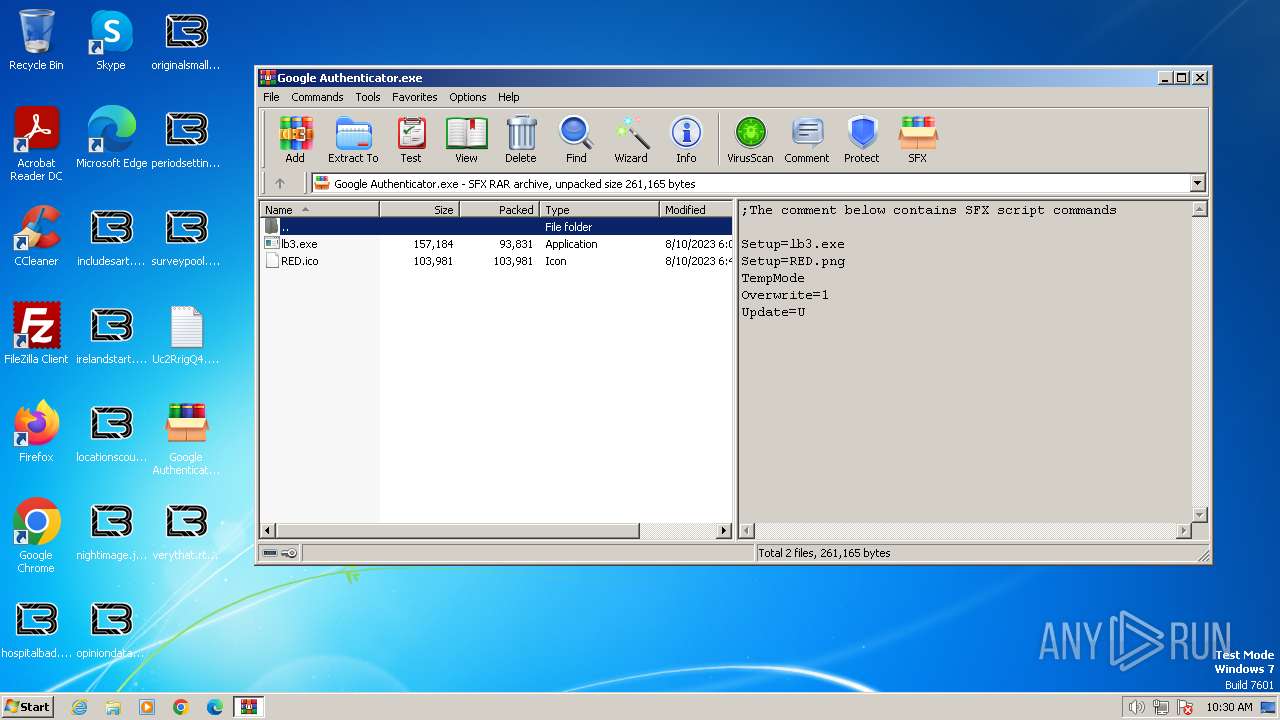
| File name: | Google Authenticator.exe |
| Full analysis: | https://app.any.run/tasks/46b314c4-1f61-4afb-a774-e750bd014840 |
| Verdict: | Malicious activity |
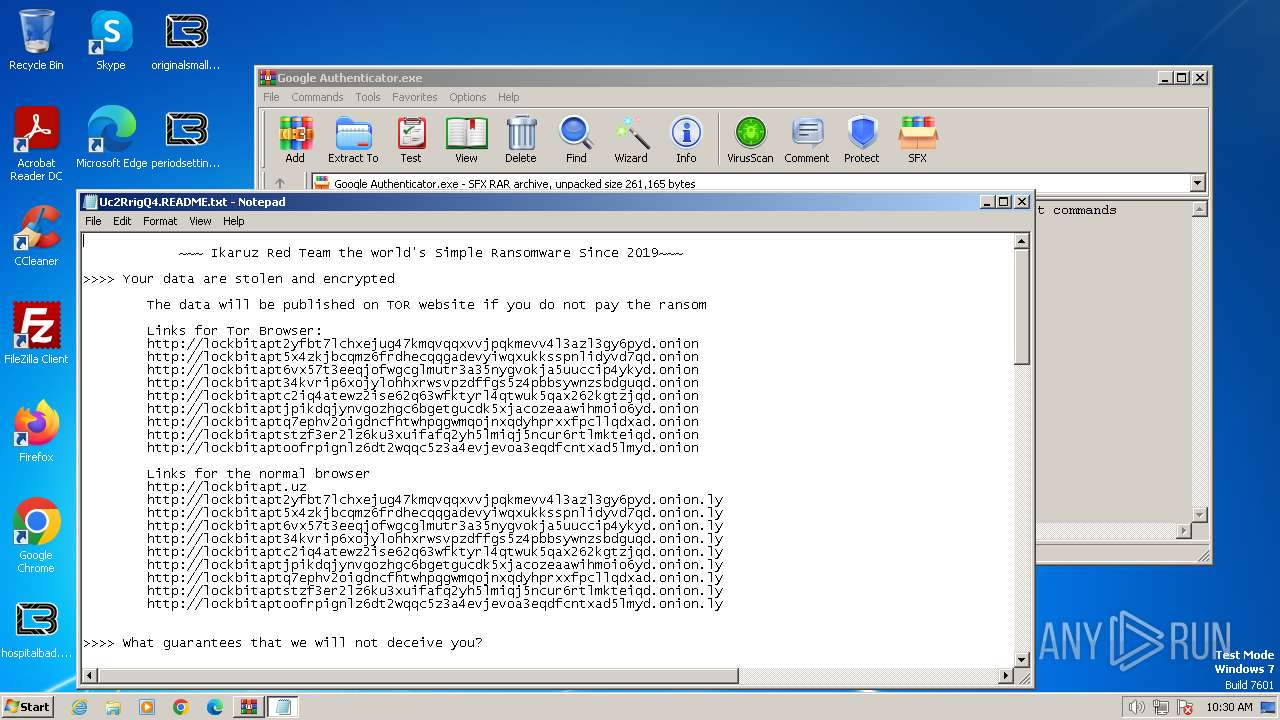
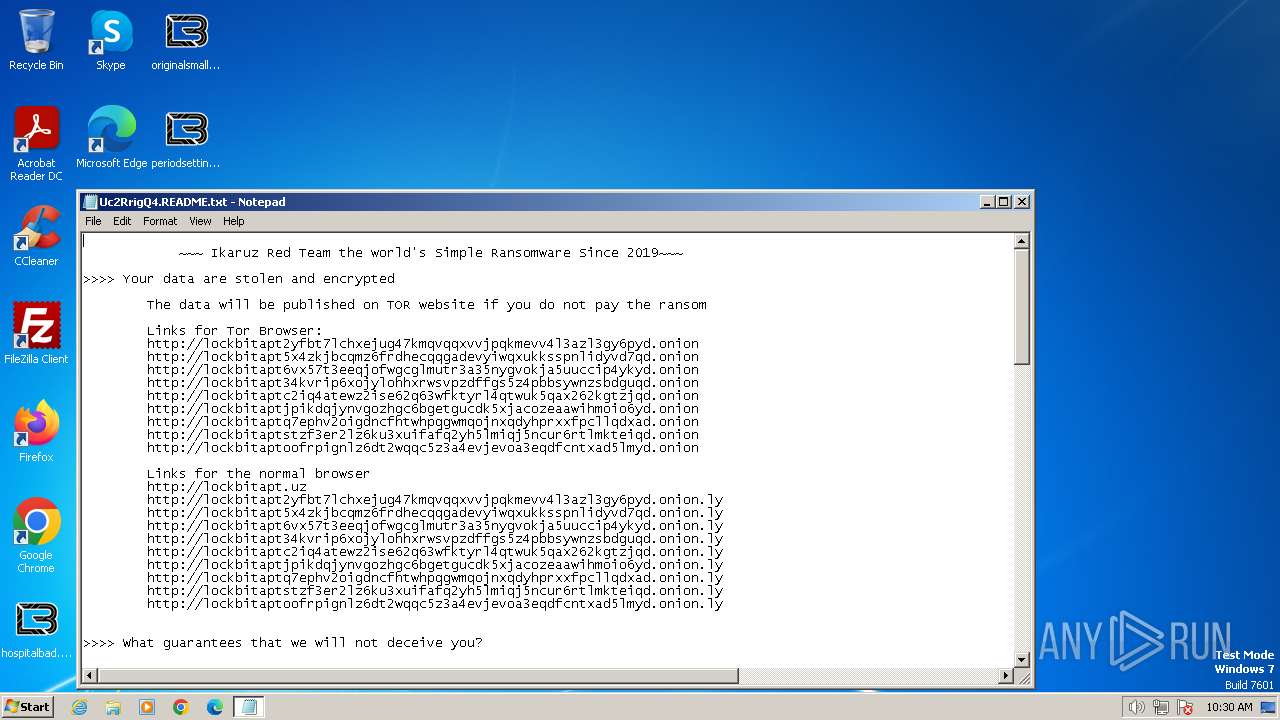
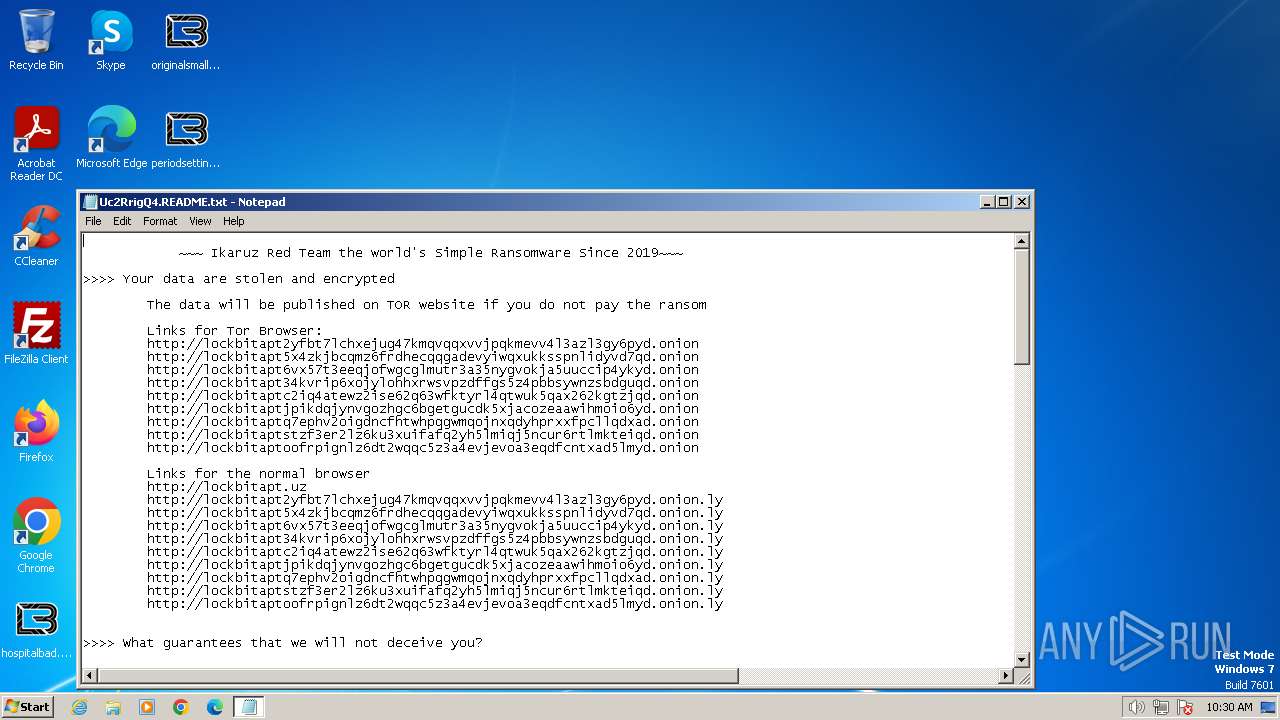
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | April 15, 2024, 09:29:21 |
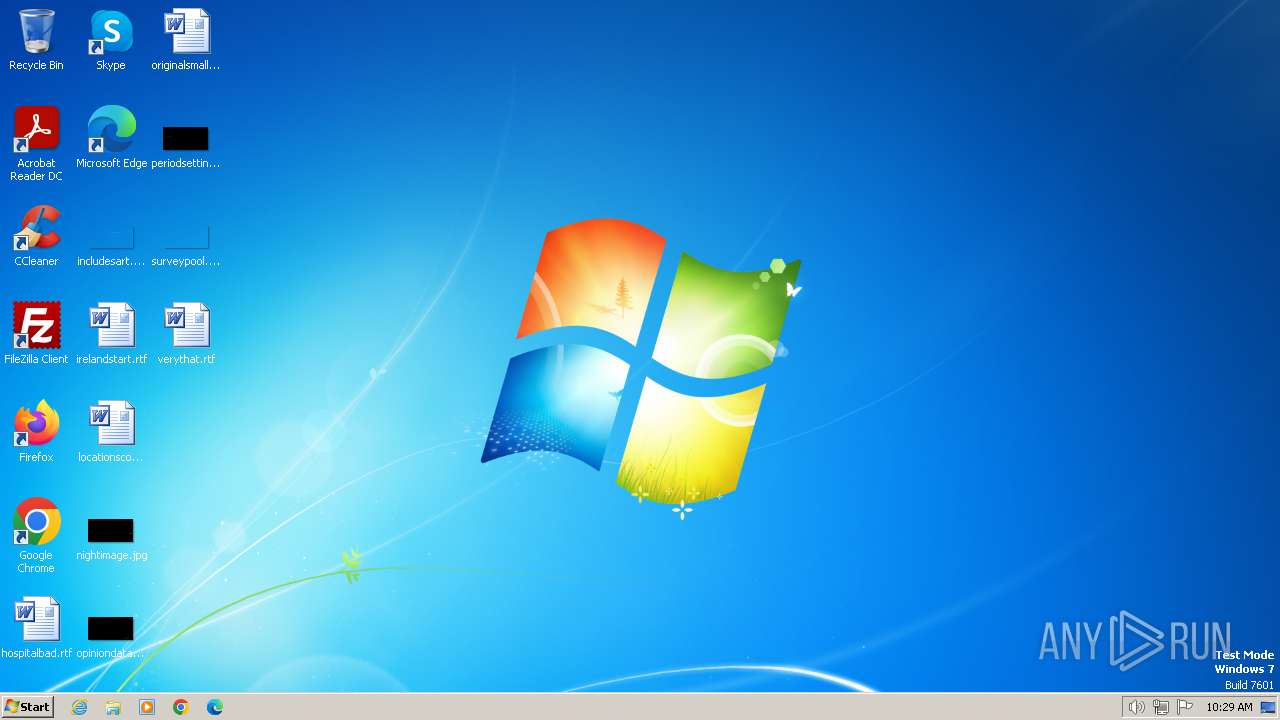
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CA9030325048D92594BC29EC5D6E5B6E |
| SHA1: | B65183CC886185A8C34860F68D3289D8E9DD84E3 |
| SHA256: | BFA1A2BD23754277EE1F31E80C92D9C5309F150083451BFC33BBEB604ADEC8F6 |
| SSDEEP: | 24576:3fV9cxnnsjRlvPvccV8iGkWw+lEKX76cYxr0Rm:3fV9cnsjRlvHHV8iGkYEK76cYxQm |
MALICIOUS
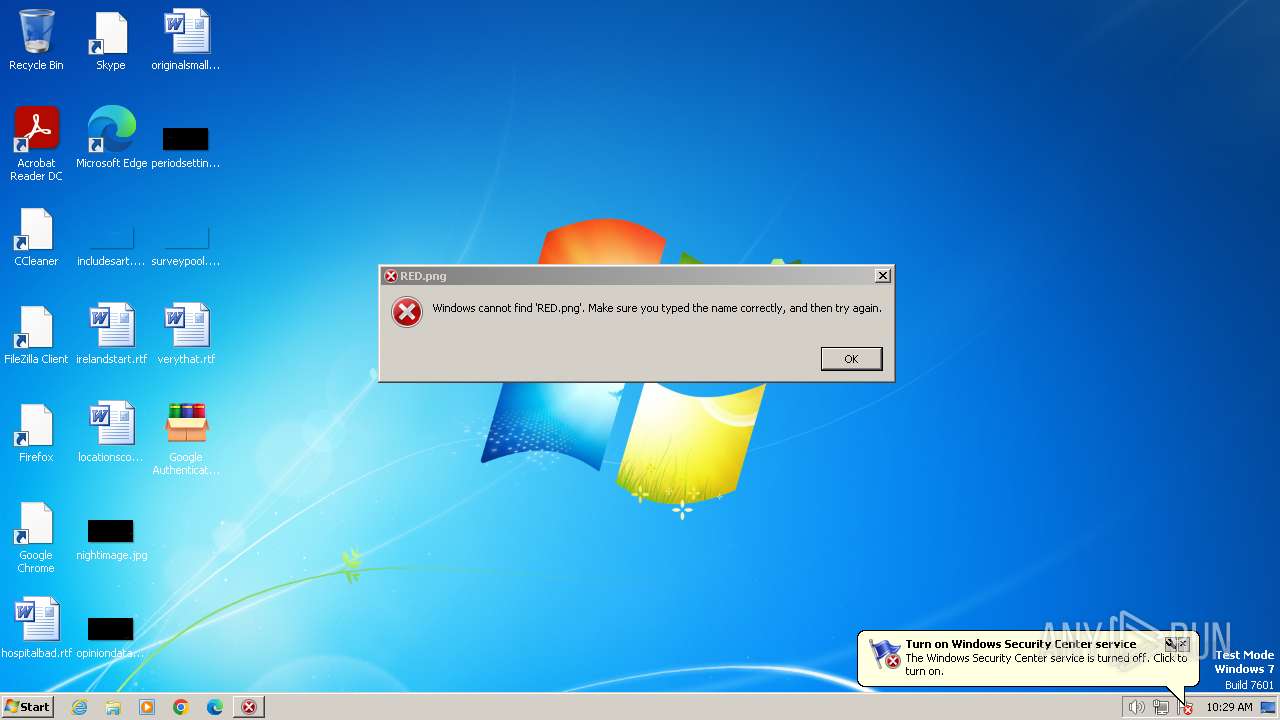
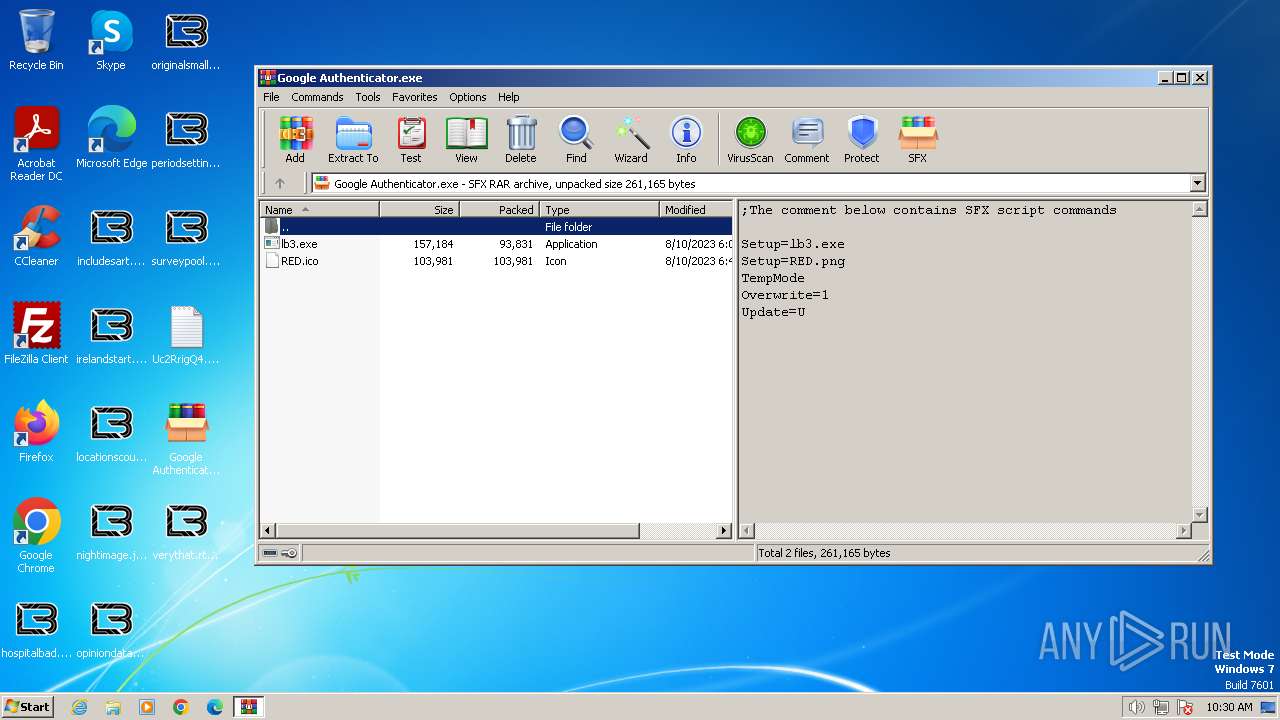
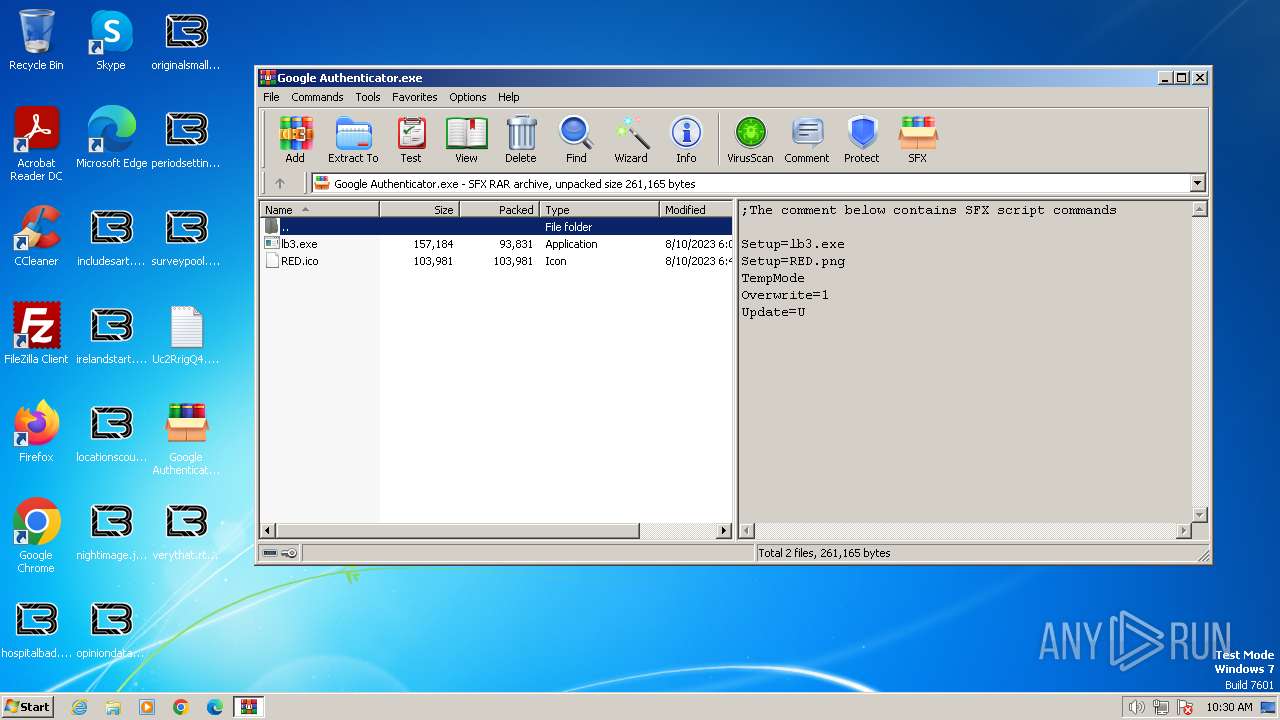
Drops the executable file immediately after the start
- Google Authenticator.exe (PID: 3212)
- lb3.exe (PID: 2256)
Known privilege escalation attack
- dllhost.exe (PID: 2408)
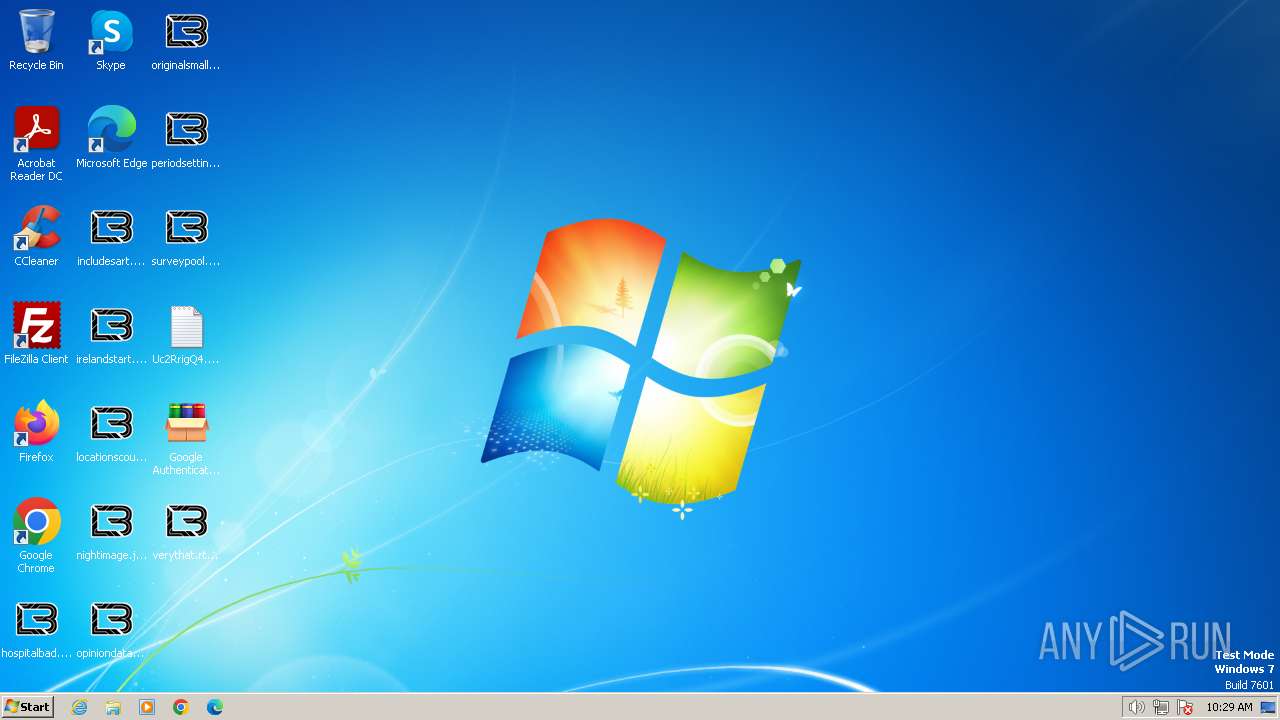
Renames files like ransomware
- lb3.exe (PID: 2256)
[YARA] LockBit is detected
- lb3.exe (PID: 2256)
Steals credentials from Web Browsers
- lb3.exe (PID: 2256)
Actions looks like stealing of personal data
- lb3.exe (PID: 2256)
SUSPICIOUS
Reads the Internet Settings
- Google Authenticator.exe (PID: 3212)
Reads security settings of Internet Explorer
- Google Authenticator.exe (PID: 3212)
Executable content was dropped or overwritten
- Google Authenticator.exe (PID: 3212)
Reads browser cookies
- lb3.exe (PID: 2256)
Write to the desktop.ini file (may be used to cloak folders)
- lb3.exe (PID: 2256)
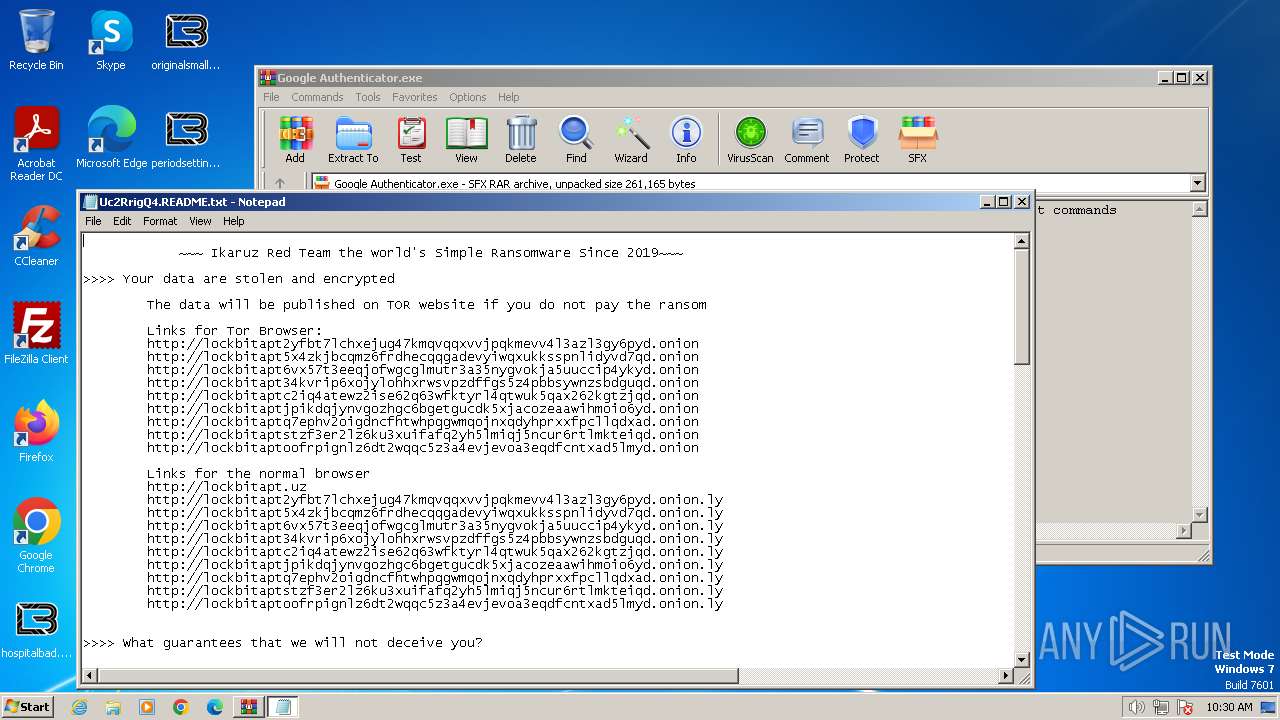
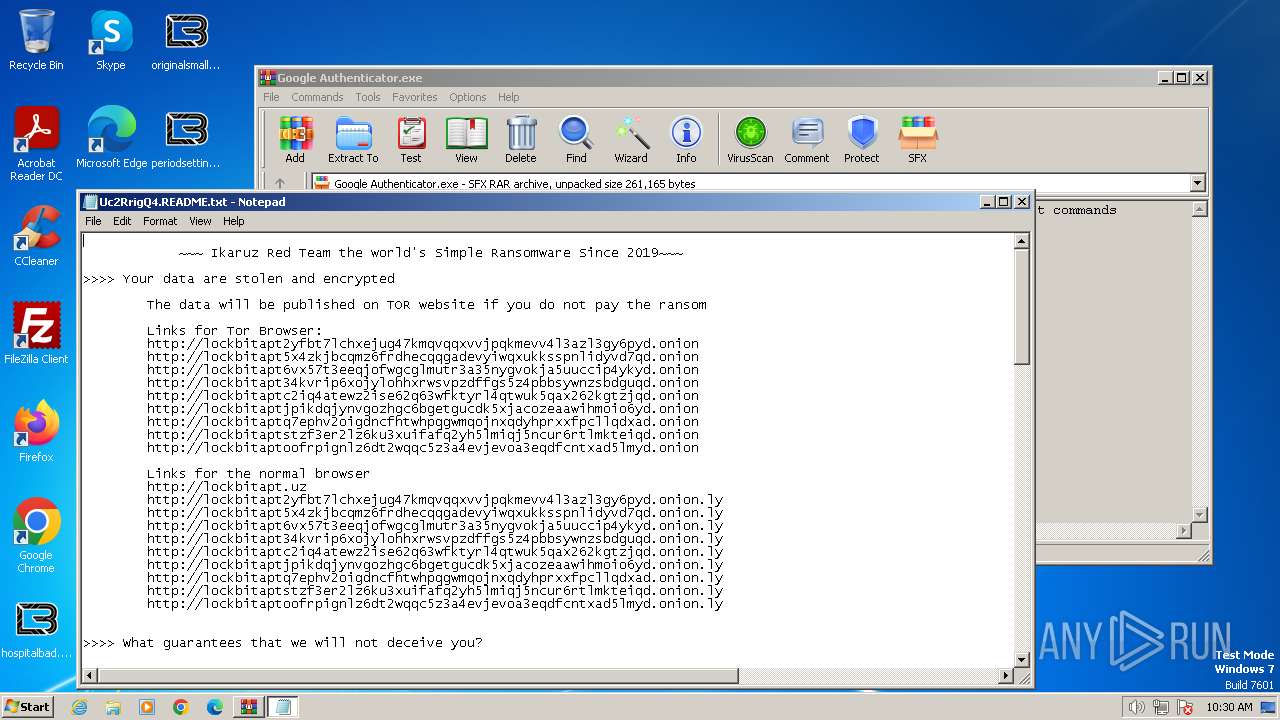
Creates files like ransomware instruction
- lb3.exe (PID: 2256)
INFO
Reads the computer name
- Google Authenticator.exe (PID: 3212)
- lb3.exe (PID: 1836)
- lb3.exe (PID: 2256)
Checks supported languages
- lb3.exe (PID: 1836)
- Google Authenticator.exe (PID: 3212)
- lb3.exe (PID: 2256)
Checks transactions between databases Windows and Oracle
- lb3.exe (PID: 1836)
Reads the machine GUID from the registry
- lb3.exe (PID: 1836)
- lb3.exe (PID: 2256)
Create files in a temporary directory
- Google Authenticator.exe (PID: 3212)
- lb3.exe (PID: 2256)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 2408)
Creates files in the program directory
- lb3.exe (PID: 2256)
Creates files or folders in the user directory
- lb3.exe (PID: 2256)
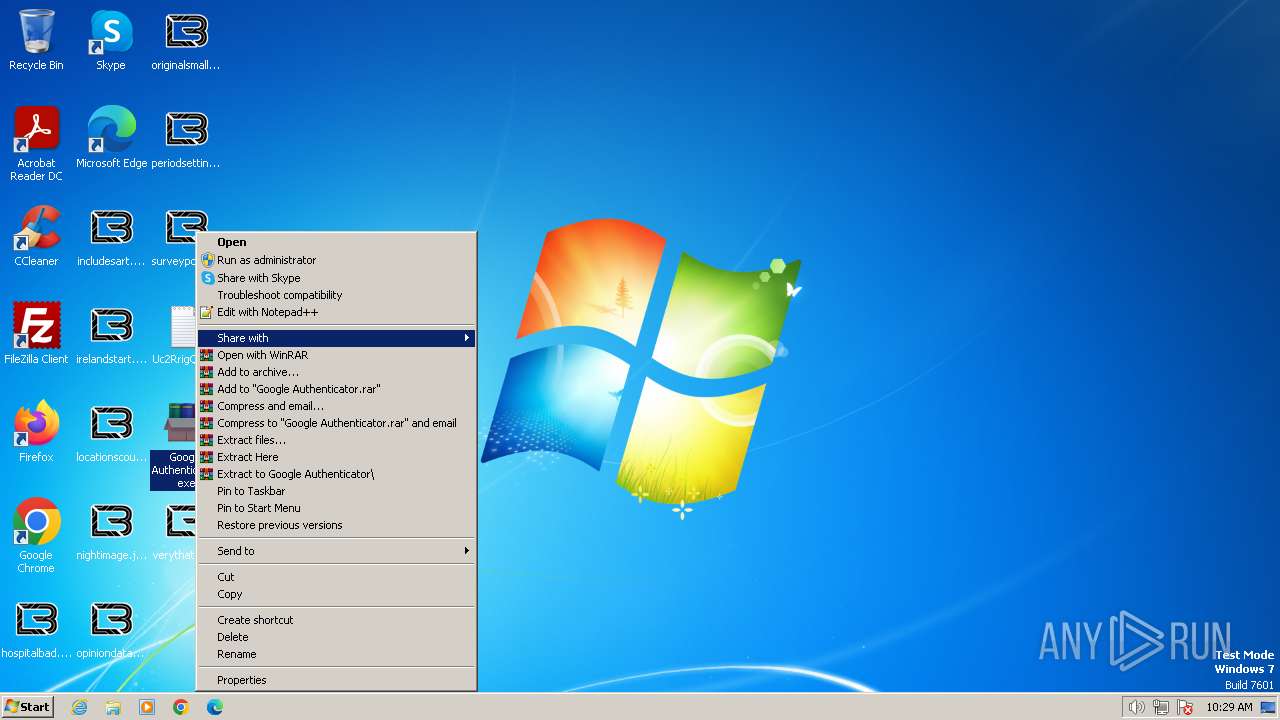
Manual execution by a user
- notepad.exe (PID: 2336)
- WinRAR.exe (PID: 2804)
- notepad.exe (PID: 1816)
- notepad.exe (PID: 2972)
- notepad.exe (PID: 3984)
- notepad.exe (PID: 2632)
- notepad.exe (PID: 2040)
Dropped object may contain TOR URL's
- lb3.exe (PID: 2256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:08:01 09:26:10+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 208384 |
| InitializedDataSize: | 262144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20790 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
53
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Uc2RrigQ4.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\lb3.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\lb3.exe | — | Google Authenticator.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2040 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Uc2RrigQ4.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\lb3.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\lb3.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2336 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Uc2RrigQ4.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Uc2RrigQ4.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
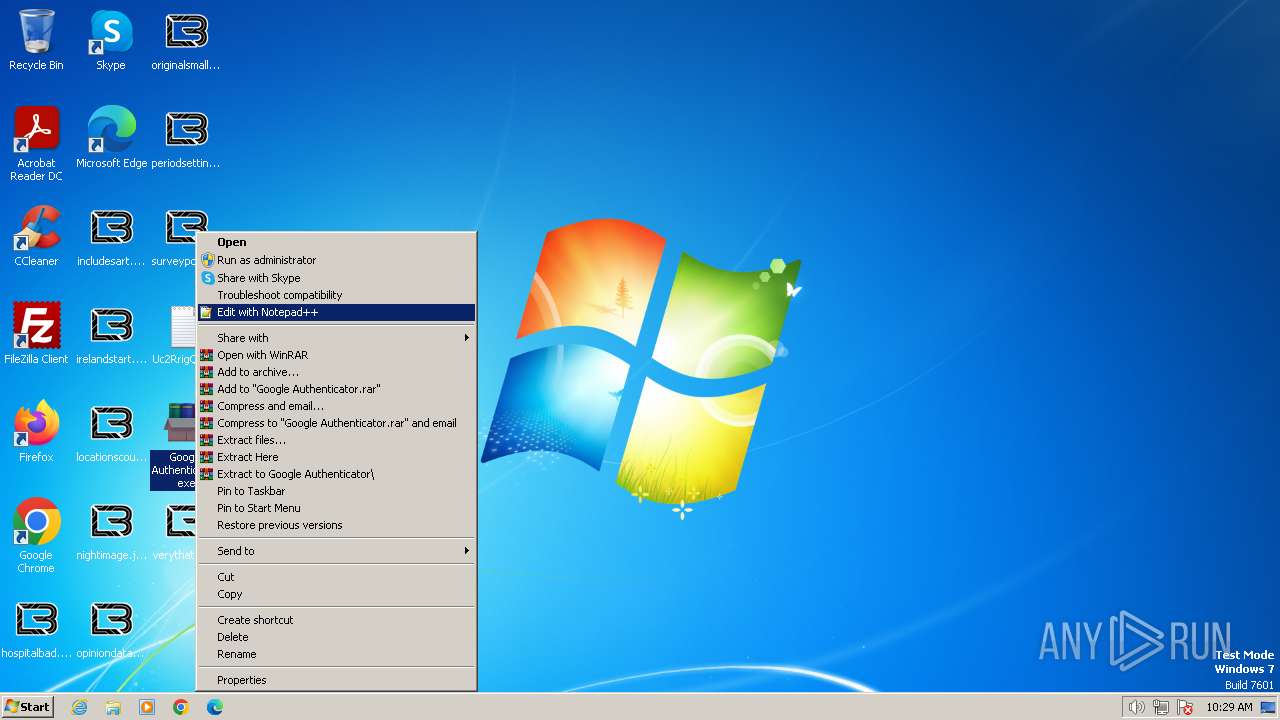
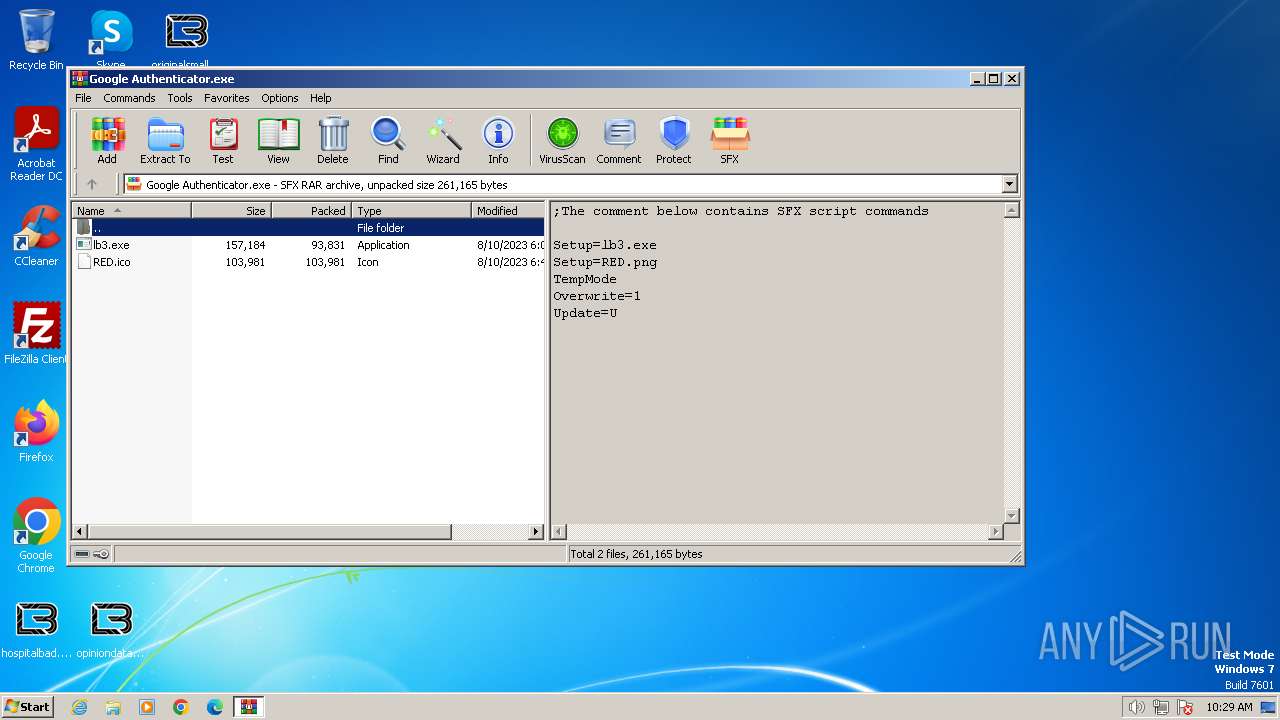
| 2804 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Google Authenticator.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2972 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Uc2RrigQ4.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | "C:\Users\admin\Desktop\Google Authenticator.exe" | C:\Users\admin\Desktop\Google Authenticator.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
9 222
Read events
9 182
Write events
40
Delete events
0
Modification events
| (PID) Process: | (3212) Google Authenticator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3212) Google Authenticator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3212) Google Authenticator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3212) Google Authenticator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2408) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2408) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2408) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2408) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2256) lb3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 116 | |||
| (PID) Process: | (2804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
11
Suspicious files
657
Text files
915
Unknown types
617
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3212 | Google Authenticator.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lb3.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | Google Authenticator.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\RED.ico | image | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\ProgramData\Uc2RrigQ4.ico | image | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini | binary | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\Uc2RrigQ4.README.txt | — | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\Users\Uc2RrigQ4.README.txt | text | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\AAAAAAAAAAA | binary | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\BBBBBBBBBBB | binary | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\CCCCCCCCCCC | binary | |
MD5:— | SHA256:— | |||
| 2256 | lb3.exe | C:\Users\Administrator\Uc2RrigQ4.README.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |