| File name: | Letter regarding loss of Diplomatic Bag with Sensitive Documents.exe.bin |
| Full analysis: | https://app.any.run/tasks/181b9668-ad9c-4cb7-9dfa-c2ce03866fdd |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2020, 06:32:49 |
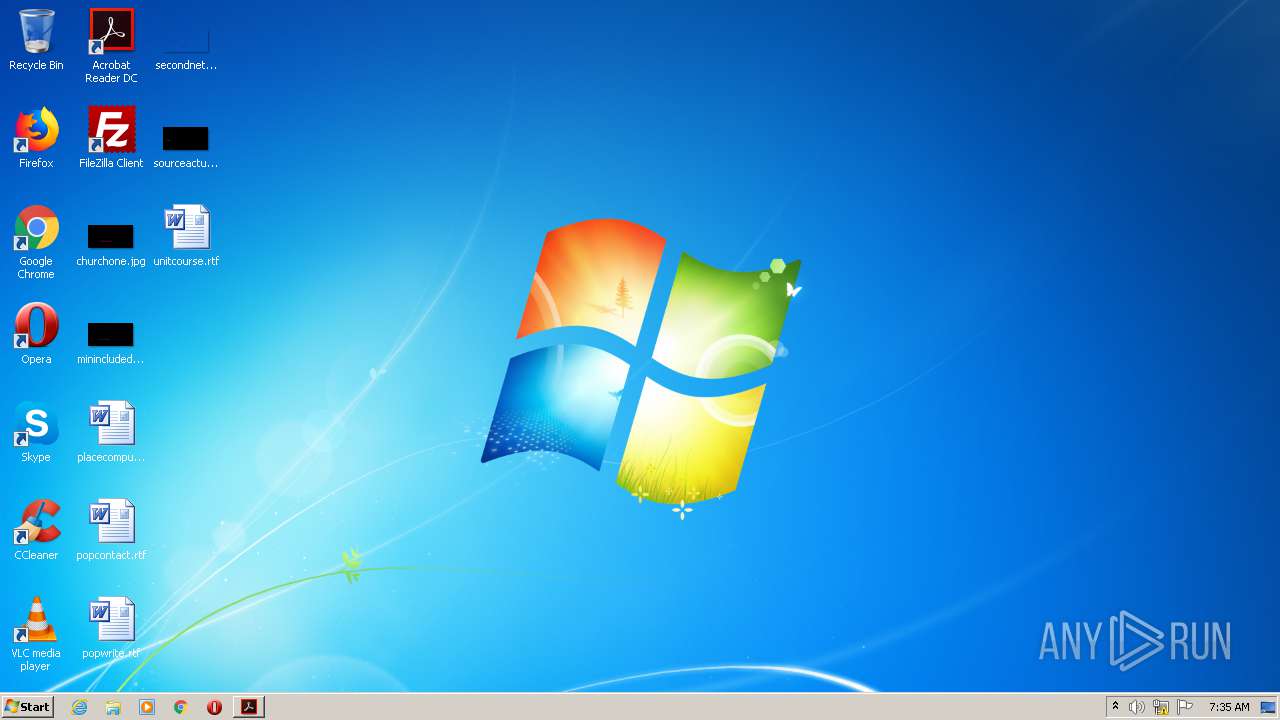
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 9F4649FF692011615D5CF3C5D410B95E |
| SHA1: | 5F7C6637088B8E1A64C5F0E1FF0695C3E050616D |
| SHA256: | BF8E469A058F90D9CCBE081B0DA470D3314AA4CD34F916865F0C0B4FA28EACD8 |
| SSDEEP: | 49152:TdriCUQHoN4zzTEsqWvjrKELEjriLFGP6s8fnZORiVqWA2fXuHbPQPvFE:TpjbHo0z4sqWrvuPP3GMRoBAvH2vq |
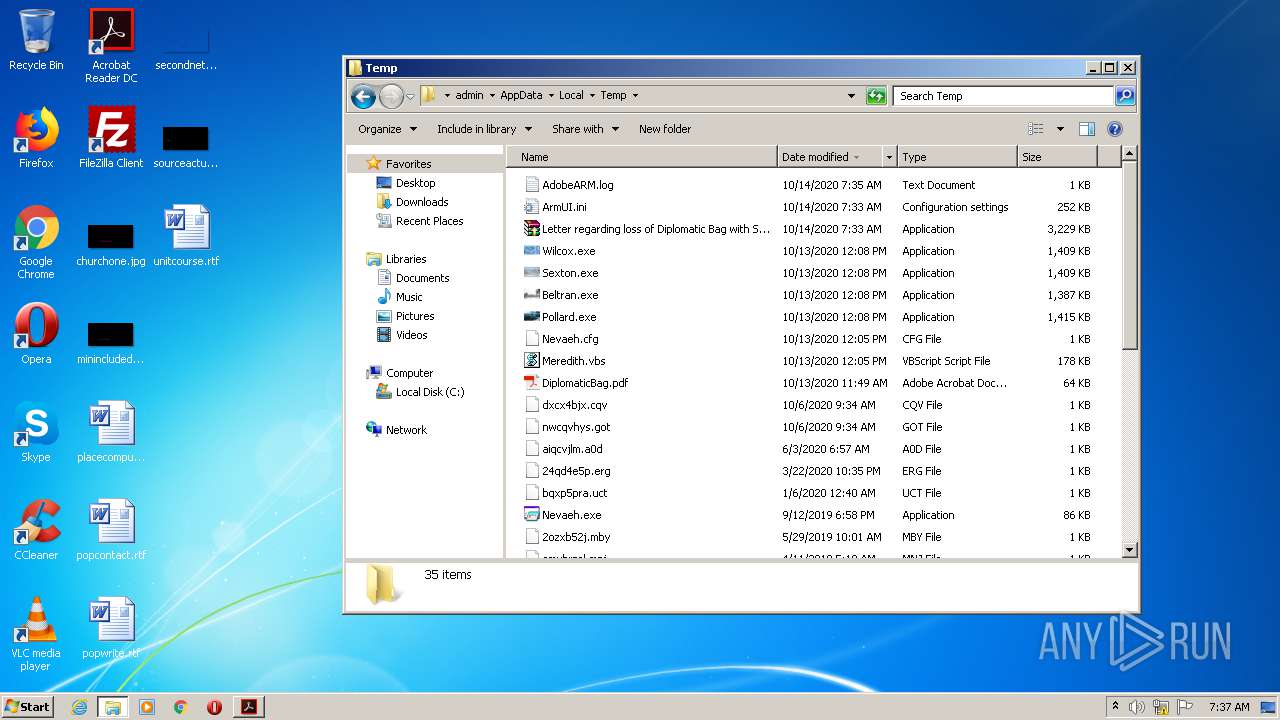
MALICIOUS
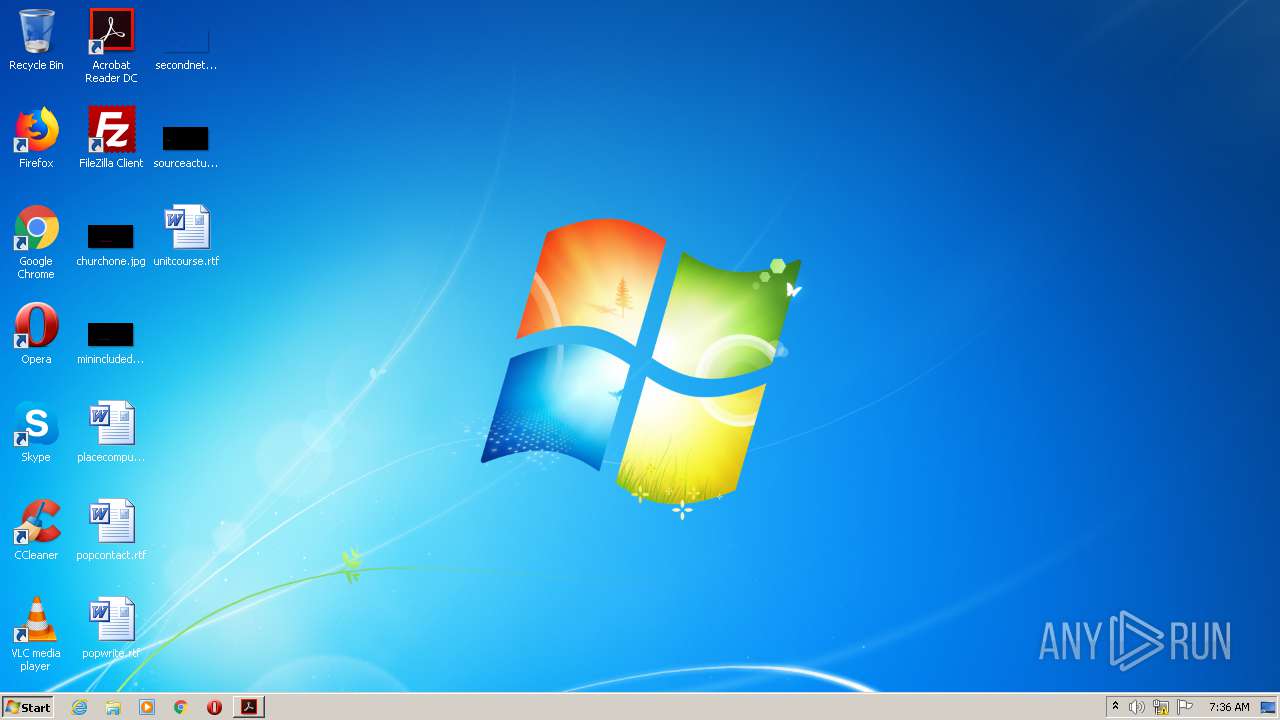
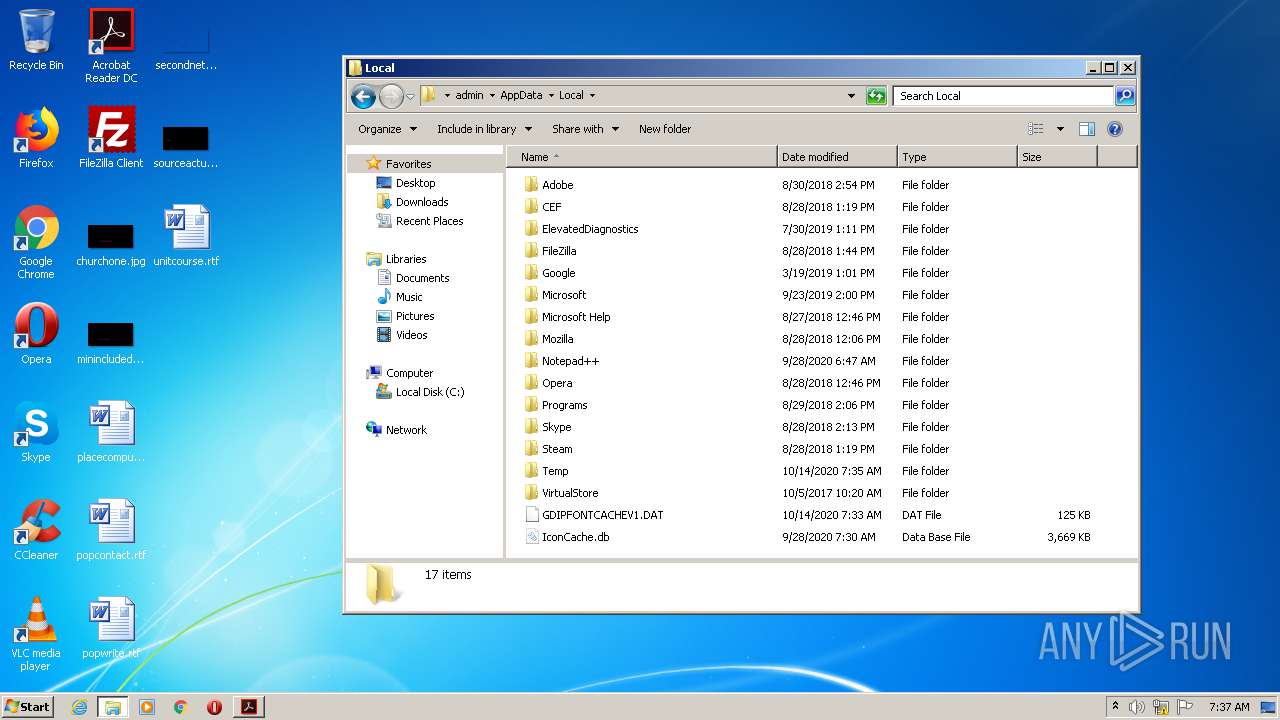
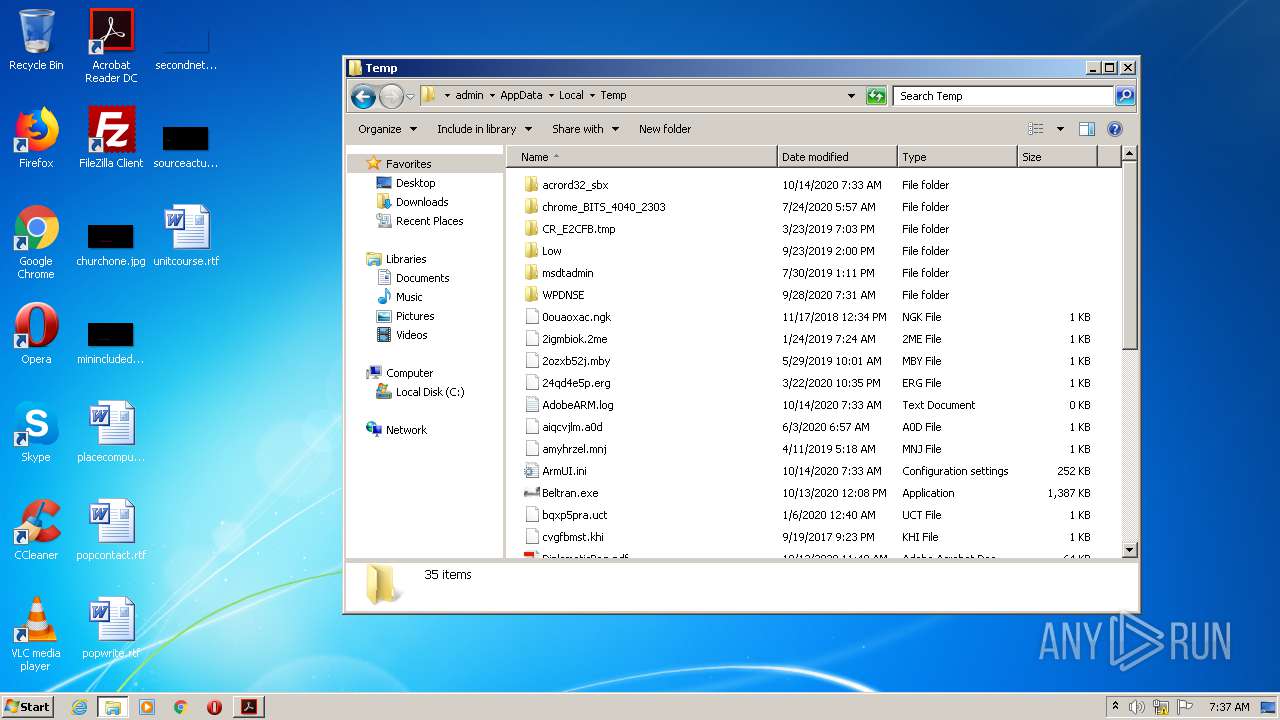
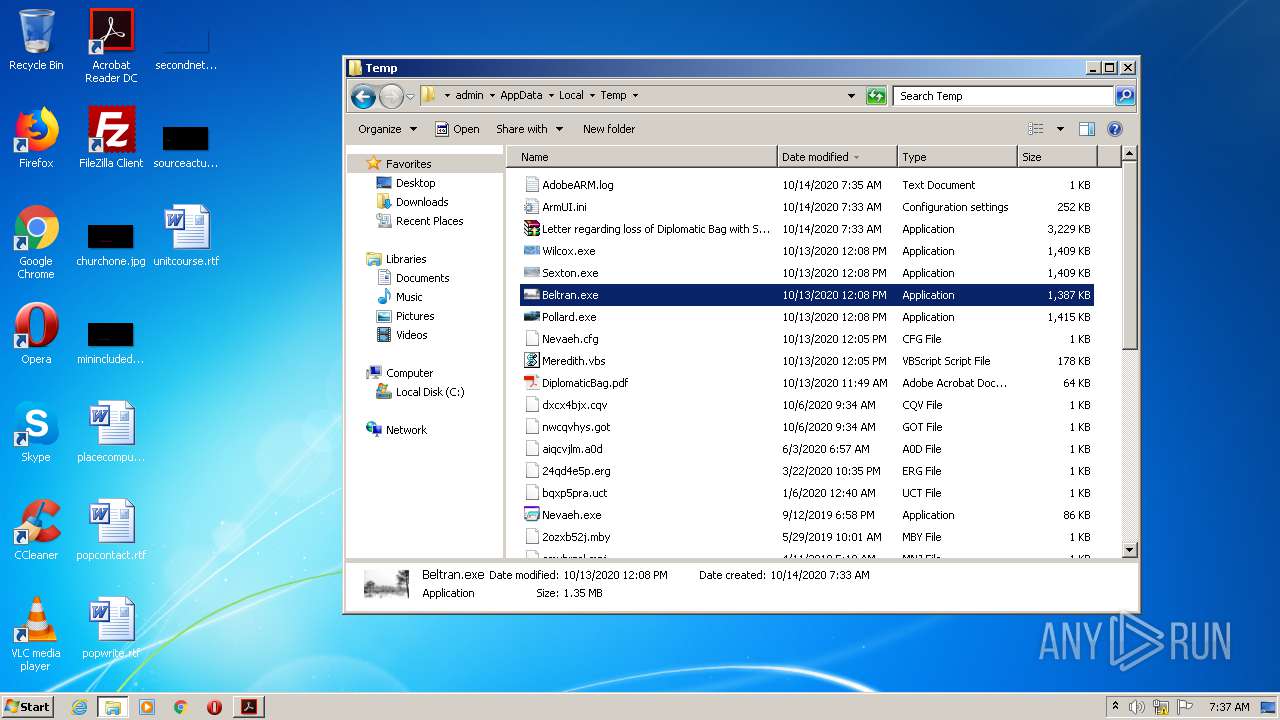
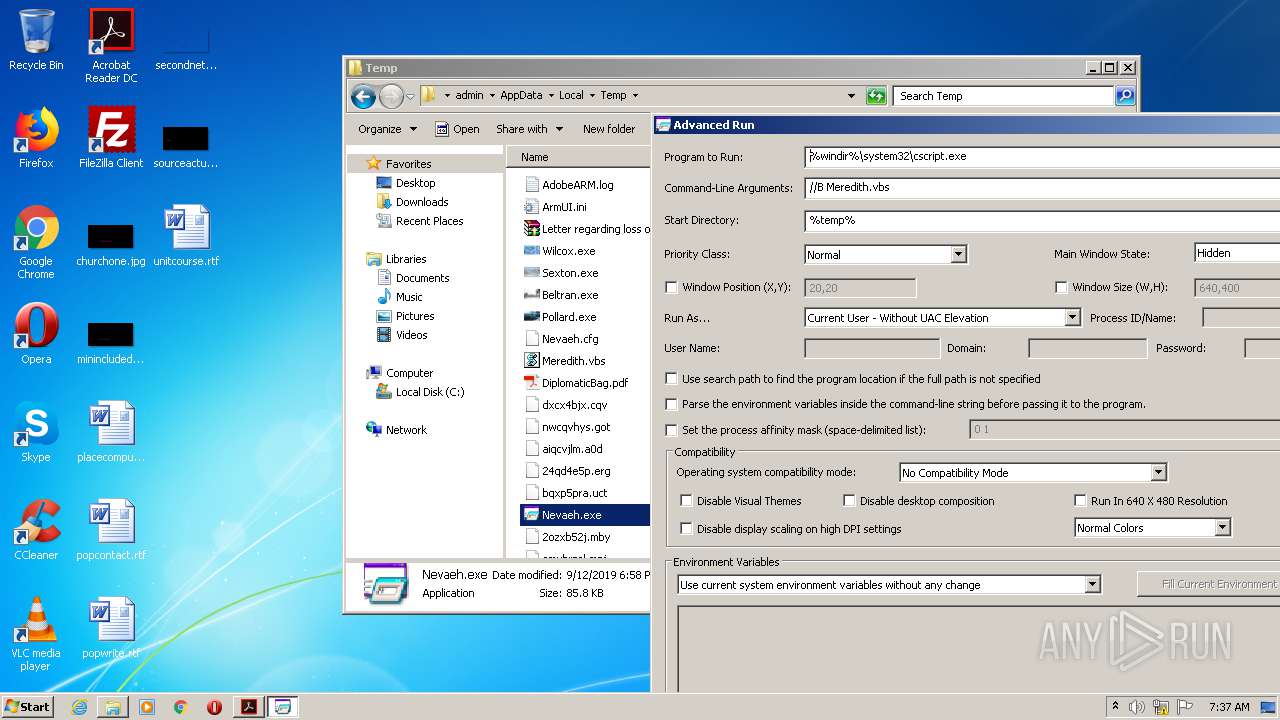
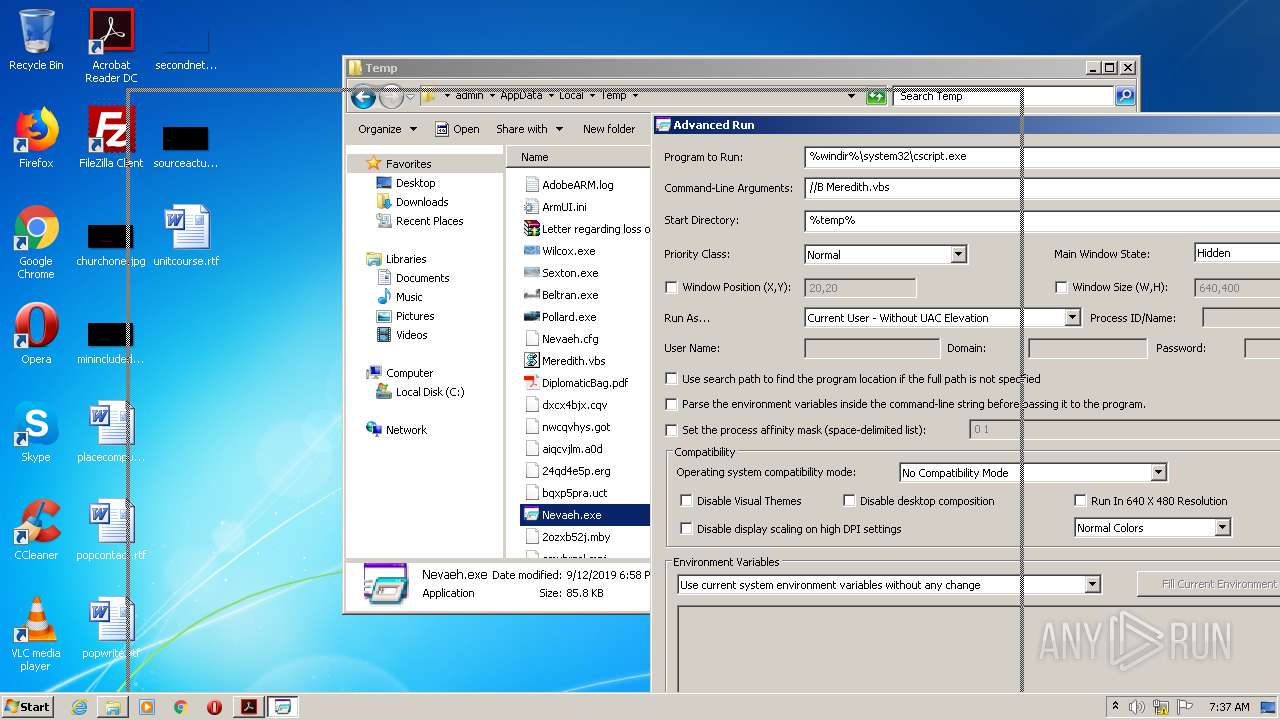
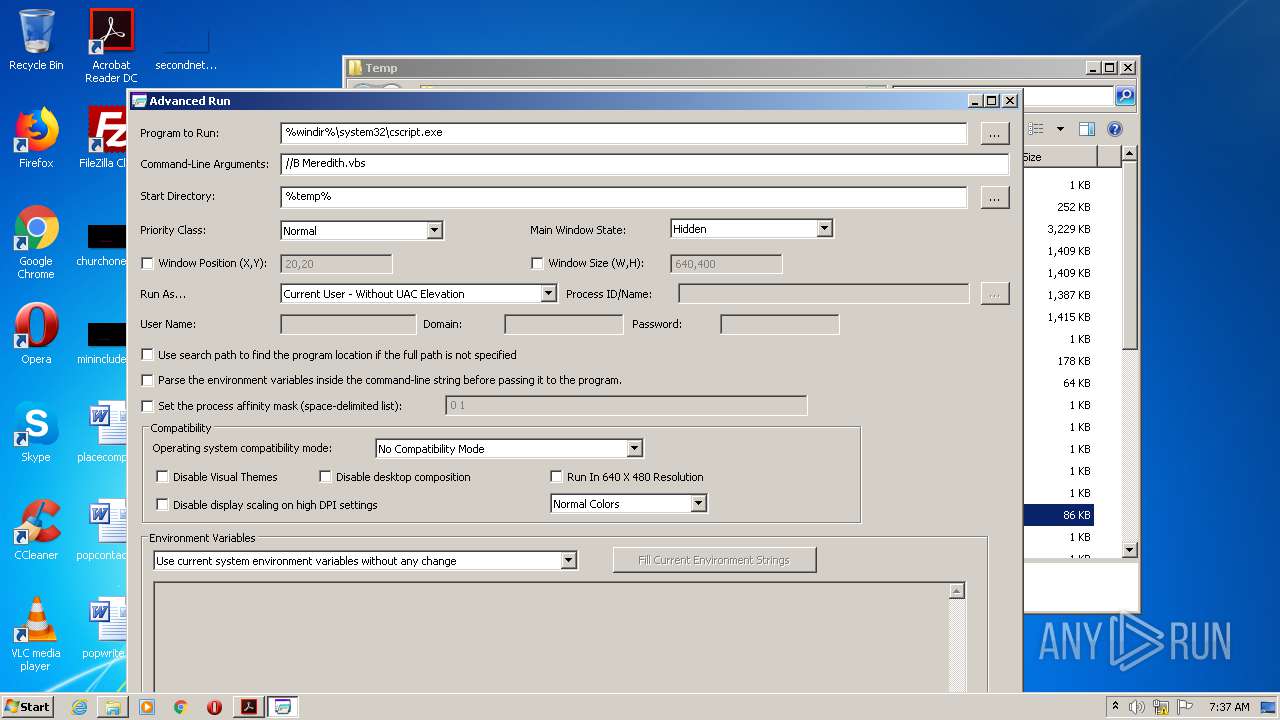
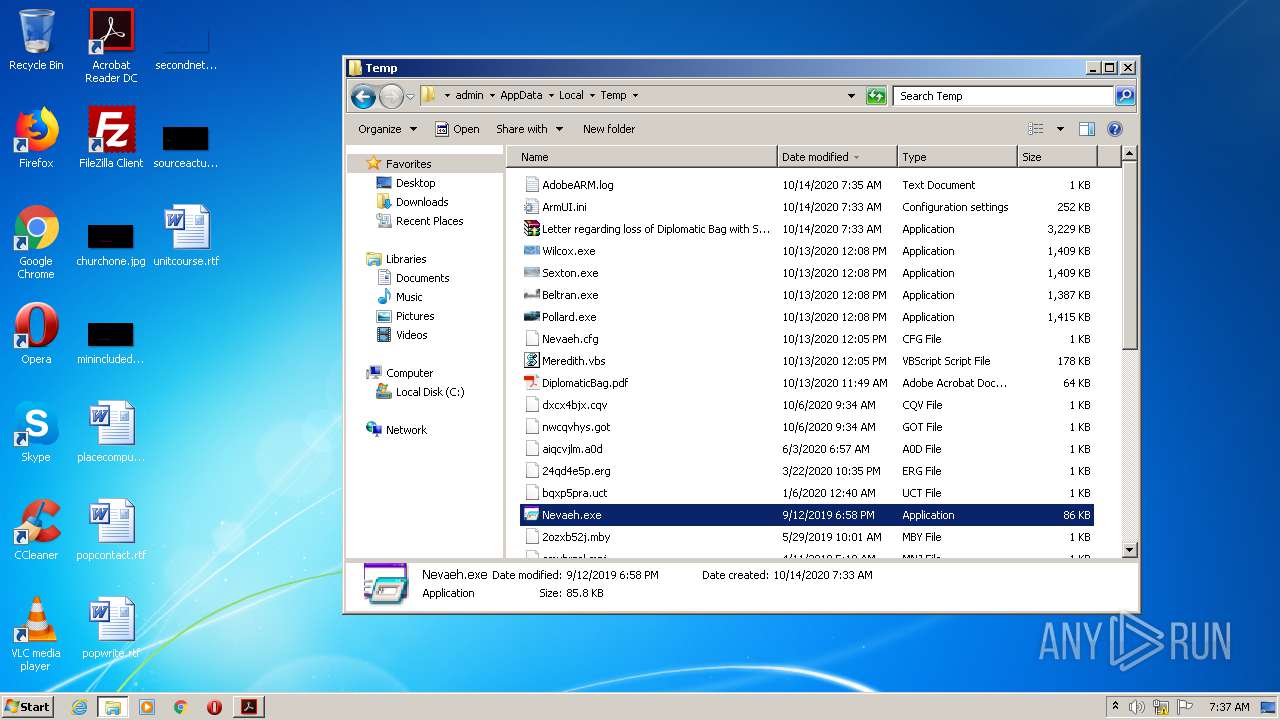
Application was dropped or rewritten from another process
- Nevaeh.exe (PID: 1340)
- Sexton.exe (PID: 2620)
- Wilcox.exe (PID: 3908)
- Beltran.exe (PID: 3356)
- Pollard.exe (PID: 184)
- Nevaeh.exe (PID: 2900)
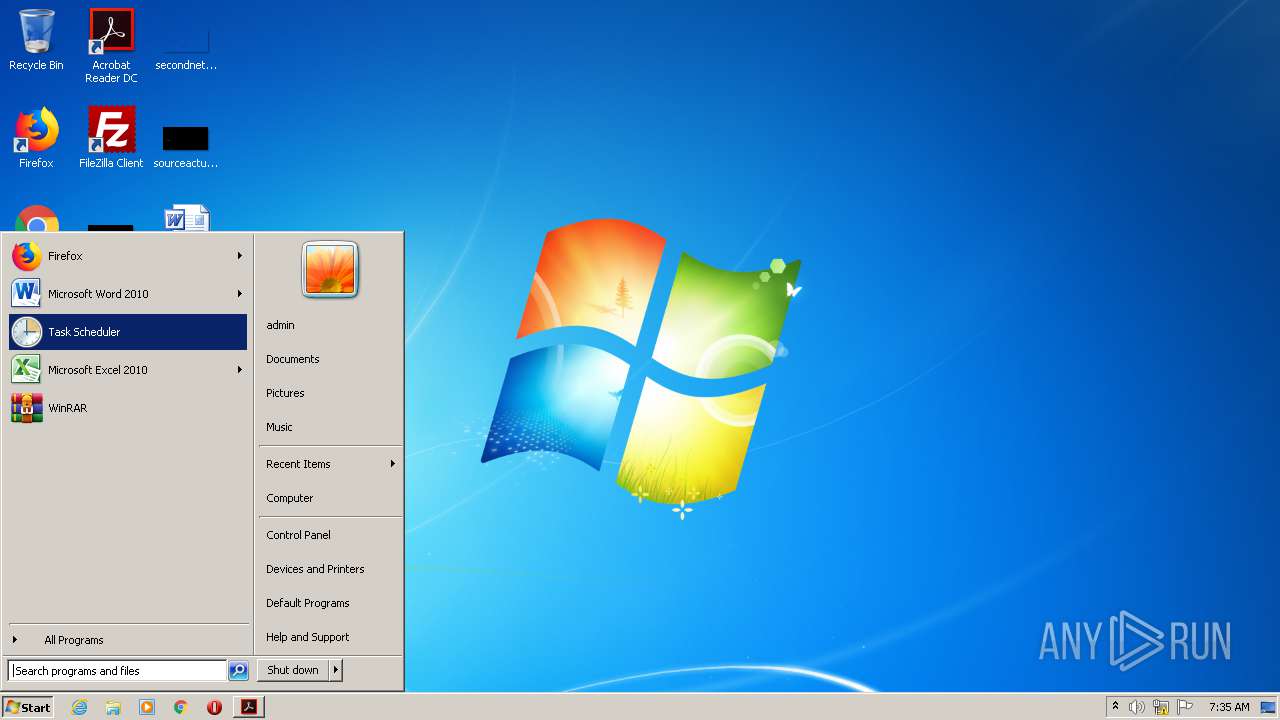
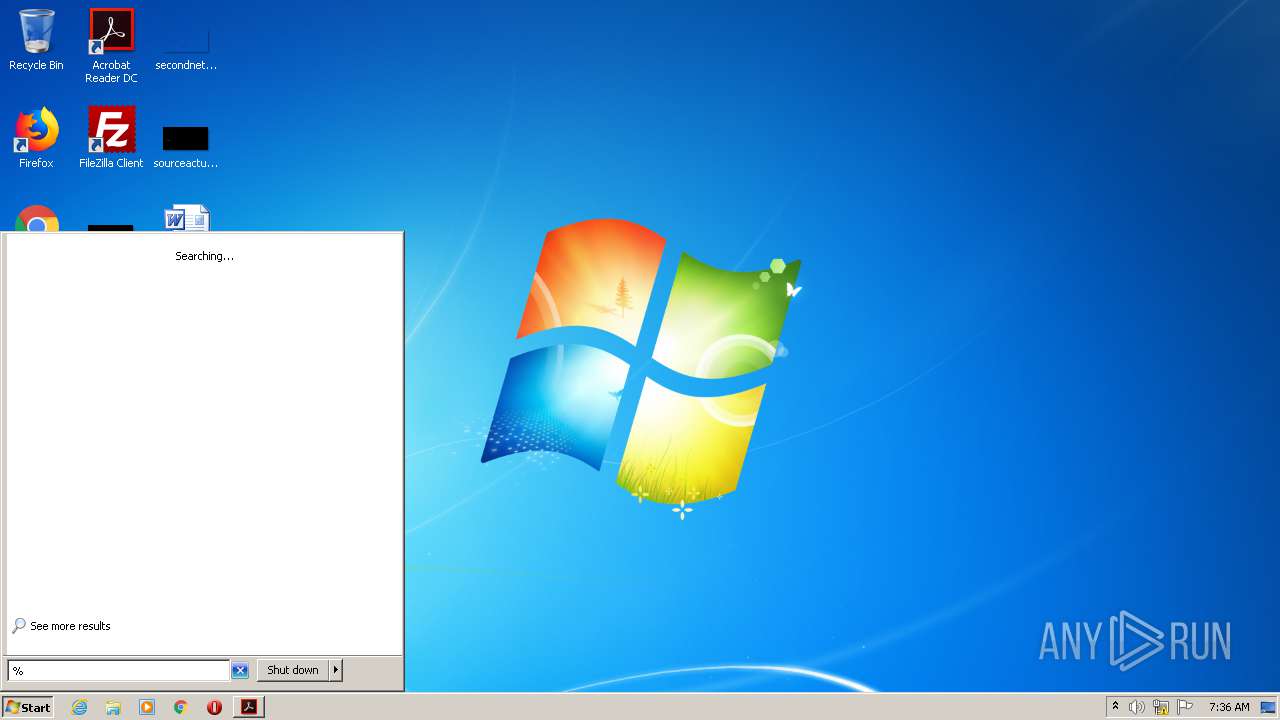
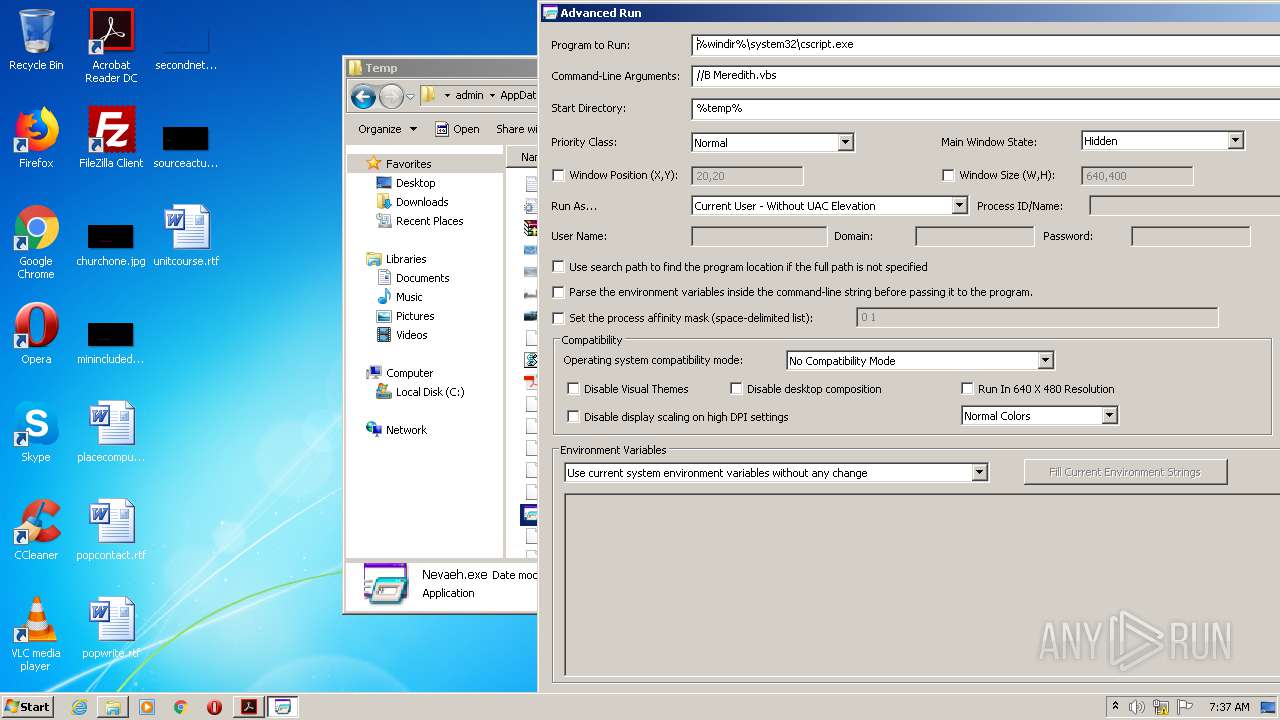
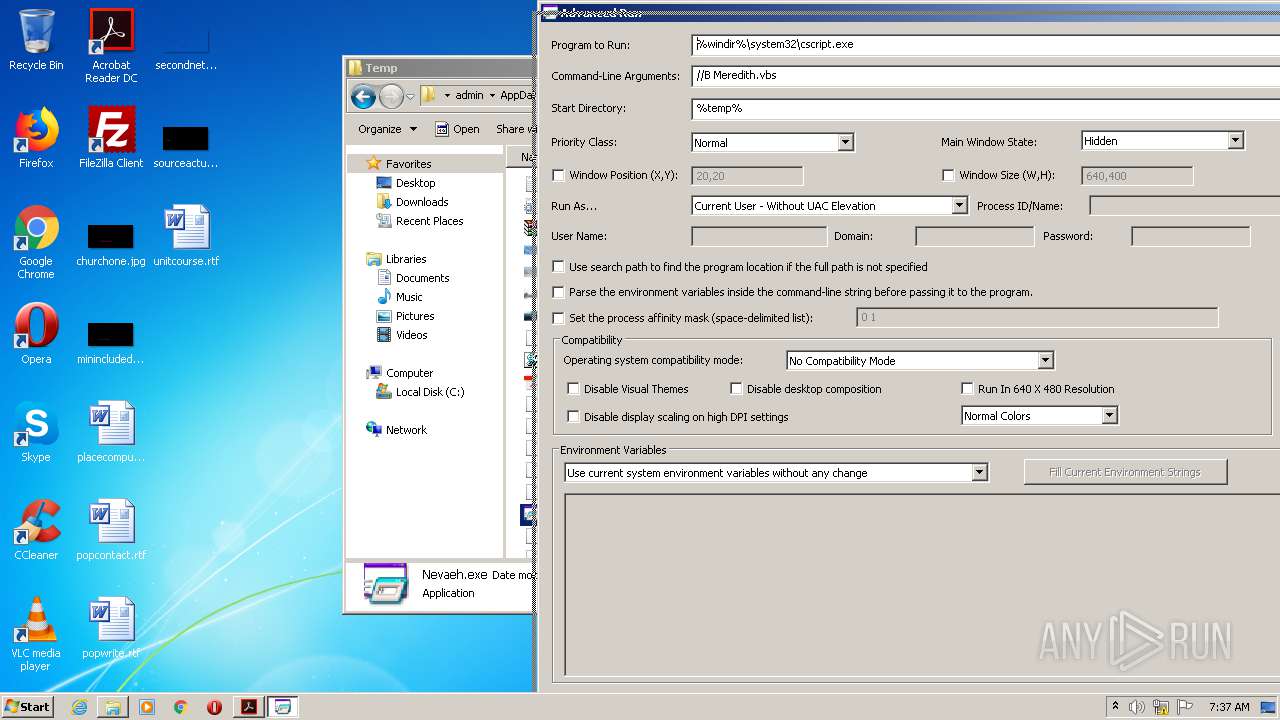
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4048)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 1744)
- cmd.exe (PID: 3460)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1452)
- schtasks.exe (PID: 1896)
- schtasks.exe (PID: 2592)
- schtasks.exe (PID: 3516)
- schtasks.exe (PID: 2376)
- schtasks.exe (PID: 3292)
SUSPICIOUS
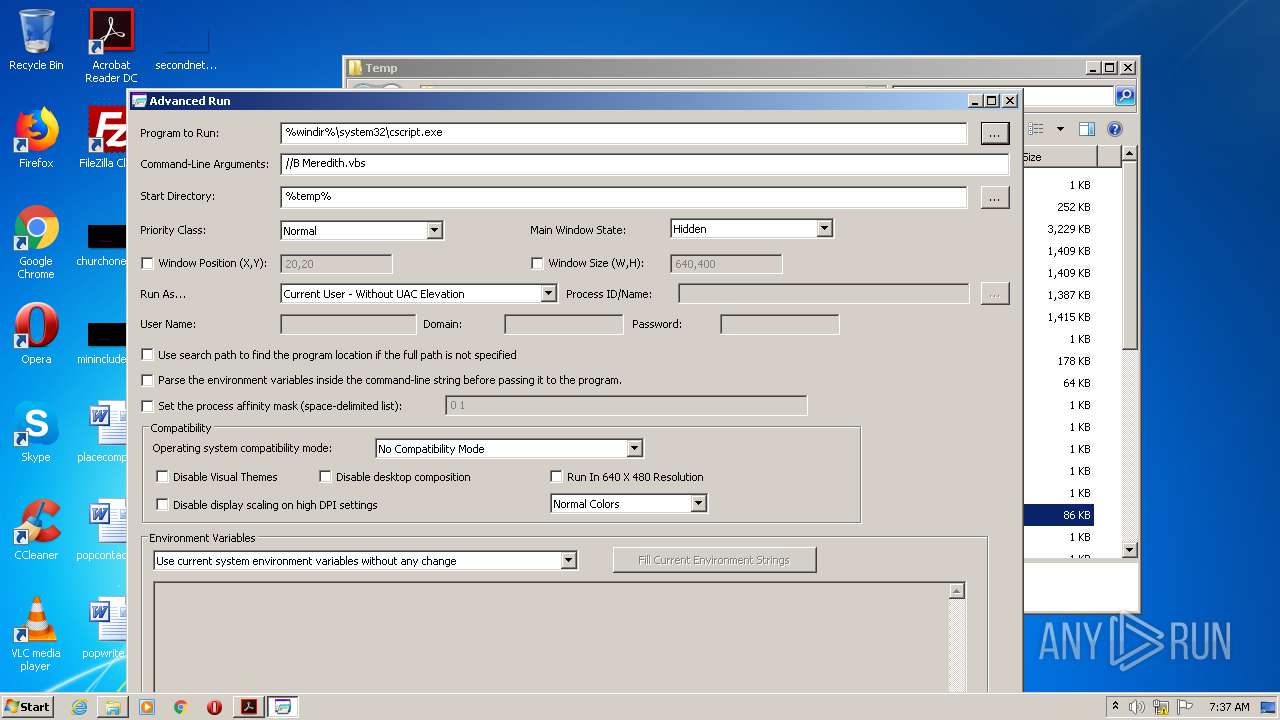
Starts CMD.EXE for commands execution
- cscript.exe (PID: 2980)
Executable content was dropped or overwritten
- Letter regarding loss of Diplomatic Bag with Sensitive Documents.exe.bin.exe (PID: 2696)
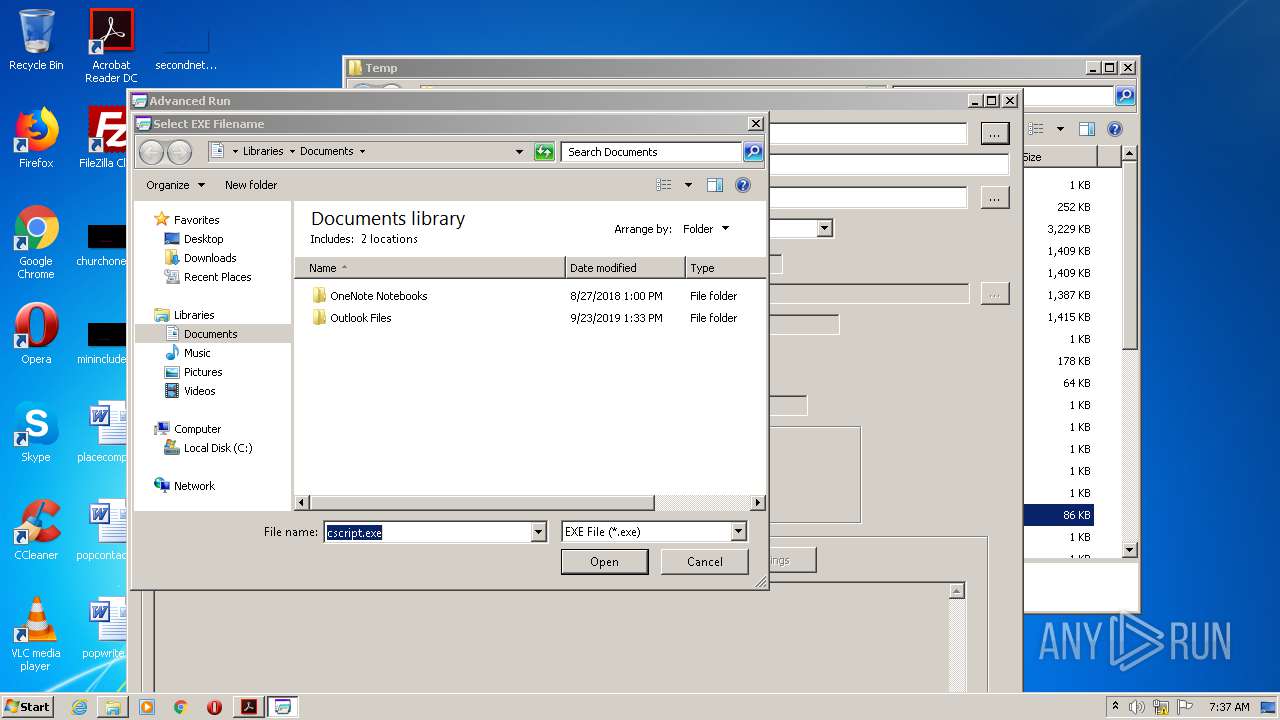
Executes scripts
- Nevaeh.exe (PID: 1340)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 4068)
Creates files in the program directory
- AdobeARM.exe (PID: 3860)
INFO
Reads Internet Cache Settings
- AcroRd32.exe (PID: 3580)
- AcroRd32.exe (PID: 1288)
Application launched itself
- AcroRd32.exe (PID: 1288)
- RdrCEF.exe (PID: 2268)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 1288)
Reads the hosts file
- RdrCEF.exe (PID: 2268)
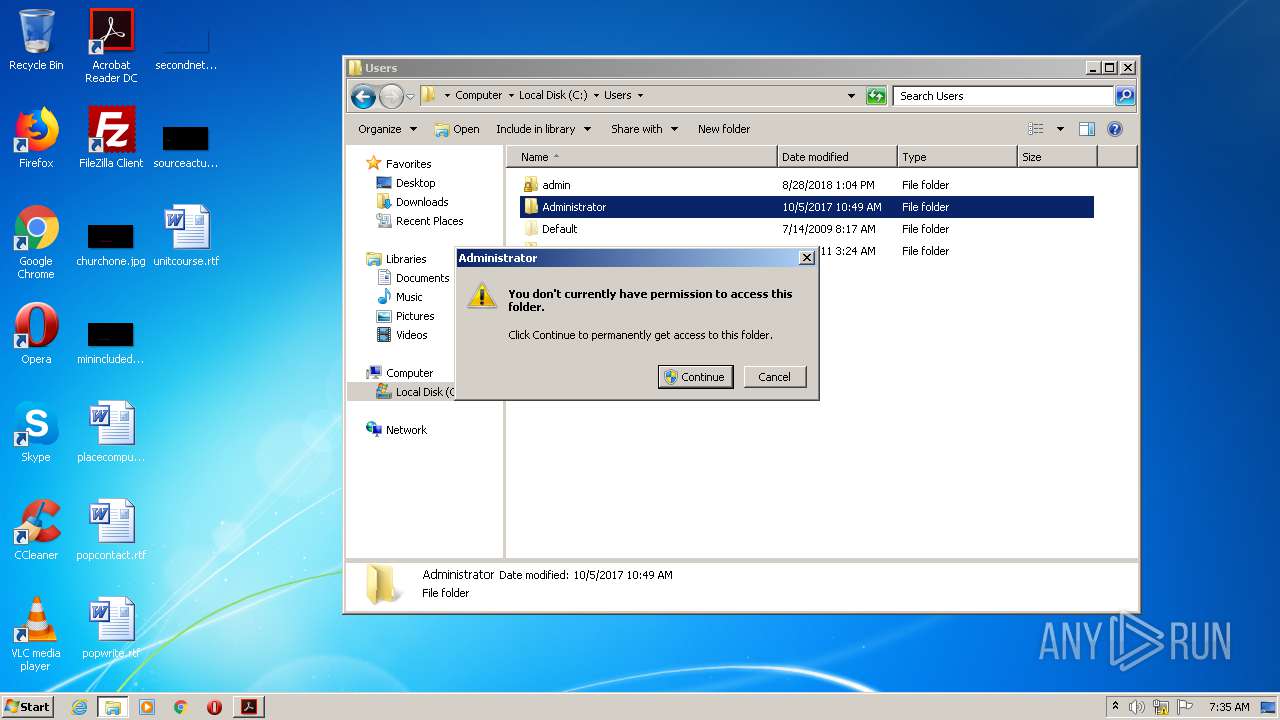
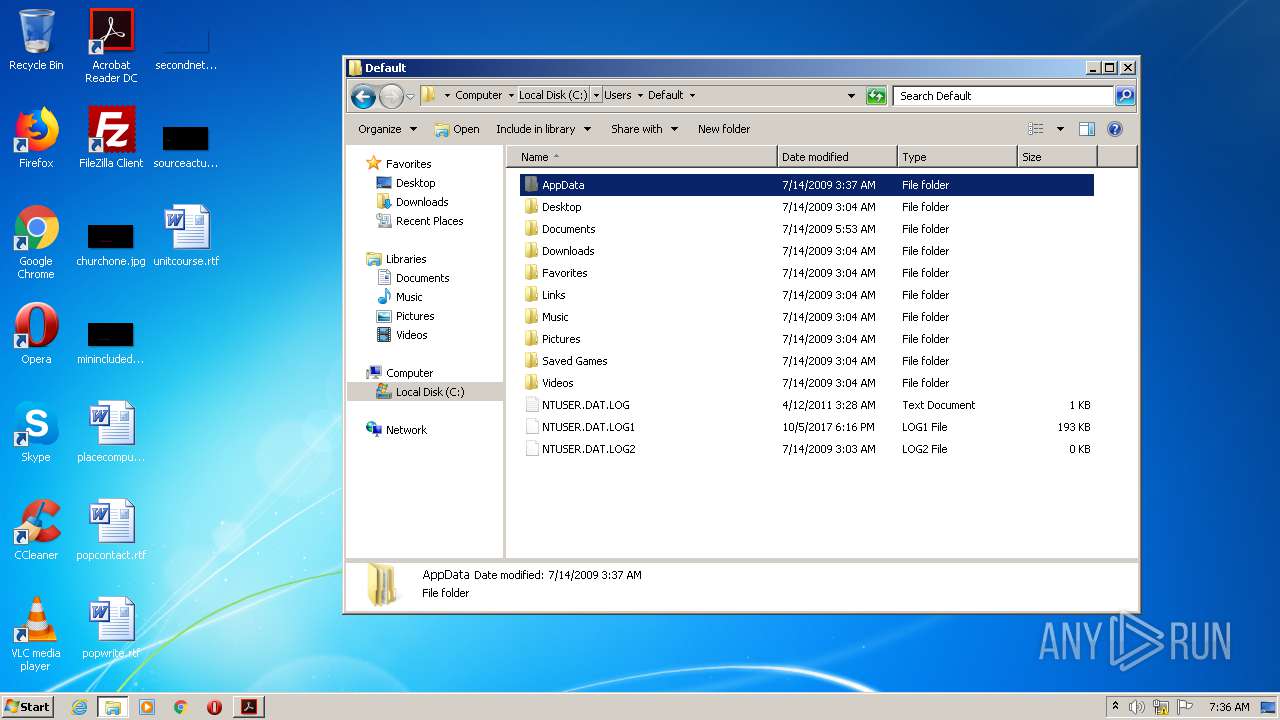
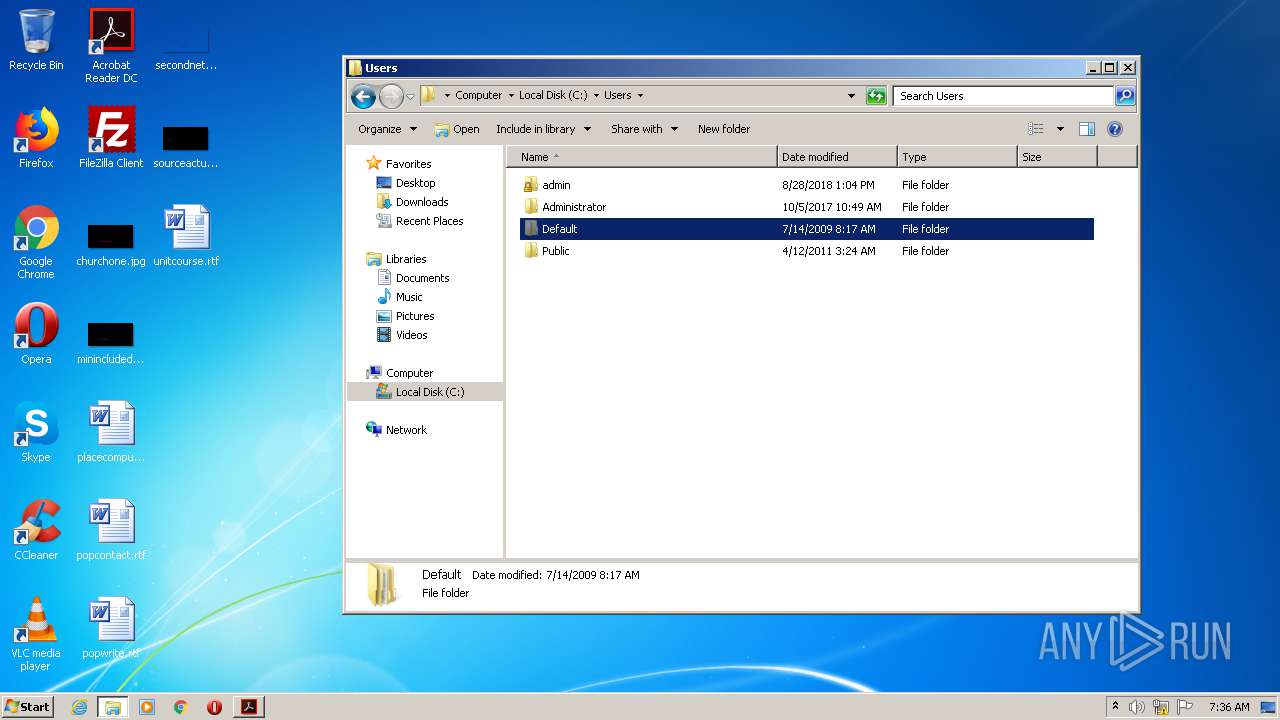
Manual execution by user
- Wilcox.exe (PID: 3908)
- Sexton.exe (PID: 2620)
- Beltran.exe (PID: 3356)
- Pollard.exe (PID: 184)
- Nevaeh.exe (PID: 2900)
- explorer.exe (PID: 3708)
- verclsid.exe (PID: 2988)
Reads settings of System Certificates
- AcroRd32.exe (PID: 1288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:09 15:19:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 74752 |
| InitializedDataSize: | 121344 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xac87 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jun-2012 13:19:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Jun-2012 13:19:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001231E | 0x00012400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55555 |
.rdata | 0x00014000 | 0x00001D15 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99401 |
.data | 0x00016000 | 0x00017724 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.54914 |
.CRT | 0x0002E000 | 0x00000020 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.394141 |
.rsrc | 0x0002F000 | 0x00004110 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67296 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.24143 | 556 | UNKNOWN | English - United States | RT_STRING |
8 | 3.26996 | 974 | UNKNOWN | English - United States | RT_STRING |
9 | 3.04375 | 530 | UNKNOWN | English - United States | RT_STRING |
10 | 3.16254 | 776 | UNKNOWN | English - United States | RT_STRING |
11 | 3.06352 | 380 | UNKNOWN | English - United States | RT_STRING |
12 | 2.33959 | 102 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
82
Monitored processes
32
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Users\admin\AppData\Local\Temp\Pollard.exe" | C:\Users\admin\AppData\Local\Temp\Pollard.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\DiplomaticBag.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | cmd.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\AppData\Local\Temp\Nevaeh.exe" /run | C:\Users\admin\AppData\Local\Temp\Nevaeh.exe | — | Letter regarding loss of Diplomatic Bag with Sensitive Documents.exe.bin.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Run a program with different settings that you choose. Exit code: 0 Version: 1.10 Modules
| |||||||||||||||
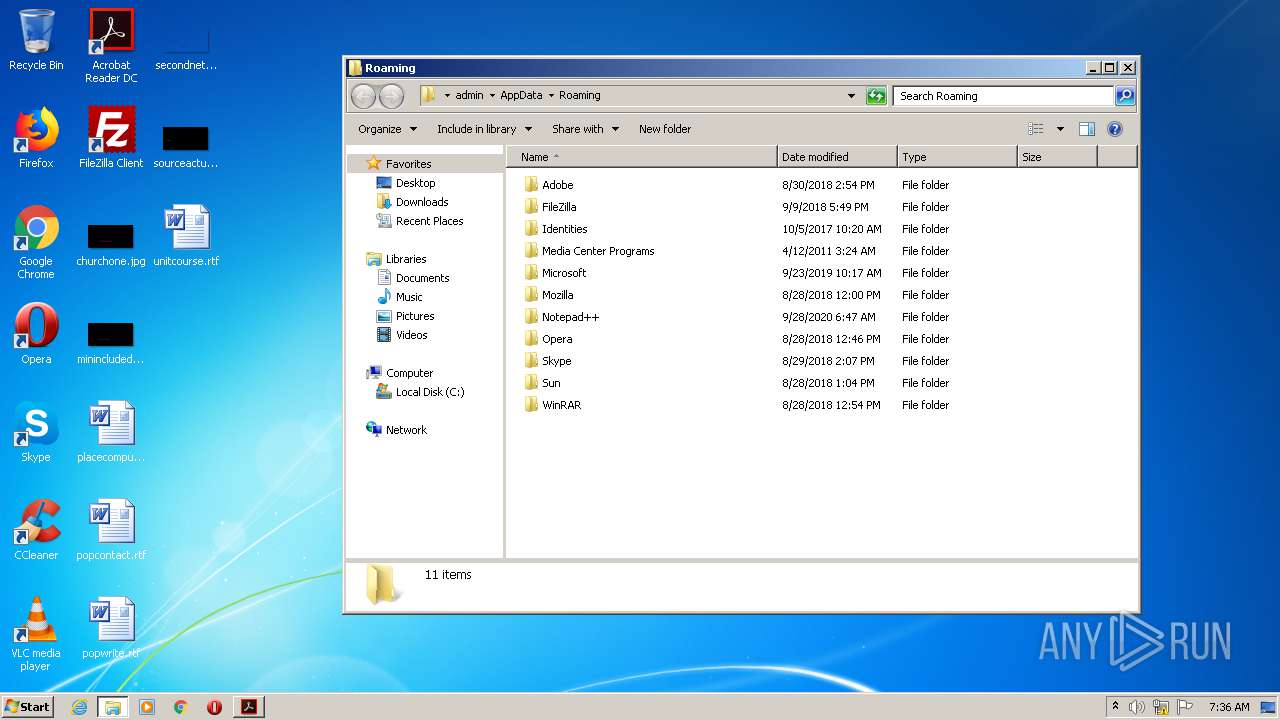
| 1452 | SCHTASKS /Create /SC MINUTE /MO 10 /TN Pollard /TR C:\Users\admin\AppData\Local\Temp\Pollard.exe /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1744 | "C:\Windows\System32\cmd.exe" /c SCHTASKS /Create /SC MINUTE /MO 70 /TN Sexton /TR C:\Users\admin\AppData\Local\Temp\Sexton.exe /F | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1760 | "C:\Windows\System32\cmd.exe" /c SCHTASKS /Create /SC HOURLY /MO 8 /TN Lotermity /TR C:\Users\admin\AppData\Roaming\HP\Lotermity.exe /F | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1896 | SCHTASKS /Create /SC HOURLY /MO 2 /TN Beltran /TR C:\Users\admin\AppData\Local\Temp\Beltran.exe /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2268.1.215895694\1377758480" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2364 | "C:\Windows\System32\cmd.exe" /c SCHTASKS /Create /SC HOURLY /MO 2 /TN Beltran /TR C:\Users\admin\AppData\Local\Temp\Beltran.exe /F | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 552
Read events
1 485
Write events
66
Delete events
1
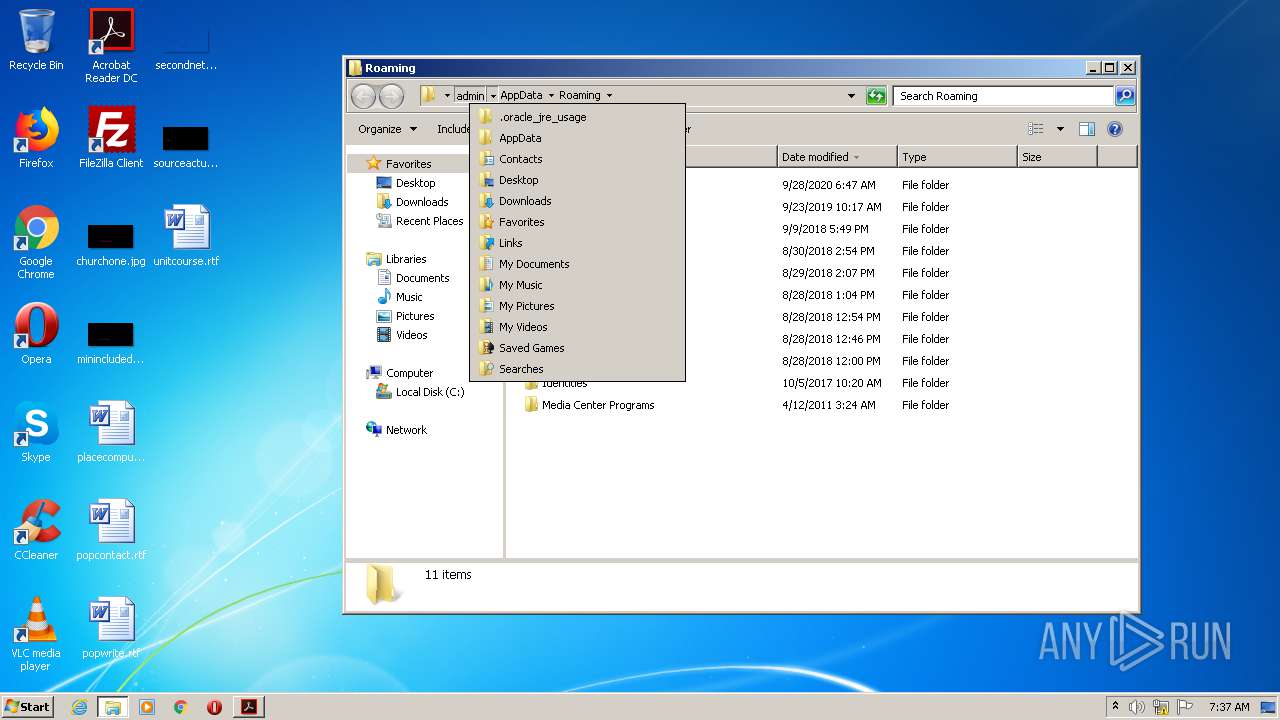
Modification events
| (PID) Process: | (2696) Letter regarding loss of Diplomatic Bag with Sensitive Documents.exe.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2696) Letter regarding loss of Diplomatic Bag with Sensitive Documents.exe.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2980) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2980) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3412) reg.exe | Key: | HKEY_CLASSES_ROOT\exefile\shell\open |
| Operation: | write | Name: | NoSmartScreen |
Value: 1 | |||
| (PID) Process: | (3580) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (3580) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (1288) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 10001 | |||
| (PID) Process: | (1288) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1288) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
3
Text files
43
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3580 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.3580 | — | |
MD5:— | SHA256:— | |||
| 3580 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.3580 | — | |
MD5:— | SHA256:— | |||
| 3580 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rz6dgfg_1v9vdh_2rg.tmp | — | |
MD5:— | SHA256:— | |||
| 3580 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Ra5ib1h_1v9vdi_2rg.tmp | — | |
MD5:— | SHA256:— | |||
| 3580 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rvn6u7y_1v9vdj_2rg.tmp | — | |
MD5:— | SHA256:— | |||
| 3580 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rikgd23_1v9vdg_2rg.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\TmpCB2B.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\TmpCB3B.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | Letter regarding loss of Diplomatic Bag with Sensitive Documents.exe.bin.exe | C:\Users\admin\AppData\Local\Temp\Meredith.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1288 | AcroRd32.exe | GET | 304 | 2.16.177.91:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
1288 | AcroRd32.exe | GET | 304 | 2.16.177.91:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
1288 | AcroRd32.exe | GET | 200 | 2.16.177.91:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | compressed | 9.54 Kb | whitelisted |
1288 | AcroRd32.exe | GET | 304 | 2.16.177.91:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.111.214.232:443 | ardownload2.adobe.com | Akamai International B.V. | NL | whitelisted |
1288 | AcroRd32.exe | 2.16.177.91:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
1288 | AcroRd32.exe | 104.79.88.64:443 | armmf.adobe.com | Time Warner Cable Internet LLC | US | suspicious |
— | — | 104.79.88.64:443 | armmf.adobe.com | Time Warner Cable Internet LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |