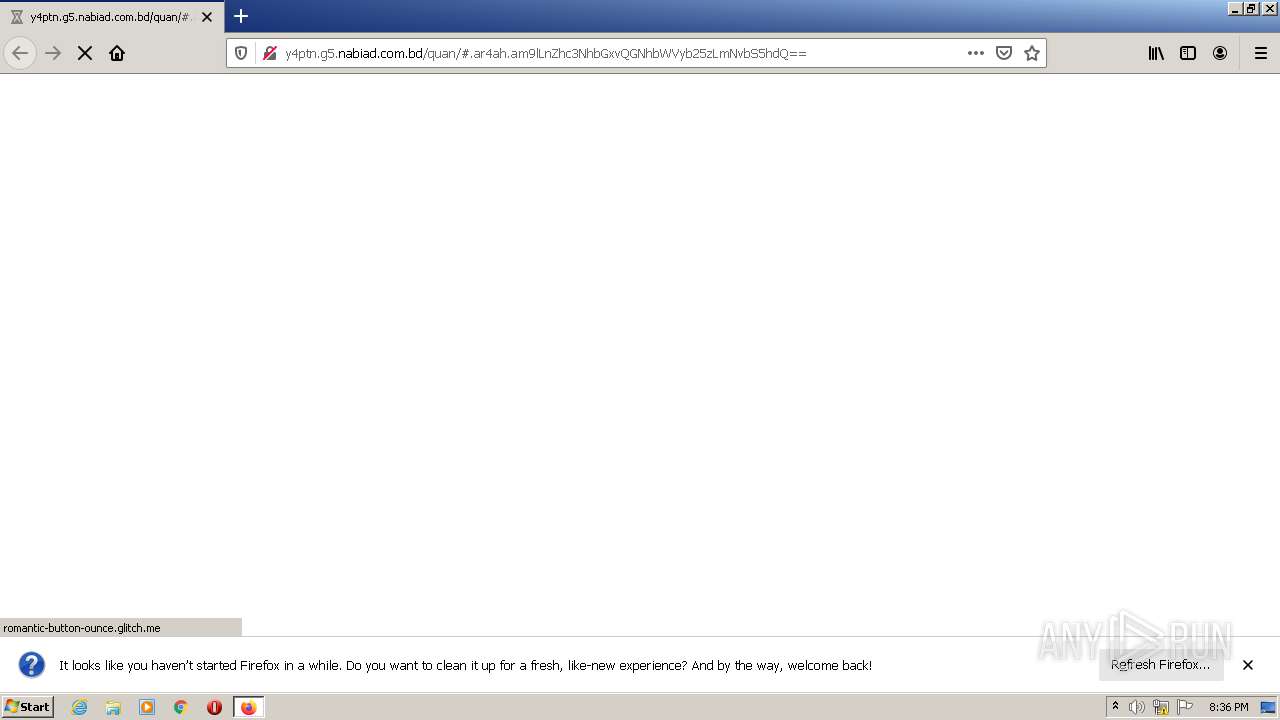
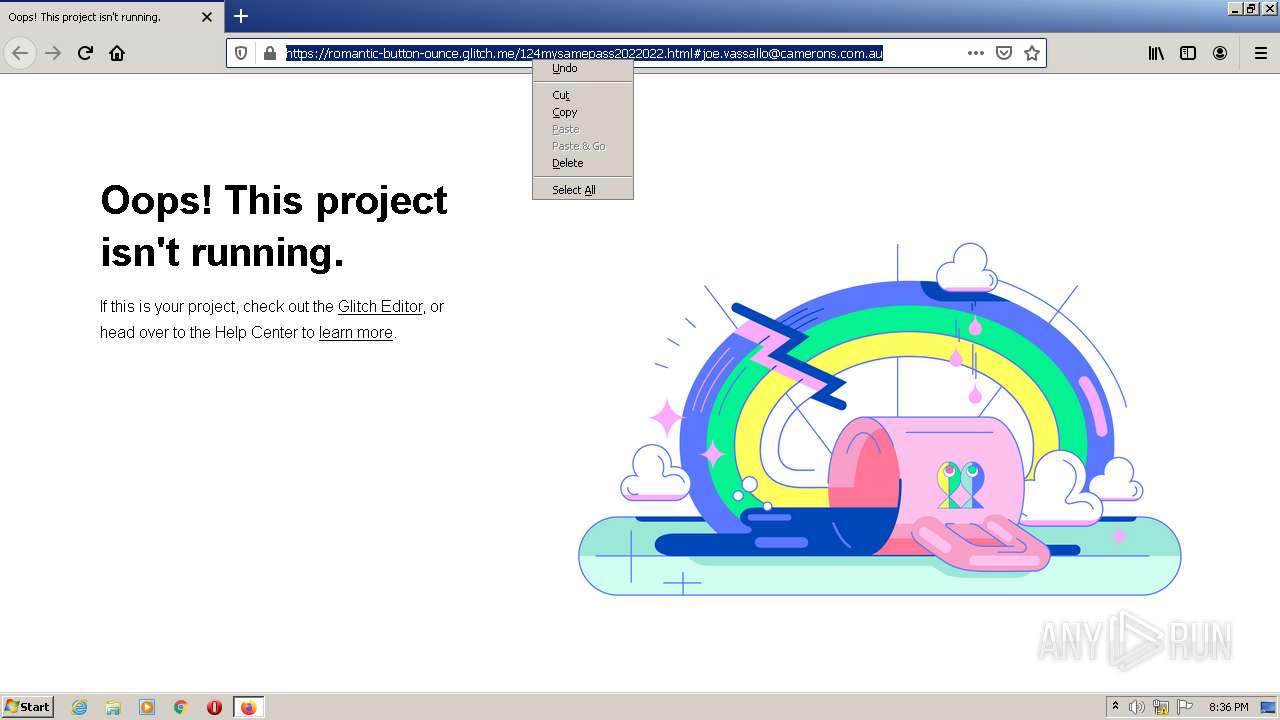
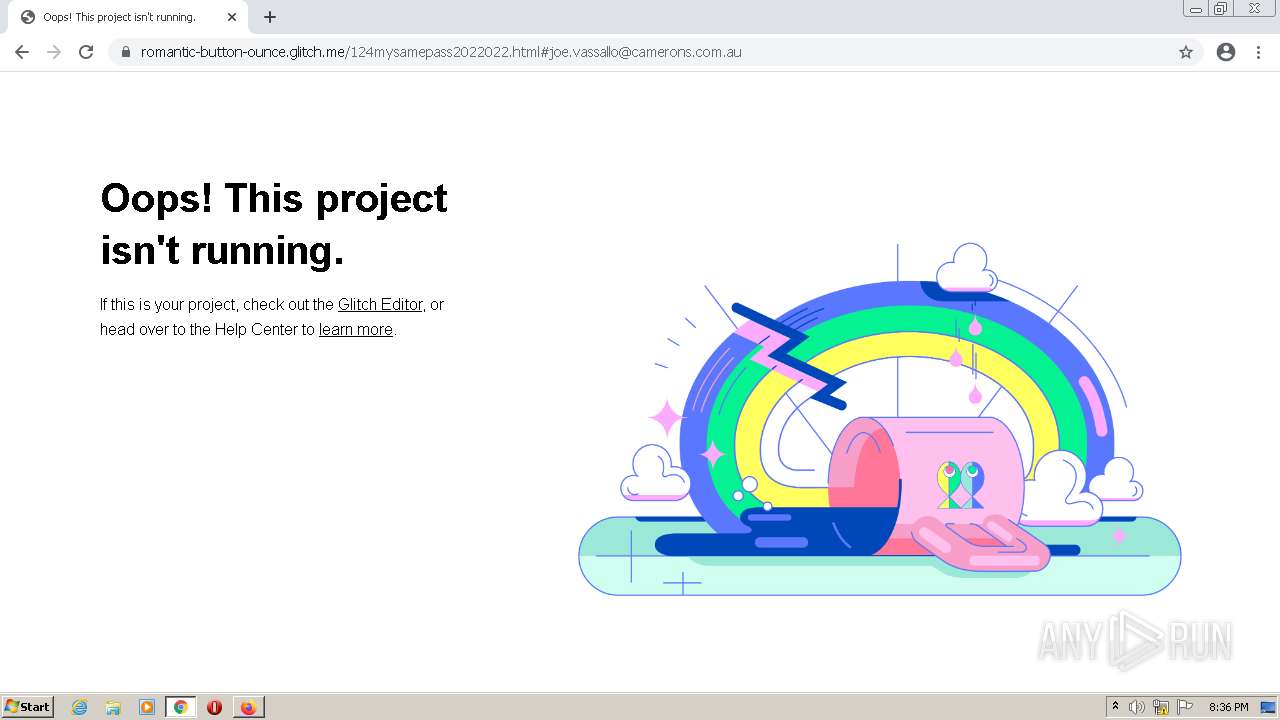
| URL: | http://y4ptn.g5.nabiad.com.bd/quan/#.ar4ah.am9lLnZhc3NhbGxvQGNhbWVyb25zLmNvbS5hdQ== |
| Full analysis: | https://app.any.run/tasks/2d4940af-c26c-4915-8b59-abcf725dbaf9 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 20:36:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 51A468C899F925215966035773B186D2 |
| SHA1: | AC66D111E4159BC7F63D1B9F5B5930ABF16C4D63 |
| SHA256: | BF6FD9F23ED78FA1A543A8EA2B4F6A5E42BE680091C241E6E07861E7F6946D56 |
| SSDEEP: | 3:N1KHp8H7Zg/n9kLvyZg+n2QTO:CJ0Zg/nOLaZgc2QTO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3108)
INFO
Checks supported languages
- firefox.exe (PID: 2760)
- firefox.exe (PID: 3184)
- firefox.exe (PID: 4068)
- firefox.exe (PID: 2180)
- firefox.exe (PID: 3456)
- firefox.exe (PID: 2848)
- firefox.exe (PID: 1344)
- firefox.exe (PID: 2664)
- chrome.exe (PID: 3176)
- firefox.exe (PID: 2744)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 992)
- chrome.exe (PID: 288)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 840)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1780)
- chrome.exe (PID: 1468)
- chrome.exe (PID: 1512)
Reads the computer name
- firefox.exe (PID: 2760)
- firefox.exe (PID: 3456)
- firefox.exe (PID: 2664)
- firefox.exe (PID: 2848)
- firefox.exe (PID: 3184)
- firefox.exe (PID: 4068)
- firefox.exe (PID: 1344)
- chrome.exe (PID: 3108)
- firefox.exe (PID: 2744)
- chrome.exe (PID: 992)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 344)
Application launched itself
- firefox.exe (PID: 2180)
- firefox.exe (PID: 3456)
- chrome.exe (PID: 3108)
Creates files in the user directory
- firefox.exe (PID: 3456)
Reads CPU info
- firefox.exe (PID: 3456)
Creates files in the program directory
- firefox.exe (PID: 3456)
Reads the hosts file
- chrome.exe (PID: 3176)
- chrome.exe (PID: 3108)
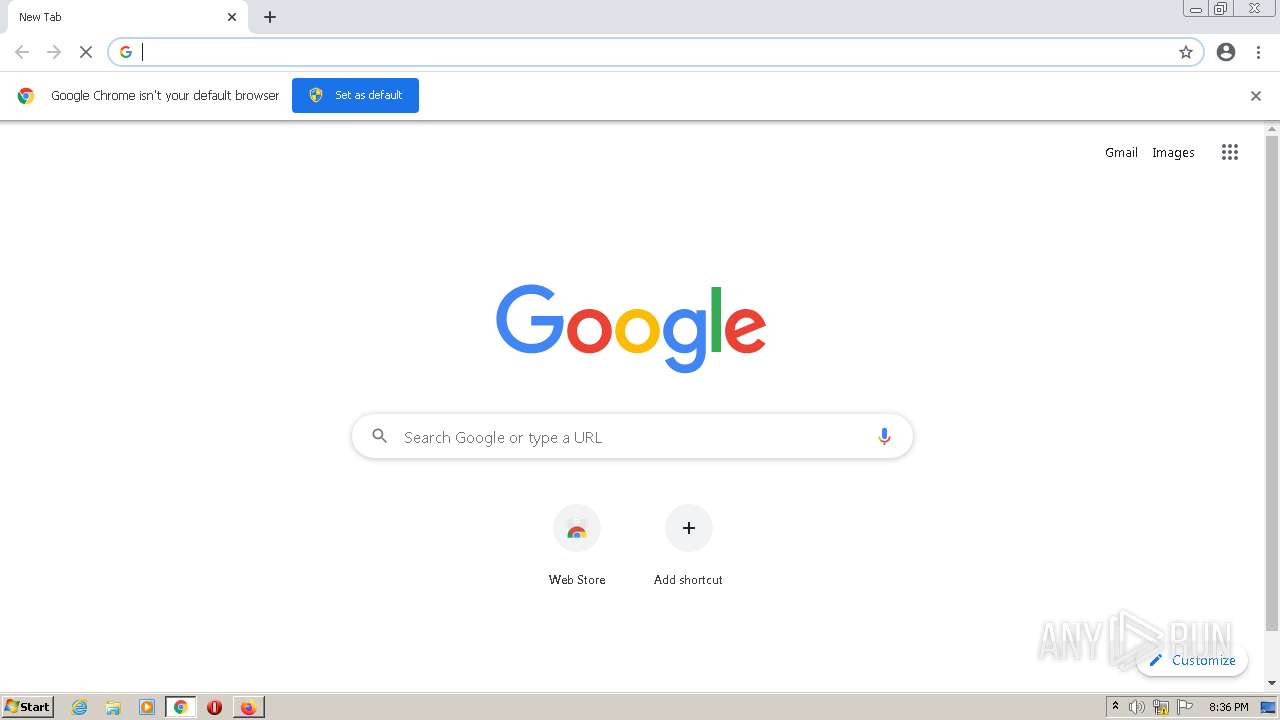
Manual execution by user
- chrome.exe (PID: 3108)
Reads settings of System Certificates
- chrome.exe (PID: 3176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6c76d988,0x6c76d998,0x6c76d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,7174392138904153285,9918873225339070371,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2988 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,7174392138904153285,9918873225339070371,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,7174392138904153285,9918873225339070371,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2860 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3456.22.681431646\16528817" -childID 5 -isForBrowser -prefsHandle 3700 -prefMapHandle 3696 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3456 "\\.\pipe\gecko-crash-server-pipe.3456" 3624 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,7174392138904153285,9918873225339070371,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,7174392138904153285,9918873225339070371,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,7174392138904153285,9918873225339070371,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,7174392138904153285,9918873225339070371,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://y4ptn.g5.nabiad.com.bd/quan/#.ar4ah.am9lLnZhc3NhbGxvQGNhbWVyb25zLmNvbS5hdQ==" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
17 034
Read events
16 950
Write events
83
Delete events
1
Modification events
| (PID) Process: | (2180) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 5560A9EB3A000000 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 586AA9EB3A000000 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3456) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
200
Text files
112
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3456 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionstore-backups\recovery.jsonlz4.tmp | jsonlz4 | |
MD5:— | SHA256:— | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionstore-backups\recovery.jsonlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_XzF51wbSk9JuoIQ | binary | |
MD5:— | SHA256:— | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-new.bin | — | |
MD5:— | SHA256:— | |||
| 3456 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache.bin | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
92
DNS requests
98
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3456 | firefox.exe | POST | 200 | 143.204.101.143:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
3456 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3456 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3456 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
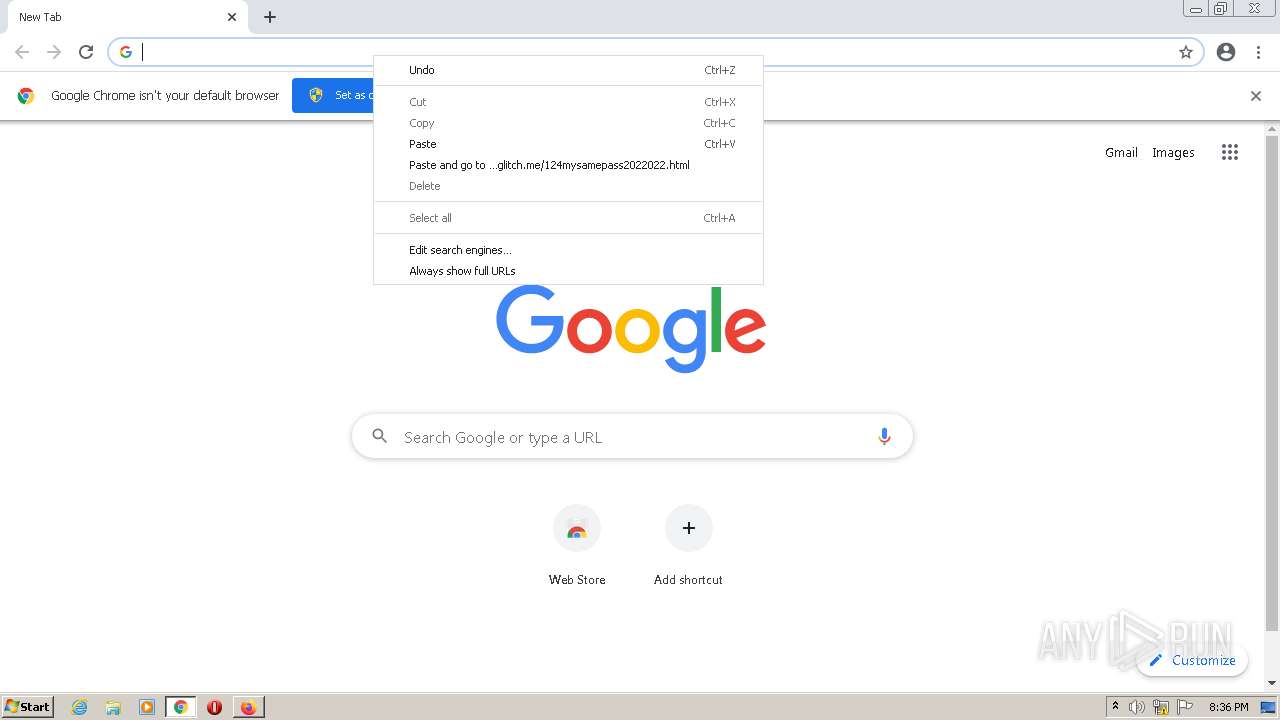
3456 | firefox.exe | GET | 200 | 198.54.126.46:80 | http://y4ptn.g5.nabiad.com.bd/quan/ | US | compressed | 399 b | suspicious |
3176 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
3456 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
3456 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
3456 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3456 | firefox.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3456 | firefox.exe | 143.204.98.120:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
3456 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3456 | firefox.exe | 143.204.98.33:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
3456 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3456 | firefox.exe | 142.250.185.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3456 | firefox.exe | 54.187.205.23:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3456 | firefox.exe | 188.114.96.7:443 | cloud.webtype.com | Cloudflare Inc | US | malicious |
3456 | firefox.exe | 192.229.233.123:443 | cloud.typenetwork.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
3456 | firefox.exe | 143.204.98.36:443 | cdn.glitch.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
y4ptn.g5.nabiad.com.bd |
| suspicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
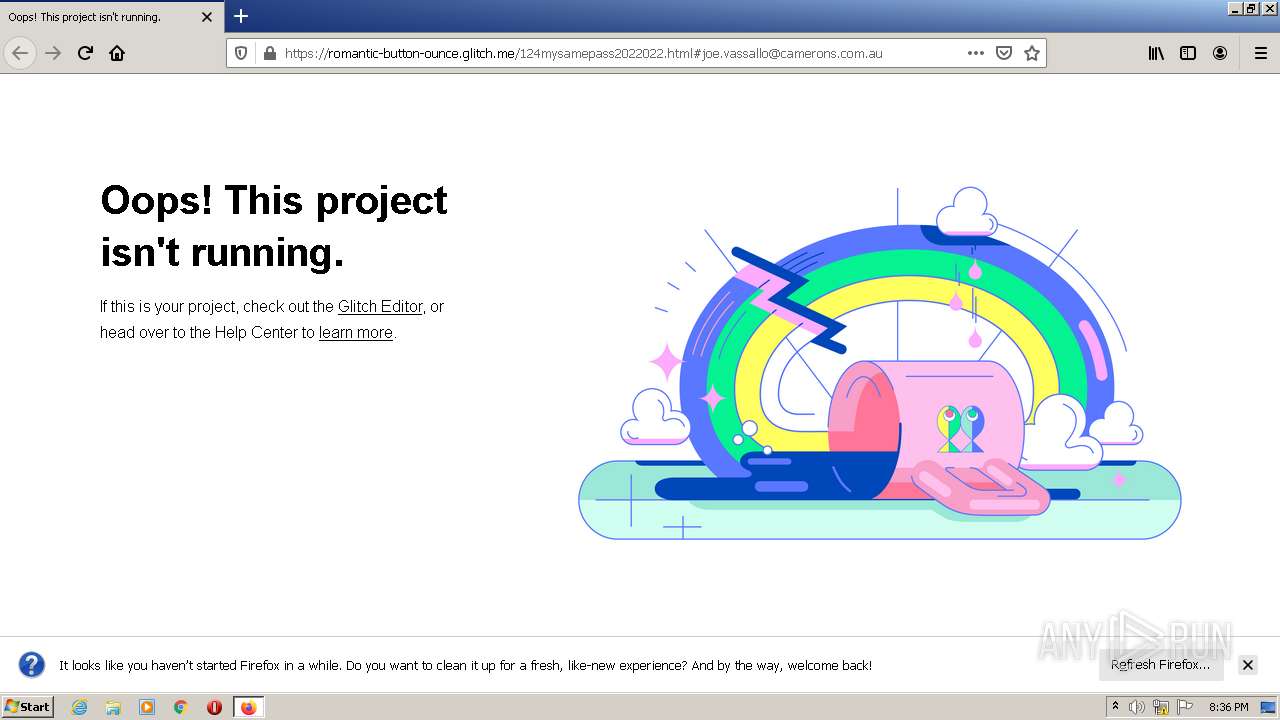
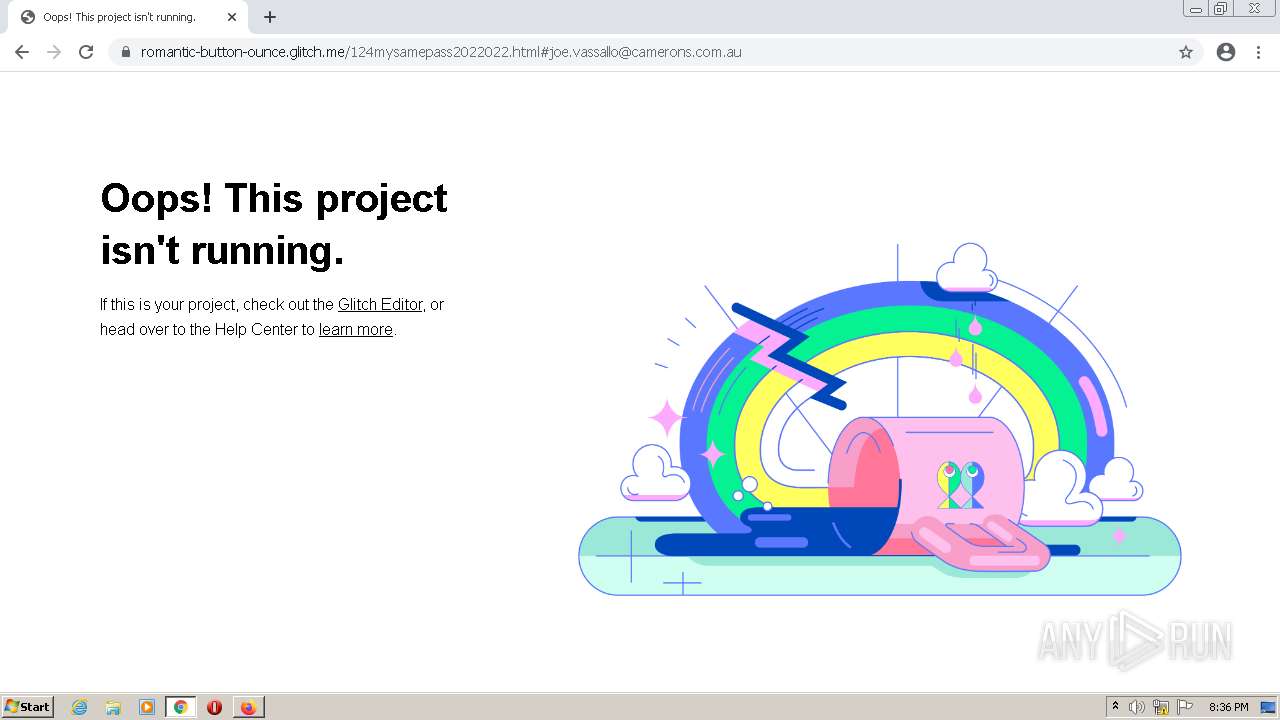
— | — | Misc activity | ET INFO Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
— | — | Misc activity | ET INFO Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
— | — | Misc activity | ET INFO Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
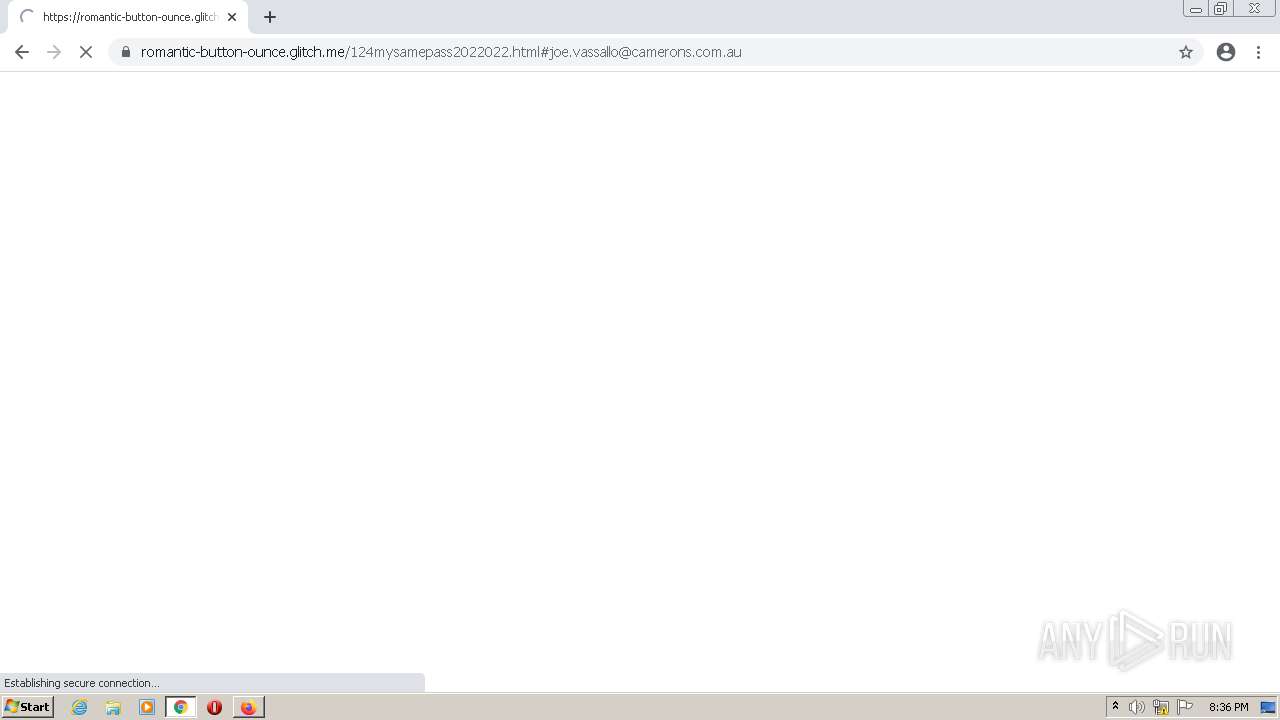
3456 | firefox.exe | Misc activity | ET INFO Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
3456 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3456 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3176 | chrome.exe | Misc activity | ET INFO Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
3176 | chrome.exe | Misc activity | ET INFO Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
3456 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3456 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |