| download: | download |
| Full analysis: | https://app.any.run/tasks/28146e03-d776-4d0d-90e5-9a1737f9415c |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 10:10:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
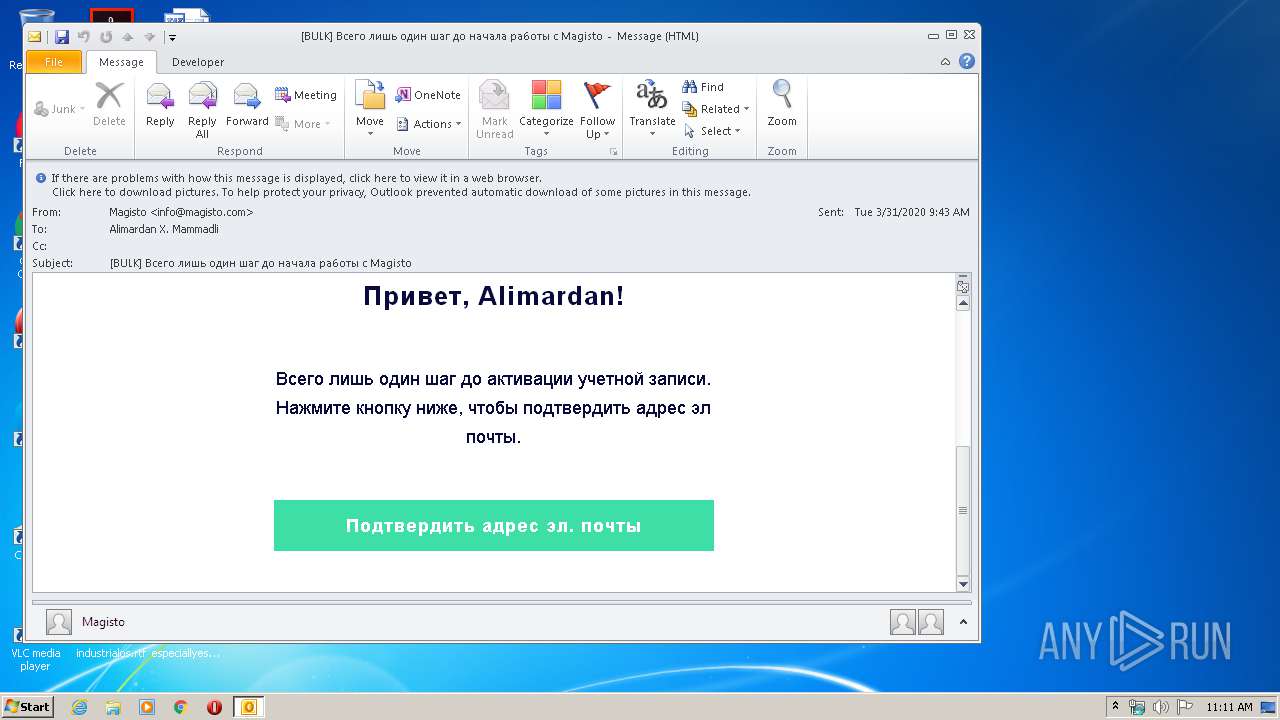
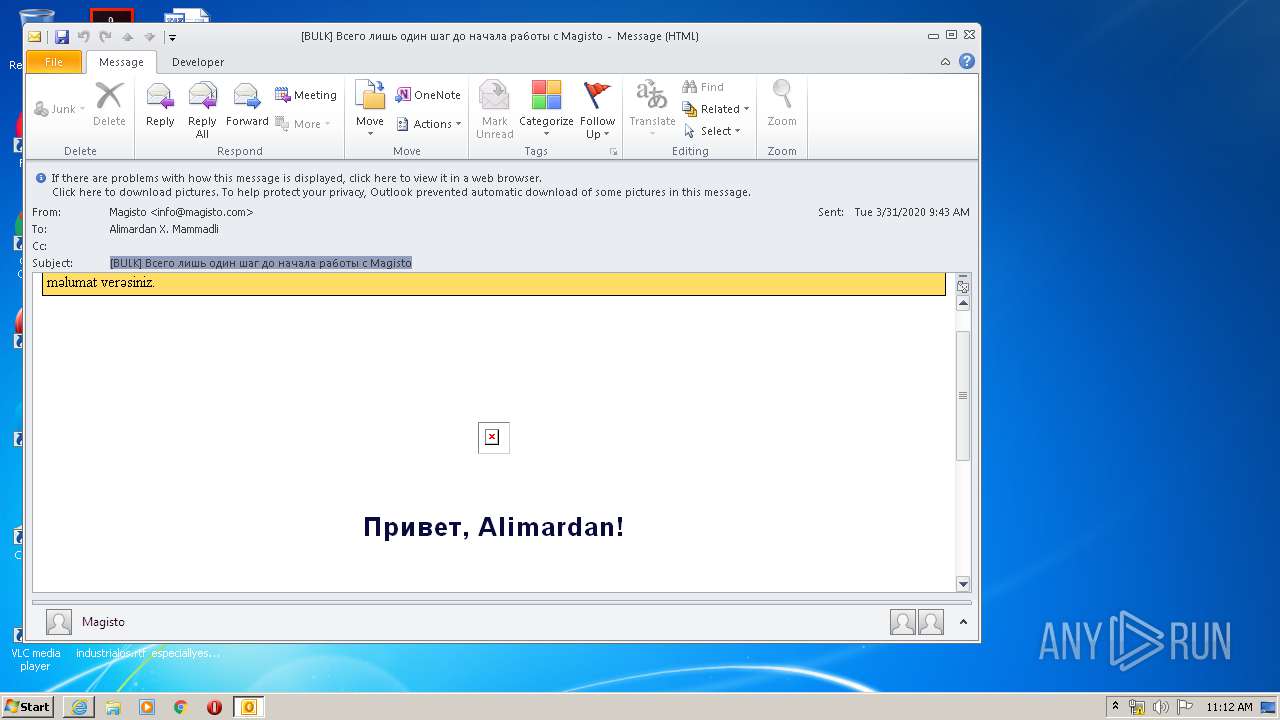
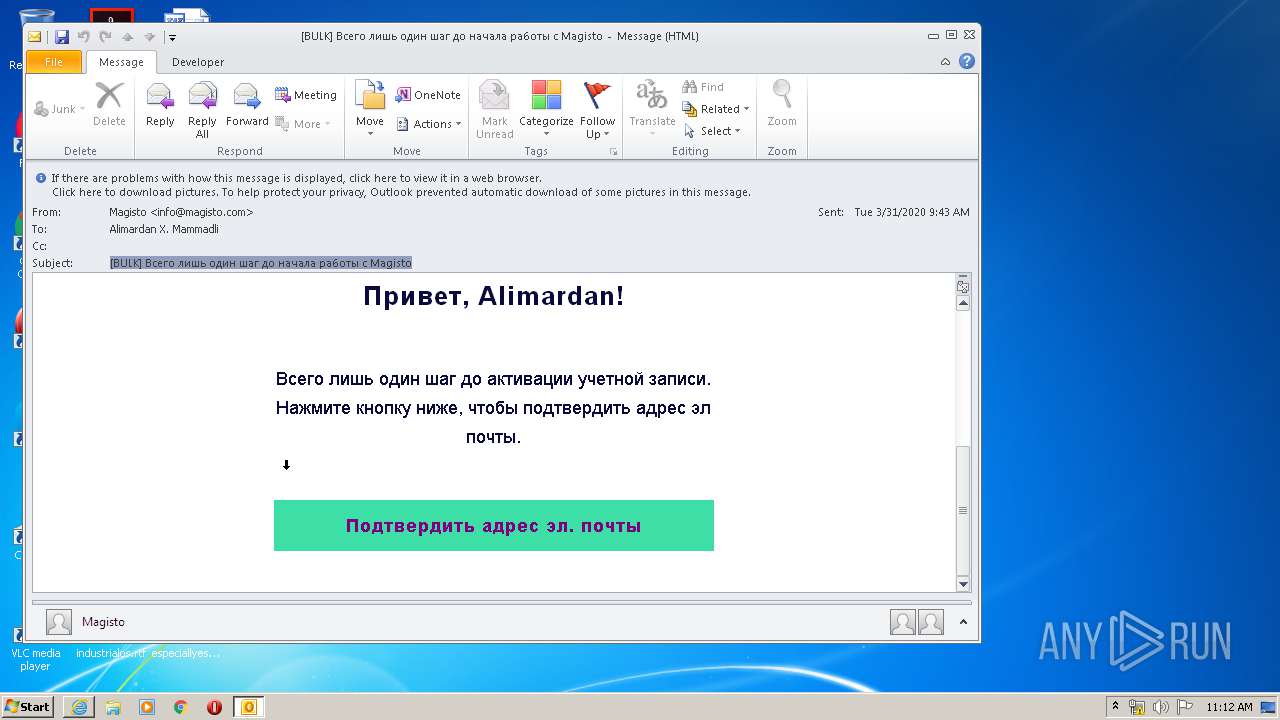
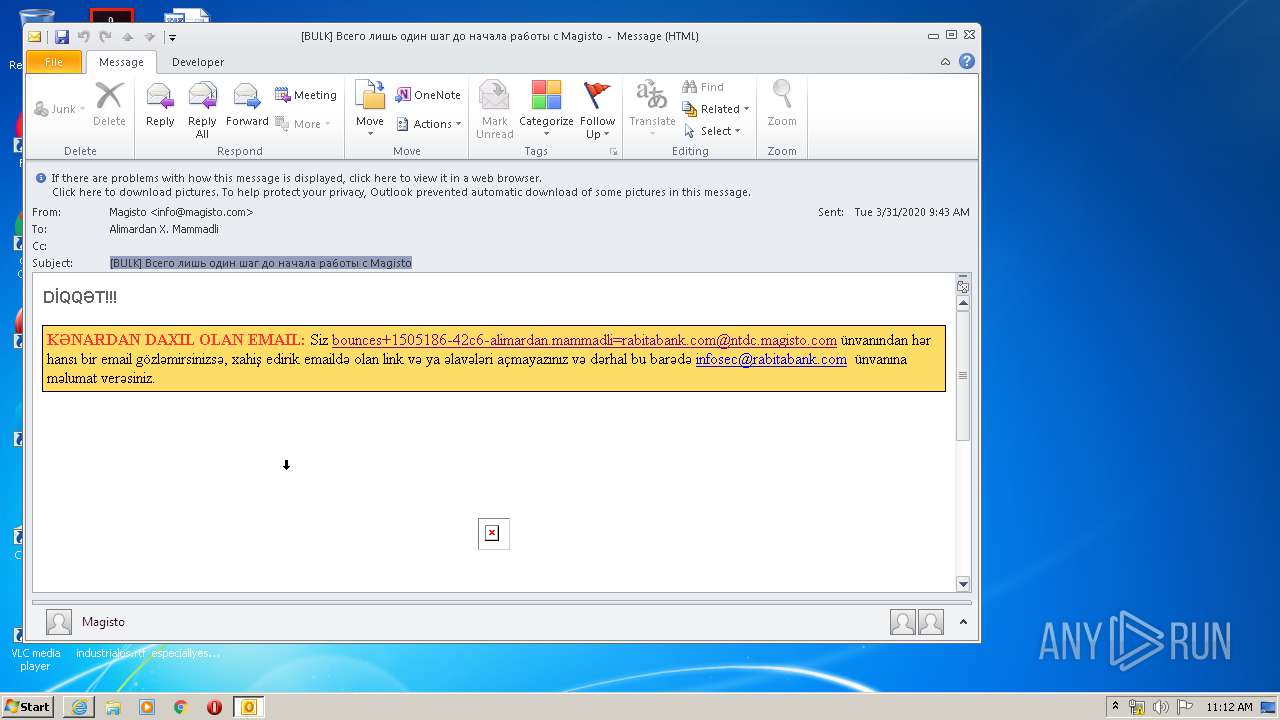
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 082A0C72831C765DA091DC89EAB6F7B7 |
| SHA1: | 80F2C8C72A0E7F7DE45434E45F3C46043263A616 |
| SHA256: | BF0A2569F7AB8CABB57D29380C70F4450039B27C8AA31FF767AC314B21F9DB62 |
| SSDEEP: | 768:44EKismA+Pf2JyUj1sbi9zA7OsKosKm0MuD3LrRP+miS5AZTf1aMQ7t1cG:bmAmfuj1x9Jw1xL1HindlQY |
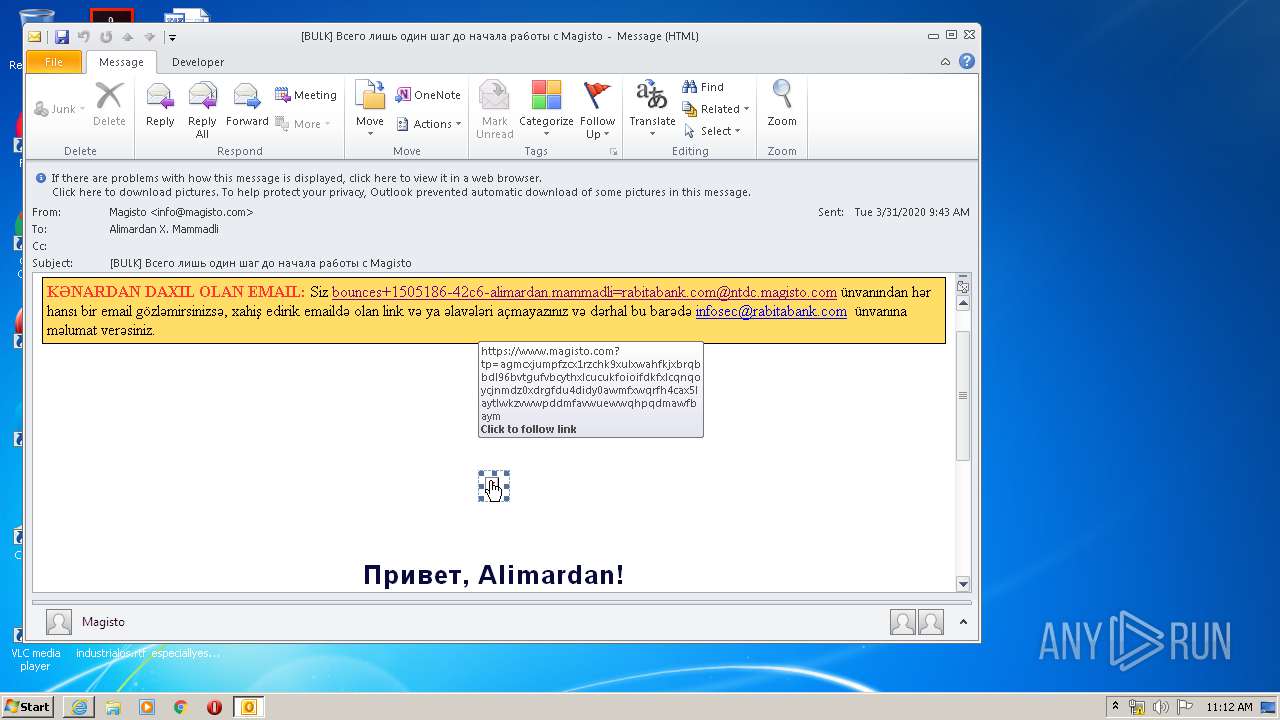
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3612)
SUSPICIOUS
Executed via COM
- OUTLOOK.EXE (PID: 2824)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3160)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3612)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3612)
Starts itself from another location
- OUTLOOK.EXE (PID: 3612)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3612)
- OUTLOOK.EXE (PID: 2824)
- OUTLOOK.EXE (PID: 2648)
Application launched itself
- iexplore.exe (PID: 3140)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3612)
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 816)
- iexplore.exe (PID: 1720)
- iexplore.exe (PID: 880)
Changes internet zones settings
- iexplore.exe (PID: 3140)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3160)
- iexplore.exe (PID: 816)
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 1720)
- iexplore.exe (PID: 880)
Reads internet explorer settings
- iexplore.exe (PID: 816)
- iexplore.exe (PID: 1720)
- iexplore.exe (PID: 880)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 816)
Reads settings of System Certificates
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 1720)
- iexplore.exe (PID: 880)
- iexplore.exe (PID: 816)
Changes settings of System certificates
- iexplore.exe (PID: 3140)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
45
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 816 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3140 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 880 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3140 CREDAT:3347732 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3140 CREDAT:3872026 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
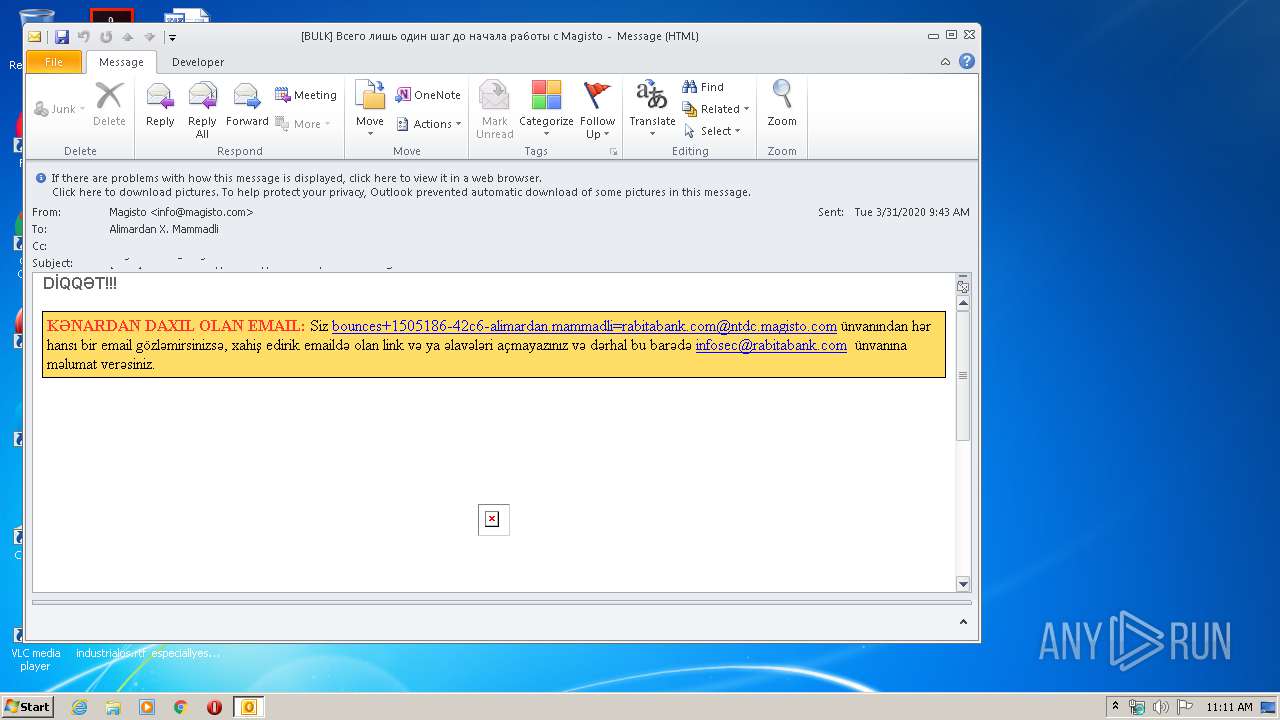
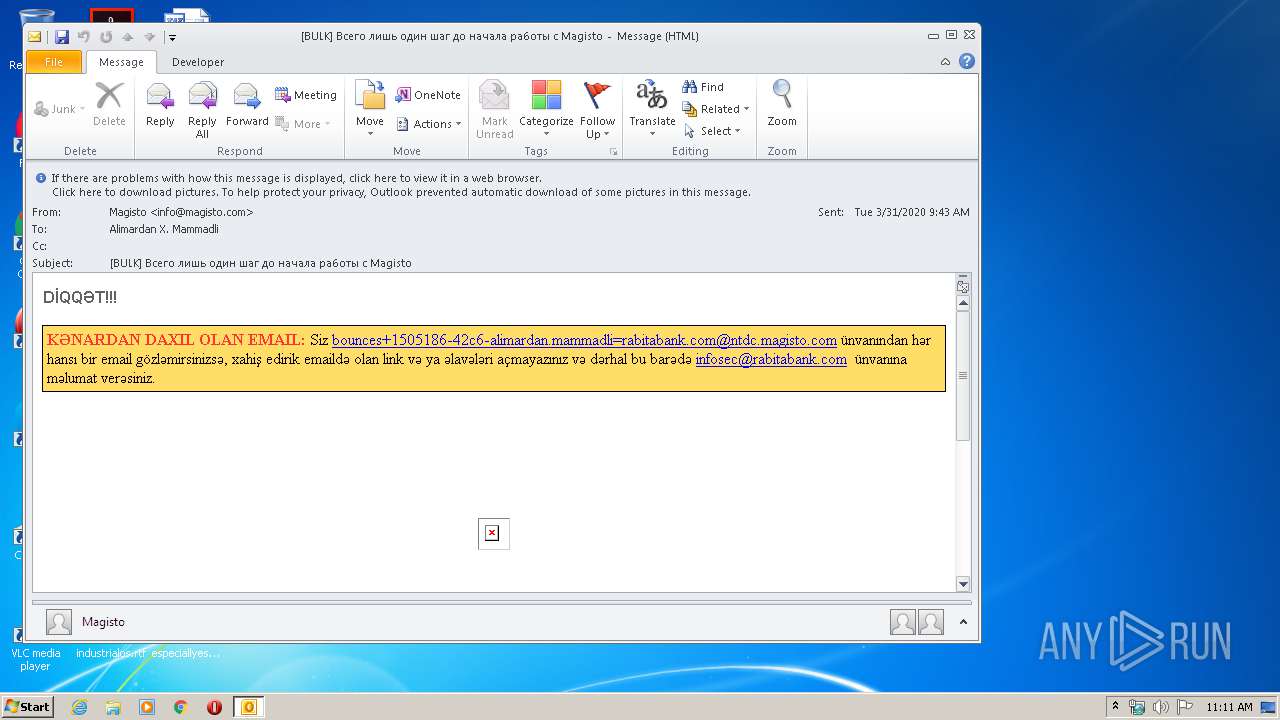
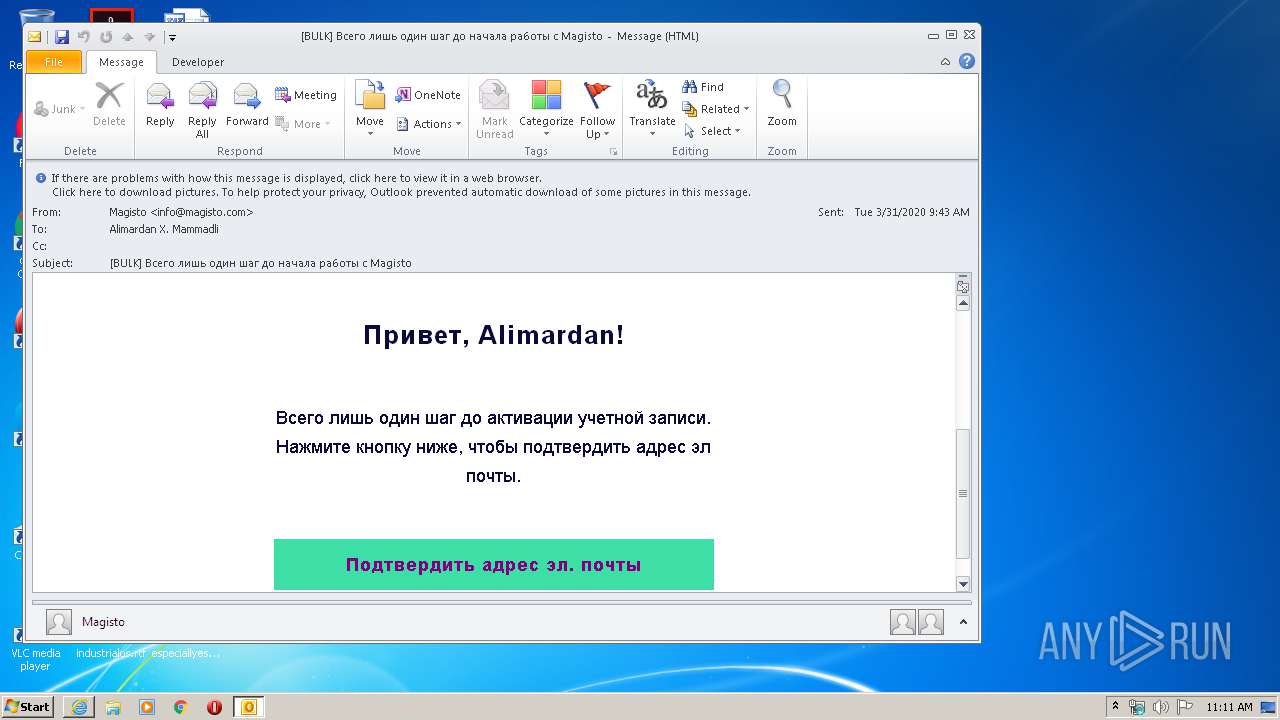
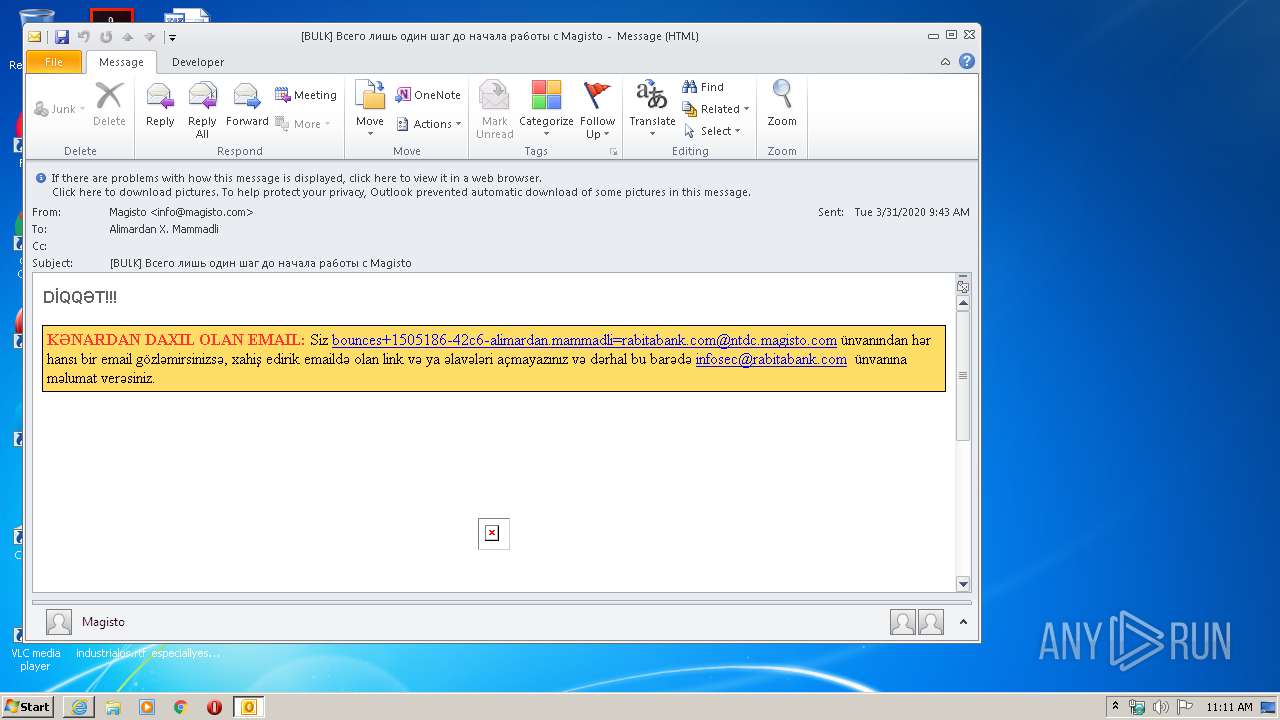
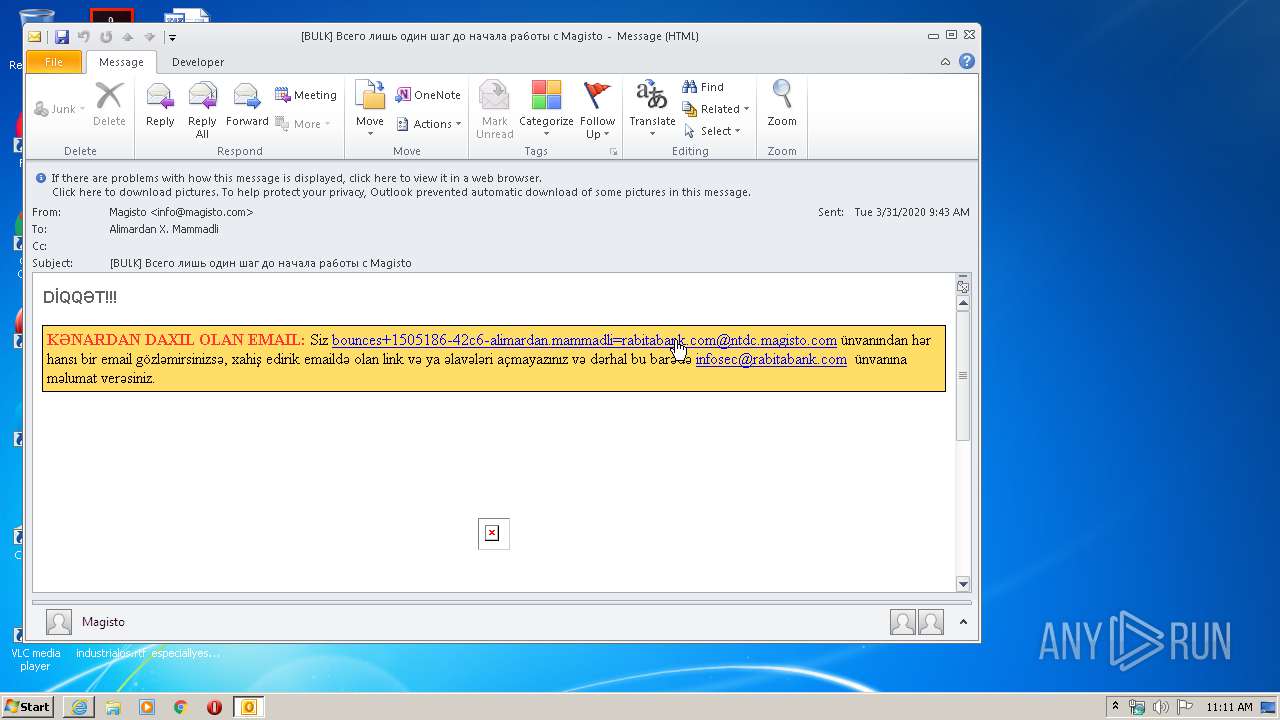
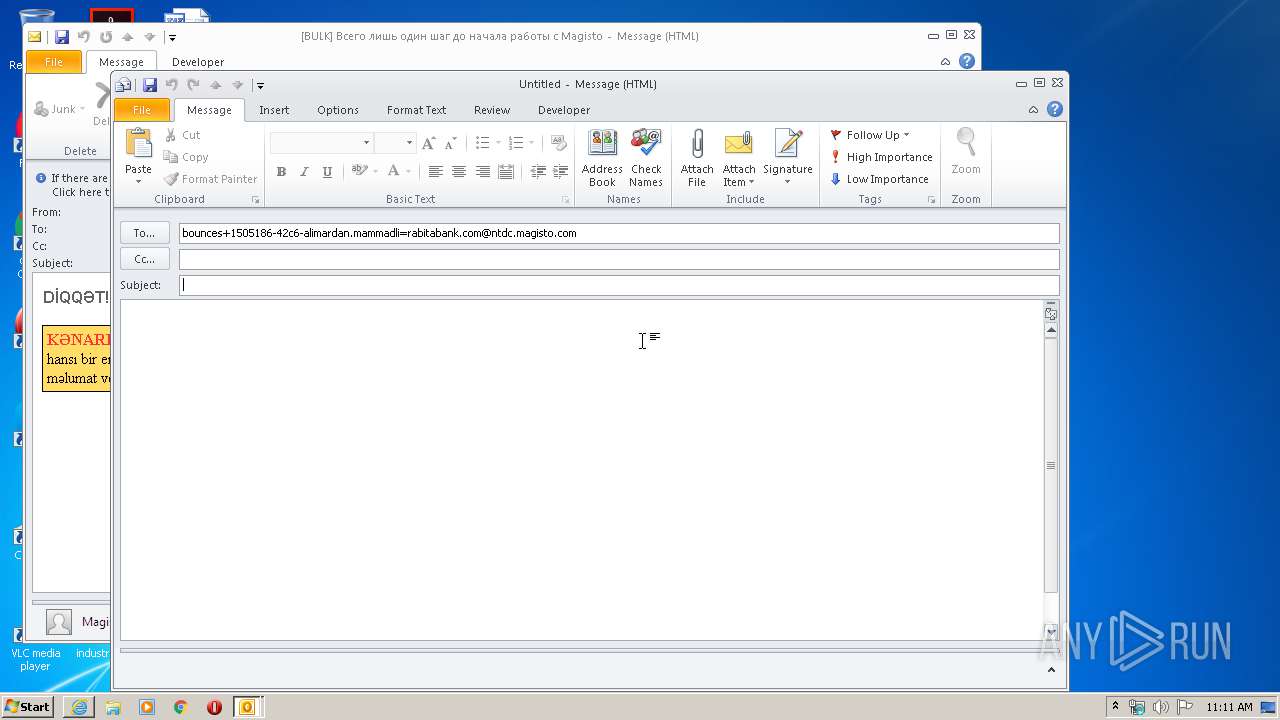
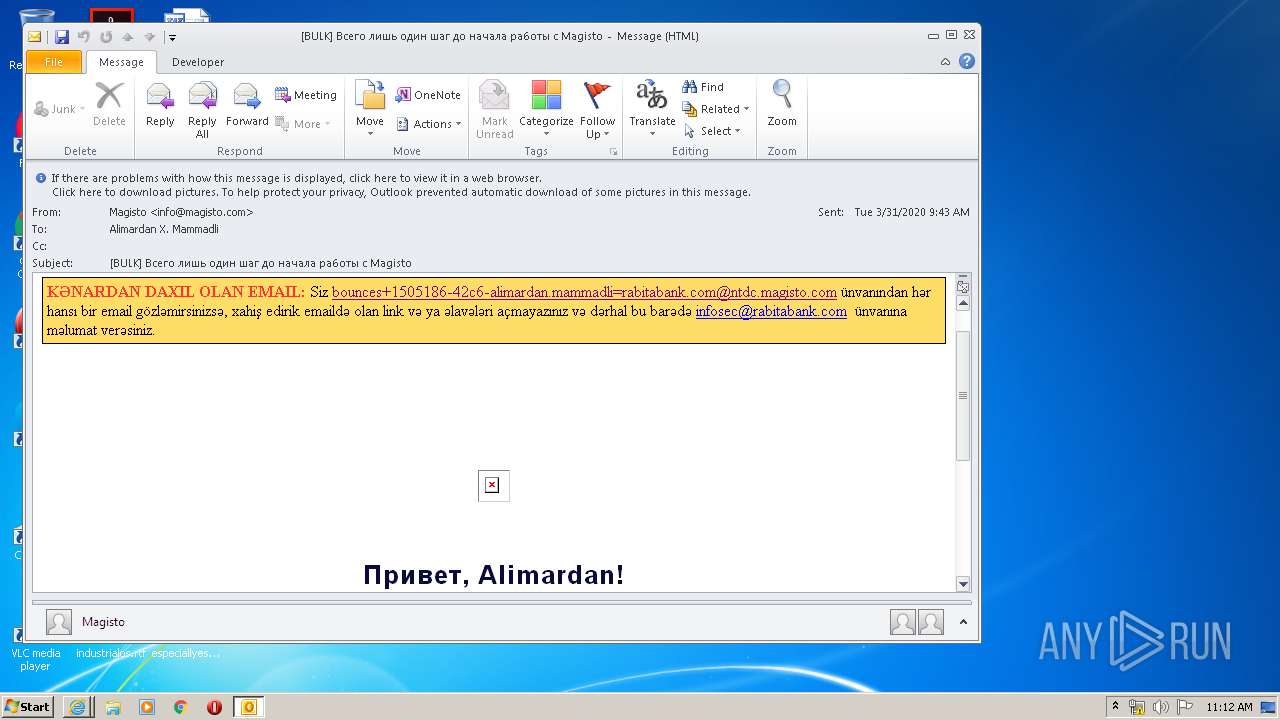
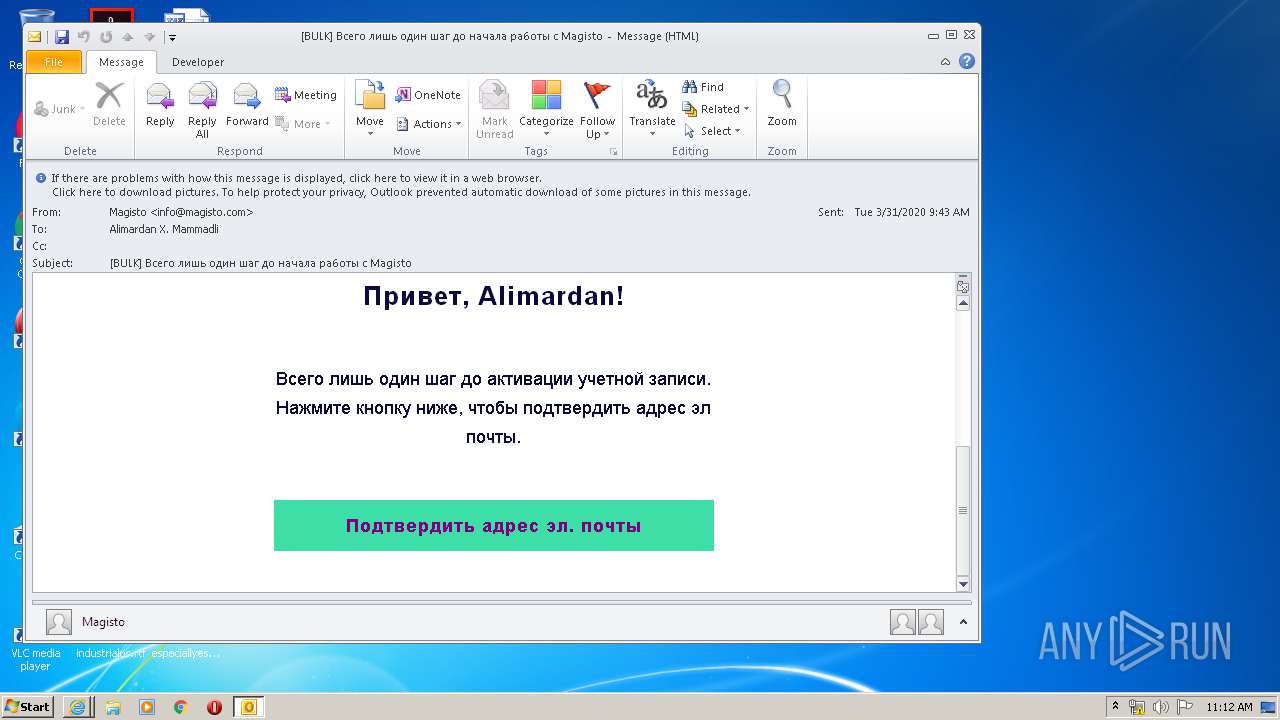
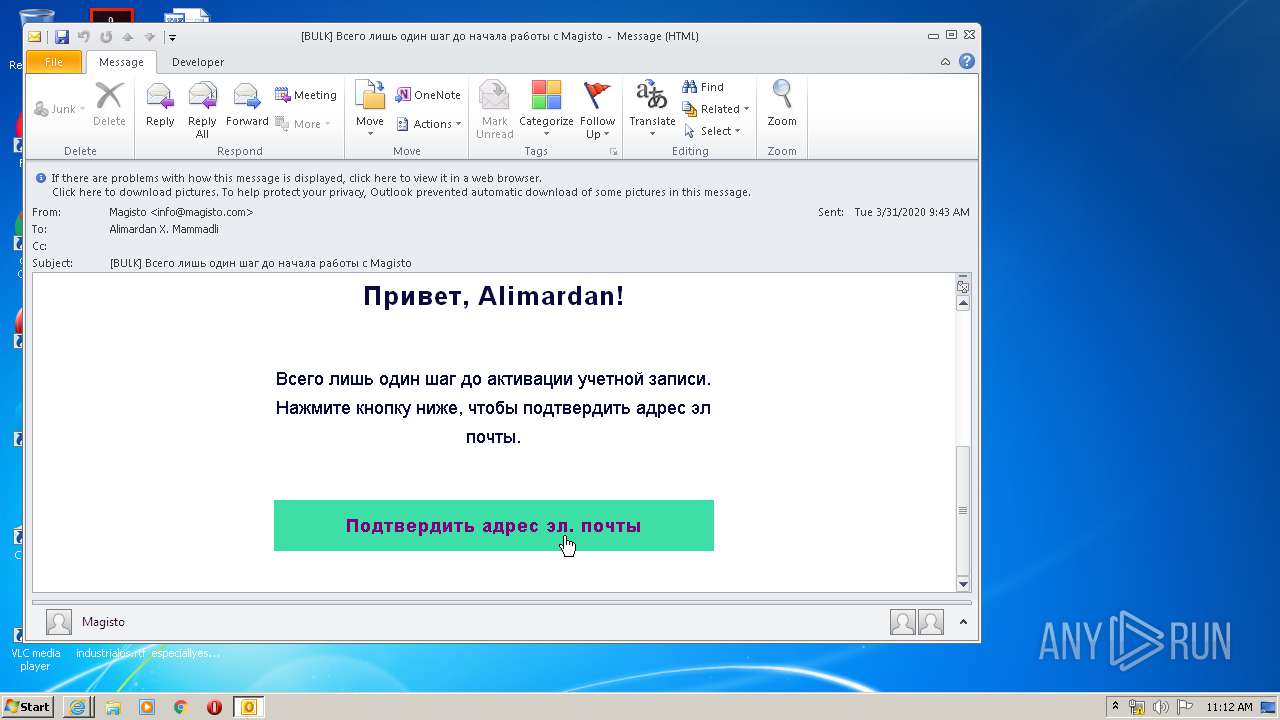
| 2648 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:bounces+1505186-42c6-alimardan.mammadli=rabitabank.com@ntdc.magisto.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
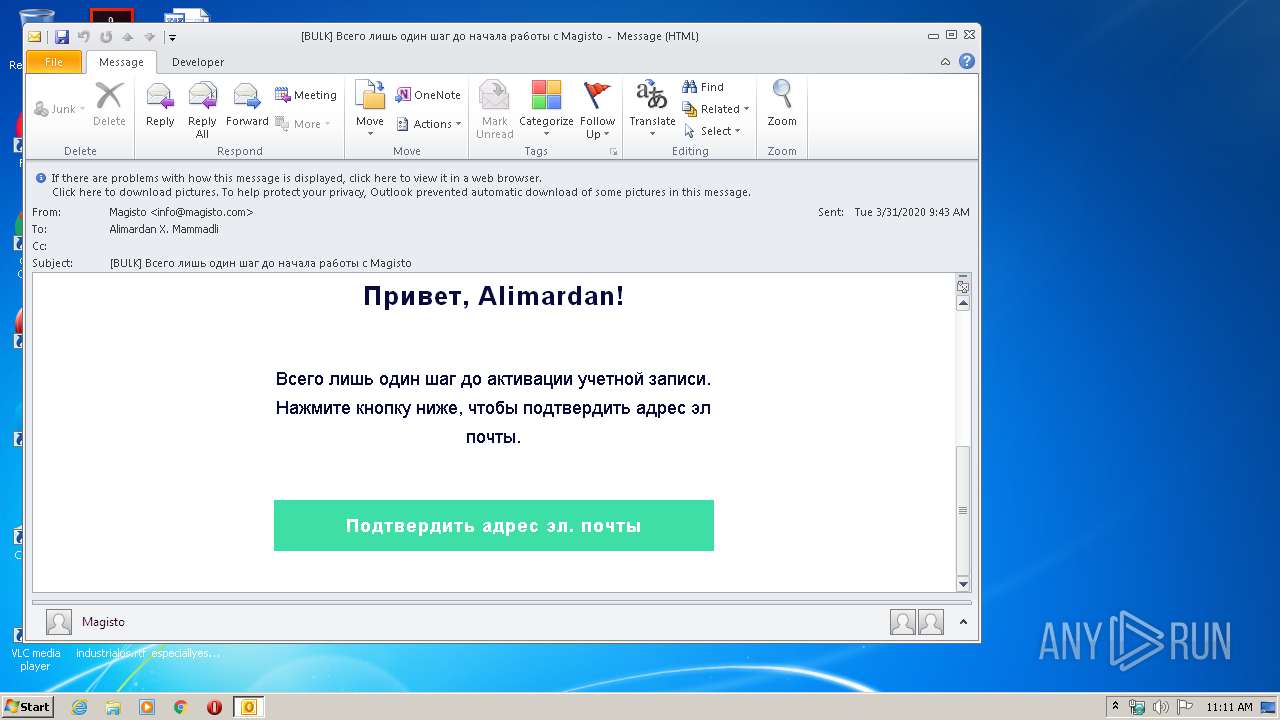
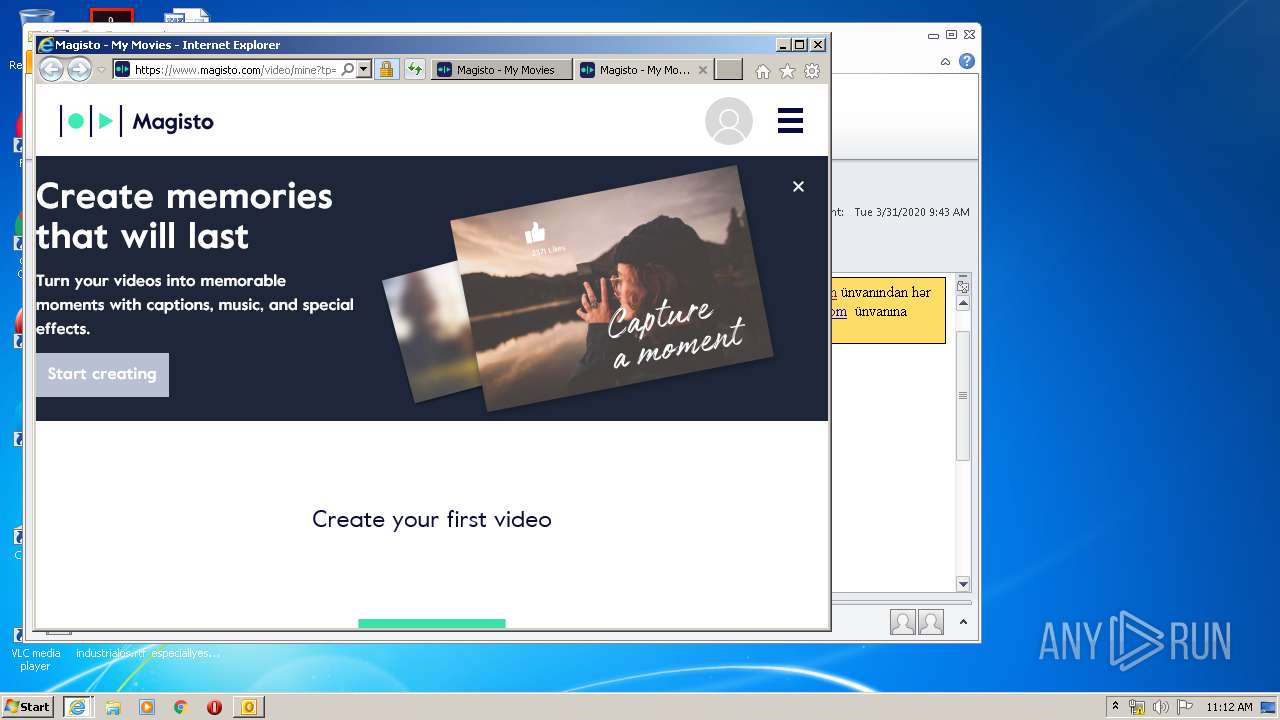
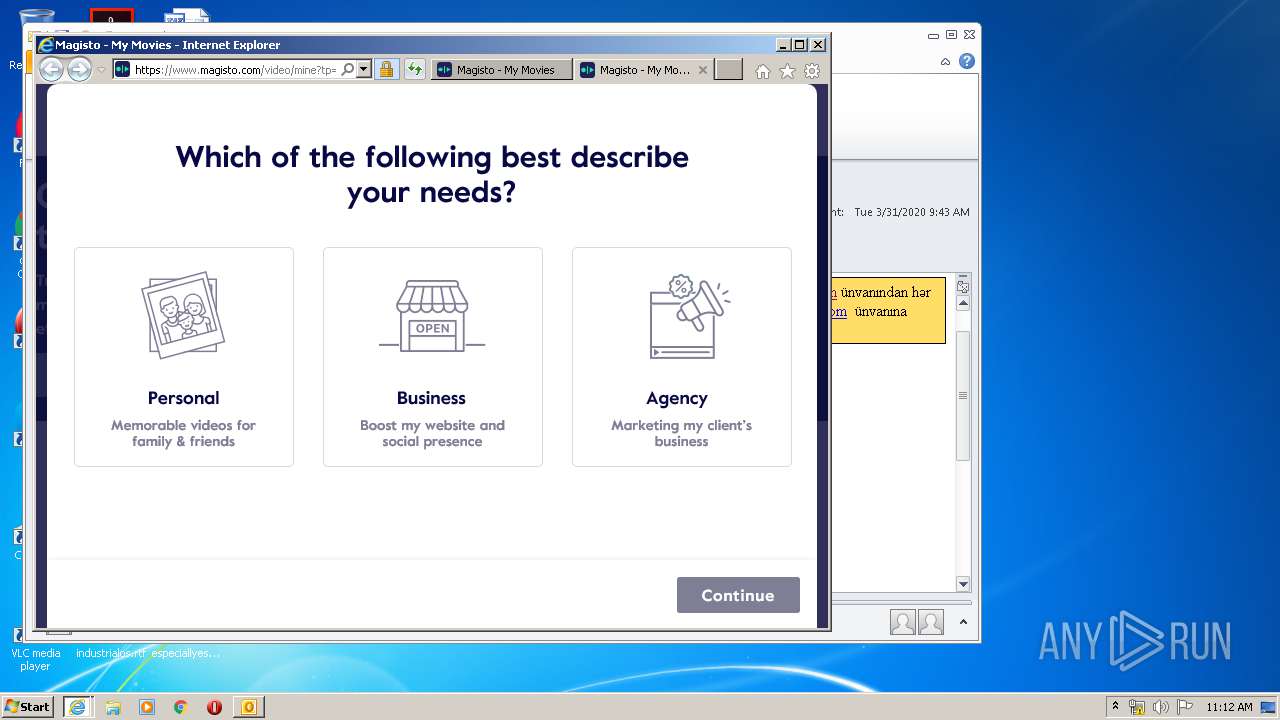
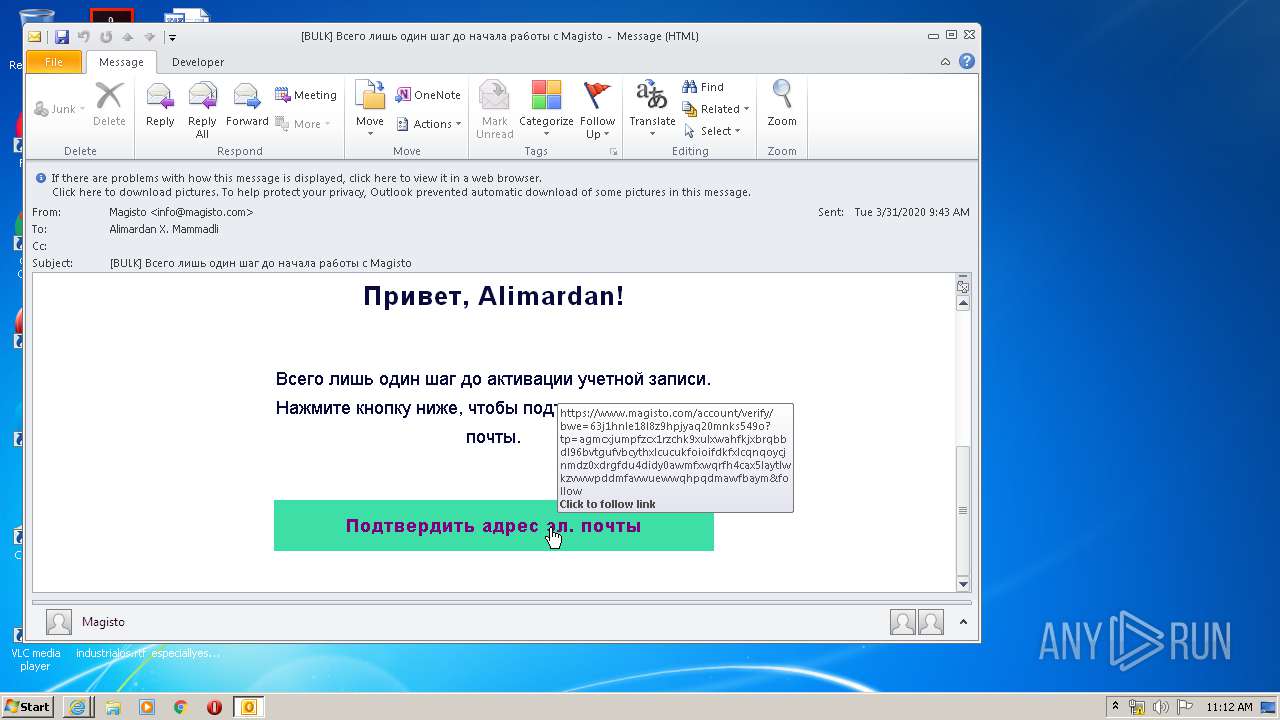
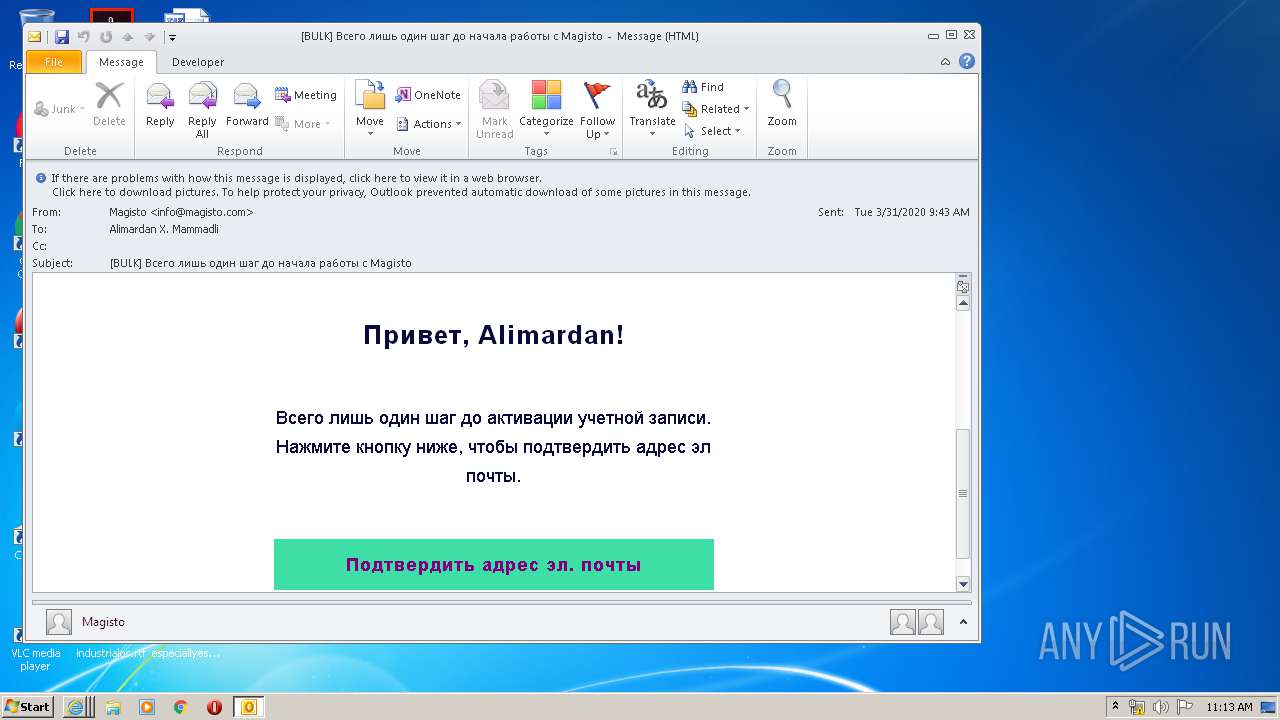
| 3140 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.magisto.com/account/verify/bWE%3D63j1hnle18l8z9hpjyaq20mnks549o?tp=AgMCXjUmPFZCX1RZCHk9XUlXWAhfKjxbRQBbDl96bVtGUFVbCythXlcUCUkFOioIFDkFXlcqNQoYCjNMDz0xDRgFDU4DIDY0AwMfXwQrfh4CAx5lAytlWkZVWwpddmFaVwUEWwQhPQdMAwFbAyM&follow | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3160 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\download.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
7 921
Read events
2 836
Write events
3 606
Delete events
1 479
Modification events
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3612) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
94
Text files
126
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B07.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2824 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA12A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 816 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabCB95.tmp | — | |
MD5:— | SHA256:— | |||
| 816 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarCB96.tmp | — | |
MD5:— | SHA256:— | |||
| 816 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EAII6FQU.txt | — | |
MD5:— | SHA256:— | |||
| 3612 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:— | SHA256:— | |||
| 816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FC5A820A001B41D68902E051F36A5282_C3B15E8B78272B90B5C15CCCF83FD2BD | der | |
MD5:— | SHA256:— | |||
| 816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
| 816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
148
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
816 | iexplore.exe | GET | 200 | 52.222.149.202:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
816 | iexplore.exe | GET | 200 | 52.222.149.213:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
816 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
816 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFeh1L3VO0beCAAAAAAyCgc%3D | US | der | 471 b | whitelisted |
816 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFFu4wHRKPokCAAAAAAyCoE%3D | US | der | 471 b | whitelisted |
816 | iexplore.exe | GET | 200 | 52.222.149.124:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAbQJ3WpgFENd1BnJNNPTJc%3D | US | der | 471 b | whitelisted |
816 | iexplore.exe | GET | 200 | 52.222.149.112:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
816 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFeh1L3VO0beCAAAAAAyCgc%3D | US | der | 471 b | whitelisted |
816 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
816 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3612 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
816 | iexplore.exe | 18.206.33.238:443 | www.magisto.com | — | US | unknown |
816 | iexplore.exe | 52.222.149.112:80 | o.ss2.us | Amazon.com, Inc. | US | whitelisted |
816 | iexplore.exe | 52.222.149.202:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
816 | iexplore.exe | 52.222.149.213:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
816 | iexplore.exe | 52.222.149.124:80 | ocsp.sca1b.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
816 | iexplore.exe | 52.222.158.228:443 | d1ekrxlws13em5.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
816 | iexplore.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
816 | iexplore.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
816 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.magisto.com |
| suspicious |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
d1ekrxlws13em5.cloudfront.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
script.crazyegg.com |
| whitelisted |
s.symcd.com |
| shared |