| File name: | new.xls |
| Full analysis: | https://app.any.run/tasks/60c982f8-cb33-46bd-a30c-7bfd605bdad1 |
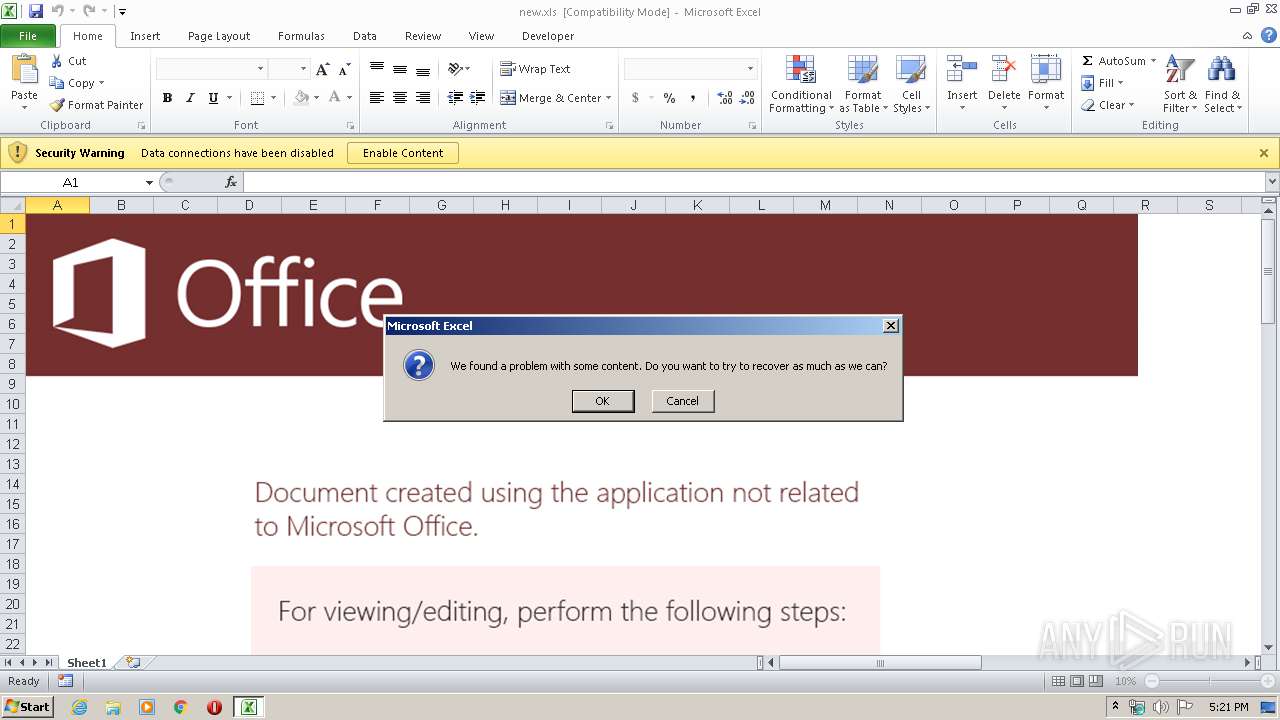
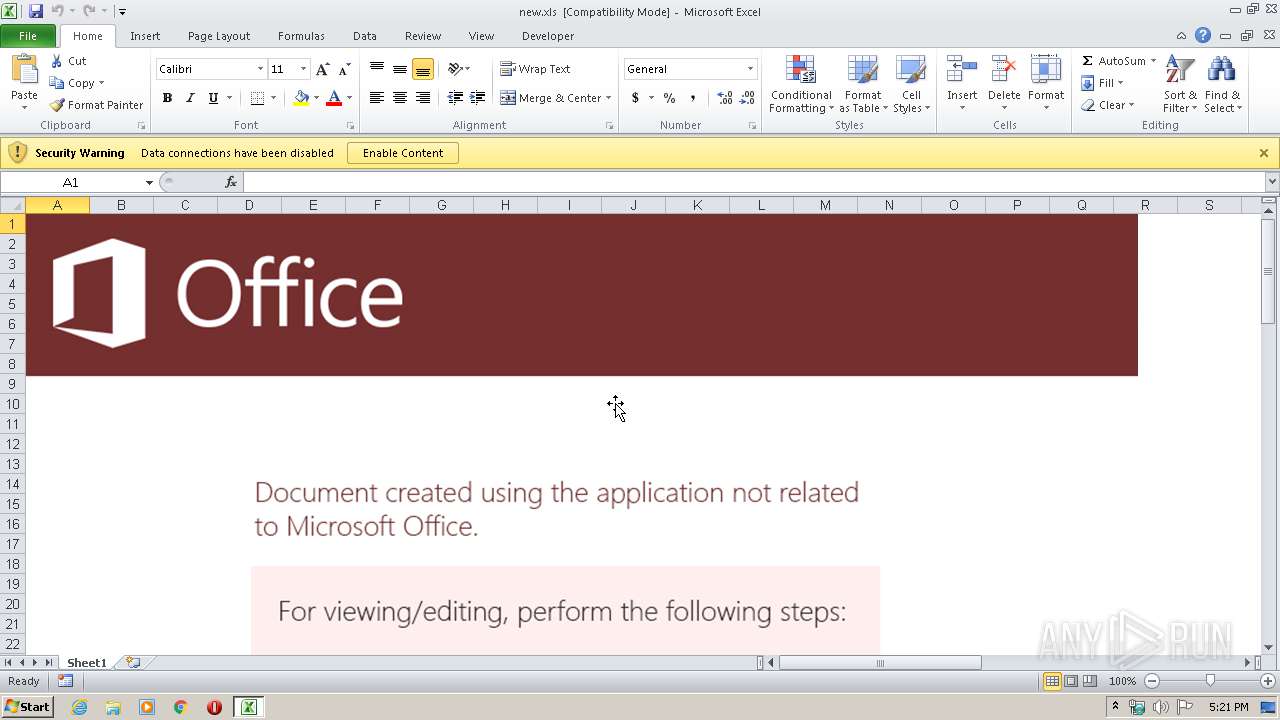
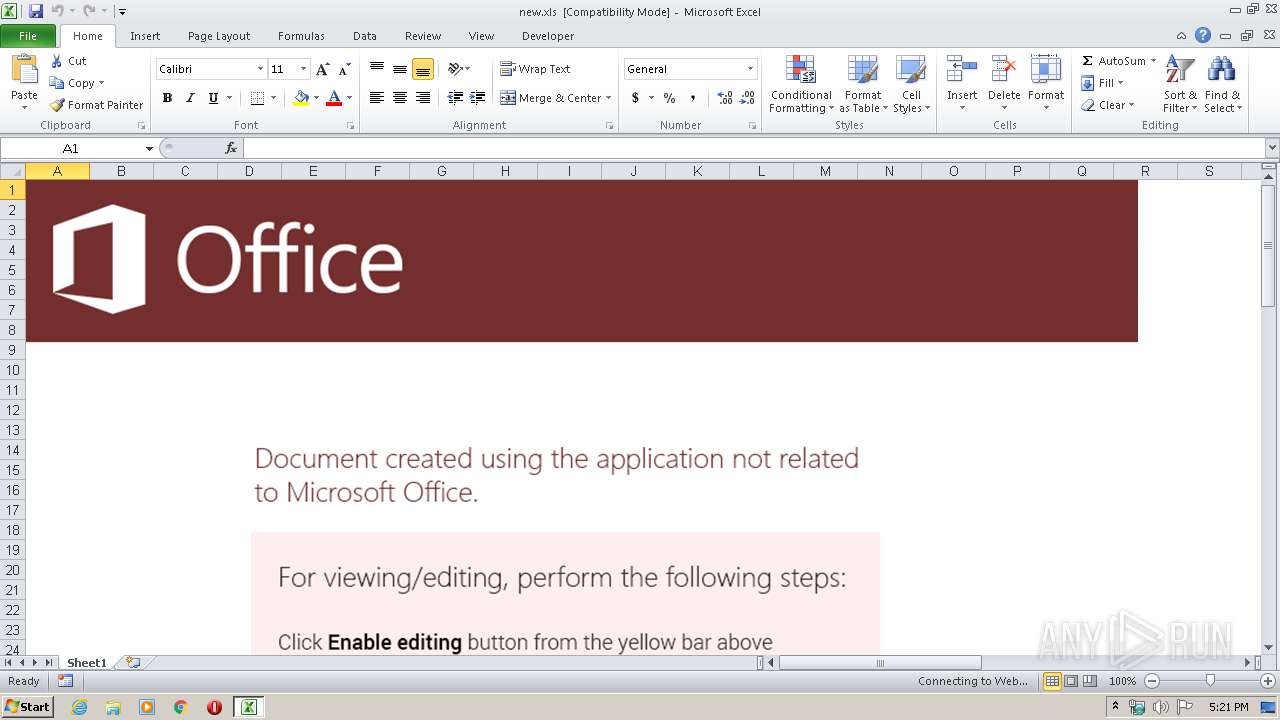
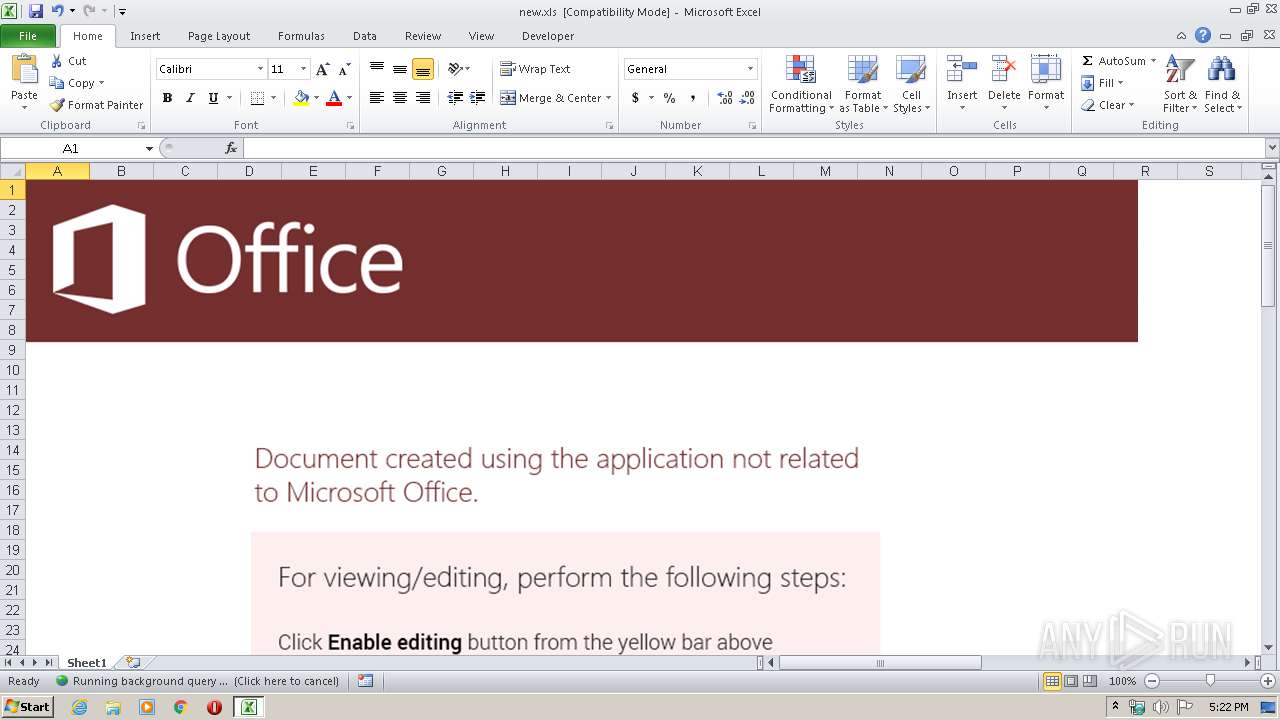
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 21, 2020, 17:21:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Name of Creating Application: Microsoft Excel, Create Time/Date: Fri Feb 14 06:29:18 2020, Last Saved Time/Date: Mon Feb 17 07:49:48 2020, Security: 0 |
| MD5: | 461246F7DD369D9E3B2A25DBEEED2508 |
| SHA1: | E9A1AADED1FA8C0D47B336976FB7423A38F31166 |
| SHA256: | BF24C5389F398A1463AB066175D5A93E3110BF3582E4249ECC224E3E8F39D500 |
| SSDEEP: | 3072:z0k3hbdlylKsgqopeJBWhZFGkE+cL2NdHzyF0Vi4m+Oi9l1isYgmNWl1oH2HU8:Ak3hbdlylKsgqopeJBWhZFVE+W2Nd+Fy |
MALICIOUS
No malicious indicators.SUSPICIOUS
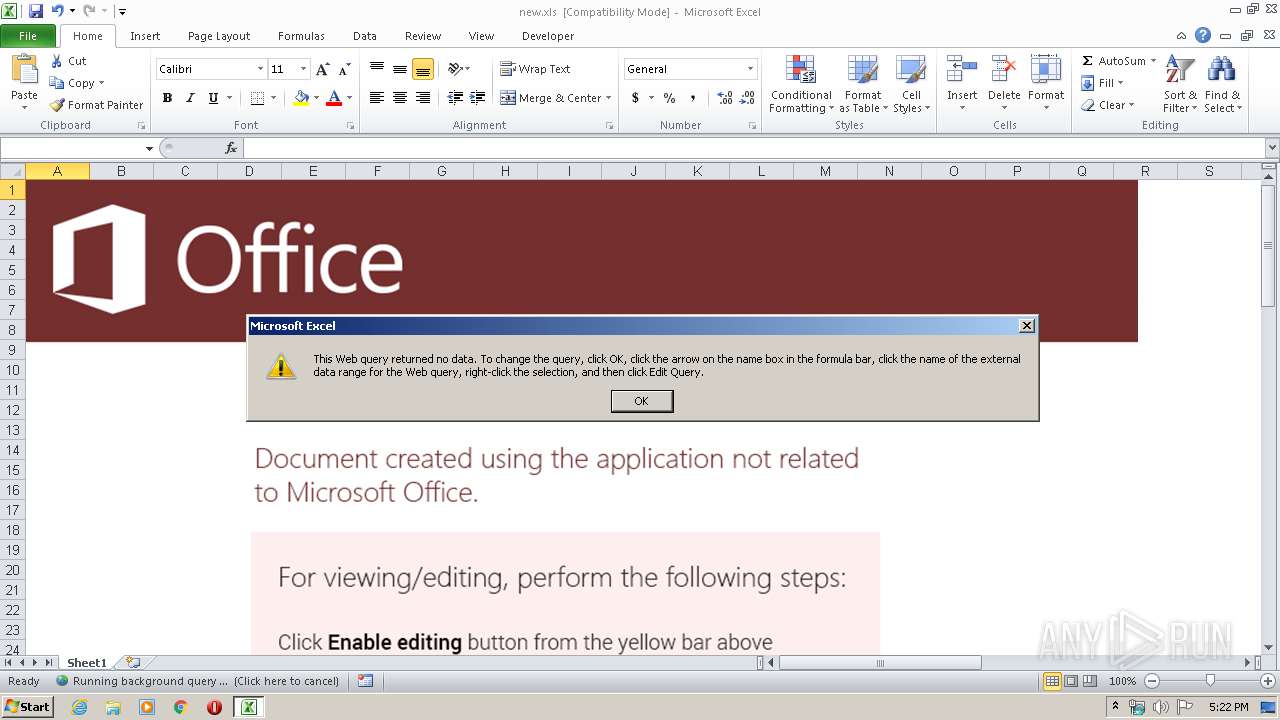
Unusual connect from Microsoft Office
- EXCEL.EXE (PID: 2952)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2952)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 2952)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2020:02:14 06:29:18 |
| ModifyDate: | 2020:02:17 07:49:48 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
35
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
669
Read events
595
Write events
63
Delete events
11
Modification events
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | !41 |
Value: 21343100880B0000010000000000000000000000 | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2952) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
34
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C01.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Cab9081.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Tar9082.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\{5CDD78E9-82C9-40CD-9E74-AFC2F8C0913C} | — | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\{35E512DE-6EAA-4DA1-A2FF-BBF75DE88823} | — | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\0N7XOESD.txt | — | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-{79F4ECF9-2678-4400-B219-154BBFBEEA76}.FSD | binary | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_375B7F179C25C4C237293A604A6DE85C | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
8
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | EXCEL.EXE | GET | 200 | 216.58.205.227:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 950 b | whitelisted |
2952 | EXCEL.EXE | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2952 | EXCEL.EXE | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDu3mVgzTXArwIAAAAAWXG3 | US | der | 472 b | whitelisted |
2952 | EXCEL.EXE | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDvdxhhS3x8DggAAAAALnGY | US | der | 472 b | whitelisted |
2952 | EXCEL.EXE | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPUFGc9jG53plGcZxTtYusmrA%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | EXCEL.EXE | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
2952 | EXCEL.EXE | 161.117.177.248:443 | merystol.xyz | — | SG | suspicious |
2952 | EXCEL.EXE | 216.58.205.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2952 | EXCEL.EXE | 172.217.23.110:443 | google.com | Google Inc. | US | whitelisted |
2952 | EXCEL.EXE | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
merystol.xyz |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
crl.pki.goog |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2952 | EXCEL.EXE | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |