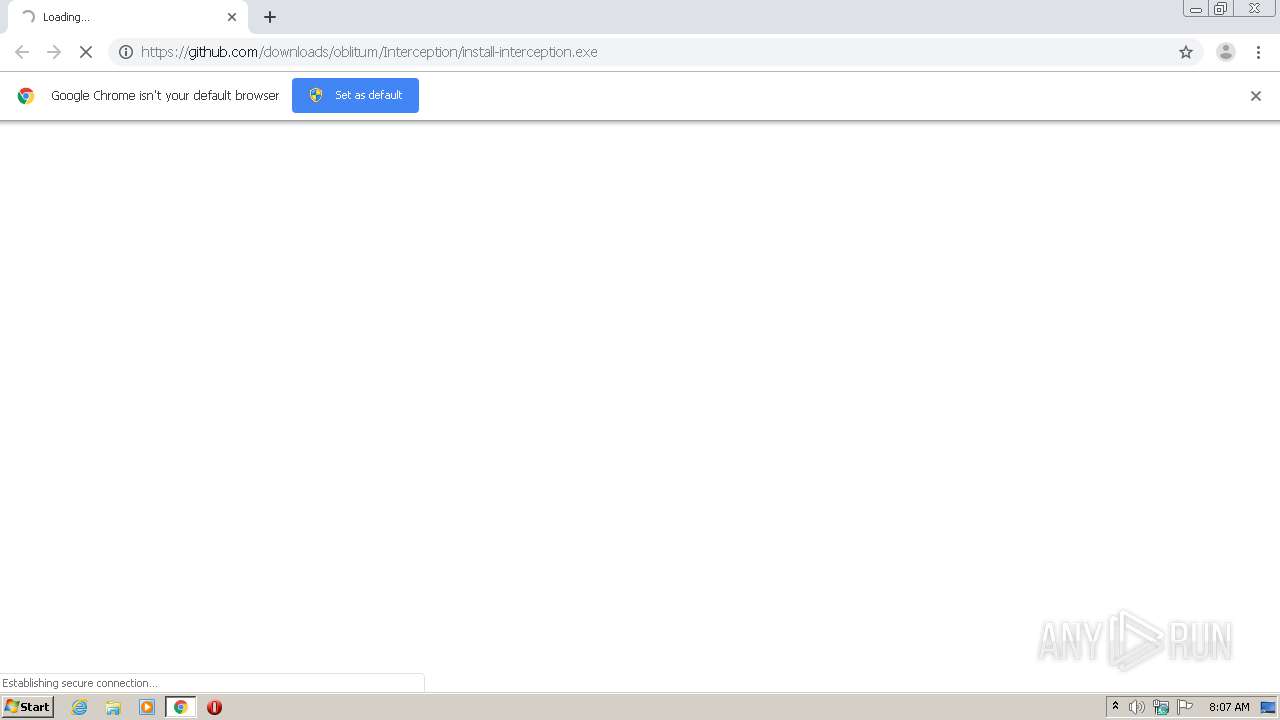
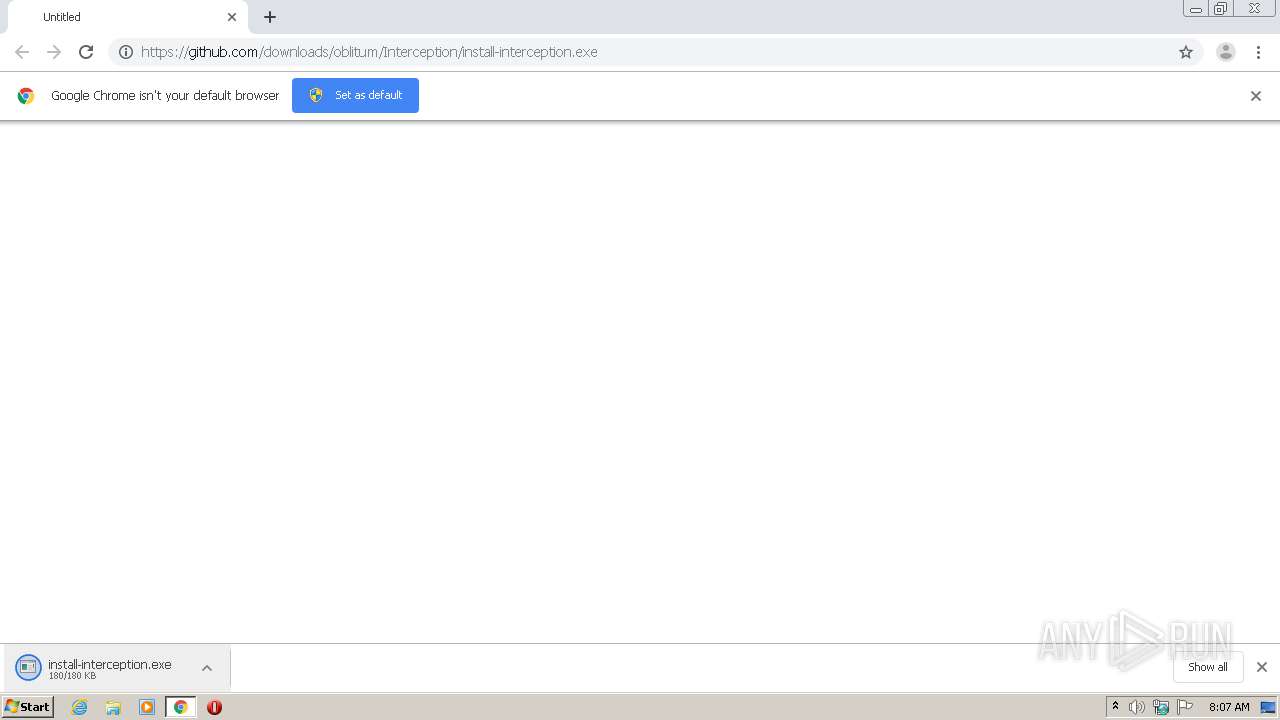
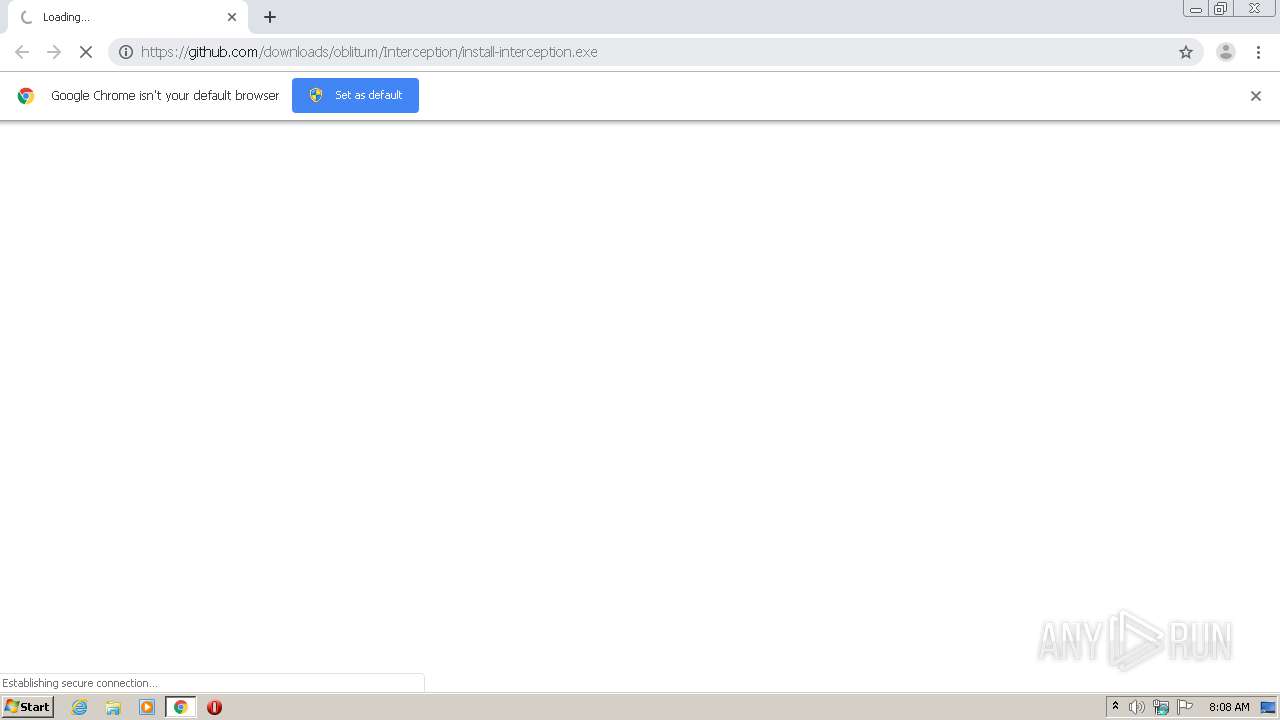
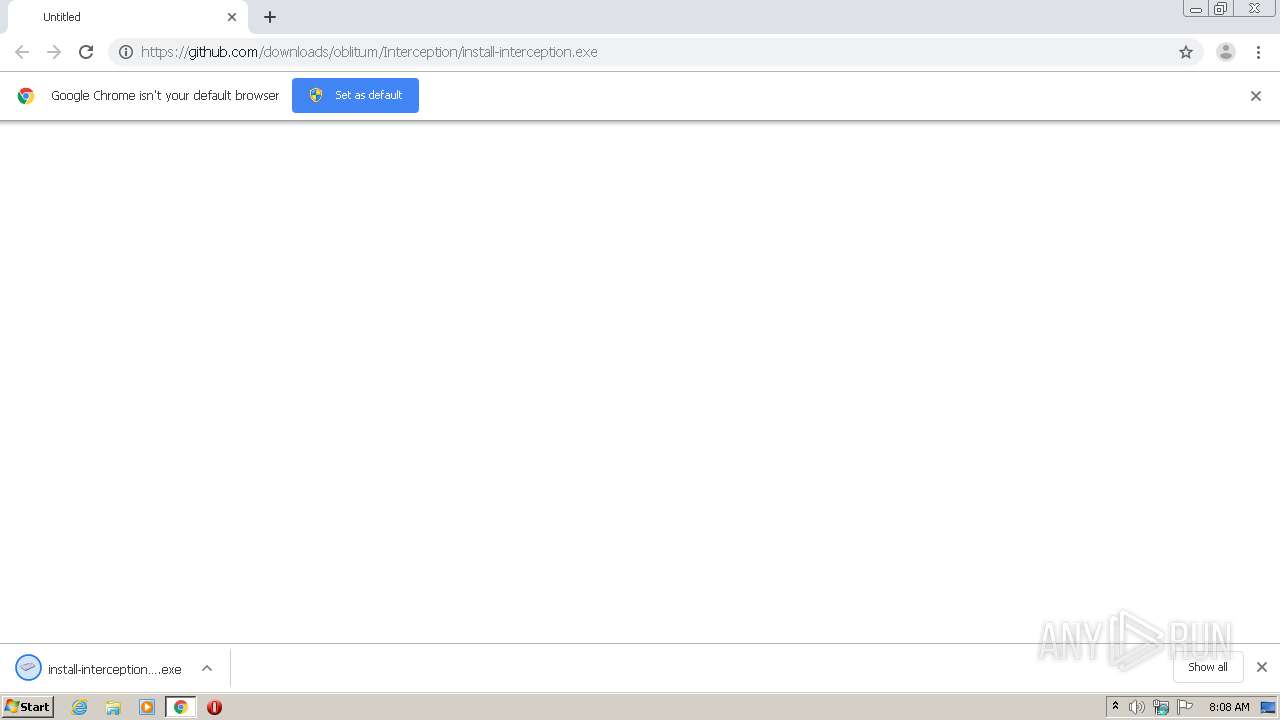
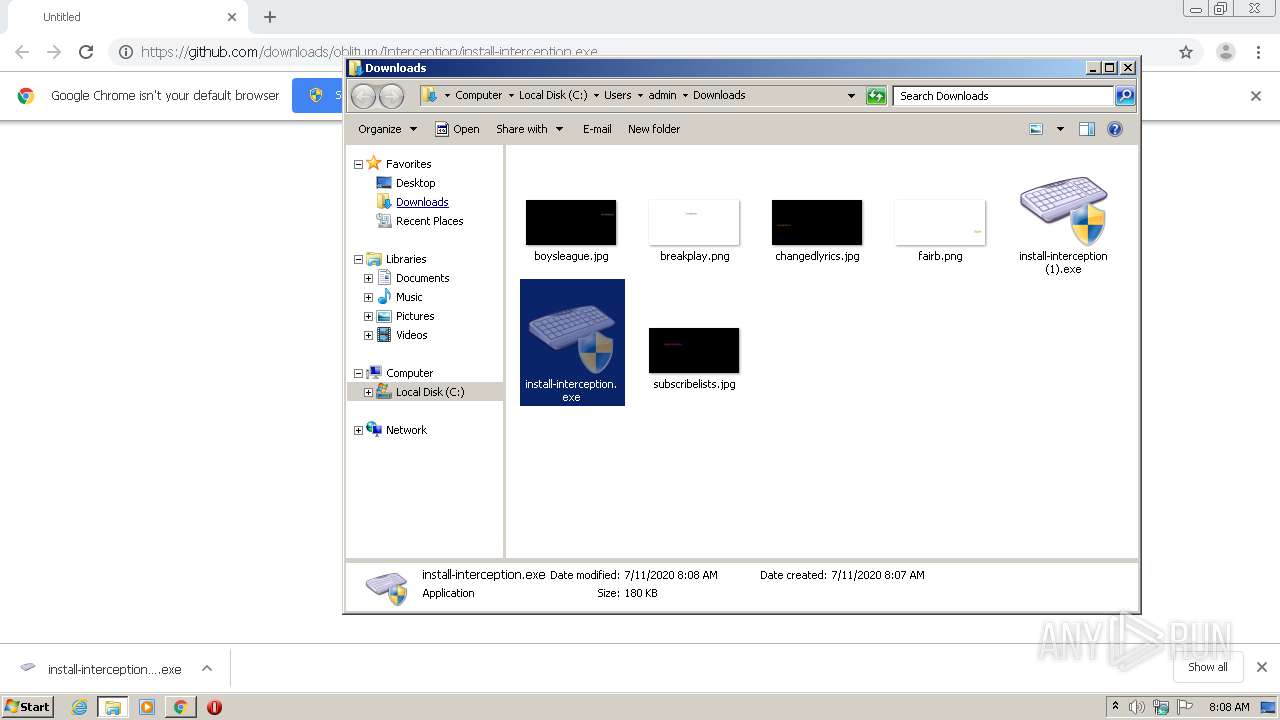
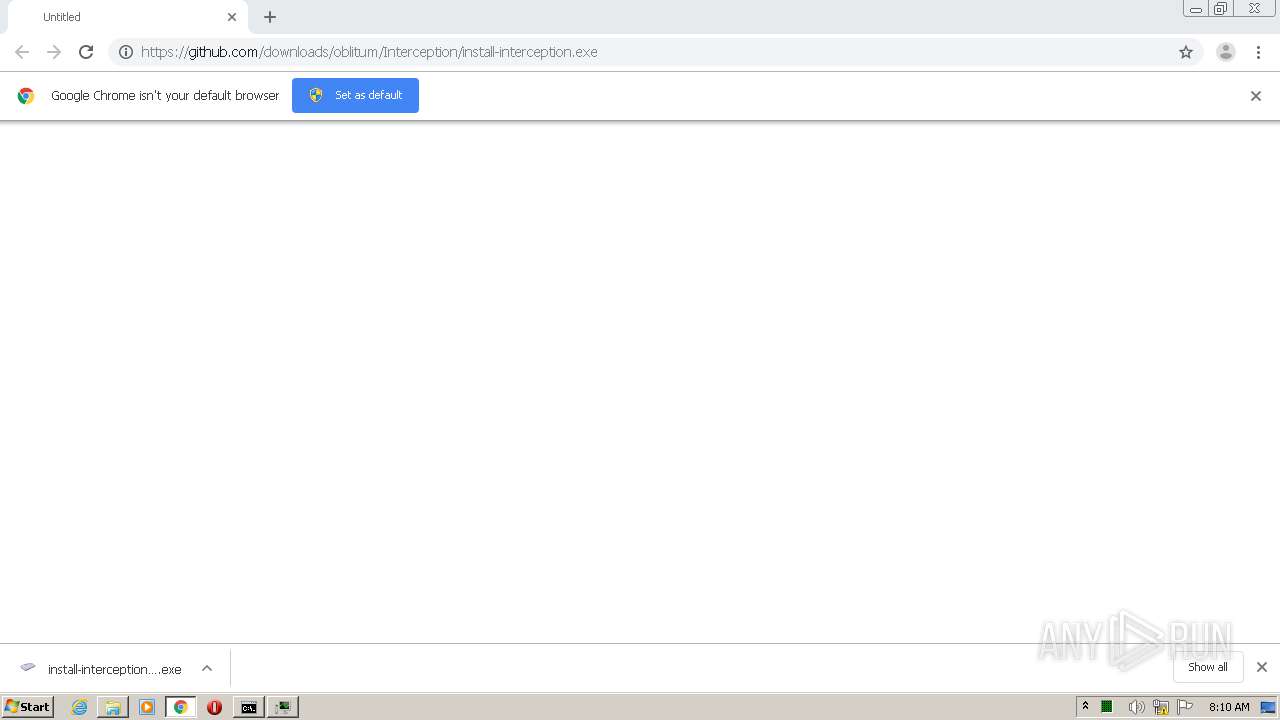
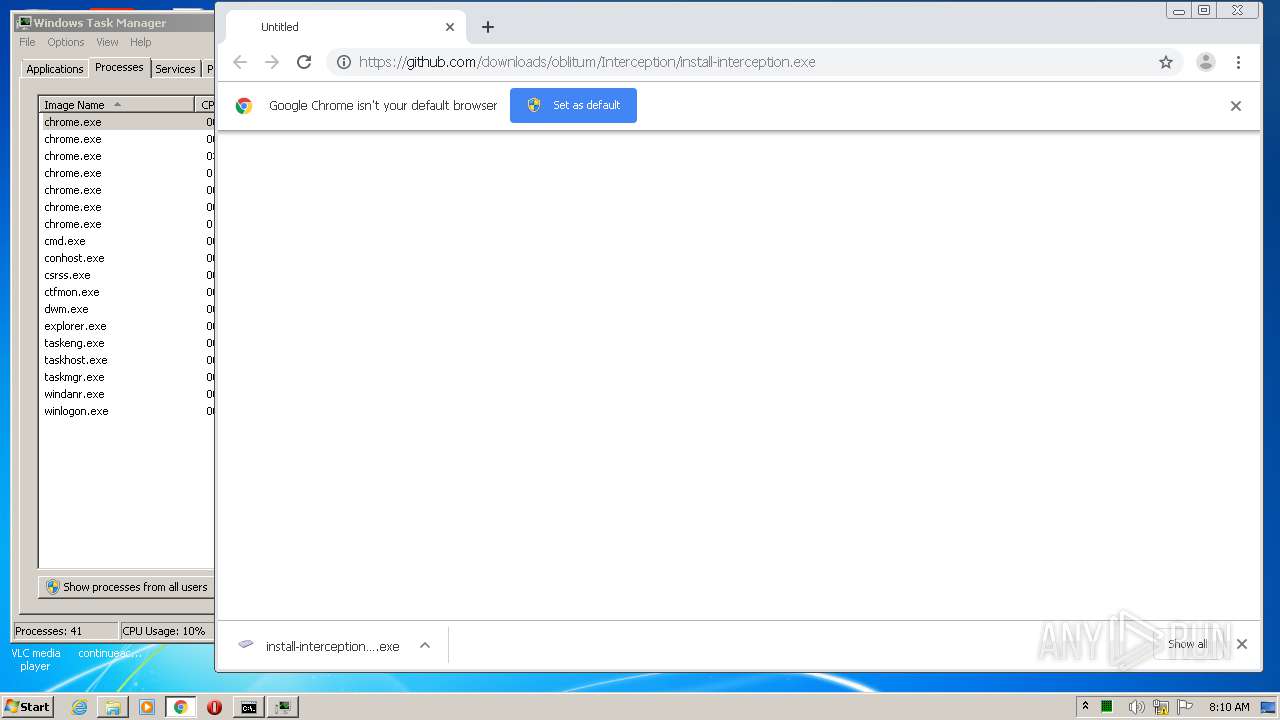
| URL: | https://github.com/downloads/oblitum/Interception/install-interception.exe |
| Full analysis: | https://app.any.run/tasks/ac9b8975-f7b9-494f-9af3-79c6578a6422 |
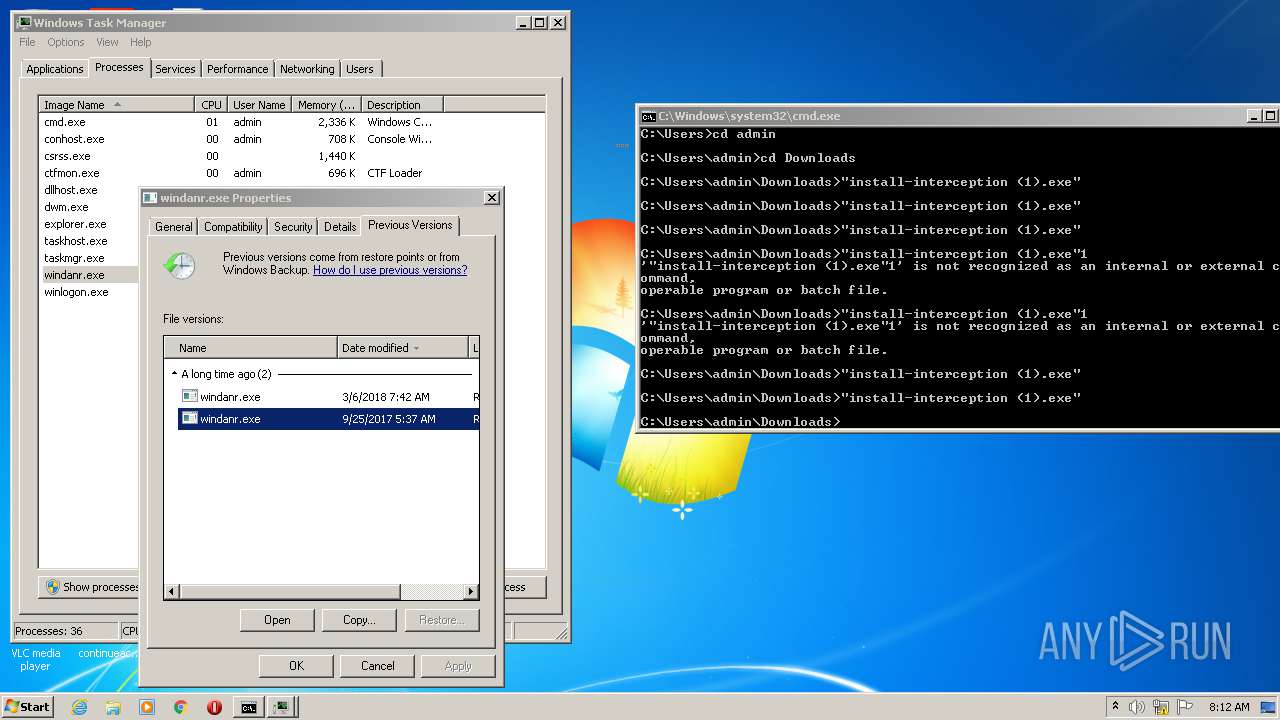
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2020, 07:07:42 |
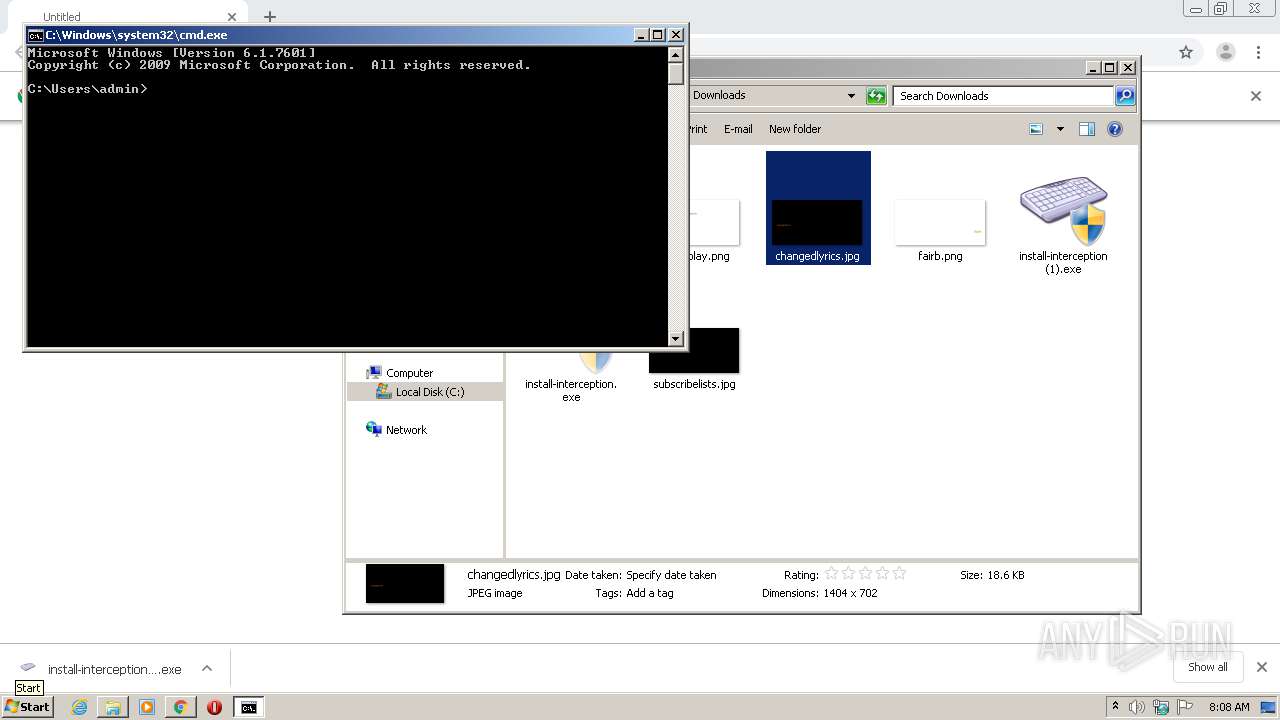
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 251A792B522C08D3885F954773B411AD |
| SHA1: | 79BCEB600690D212639EFF021549FDF3621F99A9 |
| SHA256: | BF8A16AD5C5BF4E921B8AF5B2DA0CD4CC55A2DCD2A346A19181D6A49CA693BB5 |
| SSDEEP: | 3:N8tEdxKXKcC2IKsgxLKDgGMLRqVxLLNn:2uKacCvwxVGKqVx/N |
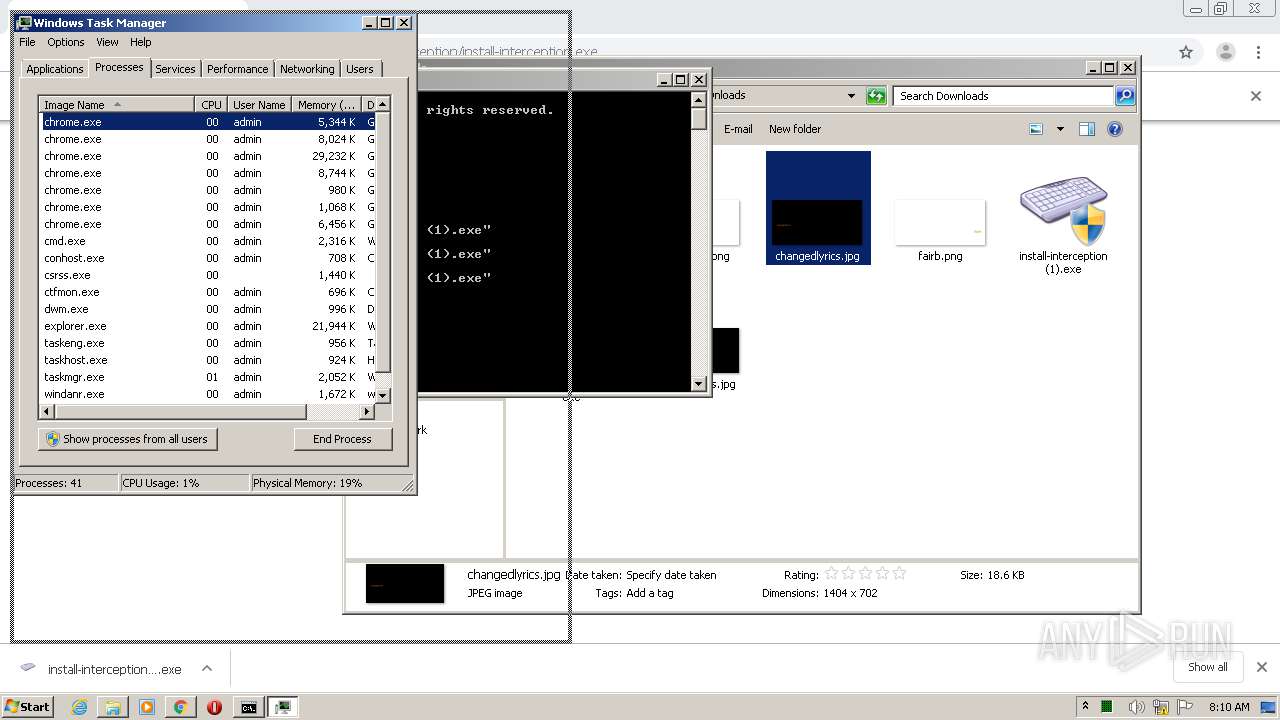
MALICIOUS
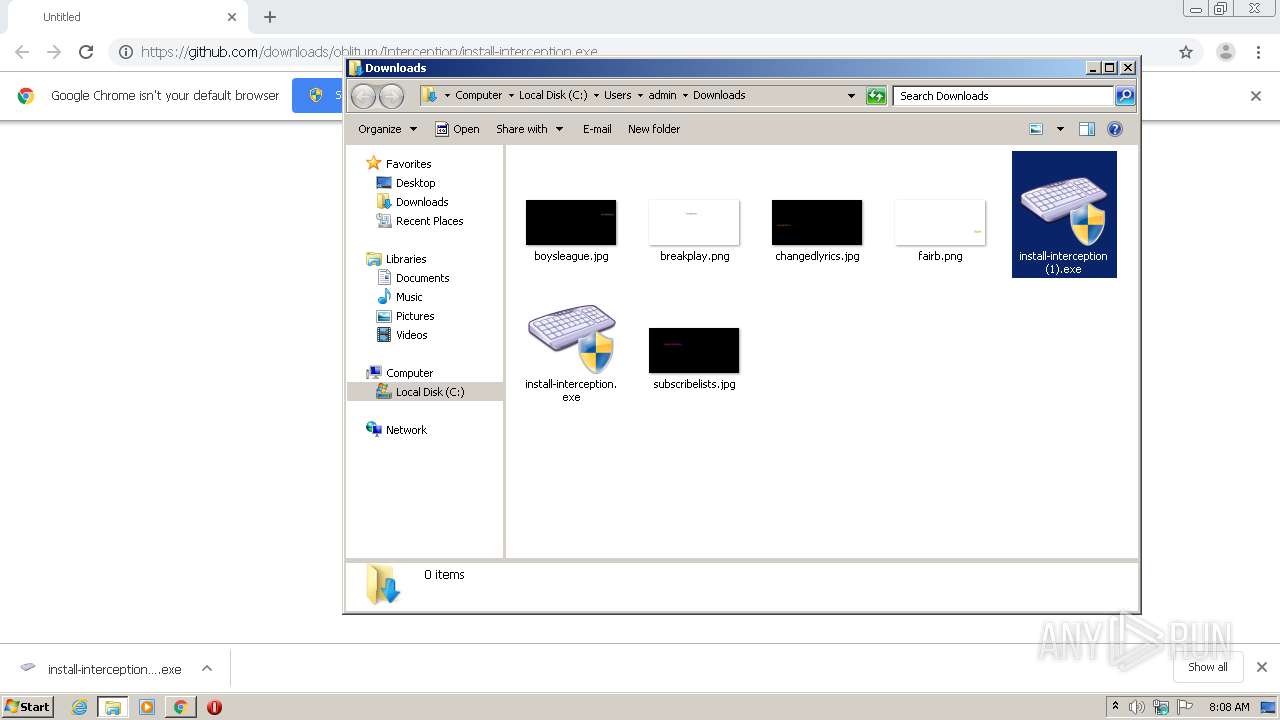
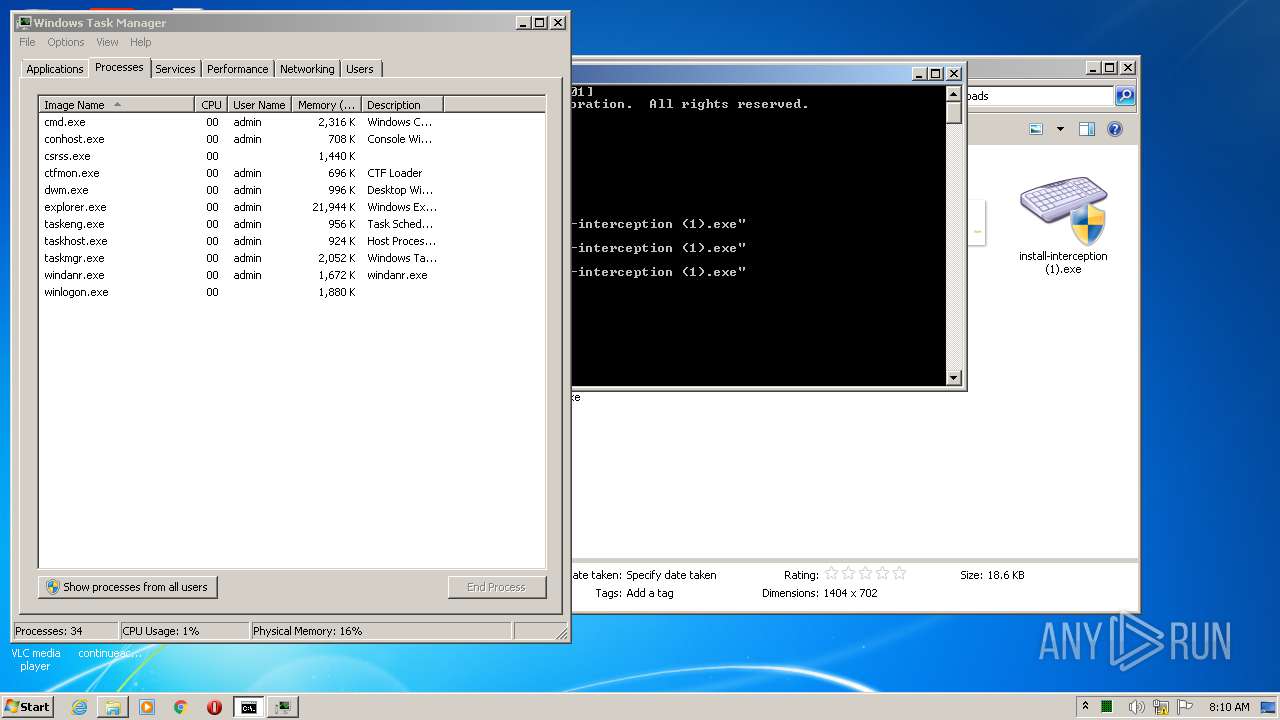
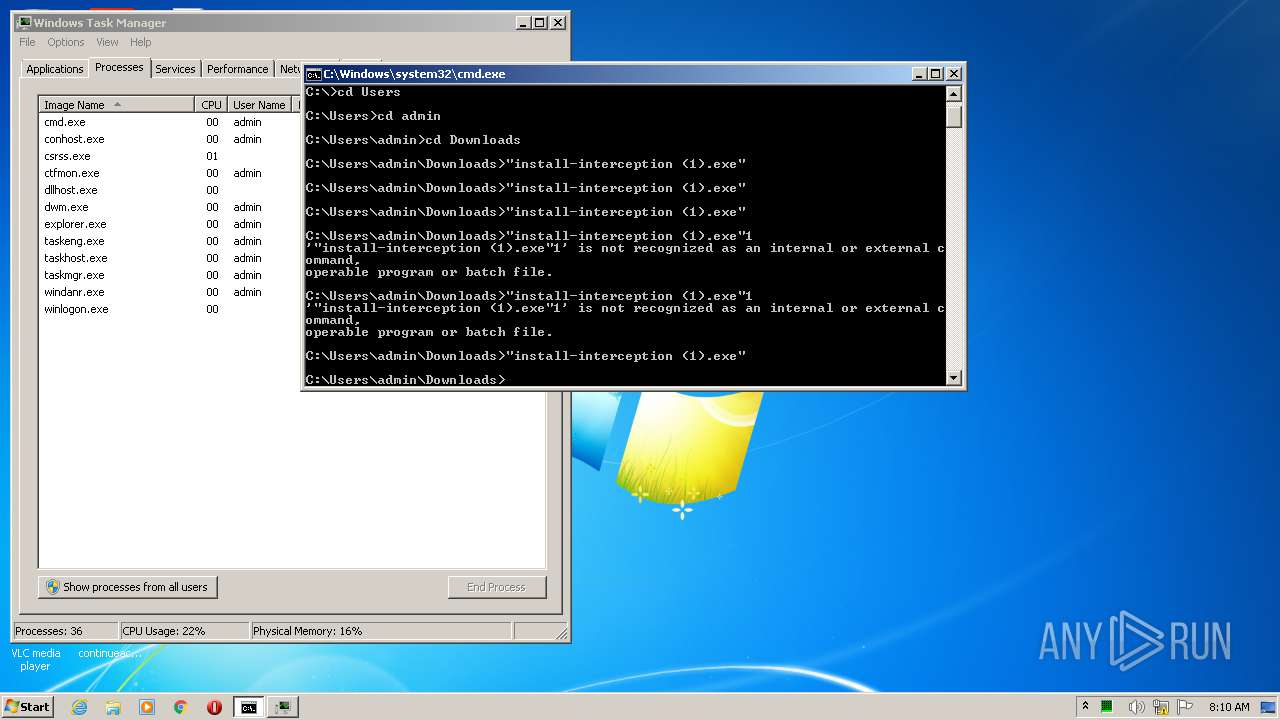
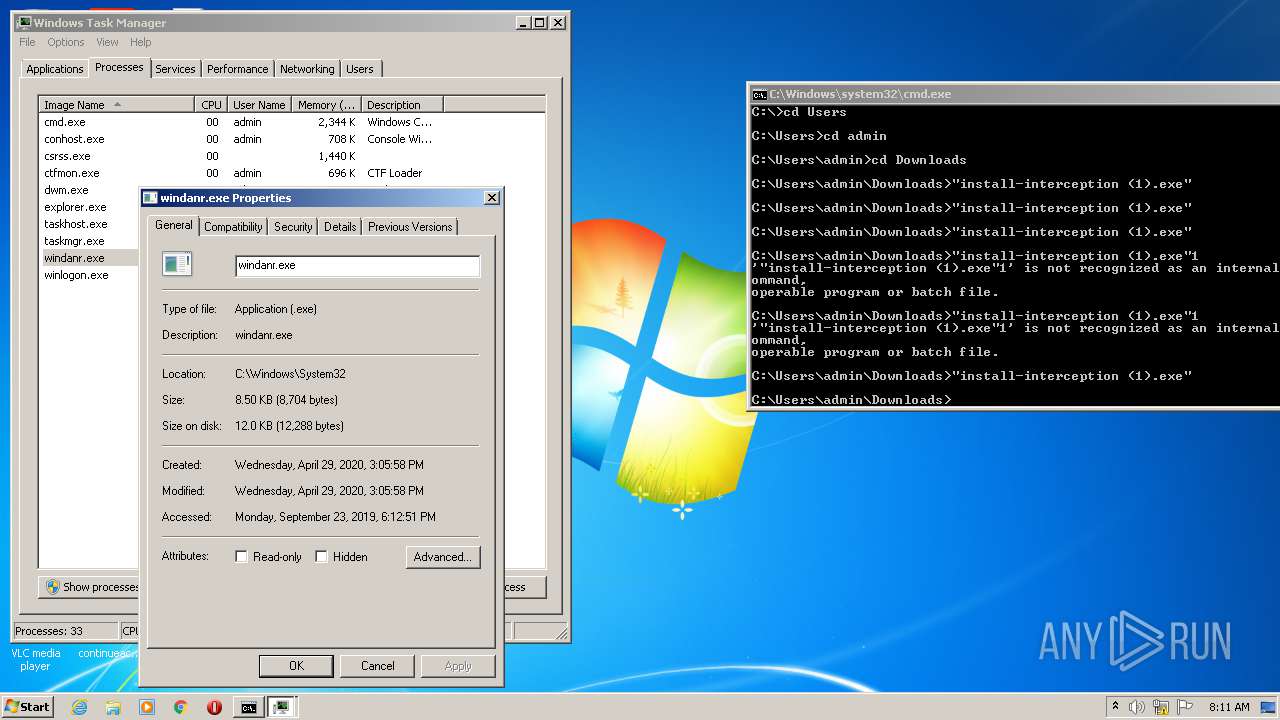
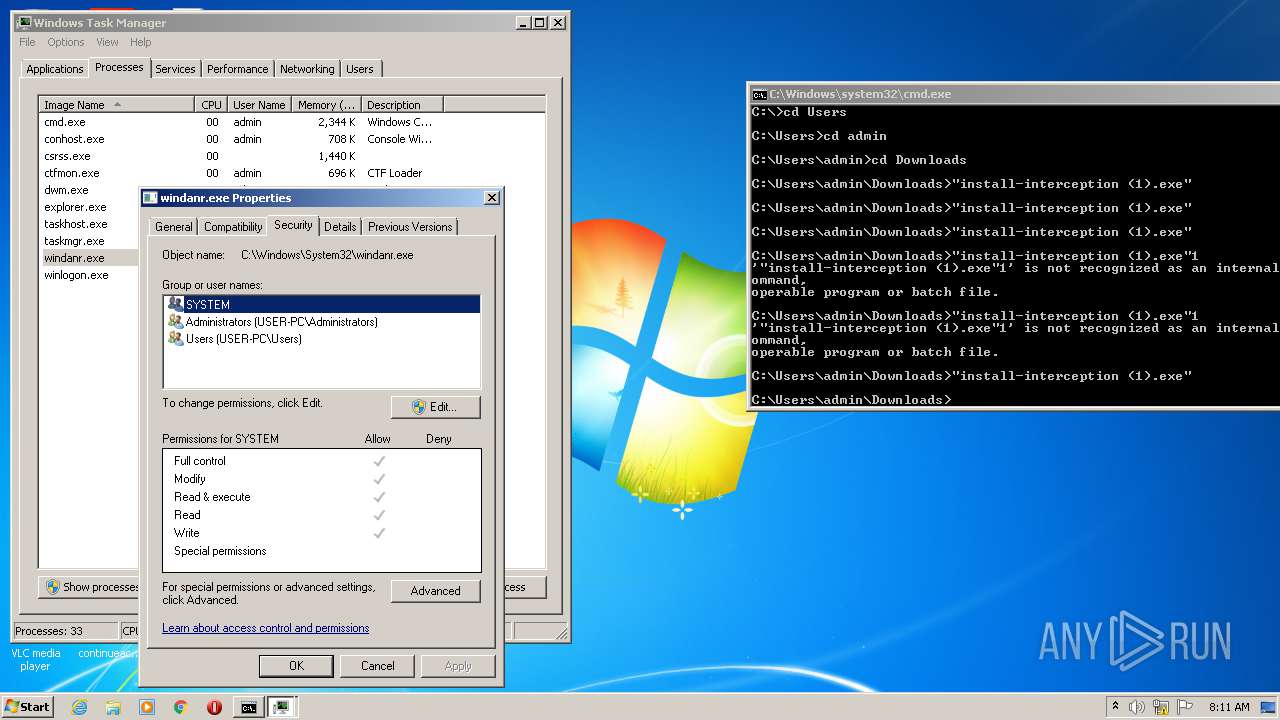
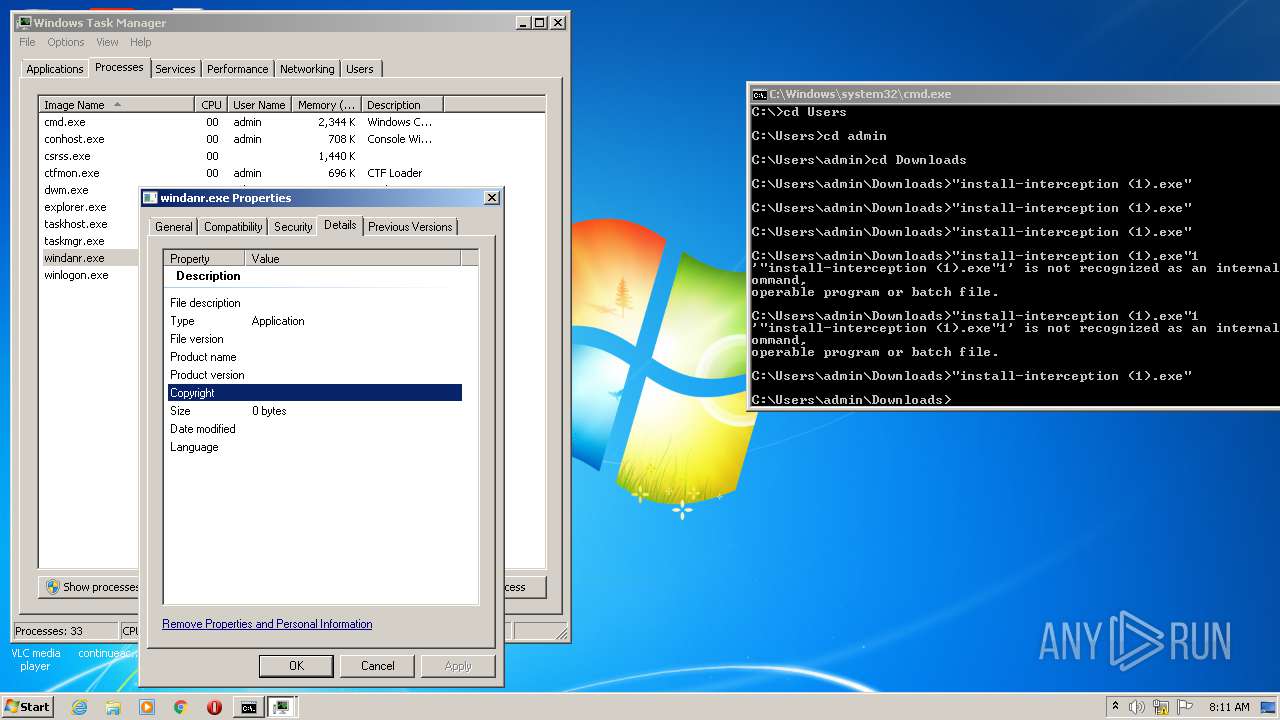
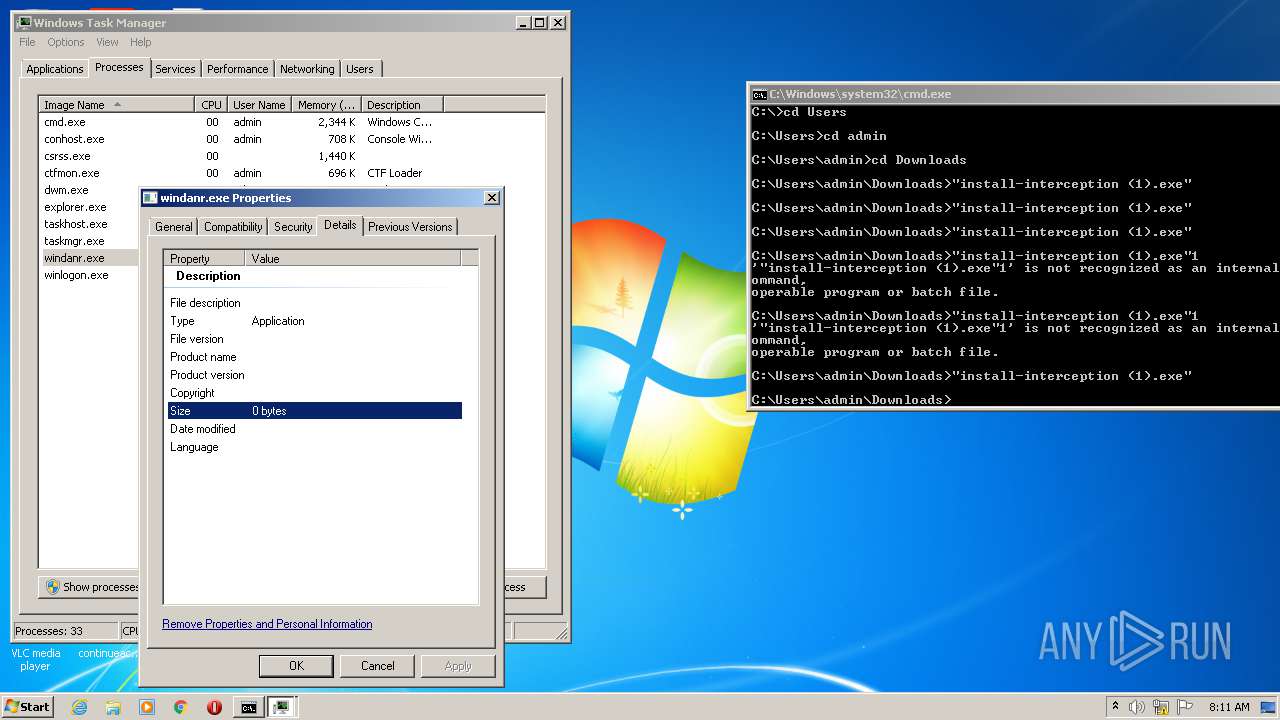
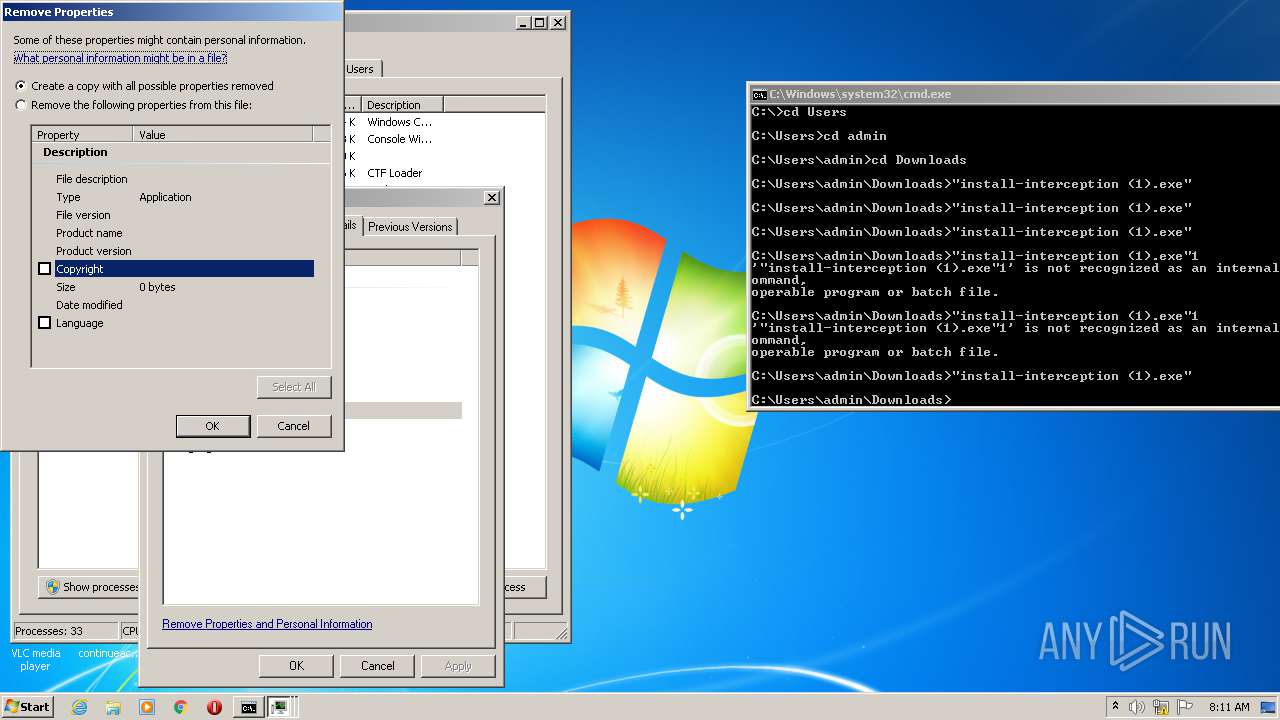
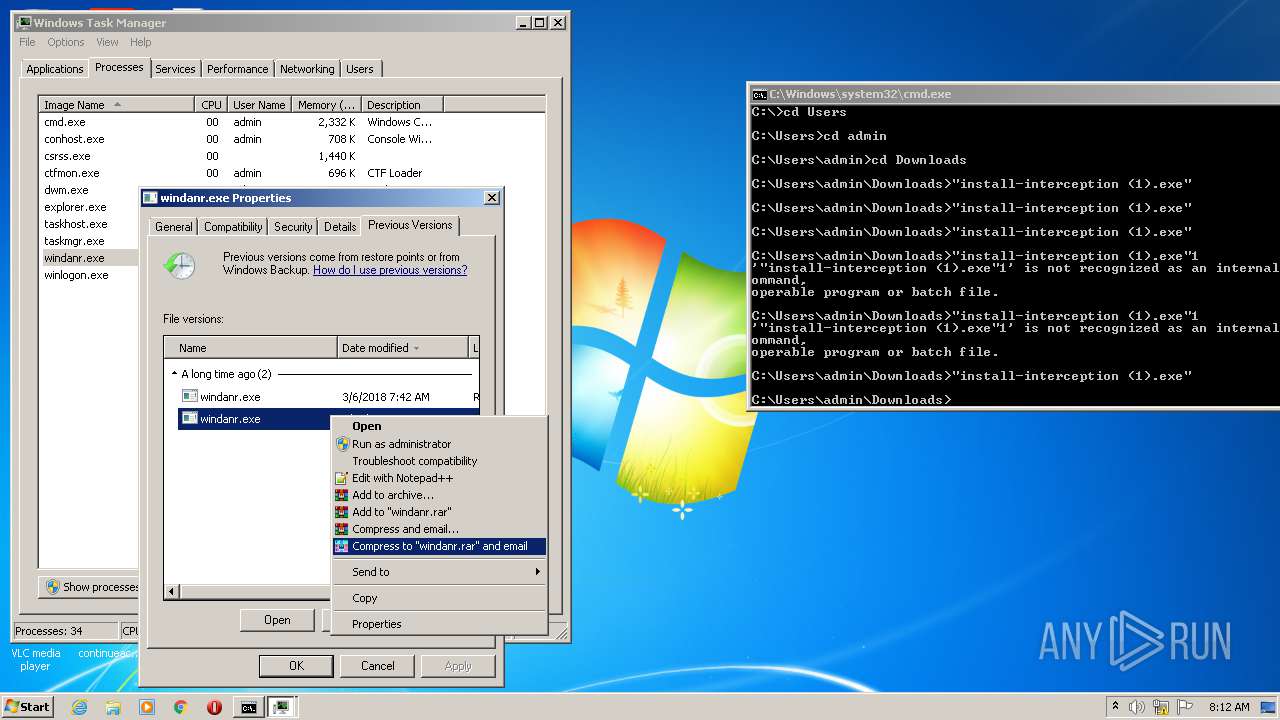
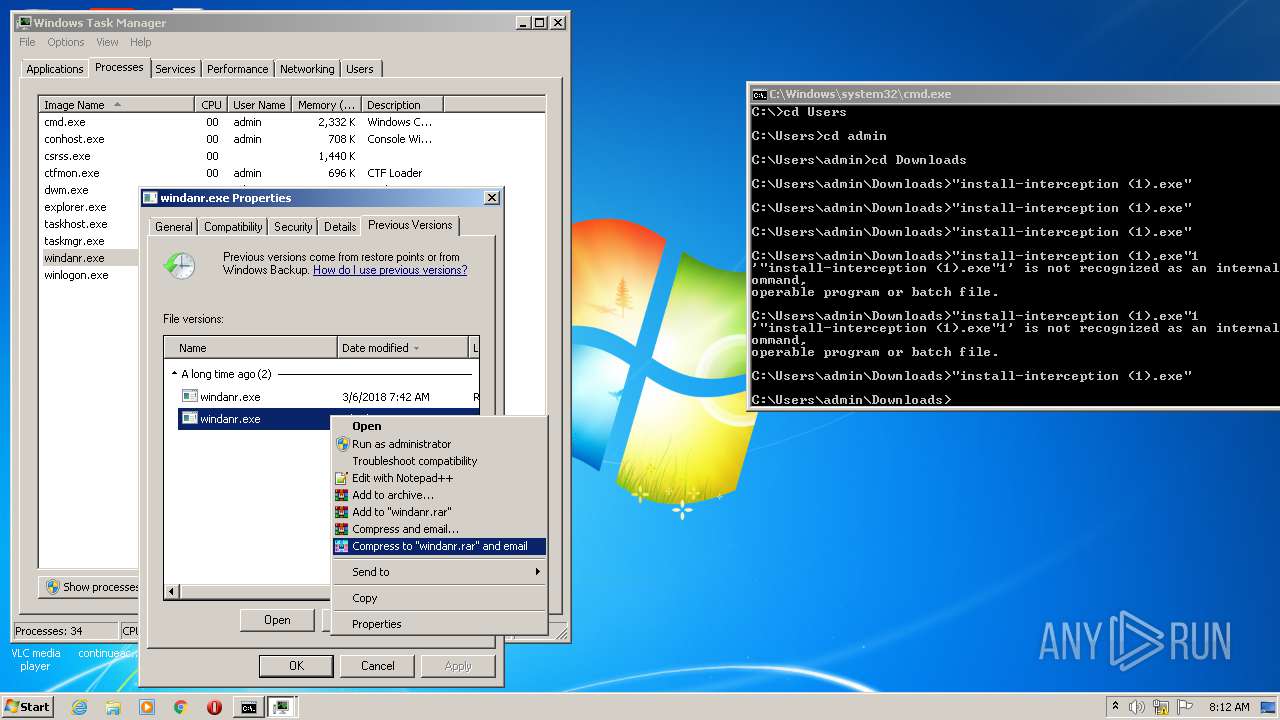
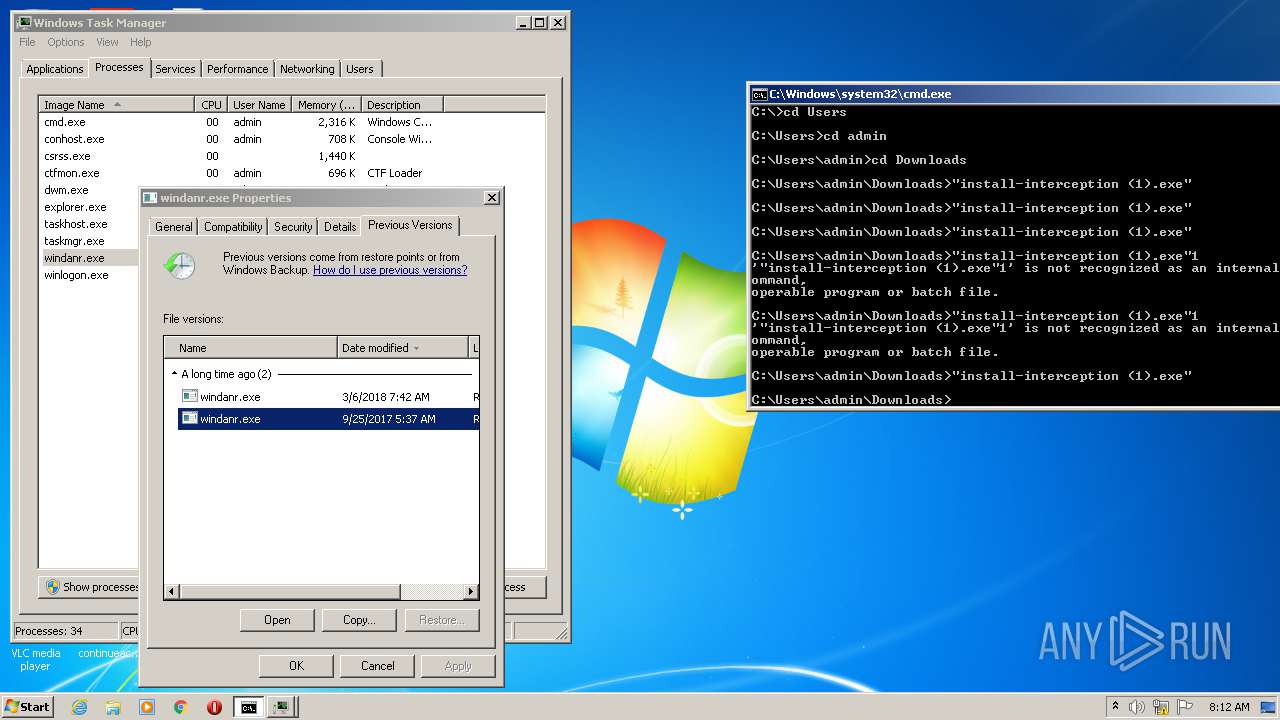
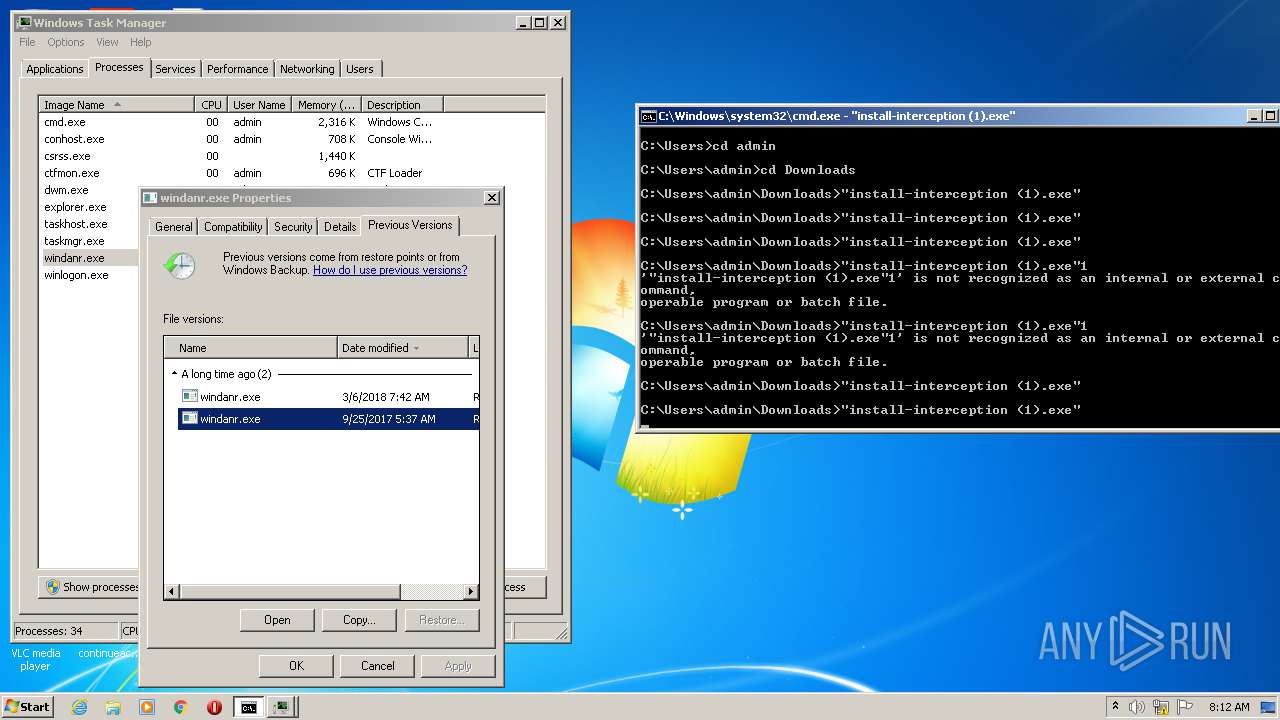
Application was dropped or rewritten from another process
- install-interception (1).exe (PID: 2188)
- install-interception.exe (PID: 4088)
- install-interception.exe (PID: 2720)
- install-interception.exe (PID: 632)
- install-interception (1).exe (PID: 2700)
- install-interception (1).exe (PID: 3668)
- install-interception (1).exe (PID: 4068)
- install-interception (1).exe (PID: 2784)
- install-interception (1).exe (PID: 788)
- install-interception (1).exe (PID: 3956)
- install-interception (1).exe (PID: 3384)
- install-interception (1).exe (PID: 1464)
- install-interception (1).exe (PID: 3580)
- install-interception (1).exe (PID: 3820)
- install-interception (1).exe (PID: 4092)
- install-interception (1).exe (PID: 3412)
- install-interception.exe (PID: 3800)
- install-interception (1).exe (PID: 3900)
- install-interception (1).exe (PID: 2076)
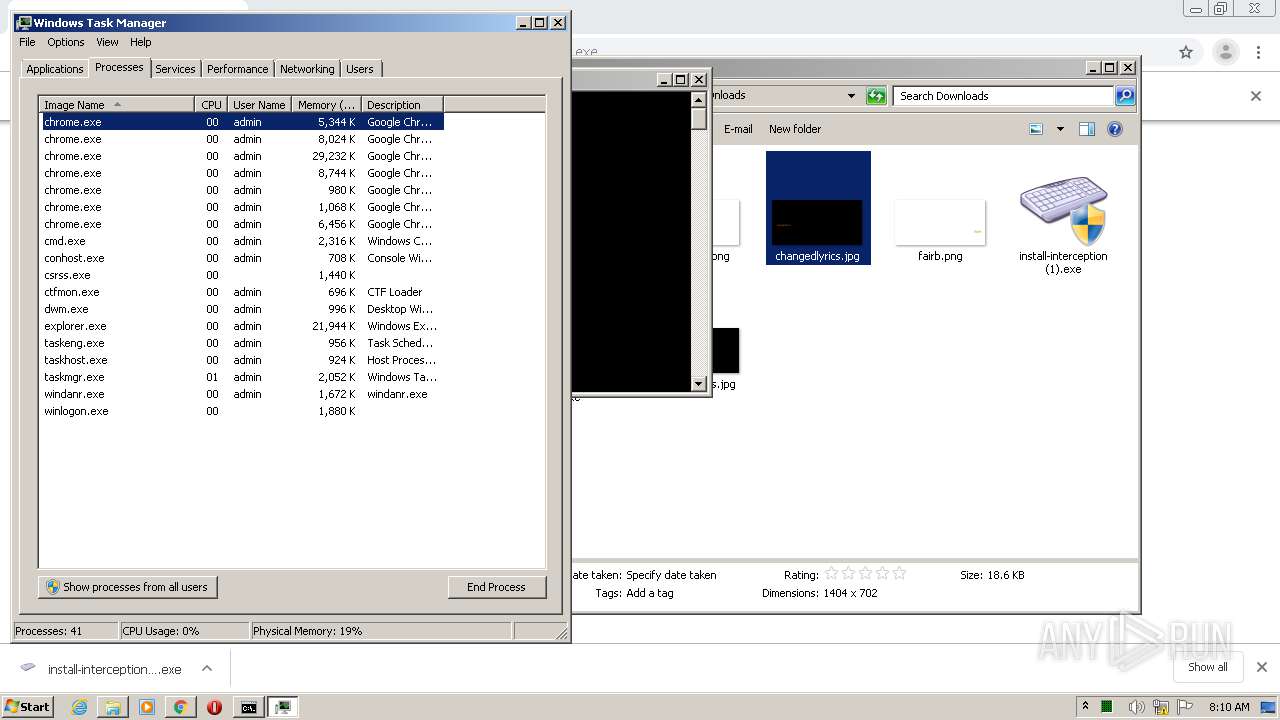
SUSPICIOUS
Executable content was dropped or overwritten
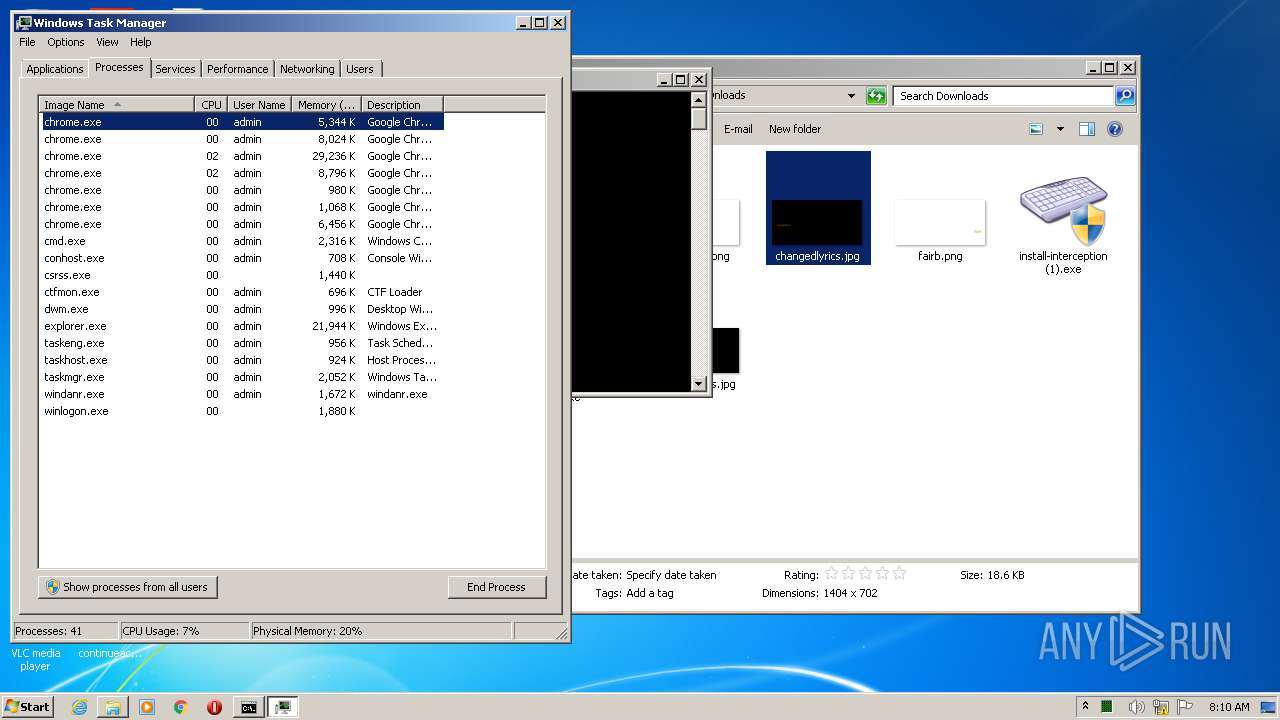
- chrome.exe (PID: 1420)
- chrome.exe (PID: 956)
INFO
Reads the hosts file
- chrome.exe (PID: 1420)
- chrome.exe (PID: 956)
Application launched itself
- chrome.exe (PID: 1420)
Reads Internet Cache Settings
- chrome.exe (PID: 1420)
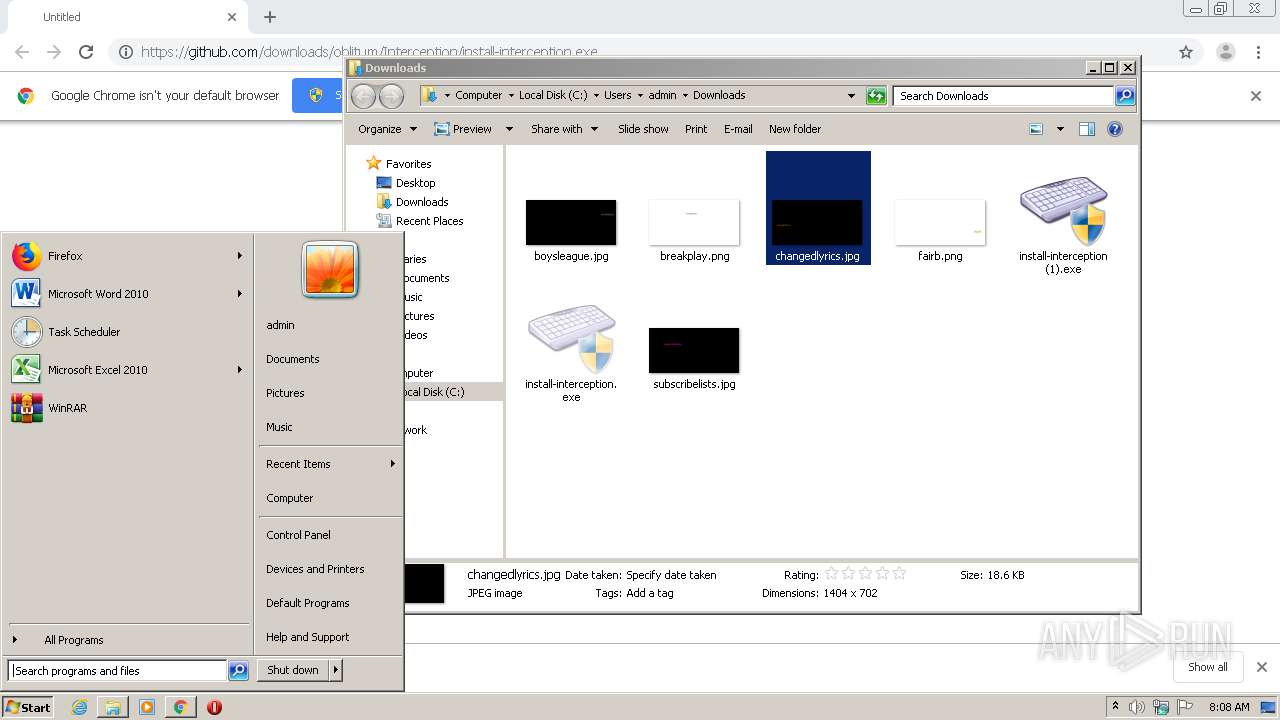
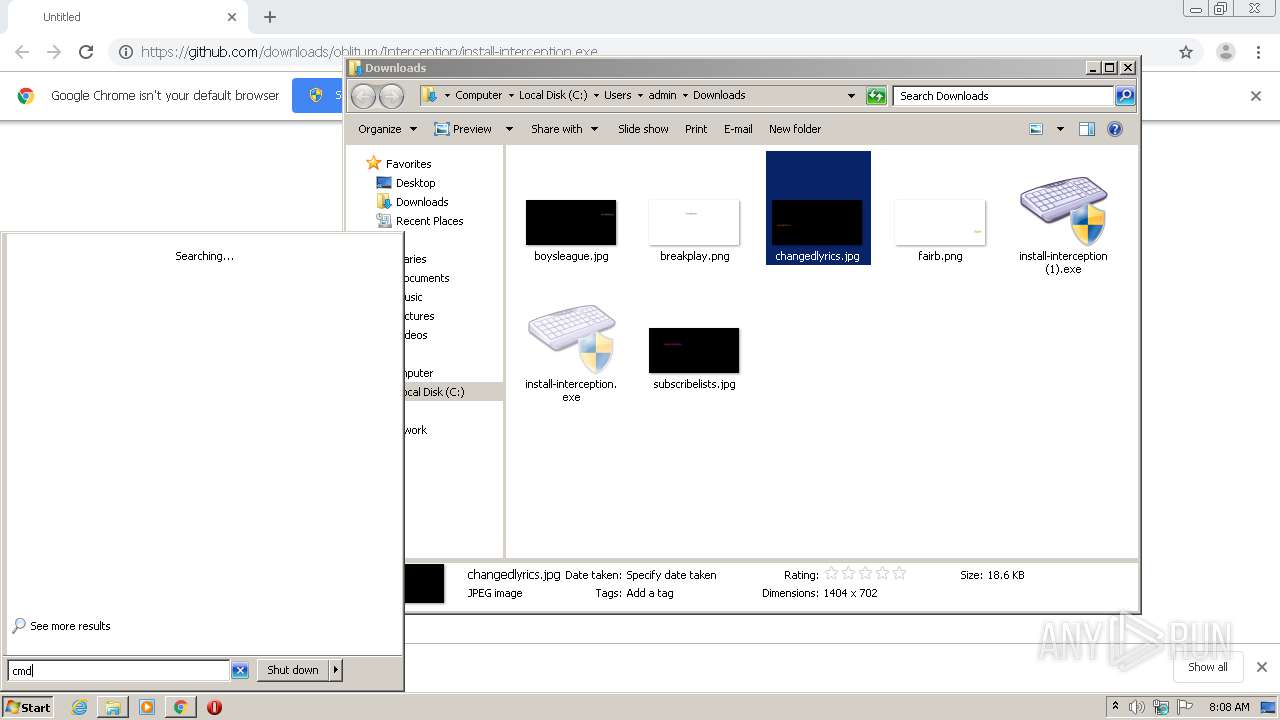
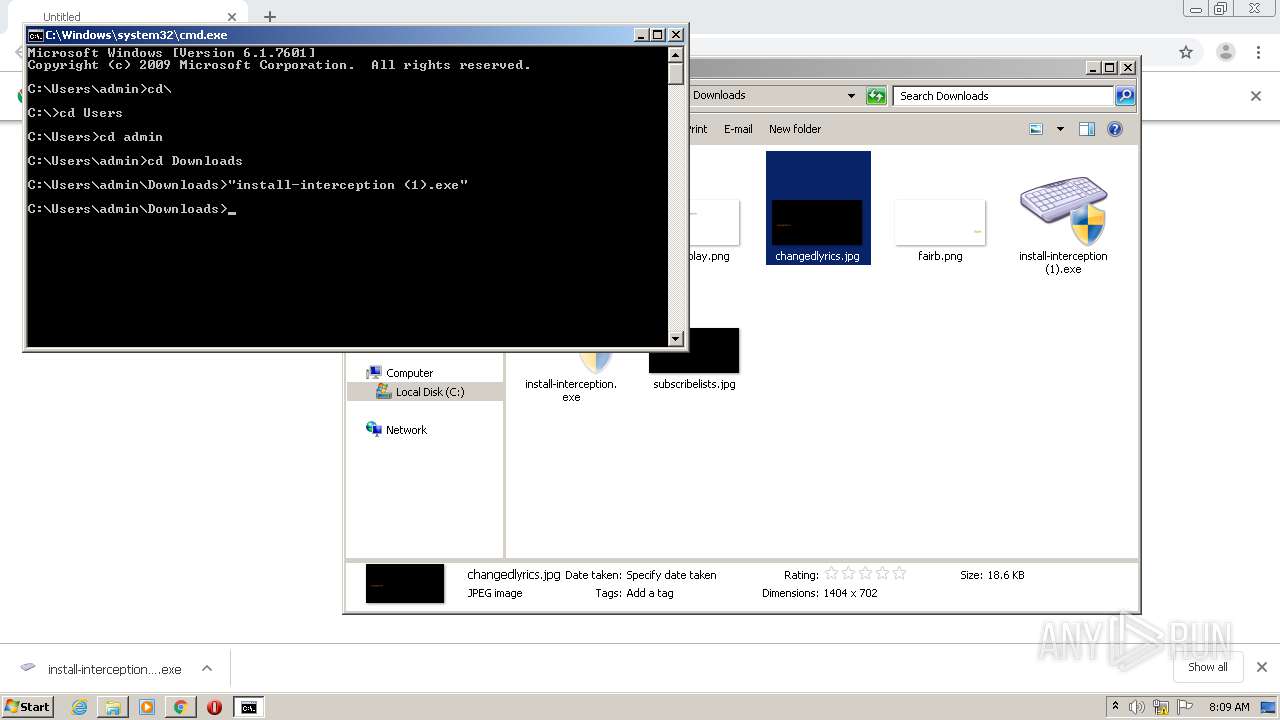
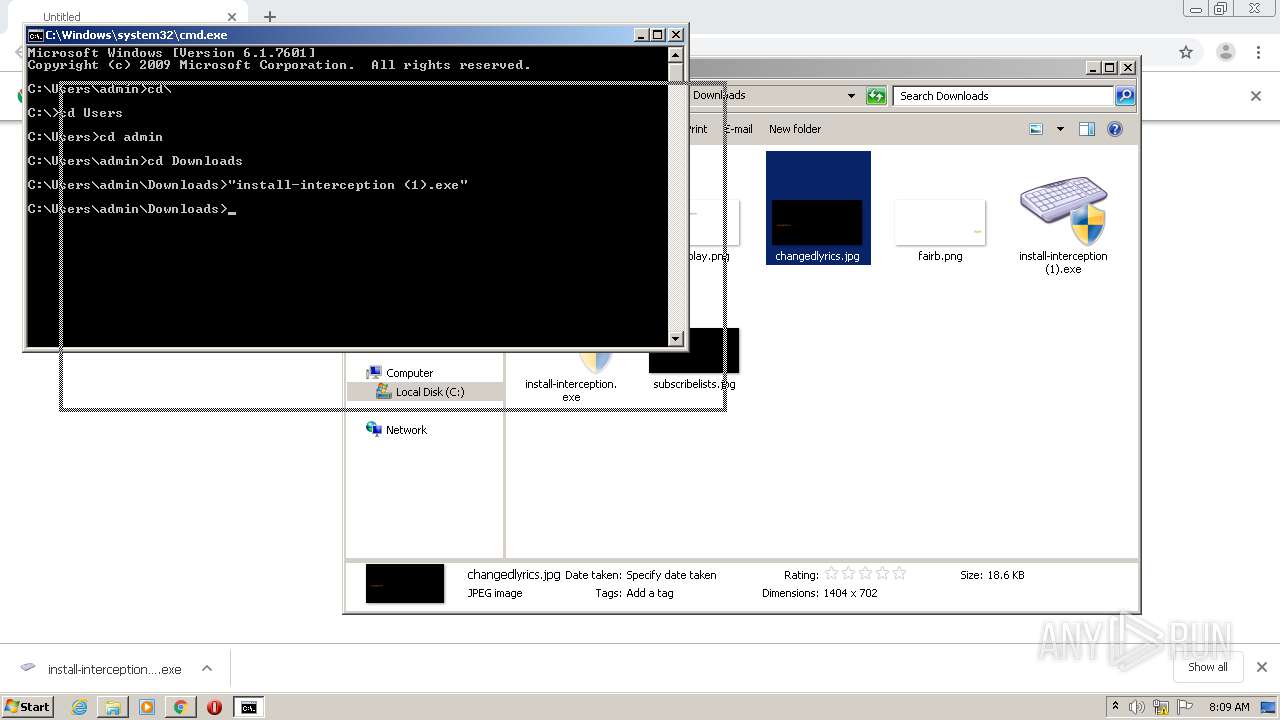
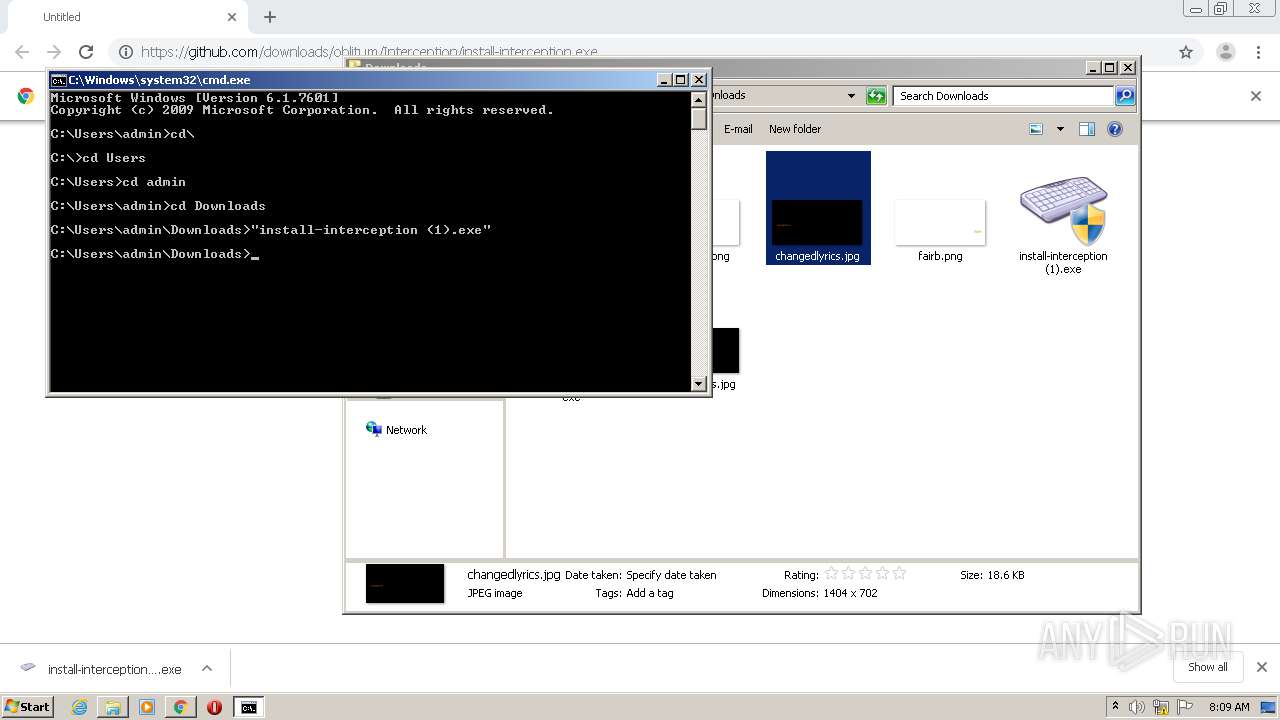
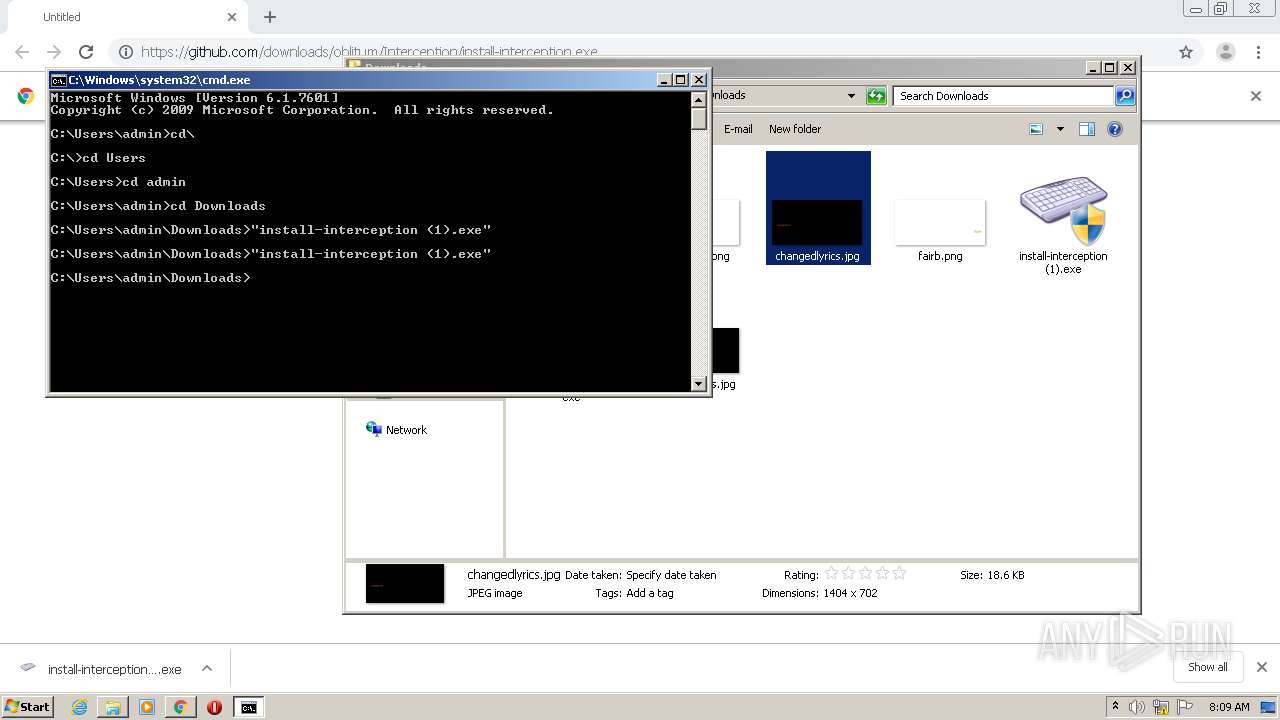
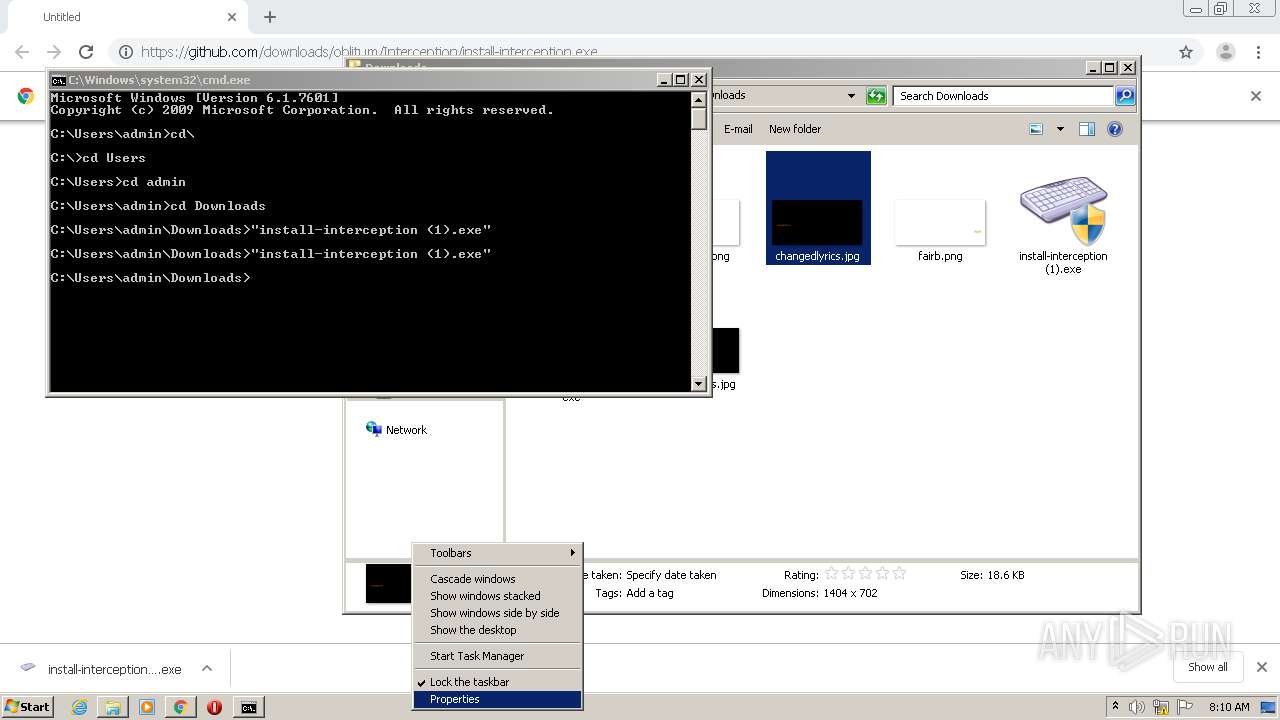
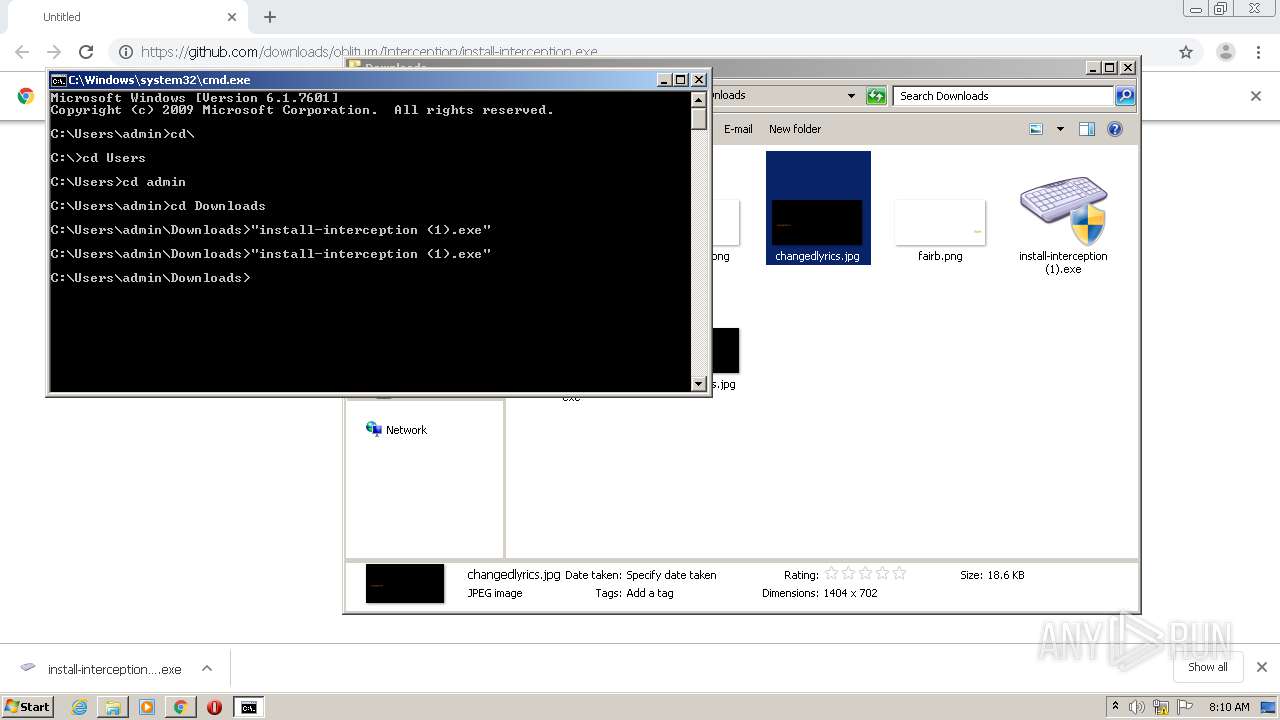
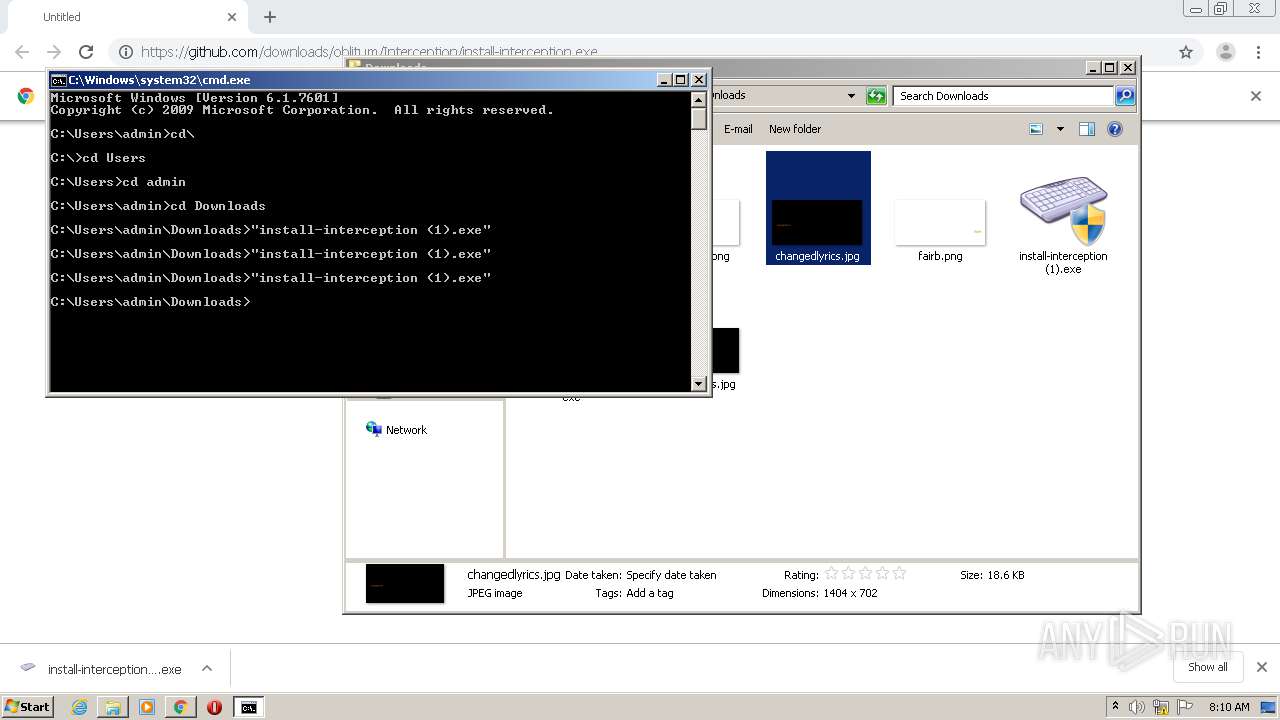
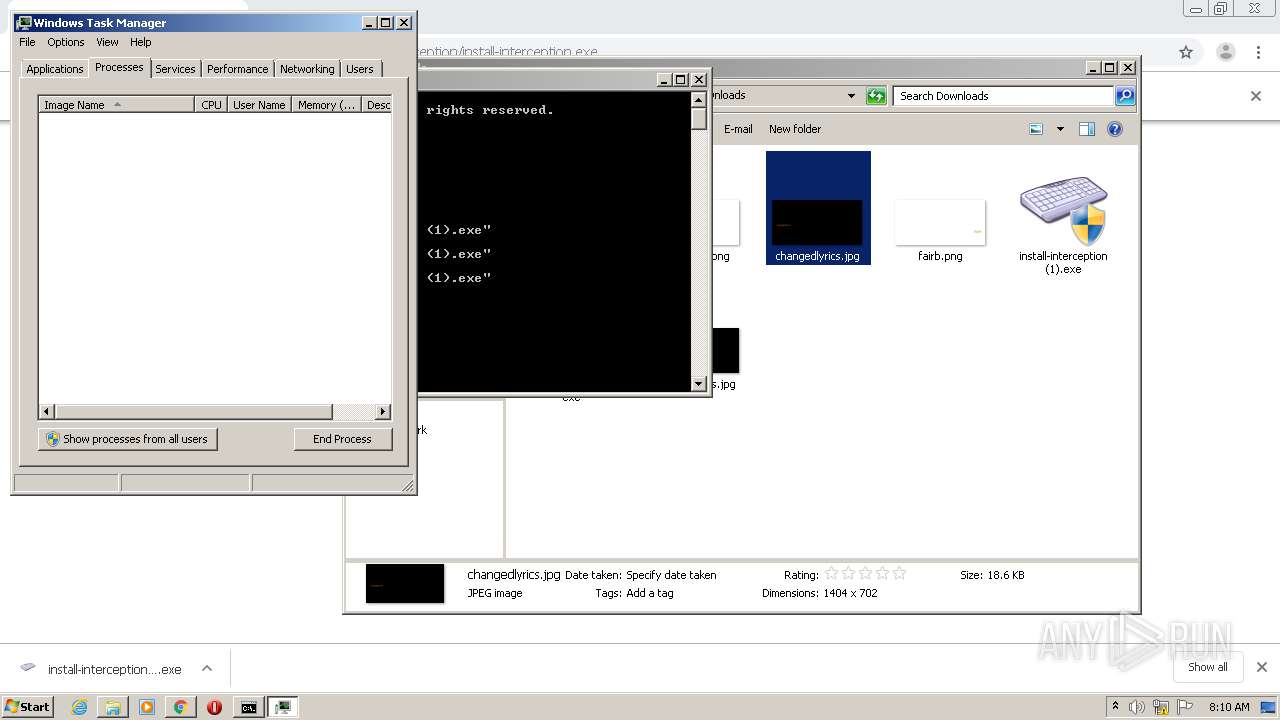
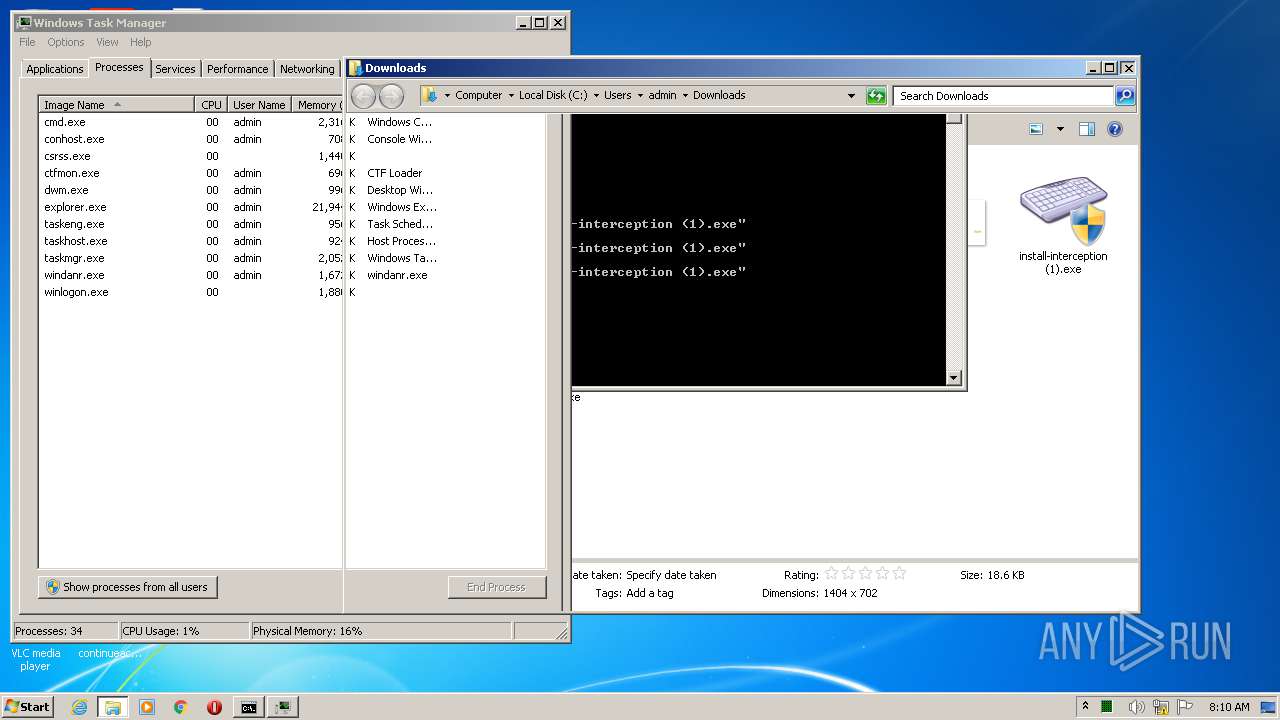
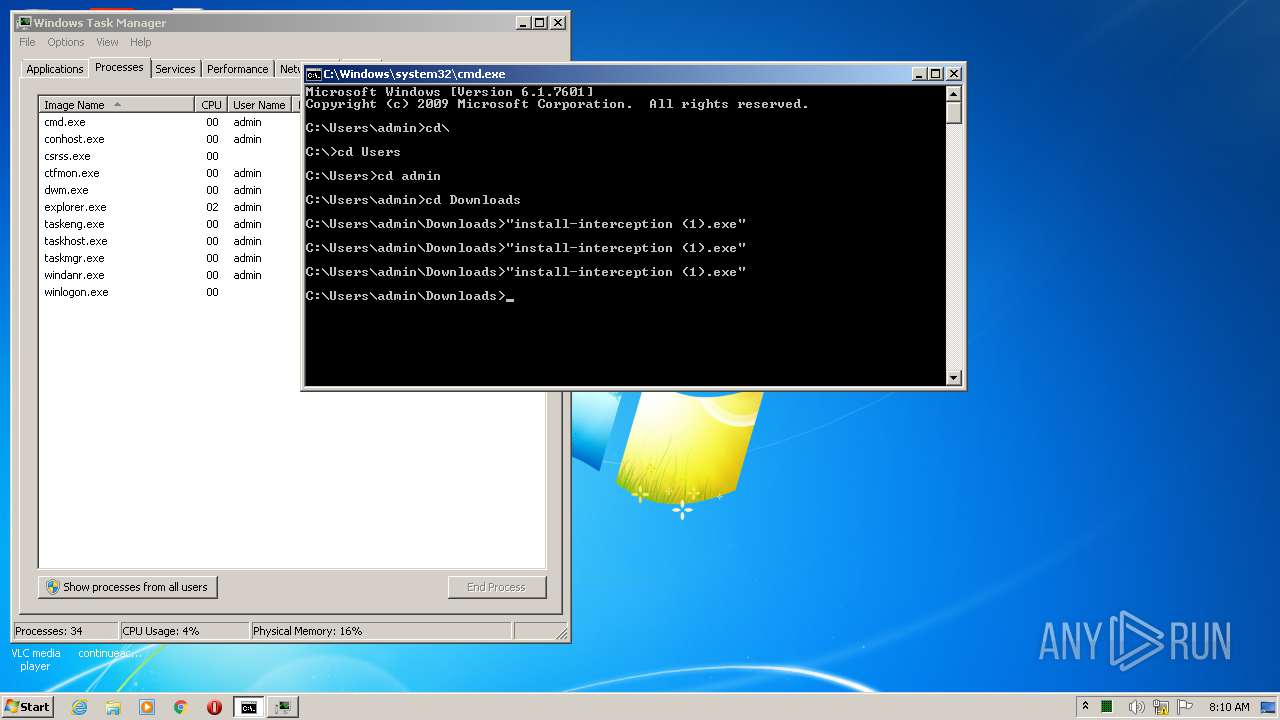
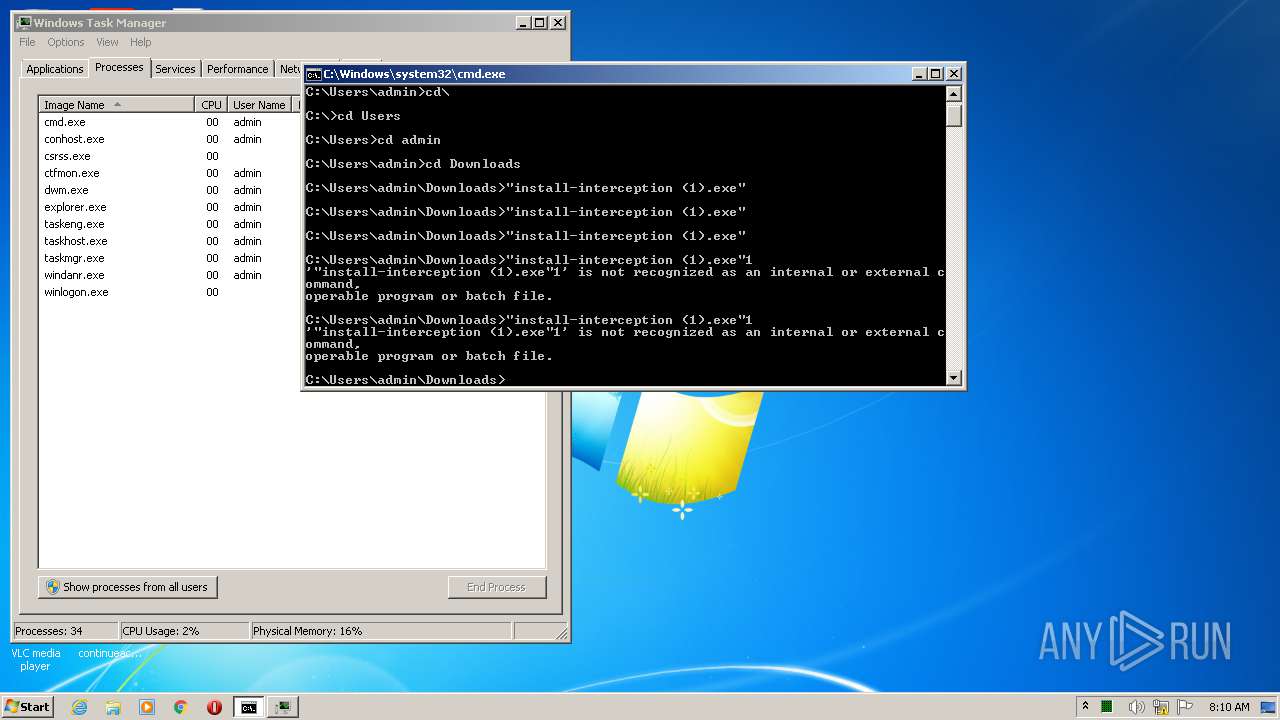
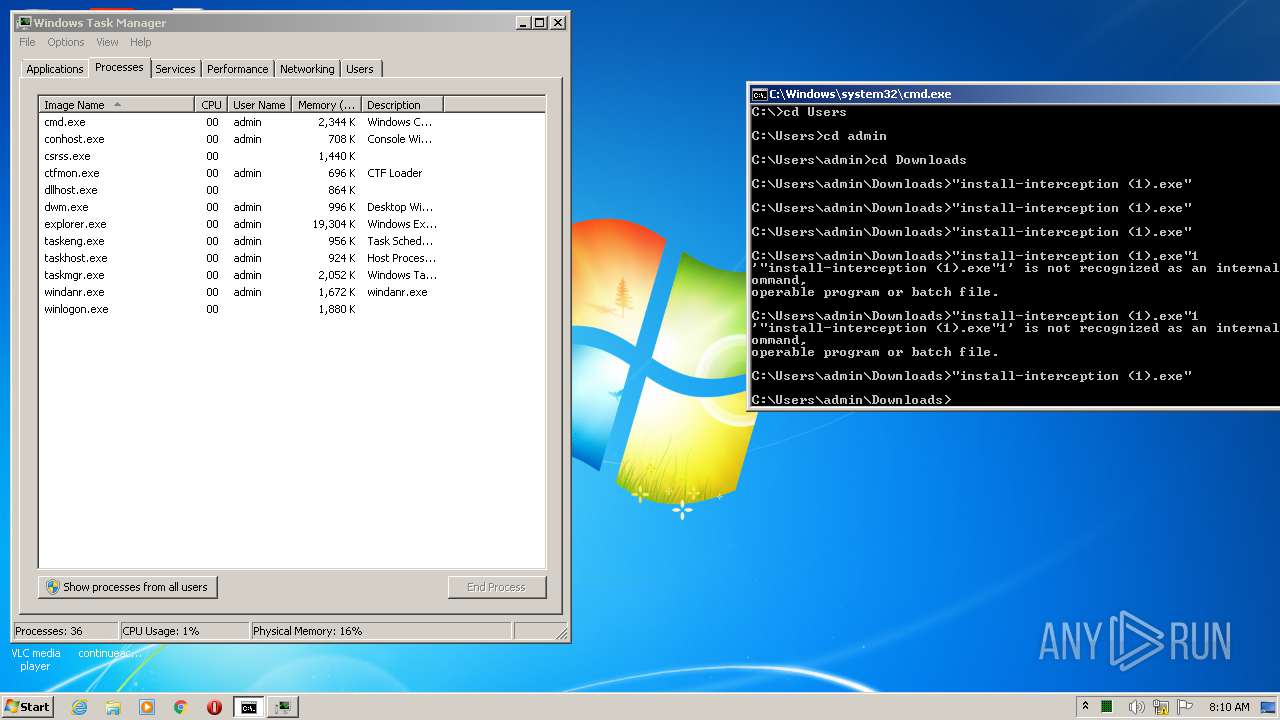
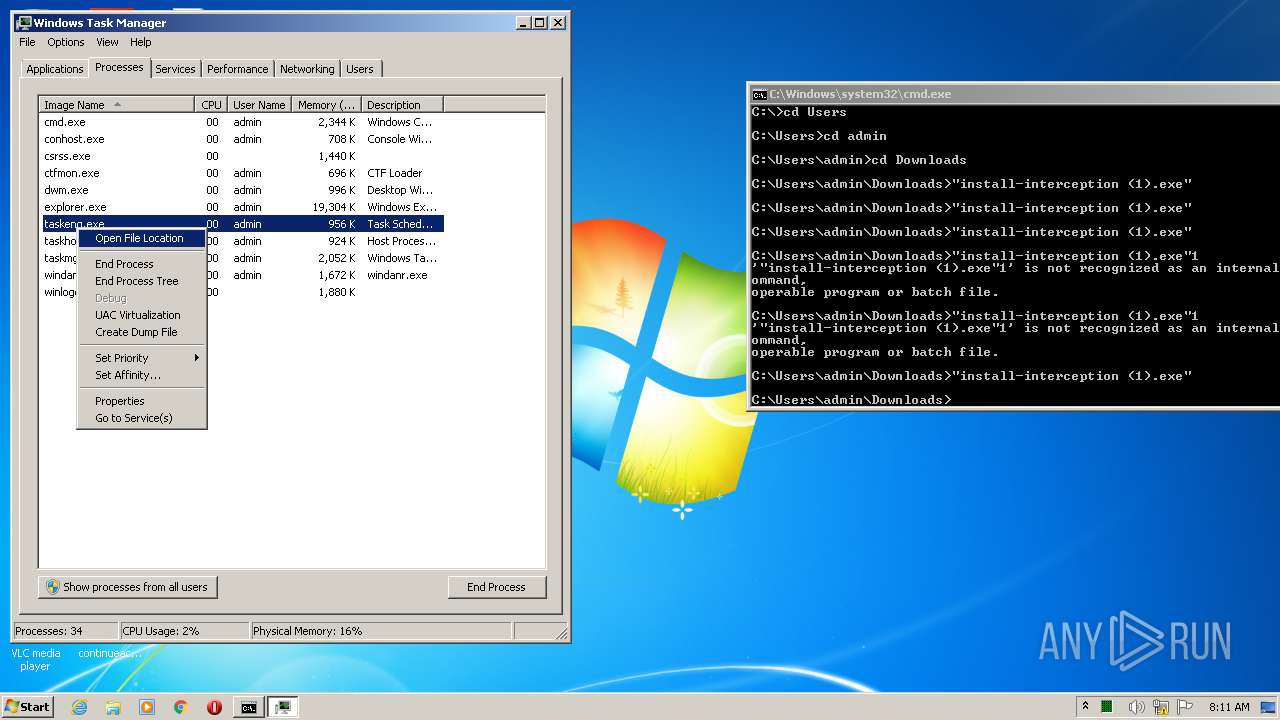
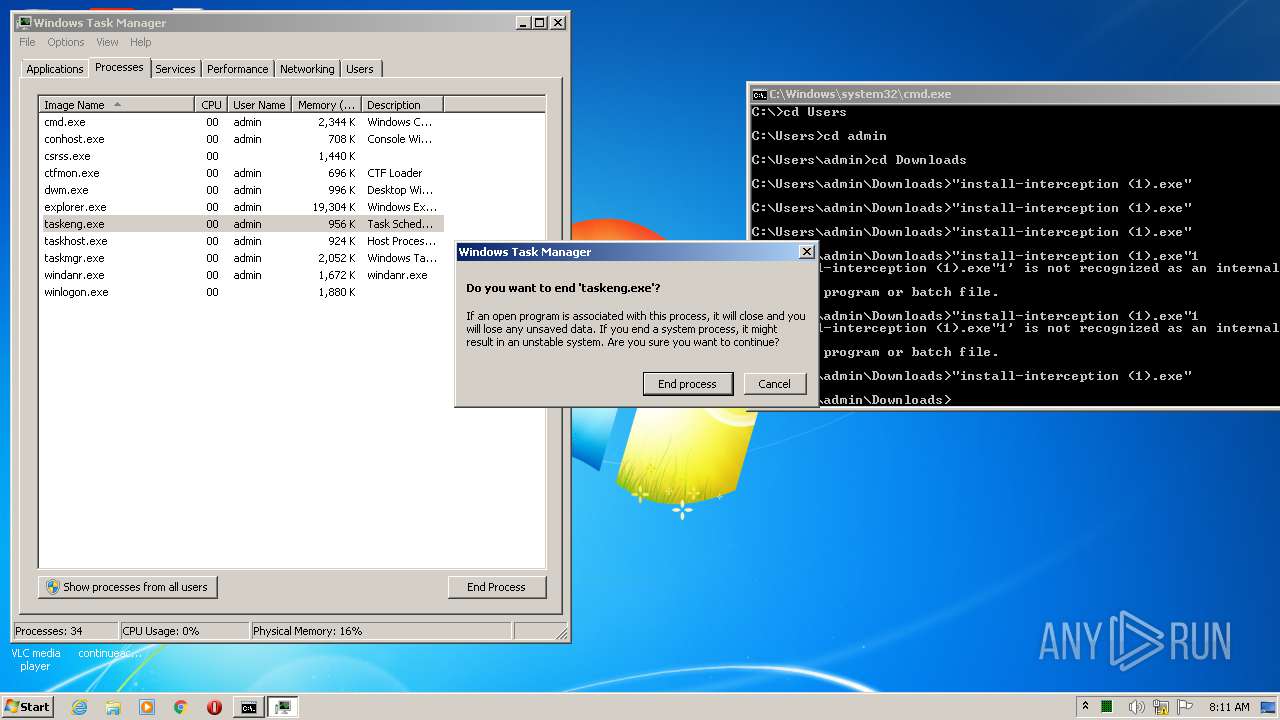
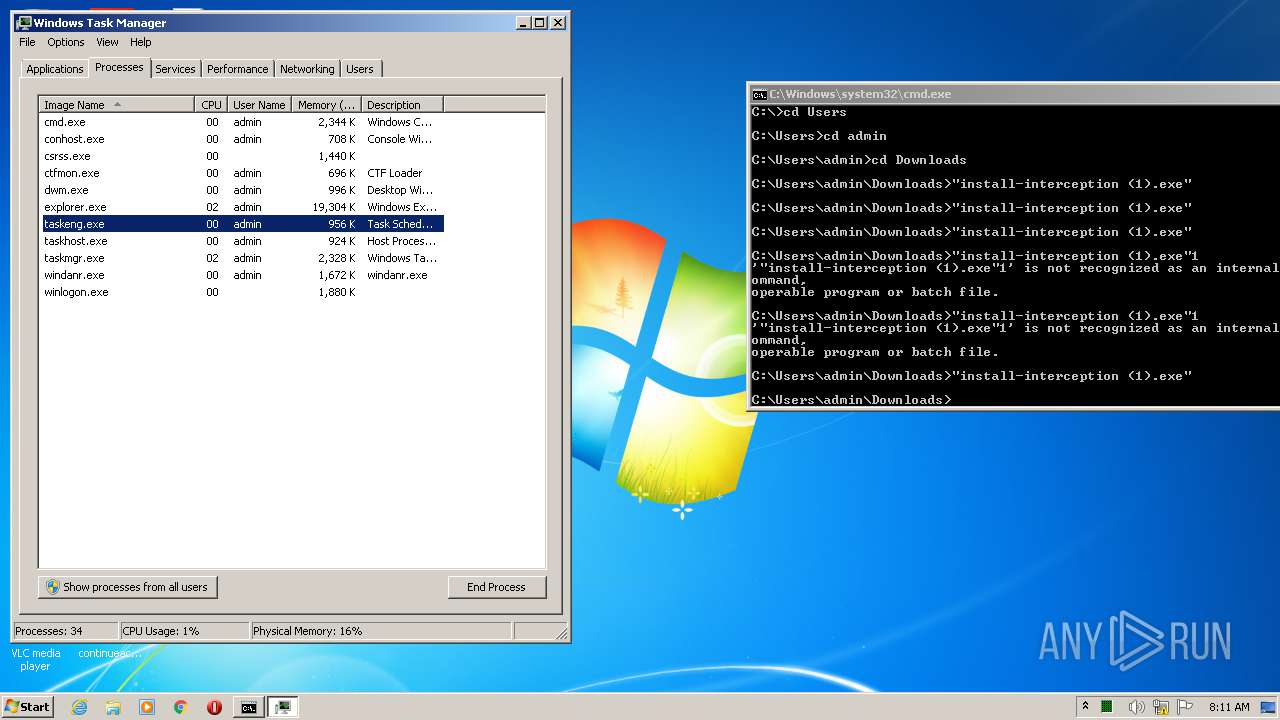
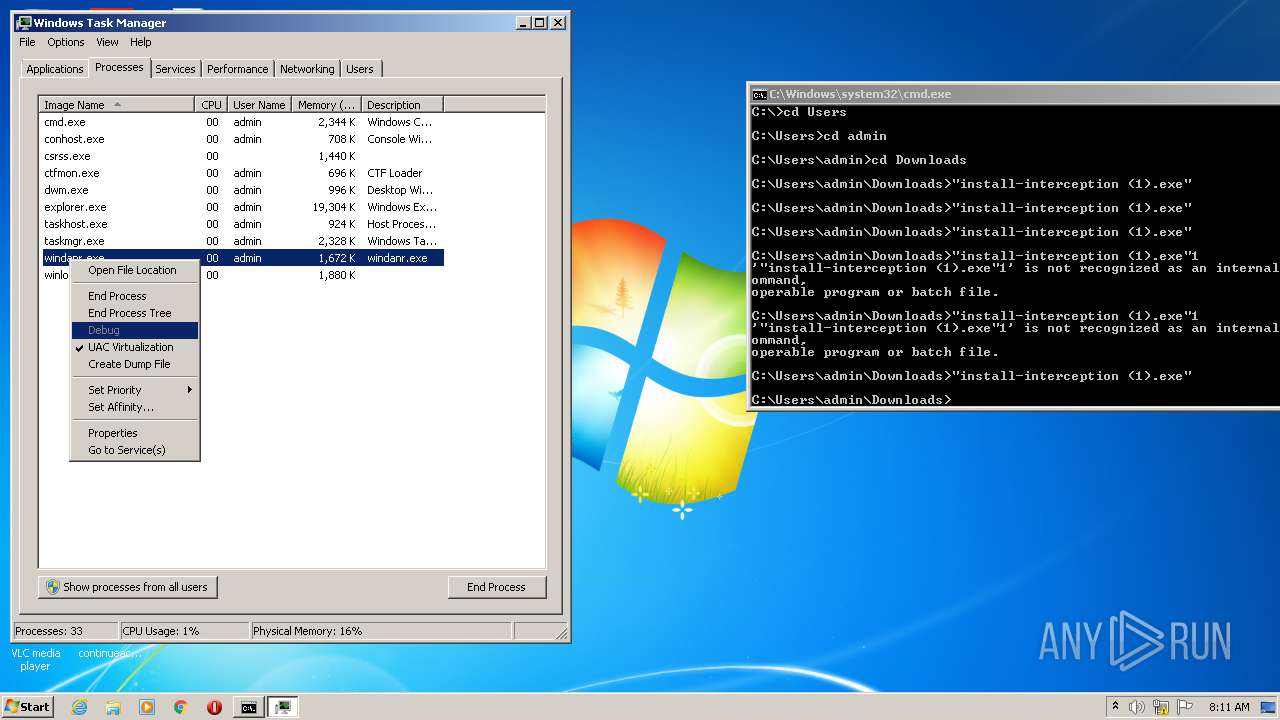
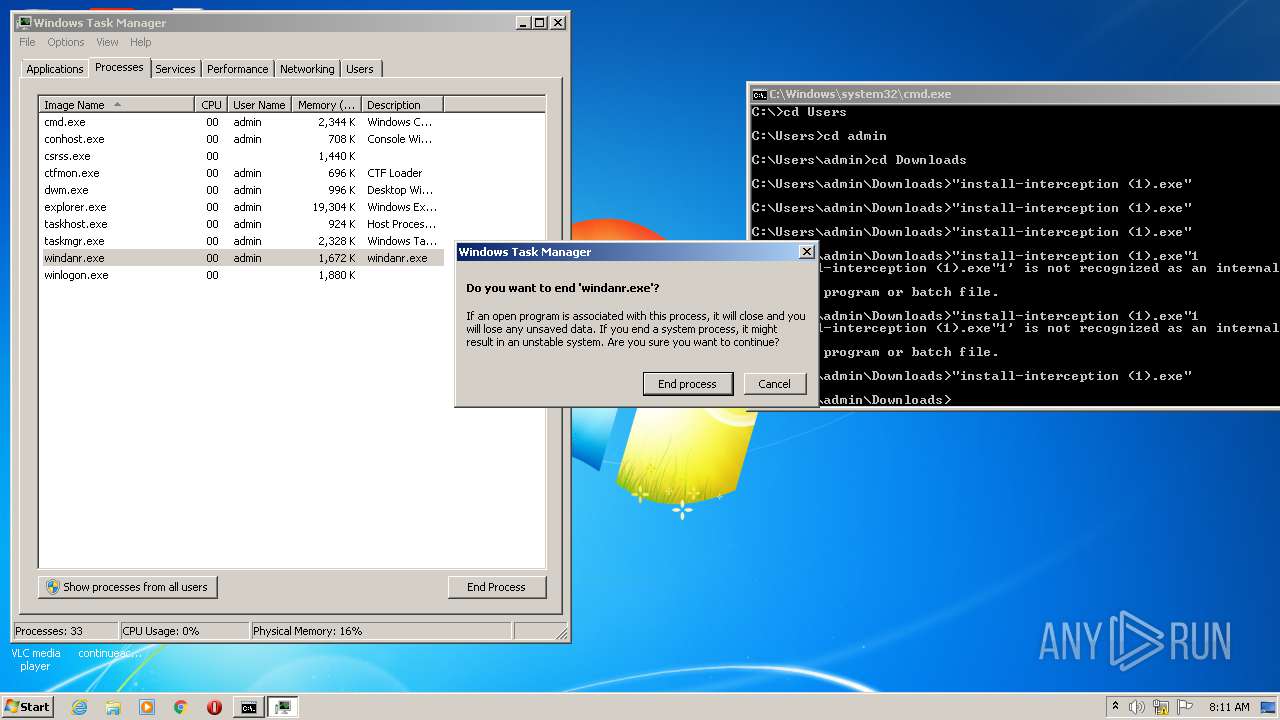
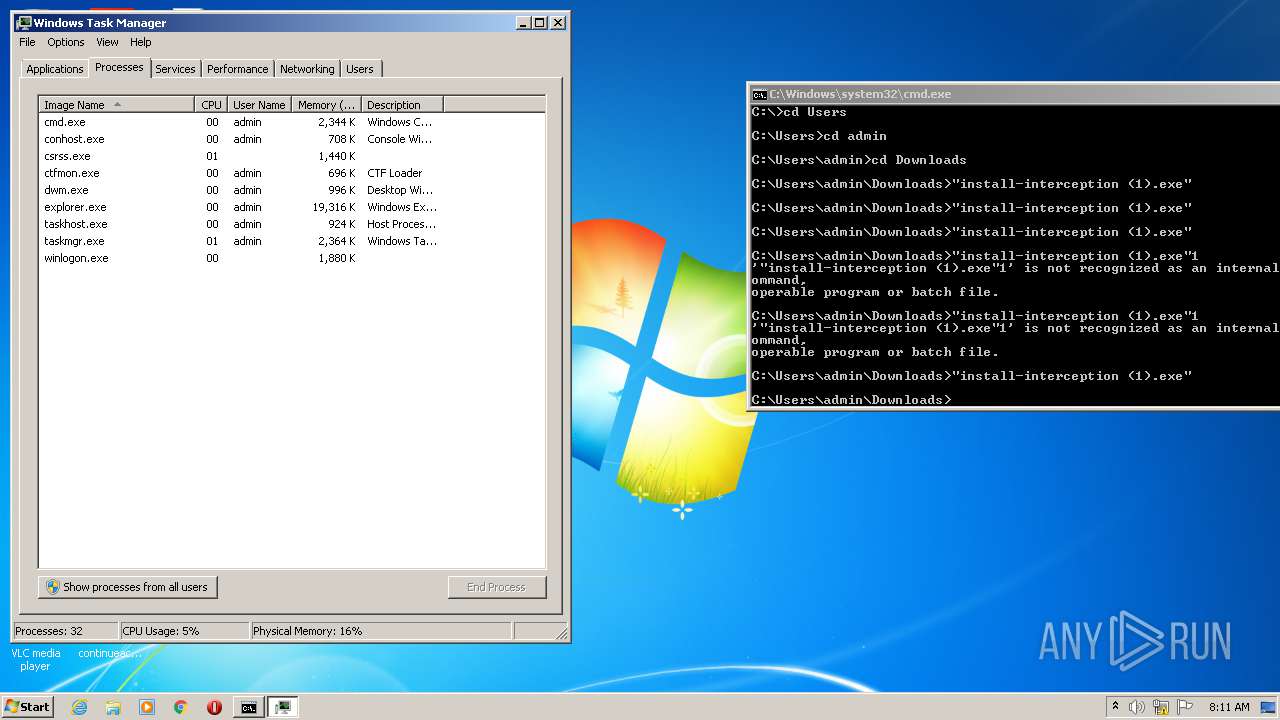
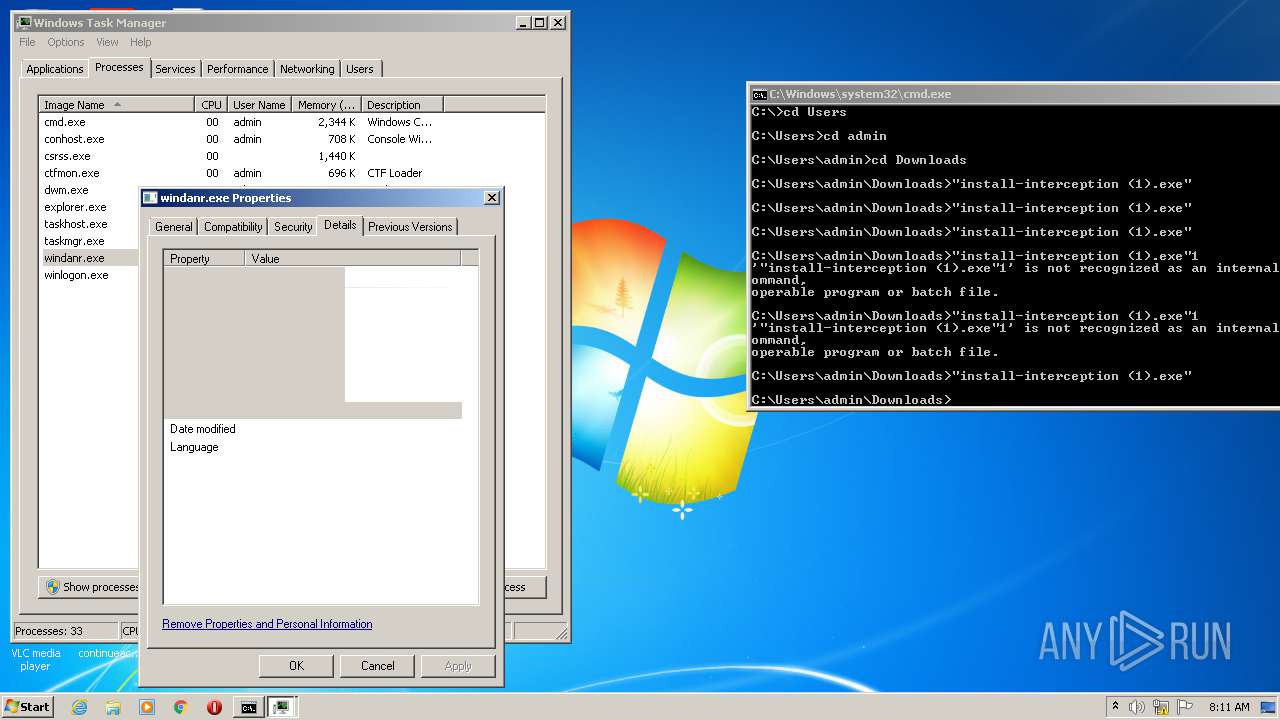
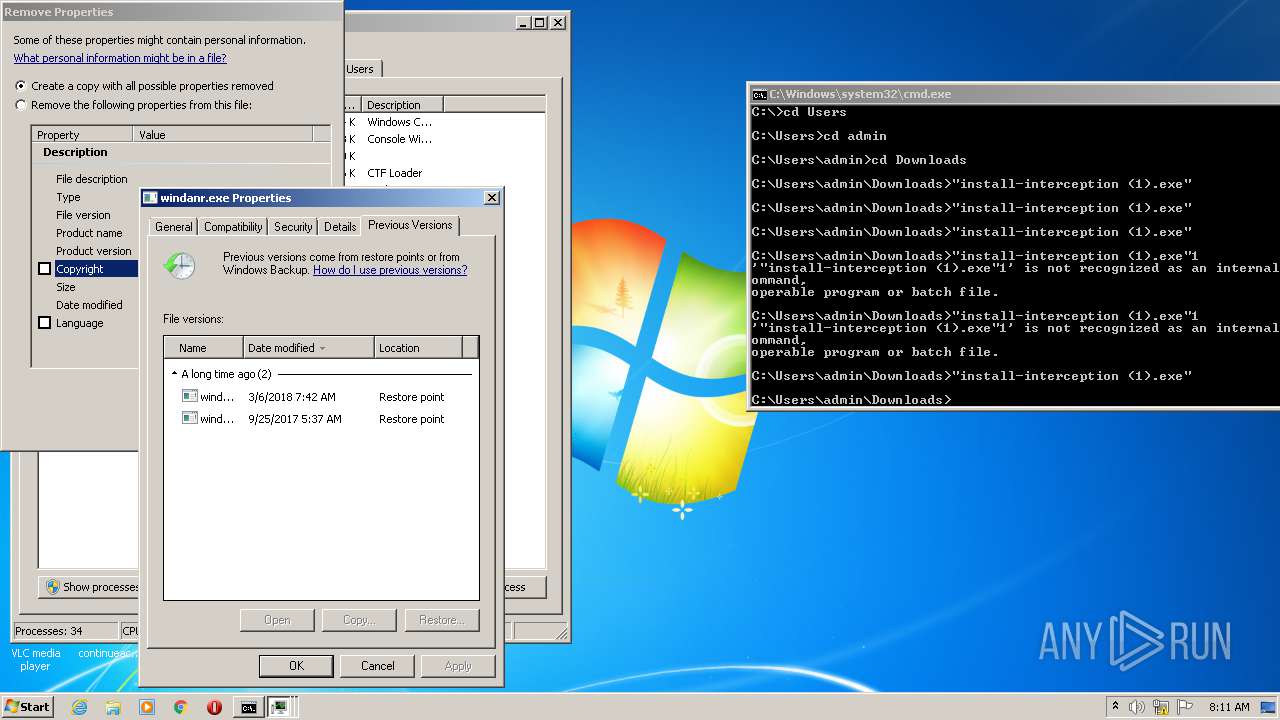
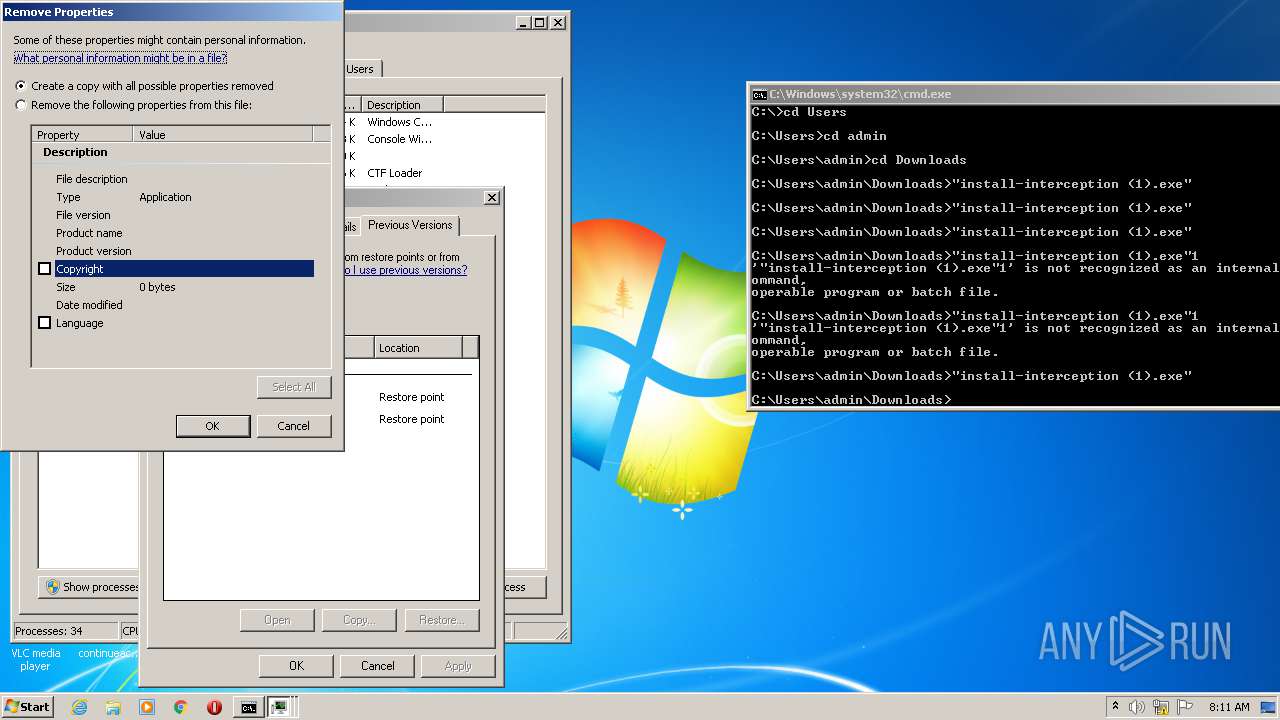
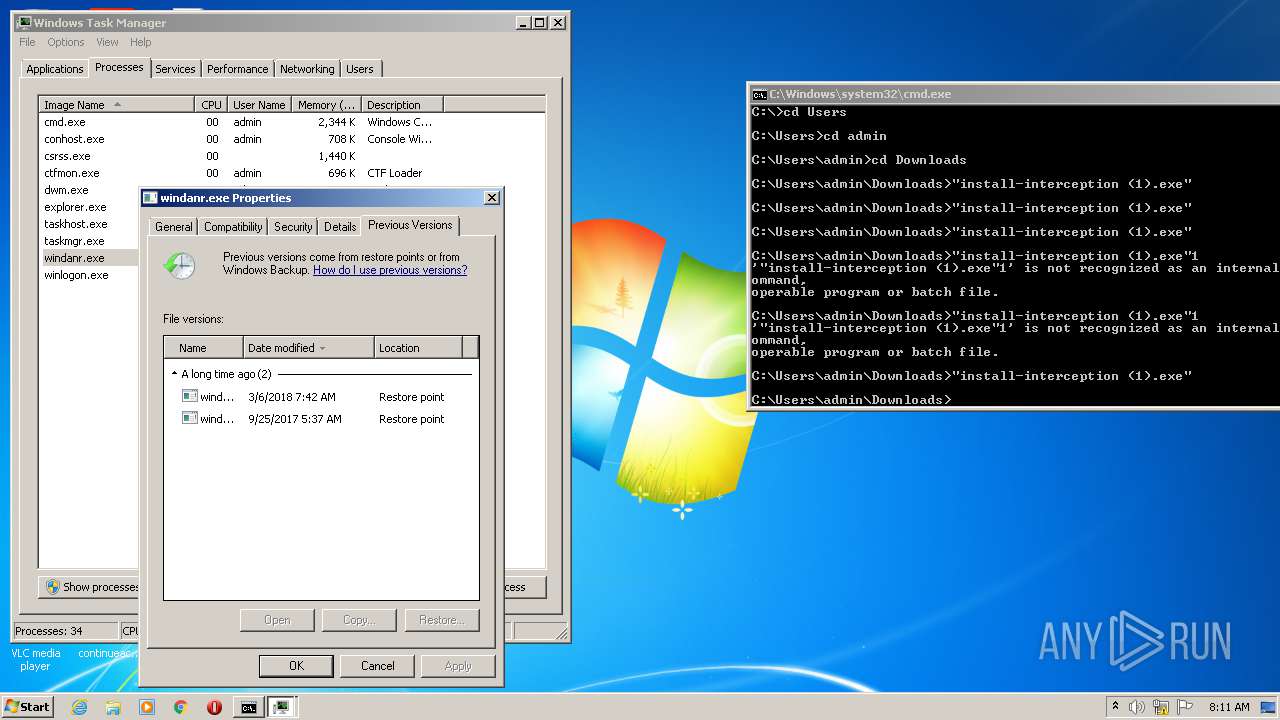
Manual execution by user
- taskmgr.exe (PID: 3228)
- cmd.exe (PID: 2928)
Reads settings of System Certificates
- chrome.exe (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
32
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,3358472333865716176,8228376285085346931,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6685314294148892067 --mojo-platform-channel-handle=2964 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3358472333865716176,8228376285085346931,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15049544206620521773 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
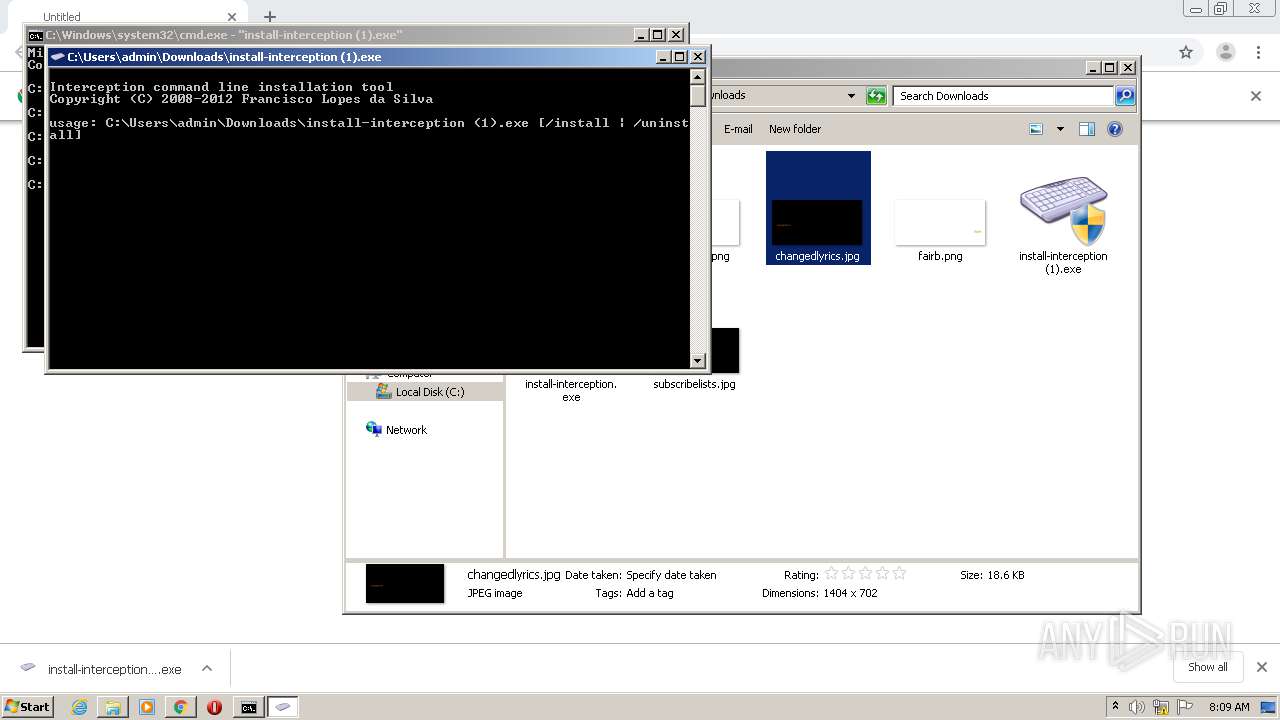
| 632 | "C:\Users\admin\Downloads\install-interception.exe" | C:\Users\admin\Downloads\install-interception.exe | — | chrome.exe | |||||||||||
User: admin Company: Oblita Integrity Level: MEDIUM Description: Interception command line installation tool Exit code: 3221226540 Version: 1.00 built by: WinDDK Modules
| |||||||||||||||
| 788 | "install-interception (1).exe" | C:\Users\admin\Downloads\install-interception (1).exe | — | cmd.exe | |||||||||||
User: admin Company: Oblita Integrity Level: MEDIUM Description: Interception command line installation tool Exit code: 3221226540 Version: 1.00 built by: WinDDK Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,3358472333865716176,8228376285085346931,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12643616212286016516 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://github.com/downloads/oblitum/Interception/install-interception.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "install-interception (1).exe" | C:\Users\admin\Downloads\install-interception (1).exe | — | cmd.exe | |||||||||||
User: admin Company: Oblita Integrity Level: MEDIUM Description: Interception command line installation tool Exit code: 3221226540 Version: 1.00 built by: WinDDK Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\Downloads\install-interception (1).exe" | C:\Users\admin\Downloads\install-interception (1).exe | cmd.exe | ||||||||||||
User: admin Company: Oblita Integrity Level: HIGH Description: Interception command line installation tool Exit code: 1 Version: 1.00 built by: WinDDK Modules
| |||||||||||||||
| 2188 | "C:\Users\admin\Downloads\install-interception (1).exe" | C:\Users\admin\Downloads\install-interception (1).exe | — | cmd.exe | |||||||||||
User: admin Company: Oblita Integrity Level: MEDIUM Description: Interception command line installation tool Exit code: 3221226540 Version: 1.00 built by: WinDDK Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,3358472333865716176,8228376285085346931,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15457099964257152319 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 904
Read events
1 688
Write events
213
Delete events
3
Modification events
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1420-13238924874121875 |
Value: 259 | |||
Executable files
7
Suspicious files
37
Text files
100
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F09654A-58C.pma | — | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6906b8bc-2b61-45ec-94e0-b9156ef7423a.tmp | — | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF27c11f.TMP | text | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF27c100.TMP | text | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF27c2d5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
956 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 216.58.212.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 52.217.45.172:443 | github.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
956 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 172.217.21.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 140.82.118.4:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
github.s3.amazonaws.com |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |