| File name: | bf5e00fa491b76fcceea0b8de133f5c28e20c556facce6652e6bca60fa946746.rar |
| Full analysis: | https://app.any.run/tasks/416a19b7-8fa7-4dcb-b215-2f4b89da6403 |
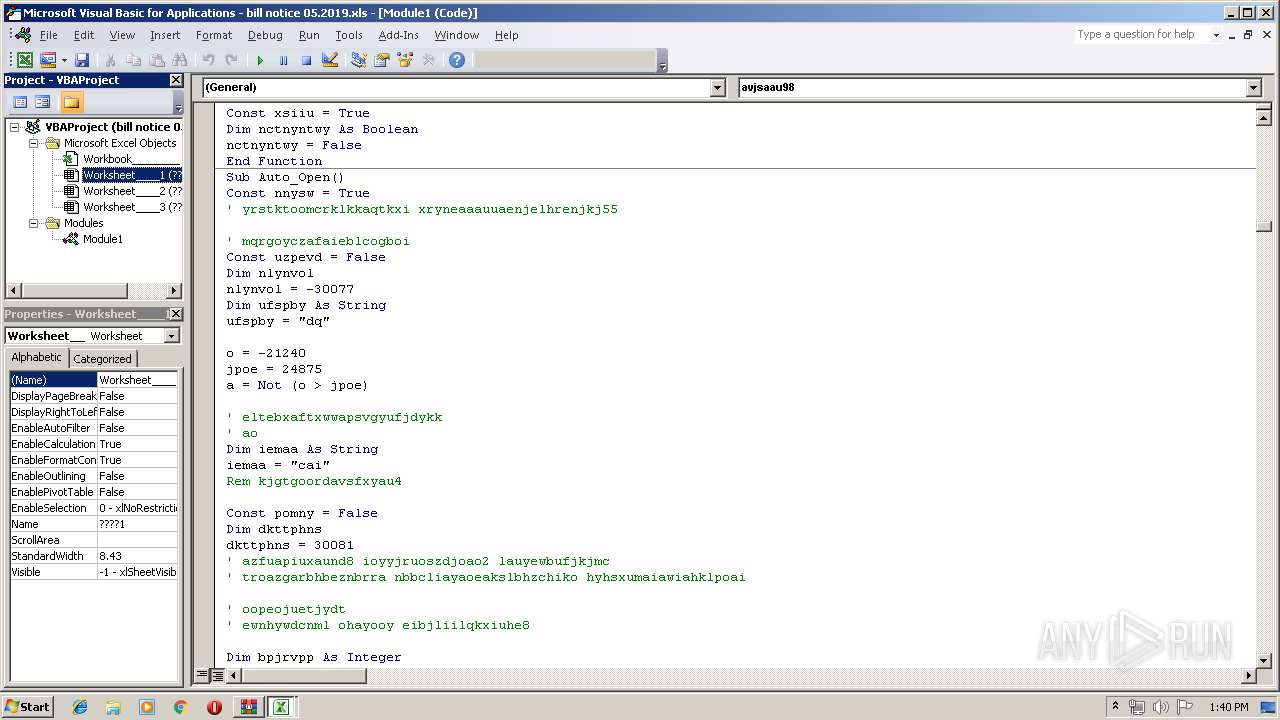
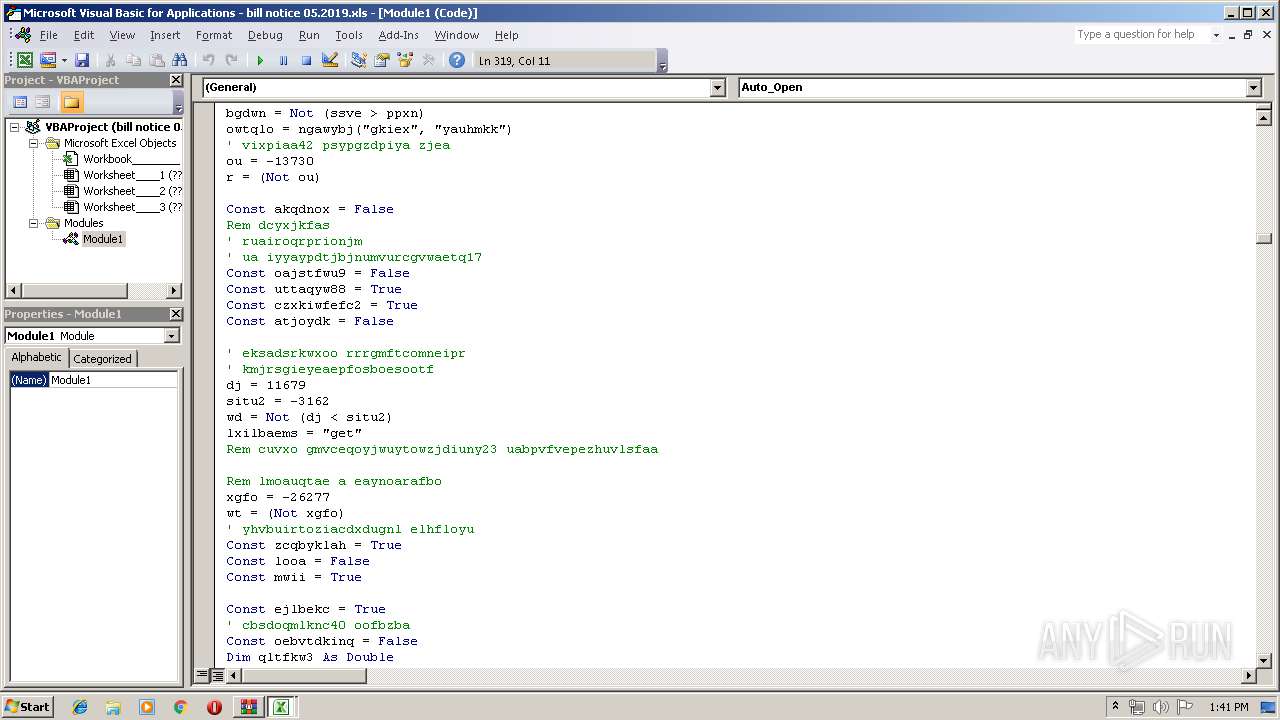
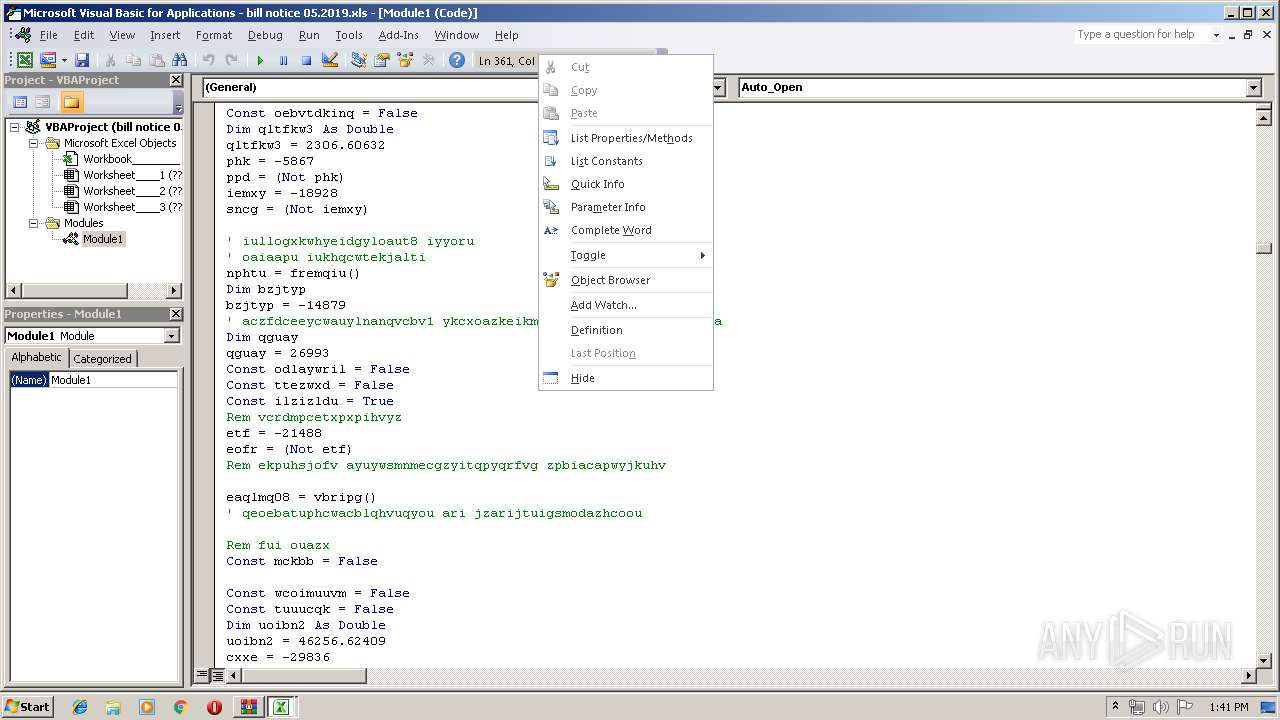
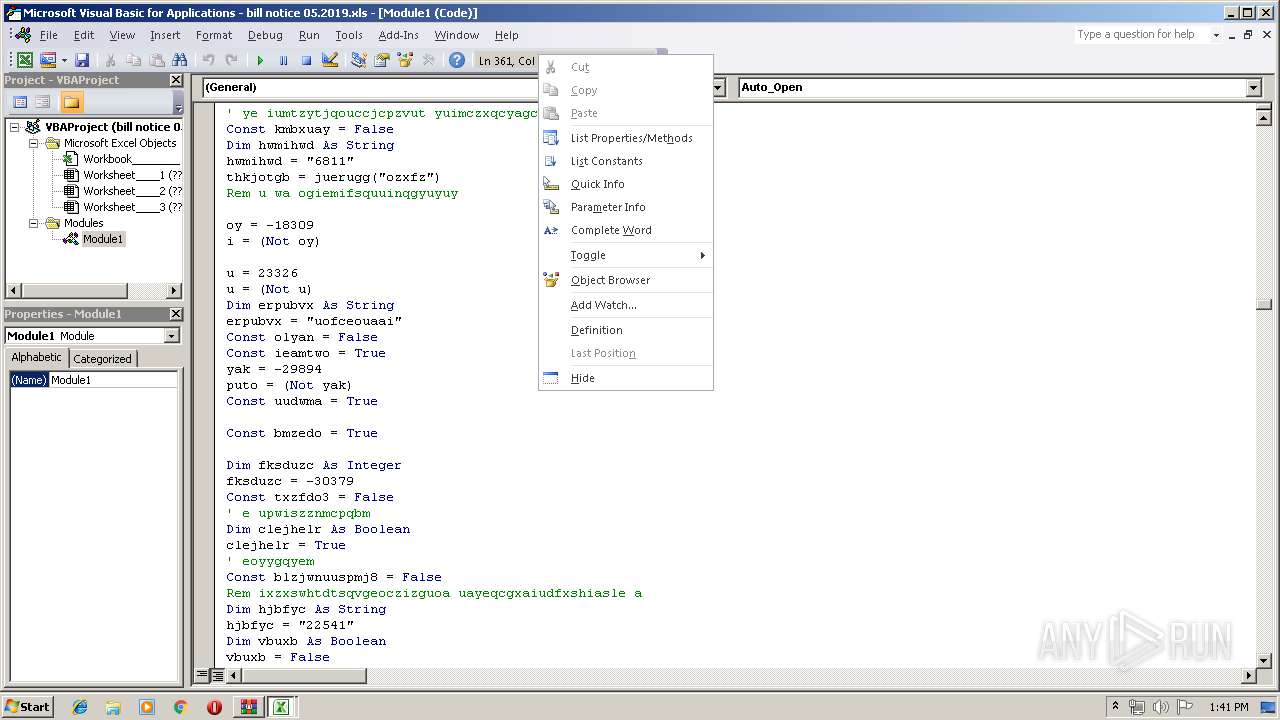
| Verdict: | Malicious activity |
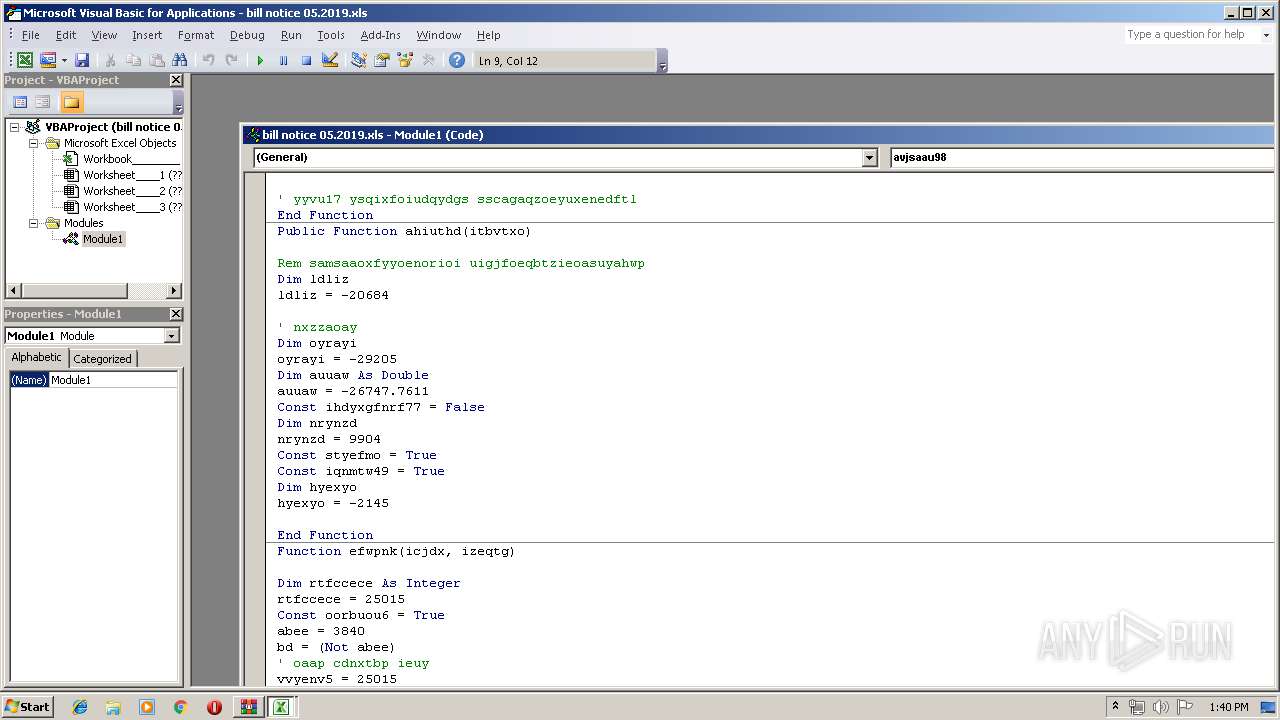
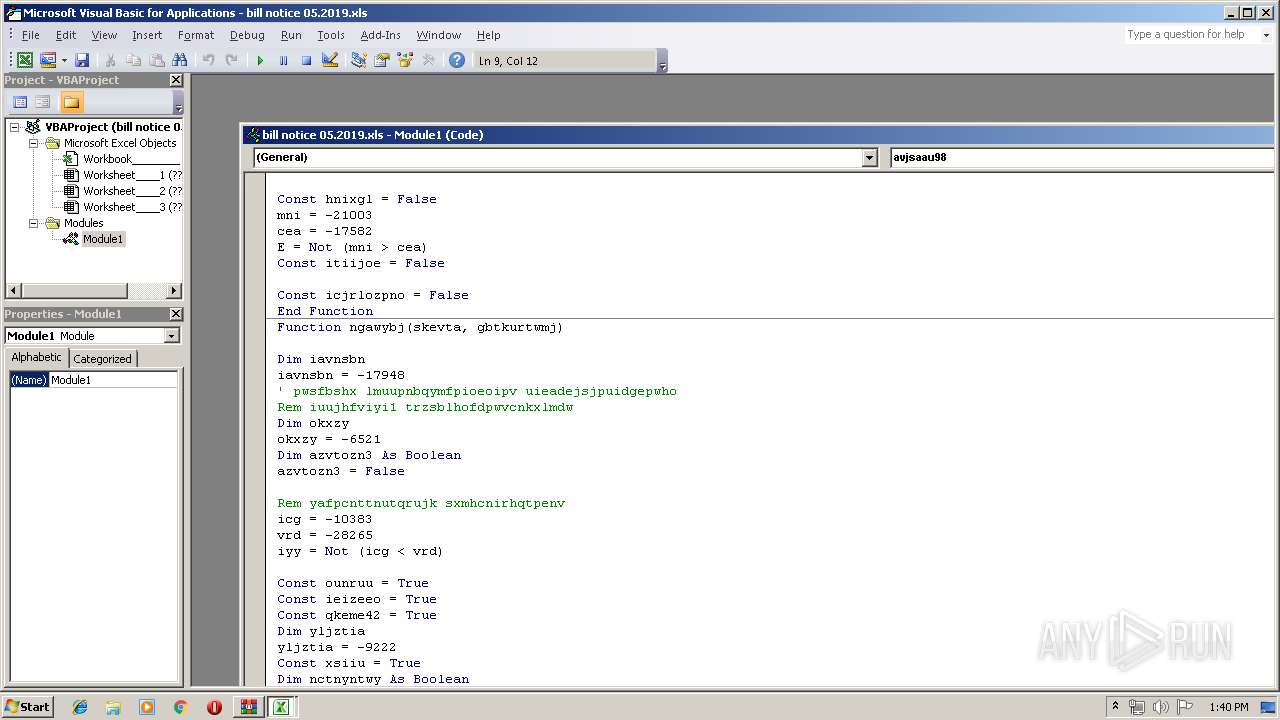
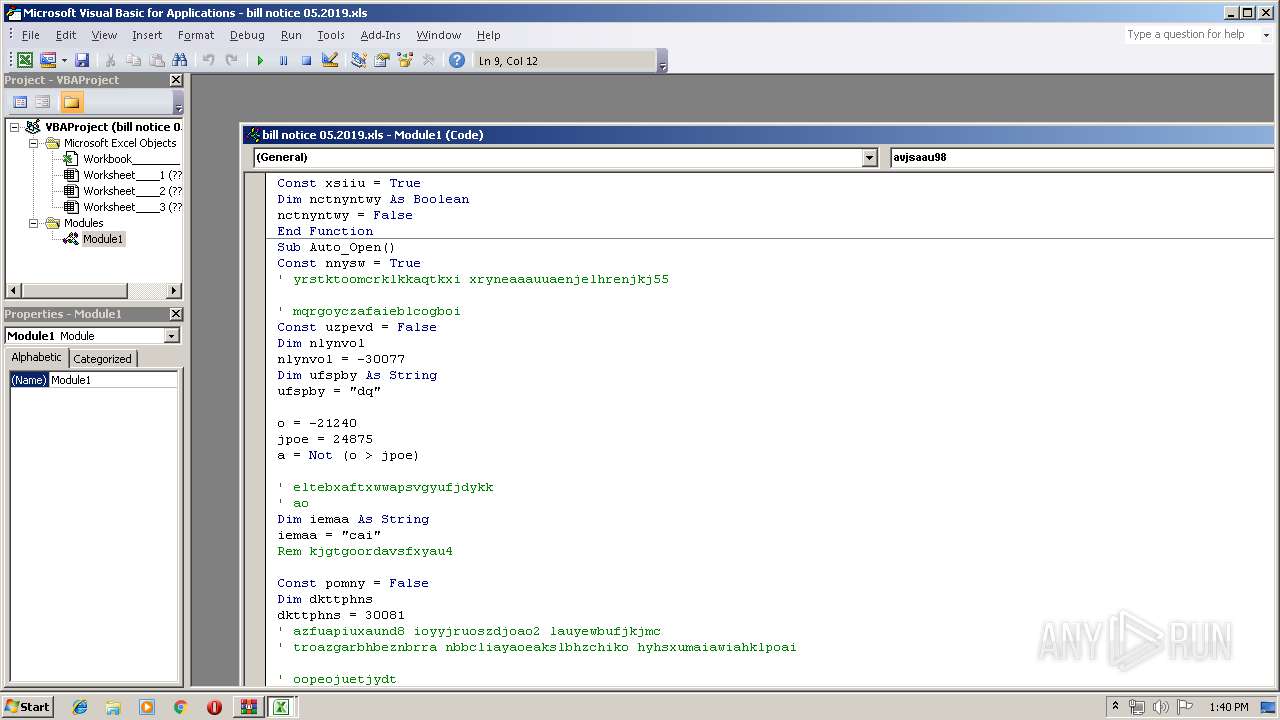
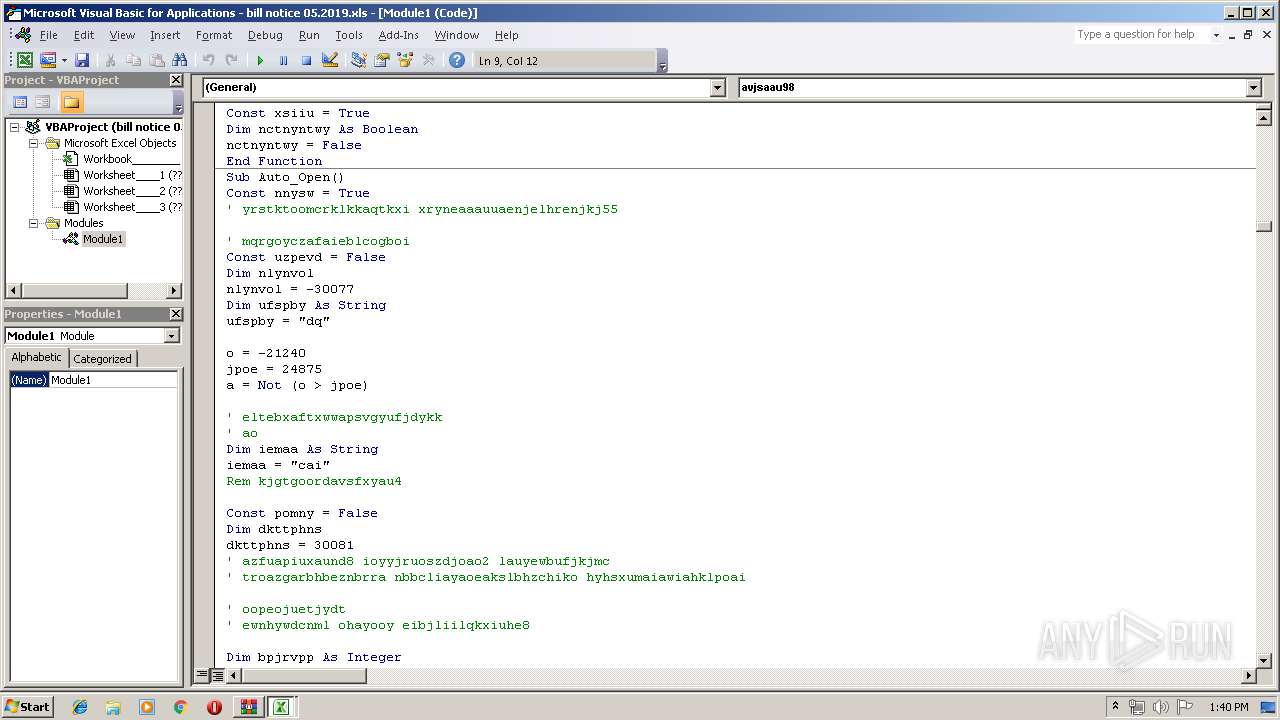
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
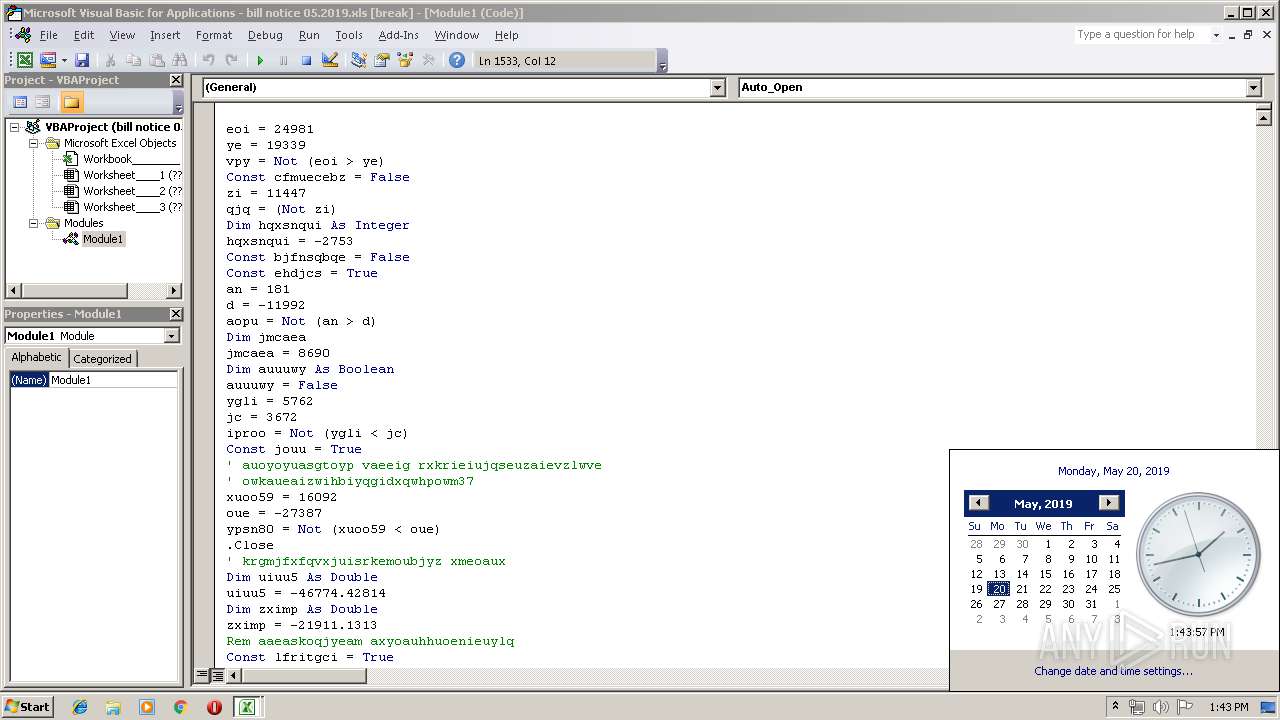
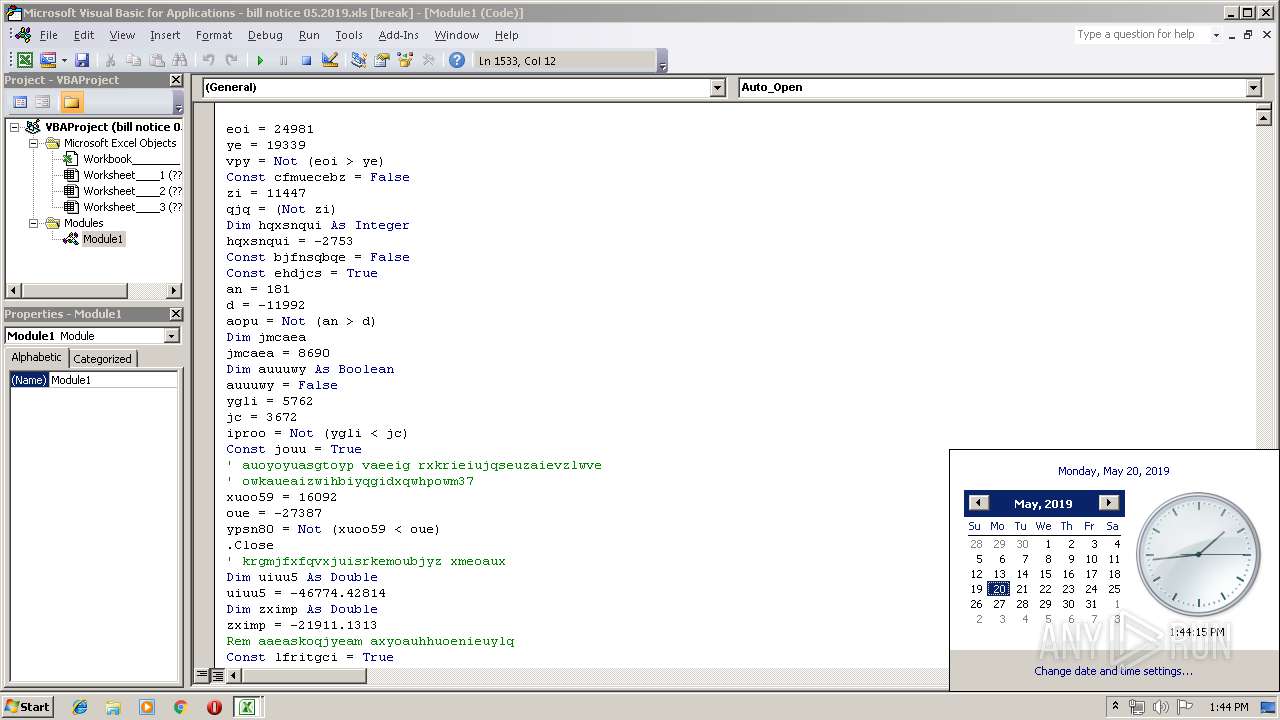
| Analysis date: | May 20, 2019, 12:39:15 |
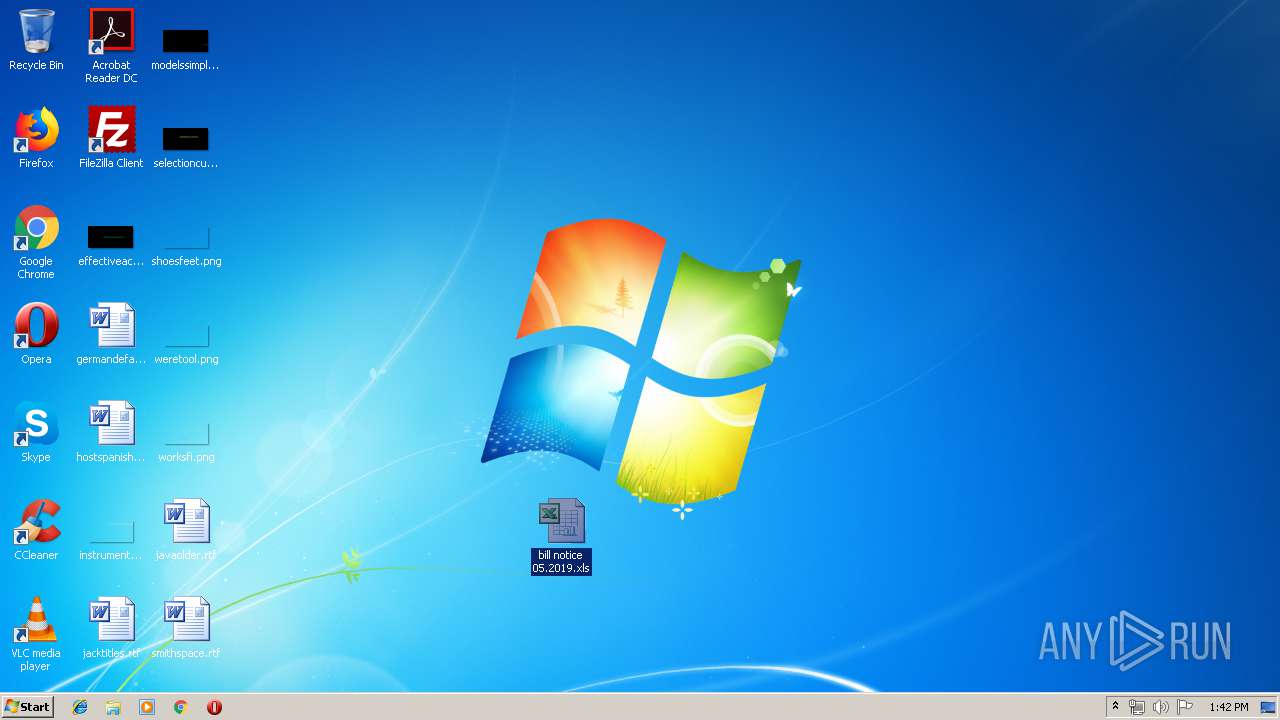
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
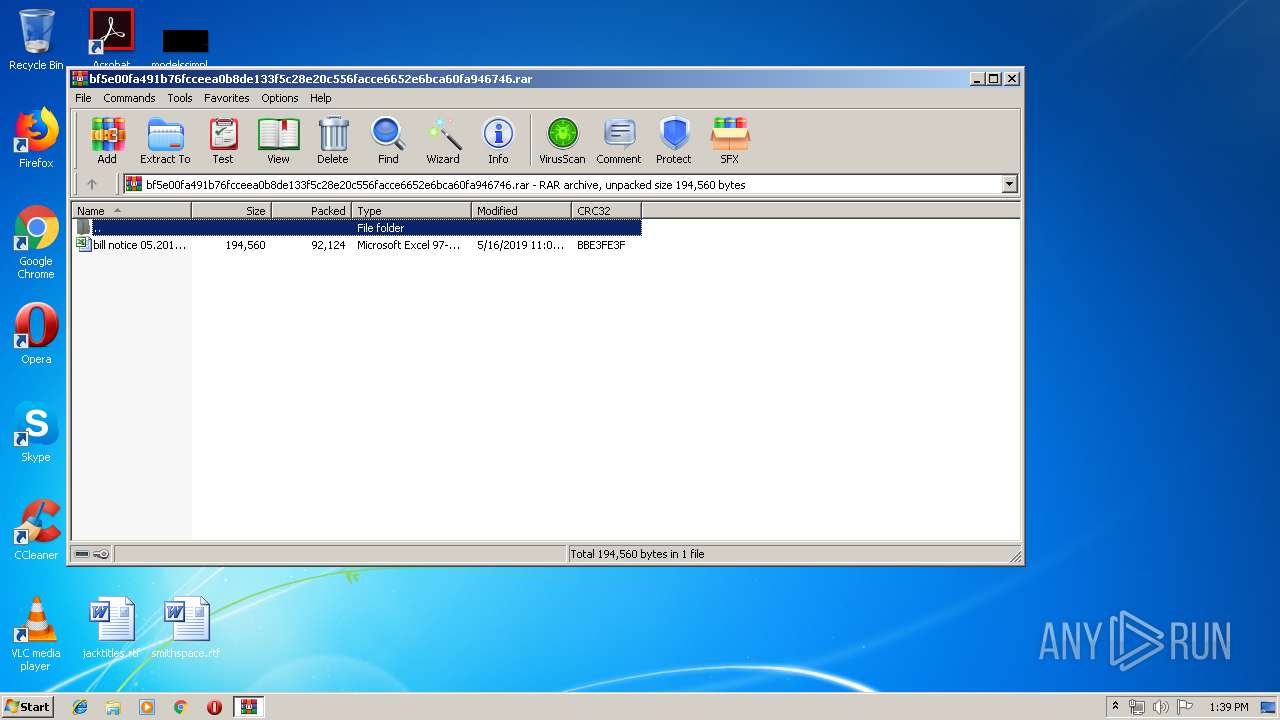
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0569CA387F8B950E00B99E9ACB612BE9 |
| SHA1: | 33D0CDACED6249AA93B4B1B54D2005A907EE563F |
| SHA256: | BF5E00FA491B76FCCEEA0B8DE133F5C28E20C556FACCE6652E6BCA60FA946746 |
| SSDEEP: | 1536:Tr99BZ4Hi14xpjaCvCl7fnrZ0L/gCwKzDQV+o5p5t/1MxxJZ/dd6mEpjKCqvDawE:d9BZ4Hddsl50LpwKzcV+CqxrZWFsawE |
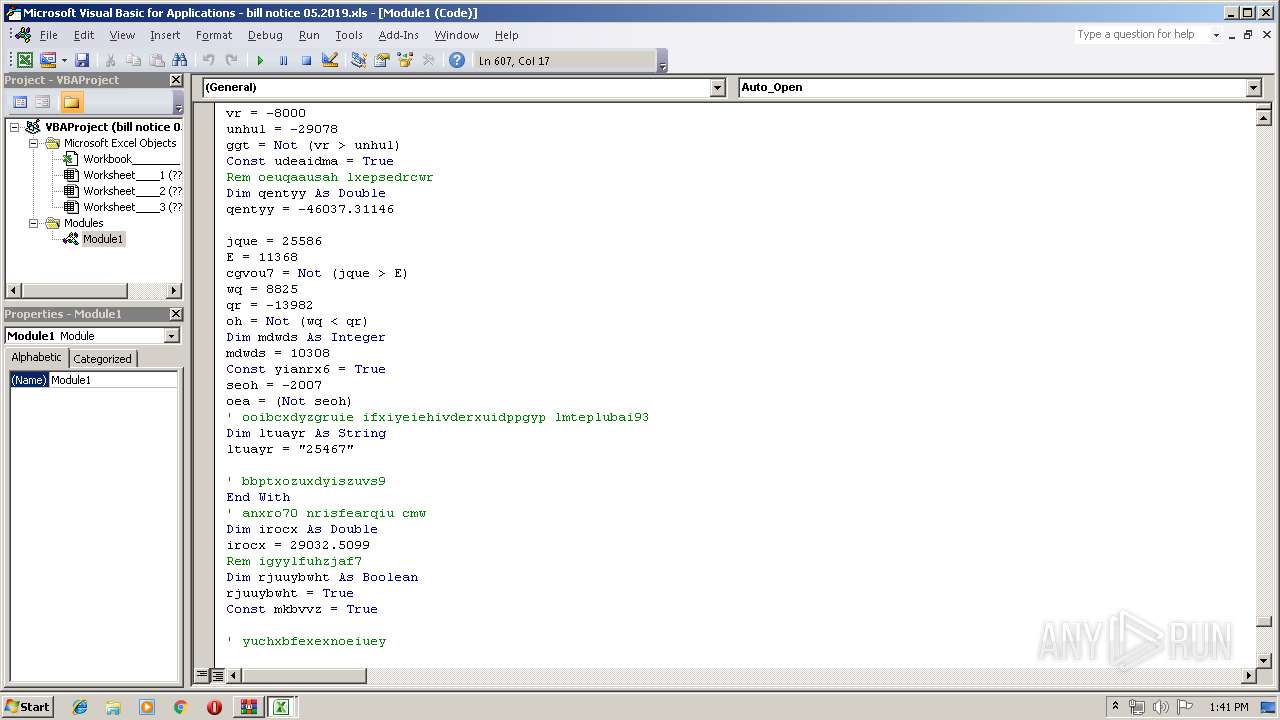
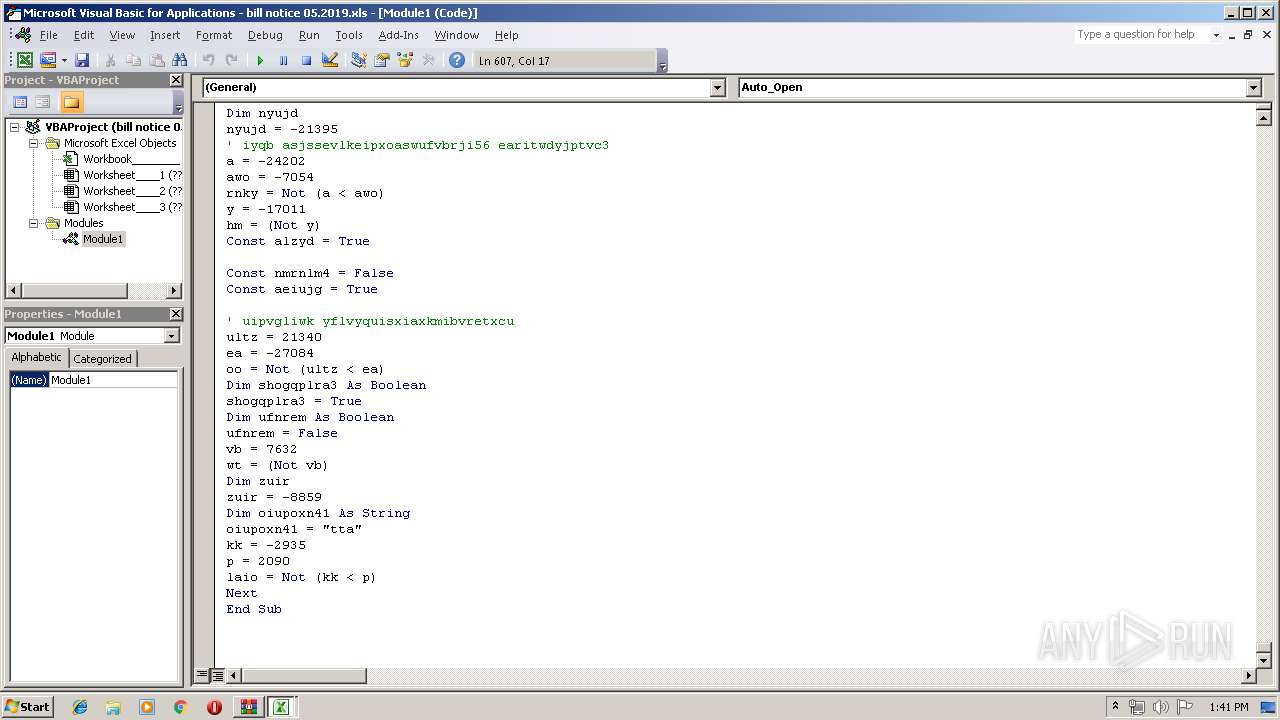
MALICIOUS
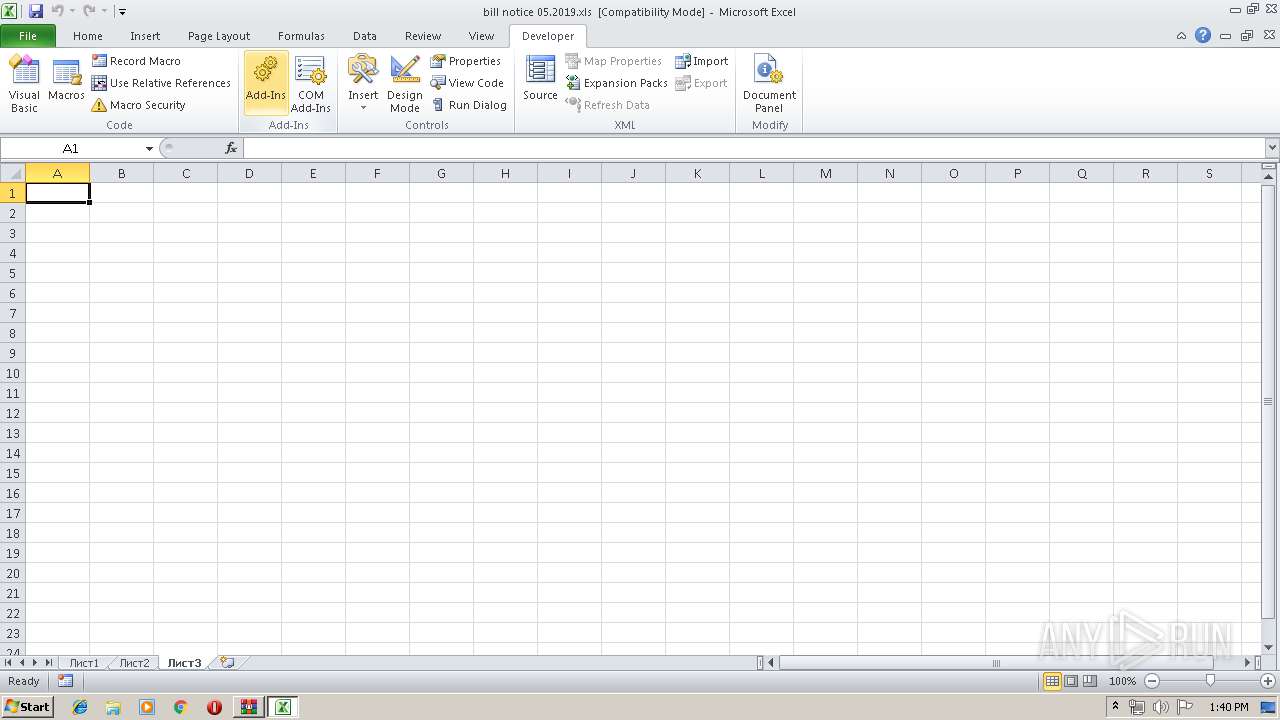
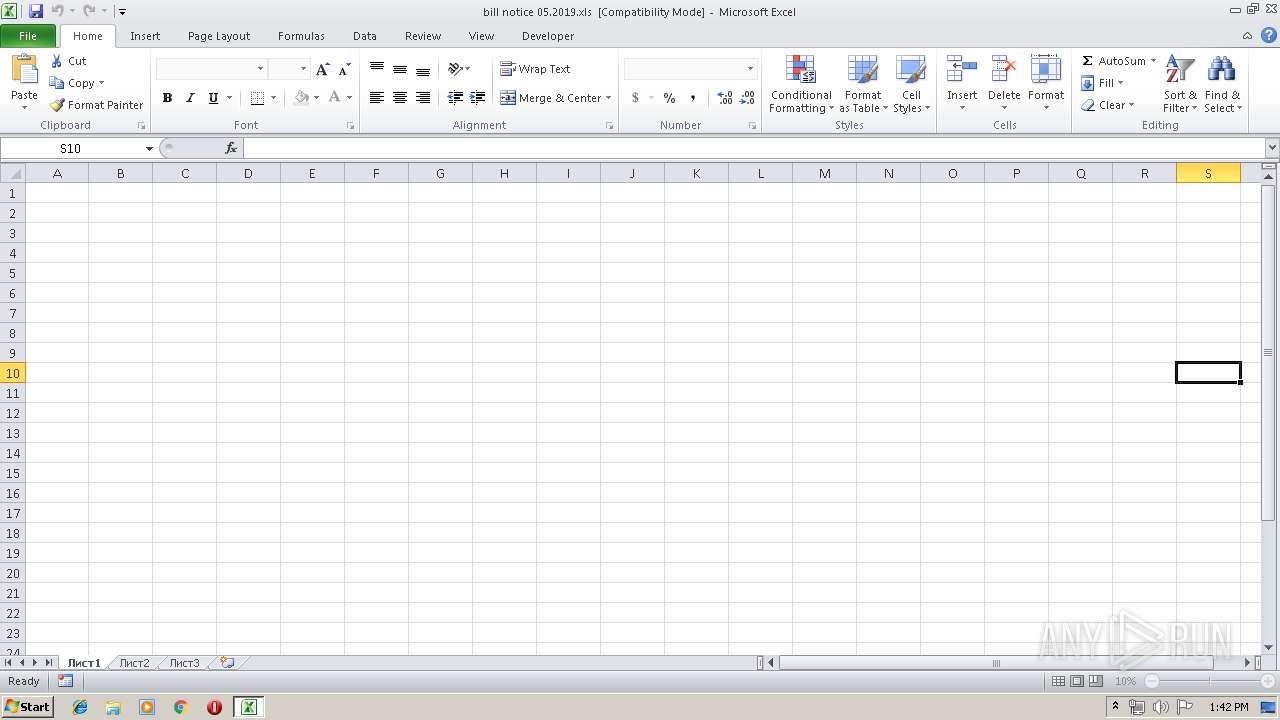
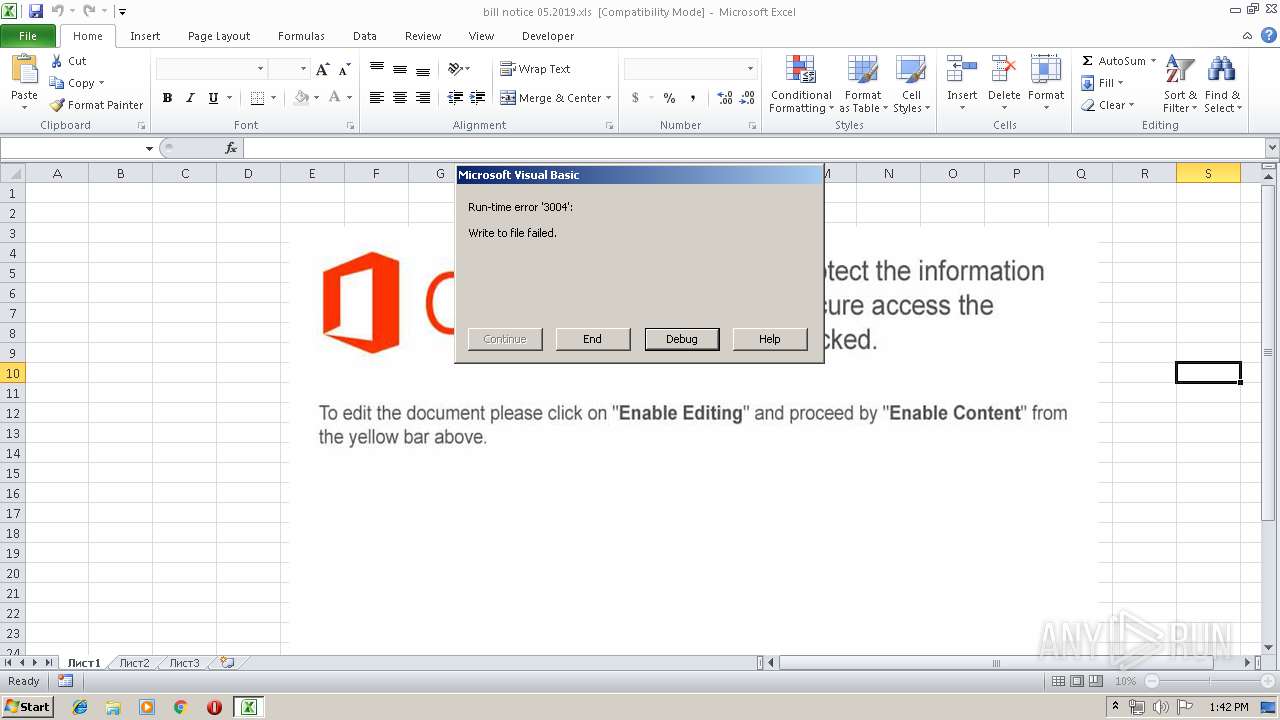
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1472)
- EXCEL.EXE (PID: 2316)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 1472)
- EXCEL.EXE (PID: 2316)
Application was dropped or rewritten from another process
- wprgxyeqd79.exe (PID: 3112)
- rtegre.exe (PID: 2852)
- wprgxyeqd79.exe (PID: 3392)
Loads dropped or rewritten executable
- wprgxyeqd79.exe (PID: 3112)
- svchost.exe (PID: 3524)
- EXCEL.EXE (PID: 1472)
- WinRAR.exe (PID: 2860)
- rtegre.exe (PID: 2852)
- OSPPSVC.EXE (PID: 3480)
- SearchProtocolHost.exe (PID: 3028)
- DllHost.exe (PID: 2224)
- SearchFilterHost.exe (PID: 1576)
- EXCEL.EXE (PID: 2316)
- wprgxyeqd79.exe (PID: 3392)
- svchost.exe (PID: 3244)
Loads the Task Scheduler COM API
- OSPPSVC.EXE (PID: 3480)
Stealing of credential data
- rtegre.exe (PID: 2852)
SUSPICIOUS
Executable content was dropped or overwritten
- wprgxyeqd79.exe (PID: 3112)
- wprgxyeqd79.exe (PID: 3392)
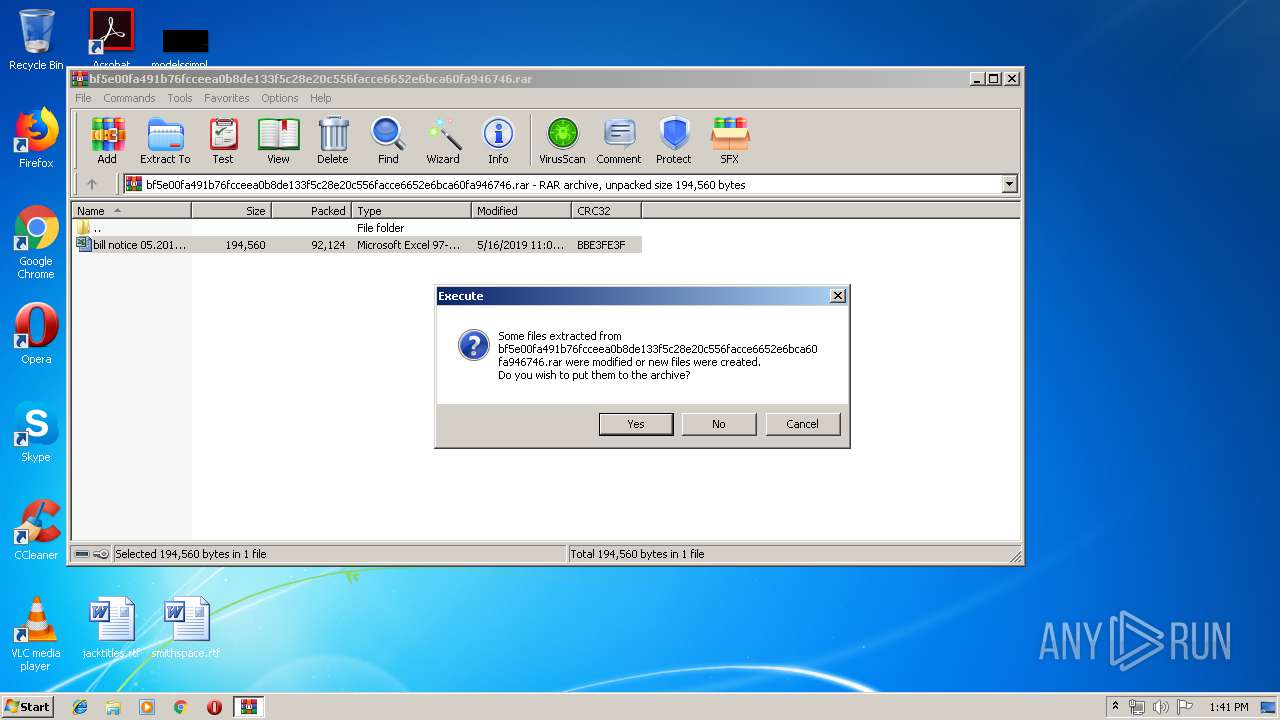
Starts Microsoft Office Application
- WinRAR.exe (PID: 2860)
Loads DLL from Mozilla Firefox
- rtegre.exe (PID: 2852)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1472)
- EXCEL.EXE (PID: 2316)
Creates files in the user directory
- EXCEL.EXE (PID: 1472)
- EXCEL.EXE (PID: 2316)
Dropped object may contain Bitcoin addresses
- EXCEL.EXE (PID: 1472)
- EXCEL.EXE (PID: 2316)
Manual execution by user
- EXCEL.EXE (PID: 2316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
43
Monitored processes
12
Malicious processes
4
Suspicious processes
2
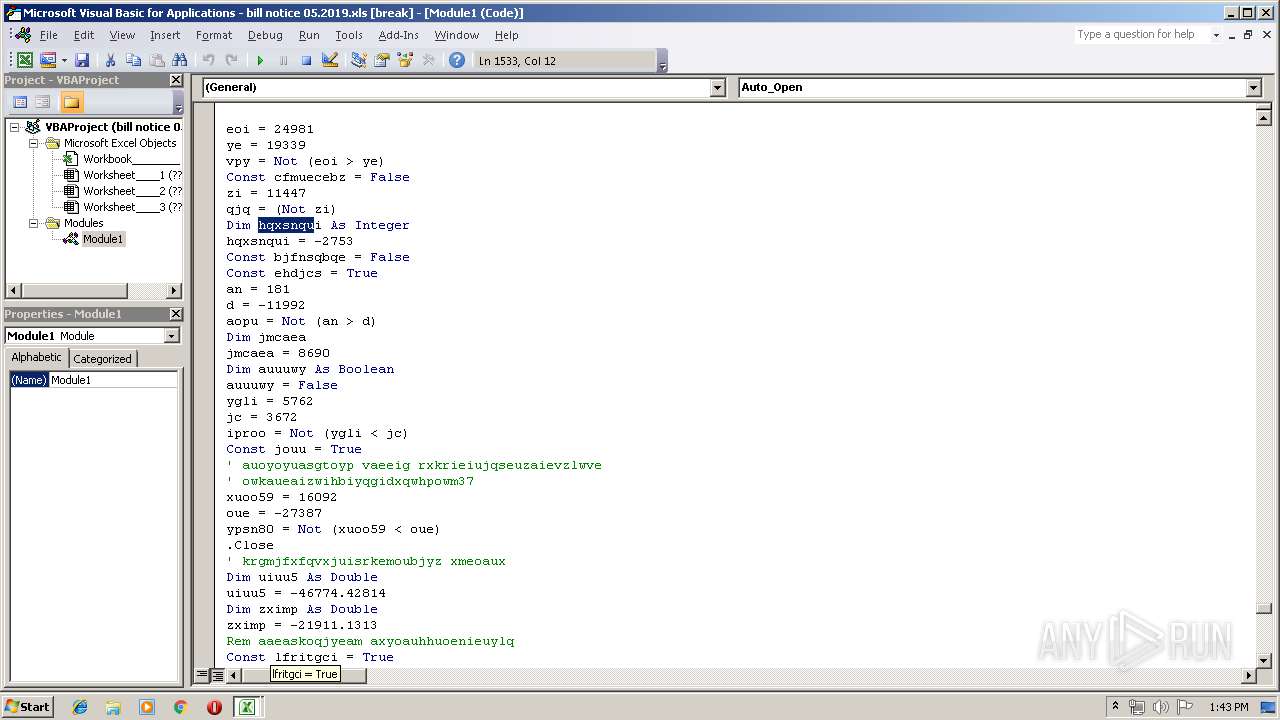
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
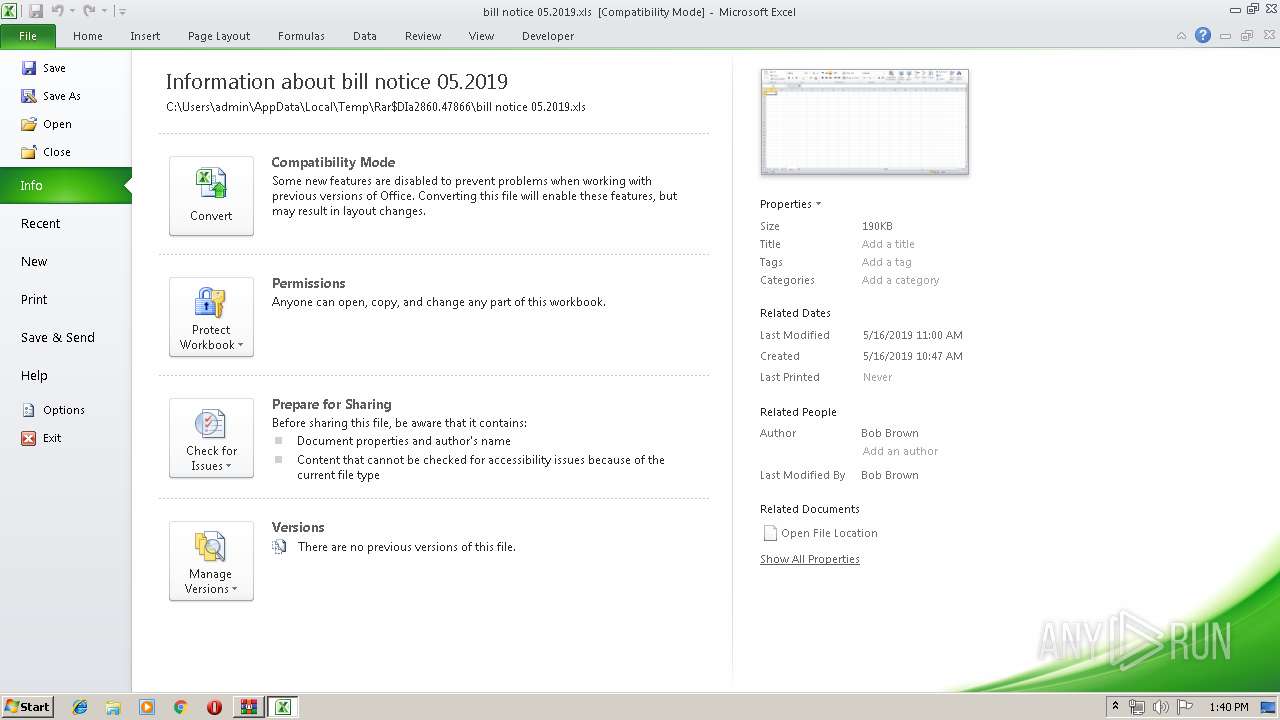
| 1472 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1576 | "C:\Windows\system32\SearchFilterHost.exe" 0 512 516 524 65536 520 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2852 | C:\Users\Public\rtegre.exe | C:\Users\Public\rtegre.exe | EXCEL.EXE | ||||||||||||
User: admin Company: x264 project Integrity Level: MEDIUM Description: Nkcreatestaticmapping Aboriginal Year Exit code: 0 Version: 5.7.3.790 Modules
| |||||||||||||||
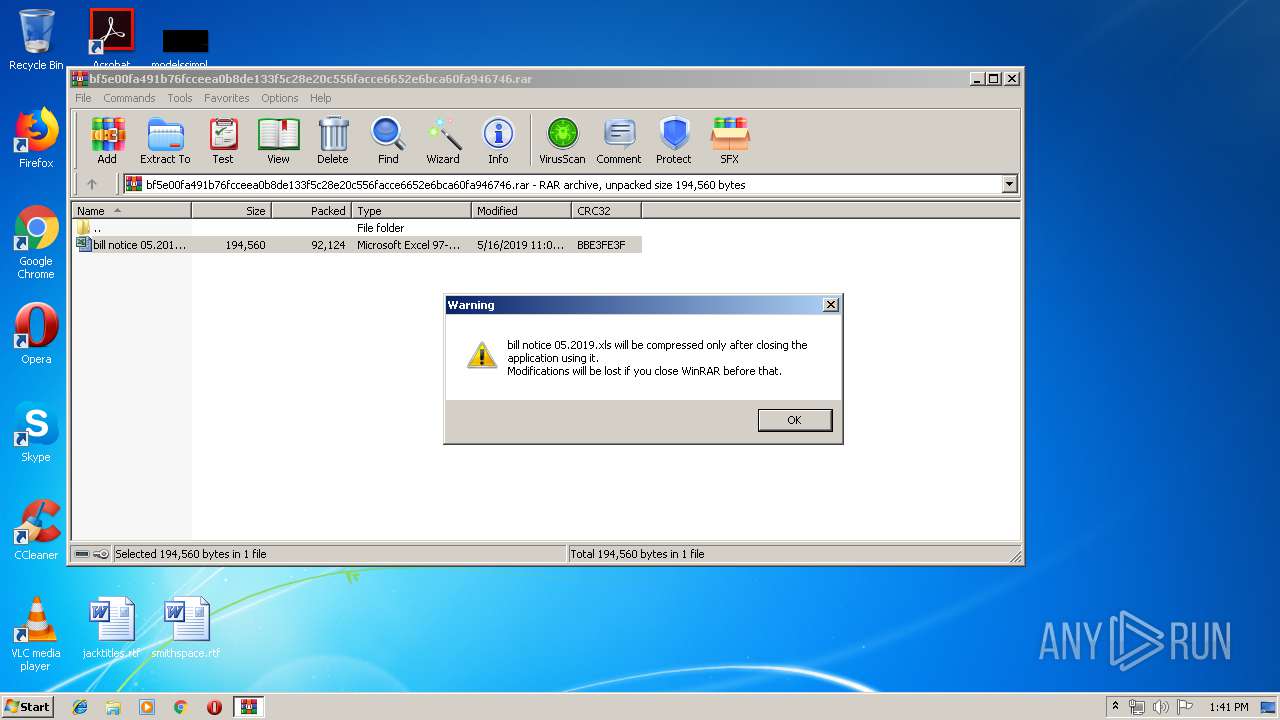
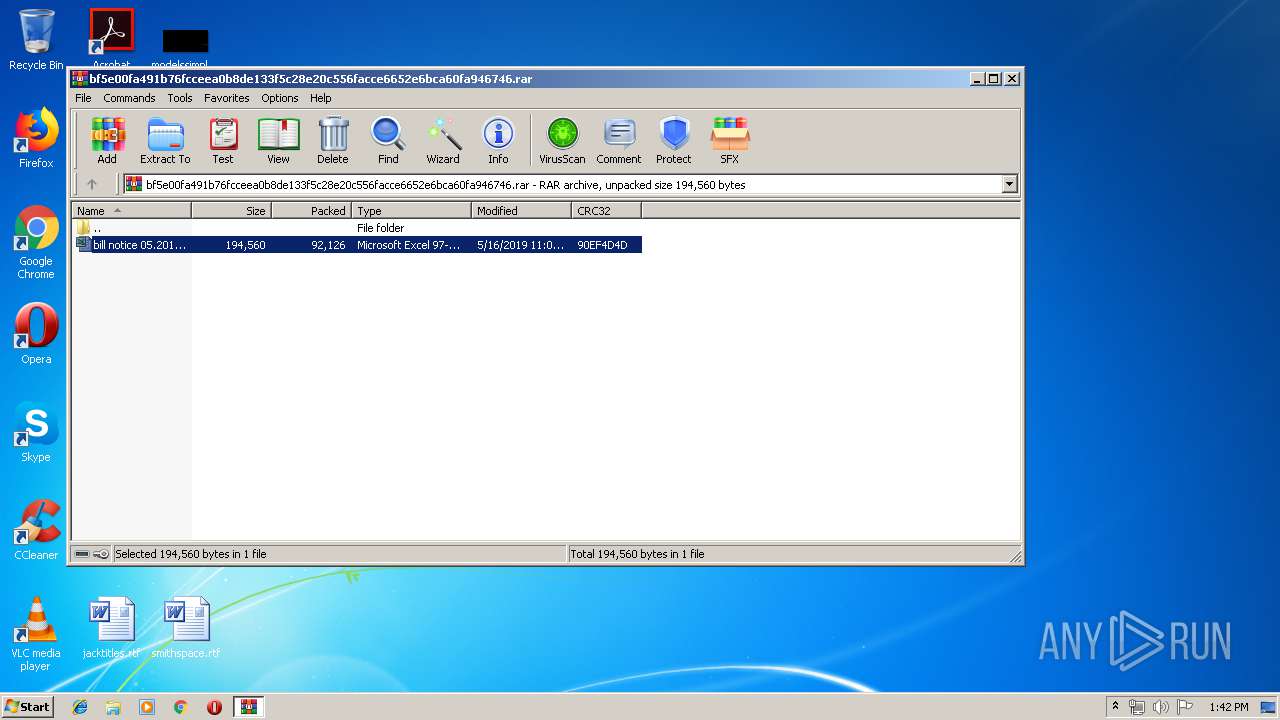
| 2860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\bf5e00fa491b76fcceea0b8de133f5c28e20c556facce6652e6bca60fa946746.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3028 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | C:\Users\Public\wprgxyeqd79.exe | C:\Users\Public\wprgxyeqd79.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Miranda IM Integrity Level: MEDIUM Description: Tile Textheight Clipbook Mostly Wading Exit code: 0 Version: 8.7.56.236 Modules
| |||||||||||||||
| 3244 | C:\Windows\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3392 | C:\Users\Public\wprgxyeqd79.exe | C:\Users\Public\wprgxyeqd79.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Miranda IM Integrity Level: MEDIUM Description: Tile Textheight Clipbook Mostly Wading Exit code: 0 Version: 8.7.56.236 Modules
| |||||||||||||||
Total events
2 653
Read events
2 478
Write events
154
Delete events
21
Modification events
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\bf5e00fa491b76fcceea0b8de133f5c28e20c556facce6652e6bca60fa946746.rar | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1320419345 | |||
| (PID) Process: | (1472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | /< |
Value: 2F7F3C00C0050000010000000000000000000000 | |||
Executable files
8
Suspicious files
5
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR2B0F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\msoE24B.tmp | — | |
MD5:— | SHA256:— | |||
| 1472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\msoE25B.tmp | — | |
MD5:— | SHA256:— | |||
| 1472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFE3985E0E6AD524F5.TMP | — | |
MD5:— | SHA256:— | |||
| 1472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFDF848E2BC84CBE54.TMP | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rar_2860.12374 | — | |
MD5:— | SHA256:— | |||
| 2316 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR7ED3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2852 | rtegre.exe | C:\Users\admin\AppData\Local\Temp\{F13B6488-555C-4C41-A787-BC3C2EBB777B}\log | — | |
MD5:— | SHA256:— | |||
| 1472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\pasmmm[1].exe | executable | |
MD5:— | SHA256:— | |||
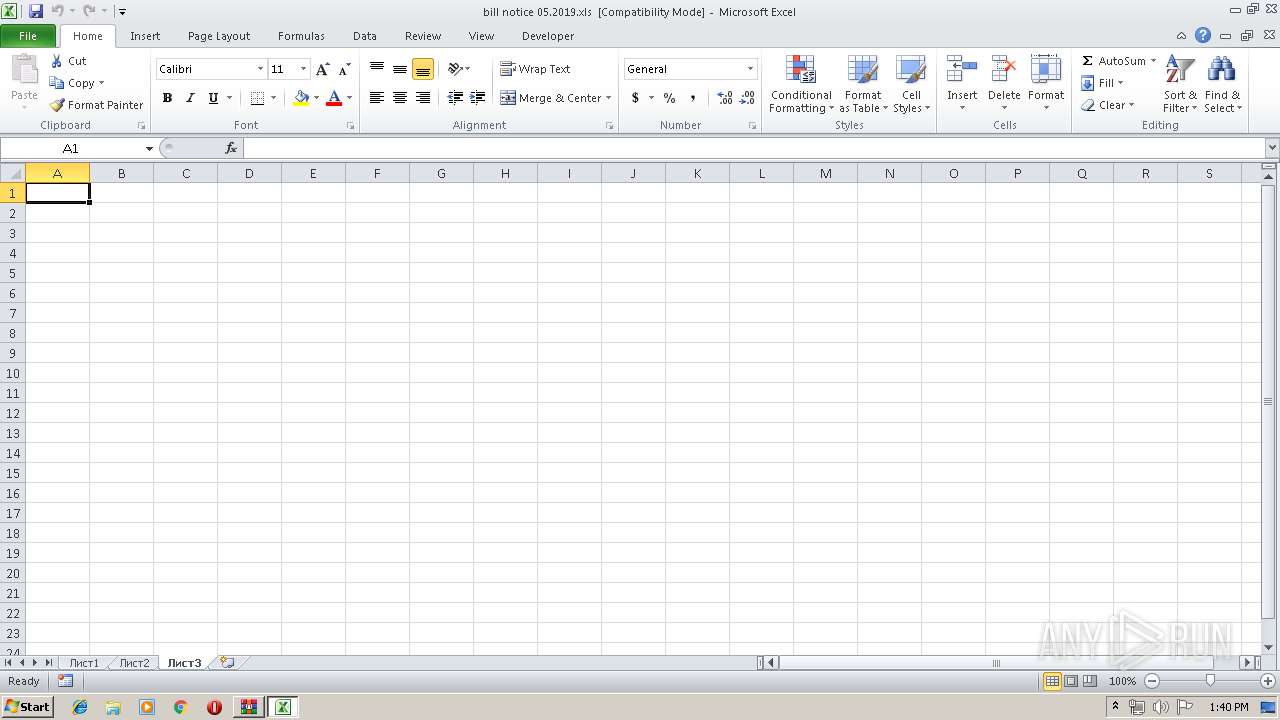
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2860.47866\bill notice 05.2019.xls | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
34
DNS requests
3
Threats
70
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2852 | rtegre.exe | GET | — | 66.111.2.131:9030 | http://66.111.2.131:9030/tor/status-vote/current/consensus | US | — | — | suspicious |
2852 | rtegre.exe | GET | — | 185.26.127.24:80 | http://185.26.127.24/tor/server/fp/53b8b5c2a33c489b54300d558bfee2c3b12f3875 | LU | — | — | suspicious |
2852 | rtegre.exe | GET | — | 93.115.86.6:80 | http://93.115.86.6/tor/server/fp/508eaaa5322c7bf048c8fadbbfb37d0a3e1d9262 | RO | — | — | suspicious |
2852 | rtegre.exe | GET | — | 185.217.93.92:80 | http://185.217.93.92/tor/server/fp/1b9638c3e98d8e9dc03350b25e87128cc79860d8 | NL | — | — | suspicious |
2852 | rtegre.exe | GET | — | 51.77.72.200:80 | http://51.77.72.200/tor/server/fp/592031cfdba17dd46e1e365e6c60ad1f81655033 | GB | — | — | suspicious |
2852 | rtegre.exe | GET | — | 94.156.175.120:80 | http://94.156.175.120/tor/server/fp/495985474f547b5d97acb2941c7aed048d7e7e14 | BG | — | — | suspicious |
2852 | rtegre.exe | GET | — | 212.186.71.38:80 | http://212.186.71.38/tor/server/fp/52bfada8beaa01ba46c8f767f83c18e2fe50c1b9 | AT | — | — | suspicious |
2852 | rtegre.exe | GET | — | 185.10.68.52:80 | http://185.10.68.52/tor/server/fp/bcc274eff09434289b2471df35cfff0894f54d25 | SC | — | — | malicious |
2852 | rtegre.exe | GET | — | 199.249.230.67:80 | http://199.249.230.67/tor/server/fp/424bf86927e80d916589bb12248bd468bb470684 | US | — | — | suspicious |
2852 | rtegre.exe | GET | — | 49.50.107.221:80 | http://49.50.107.221/tor/server/fp/d1afbf3117b308b6d1a7aa762b1315fd86a6b8af | IN | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1472 | EXCEL.EXE | 47.245.58.124:443 | kentona.su | — | US | suspicious |
2852 | rtegre.exe | 66.111.2.131:9030 | — | The New York Internet Company | US | suspicious |
2852 | rtegre.exe | 23.21.121.219:443 | api.ipify.org | Amazon.com, Inc. | US | whitelisted |
2852 | rtegre.exe | 185.26.127.24:80 | — | GANDI SAS | LU | suspicious |
2852 | rtegre.exe | 104.244.77.111:443 | — | FranTech Solutions | US | suspicious |
— | — | 129.6.15.28:13 | time-a.nist.gov | National Bureau of Standards | US | unknown |
2852 | rtegre.exe | 93.115.86.6:80 | — | Voxility S.R.L. | RO | suspicious |
2852 | rtegre.exe | 185.217.93.92:80 | — | AbeloHost B.V. | NL | suspicious |
— | — | 51.77.72.200:80 | — | — | GB | suspicious |
2852 | rtegre.exe | 212.186.71.38:80 | — | Liberty Global Operations B.V. | AT | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kentona.su |
| malicious |
api.ipify.org |
| shared |
time-a.nist.gov |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2852 | rtegre.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 550 |
2852 | rtegre.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2852 | rtegre.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2852 | rtegre.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 242 |
2852 | rtegre.exe | Potential Corporate Privacy Violation | ET P2P Tor Get Server Request |
2852 | rtegre.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 98 |
2852 | rtegre.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 697 |
2852 | rtegre.exe | Potential Corporate Privacy Violation | ET P2P Tor Get Server Request |
2852 | rtegre.exe | A Network Trojan was detected | MALWARE [PTsecurity] Suspicious TOR Connection (Possible Spy.Ursnif/RTM/Crypt0l0cker activity) |
1 ETPRO signatures available at the full report