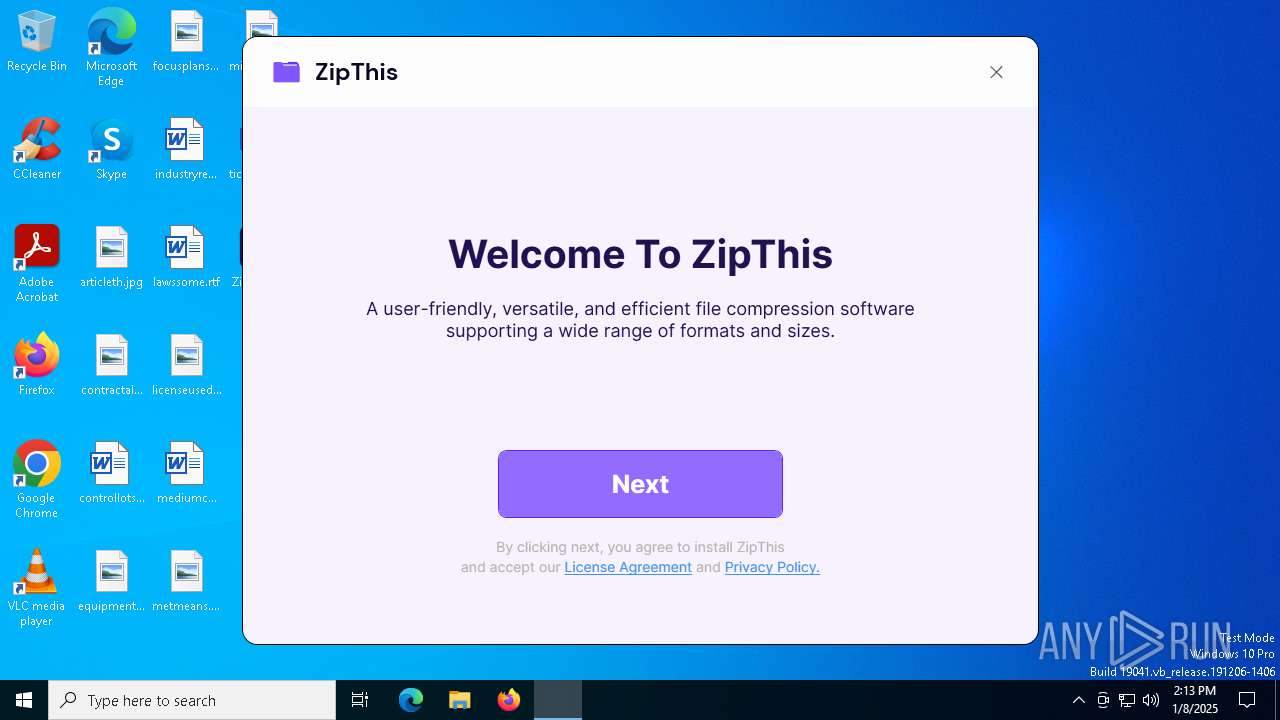
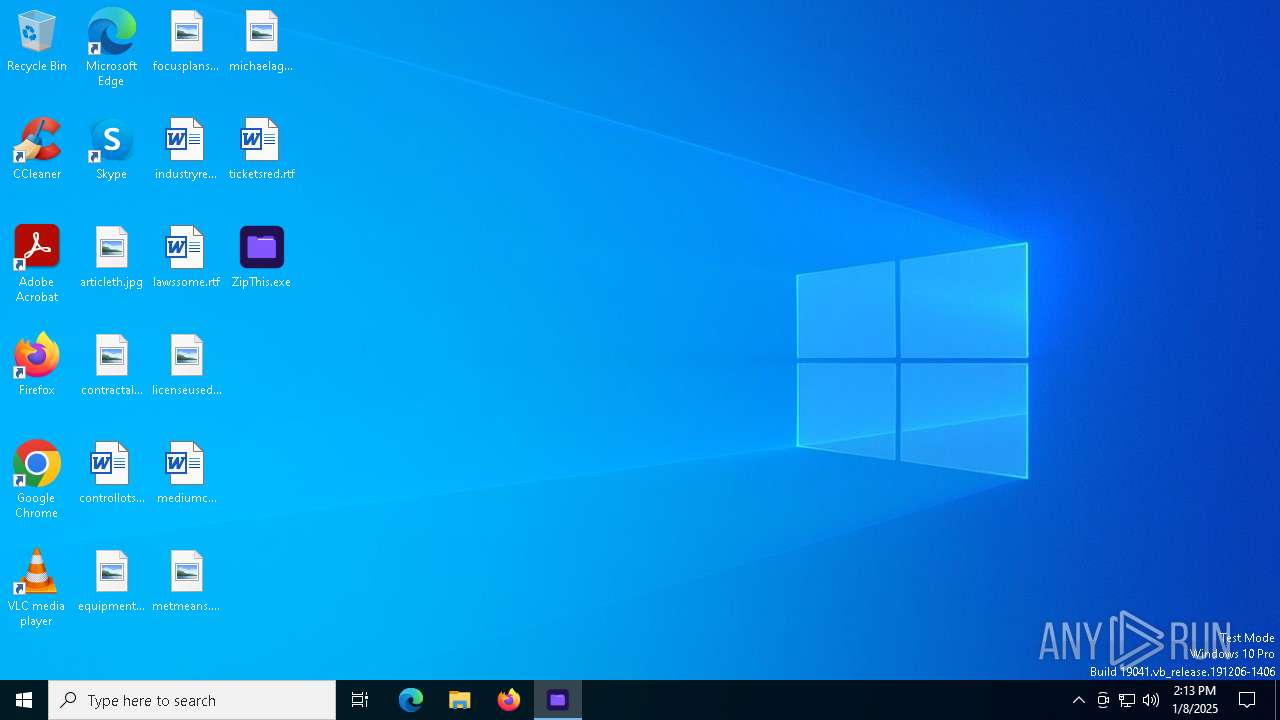
| File name: | ZipThis.exe |
| Full analysis: | https://app.any.run/tasks/7d1c85ca-3f69-4409-806b-0d4e20511197 |
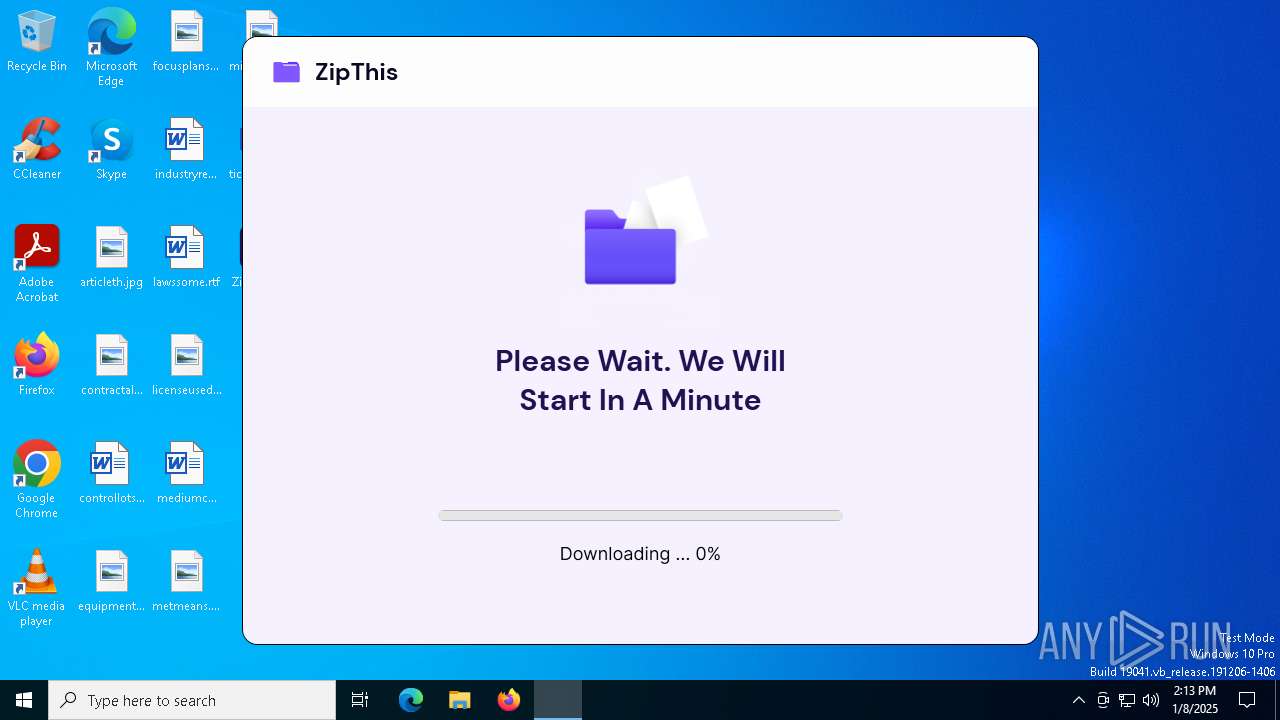
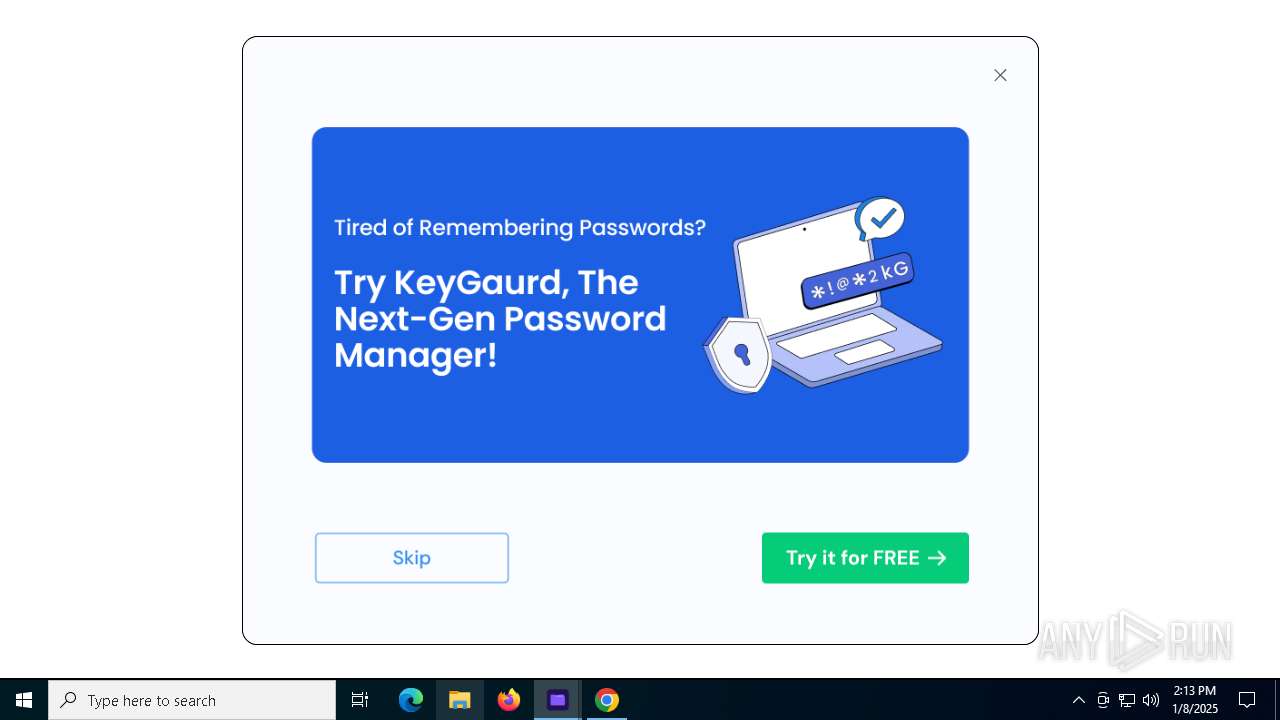
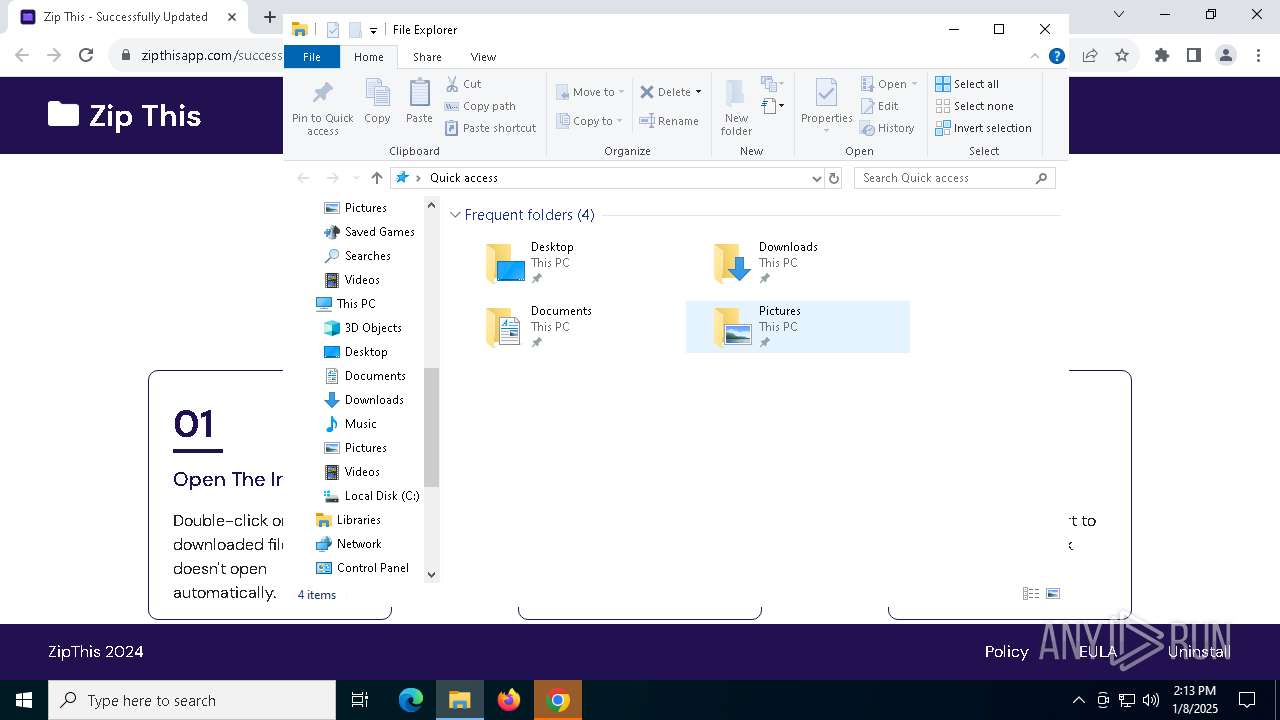
| Verdict: | Malicious activity |
| Analysis date: | January 08, 2025, 14:12:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 22A6CB7348B496600E7151A8112CBAC9 |
| SHA1: | F0CD50658868A3D347BEFF6977A54520C19AB640 |
| SHA256: | BF2F238D09AC55E7BAF3D73C80C82D3DF935DAA6B94ADF67A299AD3665E879E2 |
| SSDEEP: | 98304:gw4Duw4xT2ZyydruTlIseLSzW81j2iXrVfY9cZm4zdFhb4jyH1ZI30KqNJwFs1Du:pqwqz |
MALICIOUS
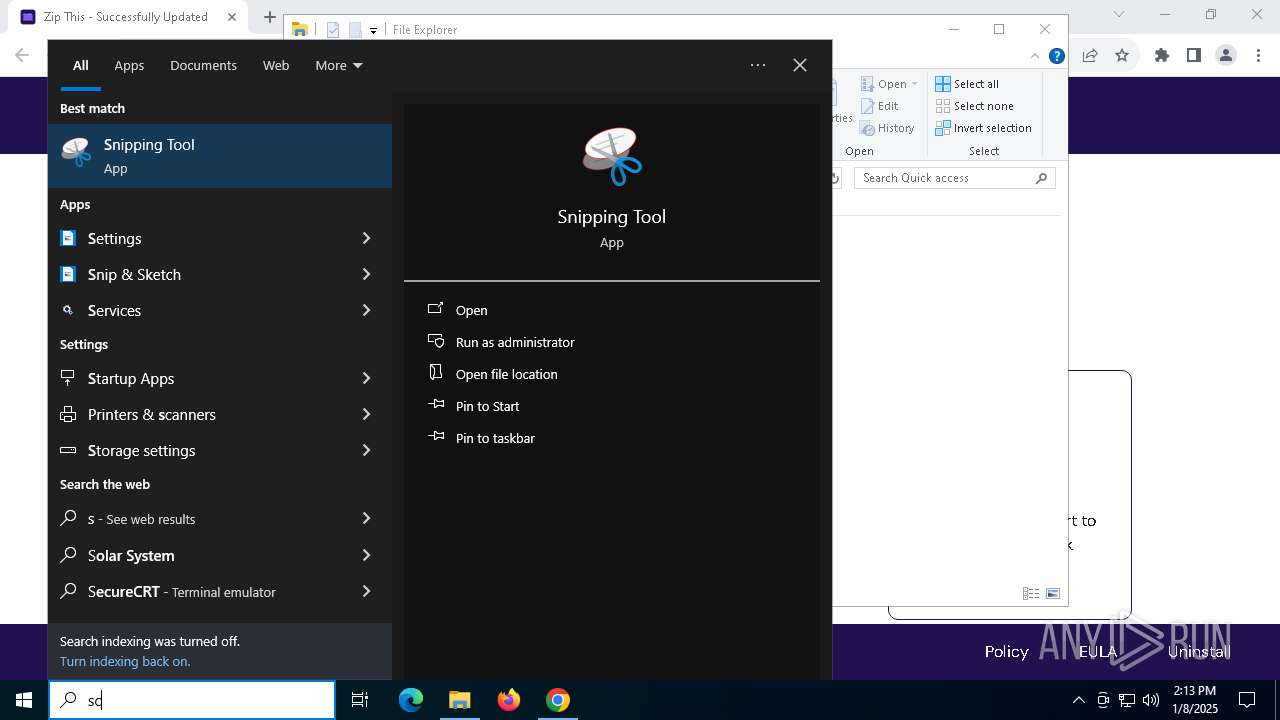
Changes powershell execution policy (RemoteSigned)
- ZipThis.exe (PID: 6924)
SUSPICIOUS
Process drops legitimate windows executable
- ZipThis.exe (PID: 6924)
The process drops C-runtime libraries
- ZipThis.exe (PID: 6924)
The process executes Powershell scripts
- ZipThis.exe (PID: 6924)
Starts POWERSHELL.EXE for commands execution
- ZipThis.exe (PID: 6924)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 6444)
Executable content was dropped or overwritten
- ZipThis.exe (PID: 6924)
Reads security settings of Internet Explorer
- ZipThis.exe (PID: 6924)
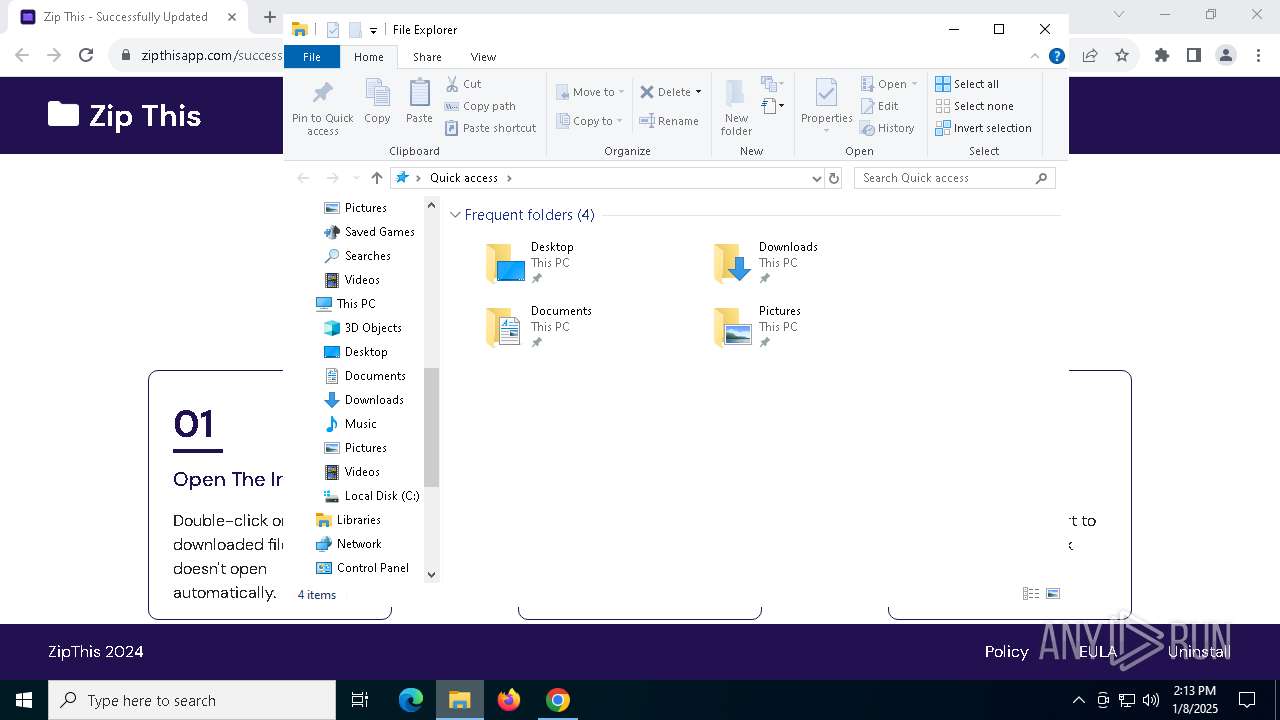
Creates a software uninstall entry
- ZipThis.exe (PID: 6924)
Searches for installed software
- ZipThis.exe (PID: 6924)
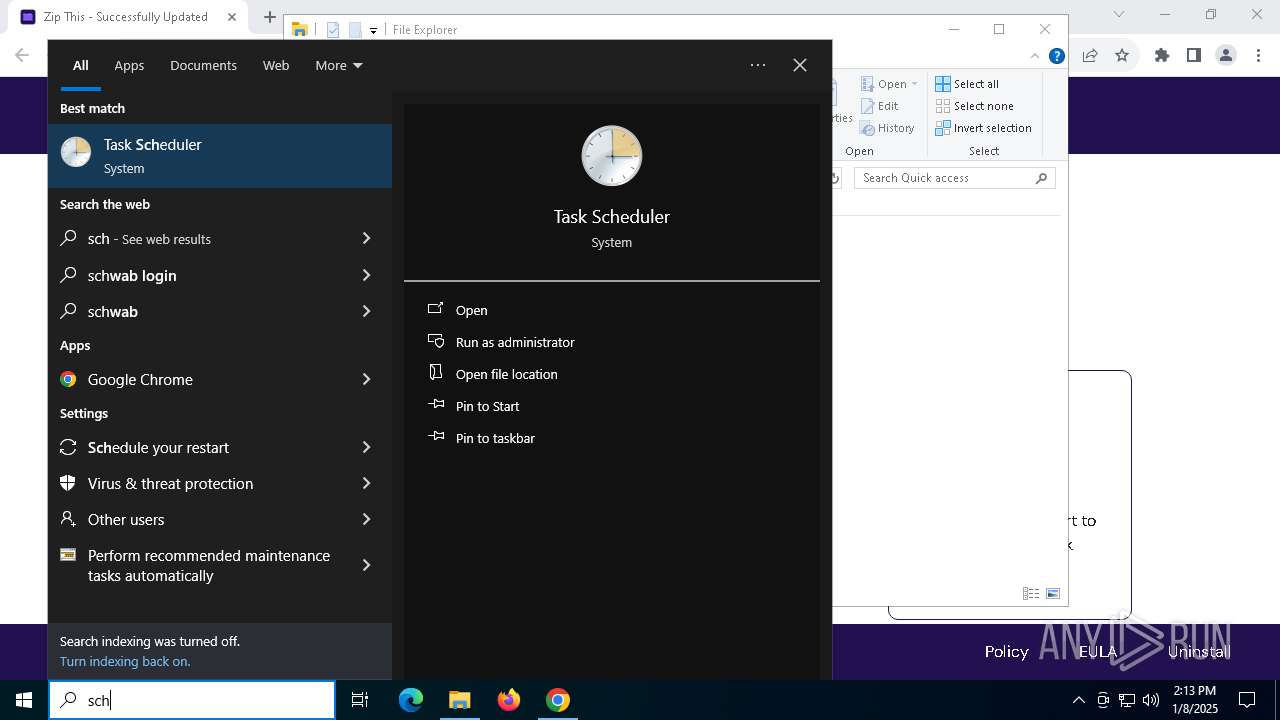
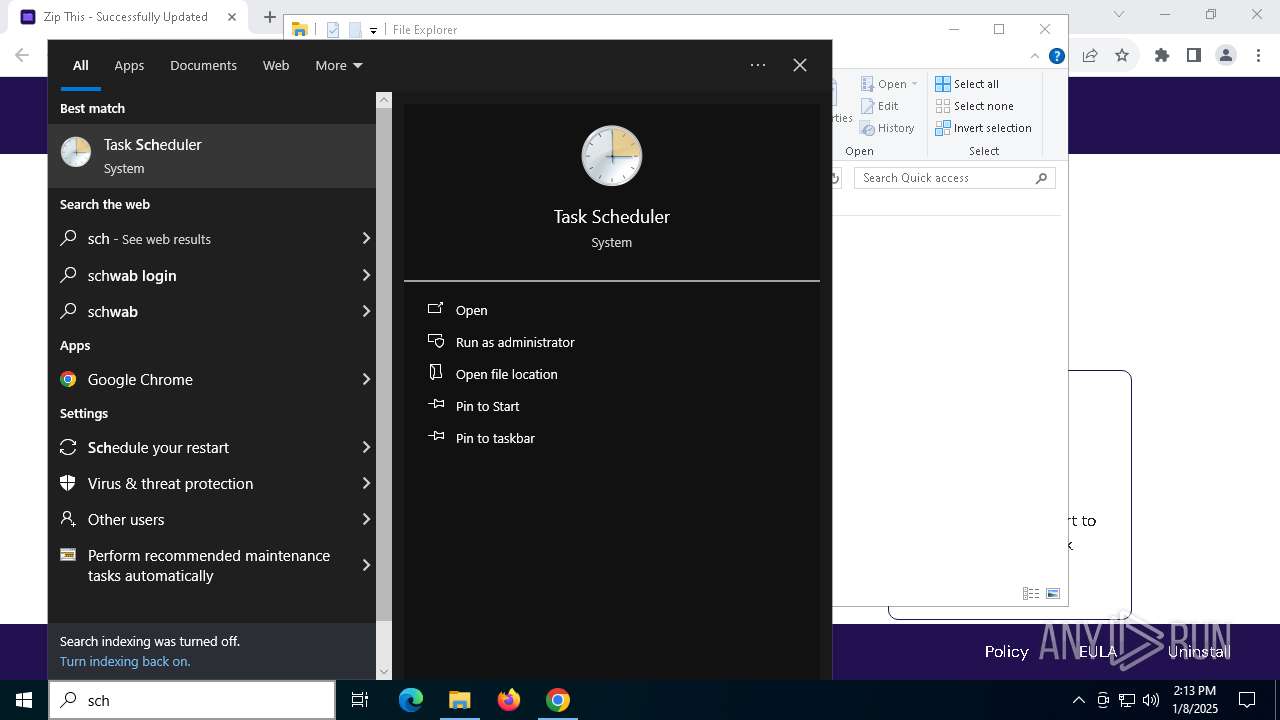
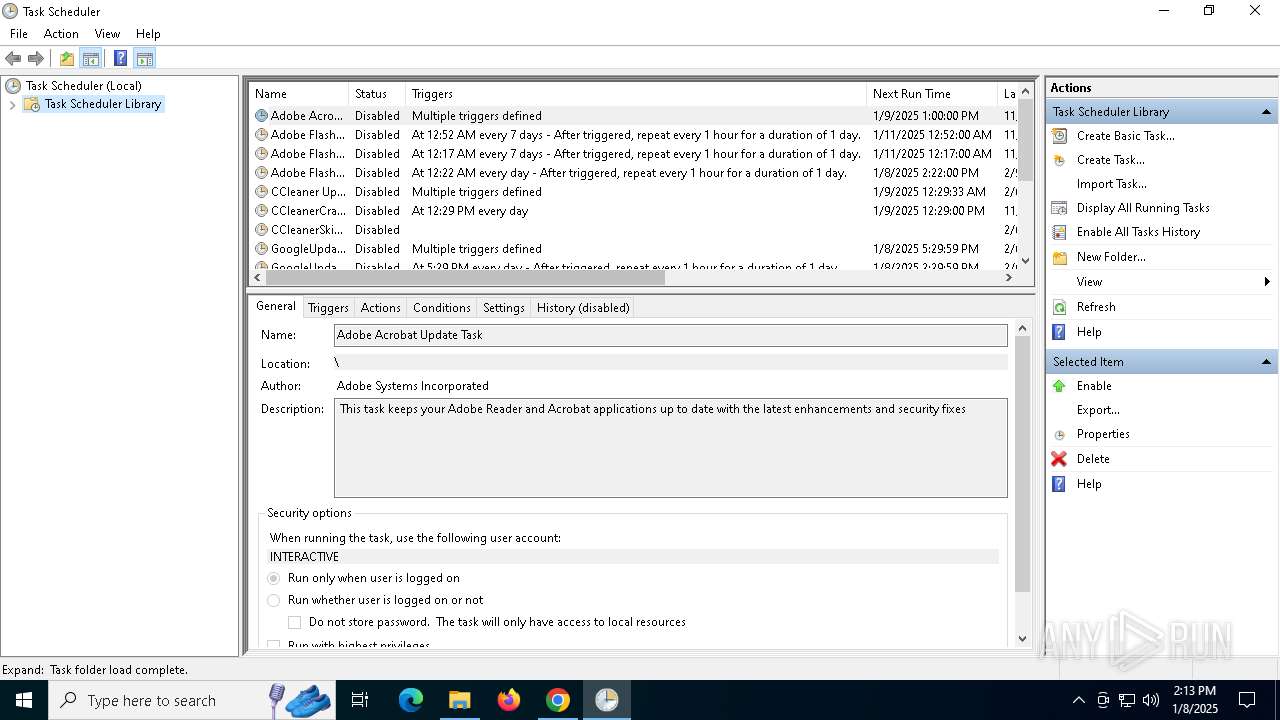
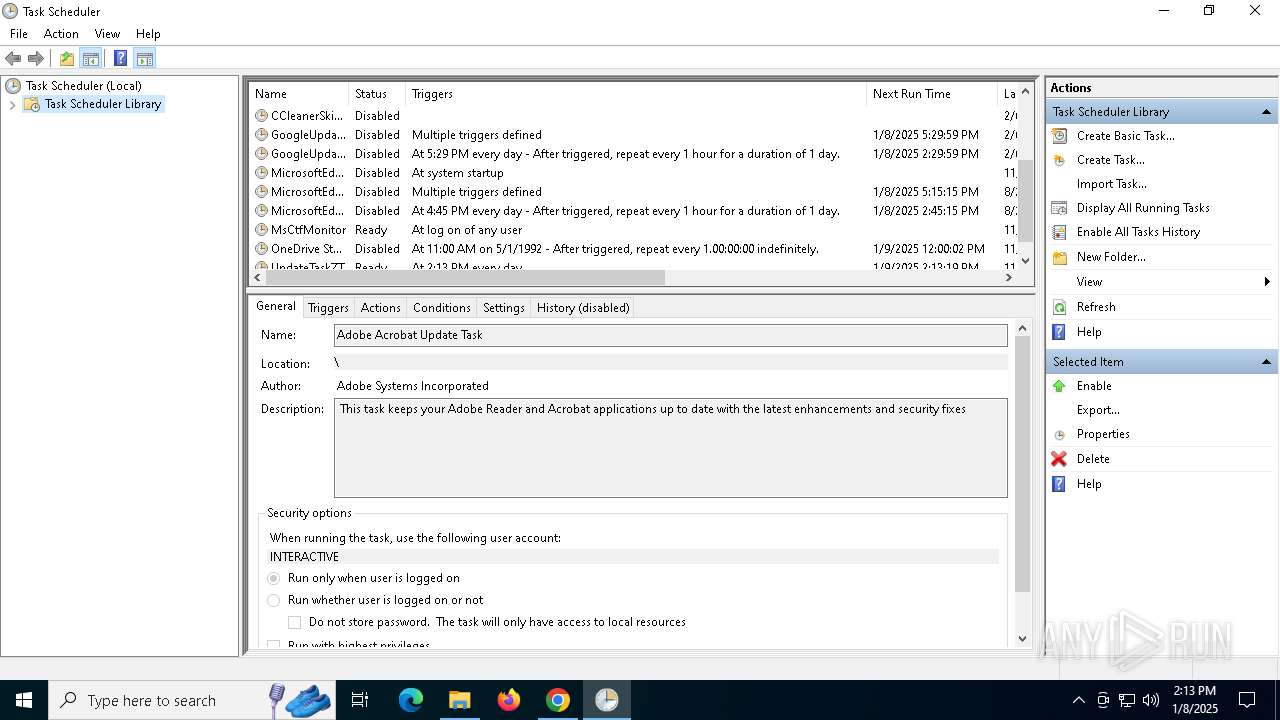
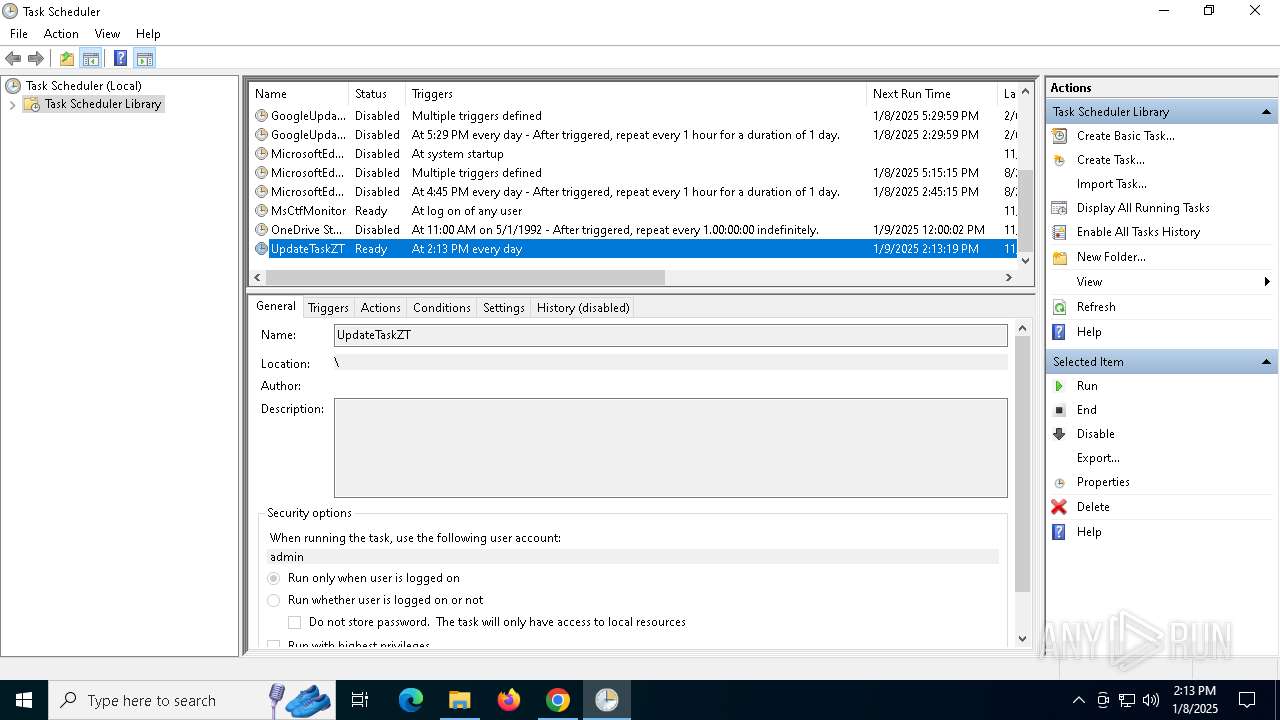
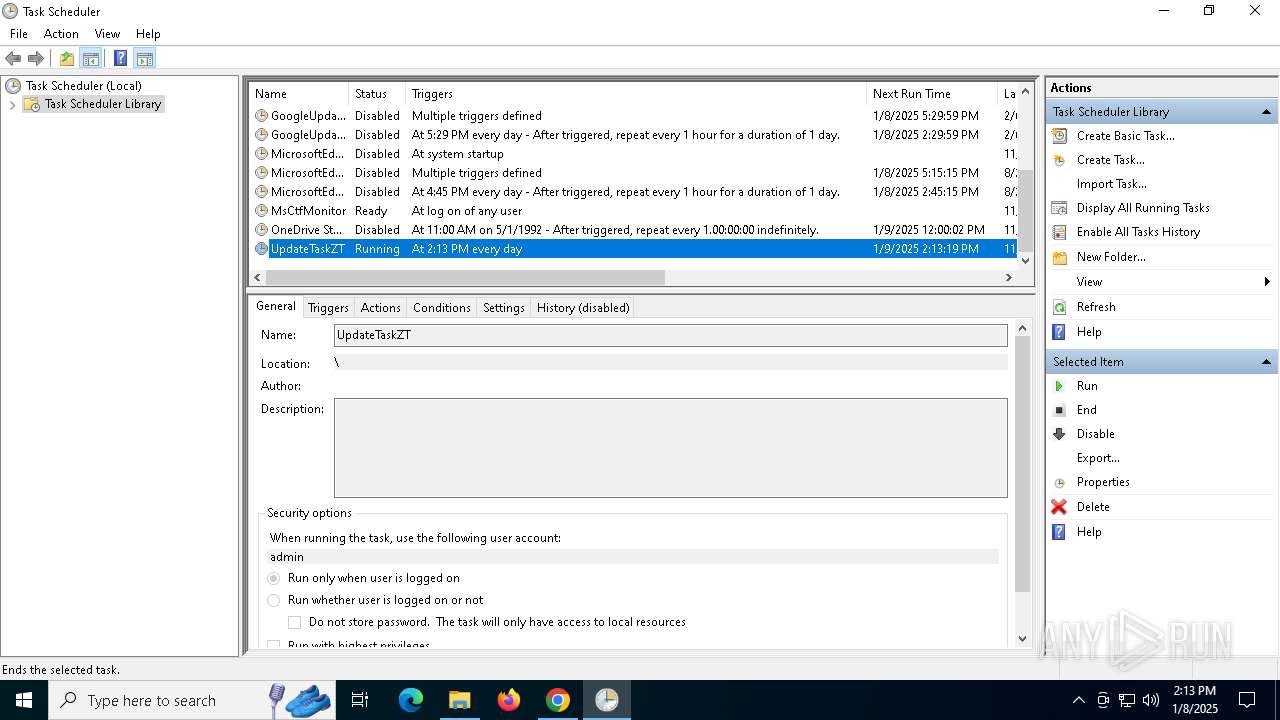
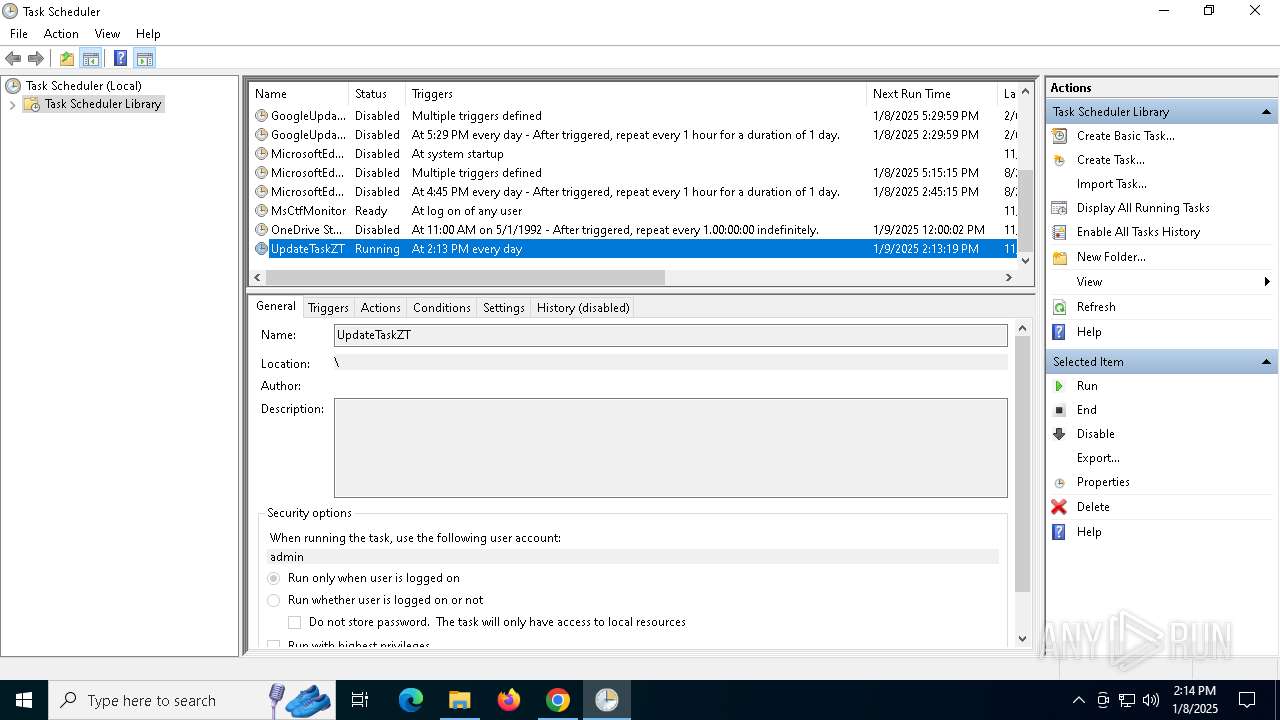
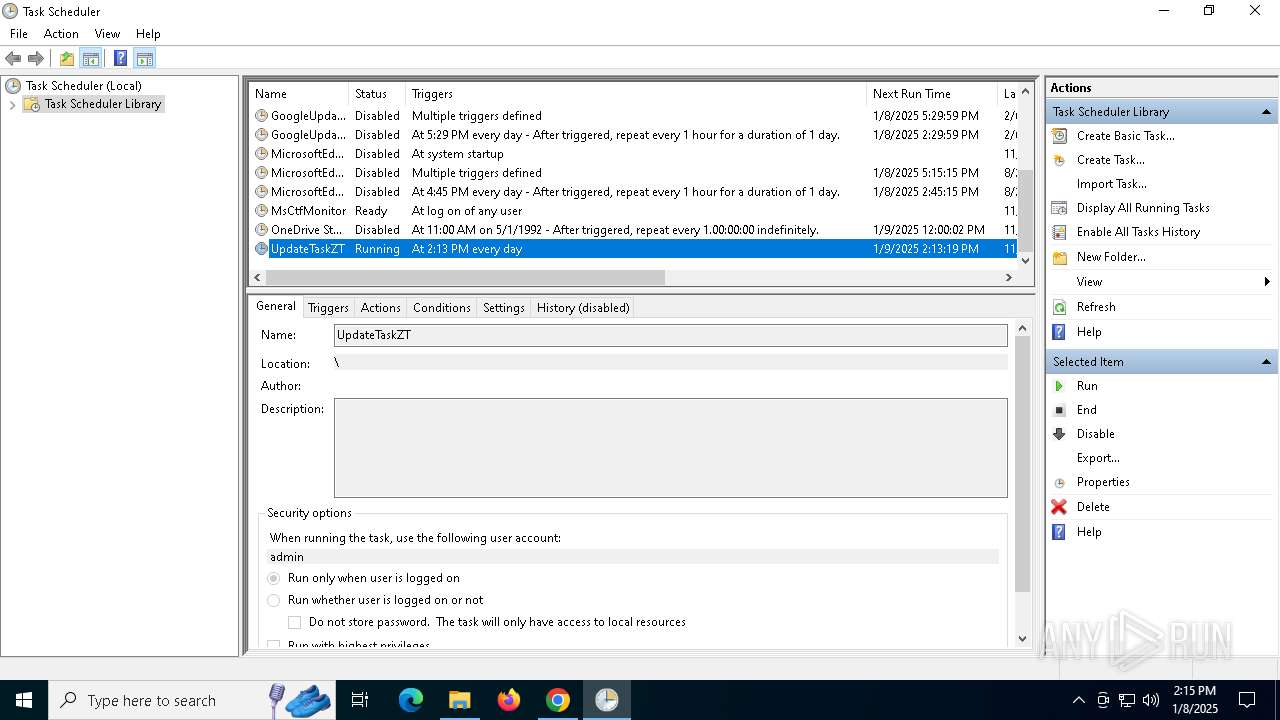
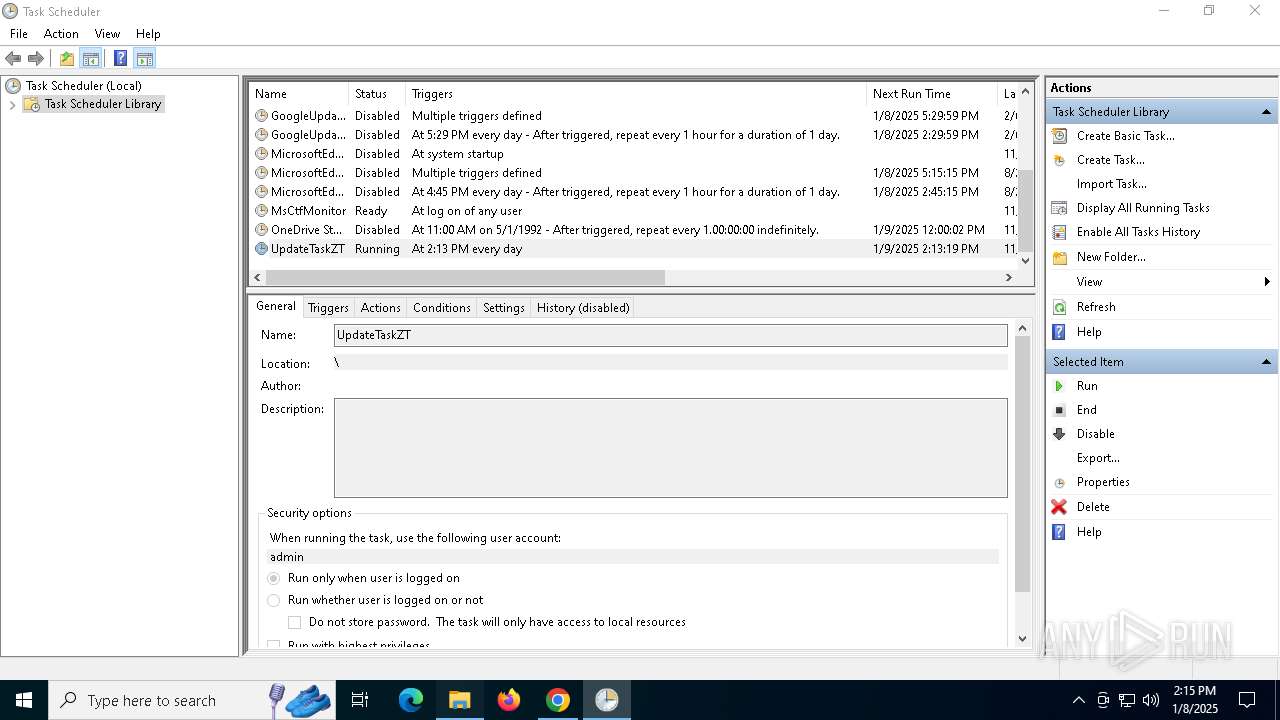
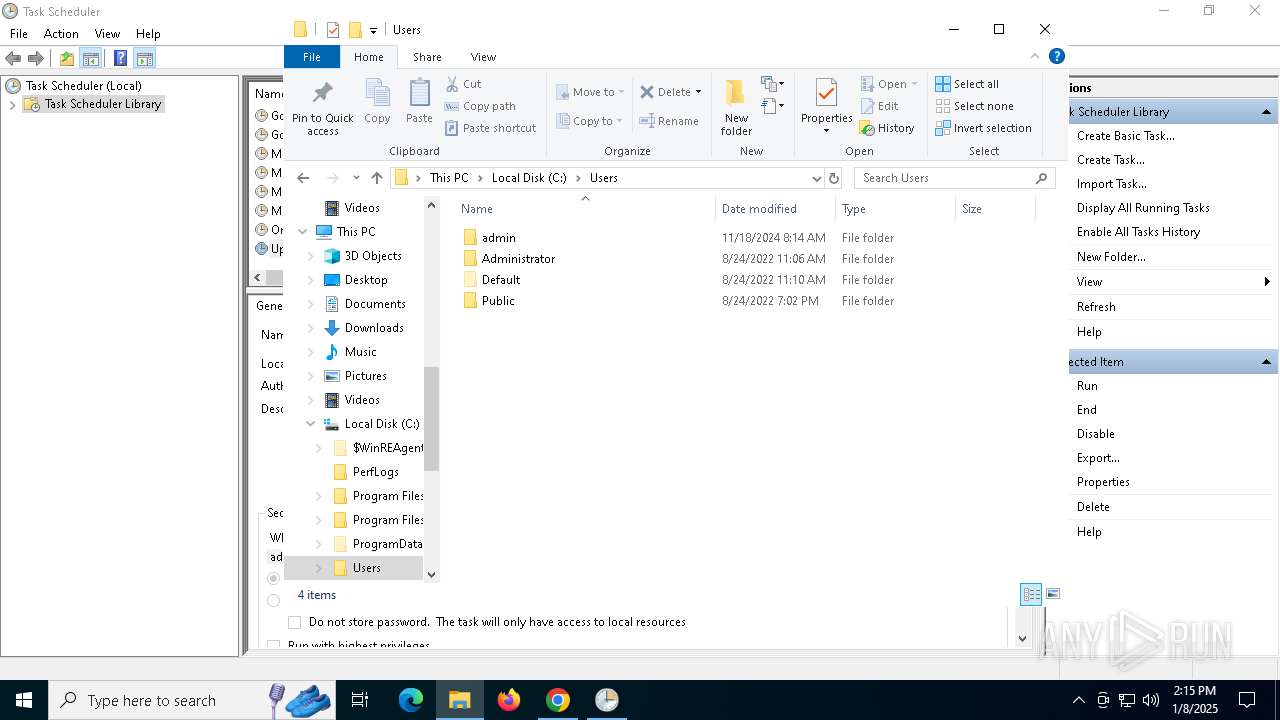
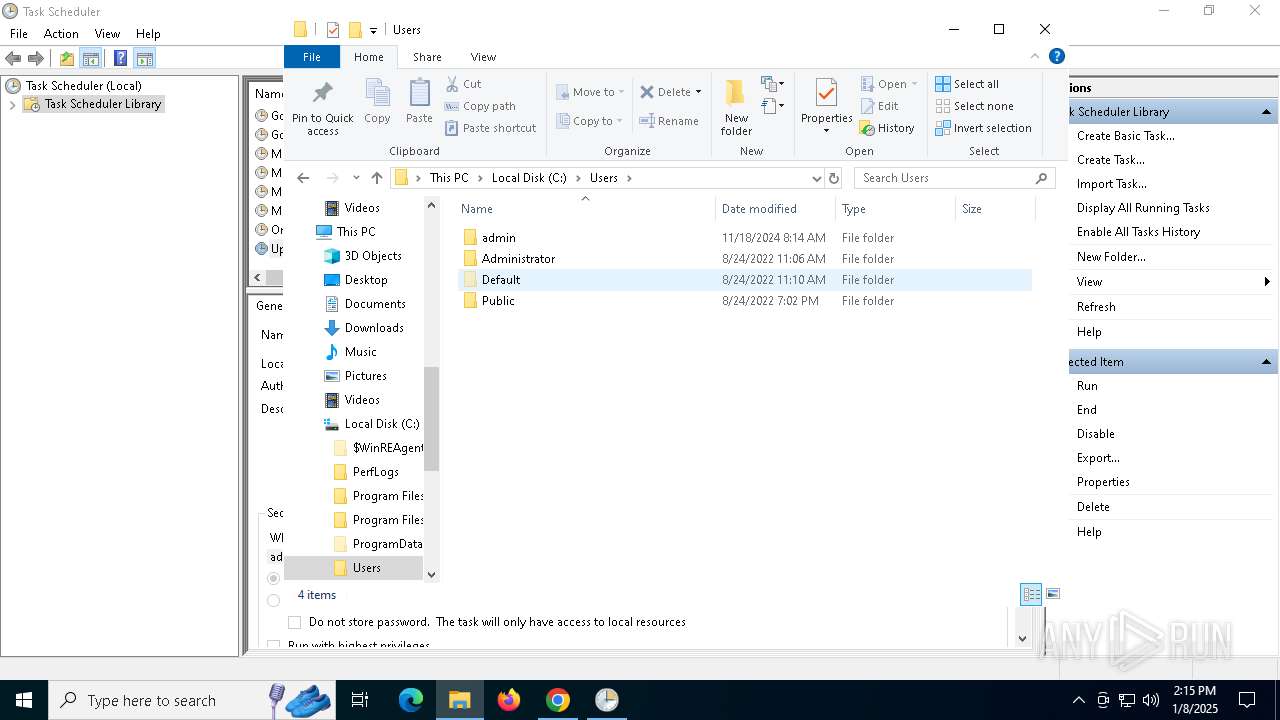
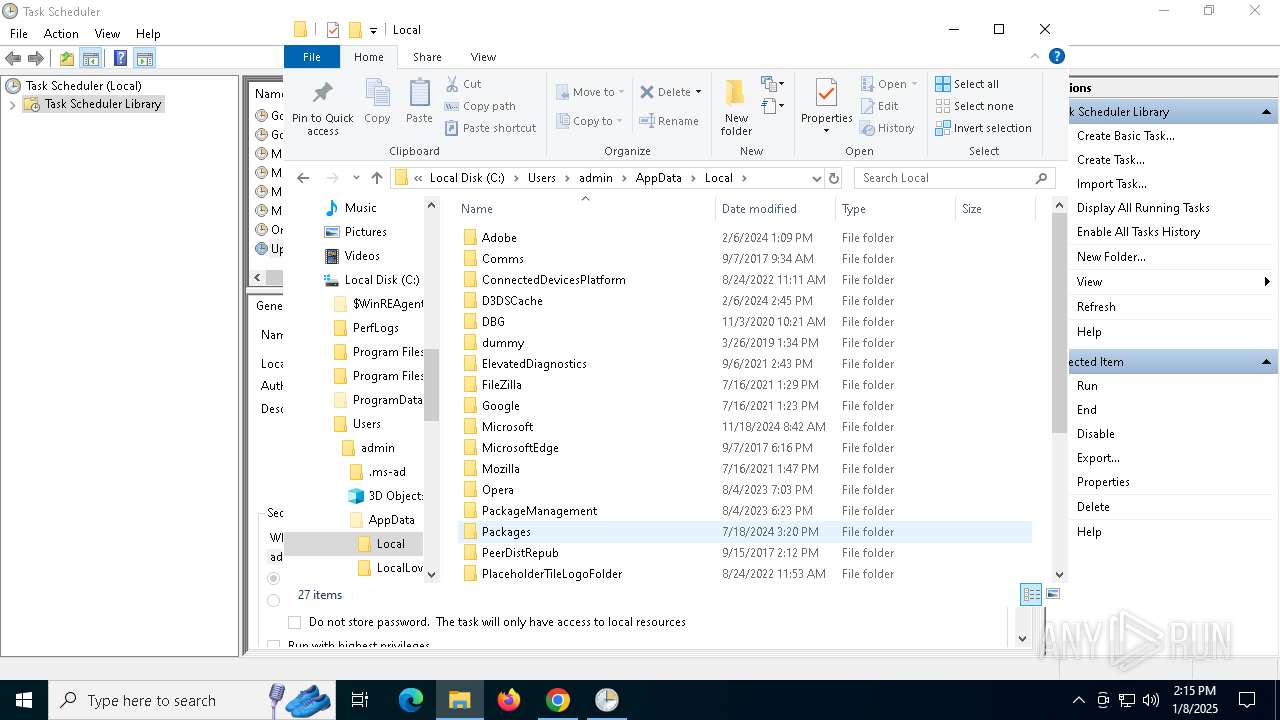
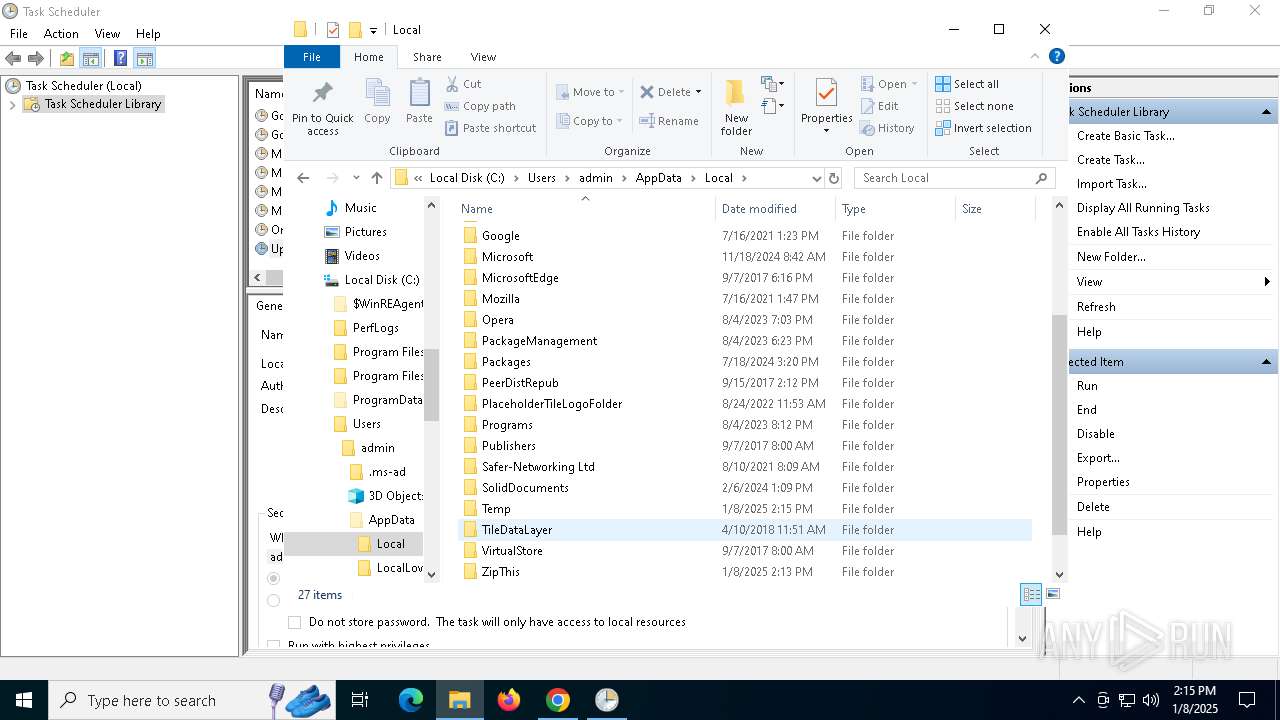
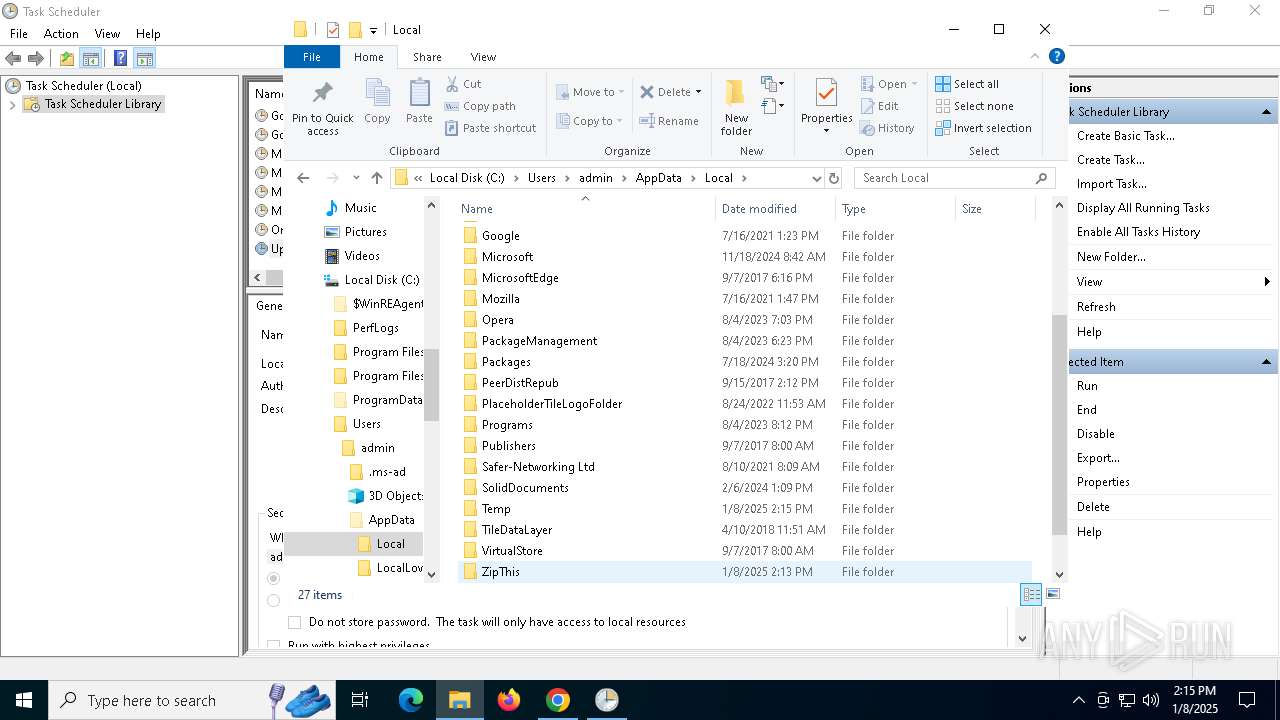
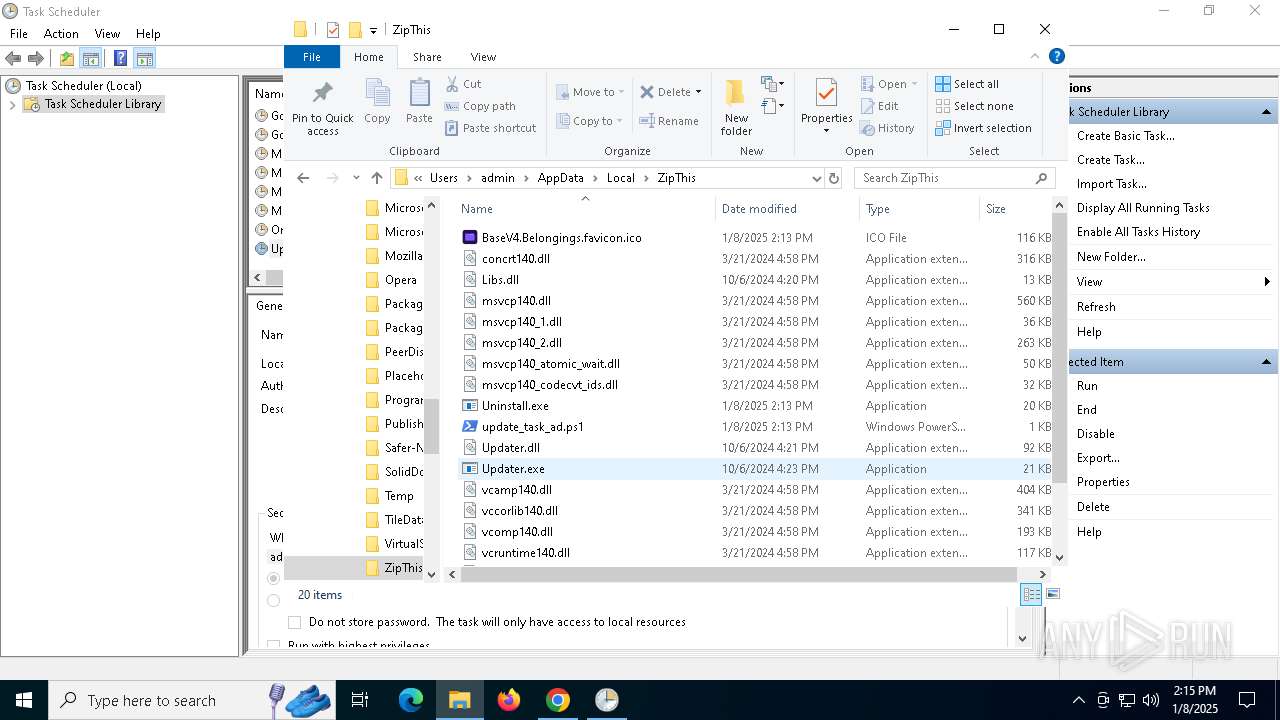
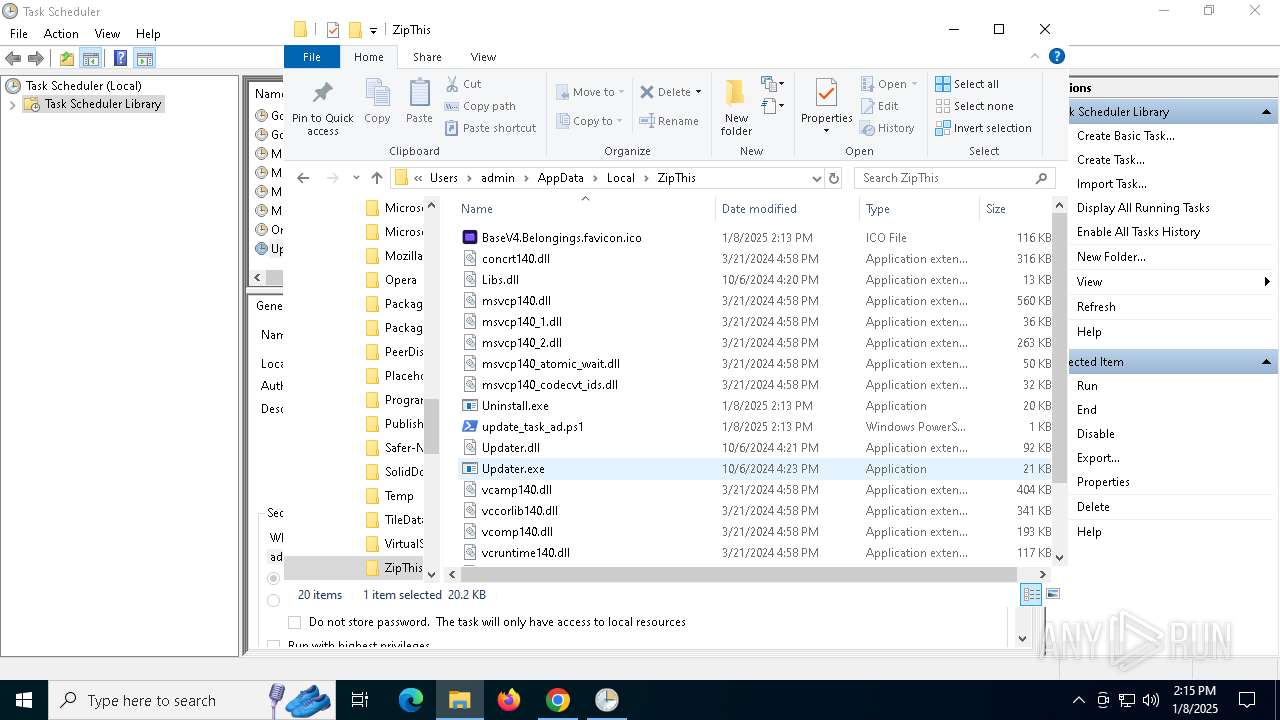
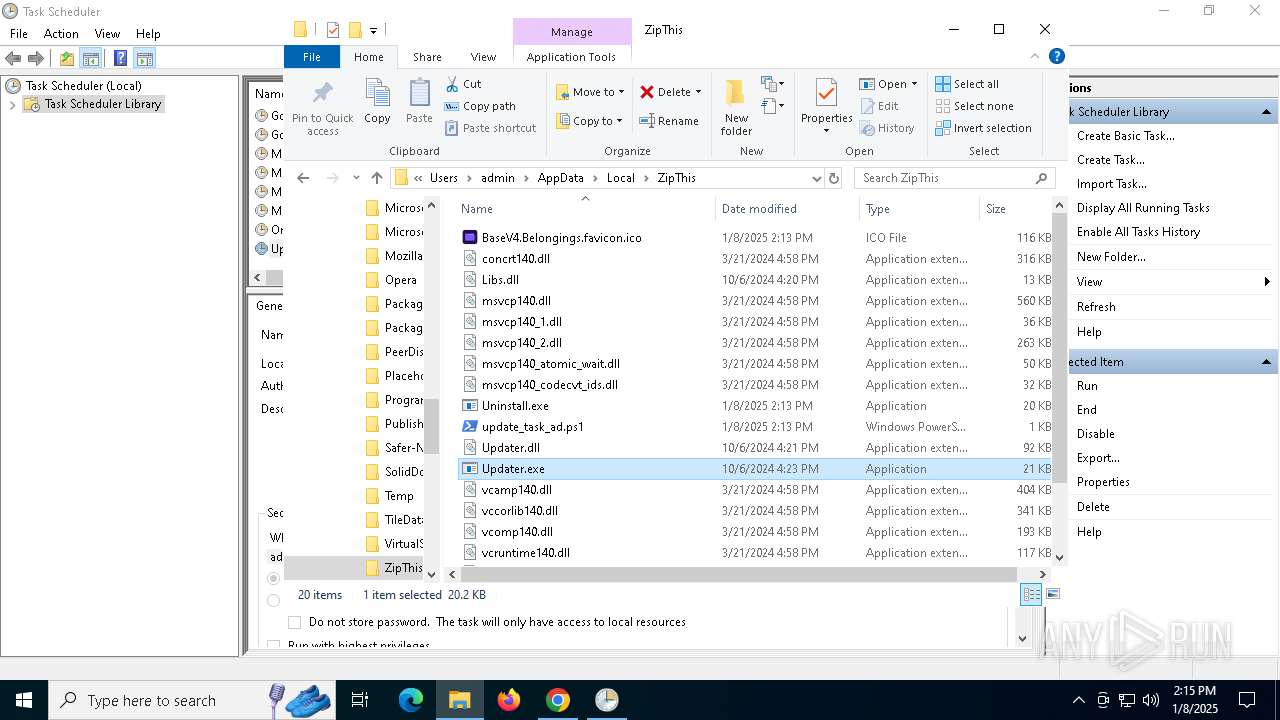
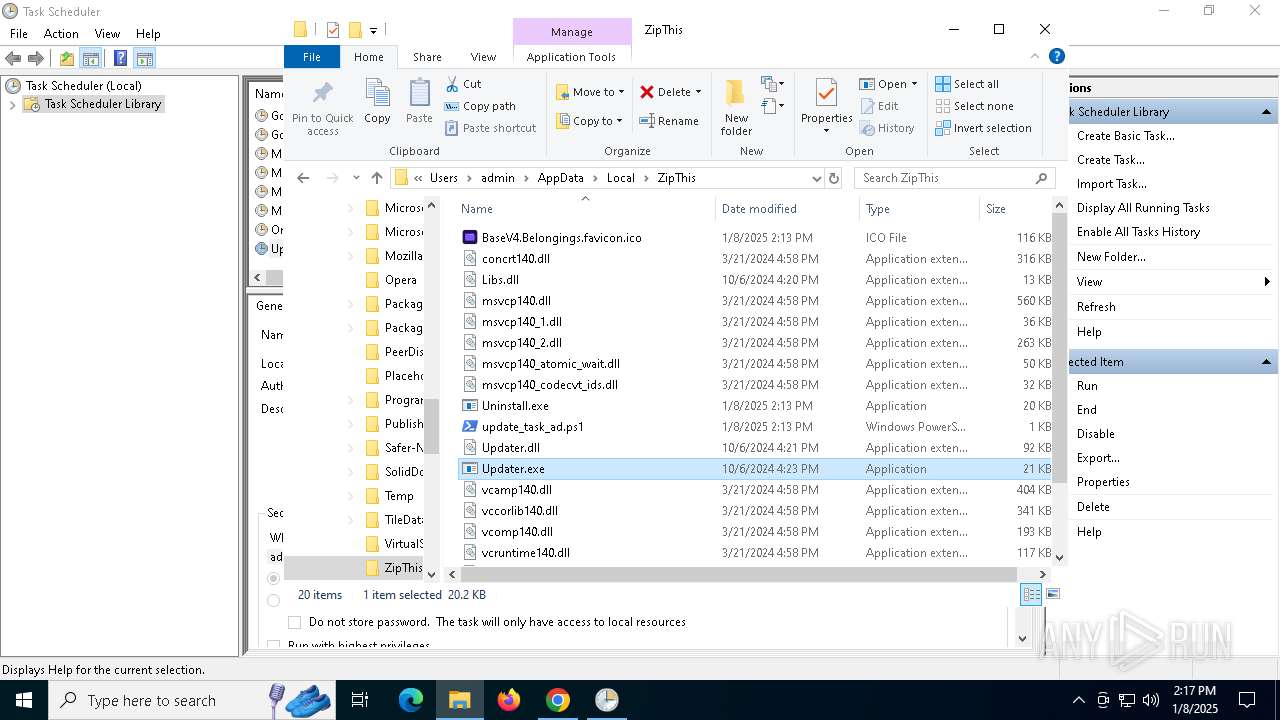
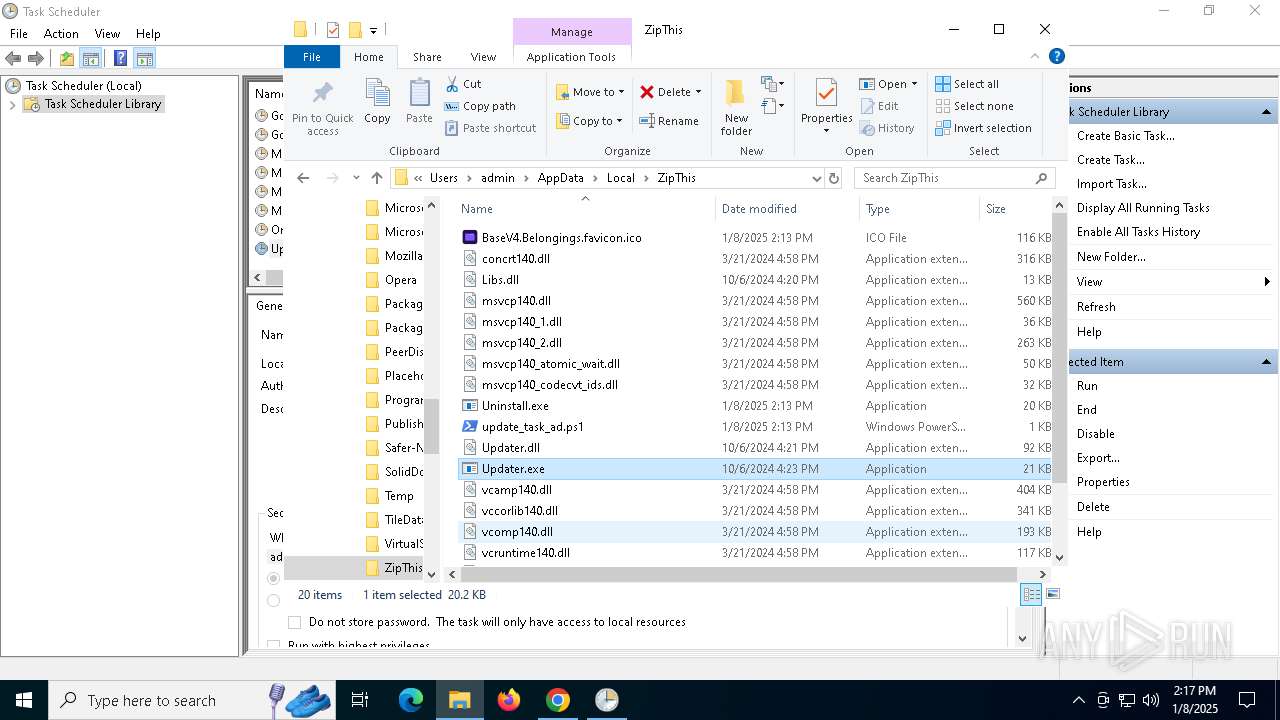
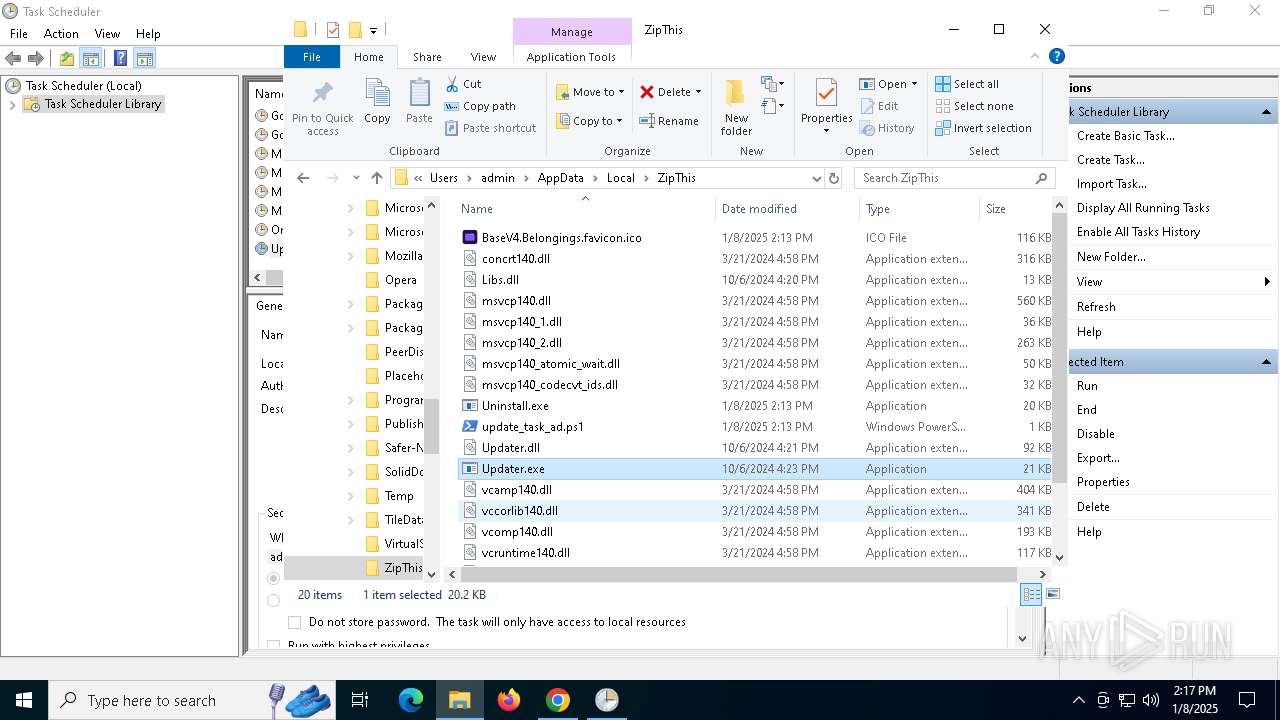
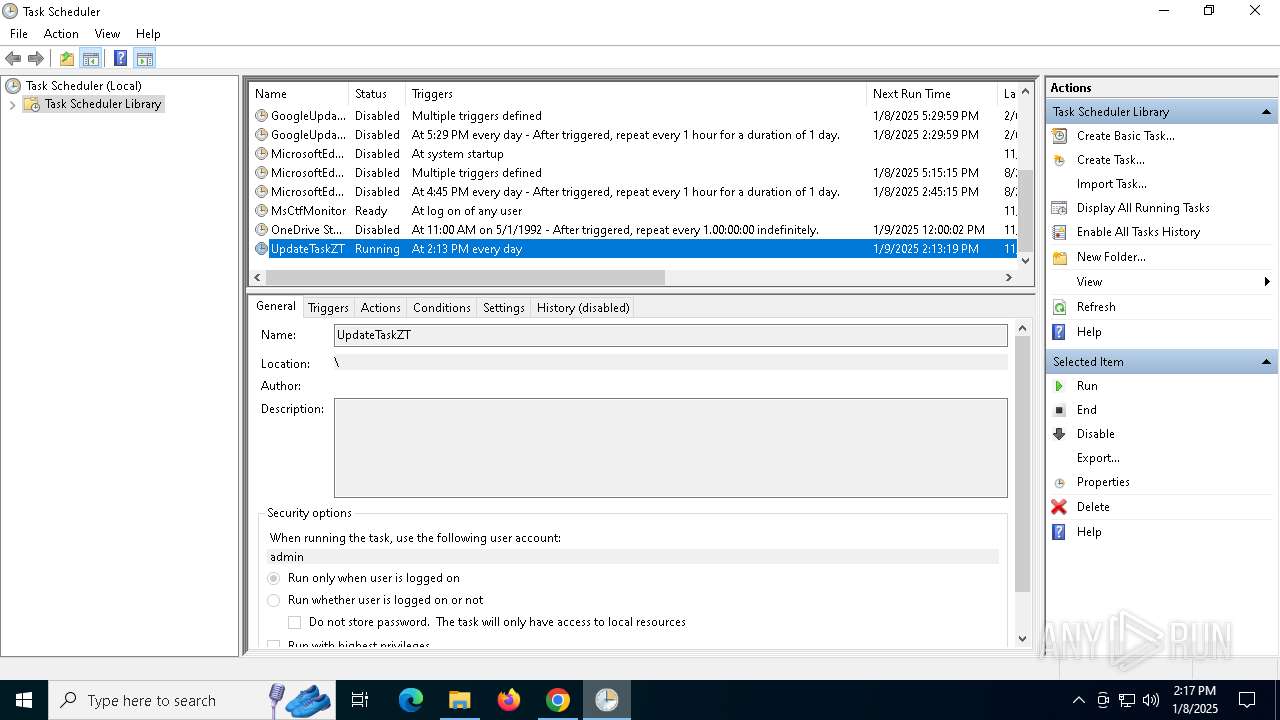
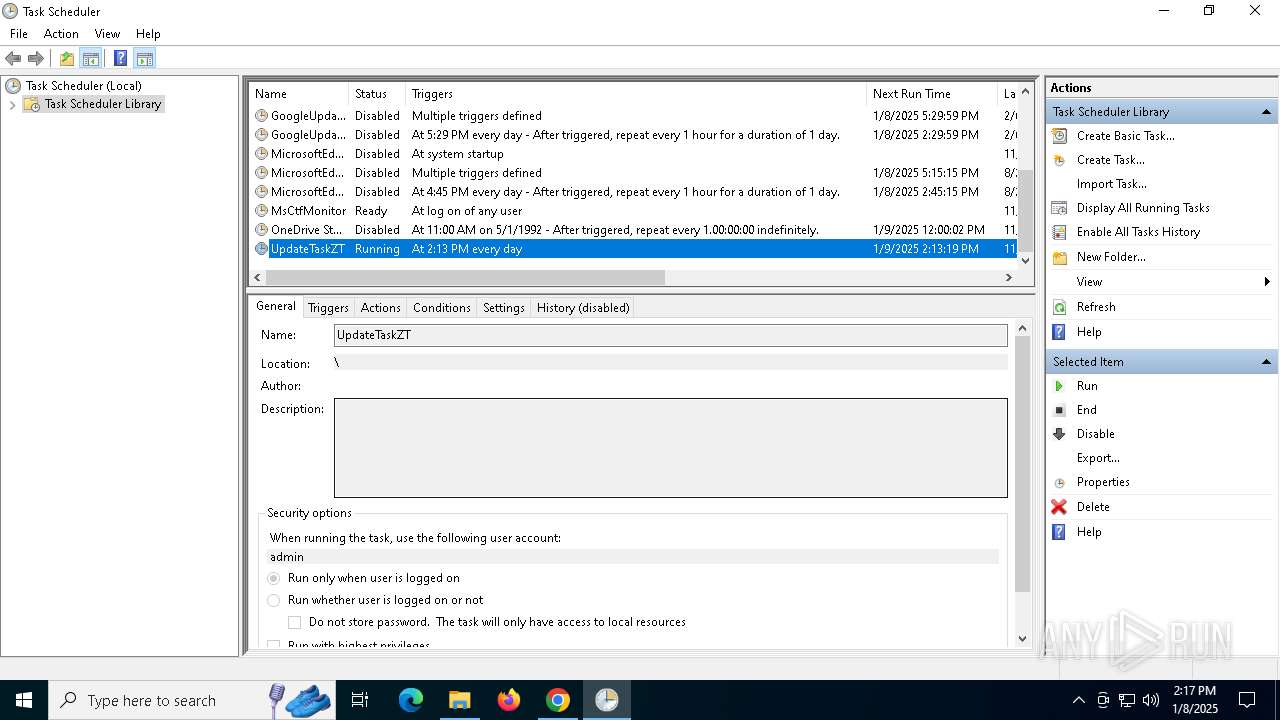
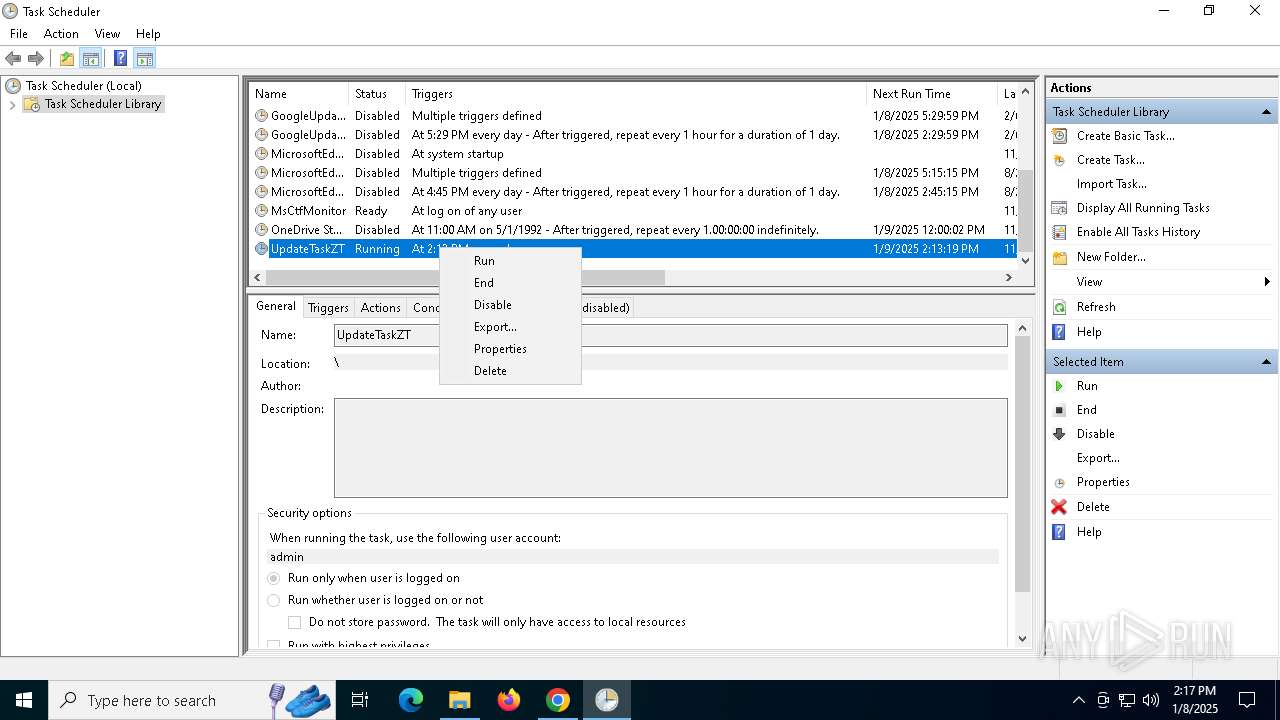
The process executes via Task Scheduler
- Updater.exe (PID: 7112)
- Updater.exe (PID: 5980)
- Updater.exe (PID: 5400)
INFO
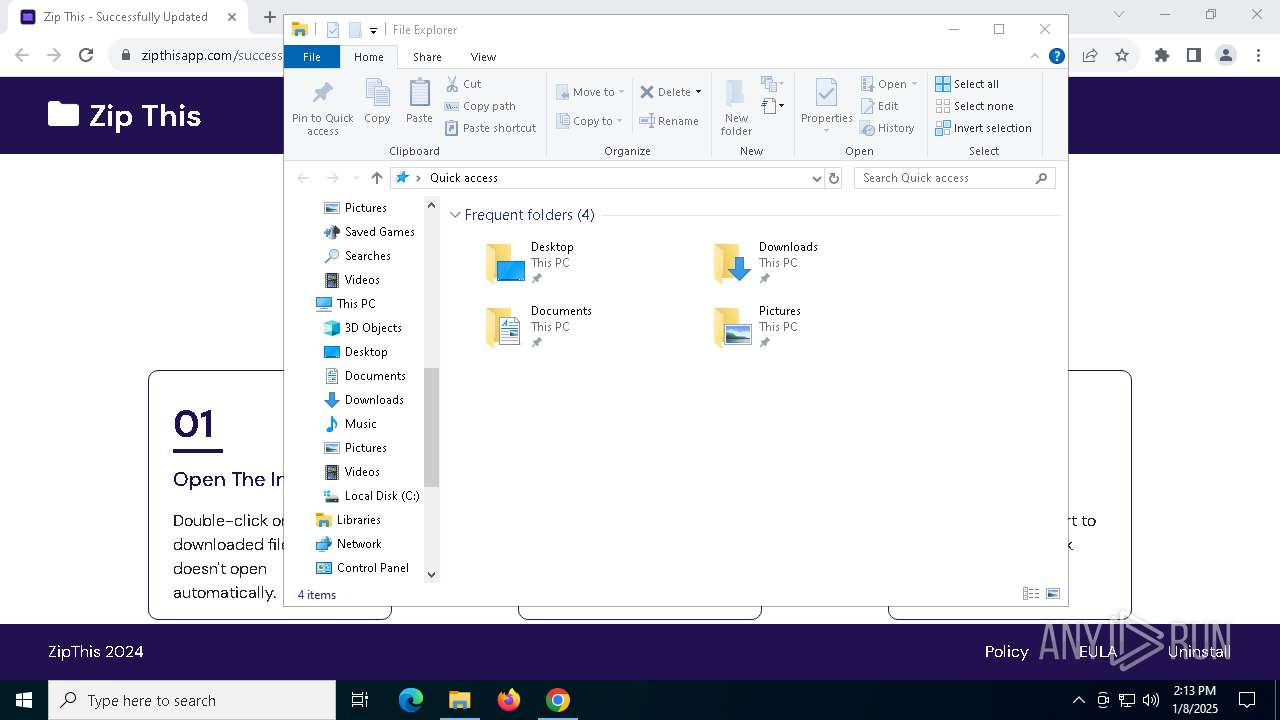
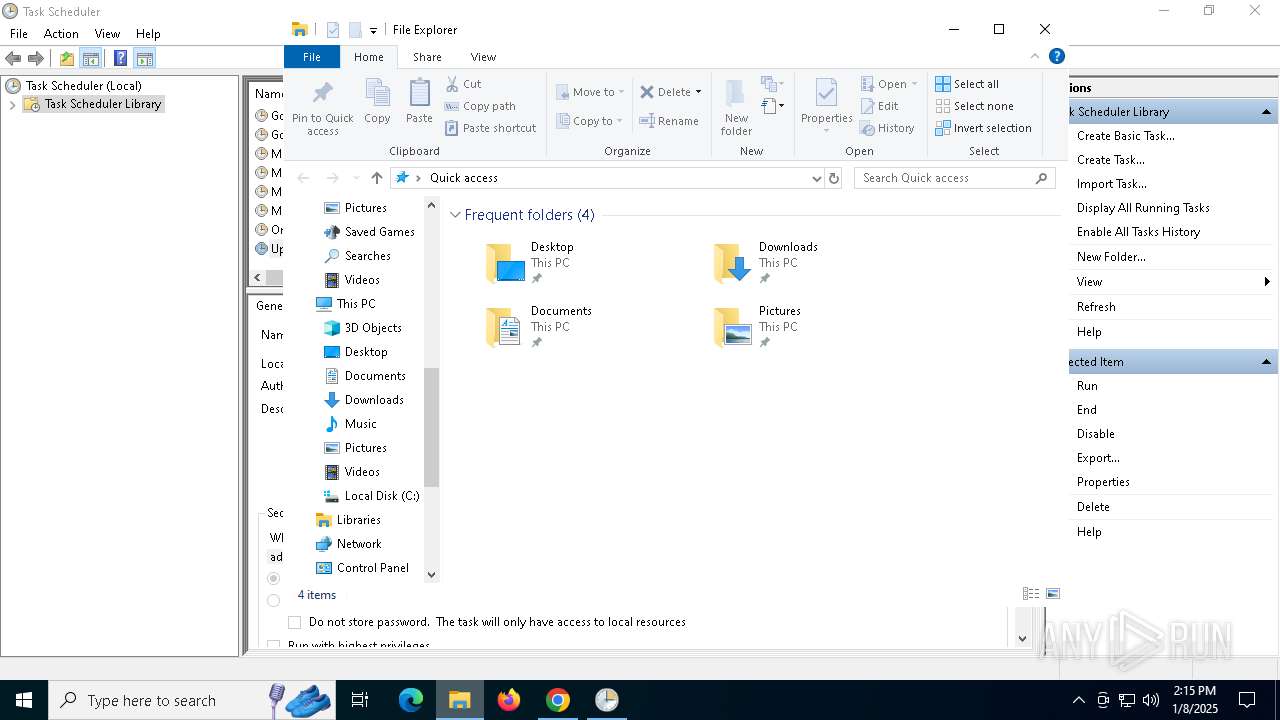
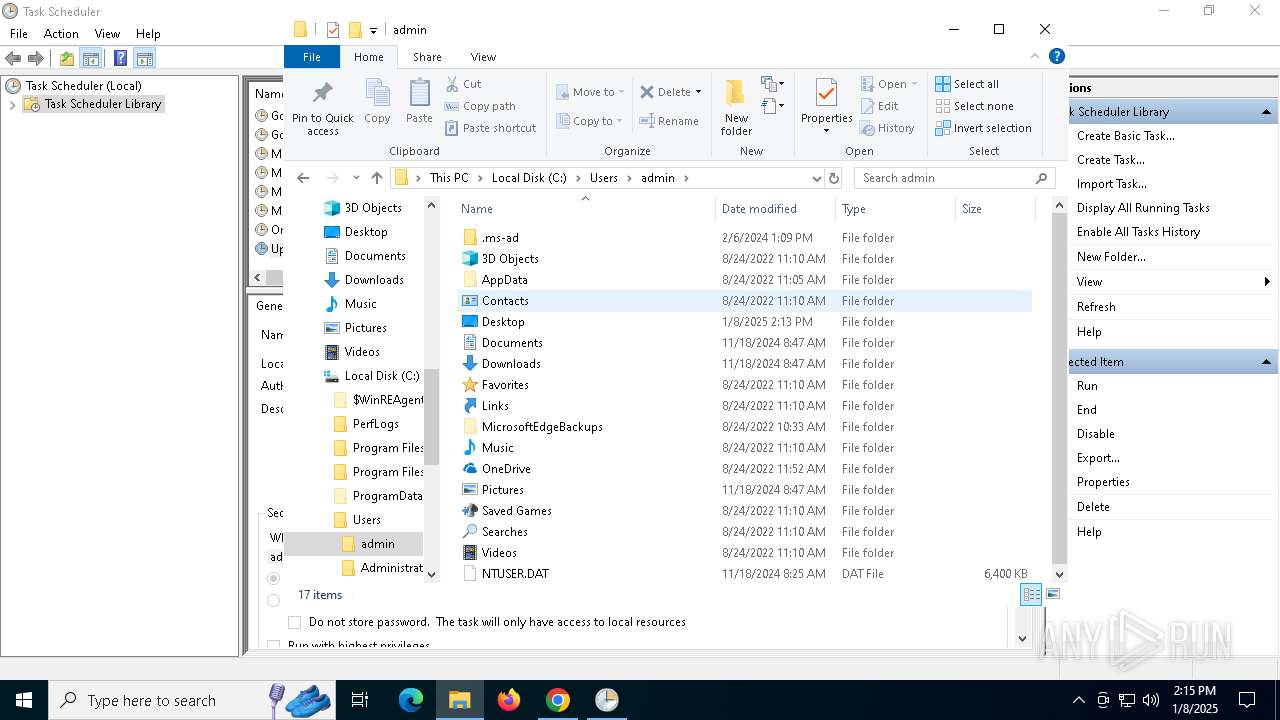
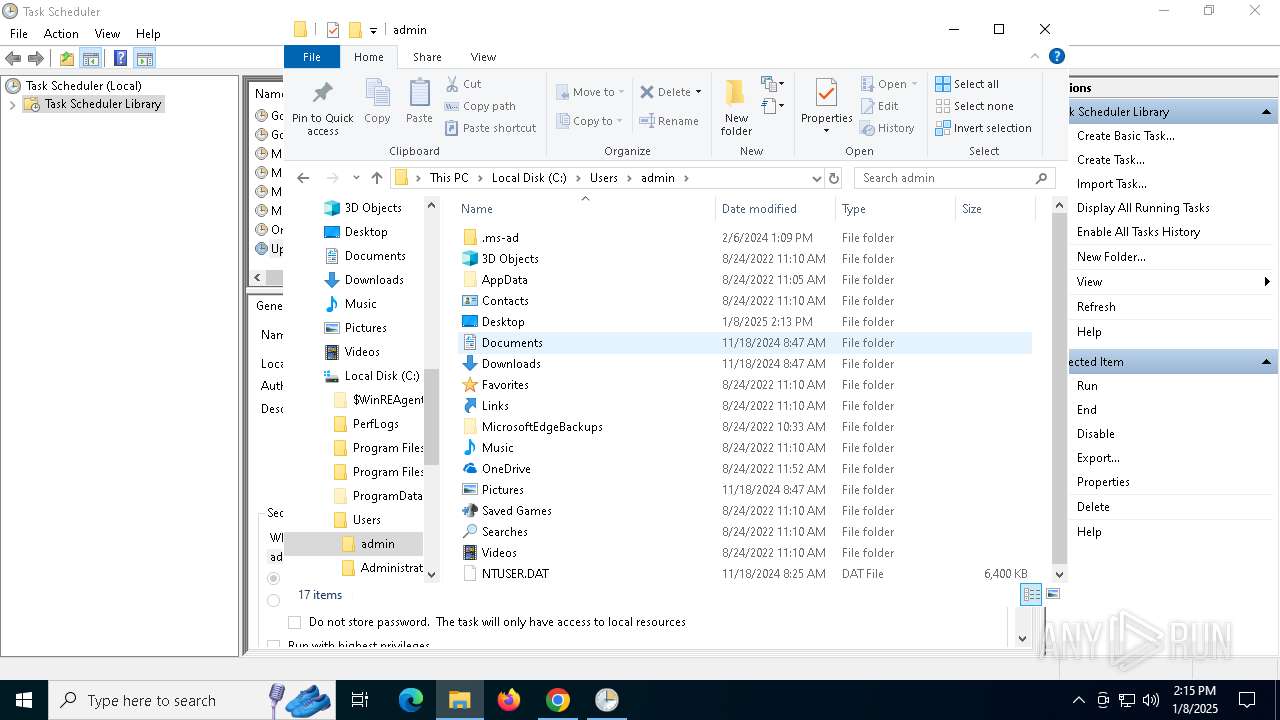
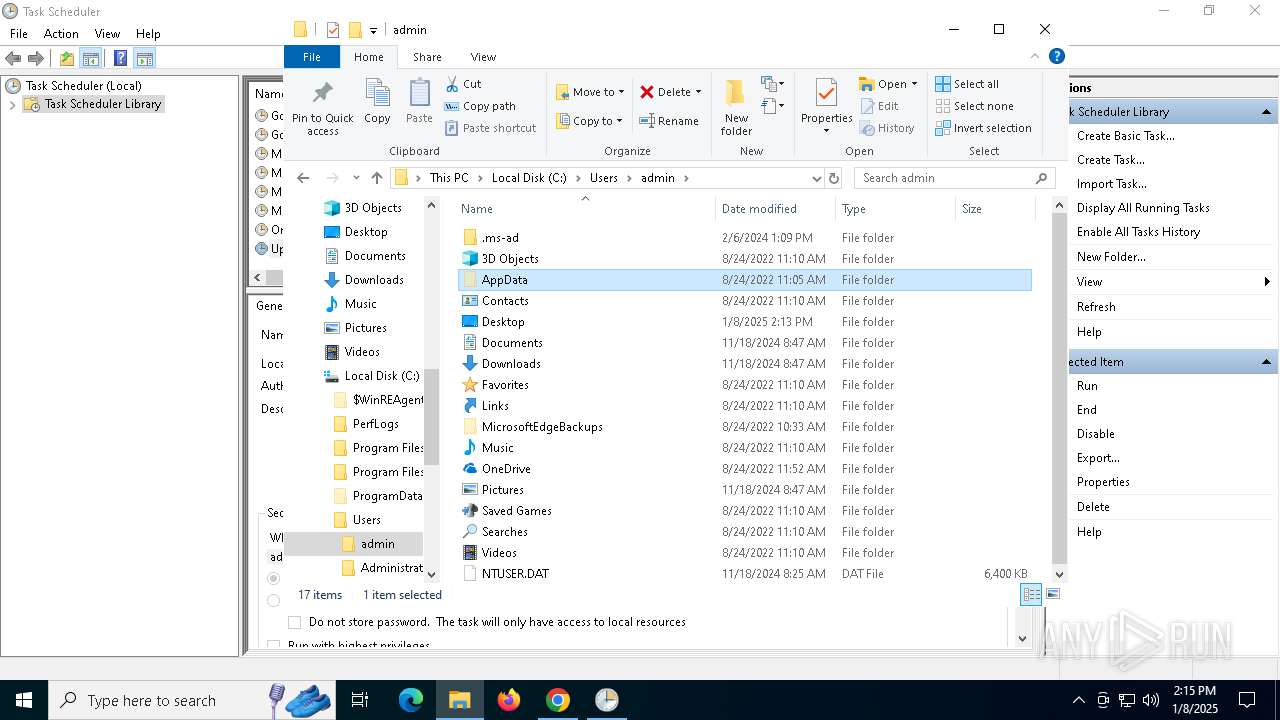
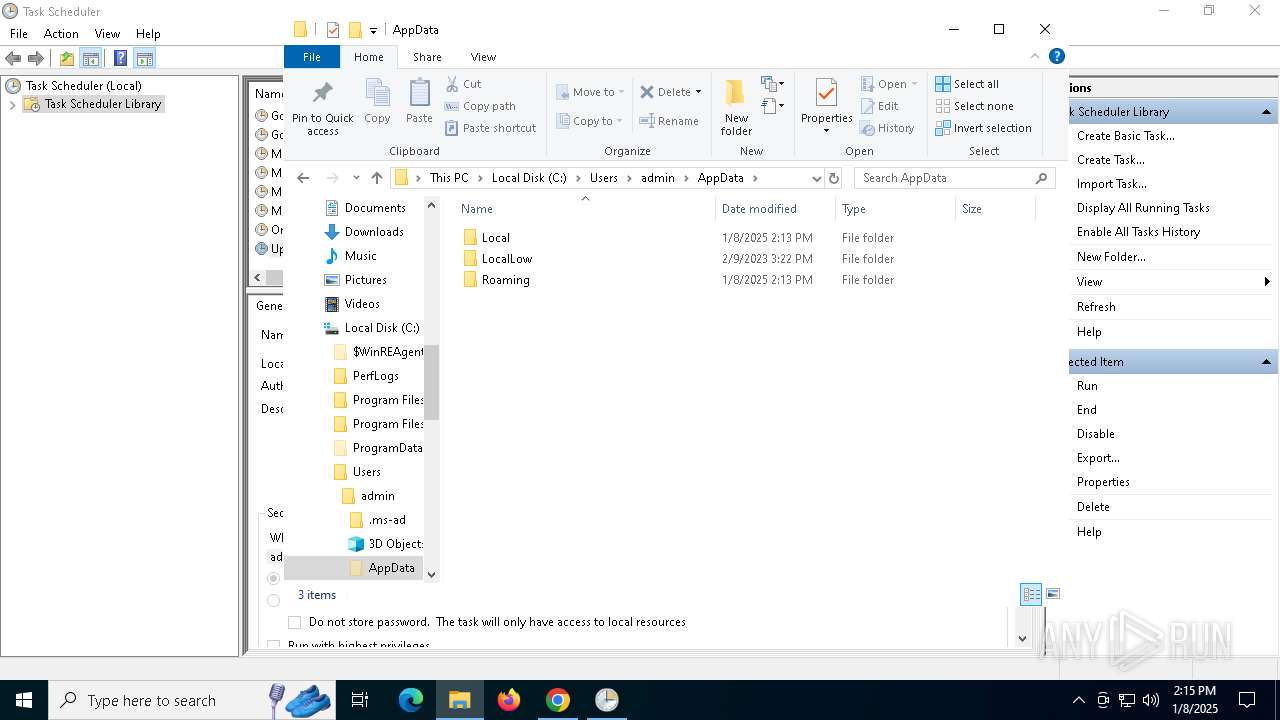
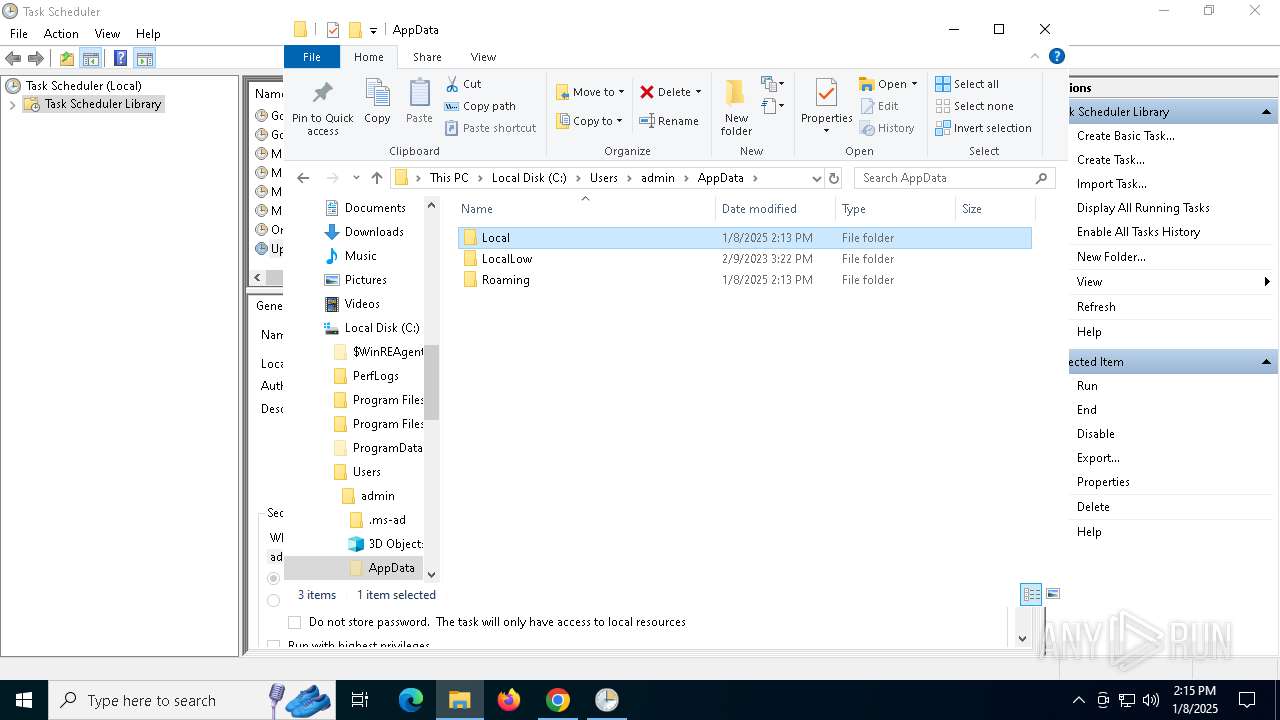
Creates files or folders in the user directory
- ZipThis.exe (PID: 6924)
Reads the computer name
- ZipThis.exe (PID: 6924)
Reads the machine GUID from the registry
- ZipThis.exe (PID: 6924)
- ZipThisApp.exe (PID: 5920)
- Updater.exe (PID: 7112)
- Updater.exe (PID: 5980)
- Updater.exe (PID: 6096)
Checks supported languages
- ZipThis.exe (PID: 6924)
- ZipThisApp.exe (PID: 5920)
The sample compiled with english language support
- ZipThis.exe (PID: 6924)
- chrome.exe (PID: 2216)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6444)
The process uses the downloaded file
- powershell.exe (PID: 6444)
- ZipThis.exe (PID: 6924)
- chrome.exe (PID: 5916)
- chrome.exe (PID: 540)
- chrome.exe (PID: 6028)
- chrome.exe (PID: 440)
Application launched itself
- chrome.exe (PID: 6068)
Disables trace logs
- ZipThisApp.exe (PID: 5920)
- Updater.exe (PID: 7112)
- Updater.exe (PID: 5980)
- Updater.exe (PID: 6096)
Reads the software policy settings
- ZipThisApp.exe (PID: 5920)
- Updater.exe (PID: 7112)
Manual execution by a user
- mmc.exe (PID: 6096)
- mmc.exe (PID: 7044)
- Updater.exe (PID: 6096)
Sends debugging messages
- mmc.exe (PID: 7044)
Reads Environment values
- Updater.exe (PID: 7112)
- Updater.exe (PID: 6096)
Executable content was dropped or overwritten
- chrome.exe (PID: 2216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2071:09:11 02:59:51+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 2688000 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.1.28.102 |
| ProductVersionNumber: | 10.1.28.102 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | ZipThis |
| FileVersion: | 10.1.28.102 |
| InternalName: | ZipThis.exe |
| LegalCopyright: | Copyright © 2015-2023 Lightner Tok All rights reserved |
| LegalTrademarks: | - |
| OriginalFileName: | ZipThis.exe |
| ProductName: | ZipThis |
| ProductVersion: | 10.1.28.102 |
| AssemblyVersion: | 10.1.28.102 |
Total processes
178
Monitored processes
46
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4552 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5420 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5464 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5992 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3648 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3580 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ff82221dc40,0x7ff82221dc4c,0x7ff82221dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5392 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5376 --field-trial-handle=1940,i,2369229558590659970,15095263939339364792,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4160 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 012
Read events
30 926
Write events
79
Delete events
7
Modification events
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6924) ZipThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZipThis_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
33
Suspicious files
276
Text files
46
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
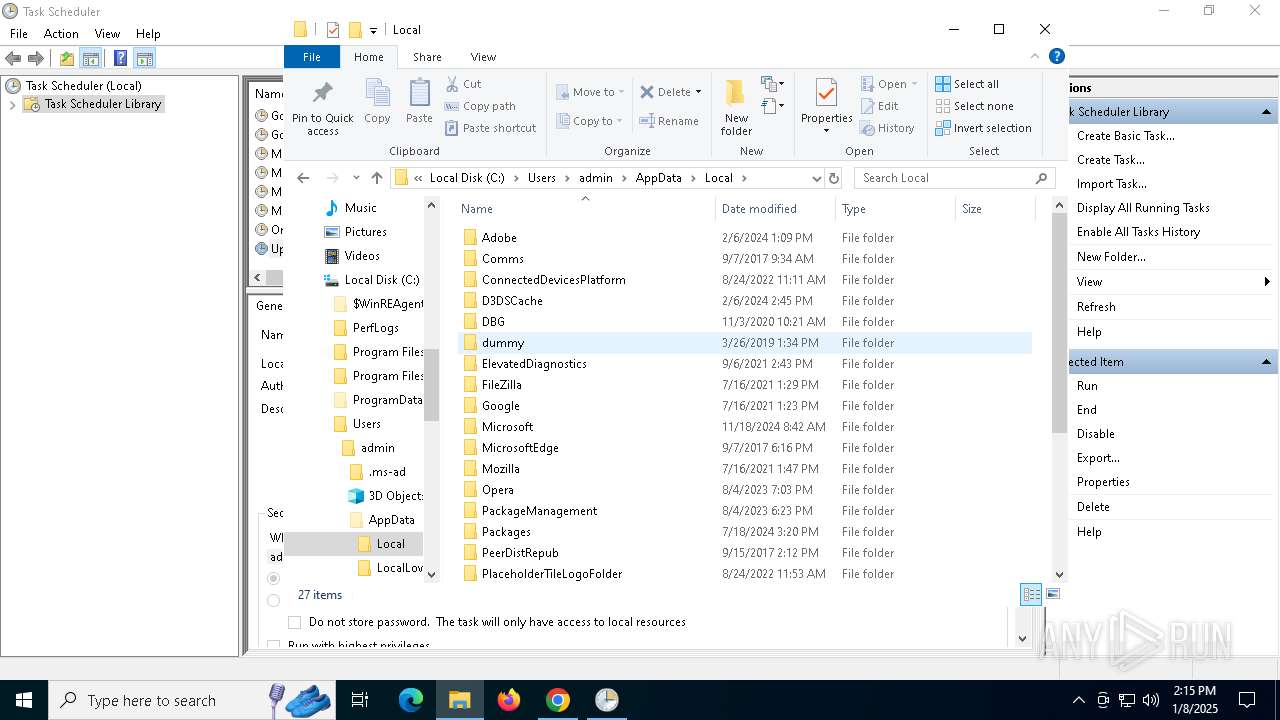
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Roaming\SMCR\userId.txt | text | |
MD5:B772C4E4DD4AF0FB568AE45E3B33A8FA | SHA256:38190E902BEEE2BB1C589CEF4F5B8933B9D3FE8F5D4E307FDA345621CFB6B1E8 | |||
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\zipthisUserId.txt | text | |
MD5:B772C4E4DD4AF0FB568AE45E3B33A8FA | SHA256:38190E902BEEE2BB1C589CEF4F5B8933B9D3FE8F5D4E307FDA345621CFB6B1E8 | |||
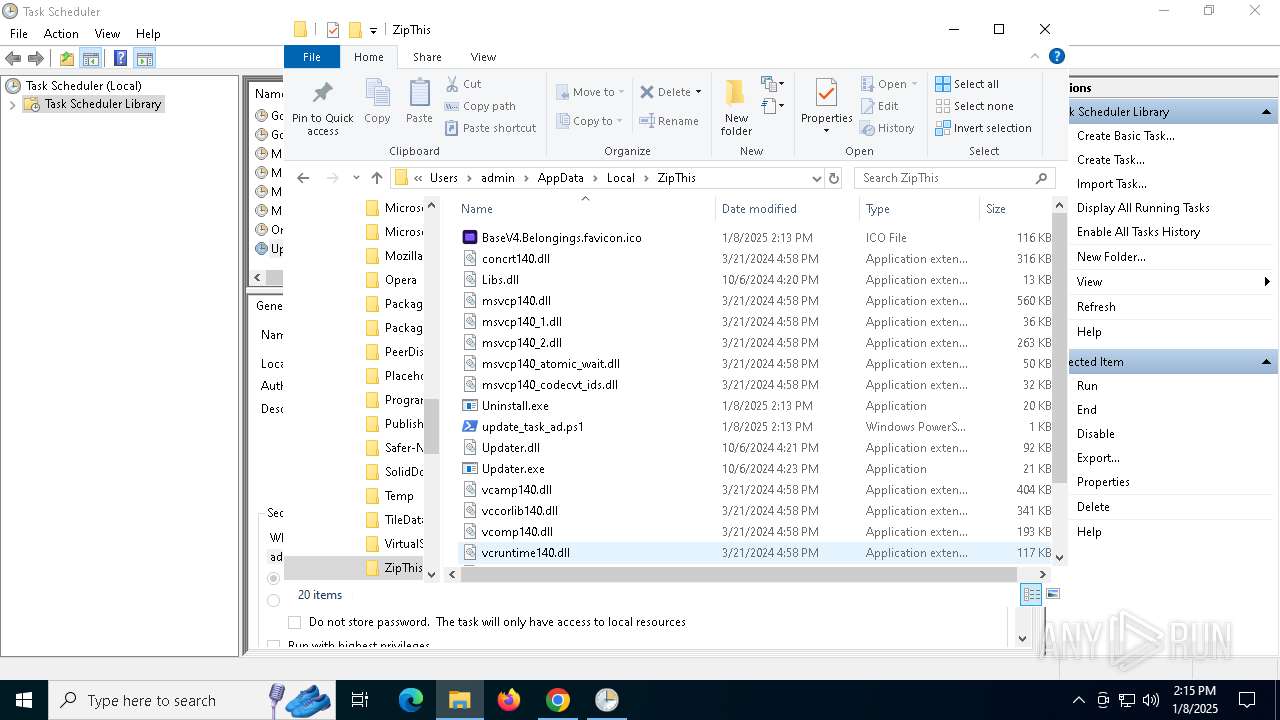
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\concrt140.dll | executable | |
MD5:9485D003573E0EAF7952AB23CC82EF7B | SHA256:5E0E8EAC57B86E2DE7CA7D6E8D34DDDEA602CE3660208FB53947A027635D59A1 | |||
| 6444 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_voi3ajwn.ofk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\Libs.dll | executable | |
MD5:8F22D1409CF9222DD8B05EB8E0456050 | SHA256:D658EA24EE115D2071DEDFF84383657BB540DC1037E6D0FEE689D2751204D4D7 | |||
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\update_task_ad.ps1 | text | |
MD5:0D4C7C2411E1BA411E24DE176494CA90 | SHA256:DC4685144E93384E88D1FC6E6DD66F6C4E703ED9173A98819F2C8BCB28D983FC | |||
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\msvcp140_2.dll | executable | |
MD5:AA0148E20D34C10E01A4A9E1BAB1D058 | SHA256:583AD842BCF2F77AF57D07B8F00ECA77BB2DF763DF96BB9C50F7E52031B54E42 | |||
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\msvcp140_1.dll | executable | |
MD5:7B0A25EEE764D8747F02CB3ED980F07A | SHA256:1274292F4CC655F295272B37E08A9683B8BB8C419B61EA2E1F43EB4D22F02F90 | |||
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\msvcp140_codecvt_ids.dll | executable | |
MD5:165308EE66D0B8F11CA20F3BCD410EA9 | SHA256:08DF3AB1B59D1F7D63F0811838E4FCCC107087FCBC469D94975C0E44477058E7 | |||
| 6924 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\vccorlib140.dll | executable | |
MD5:E3E6AA23DF3C78B29B0EE90E2712FC7E | SHA256:233E79C5AB80A2902B79C8B41E741DC06CD4A9FF8BCA99A025FE8077A35BE125 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
96
DNS requests
97
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.131:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.131:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1228 | svchost.exe | GET | 200 | 2.16.164.131:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1228 | svchost.exe | GET | 200 | 23.209.210.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.209.210.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2776 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4468 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4468 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6656 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4468 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.131:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1228 | svchost.exe | 2.16.164.131:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.131:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.209.210.103:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
1228 | svchost.exe | 23.209.210.103:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
— | — | 23.209.210.103:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
apb.thisilient.com |
| unknown |
sts.thisilient.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6004 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|