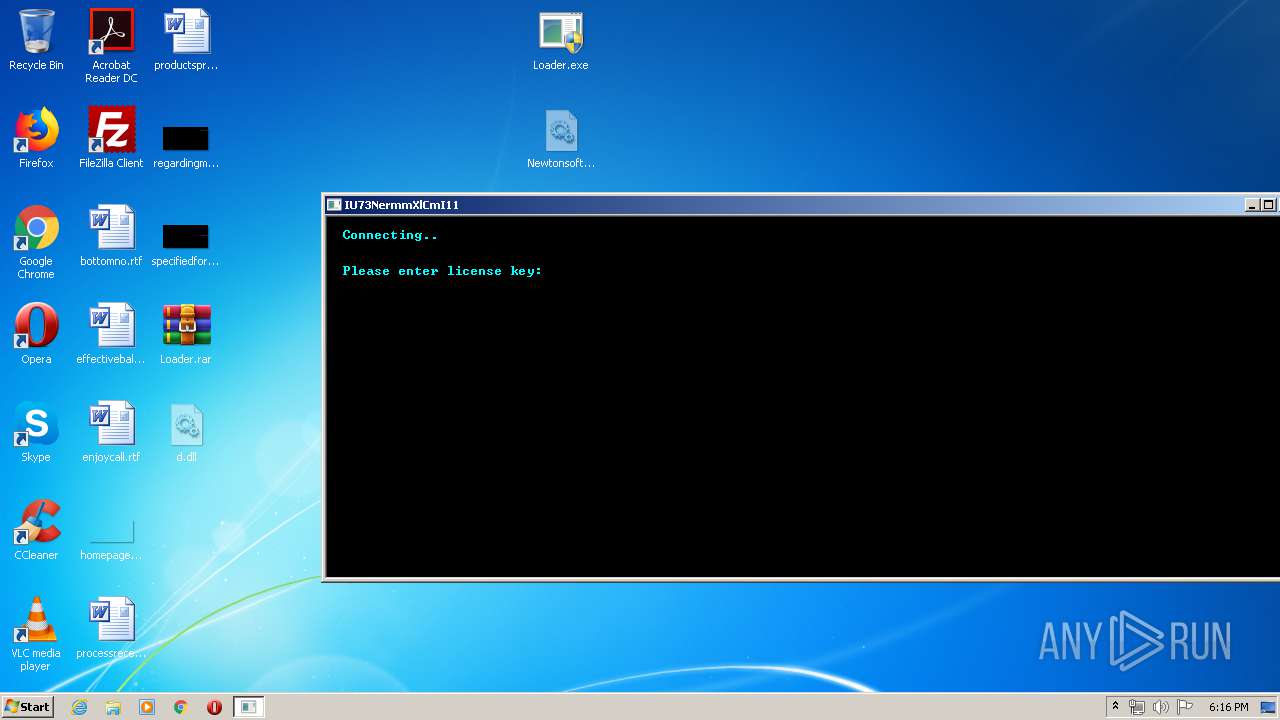
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3120 | Loader.exe | 104.27.138.23:443 | api.auth.gg | Cloudflare Inc | US | shared |
2312 | Loader.exe | 104.27.138.23:443 | api.auth.gg | Cloudflare Inc | US | shared |
2960 | Loader.exe | 104.27.138.23:443 | api.auth.gg | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
api.auth.gg |
| whitelisted |
Threats
Process | Message |
|---|---|
Loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
Loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
Loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |