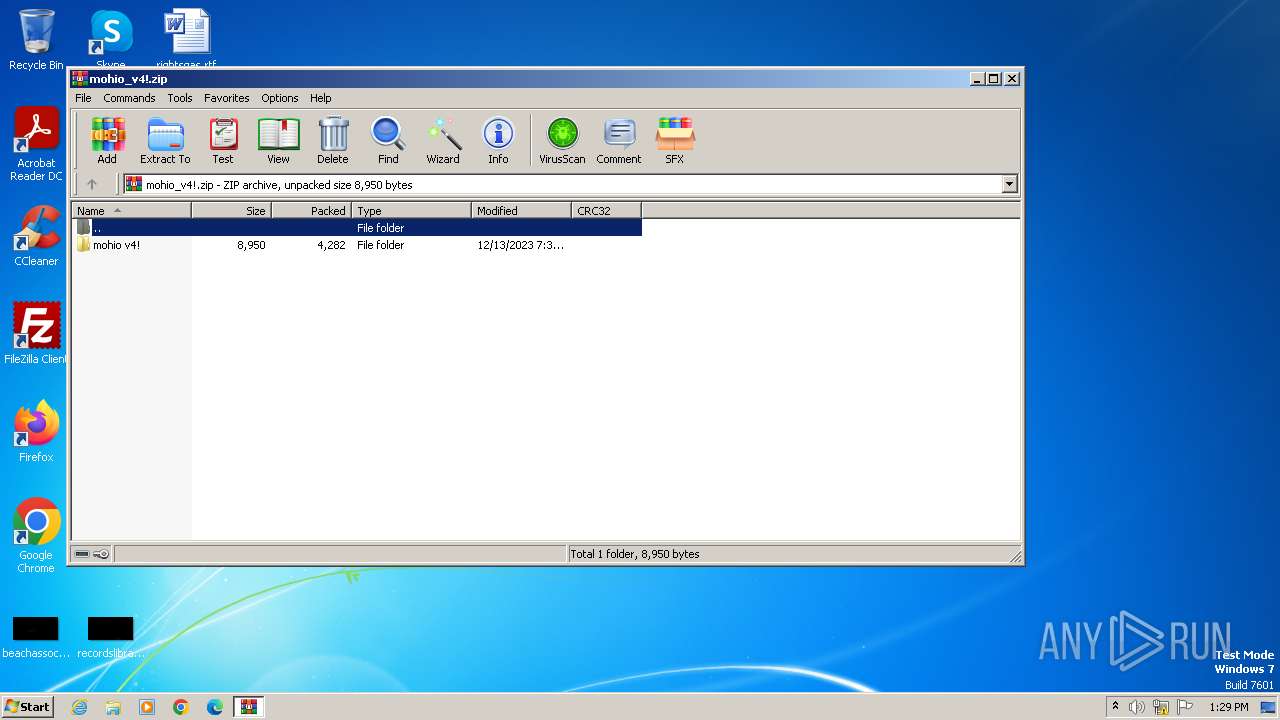
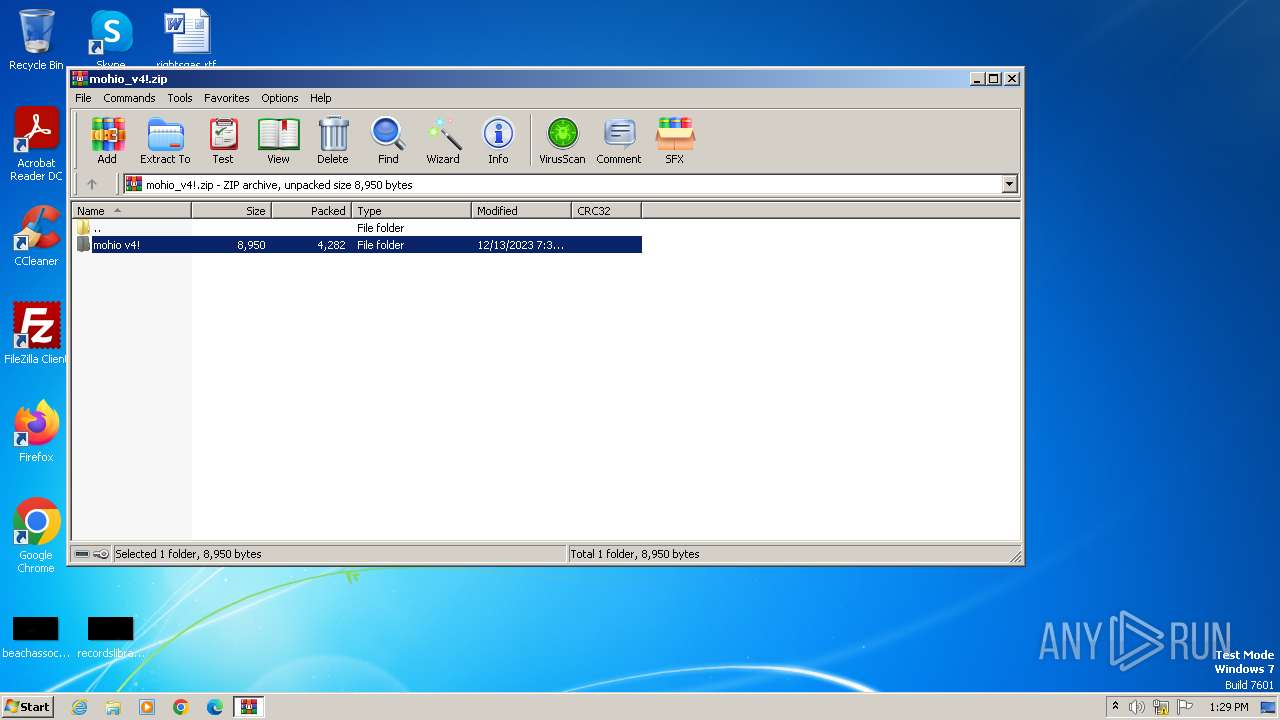
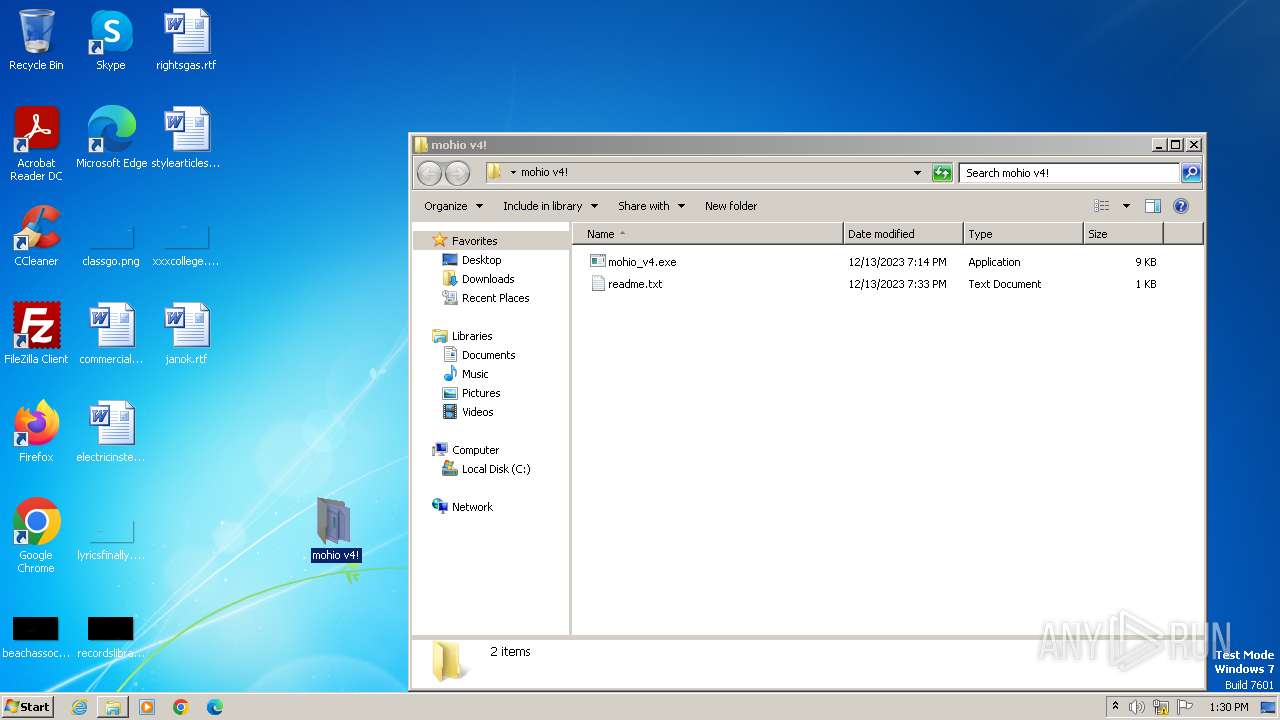
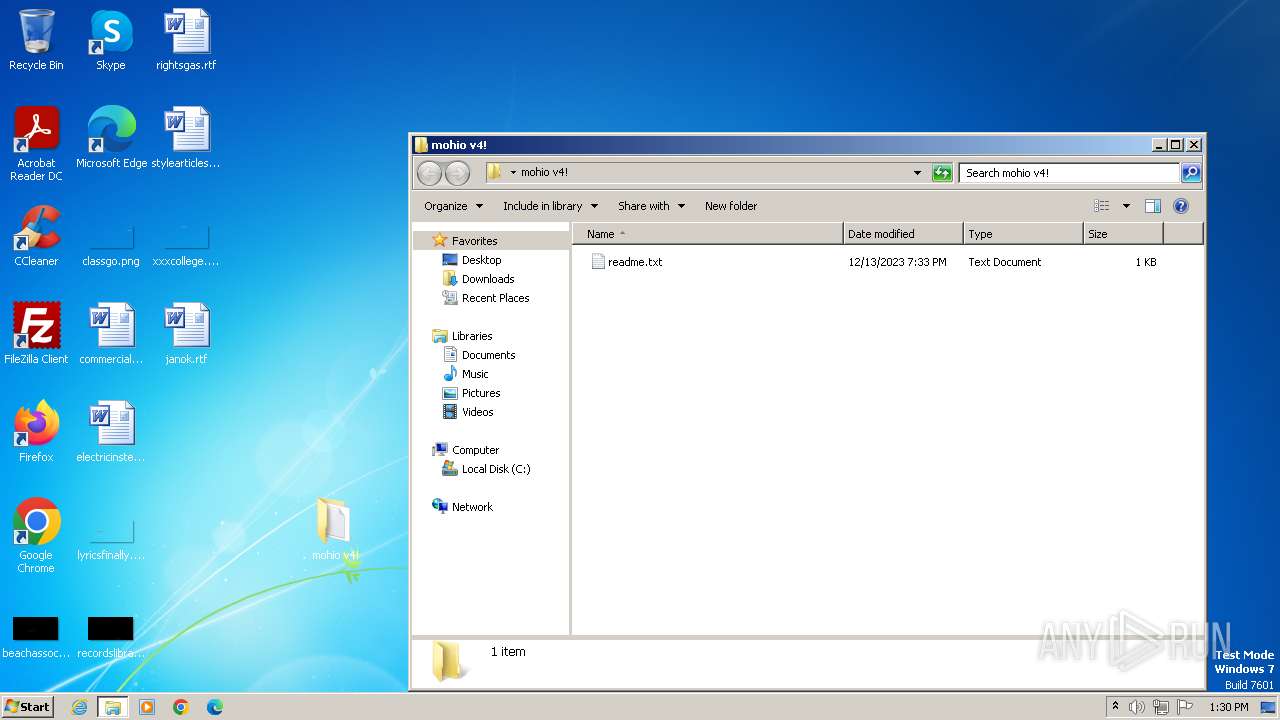
| File name: | mohio_v4!.zip |
| Full analysis: | https://app.any.run/tasks/d16c8290-eb05-4709-b7b7-a26a712495b3 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2023, 13:29:34 |
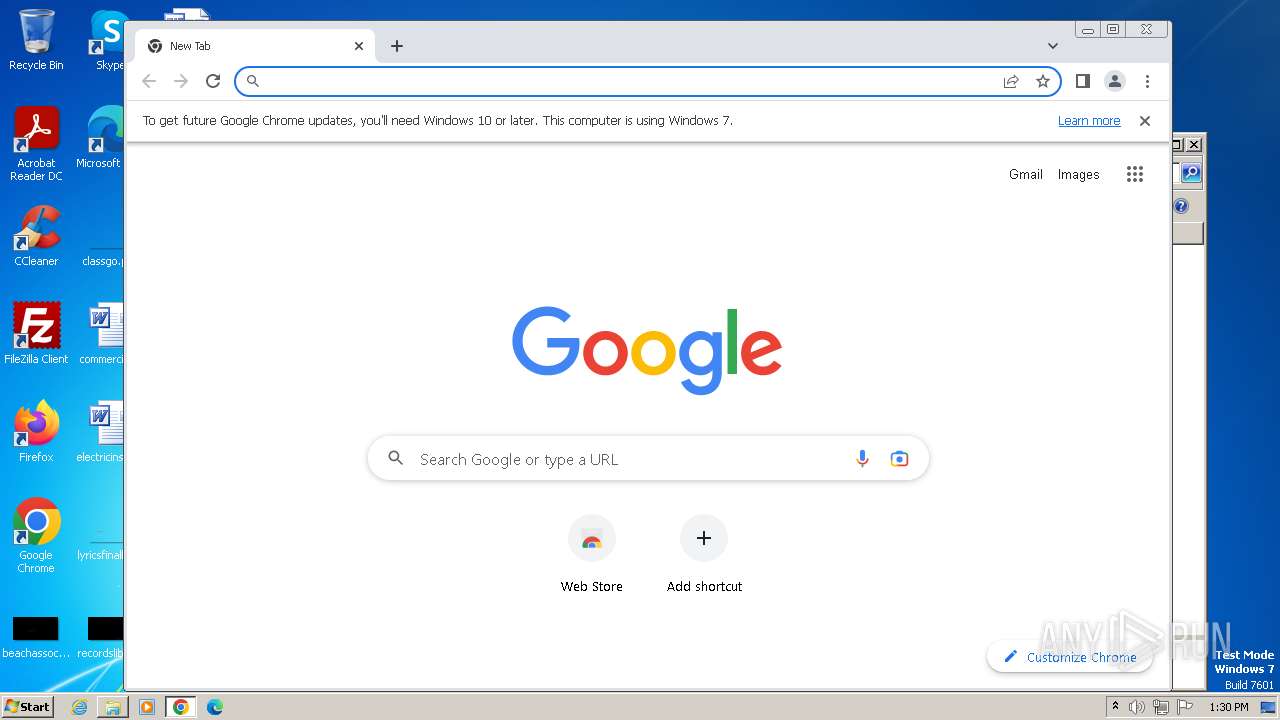
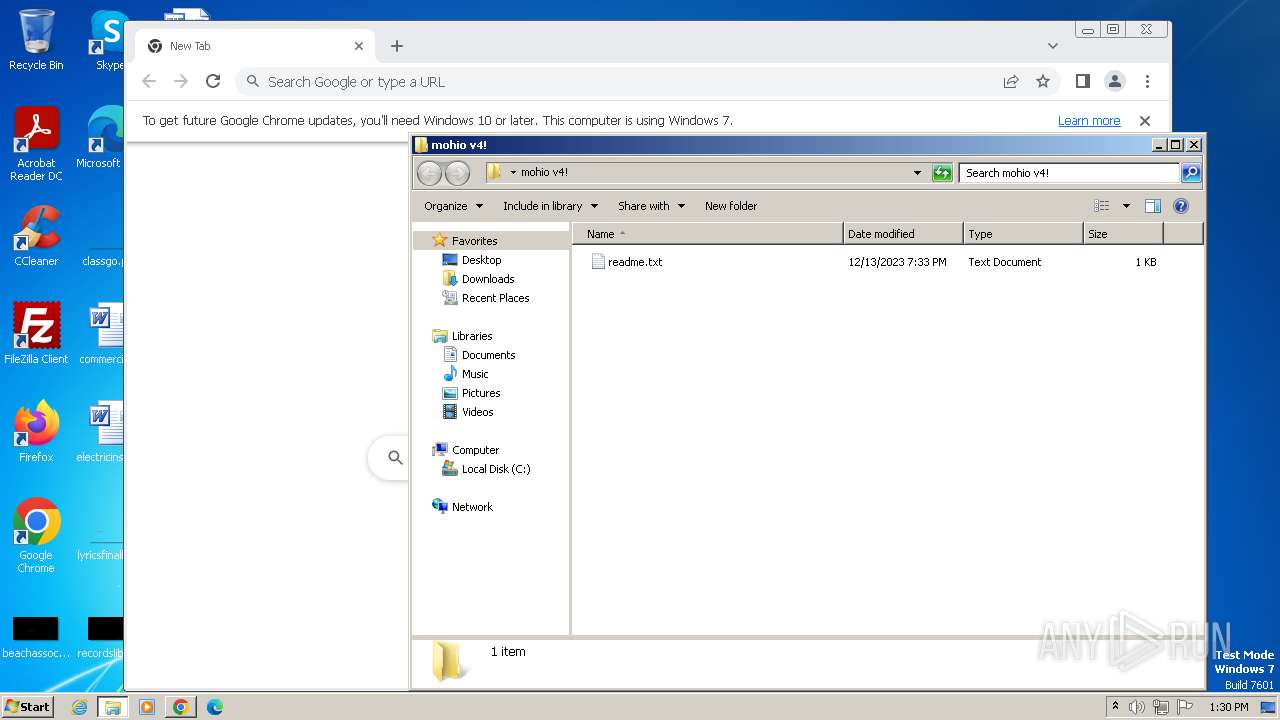
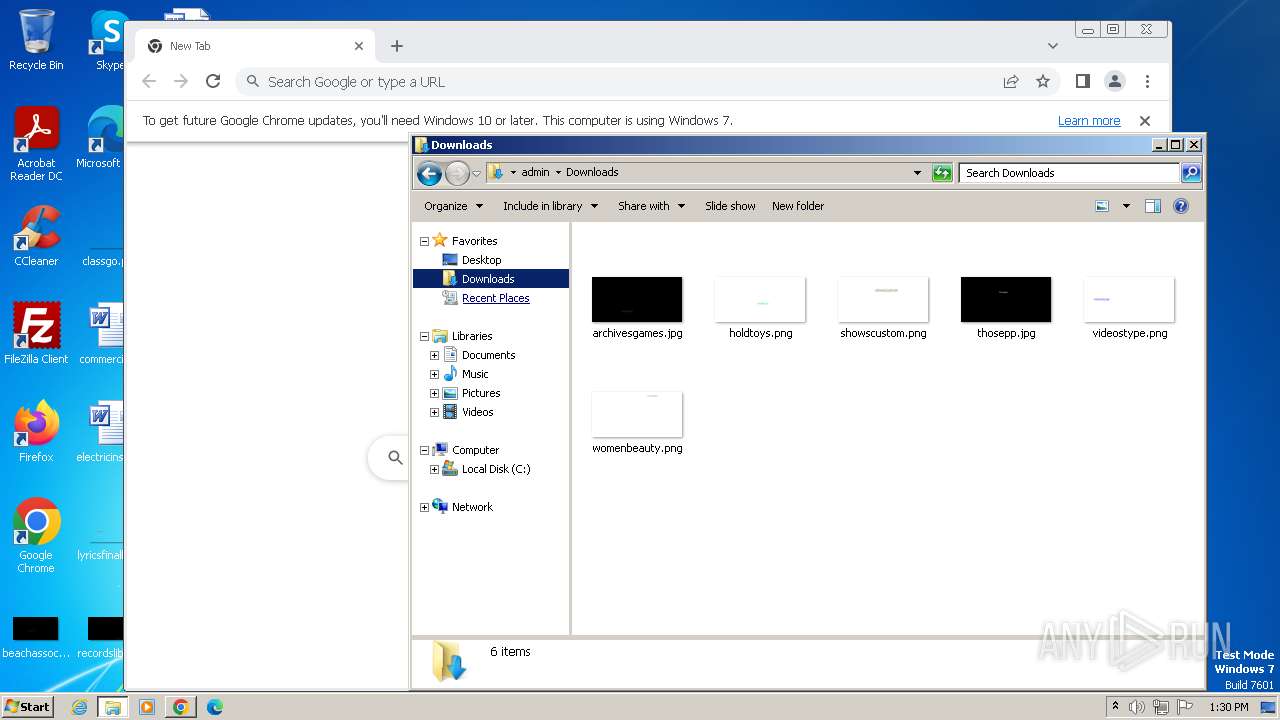
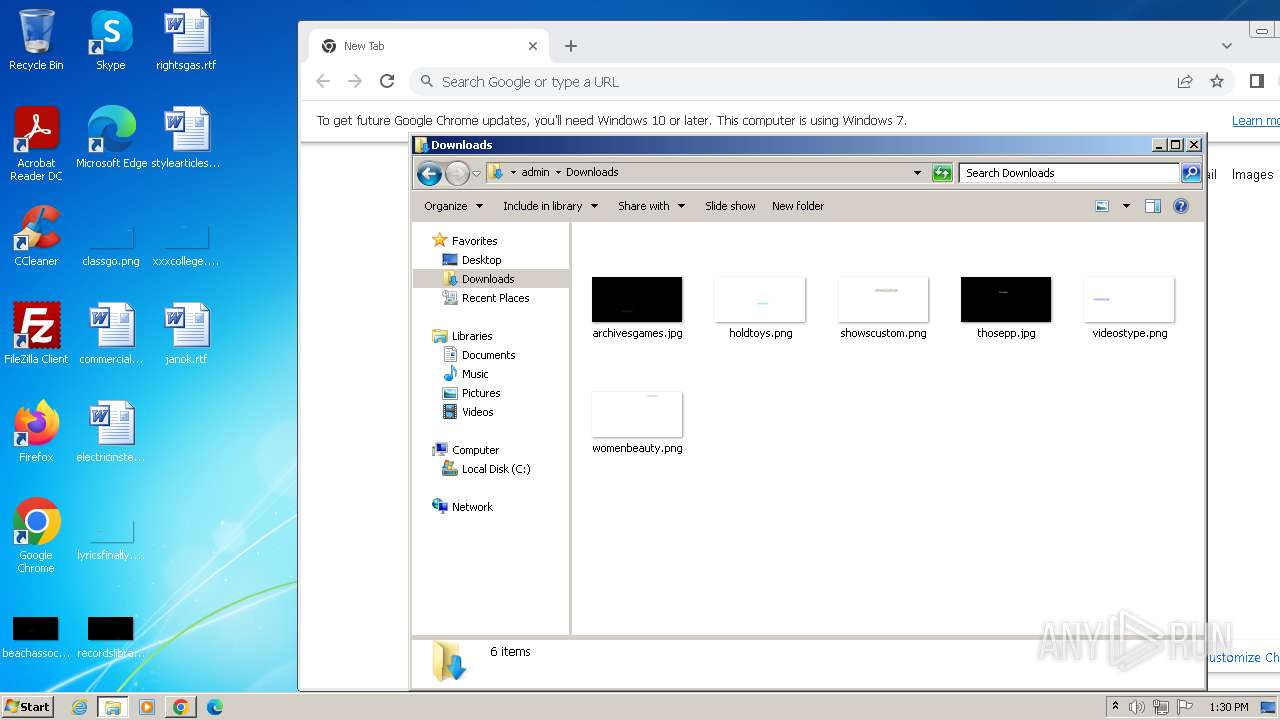
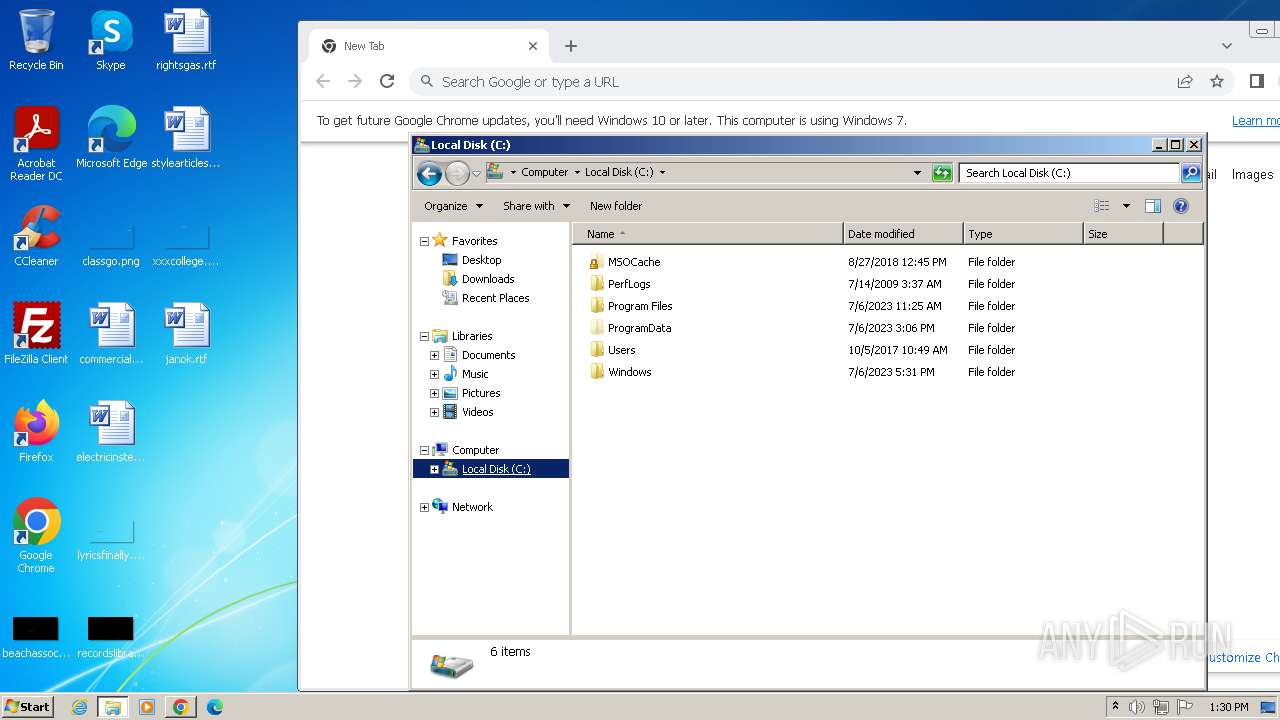
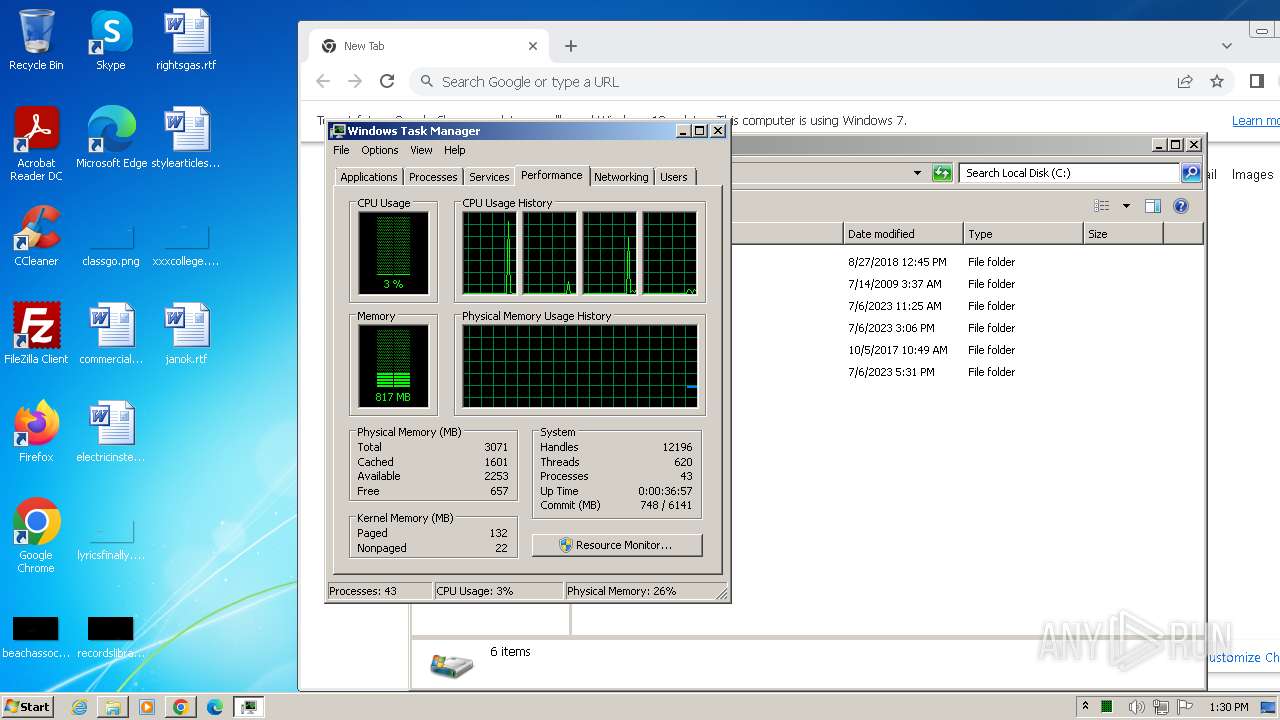
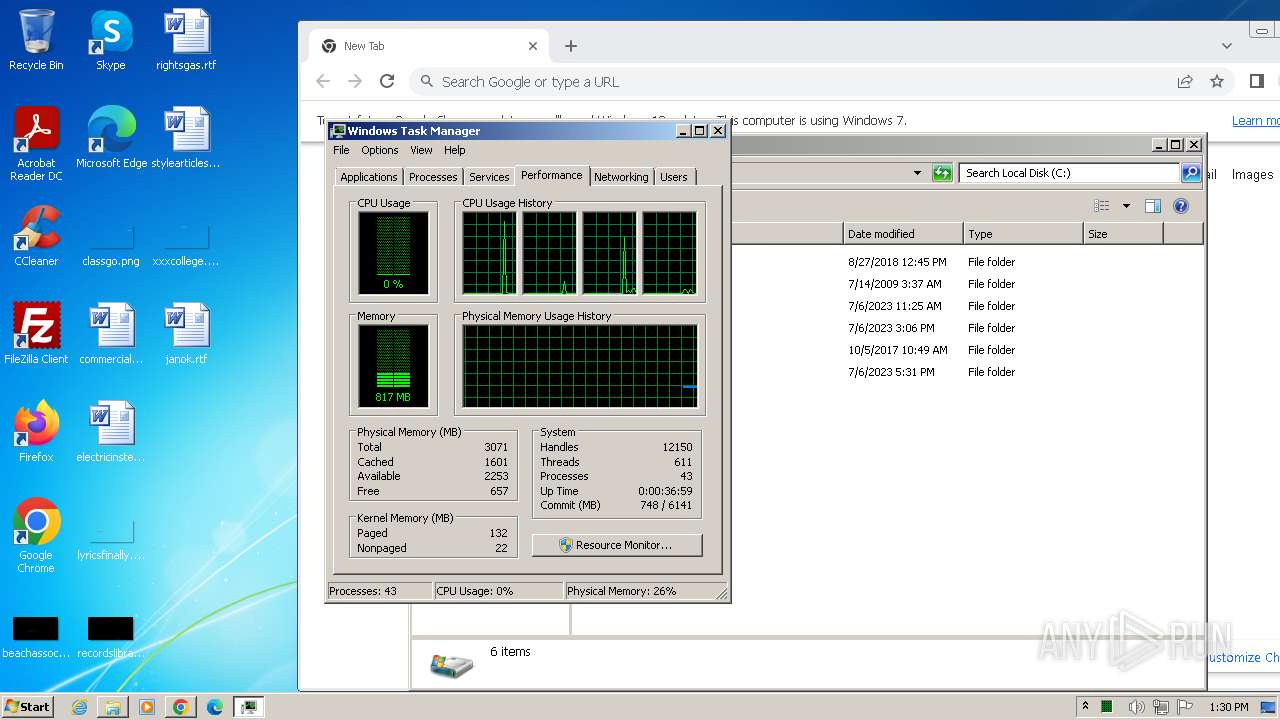
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 54F6A6F6B98E566E0317849CBF9BBB51 |
| SHA1: | 0E74611ED3A08D37B8D4BAB84BD84ECD11AAA49D |
| SHA256: | BF41C0870684D5721193099469326C54BDFAC07D4897702F3F254BD9ECC4D4F9 |
| SSDEEP: | 96:Ugpv4jmatW7dkN7P+ca9J0PM8C8F4m/ngzshxjId2JOxGlHbVtncrtJEvxZmaWk5:tOL/SsWSbNc20CHjnqtKzmaWAFJh |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- mohio_v4.exe (PID: 1036)
Reads the Internet Settings
- mohio_v4.exe (PID: 1036)
Starts CMD.EXE for commands execution
- mohio_v4.exe (PID: 1036)
Executing commands from ".cmd" file
- mohio_v4.exe (PID: 1036)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3832)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- mohio_v4.exe (PID: 1036)
Process drops legitimate windows executable
- chrome.exe (PID: 3276)
INFO
Drops the executable file immediately after the start
- WinRAR.exe (PID: 280)
- chrome.exe (PID: 3276)
Reads the computer name
- mohio_v4.exe (PID: 1036)
- wmpnscfg.exe (PID: 2316)
Checks supported languages
- mohio_v4.exe (PID: 1036)
- wmpnscfg.exe (PID: 2316)
Reads the machine GUID from the registry
- mohio_v4.exe (PID: 1036)
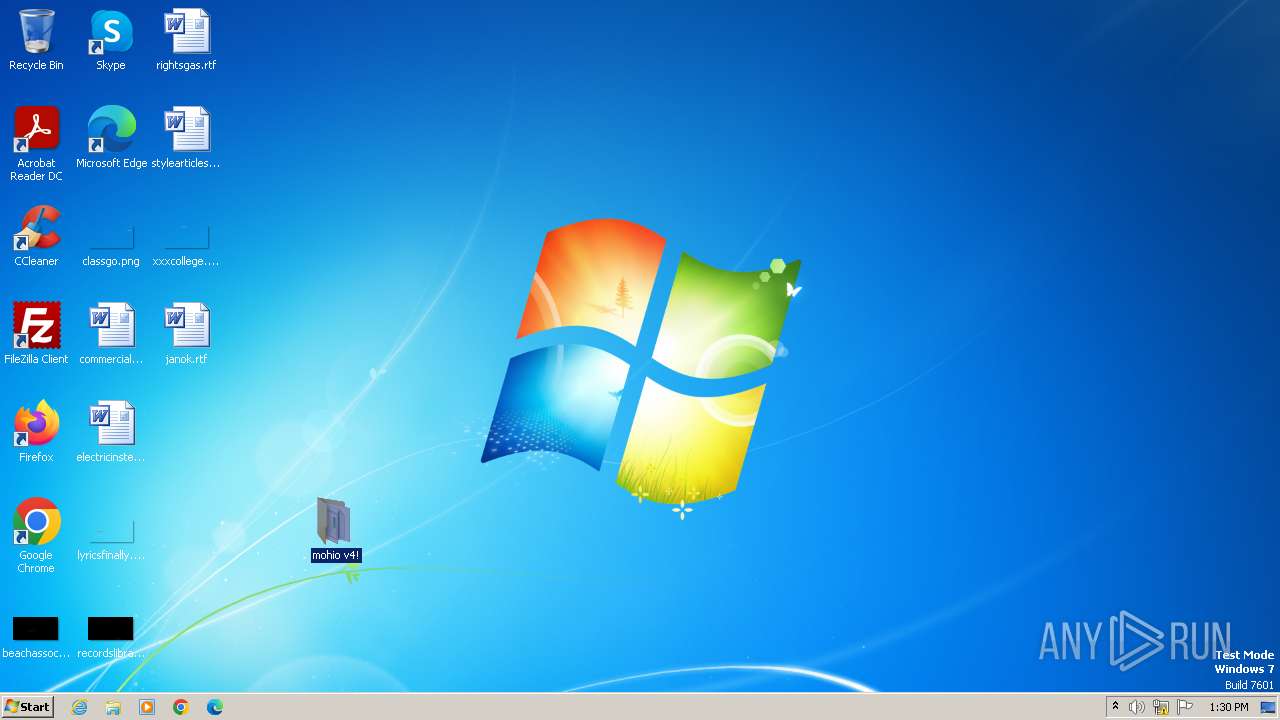
Manual execution by a user
- mohio_v4.exe (PID: 1036)
- wmpnscfg.exe (PID: 2316)
- chrome.exe (PID: 3276)
- taskmgr.exe (PID: 476)
Create files in a temporary directory
- mohio_v4.exe (PID: 1036)
Reads Environment values
- mohio_v4.exe (PID: 1036)
Application launched itself
- chrome.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:12:13 20:31:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | mohio v4!/ |
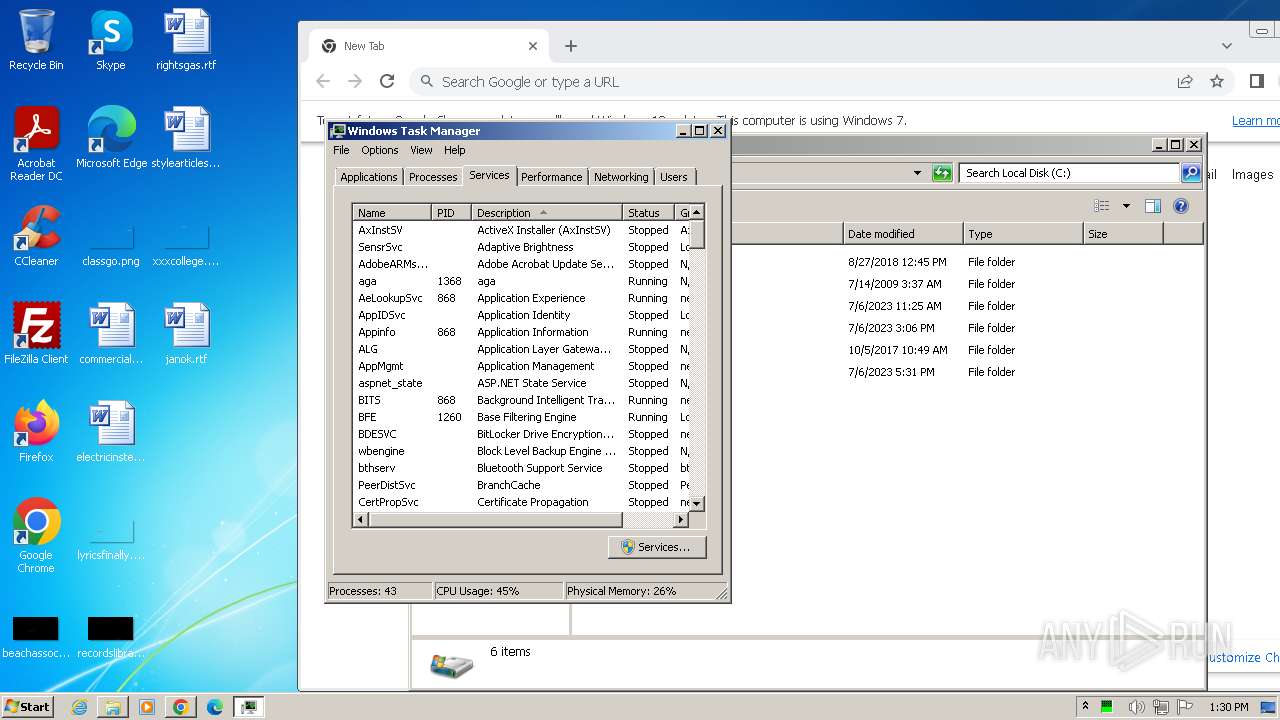
Total processes
59
Monitored processes
20
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
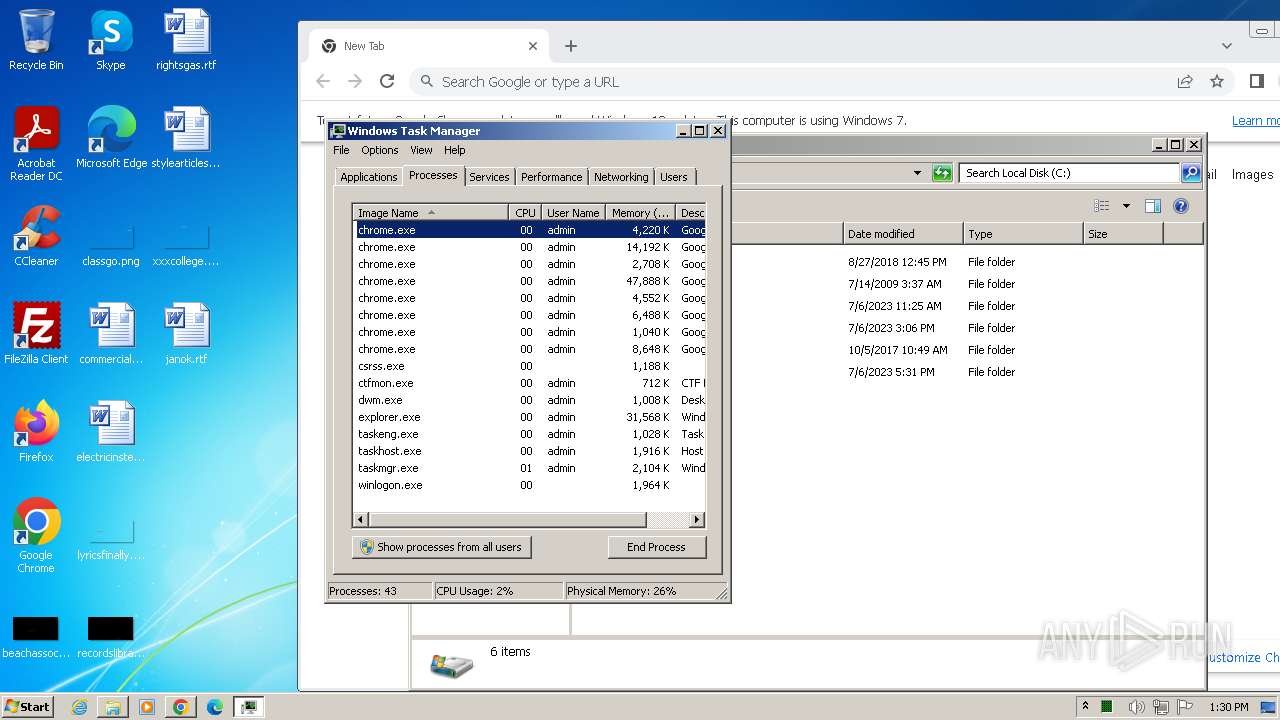
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\mohio_v4!.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 476 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\Desktop\mohio v4!\mohio_v4.exe" | C:\Users\admin\Desktop\mohio v4!\mohio_v4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3492 --field-trial-handle=1148,i,12173230244663164366,5033864398730958740,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1368 --field-trial-handle=1148,i,12173230244663164366,5033864398730958740,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3144 | timeout 4 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2104 --field-trial-handle=1148,i,12173230244663164366,5033864398730958740,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1504 --field-trial-handle=1148,i,12173230244663164366,5033864398730958740,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
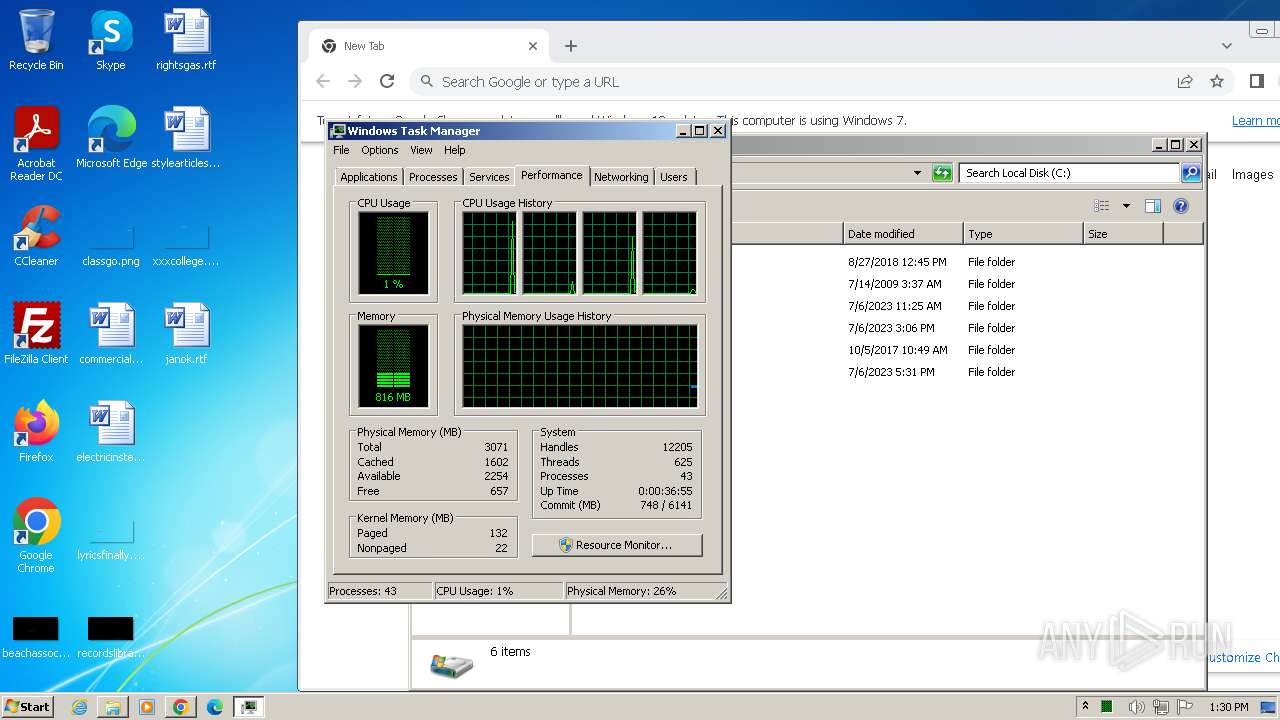
Total events
5 722
Read events
5 662
Write events
60
Delete events
0
Modification events
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
2
Suspicious files
29
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF215f84.TMP | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
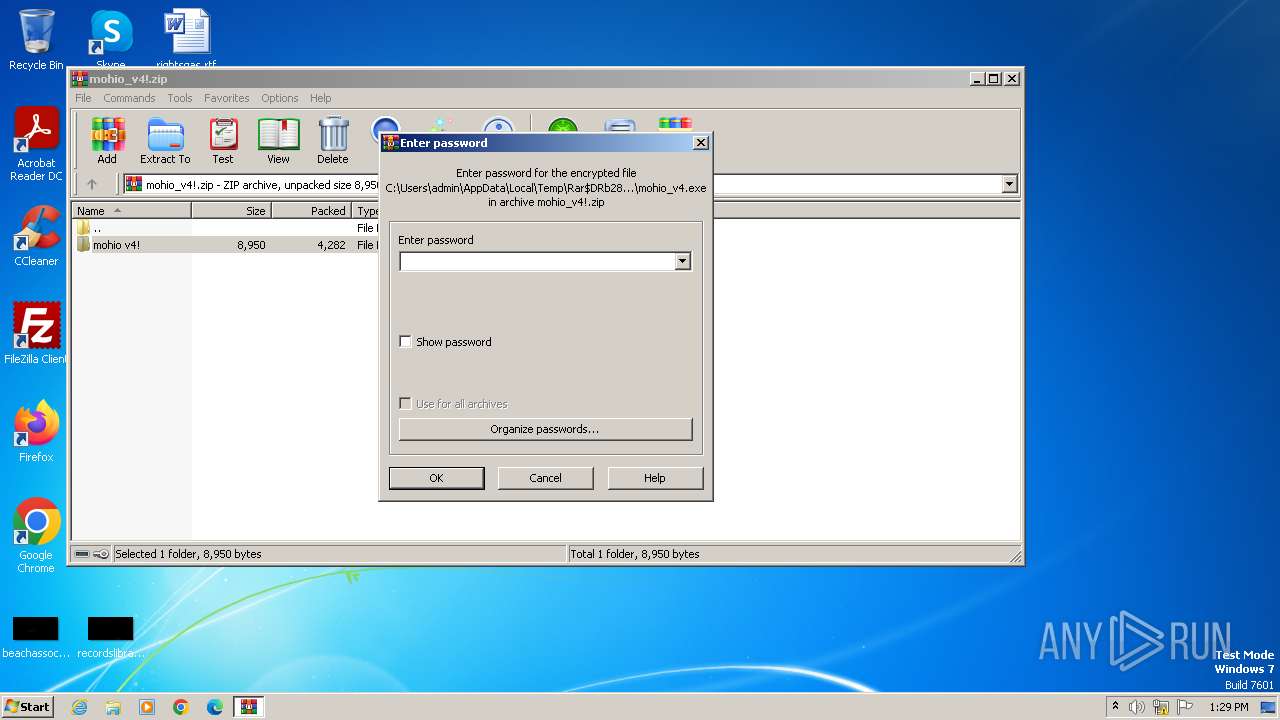
| 280 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb280.7715\mohio v4!\readme.txt | text | |
MD5:527B9FA1E138AB5904421AEB12F5E539 | SHA256:E2003E44EA455031AB3B773ED720C8AC5EF819DFFDC3A3F503095E46C4917F90 | |||
| 1036 | mohio_v4.exe | C:\Users\admin\AppData\Local\Temp\tmp4601.tmp.cmd | text | |
MD5:A27F08A2BFBF2C693E791638098425BE | SHA256:D30C29E6D97A292F2BC7E128DE104E7C25531A889F297E06941D1C1064E496A9 | |||
| 280 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb280.7715\mohio v4!\mohio_v4.exe | executable | |
MD5:3E487D6B7883E158C6A5F94BB417EC06 | SHA256:9AF35827DFB4A918A84F7D3CE1853218E0A29CD3724B9D8A7BE324C93FE30265 | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF215f84.TMP | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF2160fb.TMP | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:C97BAF91C596FA593691D5E6E7FB9F76 | SHA256:FDC084A61F5F9FB116C267A58754A89DC42B480572C3800F964BC79BF52A135B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
15
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1036 | mohio_v4.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger Inc | GB | unknown |
3276 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2696 | chrome.exe | 142.250.185.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2696 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
2696 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.telegram.org |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
1036 | mohio_v4.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
1036 | mohio_v4.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |