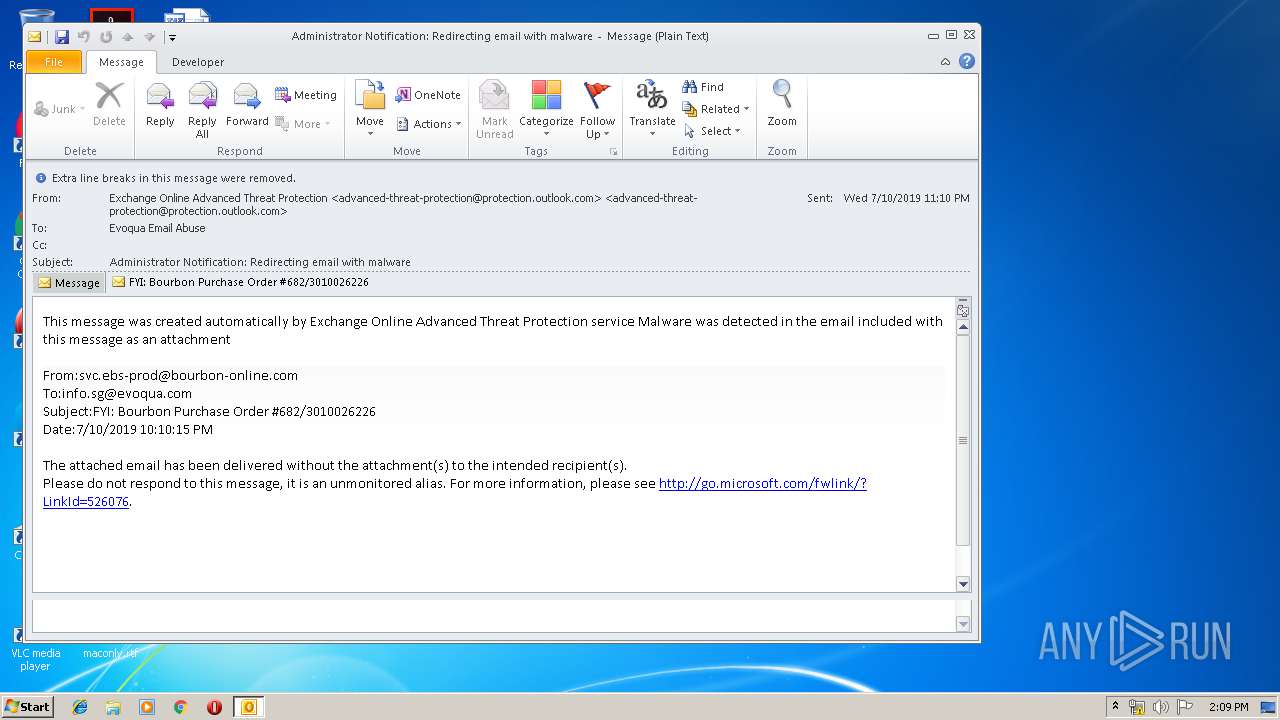
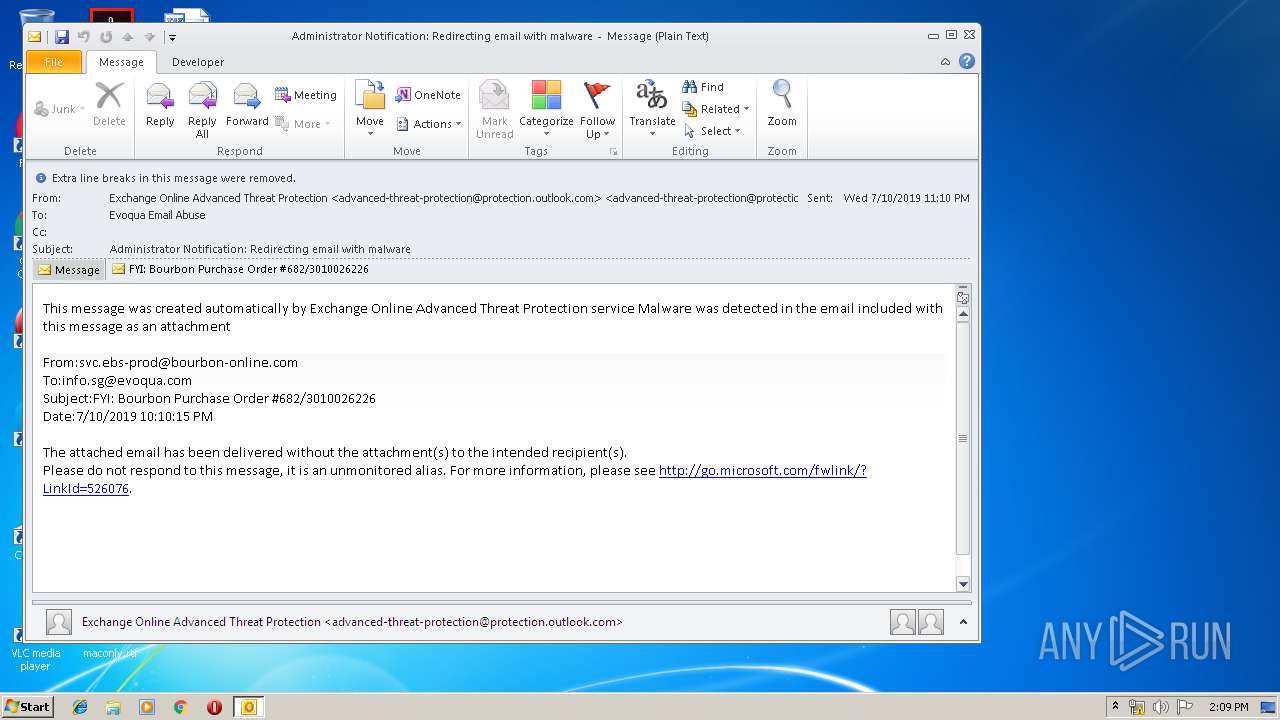
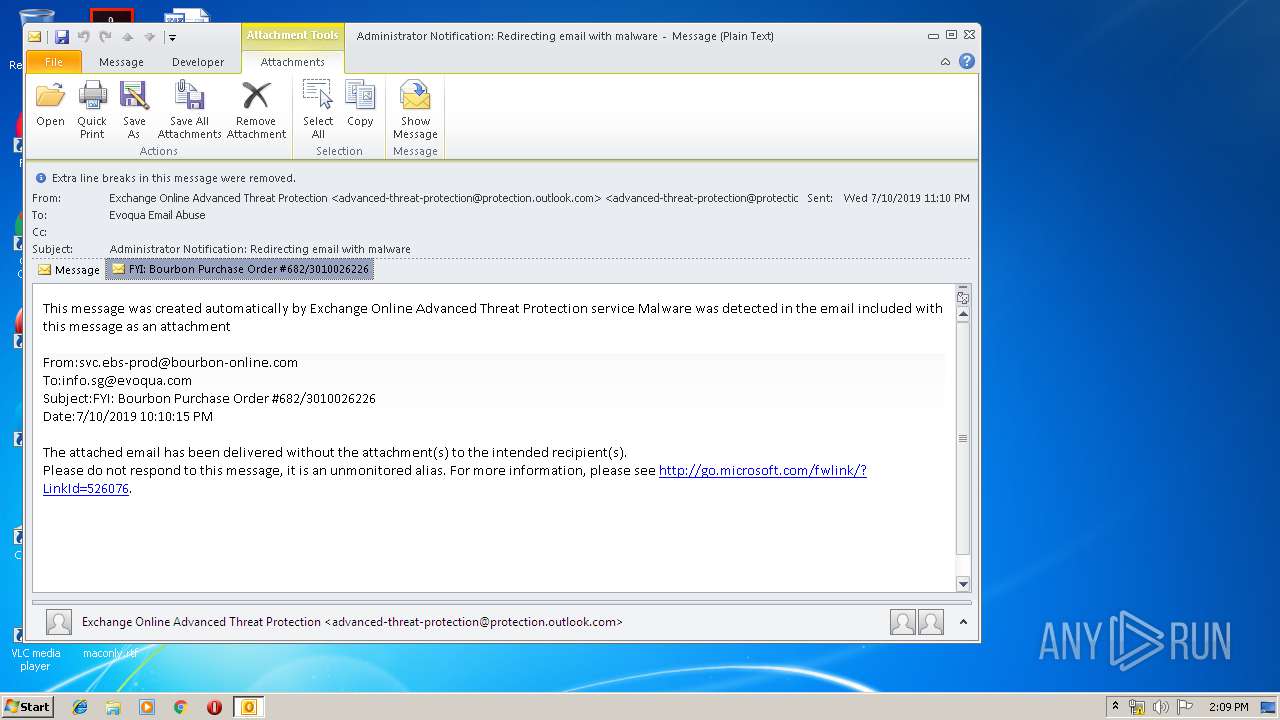
| File name: | Administrator Notification_ Redirecting email with malware.msg |
| Full analysis: | https://app.any.run/tasks/ea804f59-2573-4291-b411-3a2c9d6158f1 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 13:08:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | F4399754626A9D725C04B459BA603CCD |
| SHA1: | 0D587350DAC698DA1BA65E6E955C095EECB18386 |
| SHA256: | BF8157262AA6251E7F3FF63166AF0676FB33069ADA10B99161E0B4401A233B3B |
| SSDEEP: | 6144:gKvO2xUyygvECLCGzmX8HJuORdPveFfX8wR/6UBx/L4ok3ircTOgCbQMou:z5tmsH1kVja7ORQ |
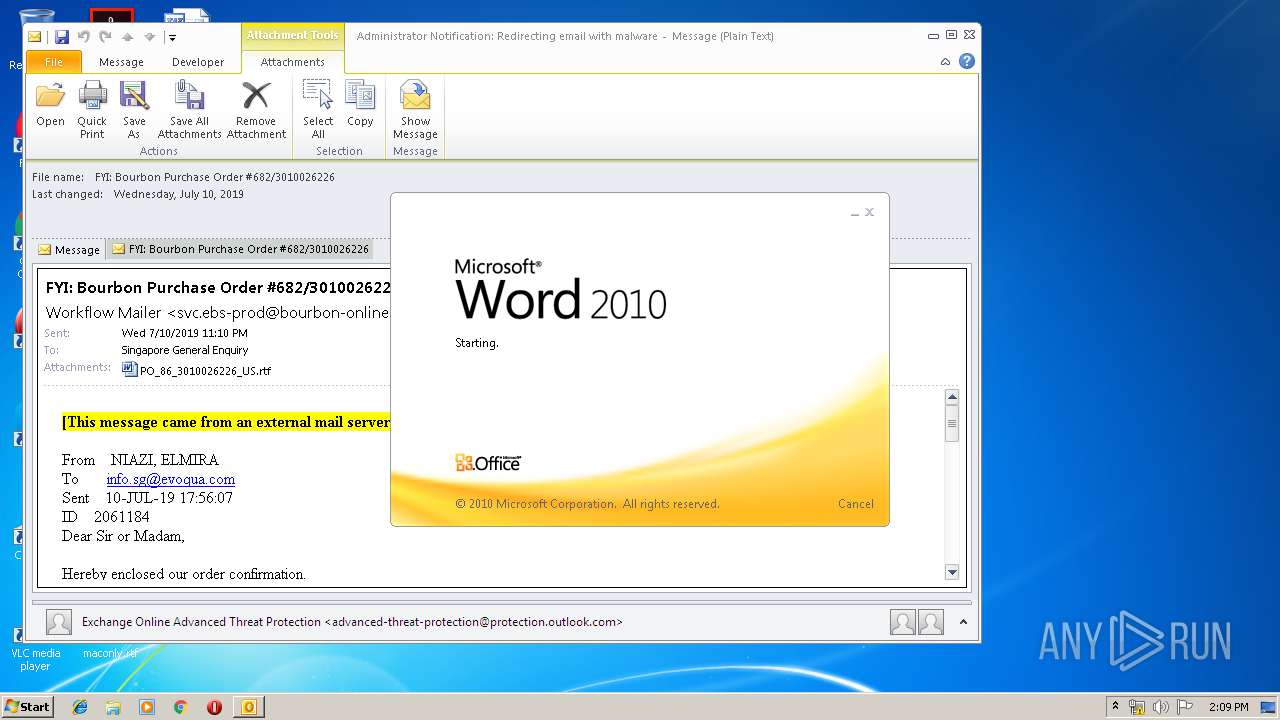
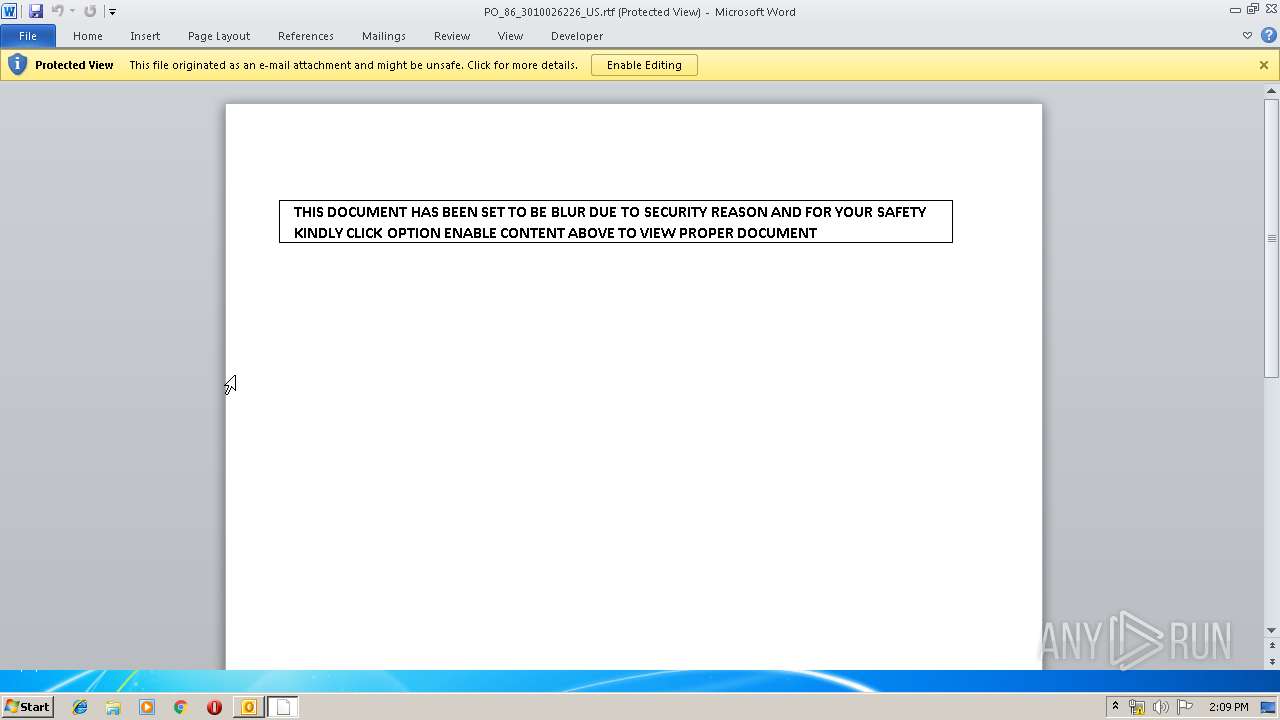
MALICIOUS
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2752)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 2752)
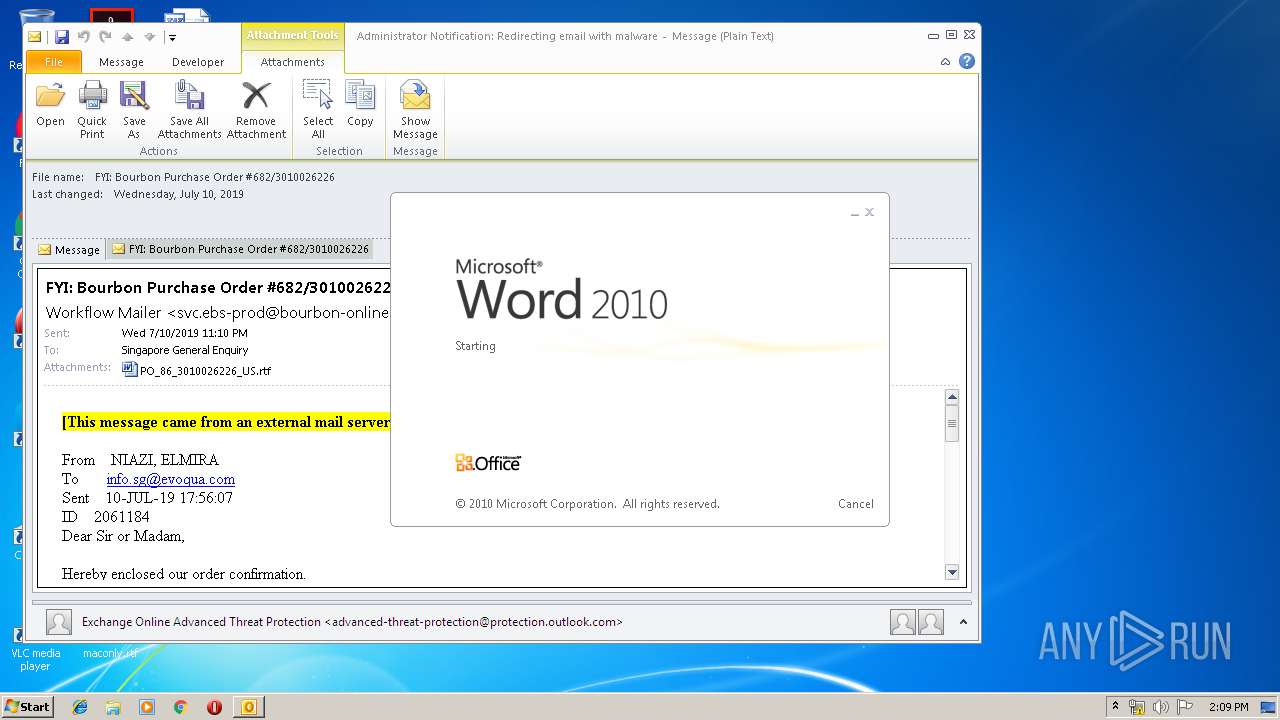
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2880)
- WINWORD.EXE (PID: 2752)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2880)
- WINWORD.EXE (PID: 2752)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2880)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2880)
- WINWORD.EXE (PID: 2752)
- WINWORD.EXE (PID: 3648)
Creates files in the user directory
- WINWORD.EXE (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
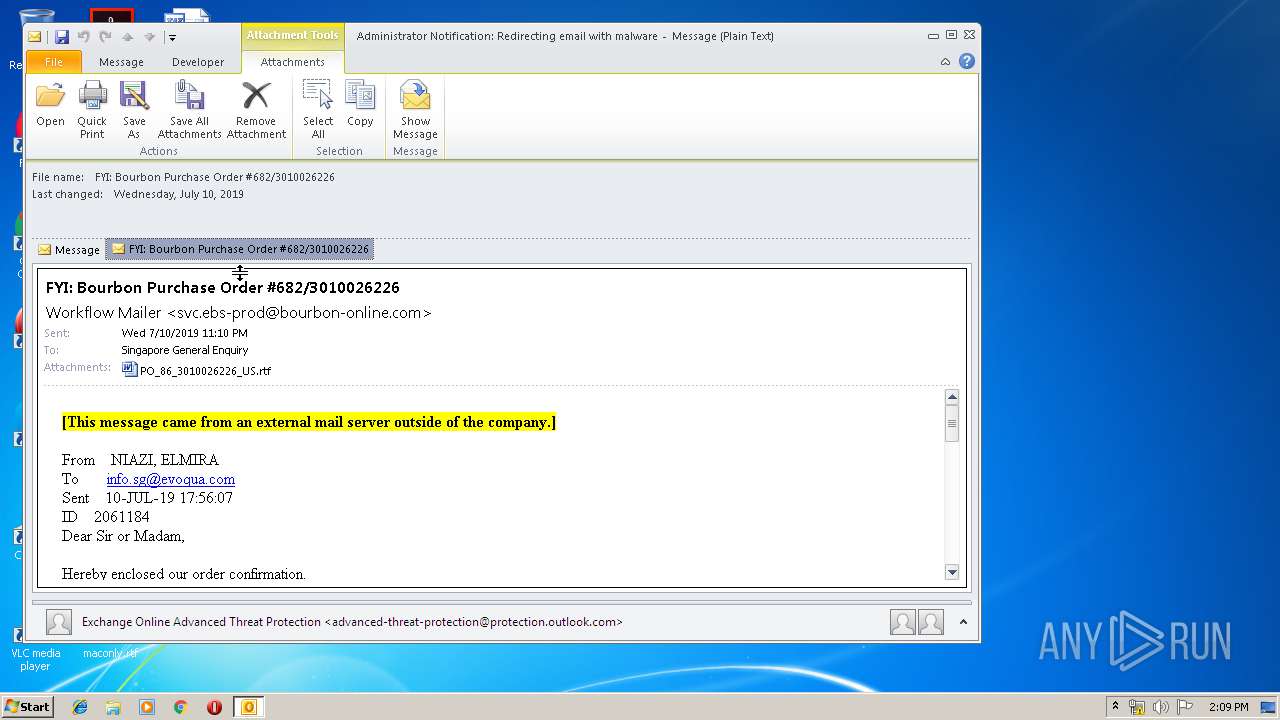
| 2752 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5OLJ62Q0\PO_86_3010026226_US.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3648 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 252
Read events
2 497
Write events
726
Delete events
29
Modification events
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | > |
Value: 3E7F2000400B0000010000000000000000000000 | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 400B0000D01CD5D1E937D50100000000 | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220121280 | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2880) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1324023829 | |||
Executable files
0
Suspicious files
4
Text files
25
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2880 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3B1E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2880 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF5240AE34144246A5.TMP | — | |
MD5:— | SHA256:— | |||
| 2880 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5OLJ62Q0\PO_86_3010026226_US (2).rtf\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR78C3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_CE72DB9B-1881-4C15-933B-5ECD614D2D4E.0\641DEE27.rtf\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3648 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_CE72DB9B-1881-4C15-933B-5ECD614D2D4E.0\~DF72DFEB4E6B58C071.TMP | — | |
MD5:— | SHA256:— | |||
| 2880 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2880 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 2880 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_8C67CA577CEB3547BBA58205FCF898CC.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 2880 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_D232CA9D627B6B4BBEB77ACCFED7FB21.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | WINWORD.EXE | GET | 302 | 95.168.186.145:80 | http://aliiff.com/app/webroot/date/ink.exe | NL | — | — | suspicious |
2880 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2752 | WINWORD.EXE | GET | 301 | 95.168.186.145:80 | http://aliiff.com/home/errorpage | NL | html | 241 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | WINWORD.EXE | 95.168.186.145:80 | aliiff.com | — | NL | suspicious |
2752 | WINWORD.EXE | 95.168.186.145:443 | aliiff.com | — | NL | suspicious |
2880 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
aliiff.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | WINWORD.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2752 | WINWORD.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |