| File name: | WARRIOR_protected (1).exe |
| Full analysis: | https://app.any.run/tasks/c19735b2-3719-4d76-a5d4-e2d4d244179c |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2025, 02:43:10 |
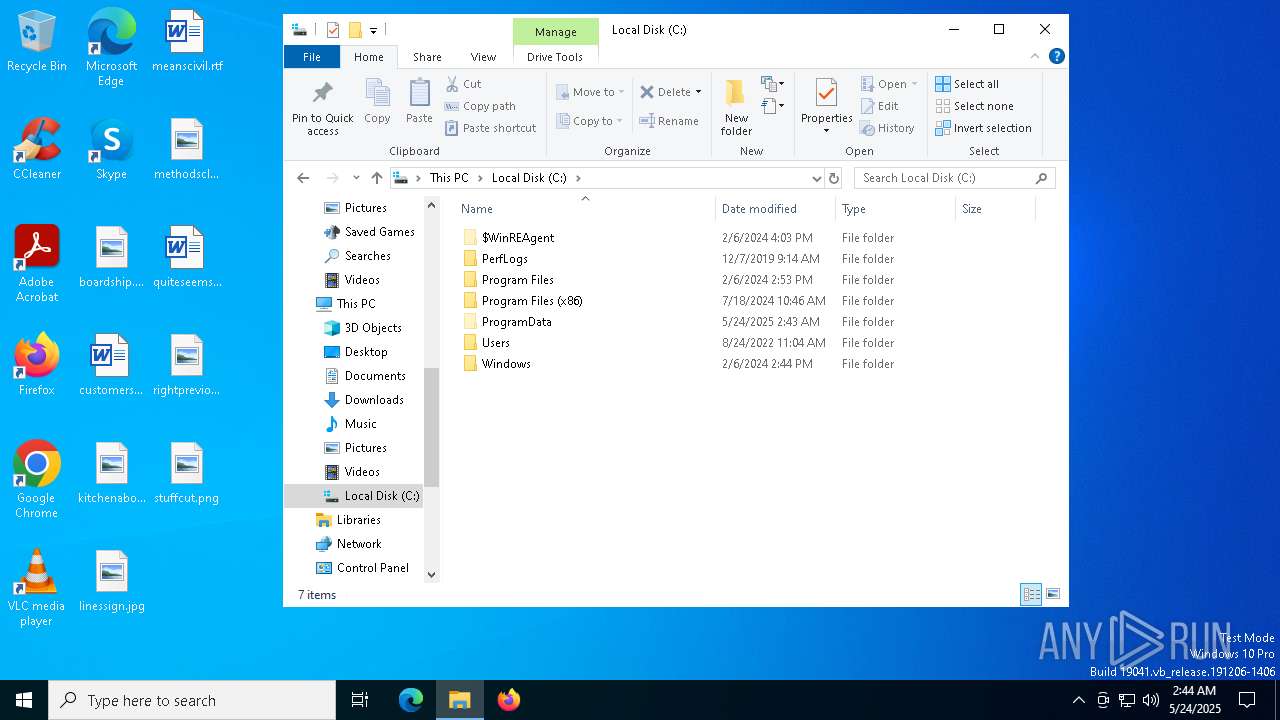
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 12 sections |
| MD5: | F9F4C2D9AE696125B4A0226A6013007C |
| SHA1: | 01667C94F93DAA266508797A7915790272706318 |
| SHA256: | BF9967037A19E478F1BE7DE87035FC81769D1CB3241E510D1EE55FD3B61A8D68 |
| SSDEEP: | 98304:K2G+/PYKWez3AMUZyO9pyTgFxonnh+XYDl8YZd+iNTP5oQV+SYZeEKpYX8jW0byE:Rmu4578SUjMlQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the BIOS version
- WARRIOR_protected (1).exe (PID: 1056)
Starts CMD.EXE for commands execution
- WARRIOR_protected (1).exe (PID: 1056)
Reads security settings of Internet Explorer
- WARRIOR_protected (1).exe (PID: 1056)
INFO
Checks proxy server information
- WARRIOR_protected (1).exe (PID: 1056)
- slui.exe (PID: 3784)
Checks supported languages
- WARRIOR_protected (1).exe (PID: 1056)
- identity_helper.exe (PID: 8020)
- identity_helper.exe (PID: 7724)
Process checks whether UAC notifications are on
- WARRIOR_protected (1).exe (PID: 1056)
Creates files in the program directory
- WARRIOR_protected (1).exe (PID: 1056)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 1184)
Reads the computer name
- WARRIOR_protected (1).exe (PID: 1056)
- identity_helper.exe (PID: 8020)
- identity_helper.exe (PID: 7724)
Application launched itself
- msedge.exe (PID: 1196)
- msedge.exe (PID: 2852)
- msedge.exe (PID: 8116)
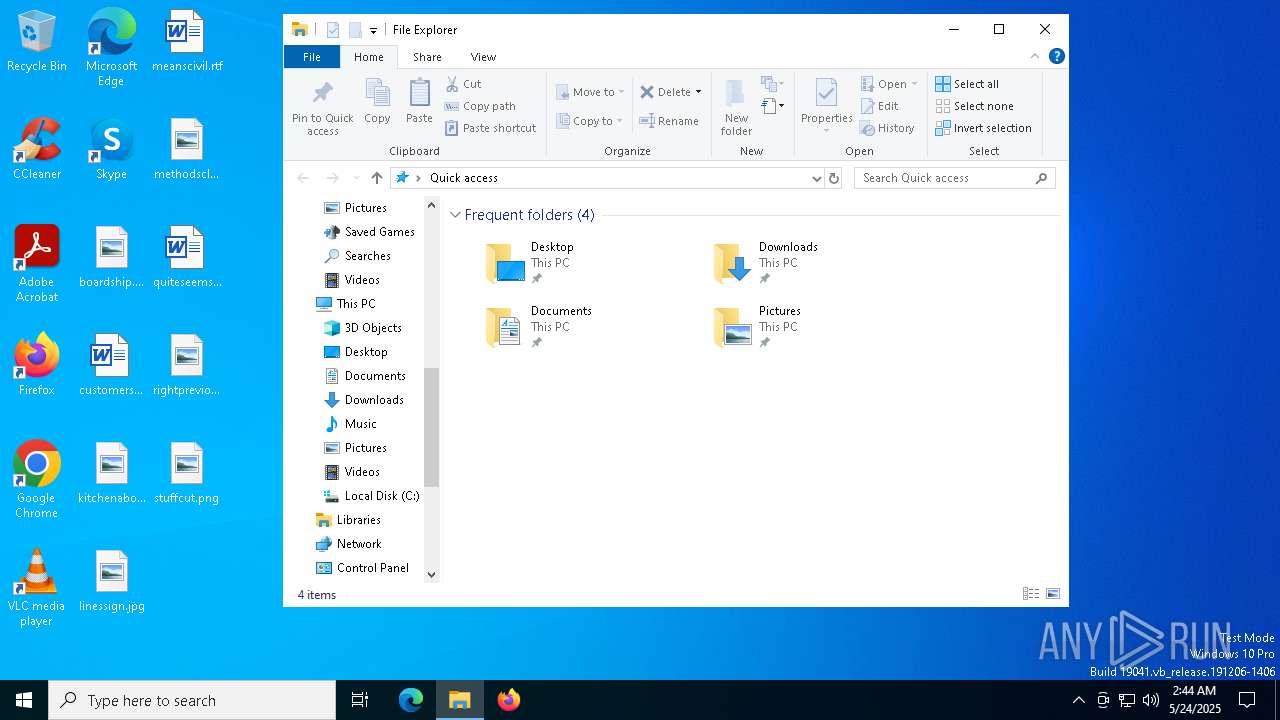
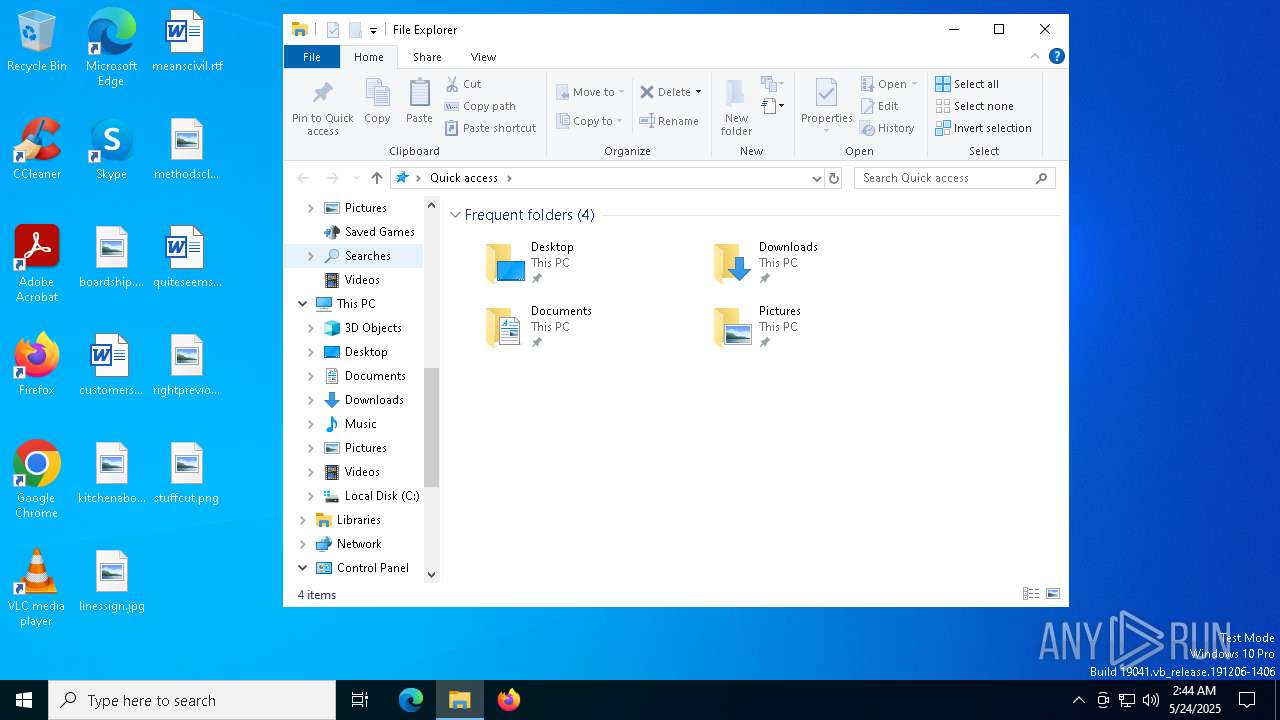
Manual execution by a user
- msedge.exe (PID: 2852)
Reads Environment values
- identity_helper.exe (PID: 8020)
- identity_helper.exe (PID: 7724)
Reads the software policy settings
- slui.exe (PID: 3784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:14 08:01:20+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 1520640 |
| InitializedDataSize: | 8670720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xfe91b8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
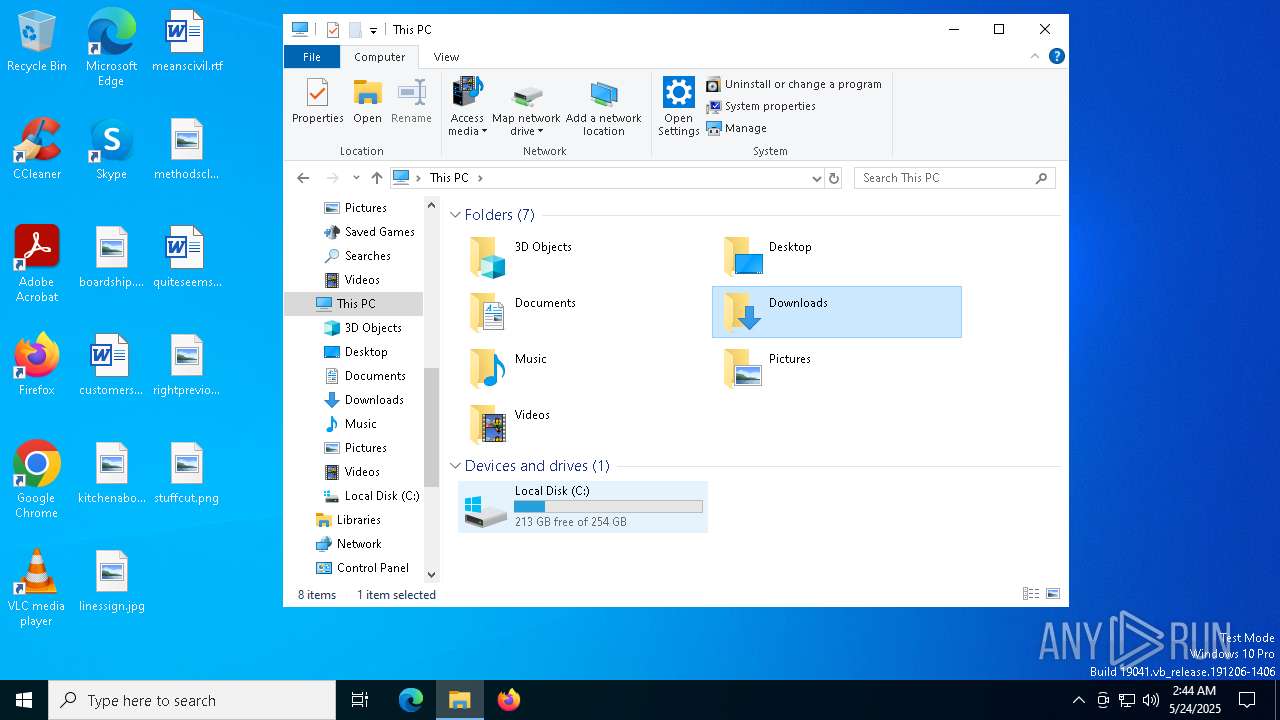
Total processes
196
Monitored processes
65
Malicious processes
0
Suspicious processes
1
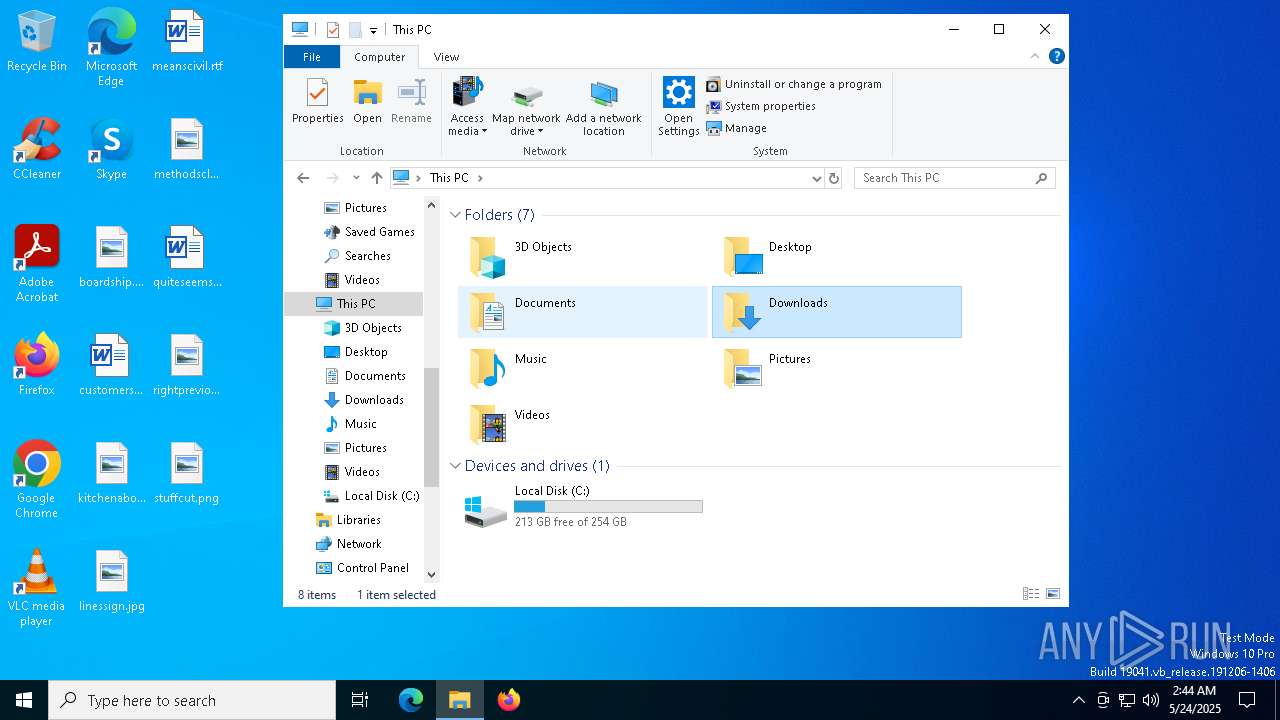
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | find /i /v "certutil" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\AppData\Local\Temp\WARRIOR_protected (1).exe" | C:\Users\admin\AppData\Local\Temp\WARRIOR_protected (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=5392 --field-trial-handle=2364,i,2452613637738084469,13154880454274553238,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | certutil -hashfile "C:\Users\admin\AppData\Local\Temp\WARRIOR_protected (1).exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2676 --field-trial-handle=2364,i,2452613637738084469,13154880454274553238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
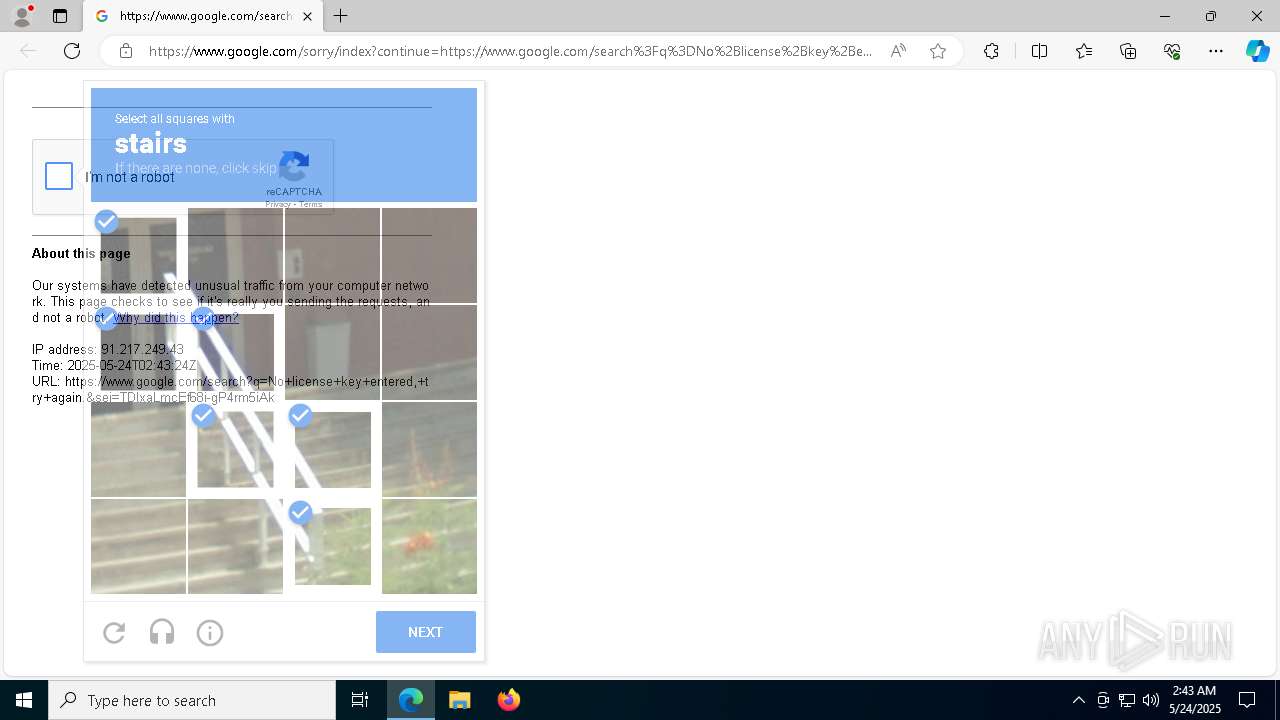
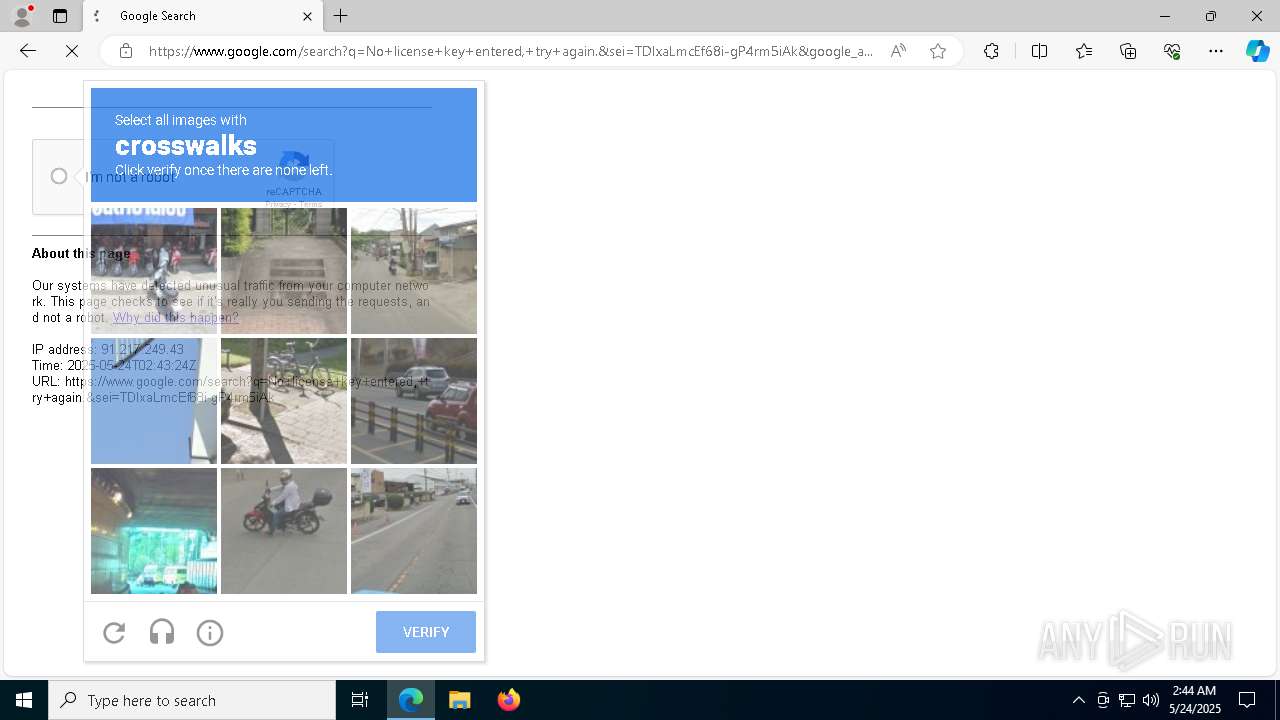
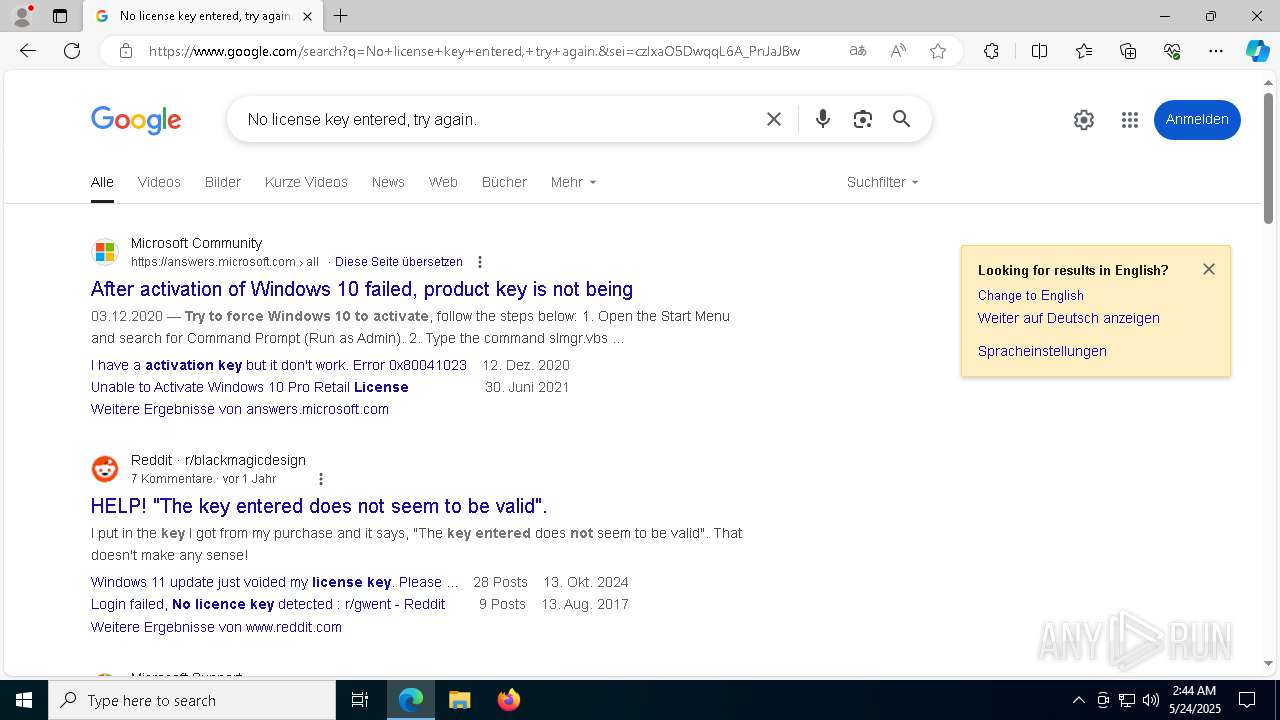
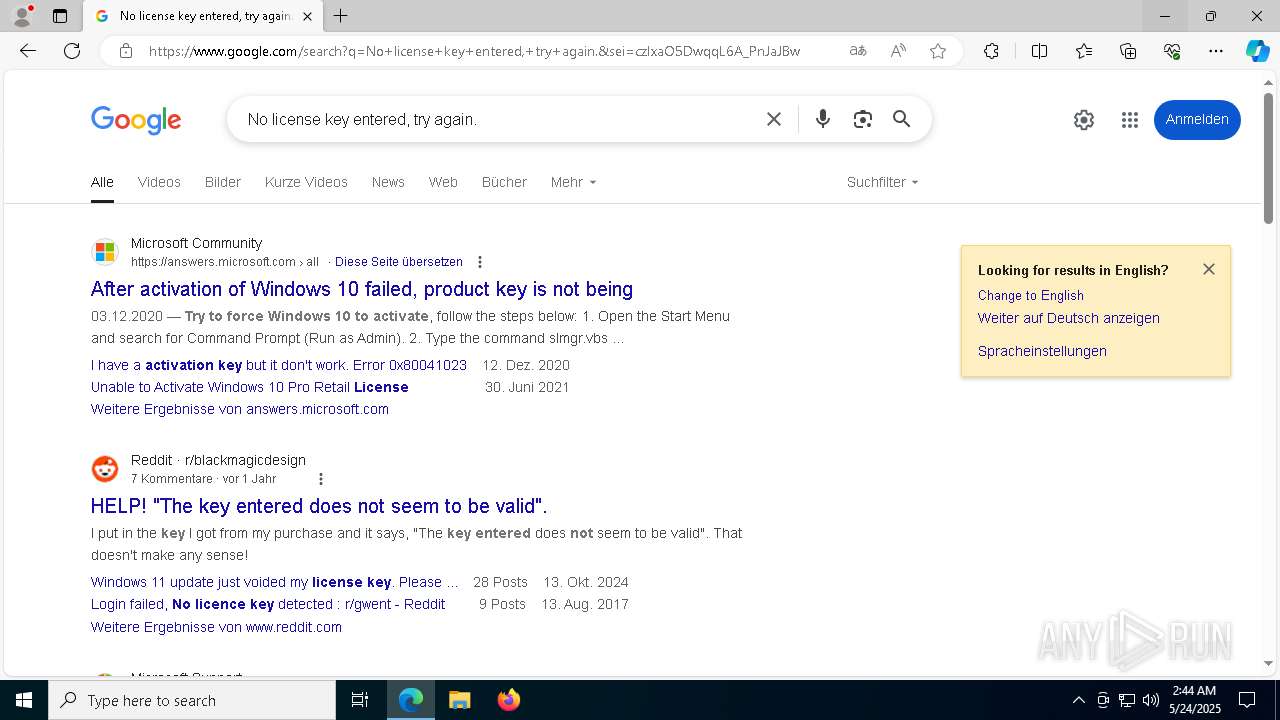
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.google.com/search?q=No+license+key+entered,+try+again. | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | WARRIOR_protected (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6448 --field-trial-handle=2364,i,2452613637738084469,13154880454274553238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Users\admin\AppData\Local\Temp\WARRIOR_protected (1).exe" | C:\Users\admin\AppData\Local\Temp\WARRIOR_protected (1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6180 --field-trial-handle=2364,i,2452613637738084469,13154880454274553238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2492 --field-trial-handle=2364,i,2452613637738084469,13154880454274553238,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
9 588
Read events
9 544
Write events
43
Delete events
1
Modification events
| (PID) Process: | (1056) WARRIOR_protected (1).exe | Key: | HKEY_CLASSES_ROOT\discord-1333388552339460116 |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (1184) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.1!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_CA_REVOCATION | |||
| (PID) Process: | (1184) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.2!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_END_REVOCATION | |||
| (PID) Process: | (1184) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.3!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_NO_OCSP_FAILOVER_TO_CRL | |||
| (PID) Process: | (1056) WARRIOR_protected (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\0165058 |
| Operation: | write | Name: | 0165058 |
Value: 0165058 | |||
| (PID) Process: | (1056) WARRIOR_protected (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (1056) WARRIOR_protected (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1056) WARRIOR_protected (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1056) WARRIOR_protected (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
11
Suspicious files
179
Text files
65
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c0a2.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c0a2.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:1E9E15EF6E531C4557100F20C9C76F01 | SHA256:46CB063CC268B69B172660F166C4394D5B4EDD802388B3EC16766DEBDB9F86C3 | |||
| 1196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:6971E42ED64D2BE125547F021EB852B1 | SHA256:B46CFDC4106DF566F71AA34D6F10B53767C561DFD17DD07A5930A18E67BB344B | |||
| 1196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\44f37c2f-c26d-43dd-a06e-ed6beca5b561.tmp | binary | |
MD5:6D728B5E2876AF64698D6604434D434B | SHA256:2D1515F5C1B0EAED058A8479B840C0194EE93DE8E95340DD3A9871EC2E434222 | |||
| 1056 | WARRIOR_protected (1).exe | C:\ProgramData\0165058 | text | |
MD5:7EC16EC5122F5E534A7DE0347D5A0571 | SHA256:F8998D35DB8CA7455DBB3842631AA08EA9F6B31B0D3CE04509A33D1A126F105F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
80
DNS requests
77
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
756 | lsass.exe | GET | 200 | 172.217.16.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 172.217.16.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6512 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748152711&P2=404&P3=2&P4=GM58SX9fHQQuEzbfKtu6yoZj2yGKrU7C2vV%2fa3K%2fwReyXRA%2bBwBWVFwM4wIzQ2HNT39D8I5FxUsjsLxC7kskeA%3d%3d | unknown | — | — | whitelisted |
6512 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748152711&P2=404&P3=2&P4=GM58SX9fHQQuEzbfKtu6yoZj2yGKrU7C2vV%2fa3K%2fwReyXRA%2bBwBWVFwM4wIzQ2HNT39D8I5FxUsjsLxC7kskeA%3d%3d | unknown | — | — | whitelisted |
6512 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748152711&P2=404&P3=2&P4=GM58SX9fHQQuEzbfKtu6yoZj2yGKrU7C2vV%2fa3K%2fwReyXRA%2bBwBWVFwM4wIzQ2HNT39D8I5FxUsjsLxC7kskeA%3d%3d | unknown | — | — | whitelisted |
6512 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748152711&P2=404&P3=2&P4=GM58SX9fHQQuEzbfKtu6yoZj2yGKrU7C2vV%2fa3K%2fwReyXRA%2bBwBWVFwM4wIzQ2HNT39D8I5FxUsjsLxC7kskeA%3d%3d | unknown | — | — | whitelisted |
6512 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748152710&P2=404&P3=2&P4=TIhKQpGFDIvZeRlam99n9d5sC9%2fJ00GCPJUS3SXrkAUbDwm0S8Qns%2bmsgLVxm%2bMRPixI27mJV%2fSznRy4bL9aDw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5796 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5344 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1056 | WARRIOR_protected (1).exe | 188.114.96.3:443 | gamebattle.in | CLOUDFLARENET | NL | malicious |
756 | lsass.exe | 172.217.16.131:80 | c.pki.goog | GOOGLE | US | whitelisted |
1056 | WARRIOR_protected (1).exe | 104.26.0.5:443 | keyauth.win | CLOUDFLARENET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
gamebattle.in |
| malicious |
c.pki.goog |
| whitelisted |
keyauth.win |
| malicious |
x1.c.lencr.org |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | WARRIOR_protected (1).exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
1056 | WARRIOR_protected (1).exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |