| File name: | Moto Auto Flash Tool v7.1.exe |
| Full analysis: | https://app.any.run/tasks/f7b5c786-df9e-4293-89cb-6d047b768ade |
| Verdict: | No threats detected |
| Analysis date: | August 10, 2018, 16:53:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BD574E0B02B46E467A54B9E42CF25371 |
| SHA1: | 739EE1F9B5DBCD3A11D1EFF3EC73BB82A3876A2B |
| SHA256: | BF4D48BCFA2E6D2E050120071F044671926E8469C927A7C2F812C0ED632CB1CE |
| SSDEEP: | 1536:xWqCR8ze0SMfFIE43jqTYf/iMJUiWWgfVRQO1:kqk0SvWTsqMJhpgfDh |
MALICIOUS
No malicious indicators.SUSPICIOUS
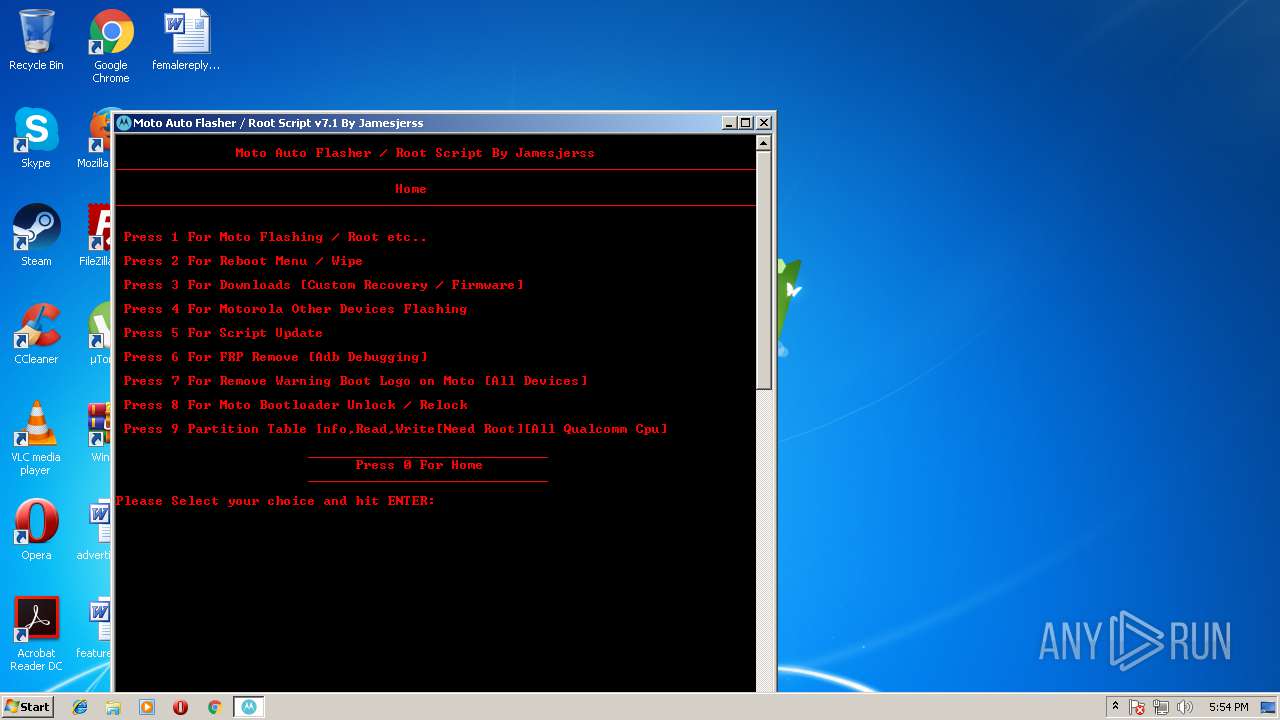
Starts CMD.EXE for commands execution
- Moto Auto Flash Tool v7.1.exe (PID: 940)
INFO
Dropped object may contain URL's
- Moto Auto Flash Tool v7.1.exe (PID: 940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (47.6) |
|---|---|---|
| .scr | | | Windows screen saver (22.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.3) |
| .exe | | | Win32 Executable (generic) (7.7) |
| .exe | | | Win16/32 Executable Delphi generic (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:11:13 14:38:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 42496 |
| InitializedDataSize: | 145408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 13-Nov-2015 13:38:31 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Nov-2015 13:38:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x00002BEB | 0x00002C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.47384 |
.text | 0x00004000 | 0x0000788A | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54213 |
.rdata | 0x0000C000 | 0x0000065E | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.24725 |
.data | 0x0000D000 | 0x000018F0 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.14318 |
.rsrc | 0x0000F000 | 0x00021B30 | 0x00021C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.34806 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.056 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.04002 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.977 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.8103 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
B | 4.86089 | 36982 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D | 3.46772 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 3.34844 | 88 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 0.918296 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | "C:\Users\admin\AppData\Local\Temp\Moto Auto Flash Tool v7.1.exe" | C:\Users\admin\AppData\Local\Temp\Moto Auto Flash Tool v7.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2268 | mode con:cols=80lines=150 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | mode con:cols=80lines=150 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | cmd /c ""C:\Users\admin\AppData\Local\Temp\2CBD.tmp\Moto Auto Flash Tool v7.1 By Jamesjerss.bat" "C:\Users\admin\AppData\Local\Temp\Moto Auto Flash Tool v7.1.exe"" | C:\Windows\system32\cmd.exe | — | Moto Auto Flash Tool v7.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
6
Read events
6
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 940 | Moto Auto Flash Tool v7.1.exe | C:\Users\admin\AppData\Local\Temp\2CBD.tmp\Moto Auto Flash Tool v7.1 By Jamesjerss.bat | text | |
MD5:— | SHA256:— | |||
| 3468 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Null | text | |
MD5:37EA882F356E462D579AA4CCD8E089D6 | SHA256:D2CF402243A6ED040E5E51FC45C4A72DA1E7DB60136D54A9C84B0955FAF3A4F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report