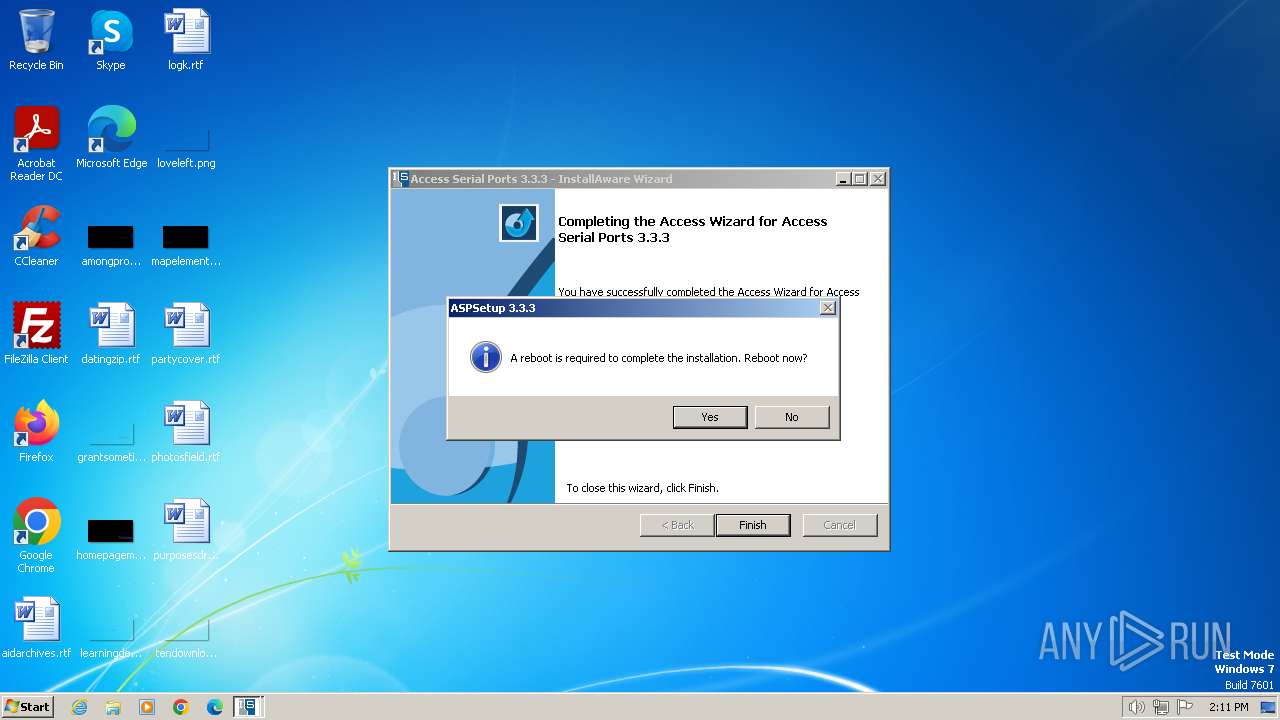
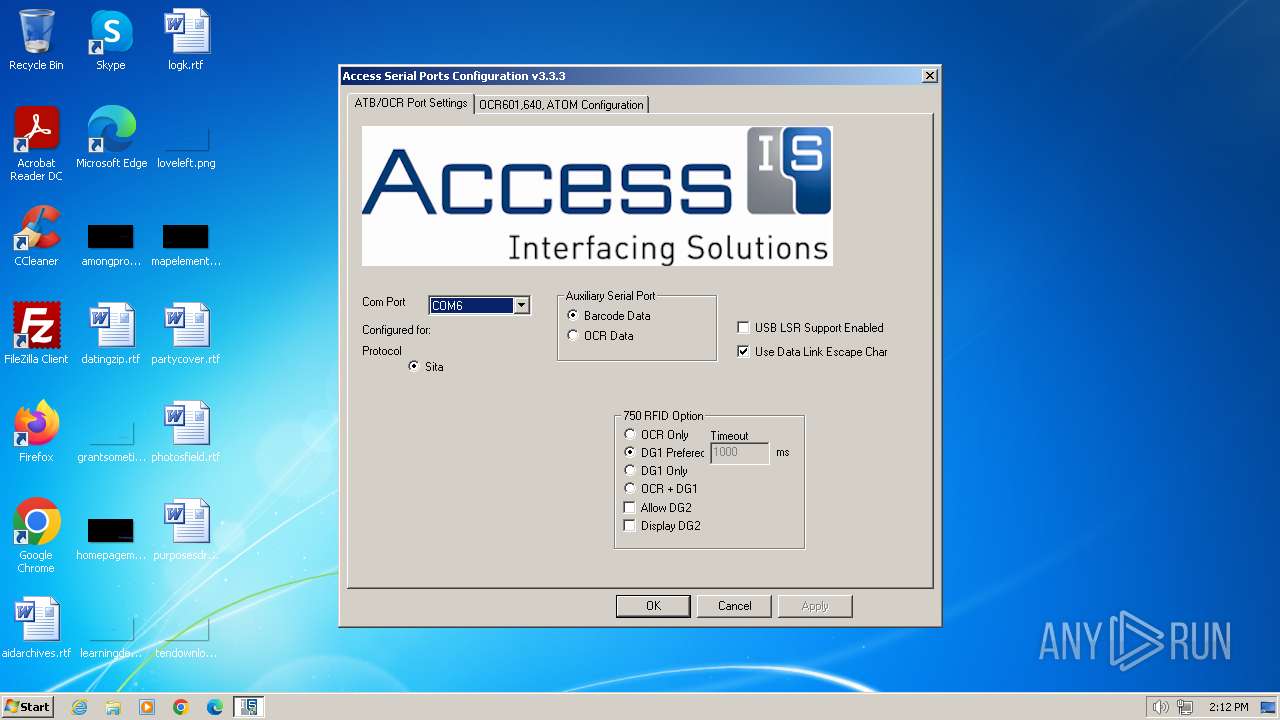
| File name: | aspsetup.3.3.3.exe |
| Full analysis: | https://app.any.run/tasks/9b743e87-0724-4e4a-a273-efb8d1503ad1 |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2024, 14:10:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 682670E7EF703A0C8A480D6F79C4CFB4 |
| SHA1: | 28ED13E35471113222997F7DA341EAE0D99CA92F |
| SHA256: | BF9784BF9187AFCF4BE95DD6EE5A2C461C6B8DA6F6C9AA8F0A690CA06E83710E |
| SSDEEP: | 196608:rR8hIawZC0frIkZRo/+KP1AVZCSmFwXxuvK6K:rR8GE0EoRXqAlmycvo |
MALICIOUS
Drops the executable file immediately after the start
- aspsetup.3.3.3.exe (PID: 1288)
- ASPSetup.exe (PID: 3248)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 2396)
- cmd.exe (PID: 752)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 2736)
- cmd.exe (PID: 1924)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 584)
- cmd.exe (PID: 3448)
- cmd.exe (PID: 1384)
- cmd.exe (PID: 3664)
- cmd.exe (PID: 4000)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 1976)
- cmd.exe (PID: 1572)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 568)
- cmd.exe (PID: 376)
- cmd.exe (PID: 1268)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 924)
- cmd.exe (PID: 668)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 3044)
- DeviceInstaller.exe (PID: 3012)
- drvinst.exe (PID: 3388)
Starts NET.EXE for service management
- ASPSetup.exe (PID: 3248)
- net.exe (PID: 1932)
Creates a writable file in the system directory
- cmd.exe (PID: 3968)
- cmd.exe (PID: 668)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 3044)
- drvinst.exe (PID: 3388)
SUSPICIOUS
Executable content was dropped or overwritten
- aspsetup.3.3.3.exe (PID: 1288)
- ASPSetup.exe (PID: 3248)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 752)
- cmd.exe (PID: 2396)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 2736)
- cmd.exe (PID: 584)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 1924)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 3448)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 3664)
- cmd.exe (PID: 1384)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 4000)
- cmd.exe (PID: 1976)
- cmd.exe (PID: 1572)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 568)
- cmd.exe (PID: 376)
- cmd.exe (PID: 1268)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 924)
- cmd.exe (PID: 3044)
- cmd.exe (PID: 668)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 3096)
- DeviceInstaller.exe (PID: 3012)
- drvinst.exe (PID: 3388)
Drops 7-zip archiver for unpacking
- aspsetup.3.3.3.exe (PID: 1288)
- ASPSetup.exe (PID: 3248)
Process drops legitimate windows executable
- ASPSetup.exe (PID: 3248)
Drops a system driver (possible attempt to evade defenses)
- ASPSetup.exe (PID: 3248)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 3044)
- DeviceInstaller.exe (PID: 3012)
- drvinst.exe (PID: 3388)
Reads the Windows owner or organization settings
- ASPSetup.exe (PID: 3248)
Reads the Internet Settings
- ASPSetup.exe (PID: 3248)
- sipnotify.exe (PID: 312)
Uses TASKKILL.EXE to kill process
- ASPSetup.exe (PID: 3248)
Executing commands from a ".bat" file
- ASPSetup.exe (PID: 3248)
Starts CMD.EXE for commands execution
- ASPSetup.exe (PID: 3248)
Creates files in the driver directory
- cmd.exe (PID: 3968)
- cmd.exe (PID: 3044)
- drvinst.exe (PID: 3388)
Starts a Microsoft application from unusual location
- dc.exe (PID: 2136)
- dc.exe (PID: 4040)
- dc.exe (PID: 1408)
- dc.exe (PID: 784)
- dc.exe (PID: 3988)
Searches for installed software
- ASPSetup.exe (PID: 3248)
Creates a software uninstall entry
- ASPSetup.exe (PID: 3248)
Adds/modifies Windows certificates
- DeviceInstaller.exe (PID: 3012)
Reads security settings of Internet Explorer
- DeviceInstaller.exe (PID: 3012)
Checks Windows Trust Settings
- DeviceInstaller.exe (PID: 3012)
- drvinst.exe (PID: 1348)
- drvinst.exe (PID: 3388)
Reads settings of System Certificates
- DeviceInstaller.exe (PID: 3012)
- sipnotify.exe (PID: 312)
The process executes via Task Scheduler
- sipnotify.exe (PID: 312)
- ctfmon.exe (PID: 360)
Executes as Windows Service
- comserv.exe (PID: 2764)
INFO
Checks supported languages
- aspsetup.3.3.3.exe (PID: 1288)
- ASPSetup.exe (PID: 3248)
- asps.exe (PID: 3624)
- asps.exe (PID: 3852)
- dc.exe (PID: 2136)
- asps.exe (PID: 3796)
- dc.exe (PID: 4040)
- asps.exe (PID: 3284)
- asps.exe (PID: 4052)
- asps.exe (PID: 3716)
- asps.exe (PID: 2036)
- asps.exe (PID: 3944)
- asps.exe (PID: 1836)
- asps.exe (PID: 4004)
- asps.exe (PID: 3948)
- asps.exe (PID: 1876)
- asps.exe (PID: 2340)
- asps.exe (PID: 3212)
- asps.exe (PID: 3684)
- asps.exe (PID: 1692)
- asps.exe (PID: 3092)
- asps.exe (PID: 2292)
- asps.exe (PID: 3724)
- asps.exe (PID: 1824)
- asps.exe (PID: 2792)
- asps.exe (PID: 2672)
- asps.exe (PID: 2152)
- asps.exe (PID: 3348)
- asps.exe (PID: 3916)
- asps.exe (PID: 1112)
- asps.exe (PID: 240)
- asps.exe (PID: 3400)
- asps.exe (PID: 1556)
- asps.exe (PID: 3072)
- asps.exe (PID: 1880)
- asps.exe (PID: 2248)
- asps.exe (PID: 3984)
- asps.exe (PID: 2780)
- asps.exe (PID: 2052)
- asps.exe (PID: 1992)
- asps.exe (PID: 3008)
- asps.exe (PID: 2472)
- asps.exe (PID: 3668)
- asps.exe (PID: 1656)
- asps.exe (PID: 3784)
- asps.exe (PID: 1696)
- asps.exe (PID: 2848)
- asps.exe (PID: 864)
- asps.exe (PID: 3964)
- asps.exe (PID: 2688)
- asps.exe (PID: 2908)
- asps.exe (PID: 1632)
- asps.exe (PID: 2980)
- asps.exe (PID: 2540)
- asps.exe (PID: 2132)
- asps.exe (PID: 2924)
- asps.exe (PID: 3180)
- dc.exe (PID: 1408)
- DeviceInstaller.exe (PID: 3012)
- drvinst.exe (PID: 3388)
- drvinst.exe (PID: 1348)
- dc.exe (PID: 784)
- comserv.exe (PID: 984)
- asps.exe (PID: 2172)
- asps.exe (PID: 896)
- asps.exe (PID: 3768)
- asps.exe (PID: 2660)
- comserv.exe (PID: 2764)
- KeyStrokeInjector.exe (PID: 3600)
- COMSERVMON.EXE (PID: 3672)
- asps.exe (PID: 3880)
- COMSERVMON.EXE (PID: 1520)
- IMEKLMG.EXE (PID: 2100)
- dc.exe (PID: 3988)
- IMEKLMG.EXE (PID: 2116)
- KeyStrokeInjector.exe (PID: 2124)
- wmpnscfg.exe (PID: 2388)
- wmpnscfg.exe (PID: 2408)
- asps.exe (PID: 2652)
- COMSERVMON.EXE (PID: 2736)
Reads the computer name
- ASPSetup.exe (PID: 3248)
- asps.exe (PID: 3624)
- asps.exe (PID: 3852)
- dc.exe (PID: 2136)
- dc.exe (PID: 4040)
- dc.exe (PID: 1408)
- DeviceInstaller.exe (PID: 3012)
- drvinst.exe (PID: 3388)
- drvinst.exe (PID: 1348)
- dc.exe (PID: 784)
- comserv.exe (PID: 984)
- asps.exe (PID: 896)
- asps.exe (PID: 2660)
- comserv.exe (PID: 2764)
- COMSERVMON.EXE (PID: 1520)
- dc.exe (PID: 3988)
- COMSERVMON.EXE (PID: 3672)
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2116)
- wmpnscfg.exe (PID: 2388)
- wmpnscfg.exe (PID: 2408)
- asps.exe (PID: 2652)
- COMSERVMON.EXE (PID: 2736)
Create files in a temporary directory
- aspsetup.3.3.3.exe (PID: 1288)
- ASPSetup.exe (PID: 3248)
- DeviceInstaller.exe (PID: 3012)
Reads the machine GUID from the registry
- ASPSetup.exe (PID: 3248)
- DeviceInstaller.exe (PID: 3012)
- drvinst.exe (PID: 3388)
- drvinst.exe (PID: 1348)
Creates files in the program directory
- ASPSetup.exe (PID: 3248)
- cmd.exe (PID: 3604)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 312)
Manual execution by a user
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2116)
- wmpnscfg.exe (PID: 2408)
- wmpnscfg.exe (PID: 2388)
- asps.exe (PID: 2652)
- asps.exe (PID: 2532)
- KeyStrokeInjector.exe (PID: 2124)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:04:15 22:43:49+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 98816 |
| InitializedDataSize: | 125952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12a70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.3.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
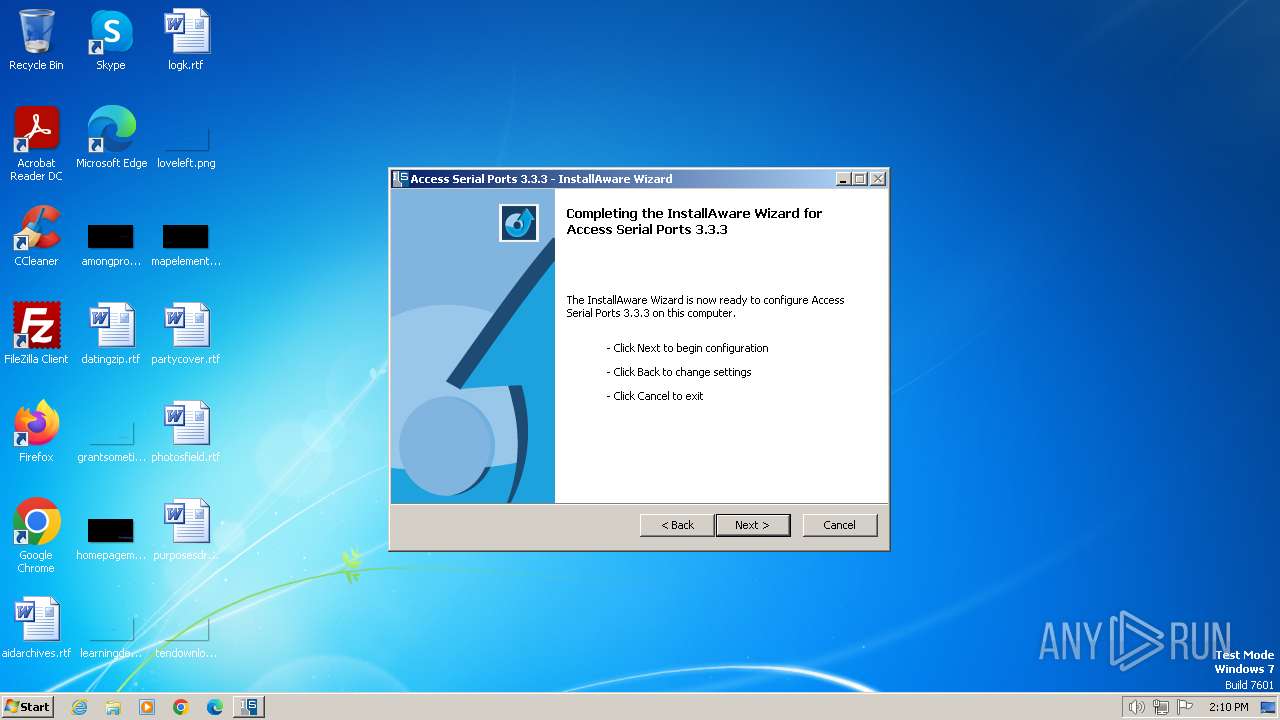
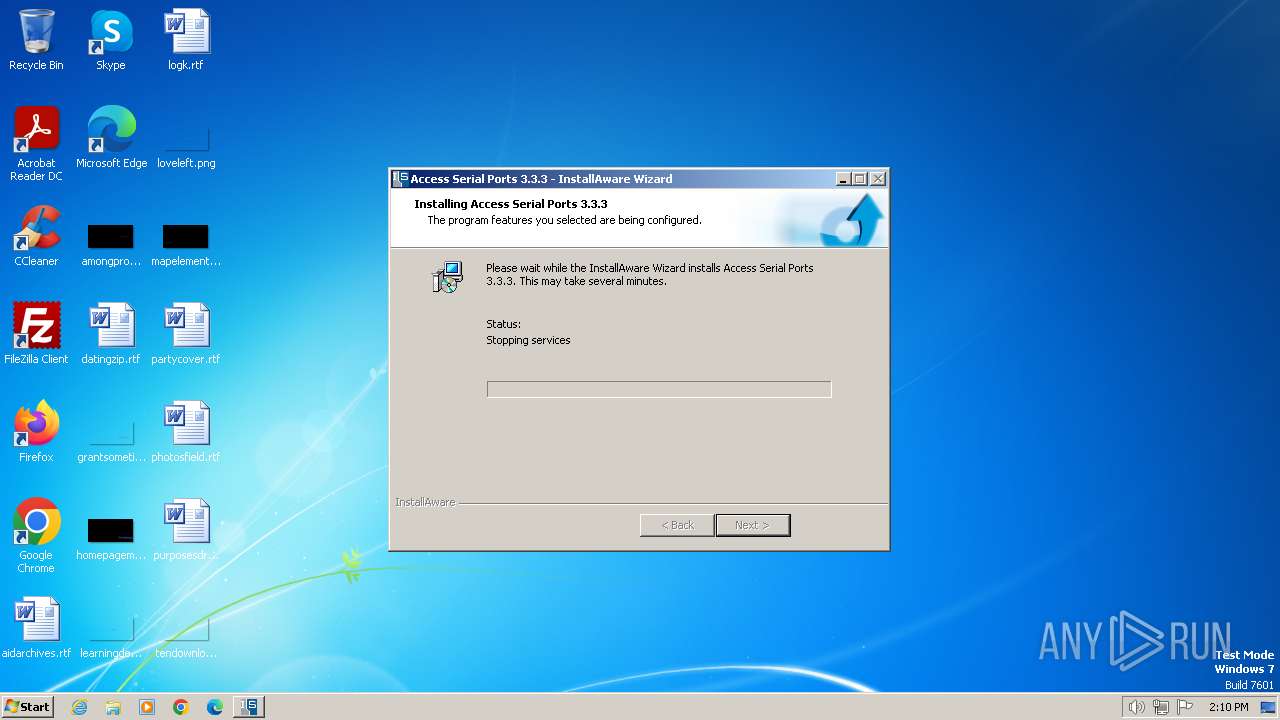
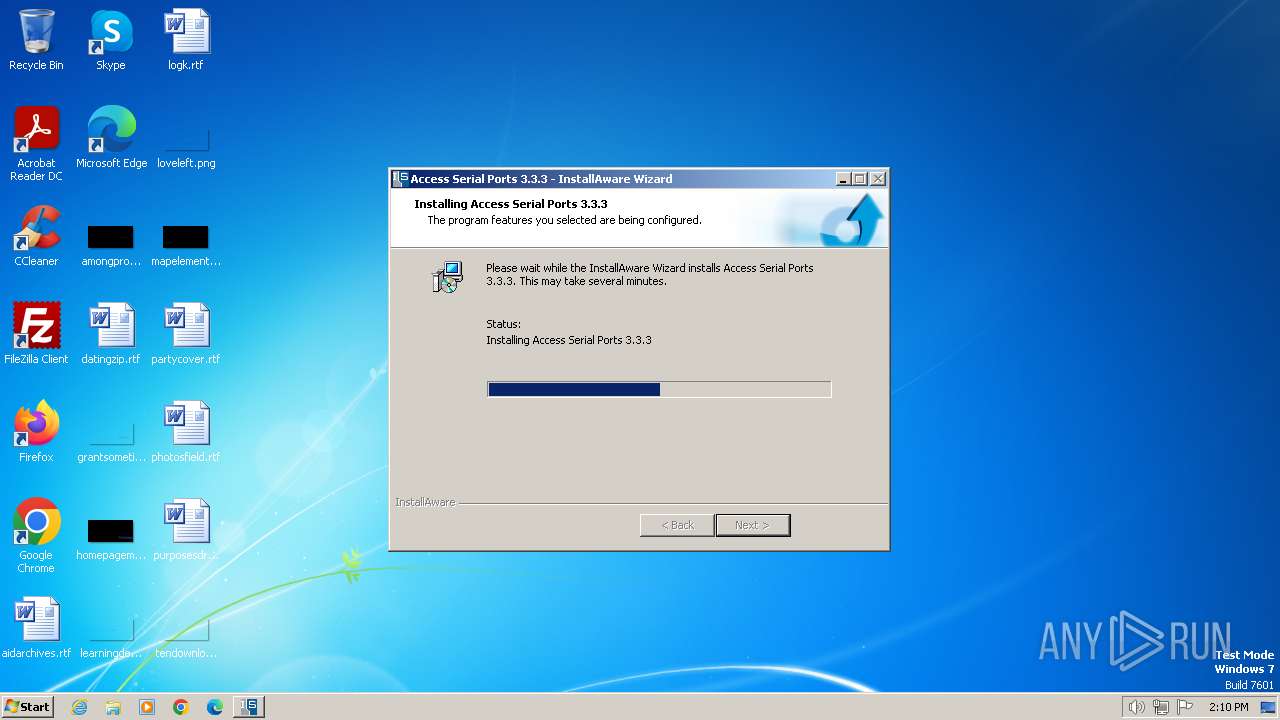
| Comments: | This installation was built with InstallAware: http://www.installaware.com |
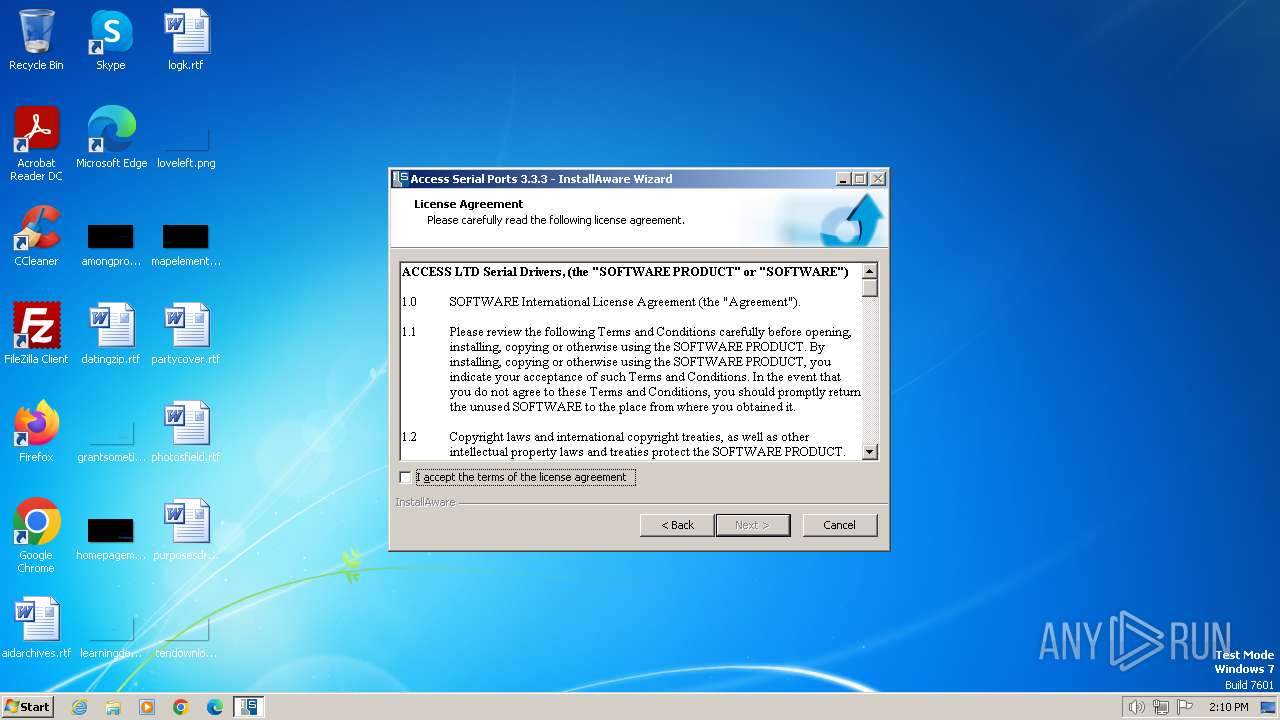
| CompanyName: | Access IS |
| FileDescription: | Access Serial Ports Installation |
| FileVersion: | 3.3.3 |
| LegalCopyright: | All rights reserved |
Total processes
339
Monitored processes
164
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileDeleteOnly.bat" "C:\Windows\KeyStrokeInjector.exe"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 240 | "C:\Users\admin\AppData\Local\Temp\mia1\asps.exe" writecomservregkey="\Settings" writecomservregname="AuxPort" writecomservregdword=0 | C:\Users\admin\AppData\Local\Temp\mia1\asps.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Access IS Integrity Level: HIGH Description: Access Serial Ports Configuration Exit code: 0 Version: 3.7.0.4 Modules
| |||||||||||||||
| 292 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileDeleteOnly.bat" "C:\Windows\ASPS.EXE"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 312 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 360 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileCopyOnly.bat" "C:\Users\admin\AppData\Local\Temp\mia1\VideoOCR.DLL" "C:\Windows\"" | C:\Windows\System32\cmd.exe | ASPSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 492 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileDeleteOnly.bat" "C:\Windows\ePassportAPI.dll"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 560 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileCopyOnly.bat" "C:\Users\admin\AppData\Local\Temp\mia1\ASPS.LNKD" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Access IS\Access Serial Port Configuration.lnk"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 568 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileCopyOnly.bat" "C:\Users\admin\AppData\Local\Temp\mia1\aspate.exe" "C:\Windows\"" | C:\Windows\System32\cmd.exe | ASPSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 584 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileCopyOnly.bat" "C:\Users\admin\AppData\Local\Temp\mia1\AccessISrfid.DLL" "C:\Windows\"" | C:\Windows\System32\cmd.exe | ASPSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
21 656
Read events
21 506
Write events
149
Delete events
1
Modification events
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
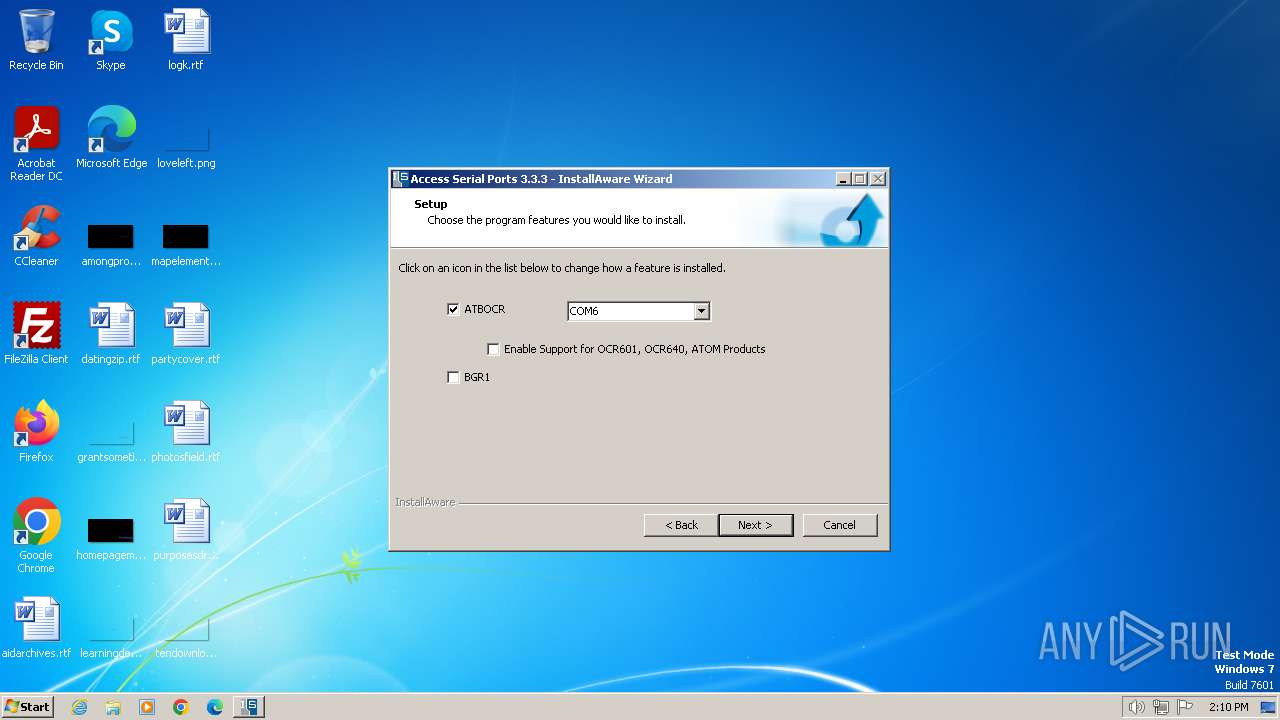
| (PID) Process: | (3852) asps.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\COM Name Arbiter |
| Operation: | write | Name: | ComDB |
Value: 0100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2688) asps.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\ComServ\Parameters\Settings |
| Operation: | write | Name: | ATBOCR |
Value: 0 | |||
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 115 | |||
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{67A7A899-5883-4359-B3EE-914C11302583} |
| Operation: | write | Name: | UninstallString |
Value: C:\ProgramData\{F2A2DBB5-2095-4AF5-8FD7-590B57048659}\ASPSetup.exe | |||
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Access Serial Ports 3.3.3 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\ProgramData\{F2A2DBB5-2095-4AF5-8FD7-590B57048659}\ASPSetup.exe | |||
| (PID) Process: | (3248) ASPSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Access Serial Ports 3.3.3 |
| Operation: | write | Name: | DisplayName |
Value: Access Serial Ports 3.3.3 | |||
Executable files
94
Suspicious files
48
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1288 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia4451.tmp\ASPSetup.res | — | |
MD5:— | SHA256:— | |||
| 1288 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia4451.tmp\data\OFFLINE\C_\development\asp_usb_driver\solution\comserv\release\comserv.exe | executable | |
MD5:3C21A4F2530311C6AD50DB1B4DD8E4C0 | SHA256:41B931C522195F94D3B2EE96714D921D47A966D3FC245737C48A09AF22007427 | |||
| 1288 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia4451.tmp\ASPSetup.exe | executable | |
MD5:7AE823C9B2B21A090635415BA863CB29 | SHA256:08F51C54256D06FC0193CE8F9FC9A13503D7D6EAE9C4B0AD1326C865C9CF4730 | |||
| 1288 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia4451.tmp\data\mIDEFunc.dll\mEXEFunc.dll | executable | |
MD5:37DC742EBBEA35E08C8D0A4368AD8779 | SHA256:199DC5A1036266838DBFD2E8590ED4DB4E6189B9BD7243E3A0CFC324CF4AD769 | |||
| 3248 | ASPSetup.exe | C:\Users\admin\AppData\Local\Temp\mia.tmp | text | |
MD5:6E9BECC6B748F5069E1F4F4276B3EAB8 | SHA256:124395CFBEB2AB33BD1693934109CB67D5C8B4A9B88F1198C83E472294D6081C | |||
| 1288 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia4451.tmp\data\ASPSetup.msi | executable | |
MD5:3CC23774907EFC7BED96A8F1D0B13C3D | SHA256:FF34CD521B5F76CC322252AC19F4A07E601FB705539281ABBE819D6175F09714 | |||
| 1288 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia4451.tmp\ASPSetup.msi | executable | |
MD5:3CC23774907EFC7BED96A8F1D0B13C3D | SHA256:FF34CD521B5F76CC322252AC19F4A07E601FB705539281ABBE819D6175F09714 | |||
| 1288 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia4451.tmp\data\OFFLINE\C_\development\asp_usb_driver\solution\comserv\release64\comserv64.exe | executable | |
MD5:6F08D93EADF52703853D2A18A1D6F853 | SHA256:4BE56008B2C7EB86C8B6878A527A19AD5D9C7560BFE8EDA744E9C8E04496BD14 | |||
| 3248 | ASPSetup.exe | C:\Users\admin\AppData\Local\Temp\mia1\componentform.dfm | binary | |
MD5:E7E166B769DA1160F6DECC0AA2BAE084 | SHA256:5644E7B0137B05CB8274636EE377044A8C9C409B96F7642CE59DADA89F915211 | |||
| 3248 | ASPSetup.exe | C:\Users\admin\AppData\Local\Temp\mia1\componentform.dfm.miaf | text | |
MD5:C7792C25B8C9DA2DEE485D549A129AAD | SHA256:3D484E506CA3B8E70D48036A35512A00C85BD50D28F38F6ADA4C8C079FA2656D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133517023104370000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
312 | sipnotify.exe | 23.197.138.118:80 | query.prod.cms.rt.microsoft.com | Akamai International B.V. | US | unknown |
1116 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |