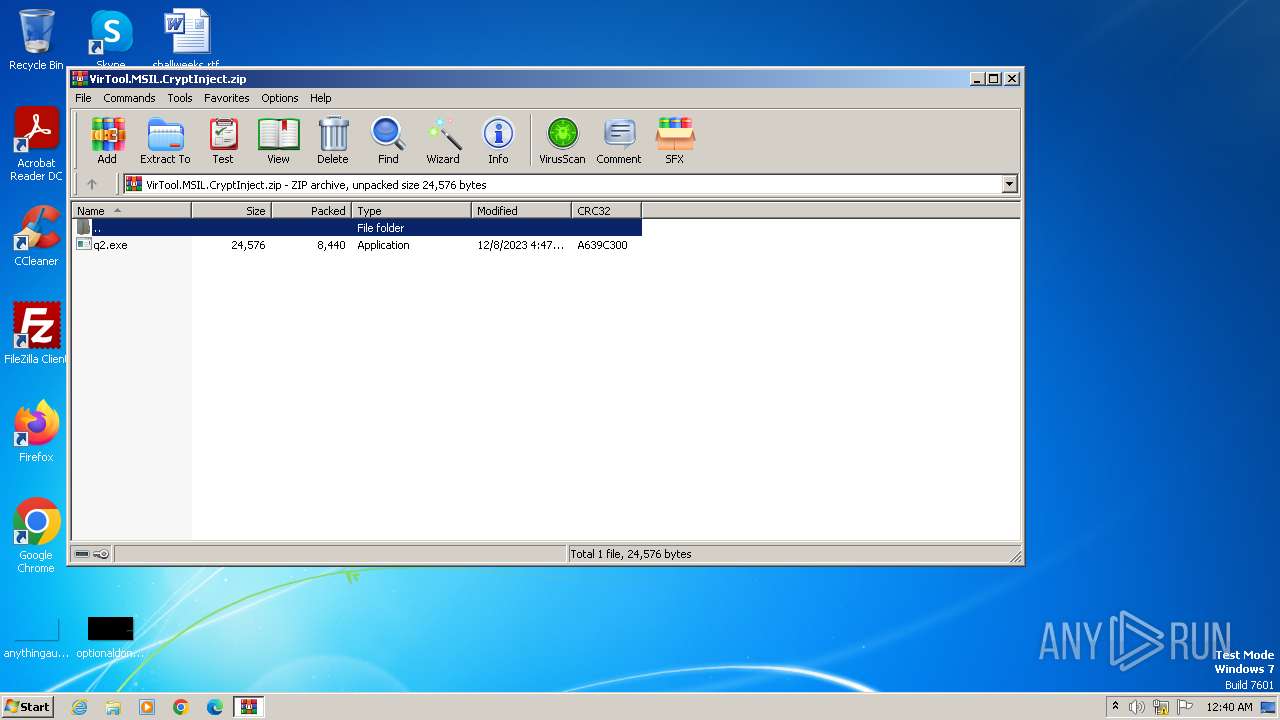
| File name: | VirTool.MSIL.CryptInject.zip |
| Full analysis: | https://app.any.run/tasks/07dc2890-a0ee-49a3-ac7f-120efe7fa6ff |
| Verdict: | Malicious activity |
| Analysis date: | December 09, 2023, 00:40:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F54A6C775A61AEF84419BA7221876B1B |
| SHA1: | 4D0DBB333CAA433D16670169D8278DE511025CF0 |
| SHA256: | BF7779098DA0EE1CD1E086C1F43DDCFE909878465B836E32D139C178B9B2815F |
| SSDEEP: | 192:KnKKduvzbRwoloJTK/0NZQCx3paXoA4BrFcgF5ak9KaCUzm1zi:KAv/RxlvGaYjB9N9VCOwi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- q2.exe (PID: 2988)
Reads settings of System Certificates
- q2.exe (PID: 2988)
Checks Windows Trust Settings
- q2.exe (PID: 2988)
Reads security settings of Internet Explorer
- q2.exe (PID: 2988)
INFO
Checks proxy server information
- q2.exe (PID: 2988)
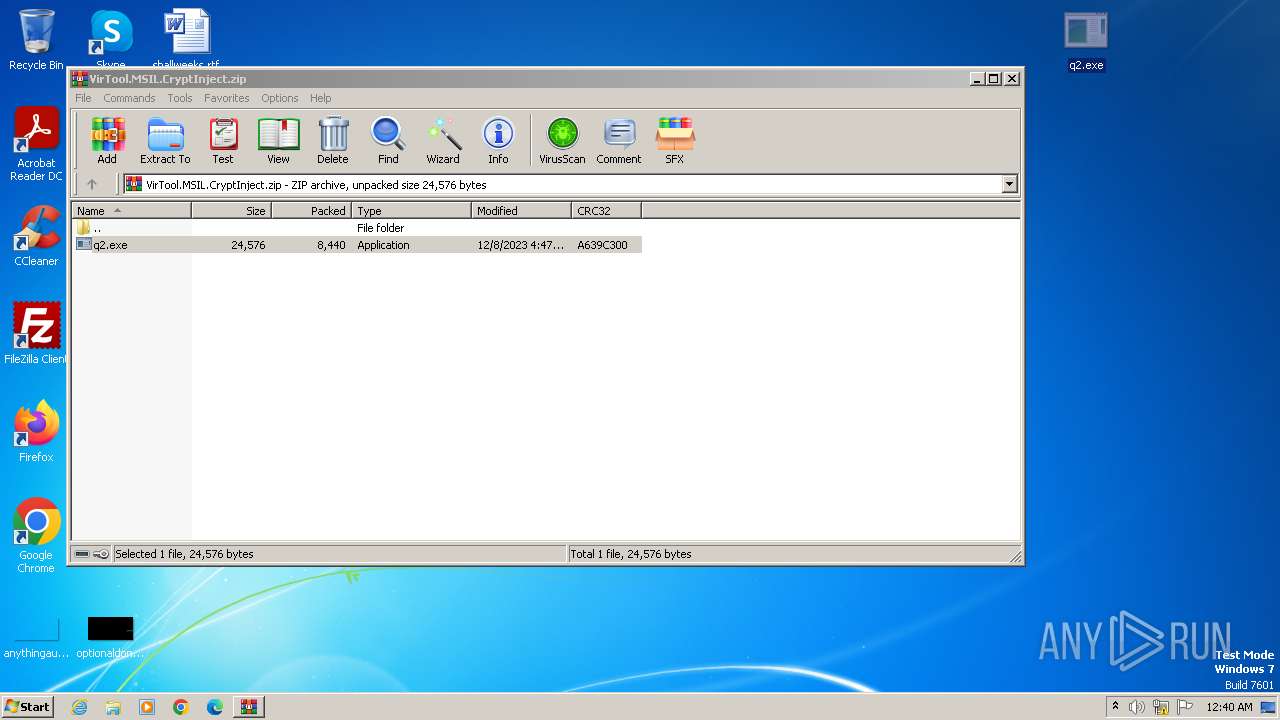
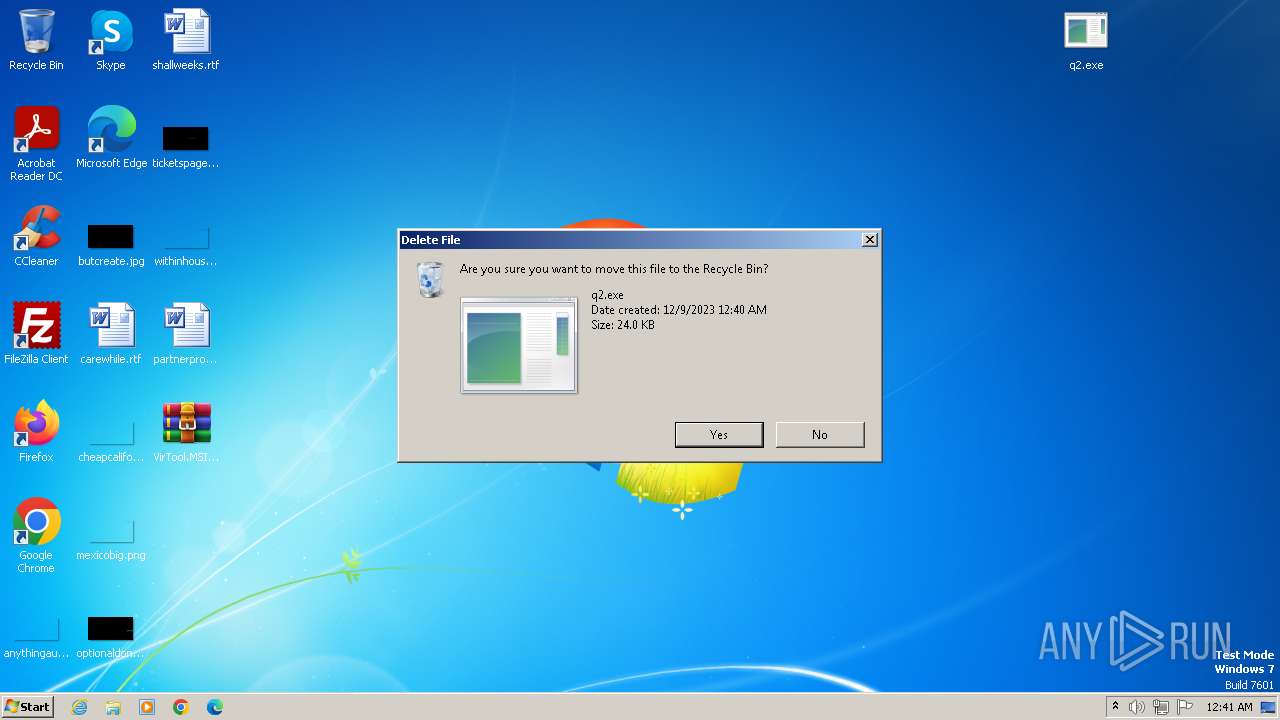
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2464)
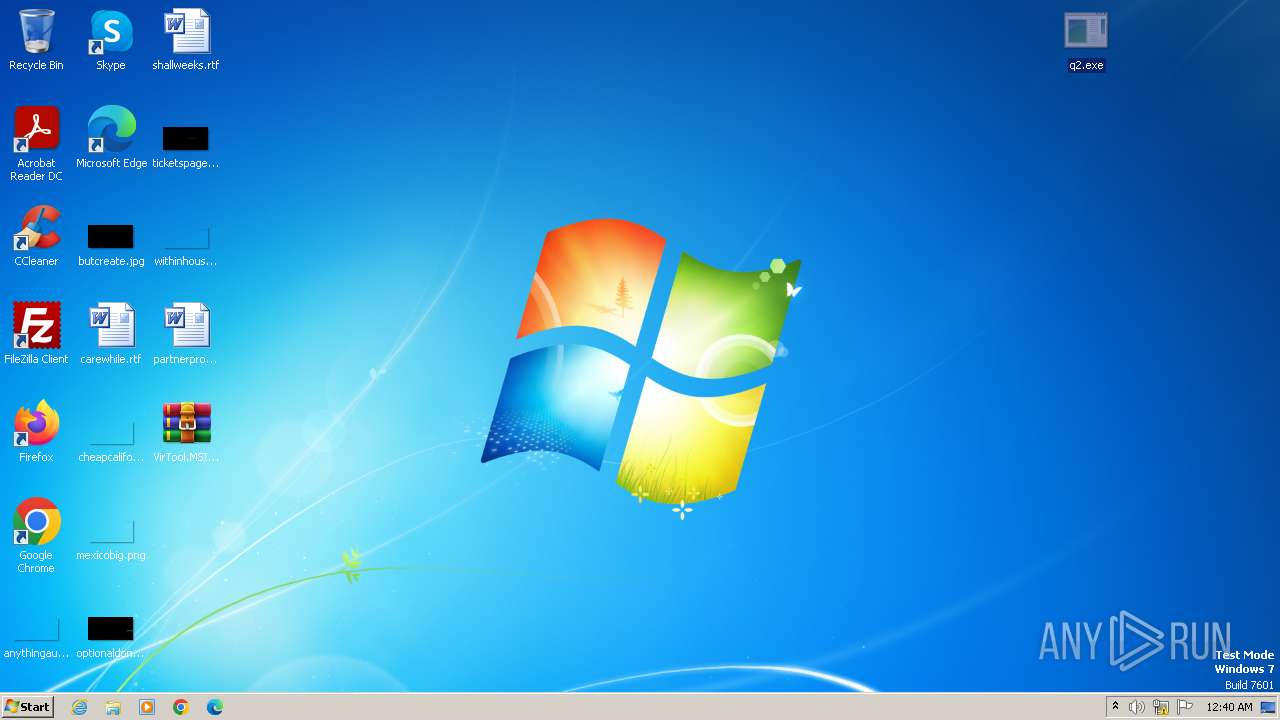
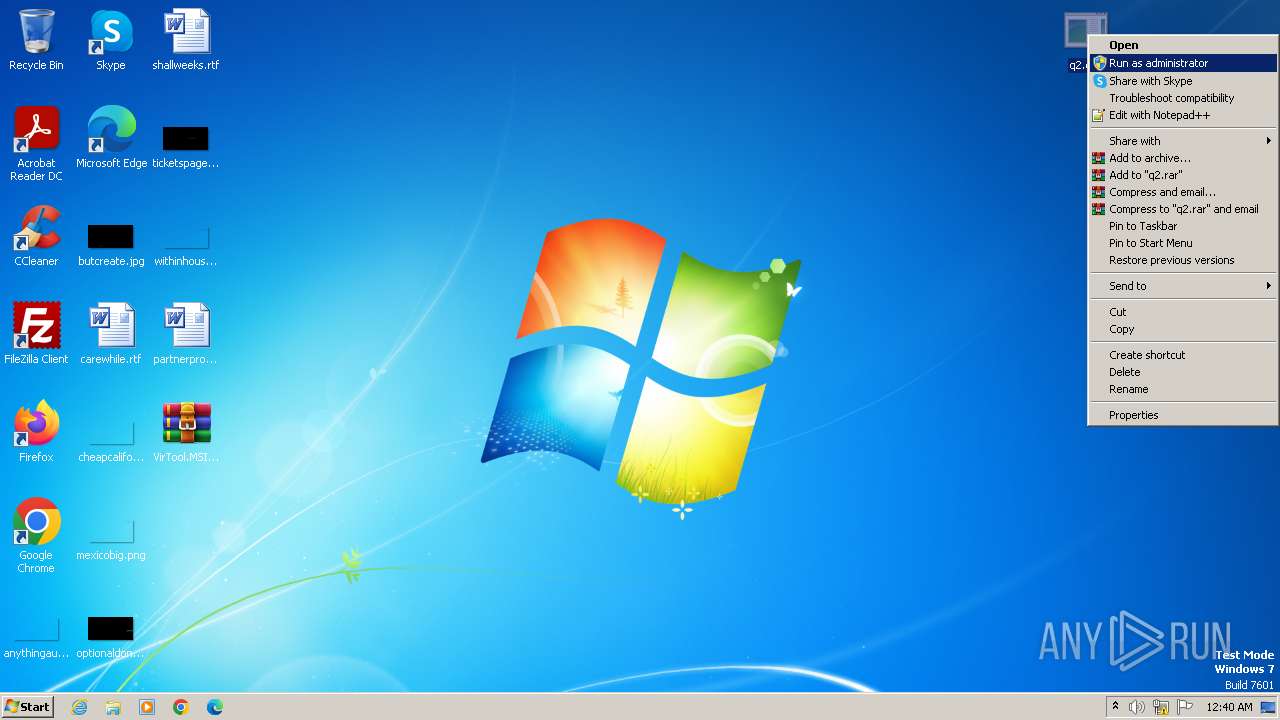
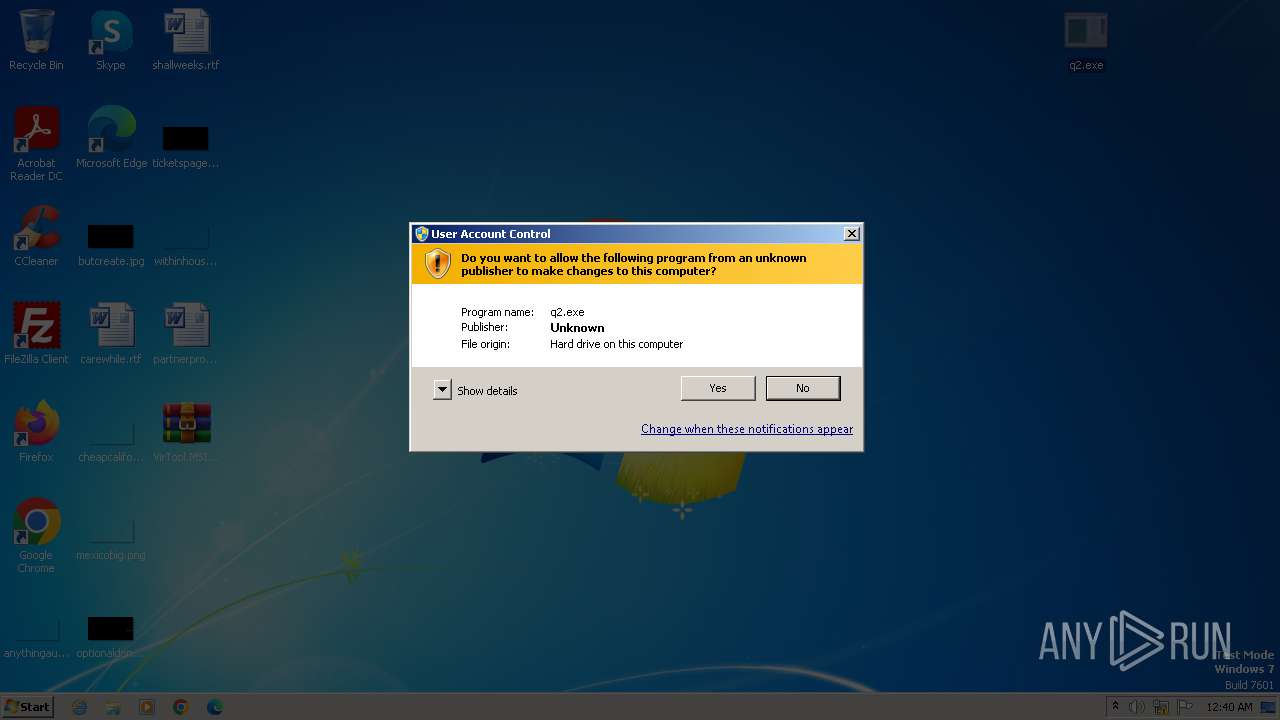
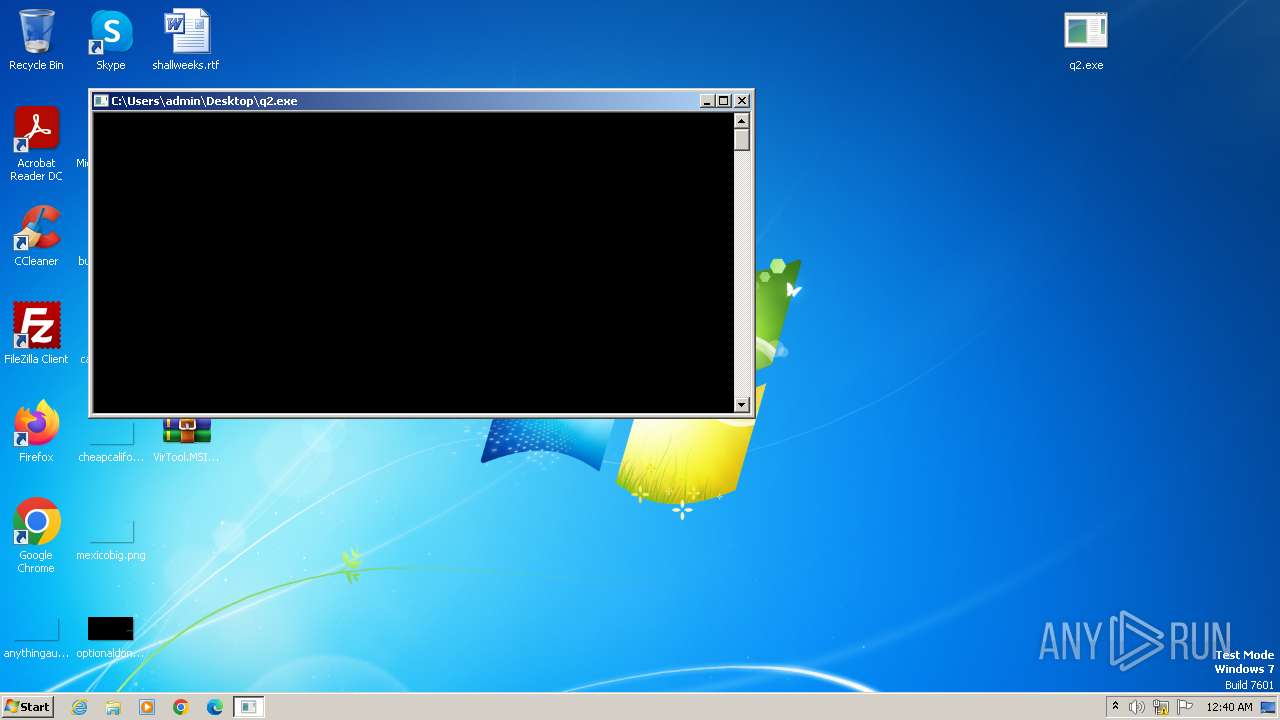
Manual execution by a user
- q2.exe (PID: 2988)
- wmpnscfg.exe (PID: 3304)
Reads the computer name
- q2.exe (PID: 2988)
- wmpnscfg.exe (PID: 3304)
Checks supported languages
- q2.exe (PID: 2988)
- wmpnscfg.exe (PID: 3304)
Reads the machine GUID from the registry
- q2.exe (PID: 2988)
Creates files or folders in the user directory
- q2.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:12:08 16:47:32 |
| ZipCRC: | 0xa639c300 |
| ZipCompressedSize: | 8440 |
| ZipUncompressedSize: | 24576 |
| ZipFileName: | q2.exe |
Total processes
45
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2464 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\VirTool.MSIL.CryptInject.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2988 | "C:\Users\admin\Desktop\q2.exe" | C:\Users\admin\Desktop\q2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
| 3304 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 974
Read events
8 931
Write events
43
Delete events
0
Modification events
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
1
Suspicious files
4
Text files
143
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\GOG3BV85.htm | html | |
MD5:5308620F06B1B61F0AE32E12A2DA954E | SHA256:F0BF2A2AB411B245AABE88214B65DCBAF37A55D9EBDAFA43DEB15FDDE6CBFE87 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\HFMBKB47.htm | html | |
MD5:5308620F06B1B61F0AE32E12A2DA954E | SHA256:F0BF2A2AB411B245AABE88214B65DCBAF37A55D9EBDAFA43DEB15FDDE6CBFE87 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\B40MXLLM.htm | html | |
MD5:5308620F06B1B61F0AE32E12A2DA954E | SHA256:F0BF2A2AB411B245AABE88214B65DCBAF37A55D9EBDAFA43DEB15FDDE6CBFE87 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\0M55NSGJ.htm | html | |
MD5:5308620F06B1B61F0AE32E12A2DA954E | SHA256:F0BF2A2AB411B245AABE88214B65DCBAF37A55D9EBDAFA43DEB15FDDE6CBFE87 | |||
| 2464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2464.42633\q2.exe | executable | |
MD5:C04FD8D9198095192E7D55345966DA2E | SHA256:0C98769E42B364711C478226EF199BFBBA90DB80175EB1B8CD565AA694C09852 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\J944RMBQ.htm | html | |
MD5:B3B7B65619C07EE6E6C7058B33FD780A | SHA256:71E7FD08F132E6E0AE6CA65C1703BA29C36B319CA8F1949009ED2EDC13CB8C70 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\1OIA0KV8.htm | html | |
MD5:5308620F06B1B61F0AE32E12A2DA954E | SHA256:F0BF2A2AB411B245AABE88214B65DCBAF37A55D9EBDAFA43DEB15FDDE6CBFE87 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\XIZLTA0U.htm | html | |
MD5:5308620F06B1B61F0AE32E12A2DA954E | SHA256:F0BF2A2AB411B245AABE88214B65DCBAF37A55D9EBDAFA43DEB15FDDE6CBFE87 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\WX731MYG.htm | html | |
MD5:5308620F06B1B61F0AE32E12A2DA954E | SHA256:F0BF2A2AB411B245AABE88214B65DCBAF37A55D9EBDAFA43DEB15FDDE6CBFE87 | |||
| 2988 | q2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\N8NJZBSA.htm | html | |
MD5:B3B7B65619C07EE6E6C7058B33FD780A | SHA256:71E7FD08F132E6E0AE6CA65C1703BA29C36B319CA8F1949009ED2EDC13CB8C70 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
150
TCP/UDP connections
13
DNS requests
6
Threats
147
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.malwareanalysisbook.com/ | unknown | html | 74 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.malwareanalysisbook.com/ | unknown | html | 74 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.malwareanalysisbook.com/ | unknown | html | 74 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.practicalmalwareanalysis.com/ | unknown | html | 63 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.malwareanalysisbook.com/ | unknown | html | 74 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.practicalmalwareanalysis.com/ | unknown | html | 63 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.malwareanalysisbook.com/ | unknown | html | 74 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.practicalmalwareanalysis.com/ | unknown | html | 63 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.practicalmalwareanalysis.com/ | unknown | html | 63 b | unknown |
2988 | q2.exe | GET | 301 | 15.197.142.173:80 | http://www.malwareanalysisbook.com/ | unknown | html | 74 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2988 | q2.exe | 15.197.142.173:80 | www.malwareanalysisbook.com | AMAZON-02 | US | unknown |
2988 | q2.exe | 104.20.120.46:443 | nostarch.com | CLOUDFLARENET | — | unknown |
2988 | q2.exe | 184.24.77.194:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2988 | q2.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.malwareanalysisbook.com |
| whitelisted |
www.practicalmalwareanalysis.com |
| whitelisted |
nostarch.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
147 ETPRO signatures available at the full report