| File name: | aspsetup.3.3.3.exe |
| Full analysis: | https://app.any.run/tasks/707d1c75-b8a6-4de2-9d2e-e79de734361c |
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2023, 10:29:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 682670E7EF703A0C8A480D6F79C4CFB4 |
| SHA1: | 28ED13E35471113222997F7DA341EAE0D99CA92F |
| SHA256: | BF9784BF9187AFCF4BE95DD6EE5A2C461C6B8DA6F6C9AA8F0A690CA06E83710E |
| SSDEEP: | 196608:rR8hIawZC0frIkZRo/+KP1AVZCSmFwXxuvK6K:rR8GE0EoRXqAlmycvo |
MALICIOUS
Drops the executable file immediately after the start
- aspsetup.3.3.3.exe (PID: 3504)
- ASPSetup.exe (PID: 3608)
- cmd.exe (PID: 3536)
- cmd.exe (PID: 3244)
- msiexec.exe (PID: 3956)
- cmd.exe (PID: 3252)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 2872)
- cmd.exe (PID: 3468)
- cmd.exe (PID: 3556)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3872)
- cmd.exe (PID: 3788)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 124)
- cmd.exe (PID: 2744)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 2932)
- cmd.exe (PID: 2748)
- cmd.exe (PID: 2964)
- cmd.exe (PID: 1432)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 1248)
- cmd.exe (PID: 2608)
- cmd.exe (PID: 3432)
- DeviceInstaller.exe (PID: 924)
- drvinst.exe (PID: 3064)
Creates a writable file the system directory
- cmd.exe (PID: 3536)
- cmd.exe (PID: 1248)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 2608)
- cmd.exe (PID: 3432)
- msiexec.exe (PID: 3956)
- drvinst.exe (PID: 3064)
Starts NET.EXE for service management
- ASPSetup.exe (PID: 3608)
- net.exe (PID: 3852)
Changes the autorun value in the registry
- msiexec.exe (PID: 3956)
SUSPICIOUS
Process drops legitimate windows executable
- ASPSetup.exe (PID: 3608)
Drops 7-zip archiver for unpacking
- aspsetup.3.3.3.exe (PID: 3504)
- ASPSetup.exe (PID: 3608)
Drops a system driver (possible attempt to evade defenses)
- ASPSetup.exe (PID: 3608)
- cmd.exe (PID: 3536)
- cmd.exe (PID: 3432)
- DeviceInstaller.exe (PID: 924)
- drvinst.exe (PID: 3064)
Reads the Windows owner or organization settings
- ASPSetup.exe (PID: 3608)
- msiexec.exe (PID: 3956)
Reads the Internet Settings
- ASPSetup.exe (PID: 3608)
Uses TASKKILL.EXE to kill process
- ASPSetup.exe (PID: 3608)
Executing commands from a ".bat" file
- ASPSetup.exe (PID: 3608)
Starts CMD.EXE for commands execution
- ASPSetup.exe (PID: 3608)
Creates files in the driver directory
- cmd.exe (PID: 3536)
- cmd.exe (PID: 3432)
- drvinst.exe (PID: 3064)
Searches for installed software
- ASPSetup.exe (PID: 3608)
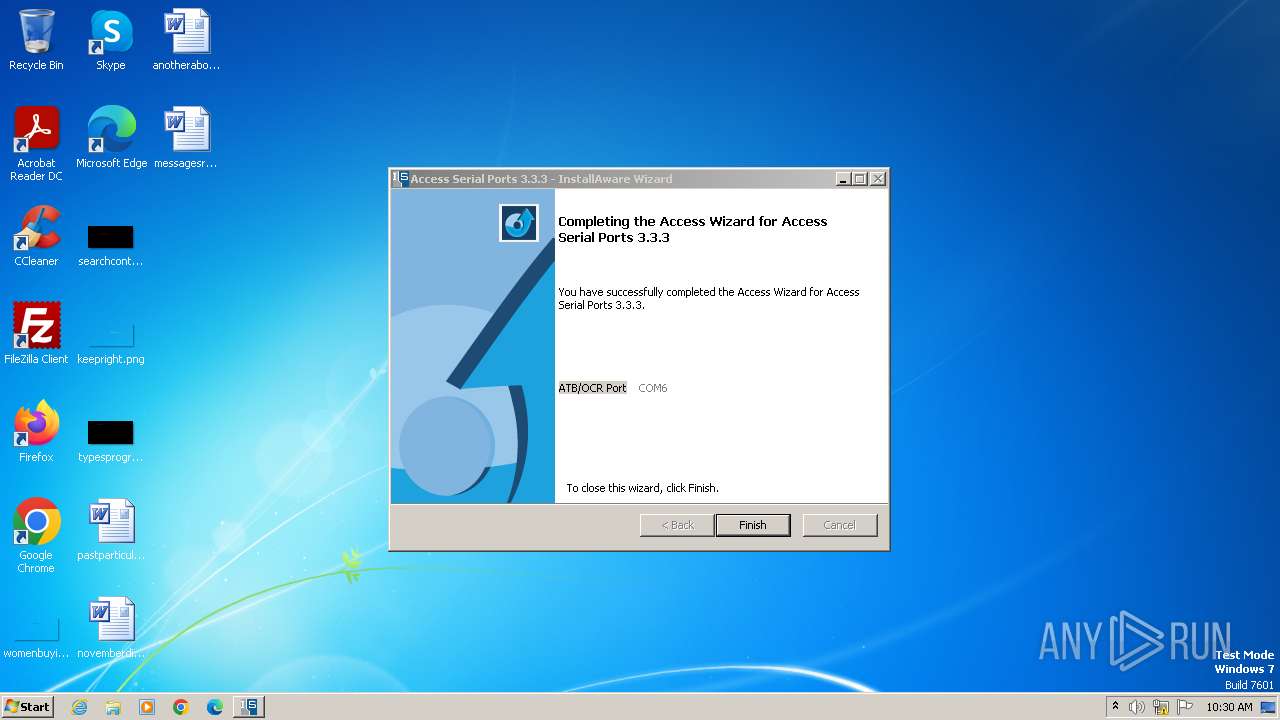
Creates a software uninstall entry
- ASPSetup.exe (PID: 3608)
Adds/modifies Windows certificates
- ASPSetup.exe (PID: 3608)
Reads security settings of Internet Explorer
- DeviceInstaller.exe (PID: 924)
Checks Windows Trust Settings
- DeviceInstaller.exe (PID: 924)
- drvinst.exe (PID: 1364)
- drvinst.exe (PID: 3064)
Reads settings of System Certificates
- DeviceInstaller.exe (PID: 924)
Executes as Windows Service
- VSSVC.exe (PID: 2404)
- comserv.exe (PID: 2996)
INFO
Checks supported languages
- aspsetup.3.3.3.exe (PID: 3504)
- ASPSetup.exe (PID: 3608)
- msiexec.exe (PID: 3956)
- asps.exe (PID: 3724)
- asps.exe (PID: 3972)
- dc.exe (PID: 4032)
- asps.exe (PID: 788)
- asps.exe (PID: 3808)
- asps.exe (PID: 1760)
- asps.exe (PID: 1808)
- asps.exe (PID: 2056)
- asps.exe (PID: 1600)
- asps.exe (PID: 148)
- asps.exe (PID: 1860)
- asps.exe (PID: 1356)
- asps.exe (PID: 2164)
- asps.exe (PID: 2092)
- dc.exe (PID: 4028)
- asps.exe (PID: 3780)
- asps.exe (PID: 328)
- asps.exe (PID: 2300)
- asps.exe (PID: 2320)
- asps.exe (PID: 188)
- asps.exe (PID: 2136)
- asps.exe (PID: 2740)
- asps.exe (PID: 2108)
- asps.exe (PID: 2560)
- asps.exe (PID: 2780)
- asps.exe (PID: 3796)
- asps.exe (PID: 1008)
- asps.exe (PID: 1228)
- asps.exe (PID: 732)
- asps.exe (PID: 2176)
- asps.exe (PID: 2760)
- asps.exe (PID: 2112)
- asps.exe (PID: 712)
- asps.exe (PID: 1812)
- asps.exe (PID: 2336)
- asps.exe (PID: 2820)
- asps.exe (PID: 2880)
- msiexec.exe (PID: 2448)
- asps.exe (PID: 2708)
- asps.exe (PID: 3736)
- asps.exe (PID: 3860)
- asps.exe (PID: 3924)
- asps.exe (PID: 4040)
- asps.exe (PID: 3164)
- asps.exe (PID: 3652)
- asps.exe (PID: 3888)
- asps.exe (PID: 756)
- asps.exe (PID: 3820)
- asps.exe (PID: 1360)
- asps.exe (PID: 916)
- asps.exe (PID: 1816)
- asps.exe (PID: 1348)
- msiexec.exe (PID: 1640)
- msiexec.exe (PID: 2408)
- asps.exe (PID: 4064)
- asps.exe (PID: 4088)
- asps.exe (PID: 3696)
- asps.exe (PID: 3084)
- dc.exe (PID: 2512)
- DeviceInstaller.exe (PID: 924)
- drvinst.exe (PID: 3064)
- drvinst.exe (PID: 1364)
- dc.exe (PID: 988)
- comserv.exe (PID: 2856)
- asps.exe (PID: 2412)
- asps.exe (PID: 3144)
- dc.exe (PID: 2436)
- asps.exe (PID: 3256)
- comserv.exe (PID: 2996)
- COMSERVMON.EXE (PID: 3760)
- KeyStrokeInjector.exe (PID: 1404)
- VideoOCRInterface.exe (PID: 3452)
- asps.exe (PID: 2620)
Reads the computer name
- ASPSetup.exe (PID: 3608)
- asps.exe (PID: 3972)
- msiexec.exe (PID: 3956)
- asps.exe (PID: 3724)
- dc.exe (PID: 4028)
- dc.exe (PID: 4032)
- msiexec.exe (PID: 2448)
- msiexec.exe (PID: 2408)
- msiexec.exe (PID: 1640)
- DeviceInstaller.exe (PID: 924)
- drvinst.exe (PID: 3064)
- dc.exe (PID: 2512)
- drvinst.exe (PID: 1364)
- dc.exe (PID: 988)
- asps.exe (PID: 3144)
- comserv.exe (PID: 2856)
- dc.exe (PID: 2436)
- asps.exe (PID: 3256)
- VideoOCRInterface.exe (PID: 3452)
- COMSERVMON.EXE (PID: 3760)
- comserv.exe (PID: 2996)
Create files in a temporary directory
- aspsetup.3.3.3.exe (PID: 3504)
- ASPSetup.exe (PID: 3608)
- msiexec.exe (PID: 3956)
- DeviceInstaller.exe (PID: 924)
Reads the machine GUID from the registry
- ASPSetup.exe (PID: 3608)
- msiexec.exe (PID: 3956)
- msiexec.exe (PID: 2448)
- msiexec.exe (PID: 2408)
- DeviceInstaller.exe (PID: 924)
- drvinst.exe (PID: 1364)
- drvinst.exe (PID: 3064)
- msiexec.exe (PID: 1640)
Application launched itself
- msiexec.exe (PID: 3956)
Creates files in the program directory
- ASPSetup.exe (PID: 3608)
- cmd.exe (PID: 3576)
Creates a software uninstall entry
- msiexec.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:04:15 22:43:49+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 98816 |
| InitializedDataSize: | 125952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12a70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.3.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
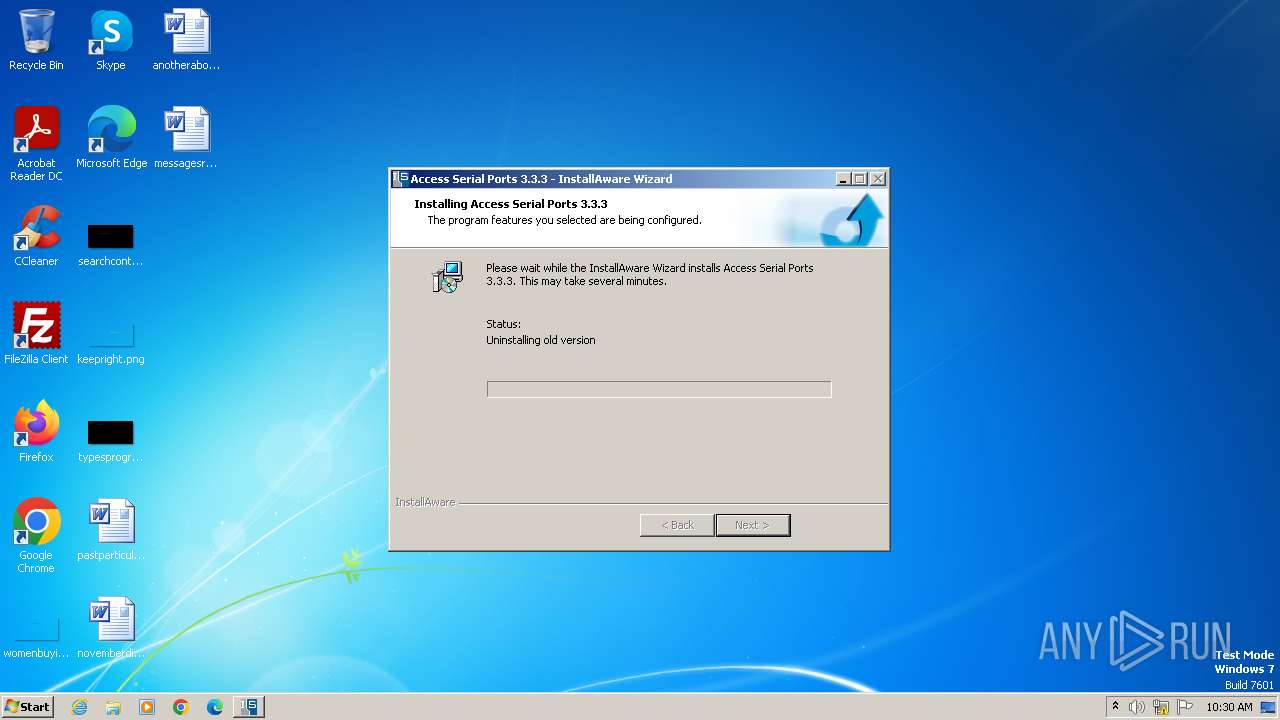
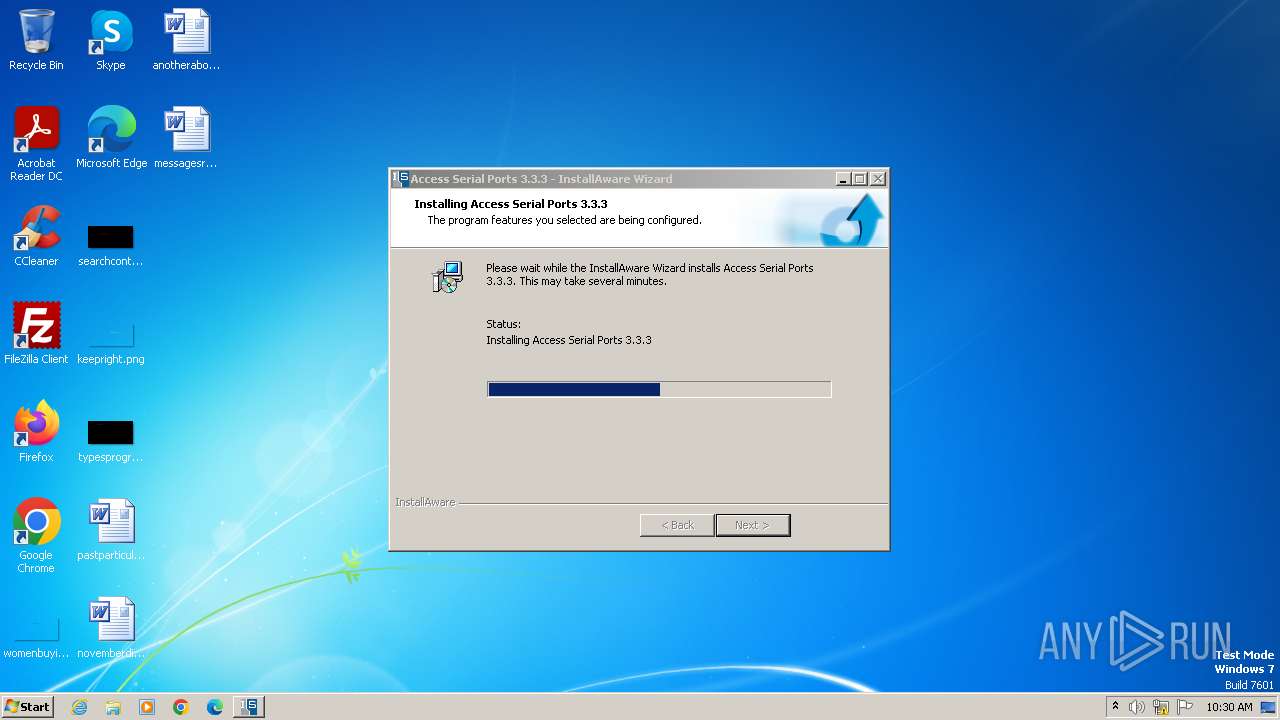
| Comments: | This installation was built with InstallAware: http://www.installaware.com |
| CompanyName: | Access IS |
| FileDescription: | Access Serial Ports Installation |
| FileVersion: | 3.3.3 |
| LegalCopyright: | All rights reserved |
Total processes
282
Monitored processes
158
Malicious processes
7
Suspicious processes
29
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileCopyOnly.bat" "C:\Users\admin\AppData\Local\Temp\mia1\pthreadVC2_vs2015.dll" "C:\Windows\"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 148 | "C:\Users\admin\AppData\Local\Temp\mia1\asps.exe" writecomservregkey="\Settings\4" writecomservregname="Parsing" writecomservregdword=0 | C:\Users\admin\AppData\Local\Temp\mia1\asps.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Access IS Integrity Level: HIGH Description: Access Serial Ports Configuration Exit code: 0 Version: 3.7.0.4 Modules
| |||||||||||||||
| 188 | "C:\Users\admin\AppData\Local\Temp\mia1\asps.exe" writecomservregkey="\Settings\2" writecomservregname="OutputType" writecomservregdword=0 | C:\Users\admin\AppData\Local\Temp\mia1\asps.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Access IS Integrity Level: HIGH Description: Access Serial Ports Configuration Exit code: 0 Version: 3.7.0.4 Modules
| |||||||||||||||
| 280 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileDeleteOnly.bat" "C:\Windows\cximage.dll"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 316 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileDeleteOnly.bat" "C:\Windows\SYSTEM32\COMSERV.EXE"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 328 | "C:\Users\admin\AppData\Local\Temp\mia1\asps.exe" writecomservregkey="\Settings\1" writecomservregname="" writecomservregstring="MSR ATB Coupon" | C:\Users\admin\AppData\Local\Temp\mia1\asps.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Access IS Integrity Level: HIGH Description: Access Serial Ports Configuration Exit code: 0 Version: 3.7.0.4 Modules
| |||||||||||||||
| 448 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileRenameOnly.bat" "C:\Windows\VideoOCRInterface.exe" "VideoOCRInterface.exe.old"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 556 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileDeleteOnly.bat" "C:\Windows\SYSTEM32\AUSBBGR.DLL"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 604 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\mia1\FileDeleteOnly.bat" "C:\Windows\cximage6.dll"" | C:\Windows\System32\cmd.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 712 | "C:\Users\admin\AppData\Local\Temp\mia1\asps.exe" writecomservregkey="\Settings\4" writecomservregname="OutputType" writecomservregdword=0 | C:\Users\admin\AppData\Local\Temp\mia1\asps.exe | — | ASPSetup.exe | |||||||||||
User: admin Company: Access IS Integrity Level: HIGH Description: Access Serial Ports Configuration Exit code: 0 Version: 3.7.0.4 Modules
| |||||||||||||||
Total events
23 464
Read events
23 225
Write events
208
Delete events
31
Modification events
| (PID) Process: | (3608) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3608) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3608) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3608) ASPSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3972) asps.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\COM Name Arbiter |
| Operation: | write | Name: | ComDB |
Value: 0100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\StringCacheSettings |
| Operation: | write | Name: | StringCacheGeneration |
Value: 378 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\17A |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\16c25e.rbs |
Value: 31067712 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
117
Suspicious files
69
Text files
28
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia7748.tmp\ASPSetup.res | — | |
MD5:— | SHA256:— | |||
| 3504 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia7748.tmp\data\ASPSetup.msi | executable | |
MD5:3CC23774907EFC7BED96A8F1D0B13C3D | SHA256:FF34CD521B5F76CC322252AC19F4A07E601FB705539281ABBE819D6175F09714 | |||
| 3504 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia7748.tmp\data\OFFLINE\C_\development\asp_usb_driver\solution\comserv\release\comserv.exe | executable | |
MD5:3C21A4F2530311C6AD50DB1B4DD8E4C0 | SHA256:41B931C522195F94D3B2EE96714D921D47A966D3FC245737C48A09AF22007427 | |||
| 3504 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia7748.tmp\data\mIDEFunc.dll\mEXEFunc.dll | executable | |
MD5:37DC742EBBEA35E08C8D0A4368AD8779 | SHA256:199DC5A1036266838DBFD2E8590ED4DB4E6189B9BD7243E3A0CFC324CF4AD769 | |||
| 3608 | ASPSetup.exe | C:\Users\admin\AppData\Local\Temp\mia1\componentform.dfm | binary | |
MD5:E7E166B769DA1160F6DECC0AA2BAE084 | SHA256:5644E7B0137B05CB8274636EE377044A8C9C409B96F7642CE59DADA89F915211 | |||
| 3504 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia7748.tmp\data\OFFLINE\mIDEFunc.dll\mEXEFunc.dll | executable | |
MD5:37DC742EBBEA35E08C8D0A4368AD8779 | SHA256:199DC5A1036266838DBFD2E8590ED4DB4E6189B9BD7243E3A0CFC324CF4AD769 | |||
| 3504 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia7748.tmp\ASPSetup.msi | executable | |
MD5:3CC23774907EFC7BED96A8F1D0B13C3D | SHA256:FF34CD521B5F76CC322252AC19F4A07E601FB705539281ABBE819D6175F09714 | |||
| 3608 | ASPSetup.exe | C:\Users\admin\AppData\Local\Temp\mia1\destination.dfm | binary | |
MD5:BF3263127CD771470559490ADB76647B | SHA256:4811574E264AEB0927806A9A953CEA2A903ED18C36A34A10B67E40B99CA1670F | |||
| 3504 | aspsetup.3.3.3.exe | C:\Users\admin\AppData\Local\Temp\mia7748.tmp\data\OFFLINE\C_\development\asp_usb_driver\solution\comserv\release64\comserv64.exe | executable | |
MD5:6F08D93EADF52703853D2A18A1D6F853 | SHA256:4BE56008B2C7EB86C8B6878A527A19AD5D9C7560BFE8EDA744E9C8E04496BD14 | |||
| 3608 | ASPSetup.exe | C:\Users\admin\AppData\Local\Temp\lang.loc | text | |
MD5:B2443D27BC6393A08F7F1ECFCC70A6FE | SHA256:B07763A11636BCBECEF5976D8E1D2E6EC811E5C2BFDECB75152F99A81EC13F7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |