| File name: | RunAsTI64.exe |
| Full analysis: | https://app.any.run/tasks/ac665a6e-e162-4e81-af6d-b7e944e85b73 |
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2025, 13:27:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 9B9F954F38F4987F1735F2A4AE15DDE0 |
| SHA1: | 2B63E22649BC554E360871ED3F8F83CC50E70987 |
| SHA256: | BF365D7D5BC3076E5A7F41BB9F0B9E9BEB58AE900BFFCB3BBB10B575C08D66DB |
| SSDEEP: | 98304:Z4XM5lNJ4oVVlA4kEm2O0uh68QqoBXSCXPGms1lw3F0YmKDSd0ujR58Vq84wE8hQ: |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- RunAsTI64.exe (PID: 7140)
- RunAsTI64.exe (PID: 5476)
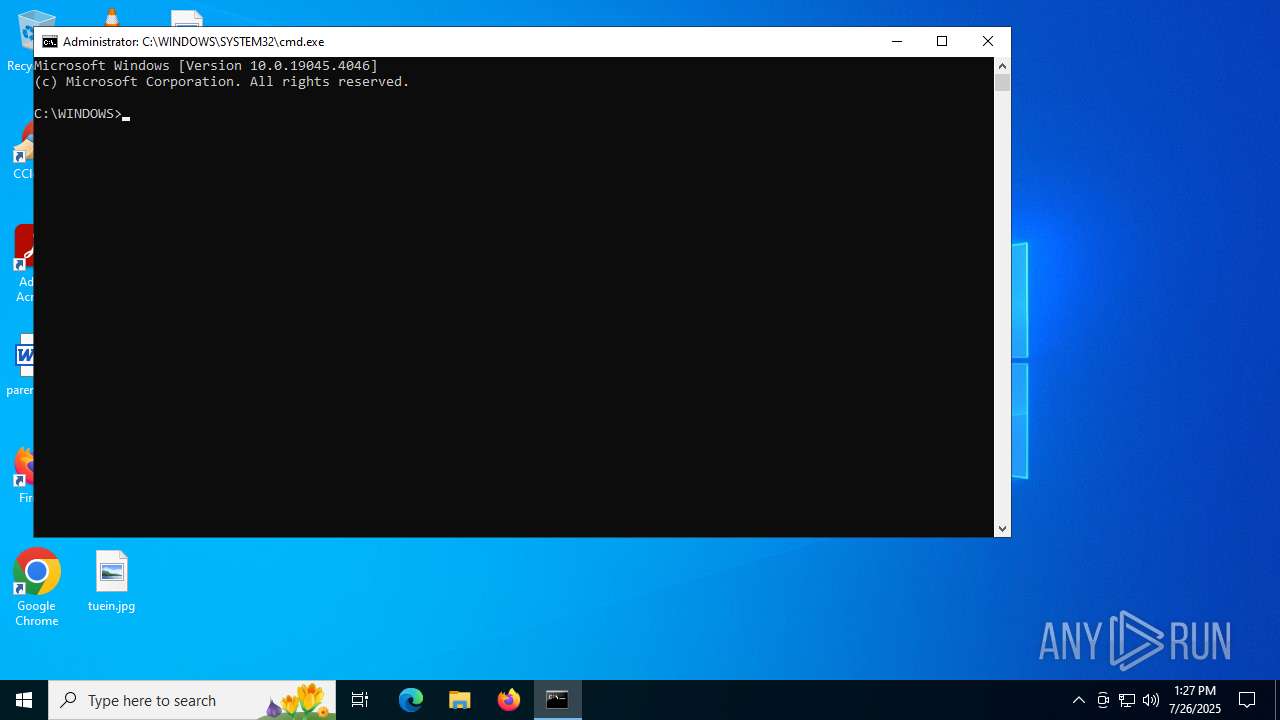
Starts CMD.EXE for commands execution
- RunAsTI64.exe (PID: 5556)
- RunFromToken64.exe (PID: 6796)
- RunAsTI64.exe (PID: 2028)
- RunFromToken64.exe (PID: 2692)
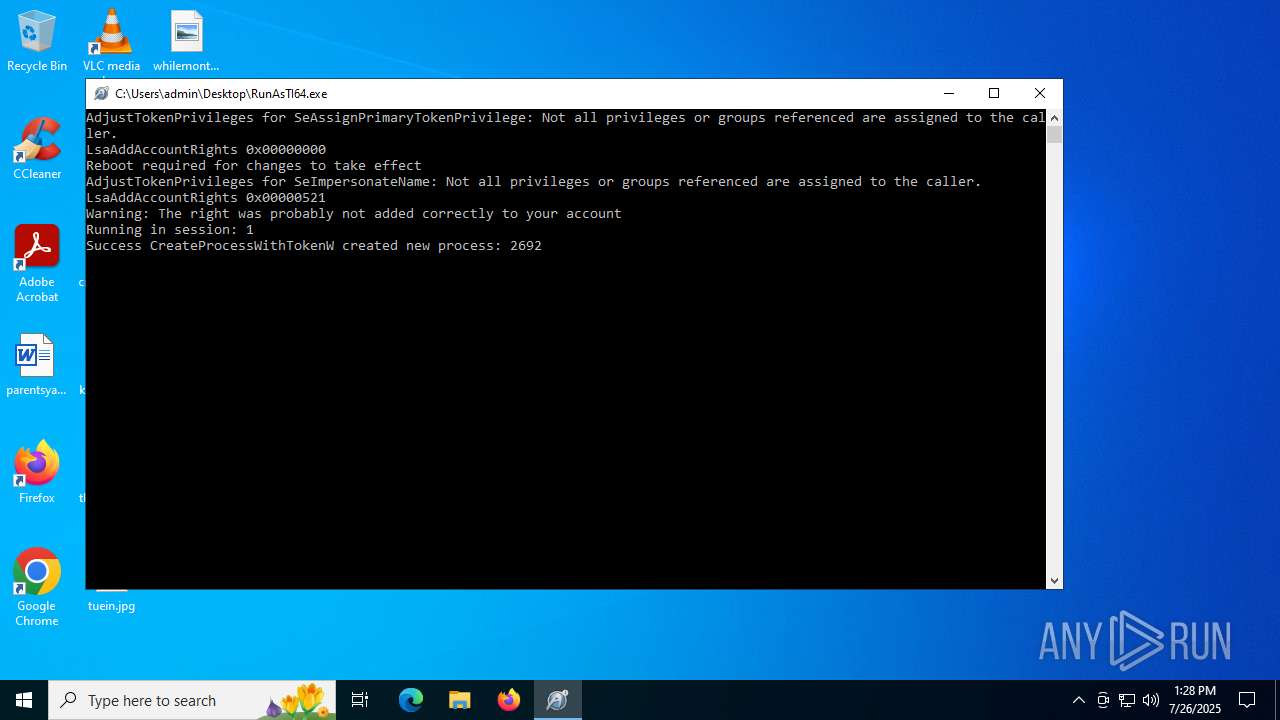
Starts SC.EXE for service management
- cmd.exe (PID: 3852)
- cmd.exe (PID: 1324)
Windows service management via SC.EXE
- sc.exe (PID: 1132)
- sc.exe (PID: 5240)
Reads security settings of Internet Explorer
- RunAsTI64.exe (PID: 5476)
- RunAsTI64.exe (PID: 7140)
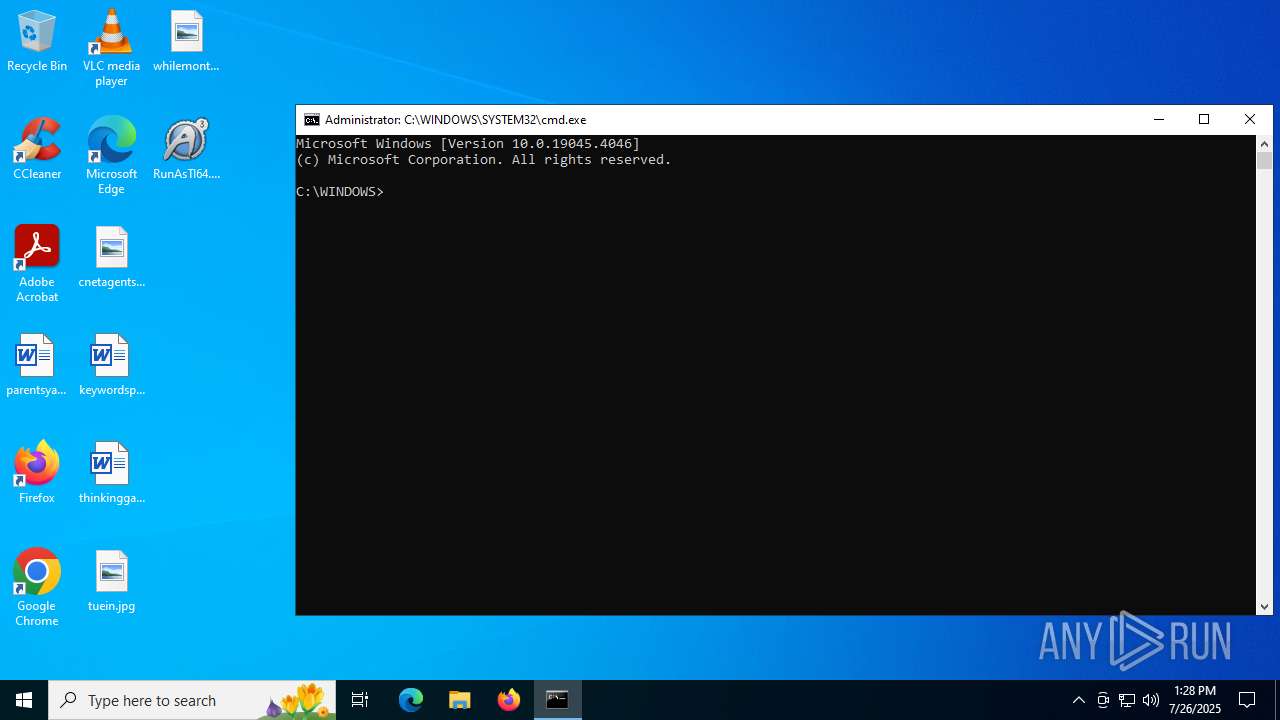
Application launched itself
- RunAsTI64.exe (PID: 5476)
- RunAsTI64.exe (PID: 7140)
Executable content was dropped or overwritten
- RunAsTI64.exe (PID: 2028)
- RunAsTI64.exe (PID: 5556)
INFO
The sample compiled with english language support
- RunAsTI64.exe (PID: 7140)
- RunAsTI64.exe (PID: 5556)
- RunAsTI64.exe (PID: 2028)
Reads mouse settings
- RunFromToken64.exe (PID: 6796)
- RunAsTI64.exe (PID: 7140)
- RunAsTI64.exe (PID: 5476)
- RunAsTI64.exe (PID: 2028)
- RunFromToken64.exe (PID: 2692)
- RunAsTI64.exe (PID: 5556)
Reads the computer name
- RunAsTI64.exe (PID: 7140)
- RunAsTI64.exe (PID: 5476)
- RunFromToken64.exe (PID: 6796)
- RunFromToken64.exe (PID: 2692)
- RunAsTI64.exe (PID: 2028)
- RunAsTI64.exe (PID: 5556)
Checks supported languages
- RunAsTI64.exe (PID: 7140)
- RunAsTI64.exe (PID: 5476)
- RunFromToken64.exe (PID: 6796)
- RunAsTI64.exe (PID: 2028)
- RunAsTI64.exe (PID: 5556)
- RunFromToken64.exe (PID: 2692)
Process checks computer location settings
- RunAsTI64.exe (PID: 7140)
- RunAsTI64.exe (PID: 5476)
Create files in a temporary directory
- RunAsTI64.exe (PID: 5556)
- RunAsTI64.exe (PID: 2028)
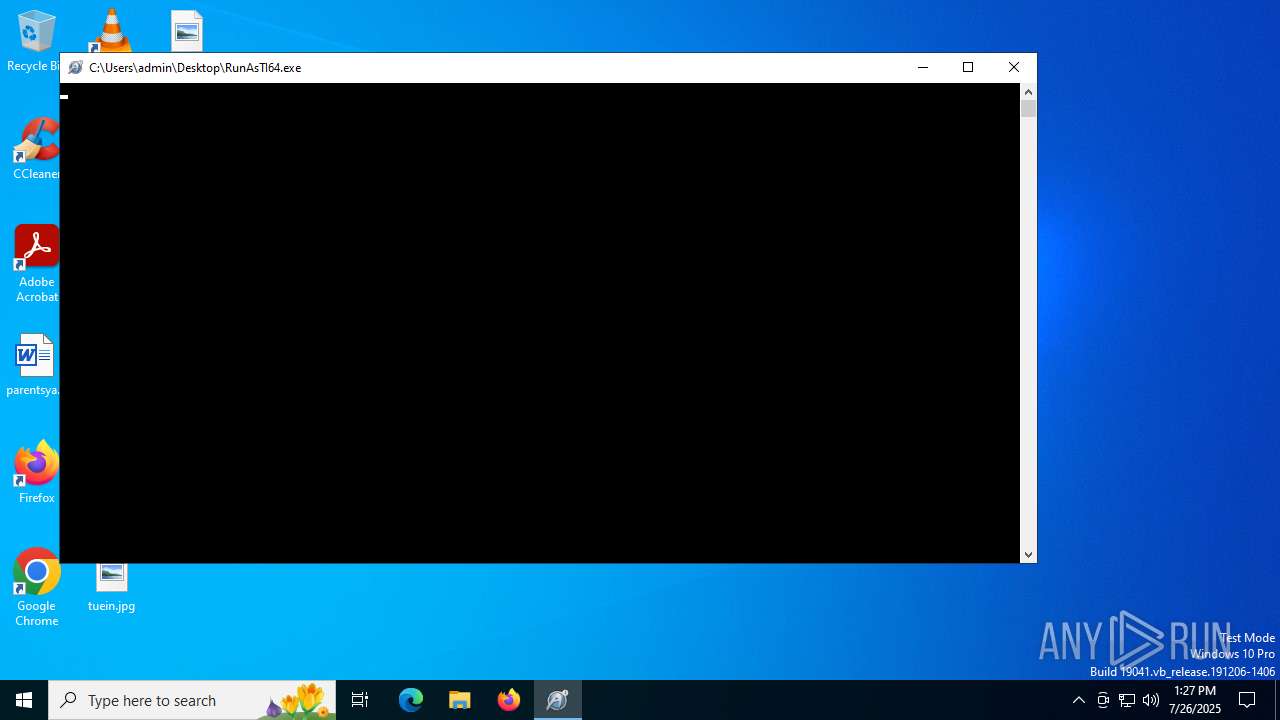
Manual execution by a user
- RunAsTI64.exe (PID: 5476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:09:28 08:02:58+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 12 |
| CodeSize: | 689152 |
| InitializedDataSize: | 2193920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2fb2c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 3.3.14.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.1 |
| Comments: | Start program with same privileges as TrustedInstaller |
| FileDescription: | Start program with same privileges as TrustedInstaller |
| ProductVersion: | 3.3.14.5 |
| LegalCopyright: | ©1999-2018 Jonathan Bennett & AutoIt Team |
Total processes
157
Monitored processes
23
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | sc start trustedinstaller | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RunAsTI64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | cmd.exe /c sc start trustedinstaller | C:\Windows\System32\cmd.exe | — | RunAsTI64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2028 | "C:\Users\admin\Desktop\RunAsTI64.exe" ! | C:\Users\admin\Desktop\RunAsTI64.exe | RunAsTI64.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Start program with same privileges as TrustedInstaller Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2312 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RunFromToken64.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | cmd.exe | C:\Windows\System32\cmd.exe | — | RunFromToken64.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | C:\Users\admin\AppData\Local\Temp\RunFromToken64.exe trustedinstaller.exe 1 cmd.exe | C:\Users\admin\AppData\Local\Temp\RunFromToken64.exe | RunAsTI64.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Start a program based on the privileges from a given process' token Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
| 3852 | cmd.exe /c sc start trustedinstaller | C:\Windows\System32\cmd.exe | — | RunAsTI64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RunFromToken64.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4688 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 165
Read events
1 165
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5556 | RunAsTI64.exe | C:\Users\admin\AppData\Local\Temp\RunFromToken64.exe | executable | |
MD5:64746CBC92ABBB261097A7FA6EECD278 | SHA256:2E62931ADA755F4F09E4F7ED05C21C6681FF011992458F4344FEDDD9FCDFC960 | |||
| 2028 | RunAsTI64.exe | C:\Users\admin\AppData\Local\Temp\RunFromToken64.exe | executable | |
MD5:64746CBC92ABBB261097A7FA6EECD278 | SHA256:2E62931ADA755F4F09E4F7ED05C21C6681FF011992458F4344FEDDD9FCDFC960 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
37
DNS requests
14
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1864 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6024 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6656 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
6656 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
18.31.95.13.in-addr.arpa |
| unknown |
6.0.1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.7.0.0.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |