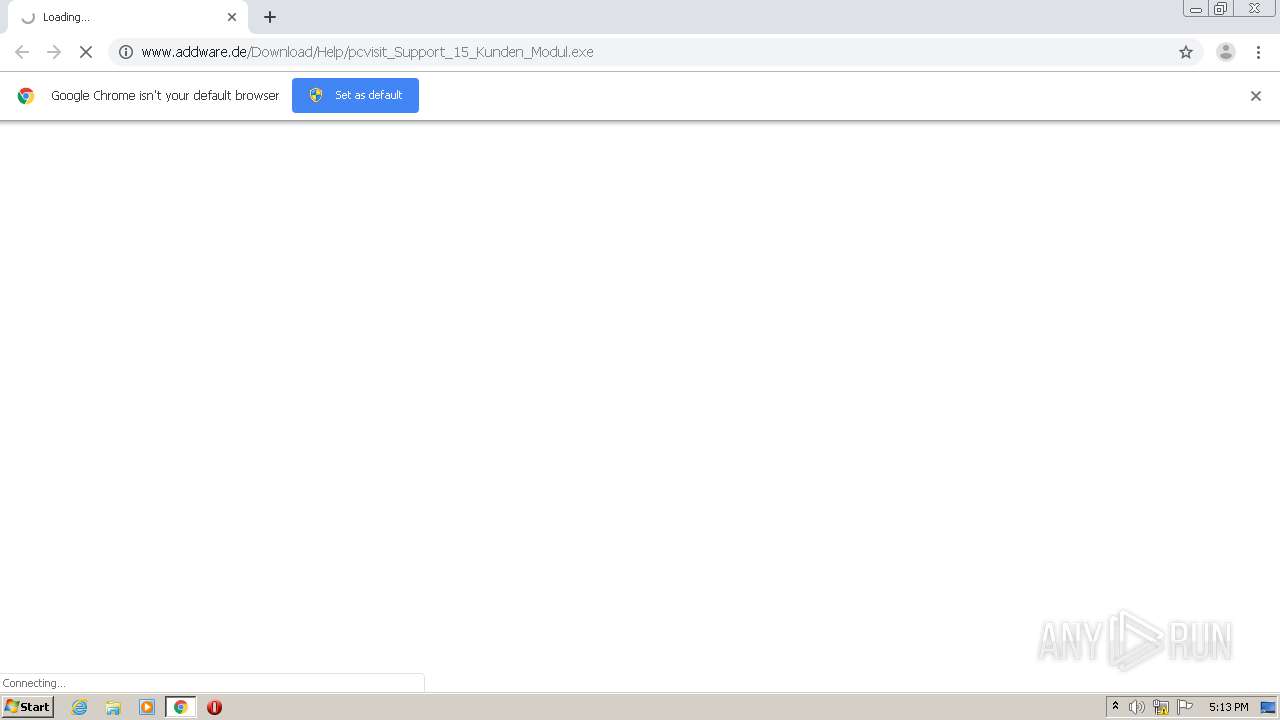
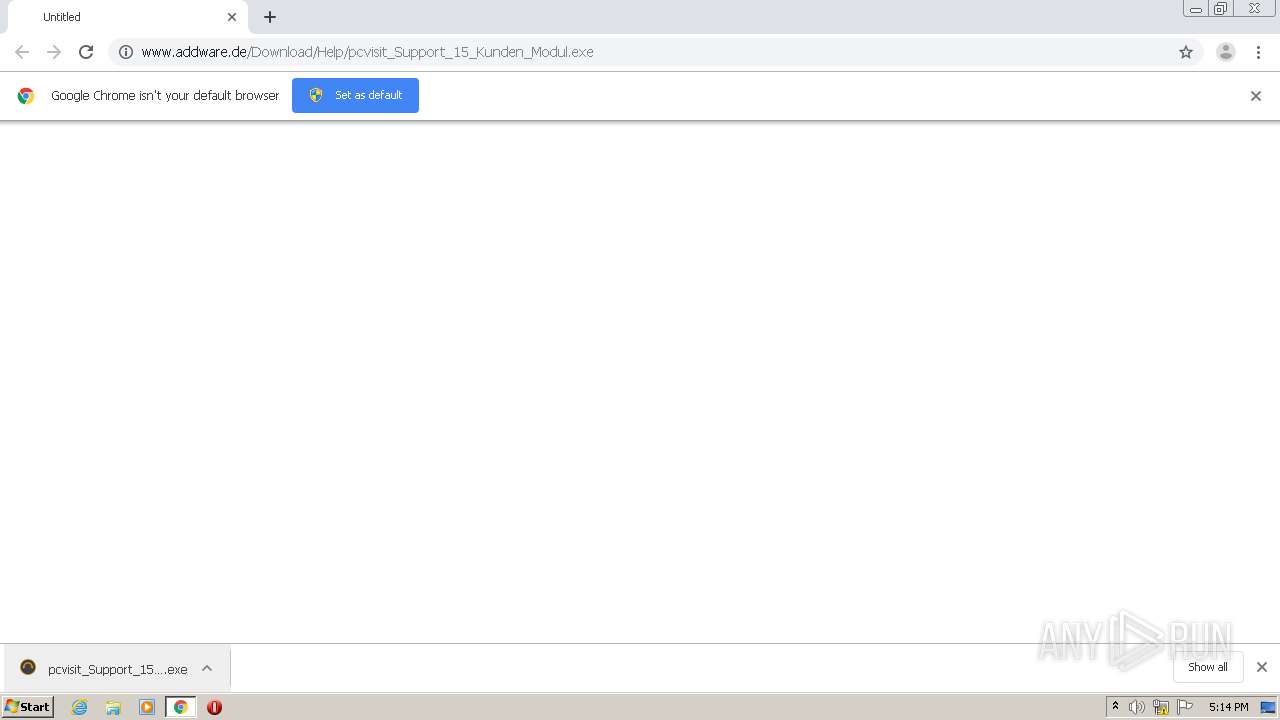
| URL: | http://www.addware.de/Download/Help/pcvisit_Support_15_Kunden_Modul.exe |
| Full analysis: | https://app.any.run/tasks/265e1921-aeef-4bec-b40b-0c4c4894638d |
| Verdict: | Malicious activity |
| Analysis date: | August 20, 2020, 16:13:44 |
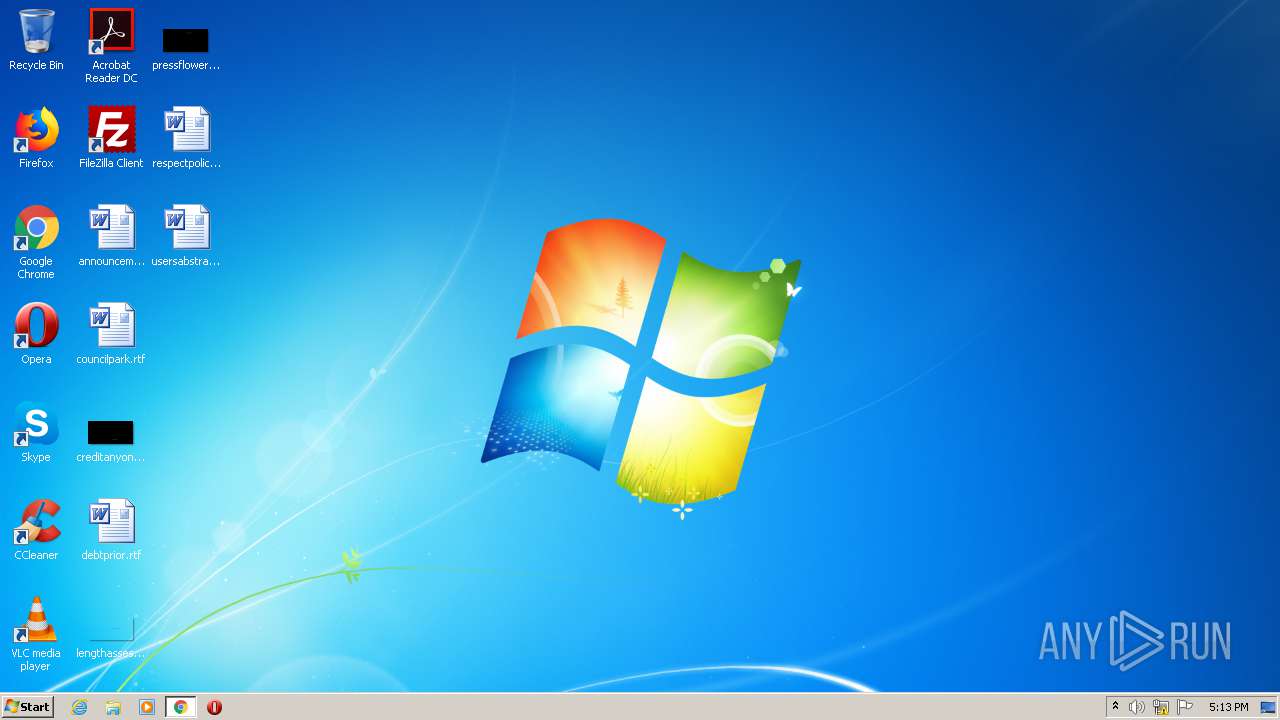
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7EA44DD38E95AFF3E17D2FB278EAF6A5 |
| SHA1: | 7BD3283EB1F65187AB9F8073476DBD844D14860F |
| SHA256: | BF6097069A26B2CE66F25E688A01FDECB3D0E47CF1D6BBE56BA61A65B71B6B9E |
| SSDEEP: | 3:N1KJS4cnOAC8yJgyMlSHJ6R6AdA:Cc4cOACvgflSp6R6AdA |
MALICIOUS
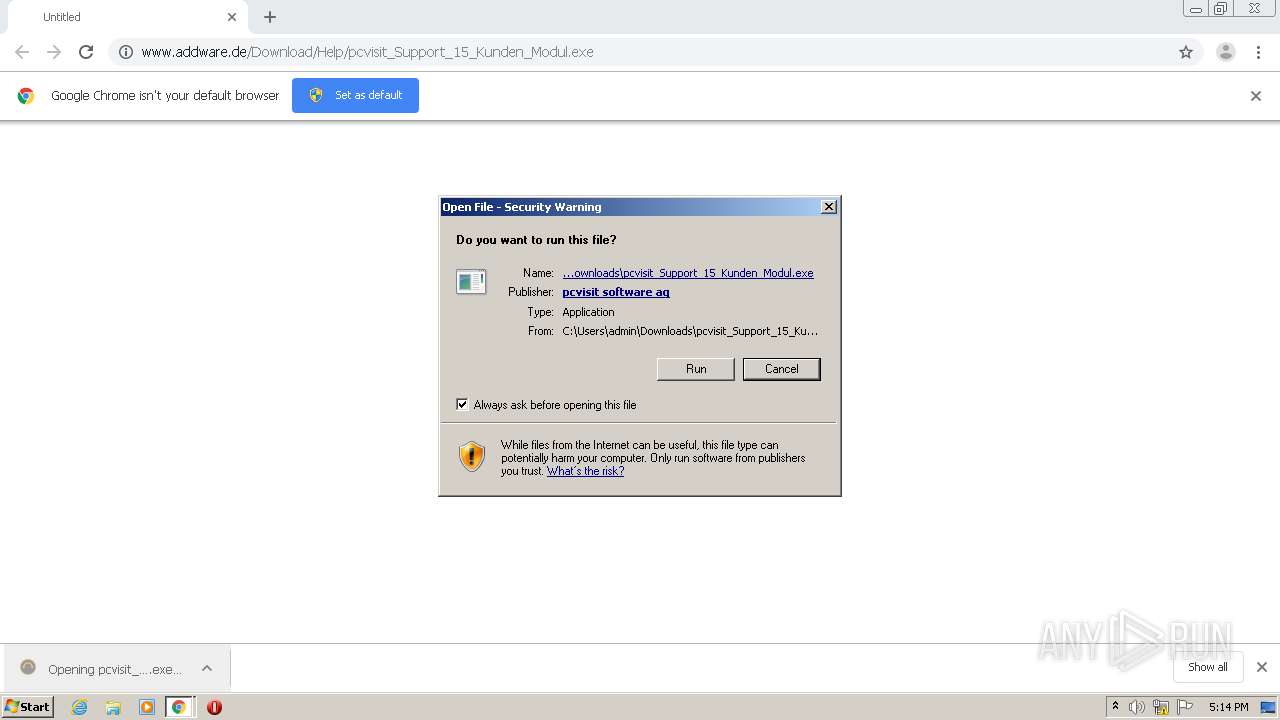
Application was dropped or rewritten from another process
- pcvisit_service_client.exe (PID: 4088)
- pcvisit_Support_15_Kunden_Modul.exe (PID: 2596)
Loads dropped or rewritten executable
- pcvisit_Support_15_Kunden_Modul.exe (PID: 2596)
- pcvisit_service_client.exe (PID: 4088)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2772)
- pcvisit_service_client.exe (PID: 4088)
- chrome.exe (PID: 2644)
- pcvisit_Support_15_Kunden_Modul.exe (PID: 2596)
Uses WMIC.EXE to obtain a list of video controllers
- pcvisit_service_client.exe (PID: 4088)
Creates files in the program directory
- pcvisit_service_client.exe (PID: 4088)
Reads Internet Cache Settings
- pcvisit_service_client.exe (PID: 4088)
Uses WMIC.EXE to obtain a system information
- pcvisit_service_client.exe (PID: 4088)
Executes PowerShell scripts
- pcvisit_service_client.exe (PID: 4088)
Creates files in the user directory
- powershell.exe (PID: 928)
INFO
Reads the hosts file
- chrome.exe (PID: 2772)
- chrome.exe (PID: 2644)
Application launched itself
- chrome.exe (PID: 2772)
Reads Internet Cache Settings
- chrome.exe (PID: 2772)
Dropped object may contain Bitcoin addresses
- pcvisit_Support_15_Kunden_Modul.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | powershell "get-ciminstance msft_physicaldisk -namespace root\microsoft\windows\storage | select model, size, allocatedsize, mediatype, healthstatus, bustype" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pcvisit_service_client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15618029008532887962,261999971011992728,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8141075932326515471 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | wmic bios get releasedate | C:\Windows\System32\Wbem\wmic.exe | — | pcvisit_service_client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15618029008532887962,261999971011992728,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=18415142224659349646 --mojo-platform-channel-handle=1136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,15618029008532887962,261999971011992728,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8271980709274715979 --mojo-platform-channel-handle=1064 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15618029008532887962,261999971011992728,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8790268162063317609 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
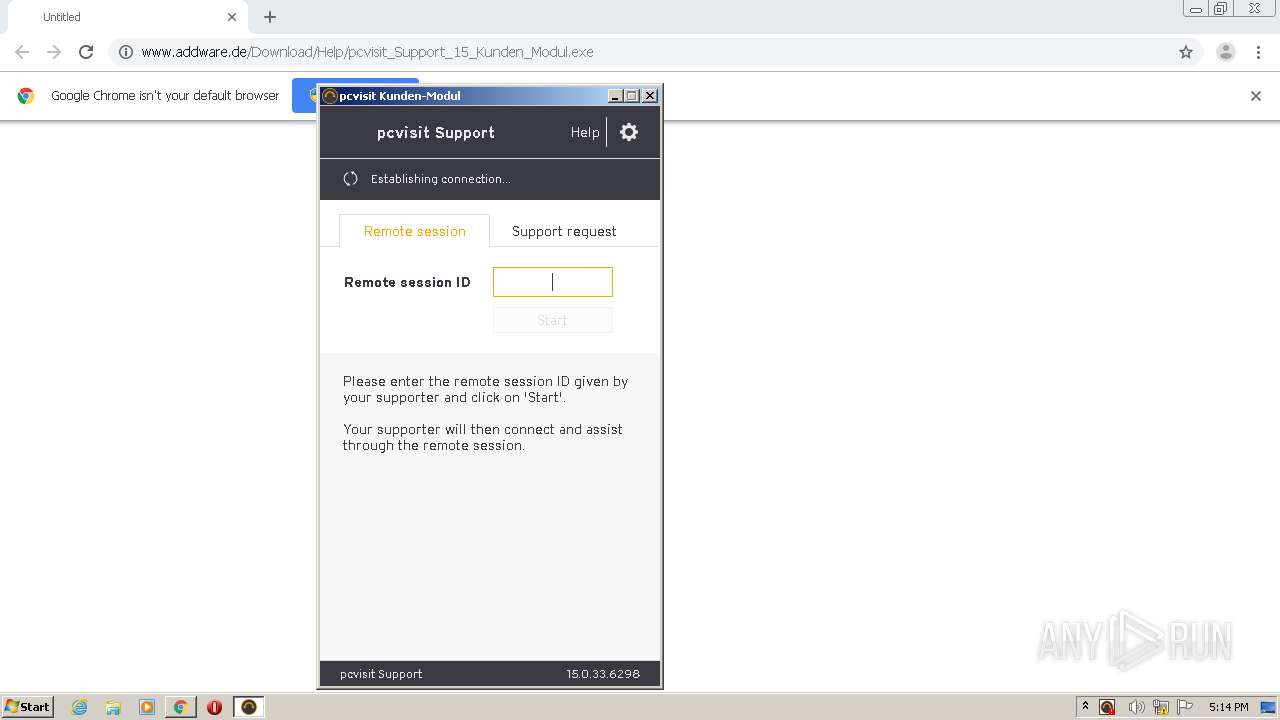
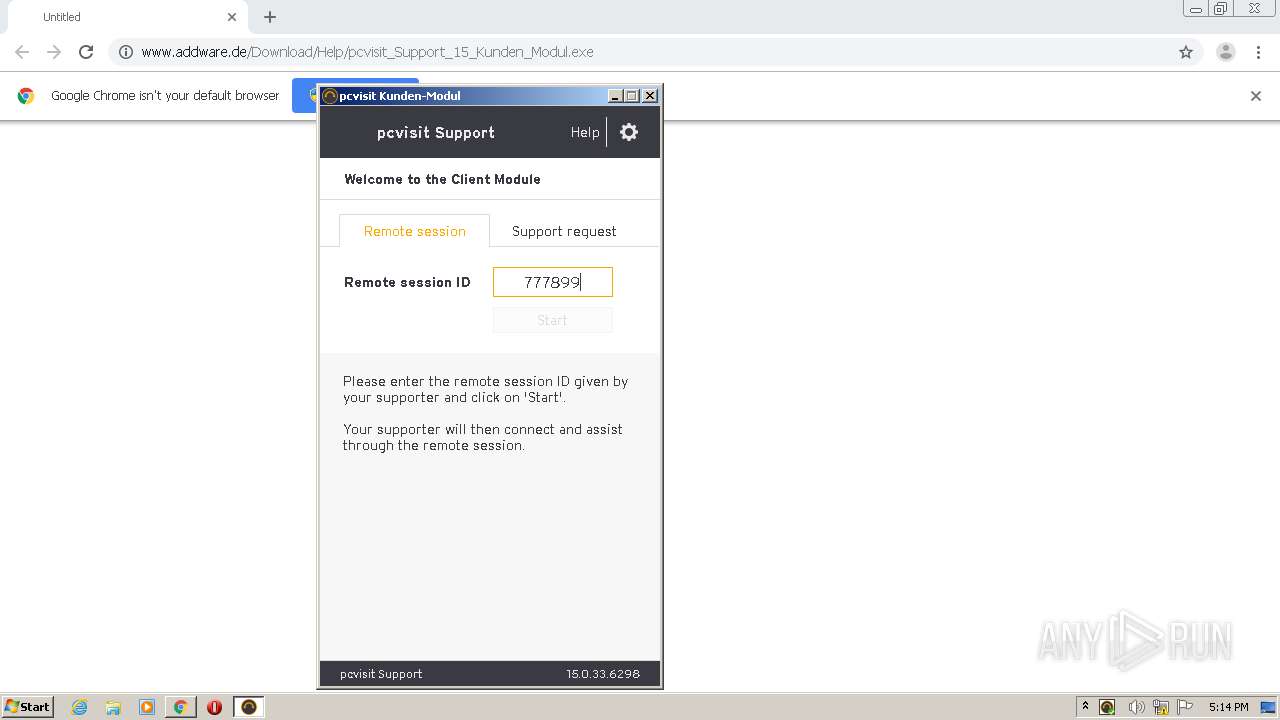
| 2596 | "C:\Users\admin\Downloads\pcvisit_Support_15_Kunden_Modul.exe" | C:\Users\admin\Downloads\pcvisit_Support_15_Kunden_Modul.exe | chrome.exe | ||||||||||||
User: admin Company: pcvisit Software AG Integrity Level: MEDIUM Description: pcvisit Support 15 Kunden-Modul Exit code: 2 Version: 15.0.33.6298 Modules
| |||||||||||||||
| 2600 | wmic diskdrive get model,size,mediatype,status | C:\Windows\System32\Wbem\wmic.exe | — | pcvisit_service_client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15618029008532887962,261999971011992728,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=146317602352022494 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2768 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 986
Read events
1 840
Write events
143
Delete events
3
Modification events
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2772-13242413638199750 |
Value: 259 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
33
Suspicious files
17
Text files
70
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b661afa9-f4de-4c2f-8cea-3a40efbd313b.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19115b.TMP | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF19118a.TMP | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF191340.TMP | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2772 | chrome.exe | GET | 200 | 2.17.46.169:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
2772 | chrome.exe | GET | 304 | 2.17.46.169:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
2644 | chrome.exe | GET | 301 | 212.223.140.104:80 | http://www.addware.de/Download/Help/pcvisit_Support_15_Kunden_Modul.exe | DE | html | 162 b | unknown |
4088 | pcvisit_service_client.exe | POST | 200 | 87.230.38.69:80 | http://lb3.pcvisit.de/detect.json | DE | text | 47 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2644 | chrome.exe | 212.223.140.104:443 | www.addware.de | Ratiokontakt GmbH | DE | unknown |
— | — | 212.223.140.104:80 | www.addware.de | Ratiokontakt GmbH | DE | unknown |
2644 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 216.58.212.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 2.17.46.169:80 | www.download.windowsupdate.com | Akamai Technologies, Inc. | — | malicious |
2644 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 212.223.140.104:80 | www.addware.de | Ratiokontakt GmbH | DE | unknown |
4088 | pcvisit_service_client.exe | 52.219.74.113:443 | pcvisit-master.s3.amazonaws.com | Amazon.com, Inc. | DE | unknown |
2644 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.addware.de |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
lb3.pcvisit.de |
| unknown |
pcvisit-master.s3.amazonaws.com |
| unknown |
Threats
Process | Message |
|---|---|
pcvisit_service_client.exe | Thu Aug 20 17:14:21 2020, 2020-08-20T16:14:21:899Z , 750
|
pcvisit_service_client.exe | LogException:0: |
pcvisit_service_client.exe | LogError:0: c:\jenkins\master_release_clean_v1\native_modules\libs\shared_app_elements\src\UiTools.cpp(42): P-T: $ff8-$fb8 : could not load dictionary 'C:\Users\admin\AppData\Local\pcvisit Software AG\caloa\pcvisit.Support.guest.15\release\15.0.33.6298\qtbase_en_US' try loading english default pack
|
pcvisit_service_client.exe | LogError:1: c:\jenkins\master_release_clean_v1\native_modules\libs\shared_app_elements\src\UiTools.cpp(46): P-T: $ff8-$fb8 : could not load dictionary 'C:\Users\admin\AppData\Local\pcvisit Software AG\caloa\pcvisit.Support.guest.15\release\15.0.33.6298\qtbase_en'
|
pcvisit_service_client.exe | Thu Aug 20 17:14:22 2020, 2020-08-20T16:14:22:264Z , 1114
|
pcvisit_service_client.exe | LogError:2: c:\jenkins\master_release_clean_v1\native_modules\libs\manager\src\threading\Process_w_Qt.cpp(107): P-T: $ff8-$3bc : set result to empty string
|
pcvisit_service_client.exe | LogError:2: c:\jenkins\master_release_clean_v1\native_modules\libs\manager\src\threading\Process_w_Qt.cpp(107): P-T: $ff8-$3bc : set result to empty string
|
pcvisit_service_client.exe | LogError:3: c:\jenkins\master_release_clean_v1\native_modules\apps\nacl\pcvisit_client\src\presentation\UI\StartView.cpp(769): P-T: $ff8-$fb8 : Invalid SessionID, due to hx_DoesNotExists
|
pcvisit_service_client.exe | LogError:4: c:\jenkins\master_release_clean_v1\native_modules\apps\nacl\pcvisit_client\src\presentation\UI\StartView.cpp(769): P-T: $ff8-$fb8 : Invalid SessionID, due to hx_DoesNotExists
|
pcvisit_service_client.exe | Thu Aug 20 17:14:48 2020, 2020-08-20T16:14:48:290Z , 27140
|