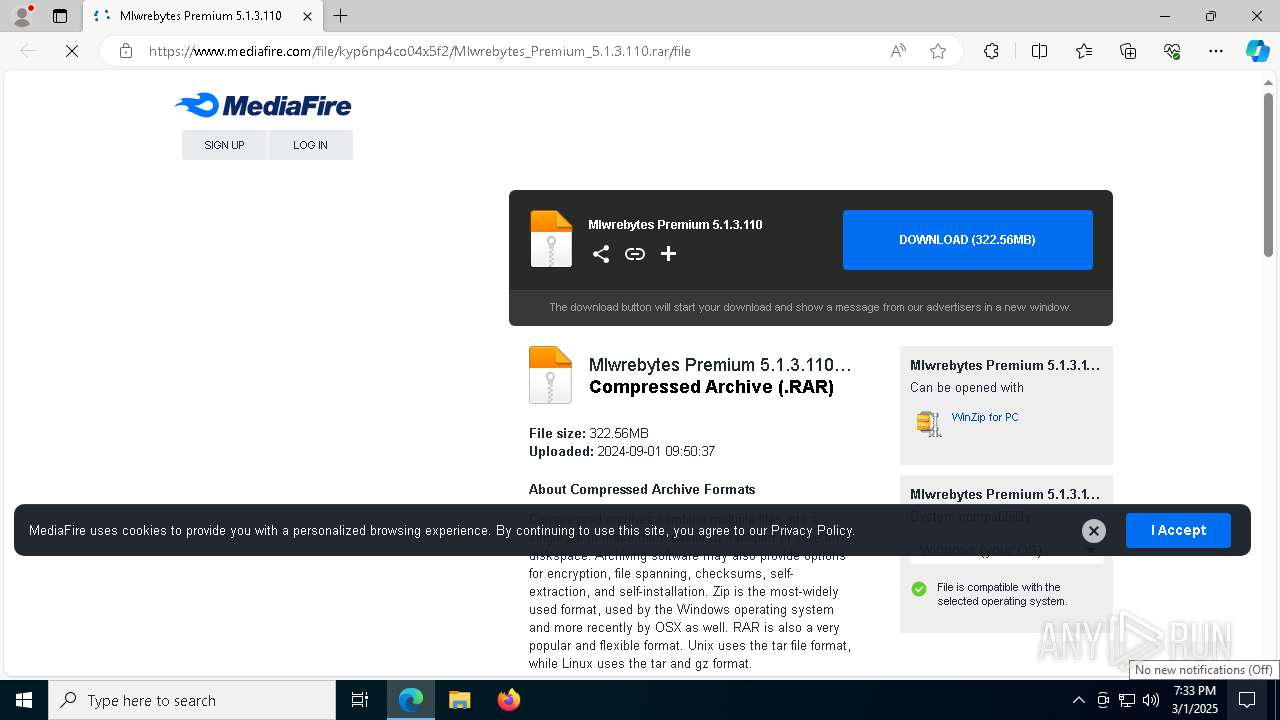
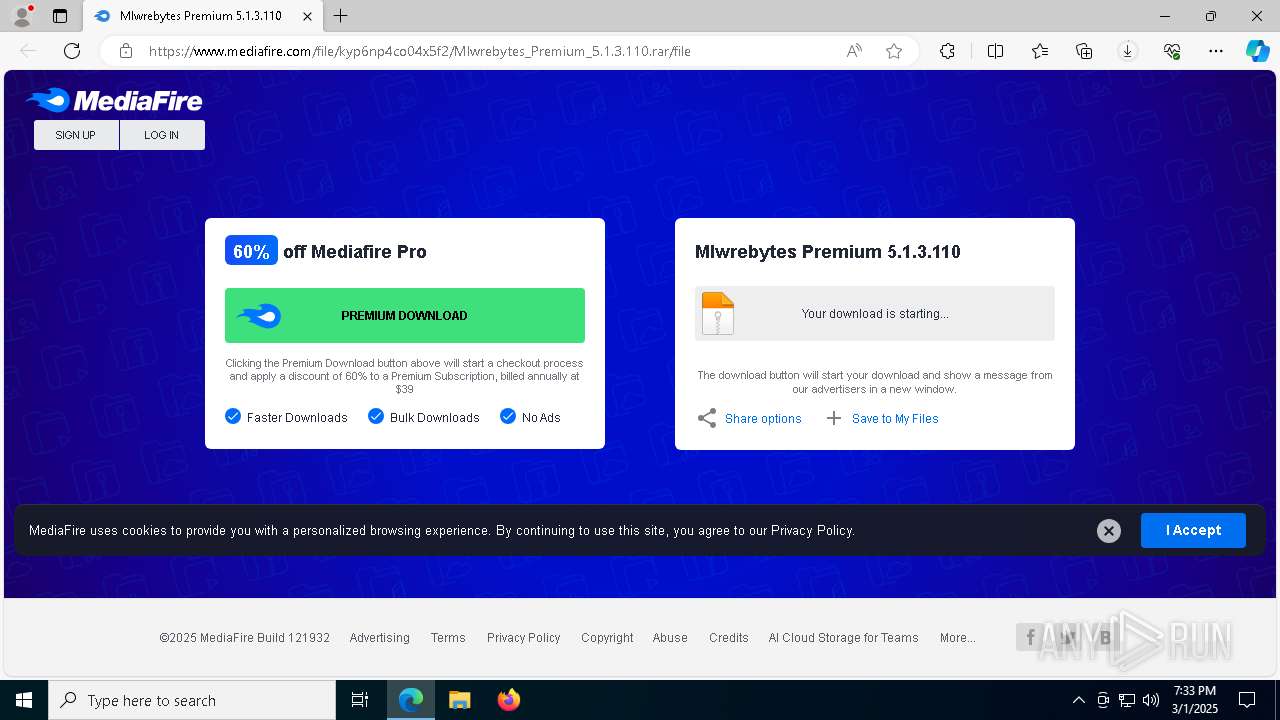
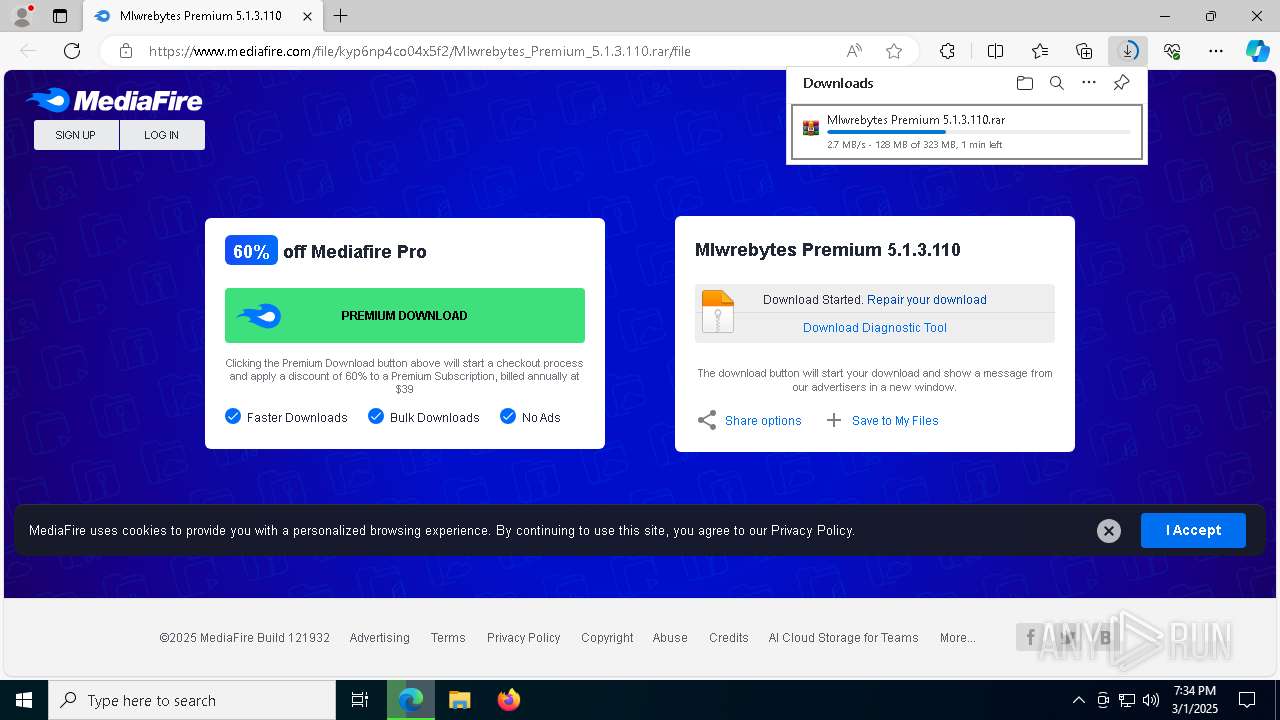
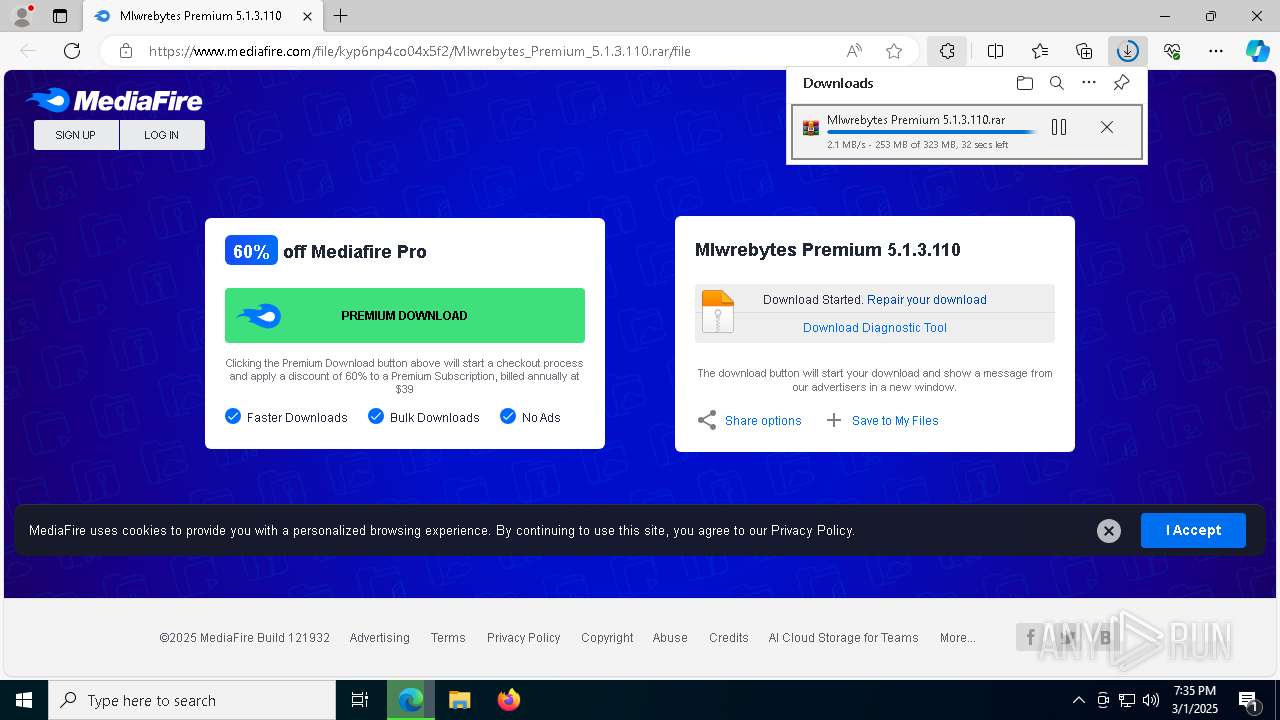
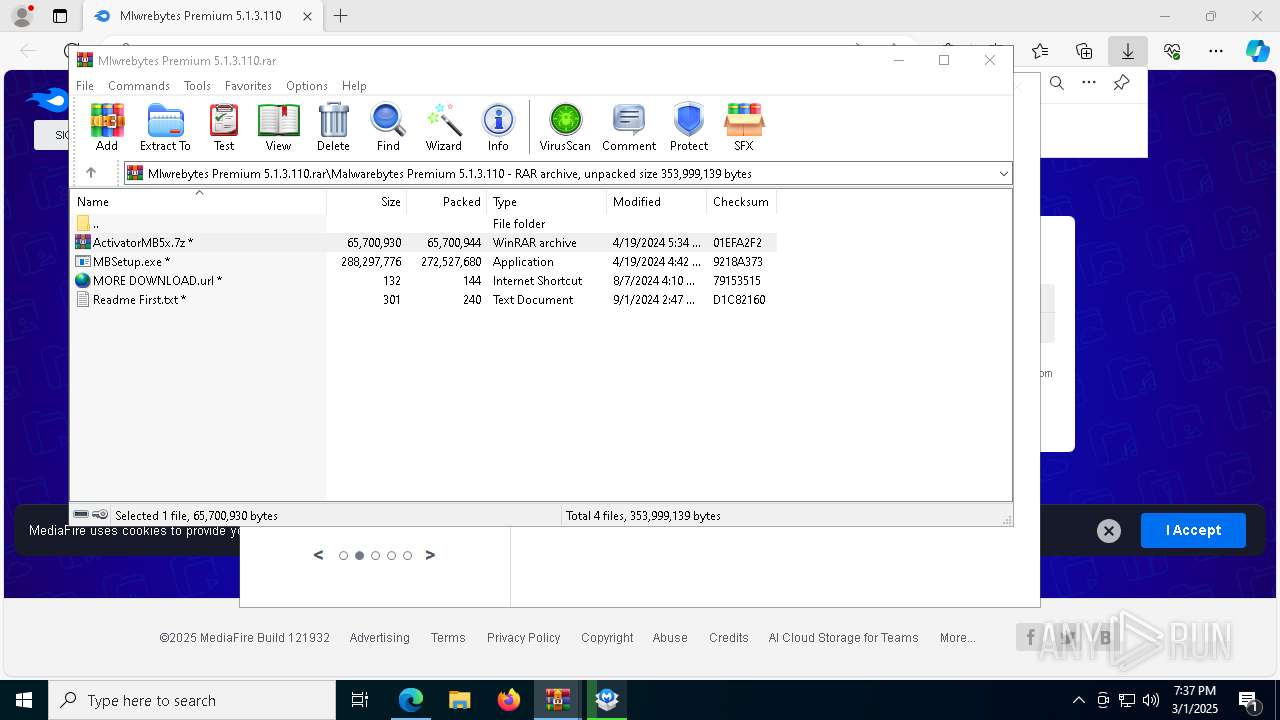
| URL: | https://www.mediafire.com/file/kyp6np4co04x5f2/Mlwrebytes_Premium_5.1.3.110.rar/file |
| Full analysis: | https://app.any.run/tasks/24f37df1-97da-42b5-8d07-b0e1119a06aa |
| Verdict: | Malicious activity |
| Analysis date: | March 01, 2025, 19:33:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | D93A62C8C441753164E191526D20998C |
| SHA1: | 5641FB30EC6C639DD029C896A75CCB8F7A710C62 |
| SHA256: | BF48AD96C35A5B40D08579A161C9887B398530AA3B9402719A63FF494639695B |
| SSDEEP: | 3:N8DSLw3eGUoN9Va1q6CW+OKDIA:2OLw3eG1vWCcA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6264)
- ShellExperienceHost.exe (PID: 7200)
- WinRAR.exe (PID: 4068)
- MBAMService.exe (PID: 5404)
- mbamtray.exe (PID: 8084)
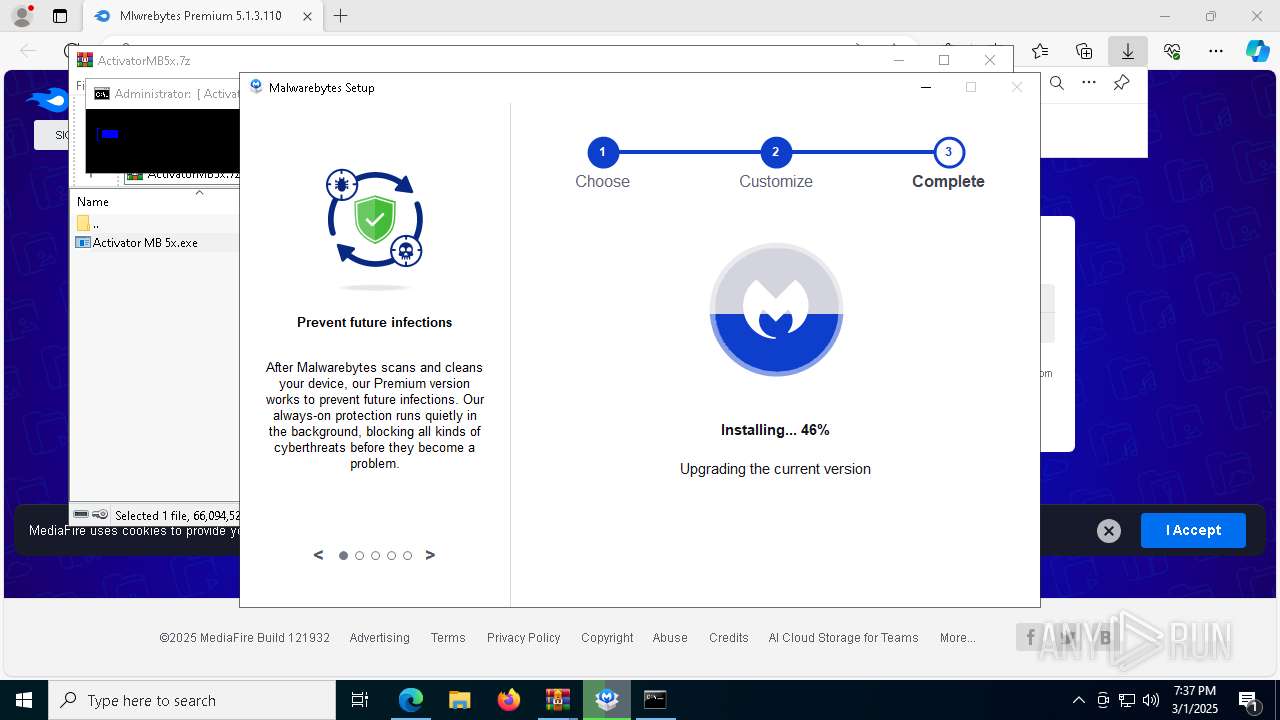
Reads the BIOS version
- MBSetup.exe (PID: 8056)
- MBAMService.exe (PID: 5404)
- MBAMInstallerService.exe (PID: 6476)
Creates files in the driver directory
- MBSetup.exe (PID: 8056)
- cmd.exe (PID: 8044)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
There is functionality for taking screenshot (YARA)
- MBSetup.exe (PID: 8056)
Process drops legitimate windows executable
- MBAMInstallerService.exe (PID: 6476)
- rs.tmp (PID: 8464)
- _iu14D2N.tmp (PID: 448)
The process creates files with name similar to system file names
- MBSetup.exe (PID: 8056)
- MBAMInstallerService.exe (PID: 6476)
The process verifies whether the antivirus software is installed
- MBSetup.exe (PID: 8056)
- MBAMInstallerService.exe (PID: 6476)
- powershell.exe (PID: 236)
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
- MBAMWsc.exe (PID: 3676)
- rs.tmp (PID: 8464)
- mbamtray.exe (PID: 8084)
- unins000.exe (PID: 8900)
- _iu14D2N.tmp (PID: 448)
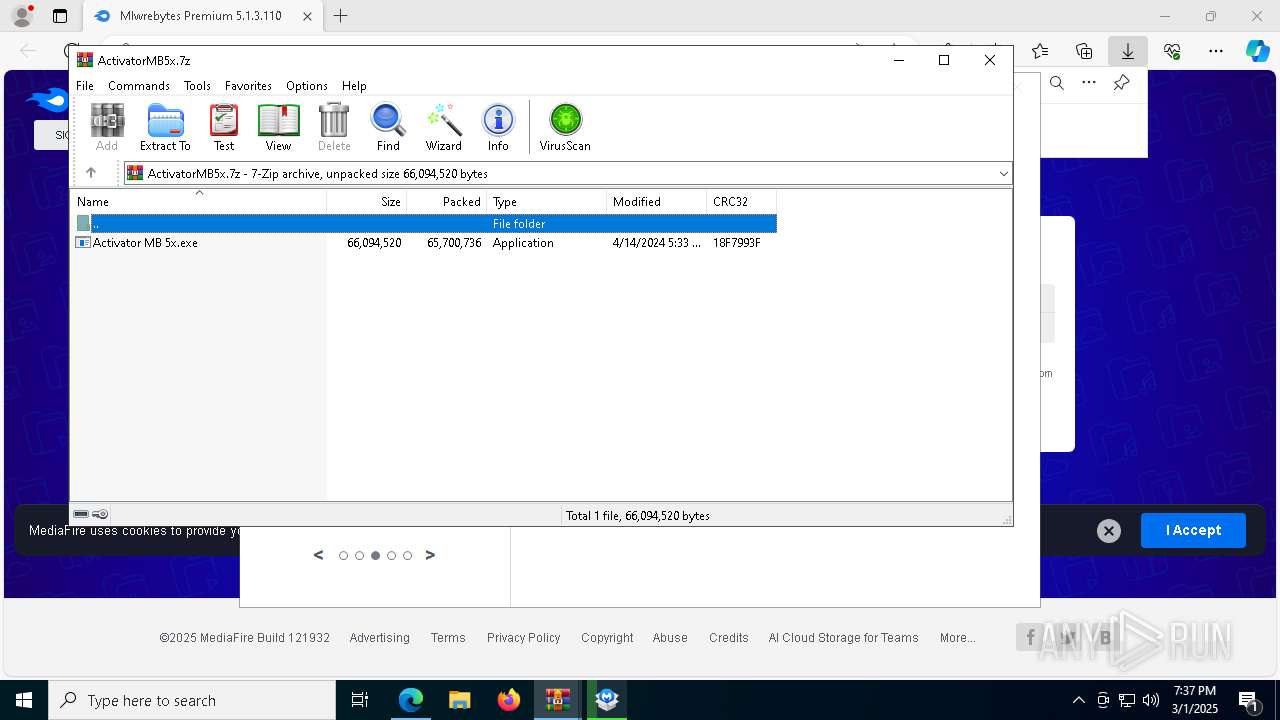
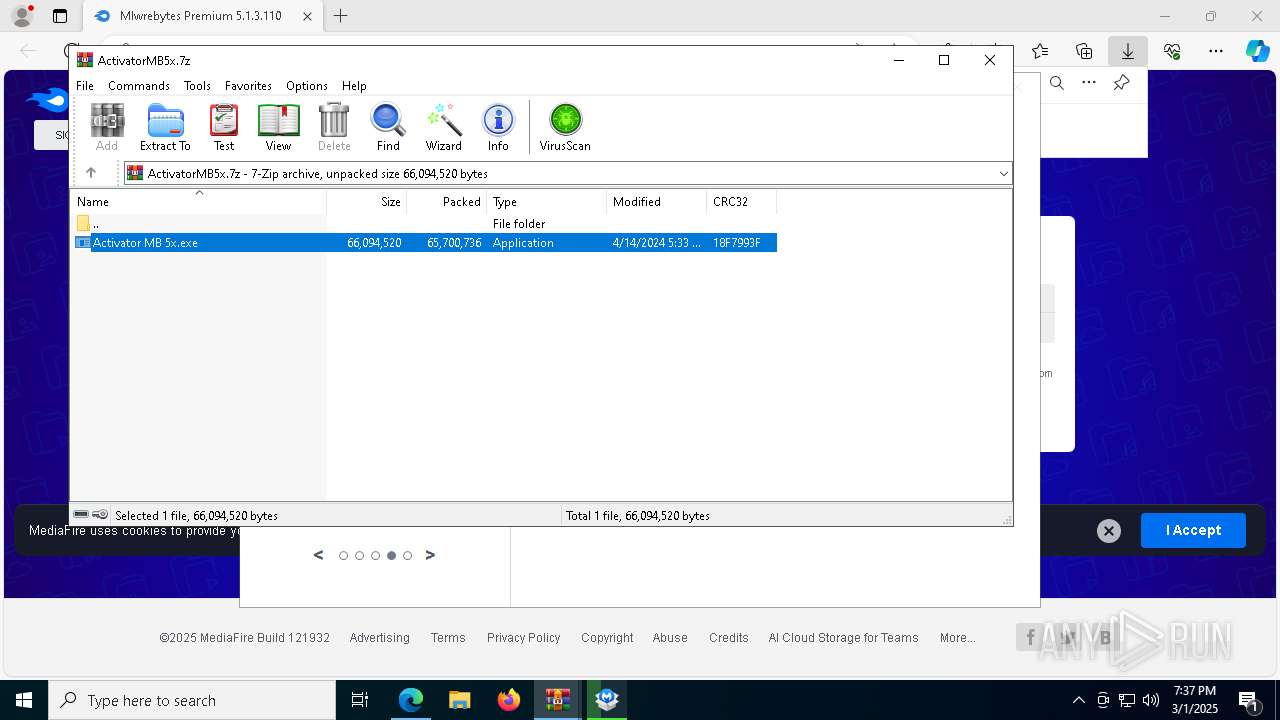
Executable content was dropped or overwritten
- MBSetup.exe (PID: 8056)
- MBAMInstallerService.exe (PID: 6476)
- Activator MB 5x.exe (PID: 8716)
- 7z2201.exe (PID: 9008)
- rs.exe (PID: 8796)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
- unins000.exe (PID: 8900)
- _iu14D2N.tmp (PID: 448)
Executes as Windows Service
- MBAMInstallerService.exe (PID: 6476)
- MBAMService.exe (PID: 5404)
Searches for installed software
- MBSetup.exe (PID: 8056)
- MBAMInstallerService.exe (PID: 6476)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5404)
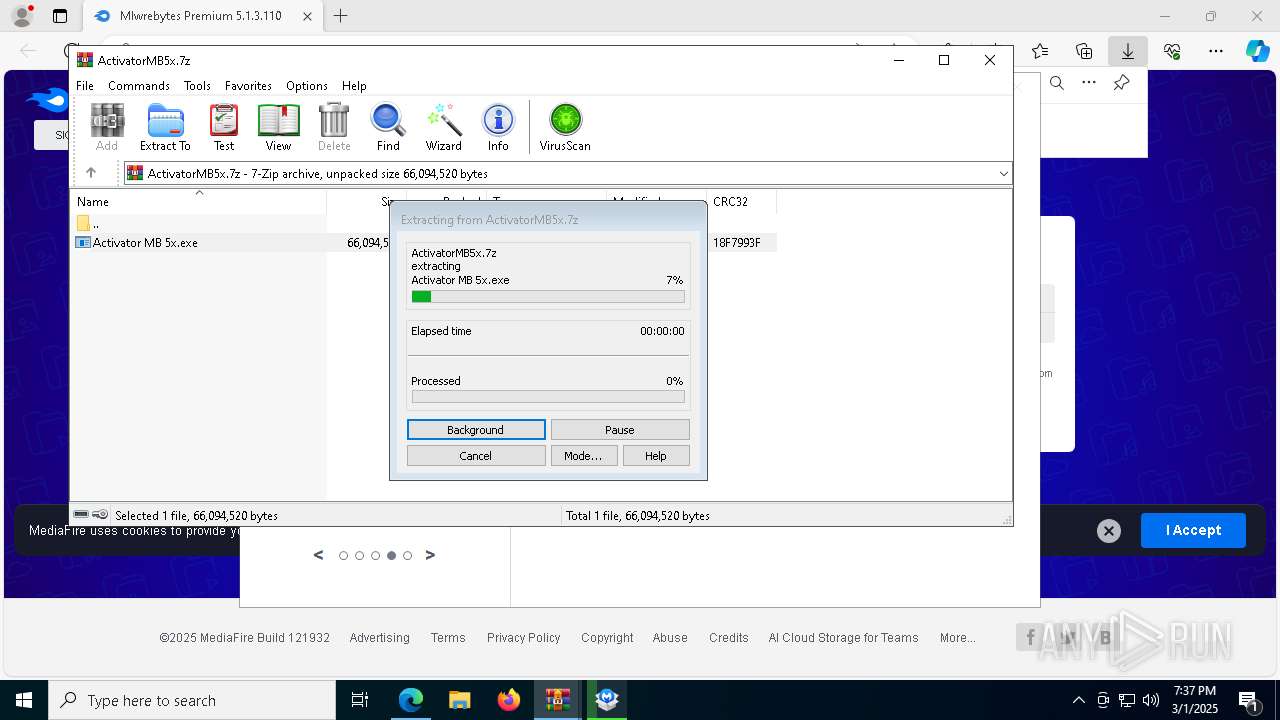
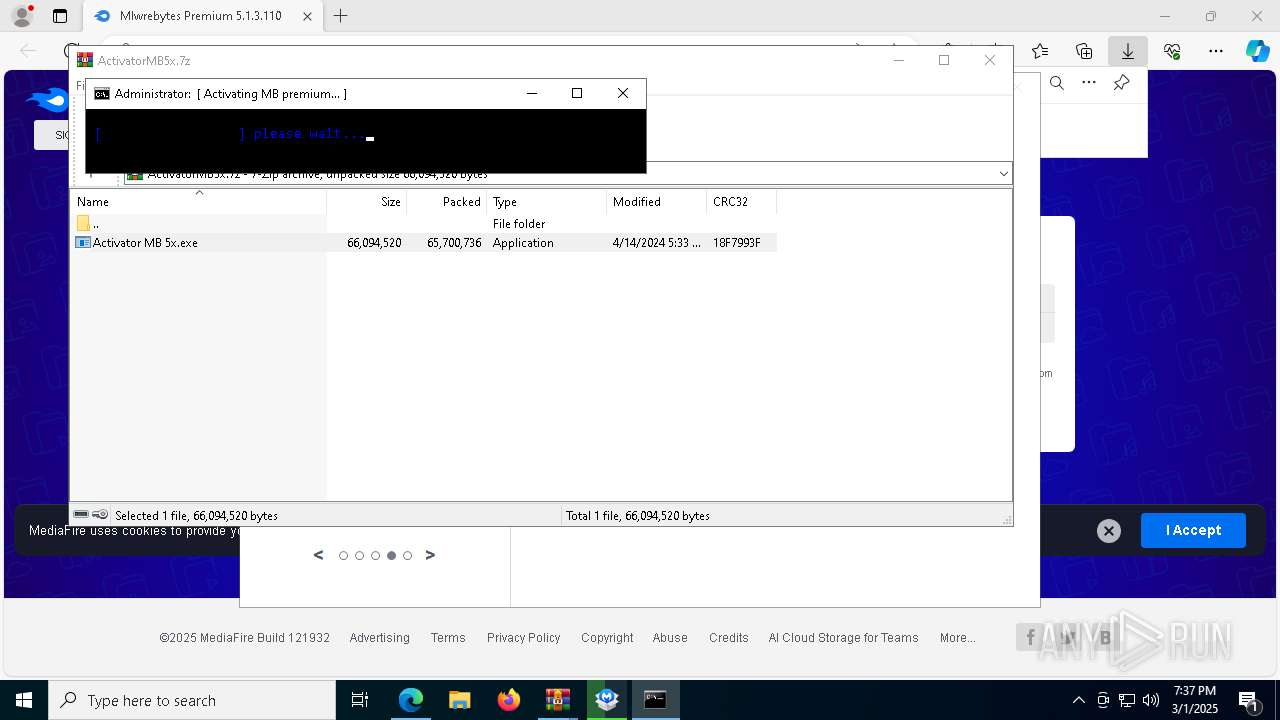
Drops 7-zip archiver for unpacking
- MBAMInstallerService.exe (PID: 6476)
- Activator MB 5x.exe (PID: 8716)
- 7z2201.exe (PID: 9008)
- rs.tmp (PID: 8464)
Drops a system driver (possible attempt to evade defenses)
- MBAMInstallerService.exe (PID: 6476)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
Application launched itself
- WinRAR.exe (PID: 6264)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 132)
- cmd.exe (PID: 8852)
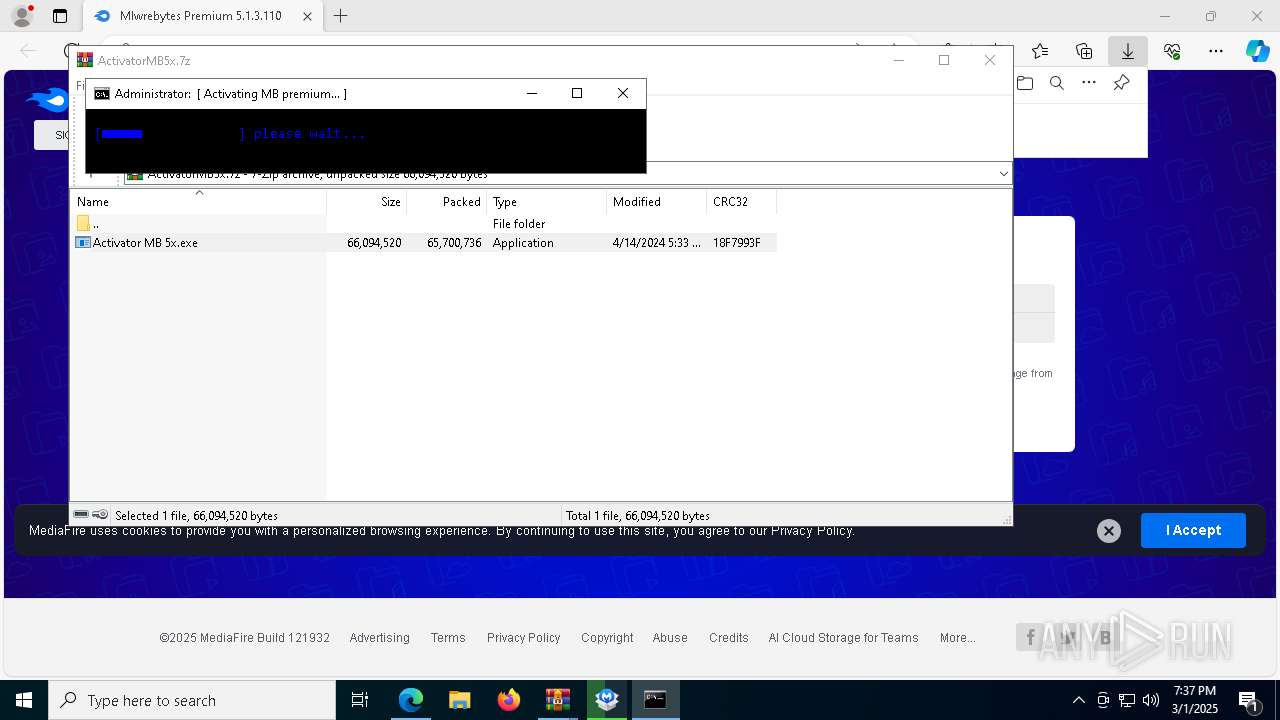
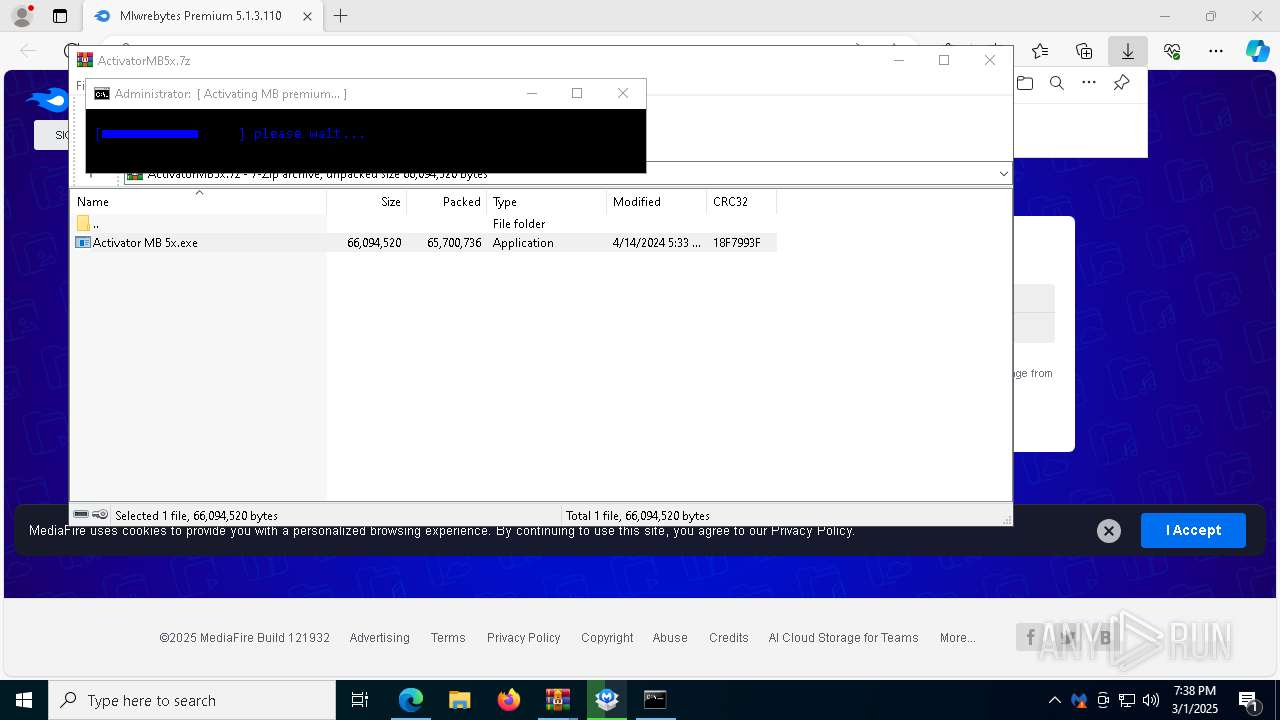
Executing commands from a ".bat" file
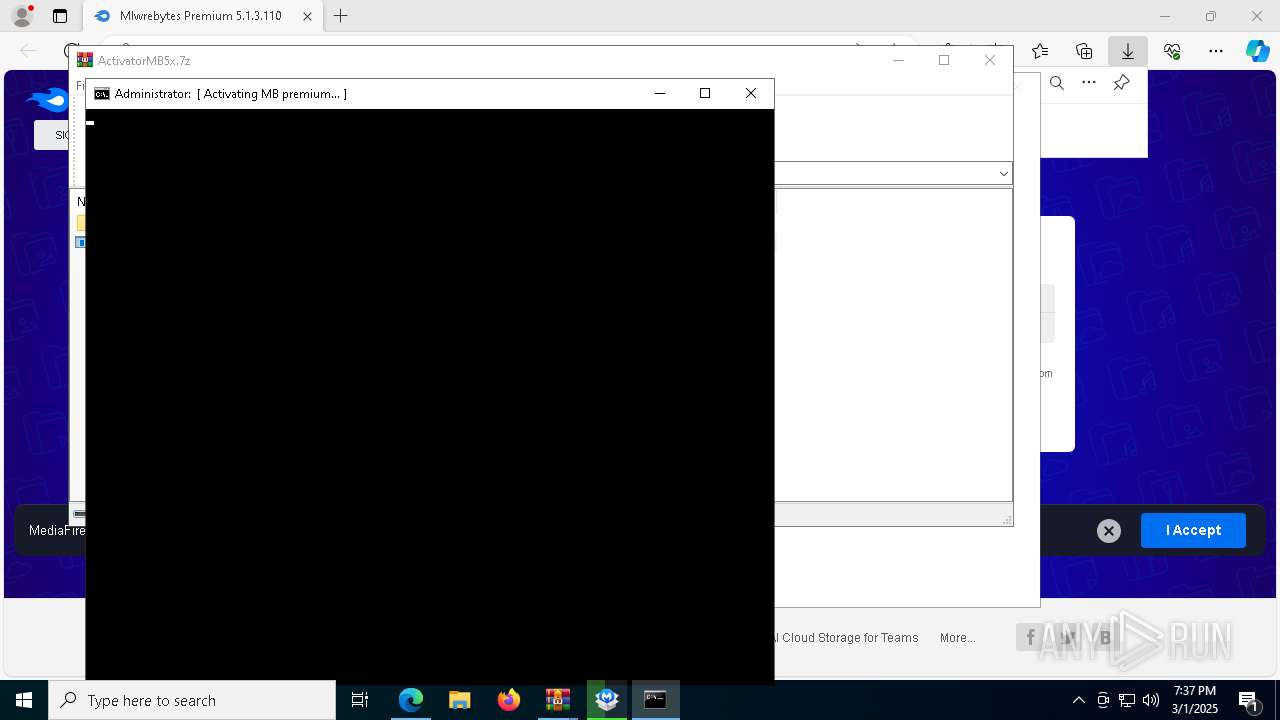
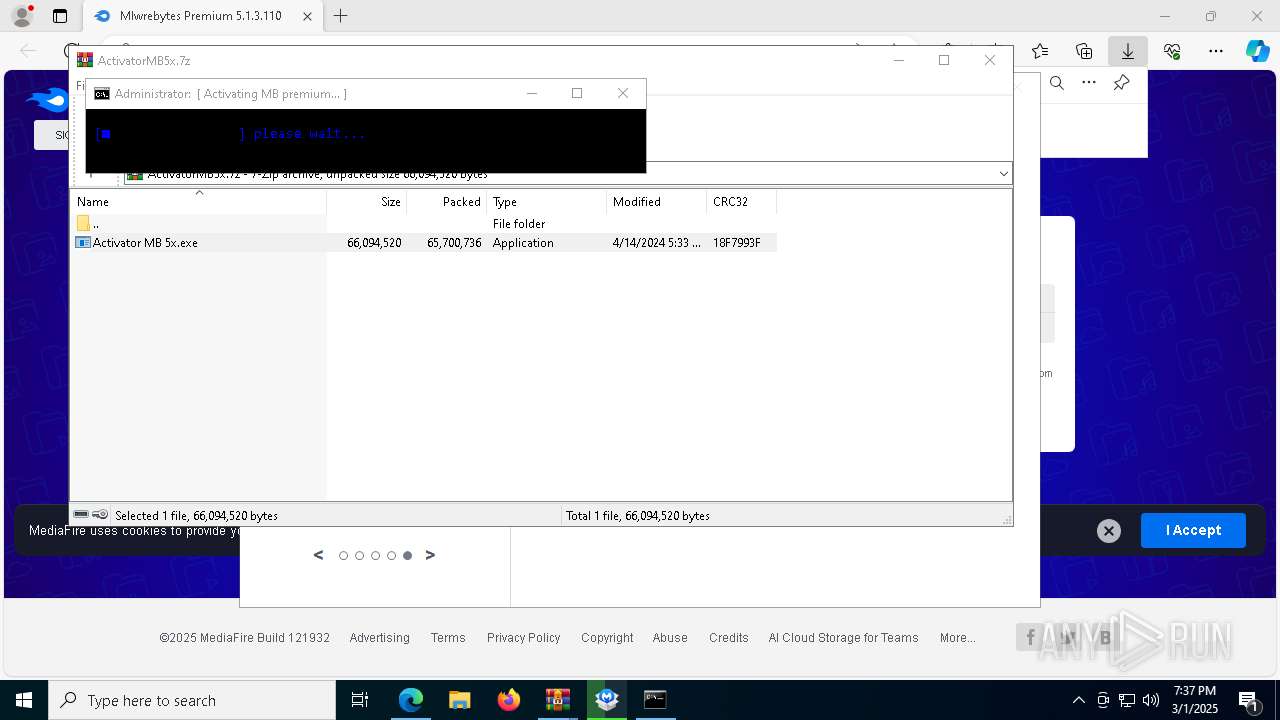
- Activator MB 5x.exe (PID: 8716)
Starts CMD.EXE for commands execution
- Activator MB 5x.exe (PID: 8716)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 132)
- cmd.exe (PID: 8852)
The executable file from the user directory is run by the CMD process
- 7z2201.exe (PID: 9008)
Creates/Modifies COM task schedule object
- 7z2201.exe (PID: 9008)
- MBAMService.exe (PID: 5404)
Creates a software uninstall entry
- 7z2201.exe (PID: 9008)
Executing commands from ".cmd" file
- cmd.exe (PID: 8044)
- cmd.exe (PID: 132)
Starts process via Powershell
- powershell.exe (PID: 236)
- powershell.exe (PID: 1132)
- powershell.exe (PID: 4608)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8044)
Starts application with an unusual extension
- cmd.exe (PID: 132)
- unins000.exe (PID: 8900)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 132)
- cmd.exe (PID: 8044)
Reads the Windows owner or organization settings
- rs.tmp (PID: 8464)
- _iu14D2N.tmp (PID: 448)
The process drops C-runtime libraries
- rs.tmp (PID: 8464)
- MBAMInstallerService.exe (PID: 6476)
Creates or modifies Windows services
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
Checks Windows Trust Settings
- MBAMService.exe (PID: 5404)
Detected use of alternative data streams (AltDS)
- MBAMService.exe (PID: 5404)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 8044)
Starts itself from another location
- unins000.exe (PID: 8900)
INFO
Reads the computer name
- identity_helper.exe (PID: 8232)
- MBSetup.exe (PID: 8056)
- ShellExperienceHost.exe (PID: 7200)
- MBAMInstallerService.exe (PID: 6476)
- 7z2201.exe (PID: 9008)
- 7z.exe (PID: 3796)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
- mbamtray.exe (PID: 8084)
- unins000.exe (PID: 8900)
- _iu14D2N.tmp (PID: 448)
- MBAMWsc.exe (PID: 3676)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5124)
- mbamtray.exe (PID: 8084)
Checks supported languages
- identity_helper.exe (PID: 8232)
- MBSetup.exe (PID: 8056)
- ShellExperienceHost.exe (PID: 7200)
- MBAMInstallerService.exe (PID: 6476)
- Activator MB 5x.exe (PID: 8716)
- 7z2201.exe (PID: 9008)
- 7z.exe (PID: 3796)
- mode.com (PID: 4692)
- mode.com (PID: 872)
- chcp.com (PID: 5500)
- rs.exe (PID: 8796)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
- mbamtray.exe (PID: 8084)
- unins000.exe (PID: 8900)
- _iu14D2N.tmp (PID: 448)
- MBAMWsc.exe (PID: 3676)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 9028)
- BackgroundTransferHost.exe (PID: 5124)
- BackgroundTransferHost.exe (PID: 8044)
- BackgroundTransferHost.exe (PID: 8836)
- BackgroundTransferHost.exe (PID: 8640)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5124)
- slui.exe (PID: 8636)
- MBSetup.exe (PID: 8056)
- mbamtray.exe (PID: 8084)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5124)
- slui.exe (PID: 5576)
- MBSetup.exe (PID: 8056)
- slui.exe (PID: 8636)
- MBAMService.exe (PID: 5404)
Creates files in the program directory
- MBSetup.exe (PID: 8056)
- MBAMInstallerService.exe (PID: 6476)
- 7z2201.exe (PID: 9008)
- cmd.exe (PID: 8044)
- xcopy.exe (PID: 1004)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5404)
- xcopy.exe (PID: 6188)
- xcopy.exe (PID: 1268)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 6264)
Create files in a temporary directory
- MBSetup.exe (PID: 8056)
- Activator MB 5x.exe (PID: 8716)
- 7z.exe (PID: 3796)
- rs.exe (PID: 8796)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5212)
- unins000.exe (PID: 8900)
- _iu14D2N.tmp (PID: 448)
Reads the machine GUID from the registry
- MBSetup.exe (PID: 8056)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5404)
- mbamtray.exe (PID: 8084)
- MBAMInstallerService.exe (PID: 6476)
The sample compiled with english language support
- msedge.exe (PID: 1180)
- MBSetup.exe (PID: 8056)
- MBAMInstallerService.exe (PID: 6476)
- Activator MB 5x.exe (PID: 8716)
- 7z2201.exe (PID: 9008)
- rs.tmp (PID: 8464)
- MBAMService.exe (PID: 5212)
- MBAMService.exe (PID: 5404)
- _iu14D2N.tmp (PID: 448)
Application launched itself
- msedge.exe (PID: 7280)
Executable content was dropped or overwritten
- msedge.exe (PID: 1180)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7280)
The sample compiled with russian language support
- 7z2201.exe (PID: 9008)
The sample compiled with spanish language support
- MBAMInstallerService.exe (PID: 6476)
- rs.tmp (PID: 8464)
Creates or changes the value of an item property via Powershell
- cmd.exe (PID: 8044)
Changes the display of characters in the console
- cmd.exe (PID: 132)
Starts MODE.COM to configure console settings
- mode.com (PID: 4692)
- mode.com (PID: 872)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 236)
The executable file from the user directory is run by the Powershell process
- rs.exe (PID: 8796)
Creates a software uninstall entry
- rs.tmp (PID: 8464)
Reads CPU info
- MBAMService.exe (PID: 5404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
264
Monitored processes
119
Malicious processes
19
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\system32\cmd.exe /K "C:\Users\admin\AppData\Local\Temp\pb.cmd" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | powershell start-process -FilePath 'C:\Program Files\Malwarebytes\Anti-Malware\unins000.exe' -ArgumentList '/VERYSILENT /SUPPRESSMSGBOXES /NORESTART /SP-' -NoNewWindow -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files\Malwarebytes\Anti-Malware\unins000.exe" /FIRSTPHASEWND=$503D2 /VERYSILENT /SUPPRESSMSGBOXES /NORESTART /SP- | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 872 | mode con:cols=86 lines=36 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | xcopy /C /H /Q /R /Y /E C:\Users\admin\AppData\Local\Temp\MB2Migration C:\ProgramData\MB2Migration | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | timeout.exe 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | powershell start-process -FilePath 'C:\Users\admin\AppData\Local\Temp\rs.exe' -ArgumentList '/VERYSILENT /SUPPRESSMSGBOXES /NORESTART /SP-' -NoNewWindow -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7036 --field-trial-handle=2360,i,6140817535139558683,7281127832531060480,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1268 | xcopy /C /H /Q /R /Y "C:\ProgramData\Malwarebytes\MBAMService\config\ScanConfig.json" "C:\ProgramData\tl" | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
66 037
Read events
65 362
Write events
624
Delete events
51
Modification events
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {65F1B8CA-F6CC-4F35-BC19-549EC5B69293} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DA9C6310-1A8D-4AE5-822D-62148A7F5F81} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BA6558DE-D3CC-4B5E-92B0-F9110FAB1A9D} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CB4D7A40-C195-466B-A41A-EB5037231EF6} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6859EBD4-0C37-47AF-9B55-4EB134D10B7A} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {25445CE3-A2A5-4085-A87E-097F9A9AAA95} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A98E2B8D-F097-4C56-8374-6D45B0BE2D8B} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A42024E6-0C69-4056-892C-C92F1E21F357} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D494E3C7-E03D-4B61-B915-245C496EEE59} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9983D94A-89D9-4E77-9CF0-EBA089880A93} | |||
Executable files
1 038
Suspicious files
846
Text files
445
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b567.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b567.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b577.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b577.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b577.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
174
DNS requests
178
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5124 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
680 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1741205671&P2=404&P3=2&P4=JqSOMwfIUg2BLgqg%2bZBy84AXvQbcN8OYdBmV89B4a23tvb6OcN5%2bsvaOOw7SiKajq3au9ZDZEpYWCiIWg%2bGtlQ%3d%3d | unknown | — | — | whitelisted |
208 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
680 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1741205671&P2=404&P3=2&P4=JqSOMwfIUg2BLgqg%2bZBy84AXvQbcN8OYdBmV89B4a23tvb6OcN5%2bsvaOOw7SiKajq3au9ZDZEpYWCiIWg%2bGtlQ%3d%3d | unknown | — | — | whitelisted |
208 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
680 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1741205671&P2=404&P3=2&P4=JqSOMwfIUg2BLgqg%2bZBy84AXvQbcN8OYdBmV89B4a23tvb6OcN5%2bsvaOOw7SiKajq3au9ZDZEpYWCiIWg%2bGtlQ%3d%3d | unknown | — | — | whitelisted |
680 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1741205671&P2=404&P3=2&P4=JqSOMwfIUg2BLgqg%2bZBy84AXvQbcN8OYdBmV89B4a23tvb6OcN5%2bsvaOOw7SiKajq3au9ZDZEpYWCiIWg%2bGtlQ%3d%3d | unknown | — | — | whitelisted |
680 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/370be913-fe5a-455b-af7f-6ca894b905e8?P1=1741308038&P2=404&P3=2&P4=lwE3UeatO5QlAO1ti569rvM4ROuSjQUWZ7m%2f2Wij1njsjHs0kF%2fjm30DW55%2b3m0BFTLGtaDFHgAqwQB0a646Yg%3d%3d | unknown | — | — | whitelisted |
680 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/370be913-fe5a-455b-af7f-6ca894b905e8?P1=1741308038&P2=404&P3=2&P4=lwE3UeatO5QlAO1ti569rvM4ROuSjQUWZ7m%2f2Wij1njsjHs0kF%2fjm30DW55%2b3m0BFTLGtaDFHgAqwQB0a646Yg%3d%3d | unknown | — | — | whitelisted |
680 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/370be913-fe5a-455b-af7f-6ca894b905e8?P1=1741308038&P2=404&P3=2&P4=lwE3UeatO5QlAO1ti569rvM4ROuSjQUWZ7m%2f2Wij1njsjHs0kF%2fjm30DW55%2b3m0BFTLGtaDFHgAqwQB0a646Yg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7572 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7572 | msedge.exe | 104.17.151.117:443 | www.mediafire.com | — | — | whitelisted |
7572 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7572 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7572 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7572 | msedge.exe | 172.67.199.186:443 | the.gatekeeperconsent.com | — | — | unknown |
7572 | msedge.exe | 2.19.11.100:443 | bzib.nelreports.net | Elisa Oyj | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
the.gatekeeperconsent.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7572 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7572 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7572 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7572 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|
MBAMService.exe | Retry XPE file open
|