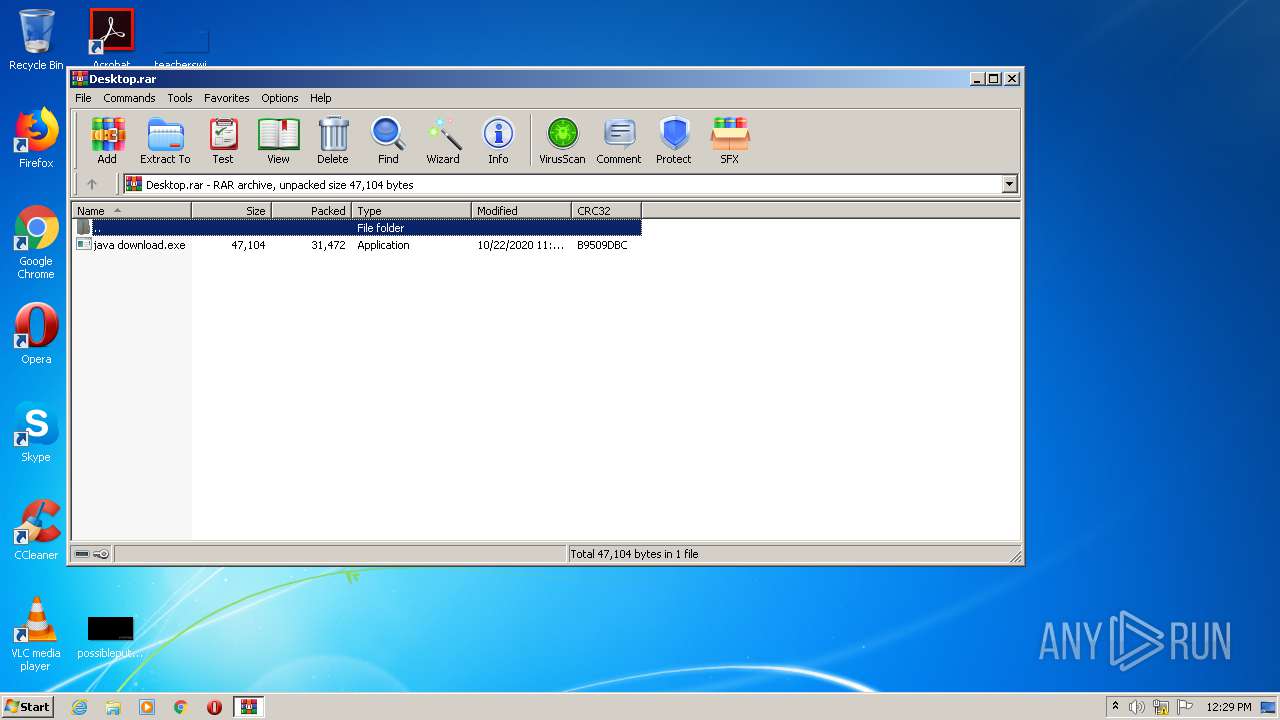
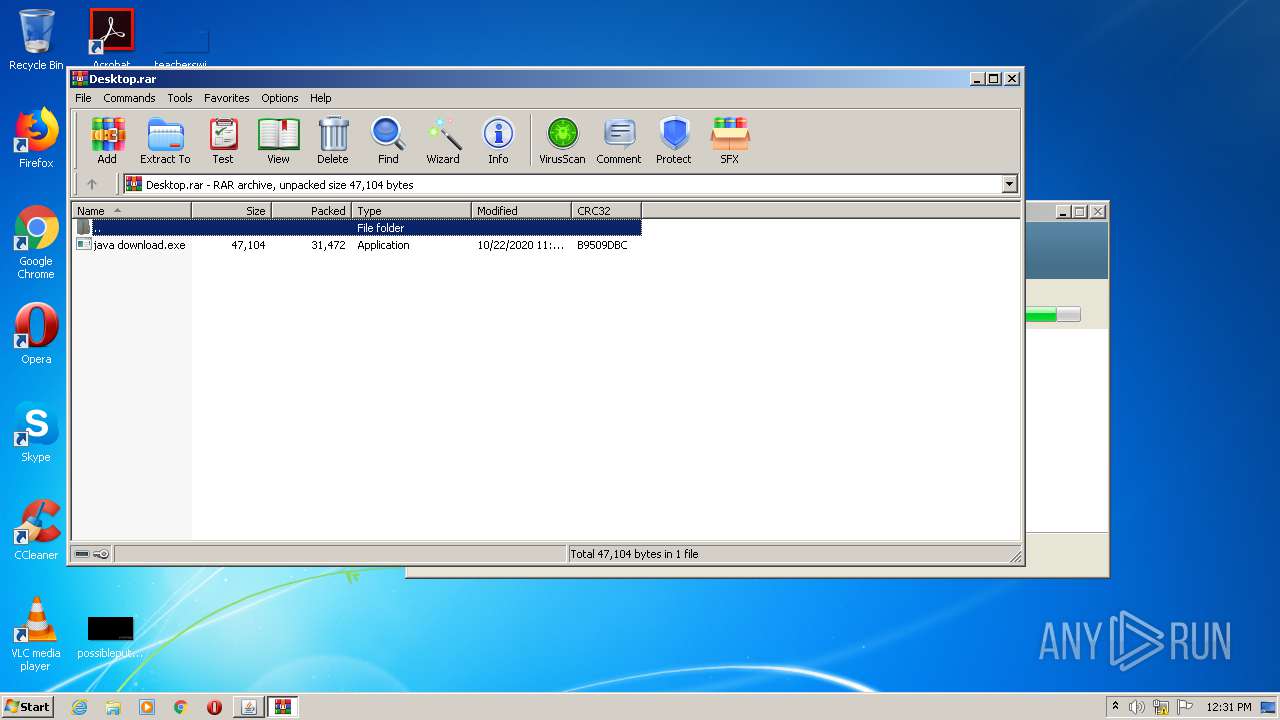
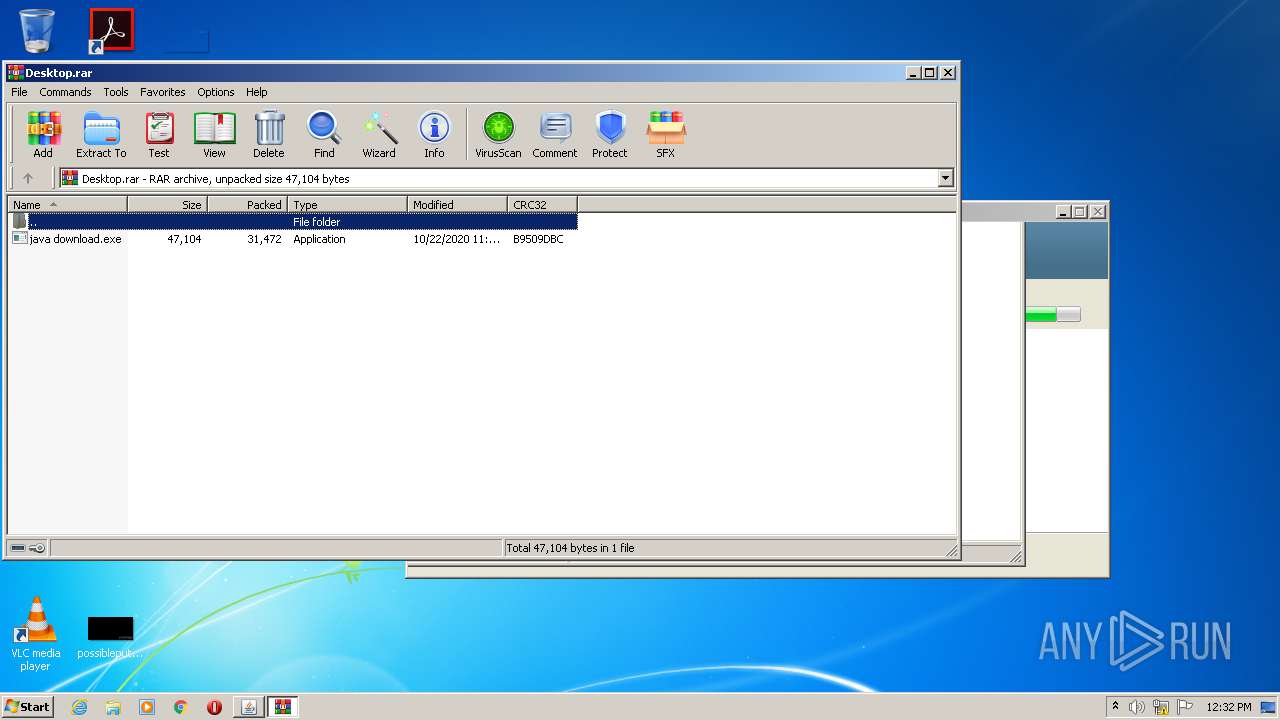
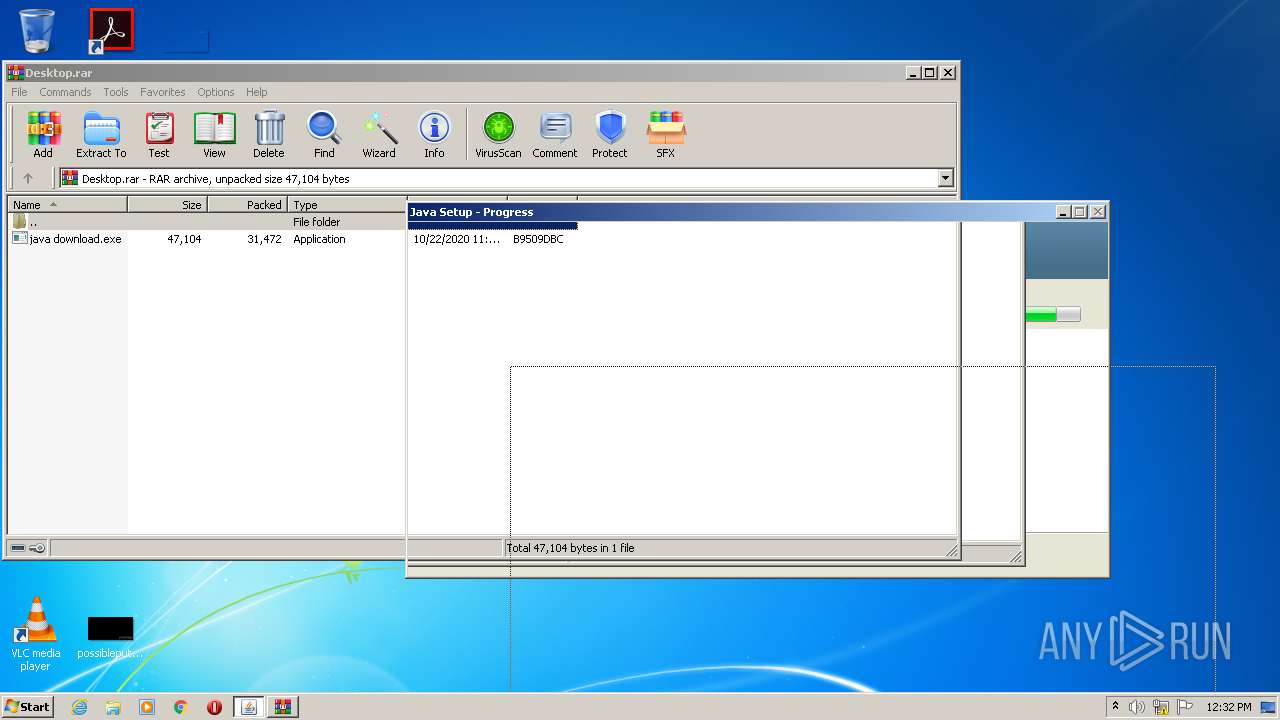
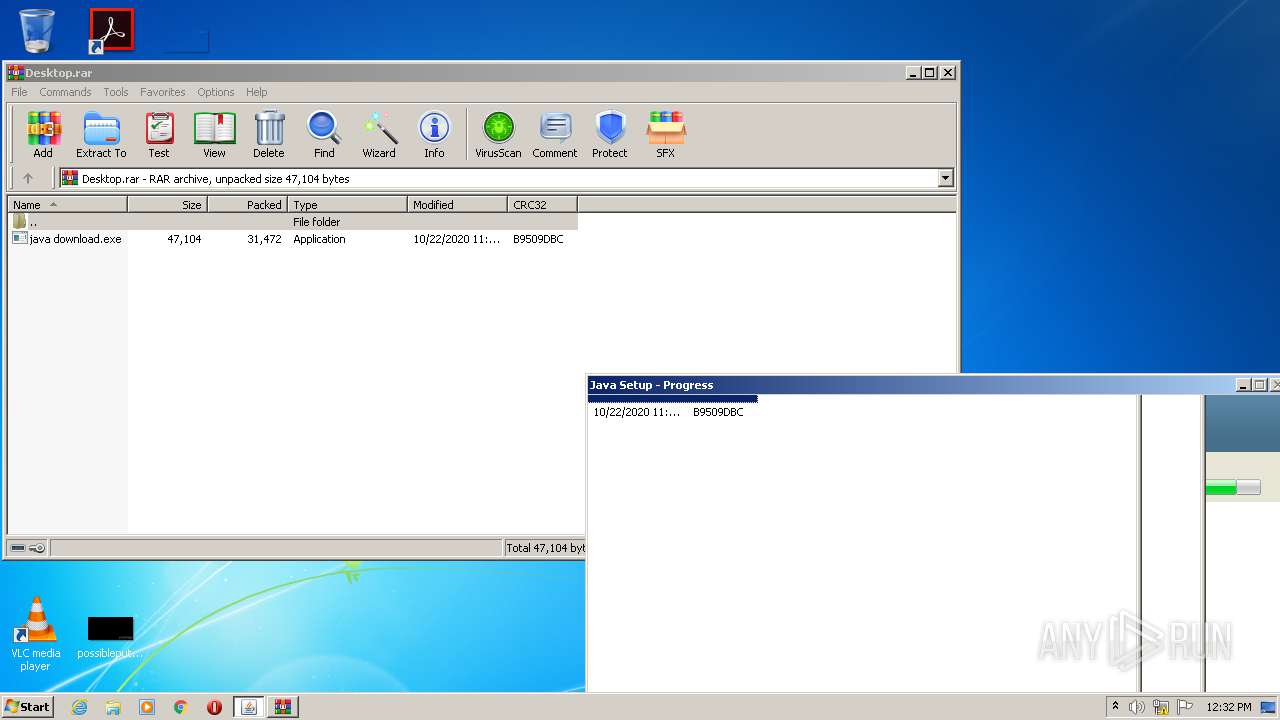
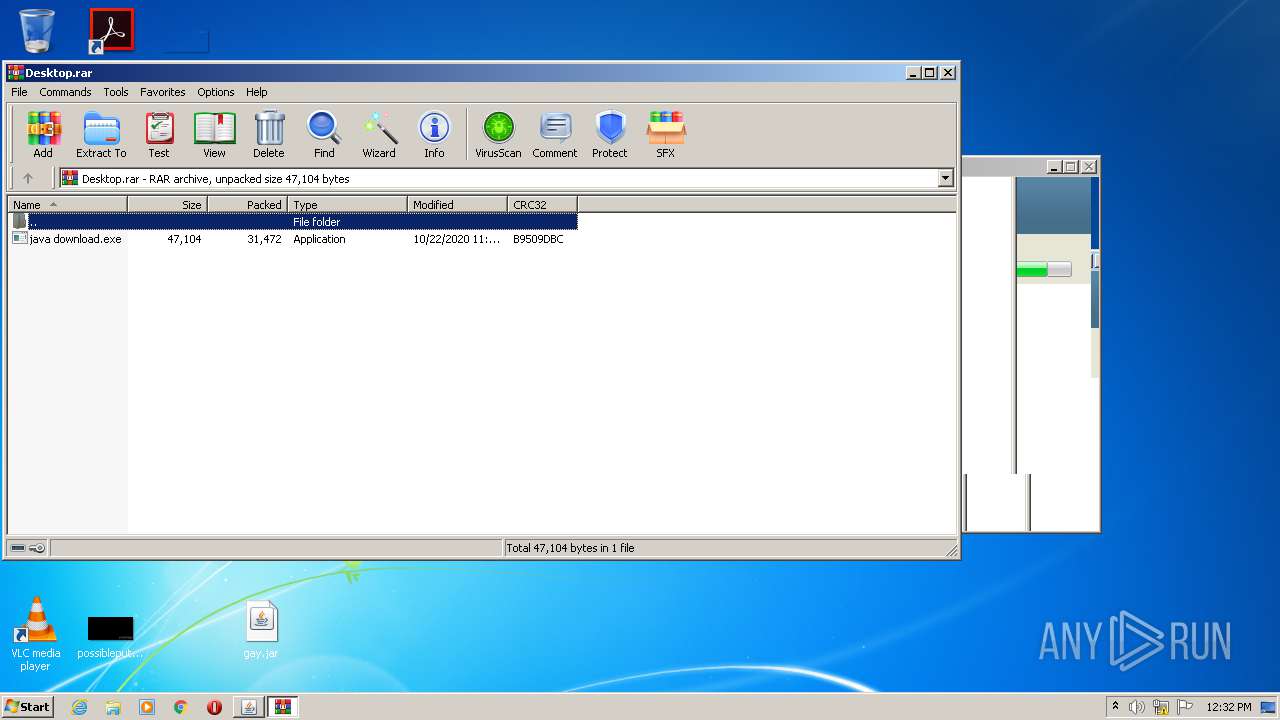
| File name: | Desktop.rar |
| Full analysis: | https://app.any.run/tasks/9d03c3a5-9194-4de7-93df-4270a290aa90 |
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2020, 11:28:41 |
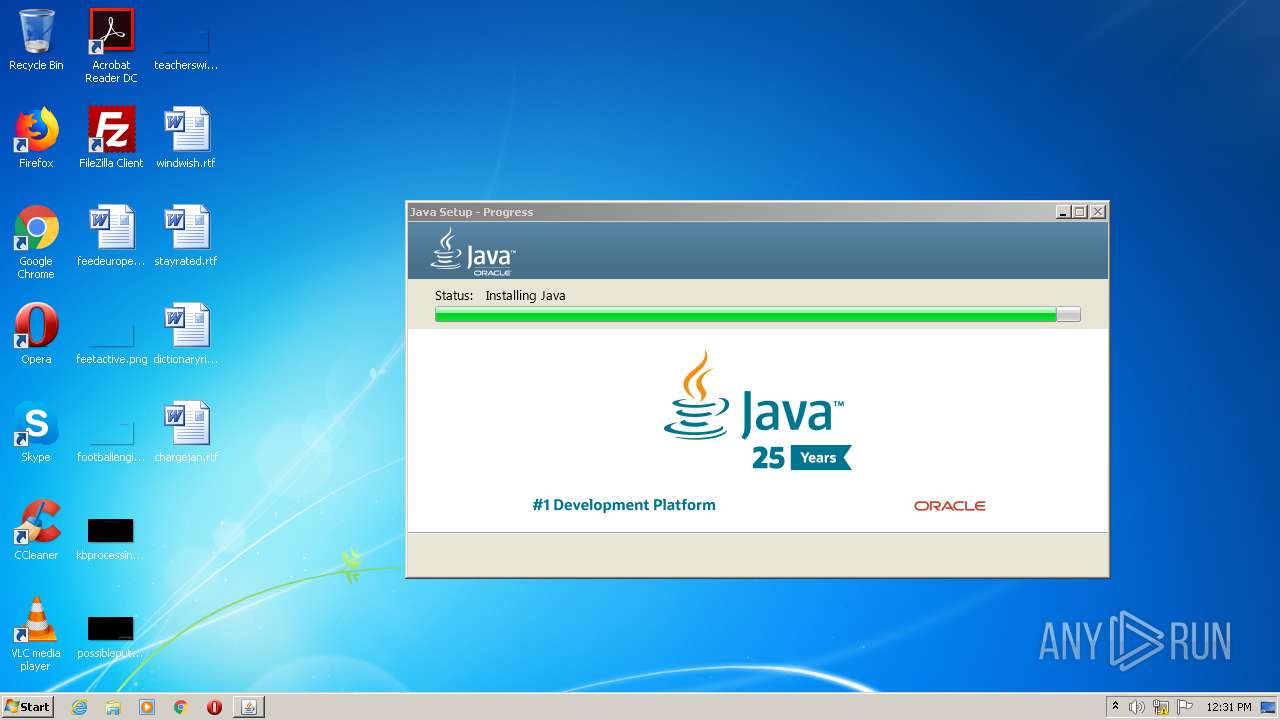
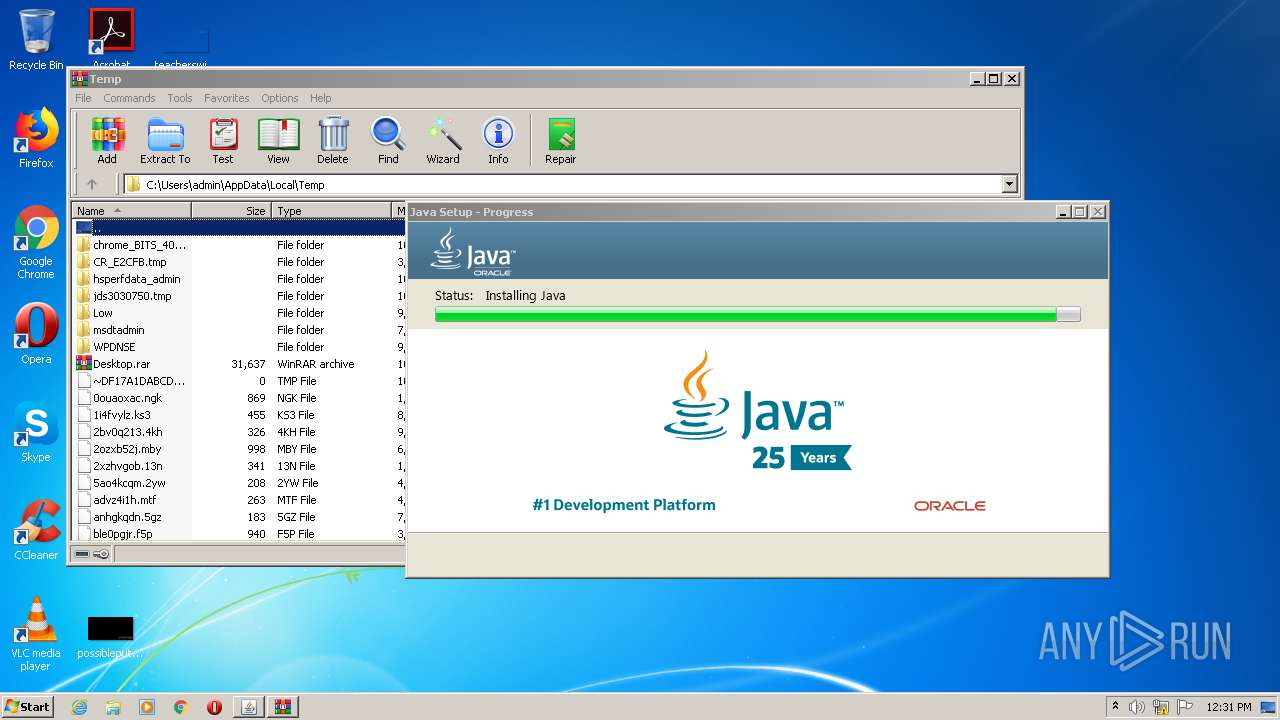
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | FFA6D2AA8EAA8547199C85DEF5A960B6 |
| SHA1: | 56085BF780CDED05822F98E9ECC207F497A6C9DA |
| SHA256: | BF08BA40D16A83FB1D60A6B2625D4B8C1CE626498AC59A57FFF36DBC53E06D60 |
| SSDEEP: | 768:Jt8OyTwzfnWxtmL2mKcc2a0+9k/0t/XQ54bq4BXJ+b:JiOyW+xt5Kce+q6Q549G |
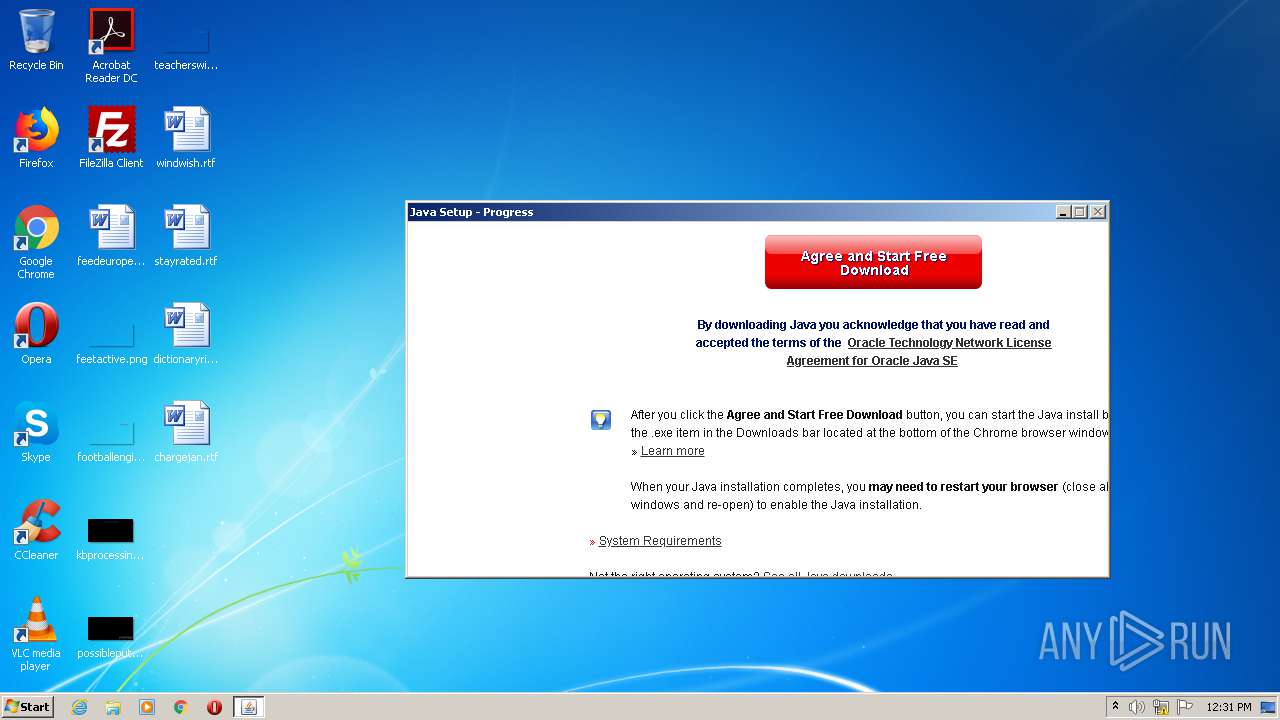
MALICIOUS
Changes settings of System certificates
- chromeinstall.exe (PID: 2964)
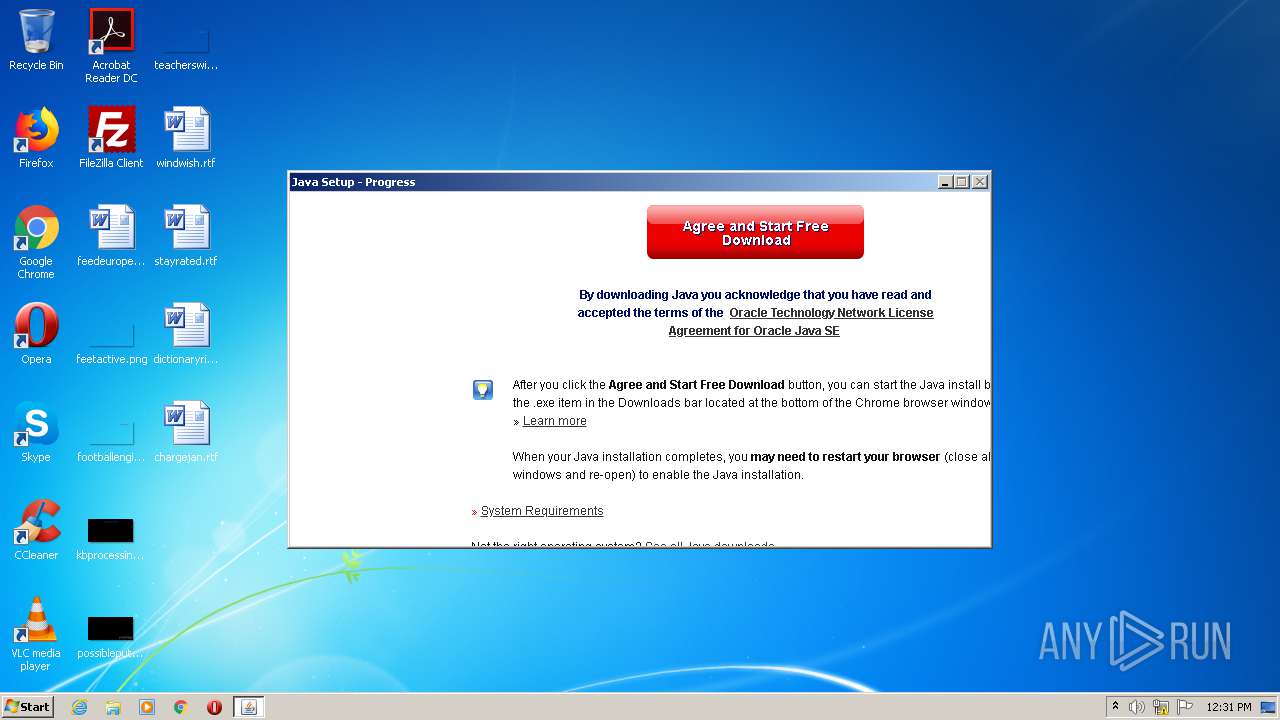
Application was dropped or rewritten from another process
- chromeinstall.exe (PID: 3712)
- chromeinstall.exe (PID: 2576)
- chromeinstall.exe (PID: 2964)
- LZMA_EXE (PID: 2384)
- LZMA_EXE (PID: 2932)
- bspatch.exe (PID: 1628)
- unpack200.exe (PID: 524)
- unpack200.exe (PID: 2112)
- unpack200.exe (PID: 2912)
- unpack200.exe (PID: 3752)
- unpack200.exe (PID: 1792)
- unpack200.exe (PID: 612)
- unpack200.exe (PID: 3548)
- javaw.exe (PID: 3736)
- ssvagent.exe (PID: 2864)
- javaws.exe (PID: 924)
- jp2launcher.exe (PID: 2820)
- javaws.exe (PID: 2724)
- javaw.exe (PID: 3716)
- jp2launcher.exe (PID: 2672)
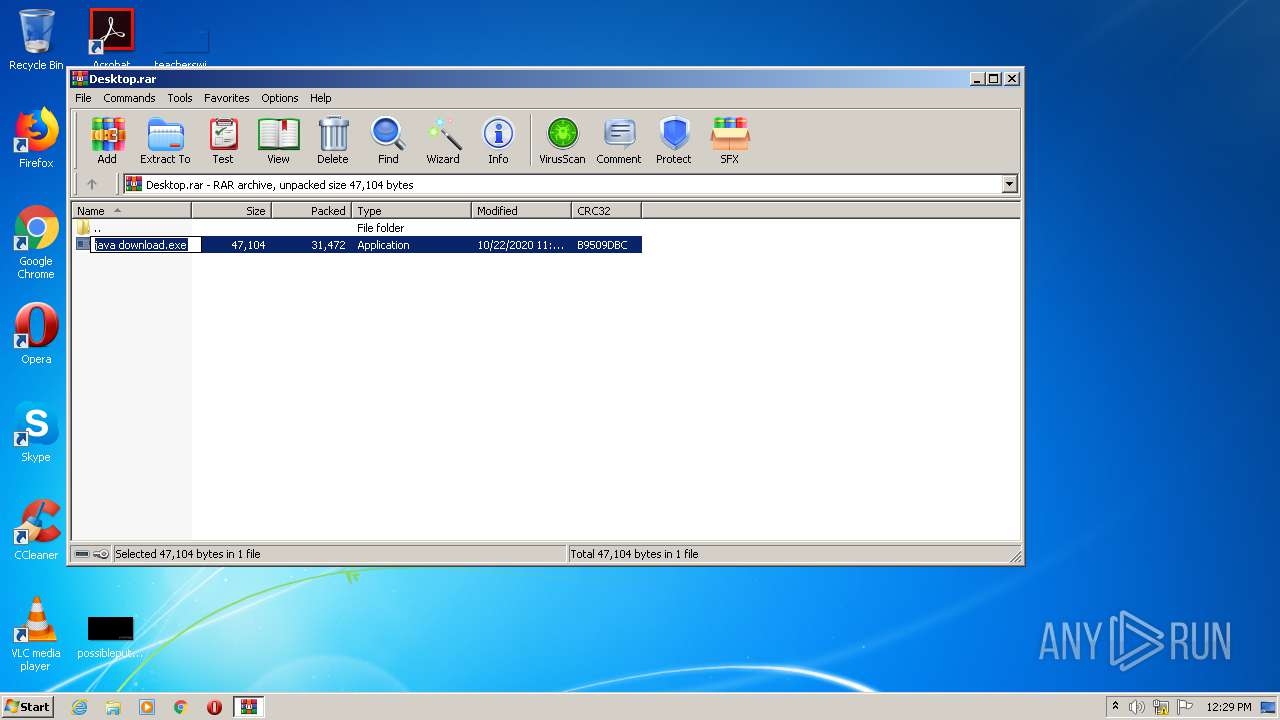
- java download.exe (PID: 4072)
Loads dropped or rewritten executable
- unpack200.exe (PID: 2112)
- unpack200.exe (PID: 2912)
- unpack200.exe (PID: 524)
- unpack200.exe (PID: 3752)
- unpack200.exe (PID: 1792)
- unpack200.exe (PID: 612)
- unpack200.exe (PID: 3548)
- javaw.exe (PID: 3736)
- installer.exe (PID: 2860)
- ssvagent.exe (PID: 2864)
- svchost.exe (PID: 872)
- jp2launcher.exe (PID: 2672)
- jp2launcher.exe (PID: 2820)
- java download.exe (PID: 4072)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 3396)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2636)
- chromeinstall.exe (PID: 2576)
- chromeinstall.exe (PID: 2964)
- installer.exe (PID: 2860)
- msiexec.exe (PID: 1144)
- WinRAR.exe (PID: 3872)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2636)
Reads Internet Cache Settings
- chromeinstall.exe (PID: 2964)
Adds / modifies Windows certificates
- chromeinstall.exe (PID: 2964)
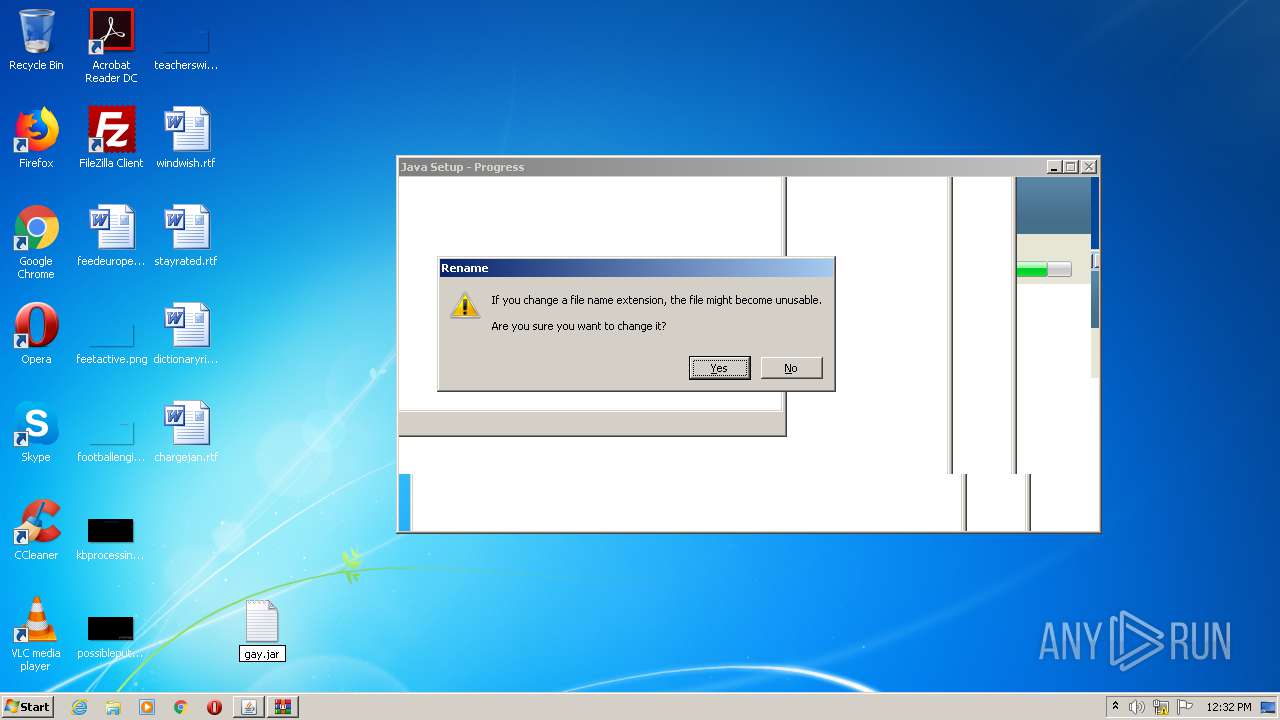
Starts application with an unusual extension
- chromeinstall.exe (PID: 2964)
Reads internet explorer settings
- chromeinstall.exe (PID: 2964)
Creates files in the program directory
- unpack200.exe (PID: 524)
- bspatch.exe (PID: 1628)
- unpack200.exe (PID: 2112)
- unpack200.exe (PID: 2912)
- unpack200.exe (PID: 3752)
- unpack200.exe (PID: 1792)
- unpack200.exe (PID: 612)
- unpack200.exe (PID: 3548)
- javaw.exe (PID: 3736)
- installer.exe (PID: 2860)
Modifies the open verb of a shell class
- installer.exe (PID: 2860)
Removes files from Windows directory
- installer.exe (PID: 2860)
Creates files in the Windows directory
- installer.exe (PID: 2860)
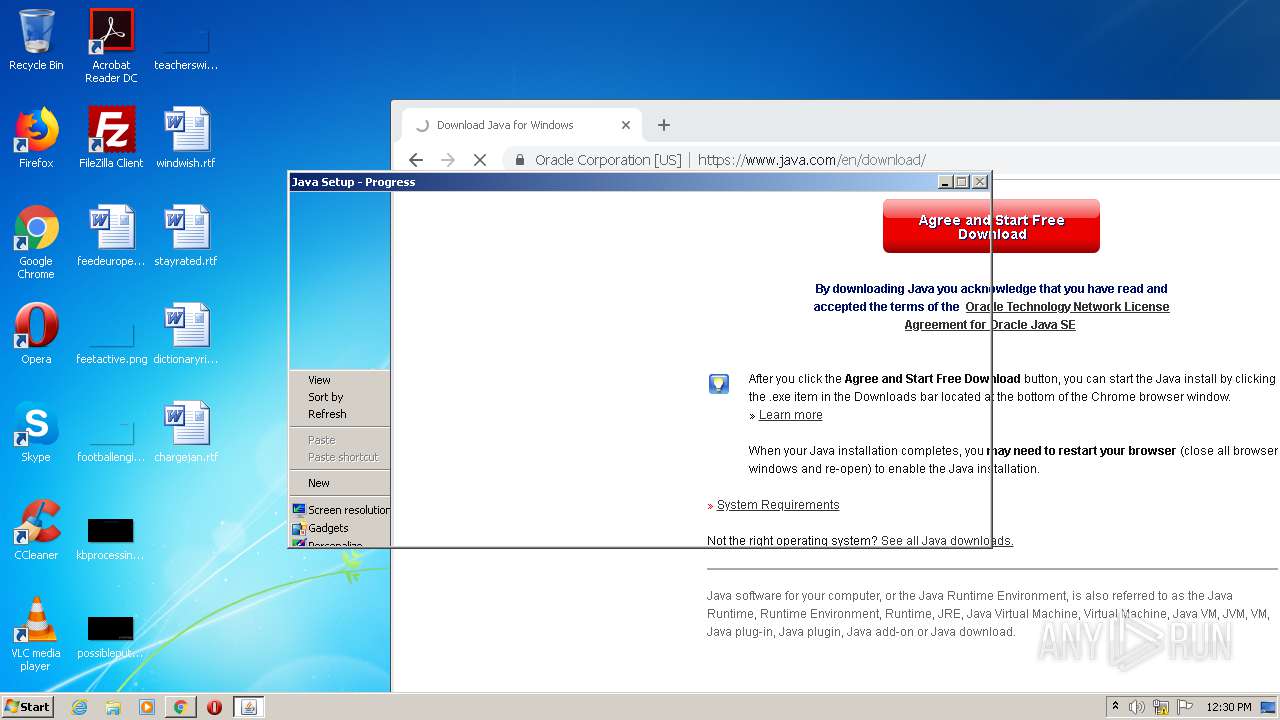
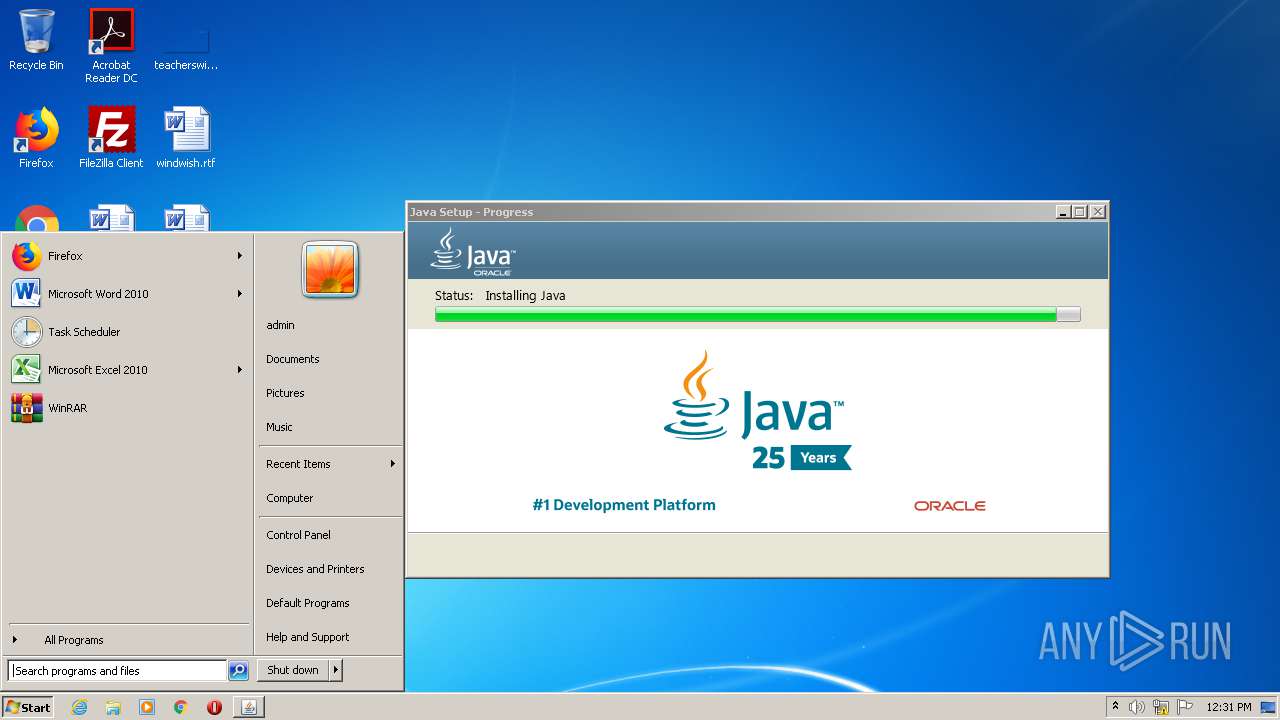
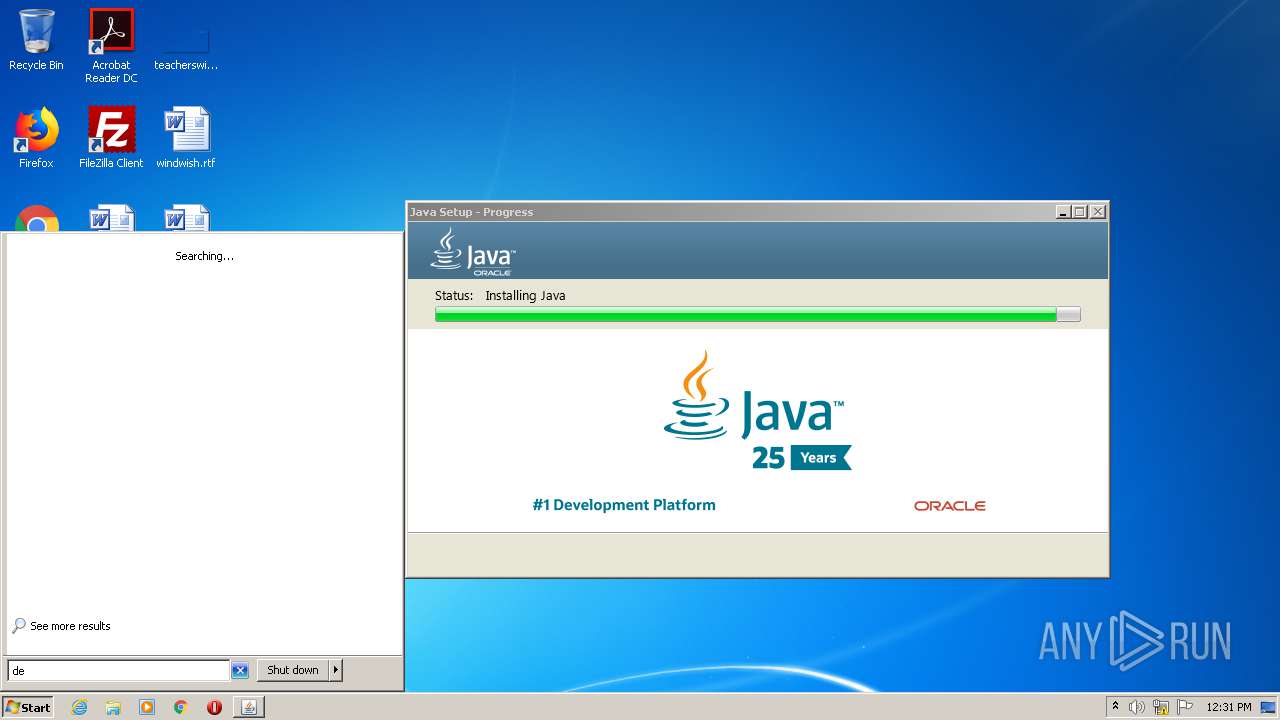
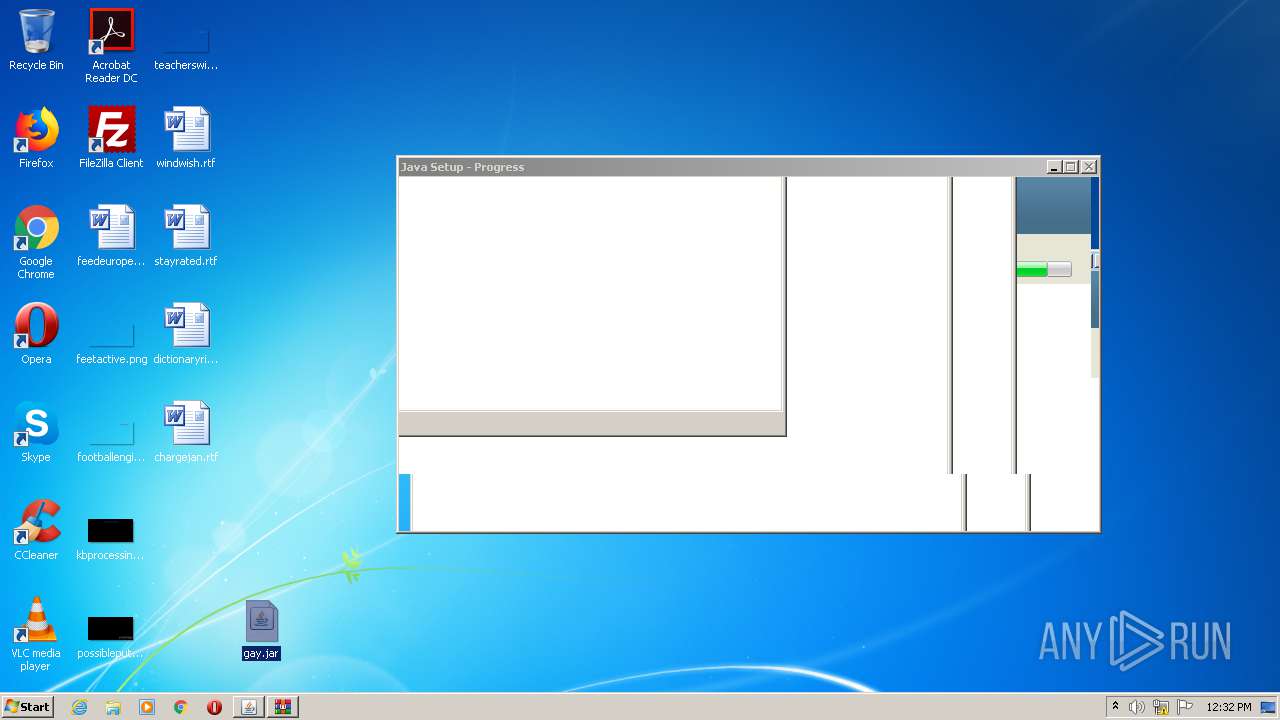
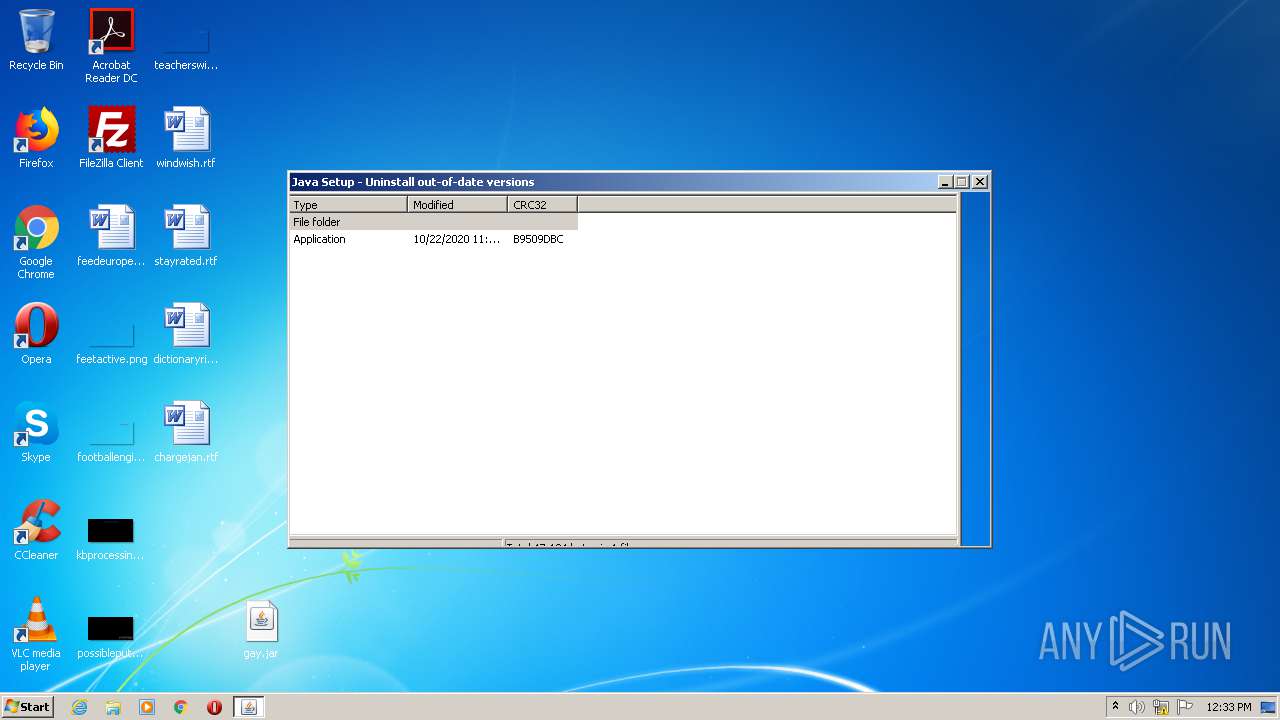
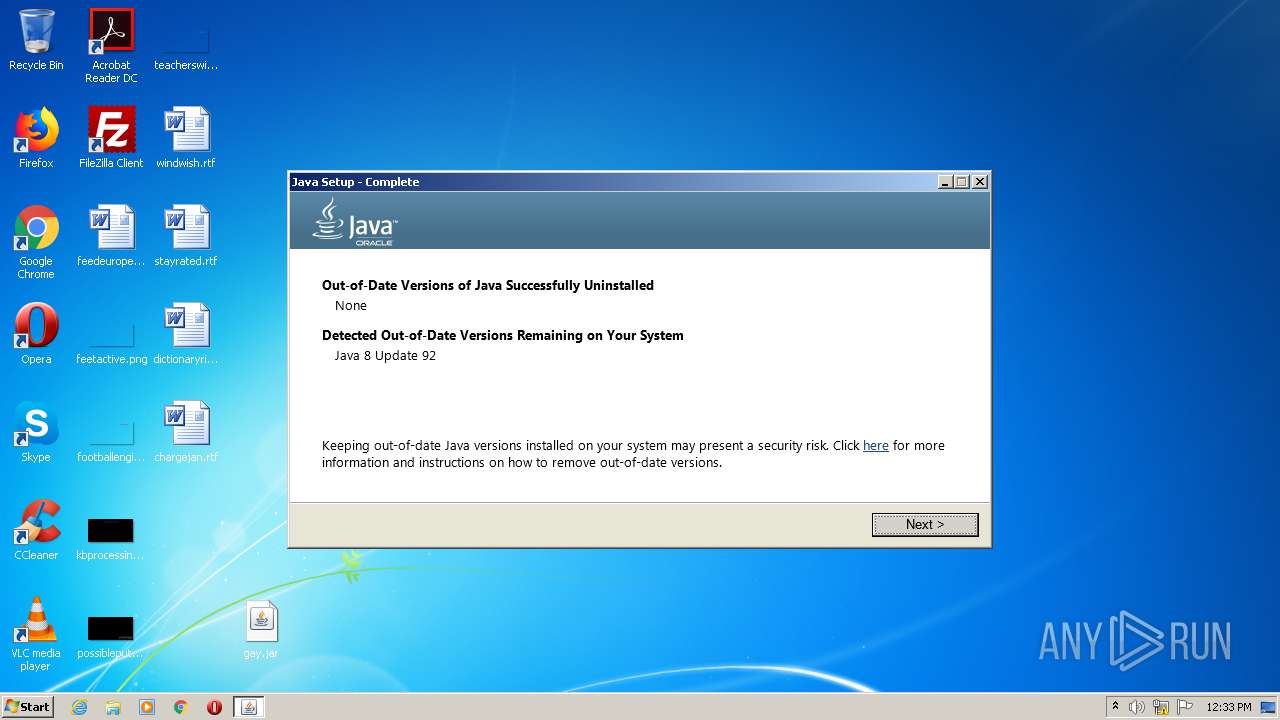
Executes JAVA applets
- installer.exe (PID: 2860)
- java download.exe (PID: 4072)
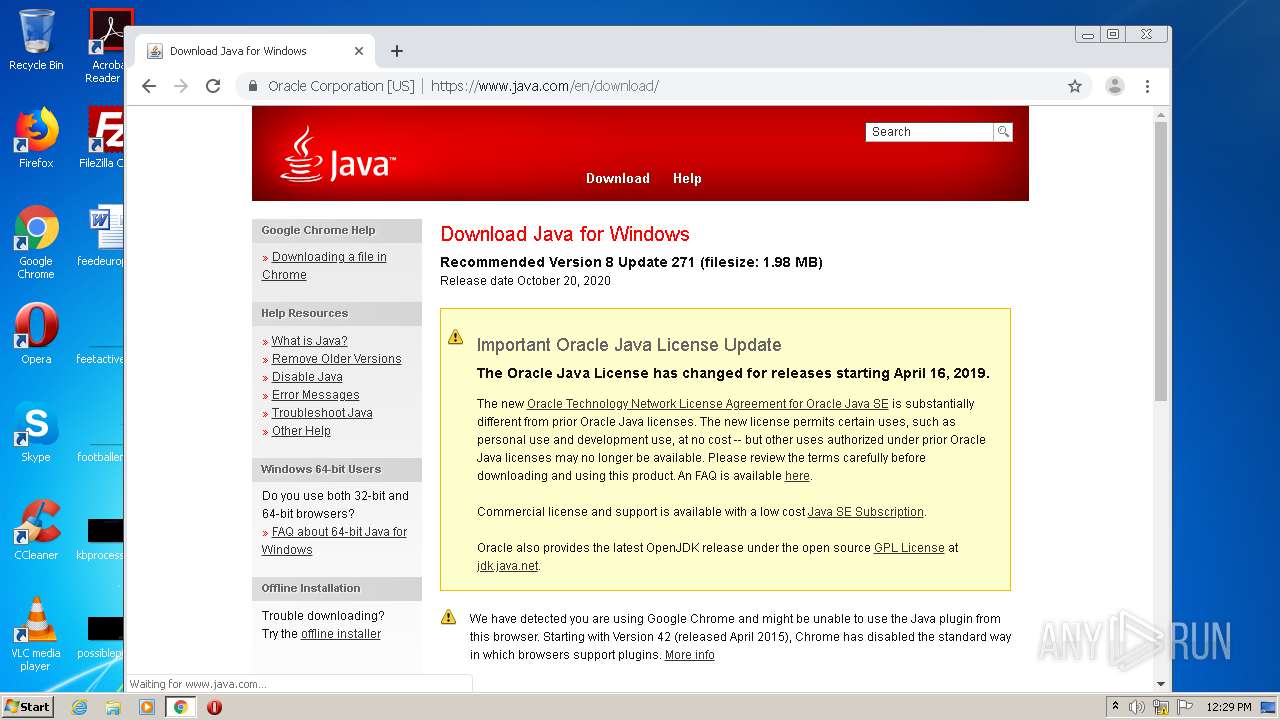
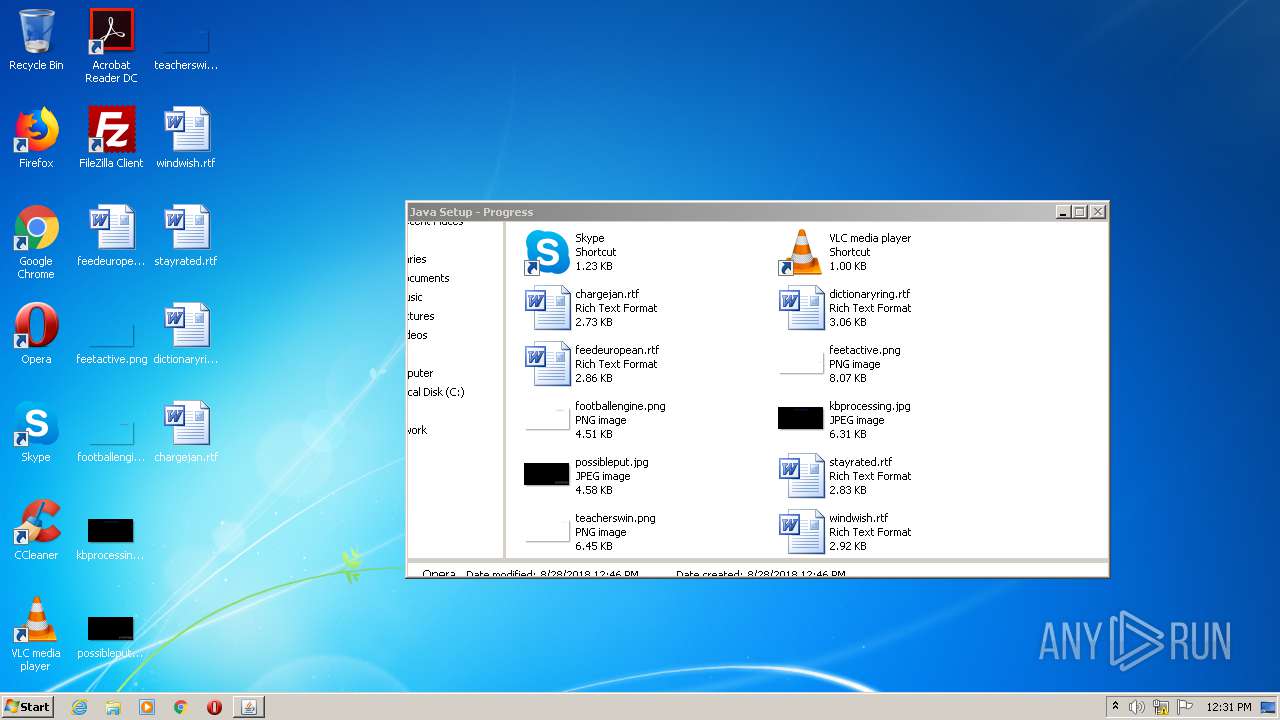
Check for Java to be installed
- installer.exe (PID: 2860)
Changes the autorun value in the registry
- msiexec.exe (PID: 1144)
Creates files in the user directory
- chromeinstall.exe (PID: 2964)
Creates COM task schedule object
- ssvagent.exe (PID: 2864)
- installer.exe (PID: 2860)
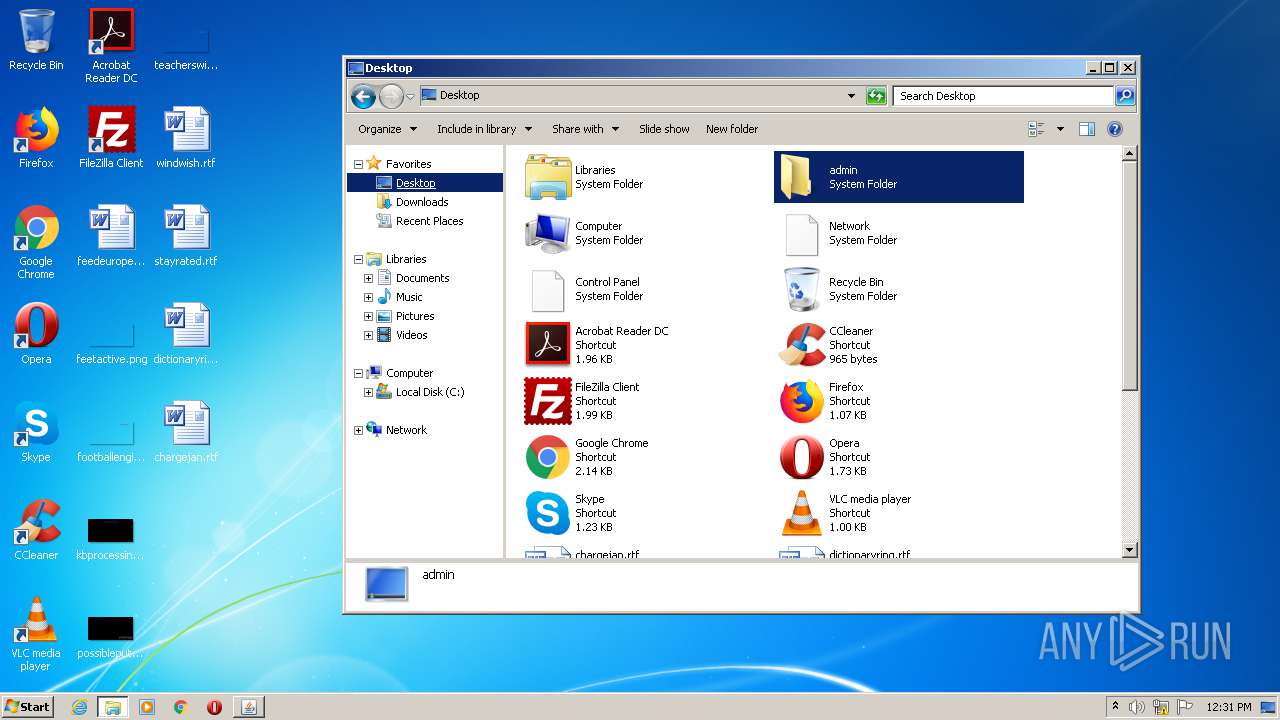
INFO
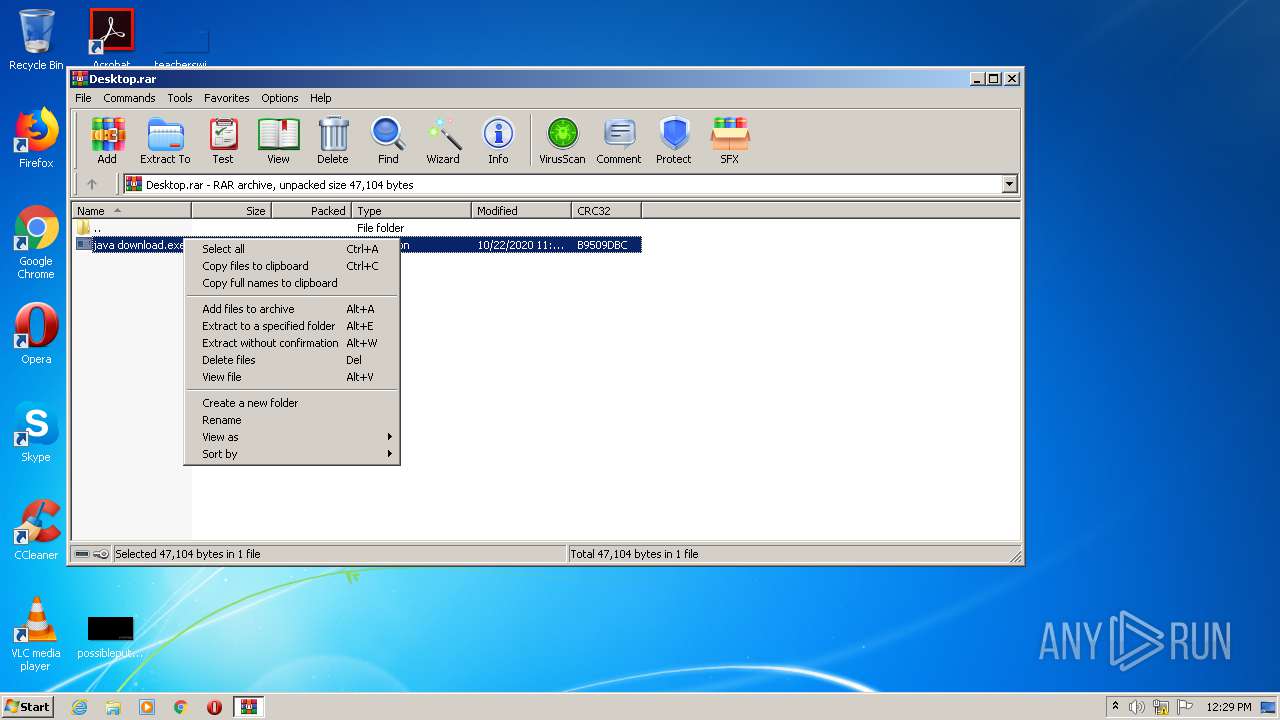
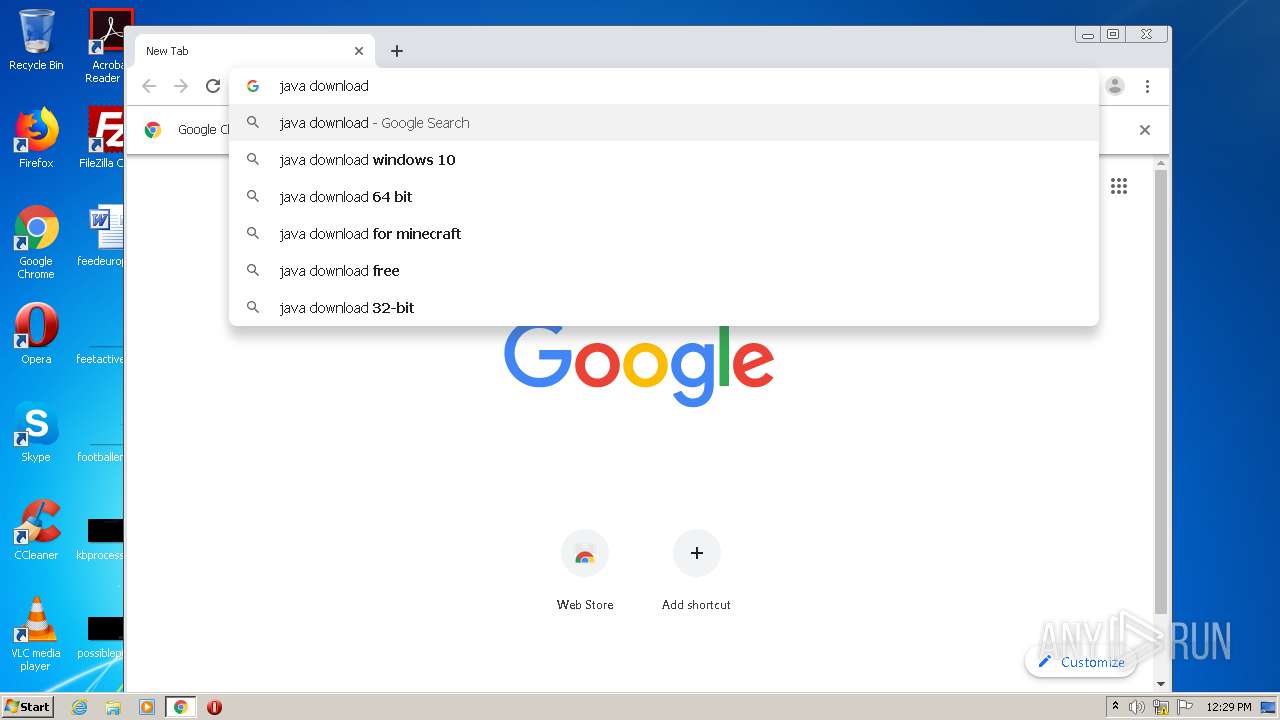
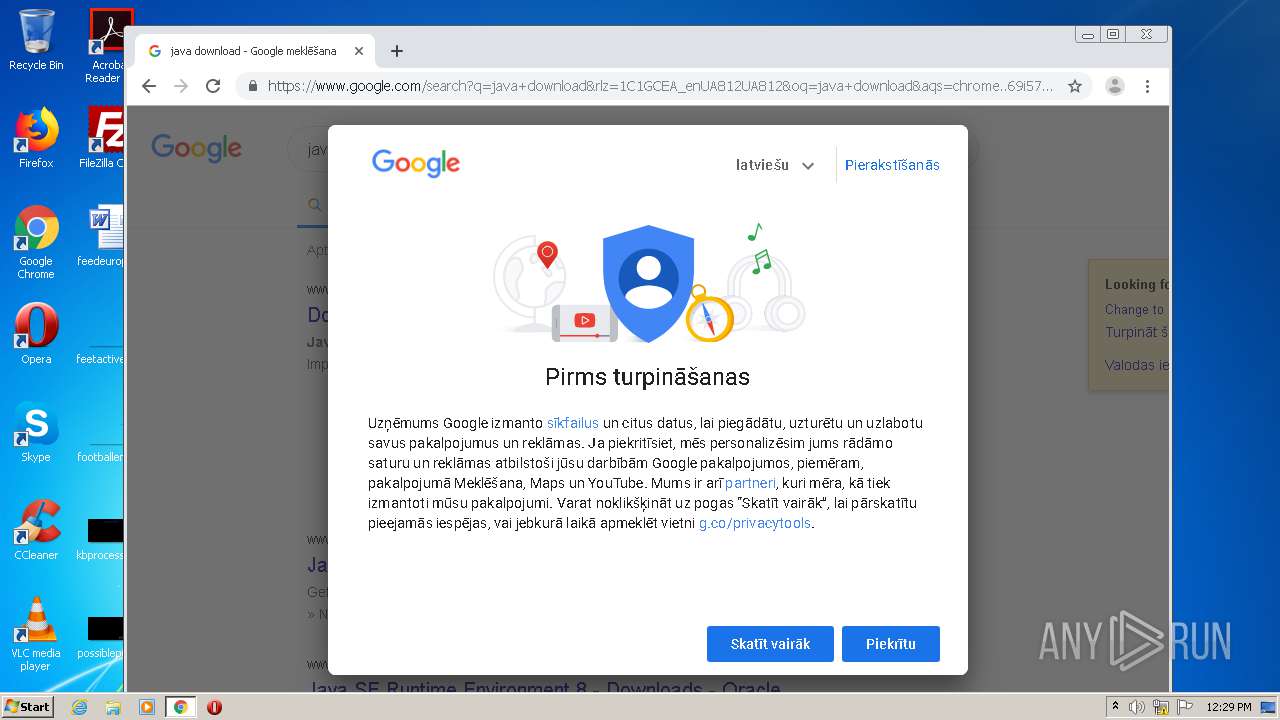
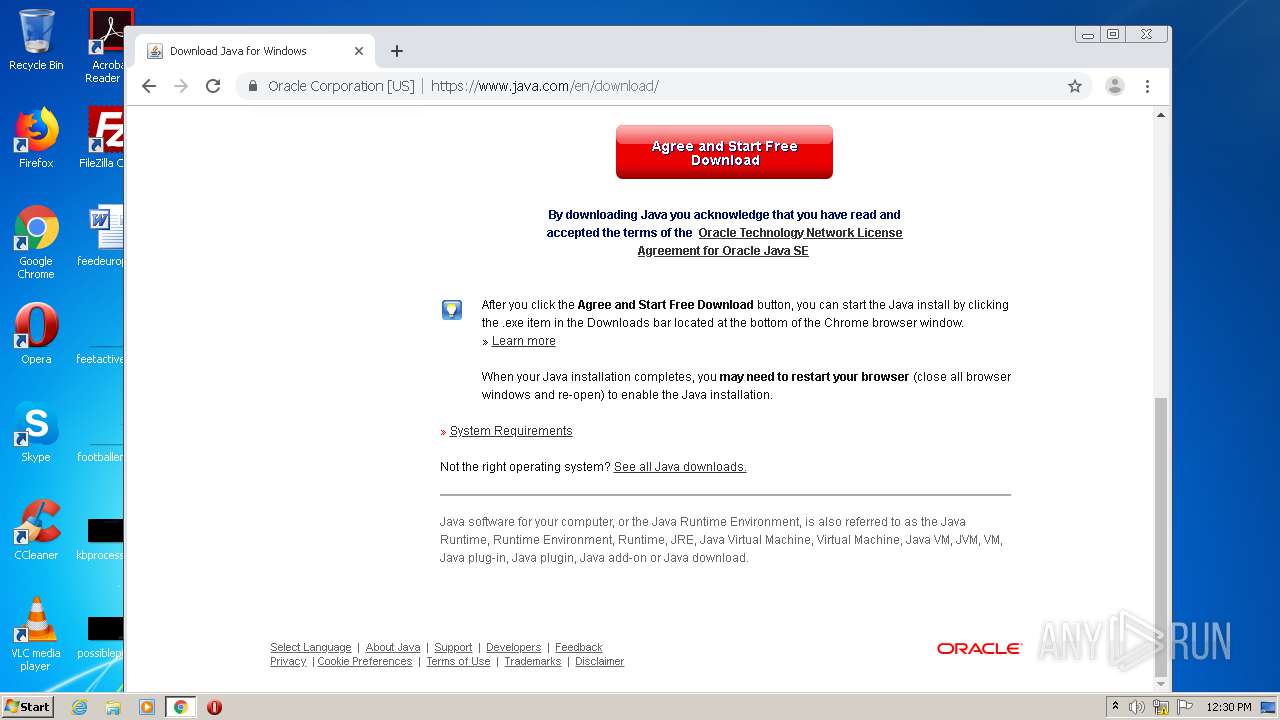
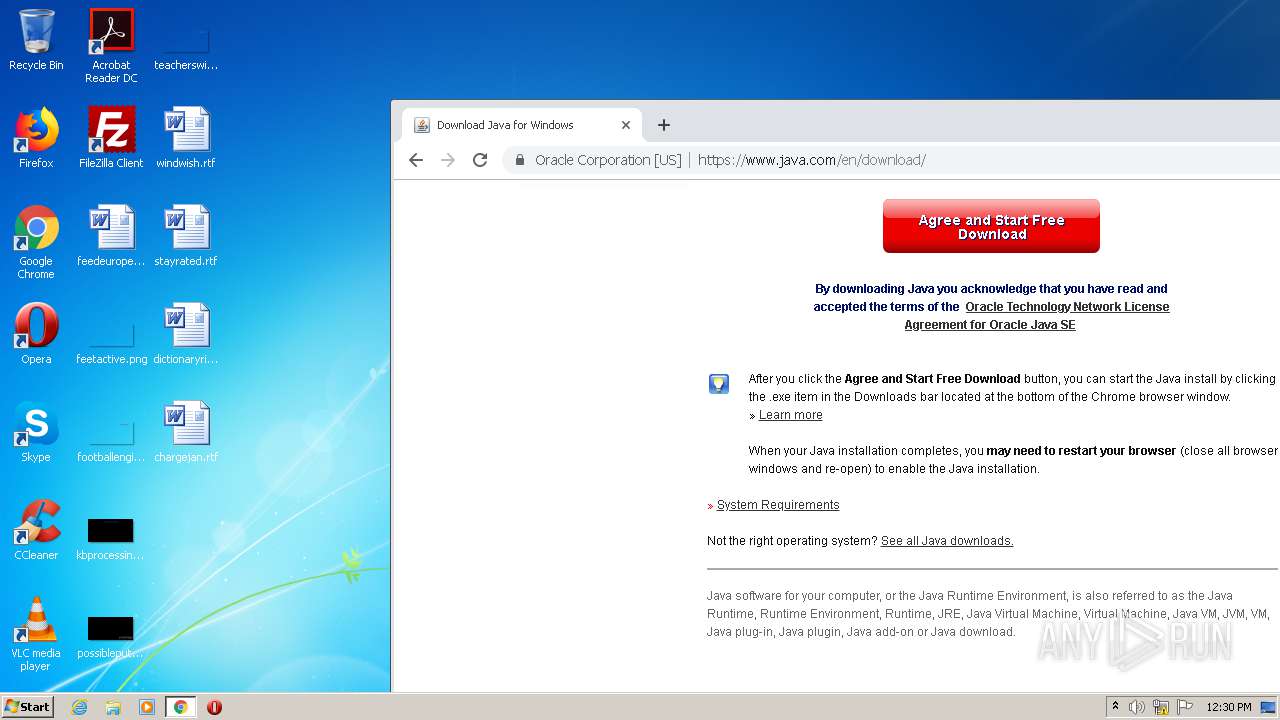
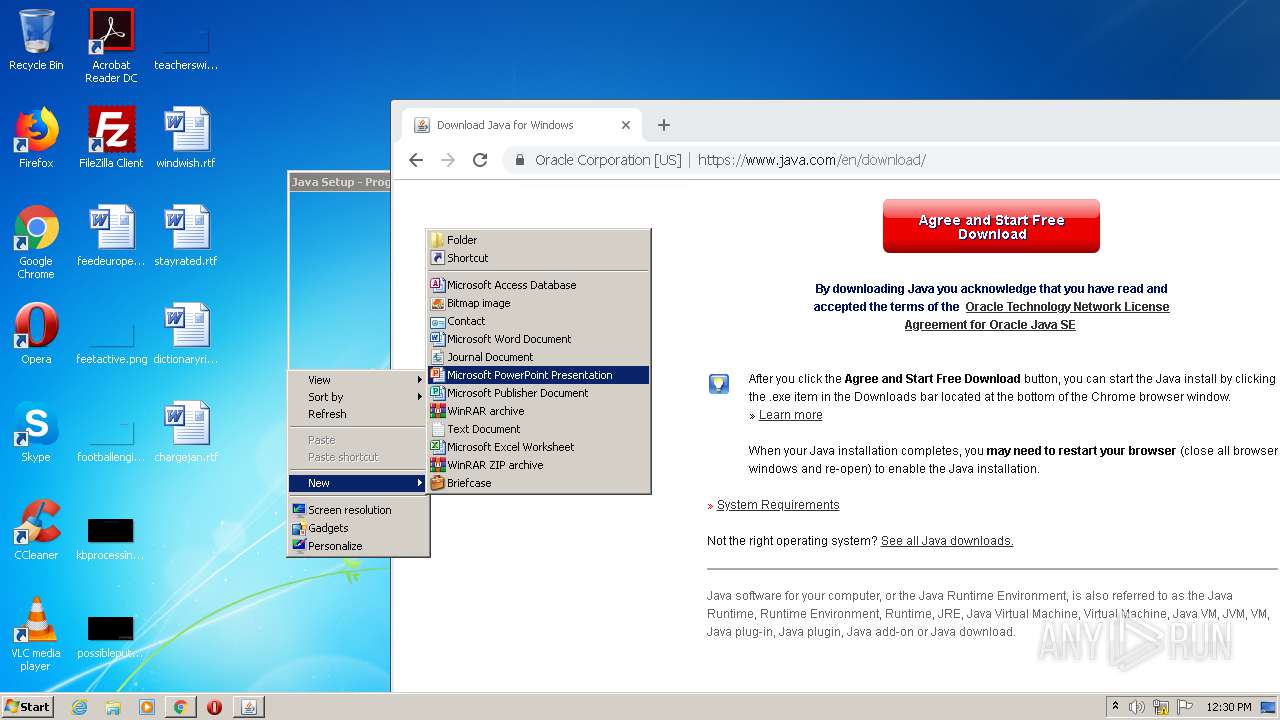
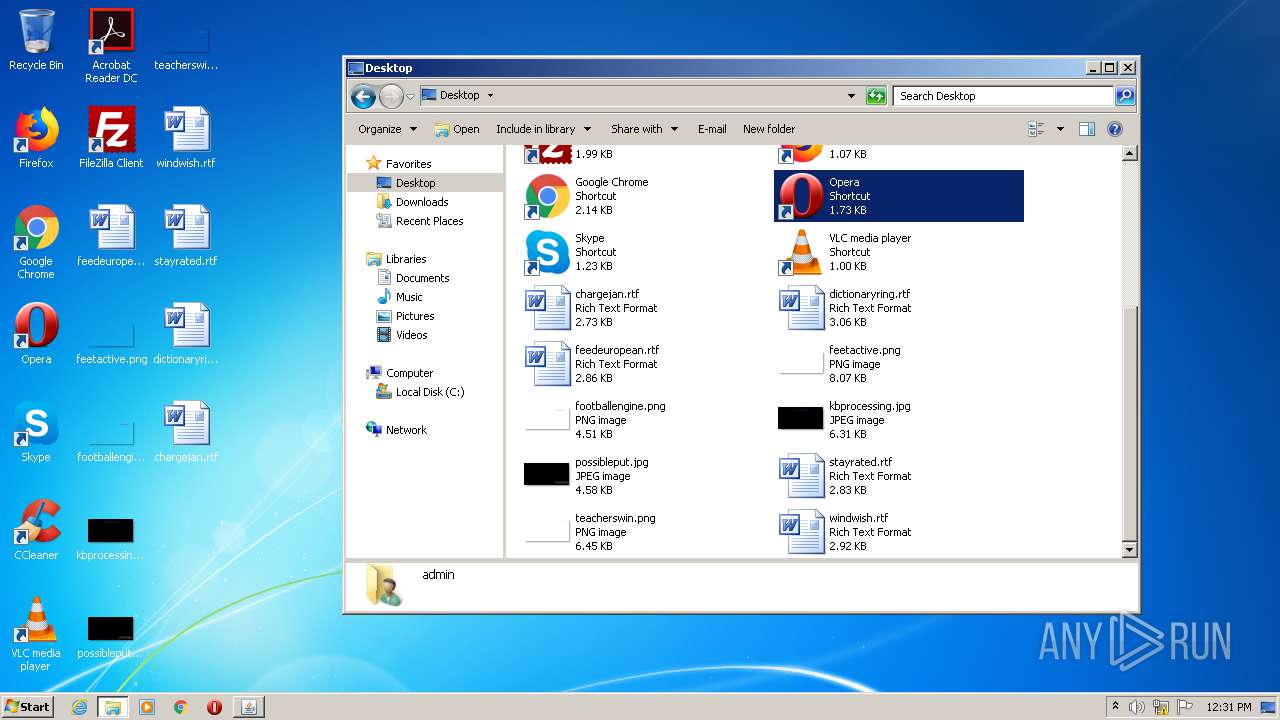
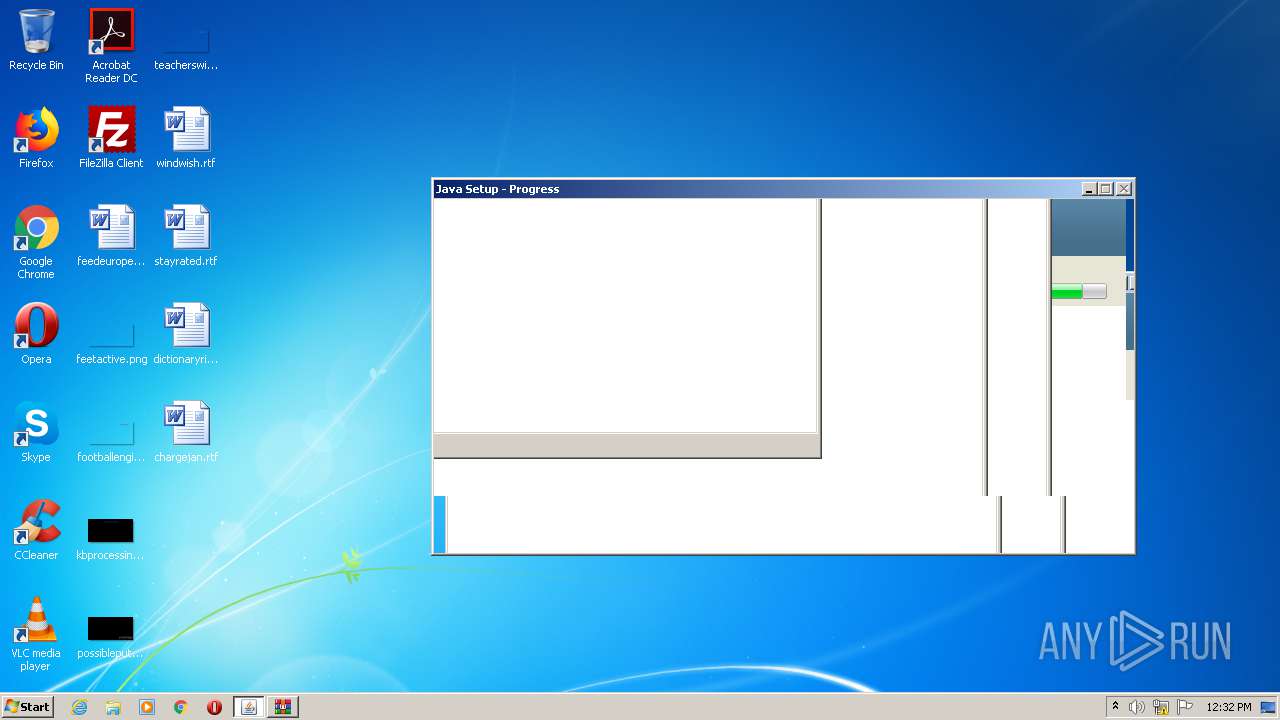
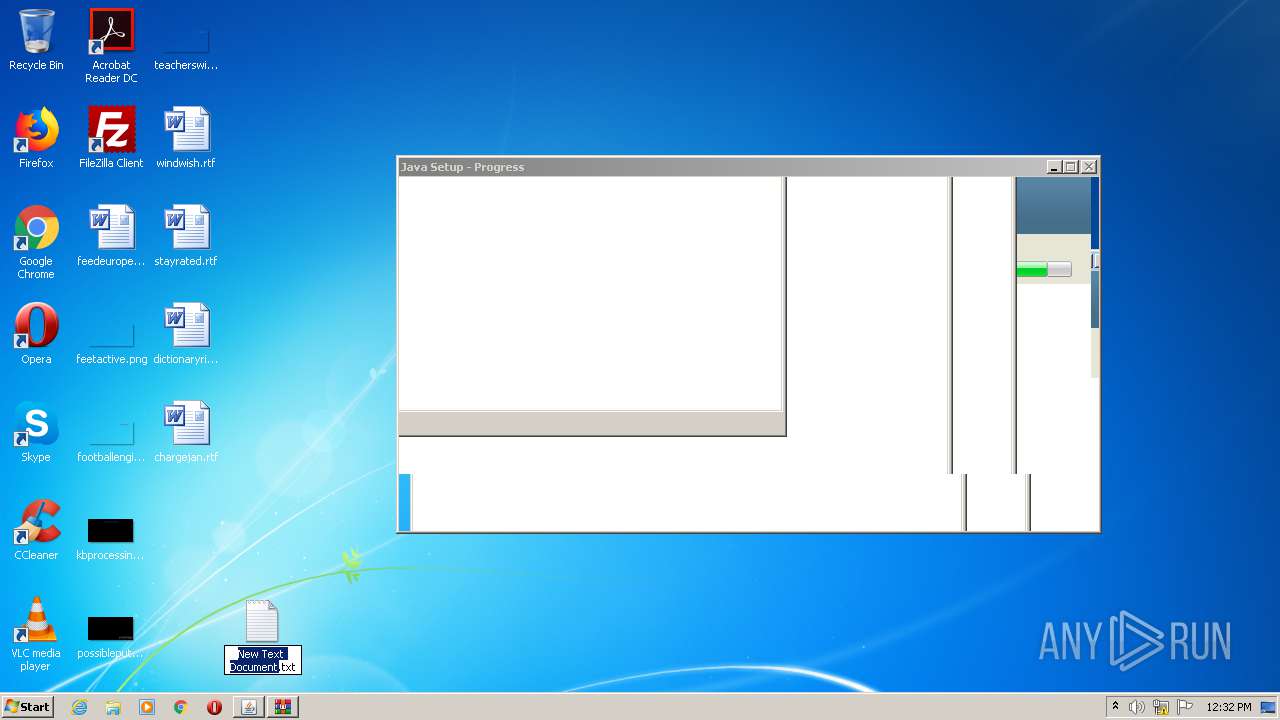
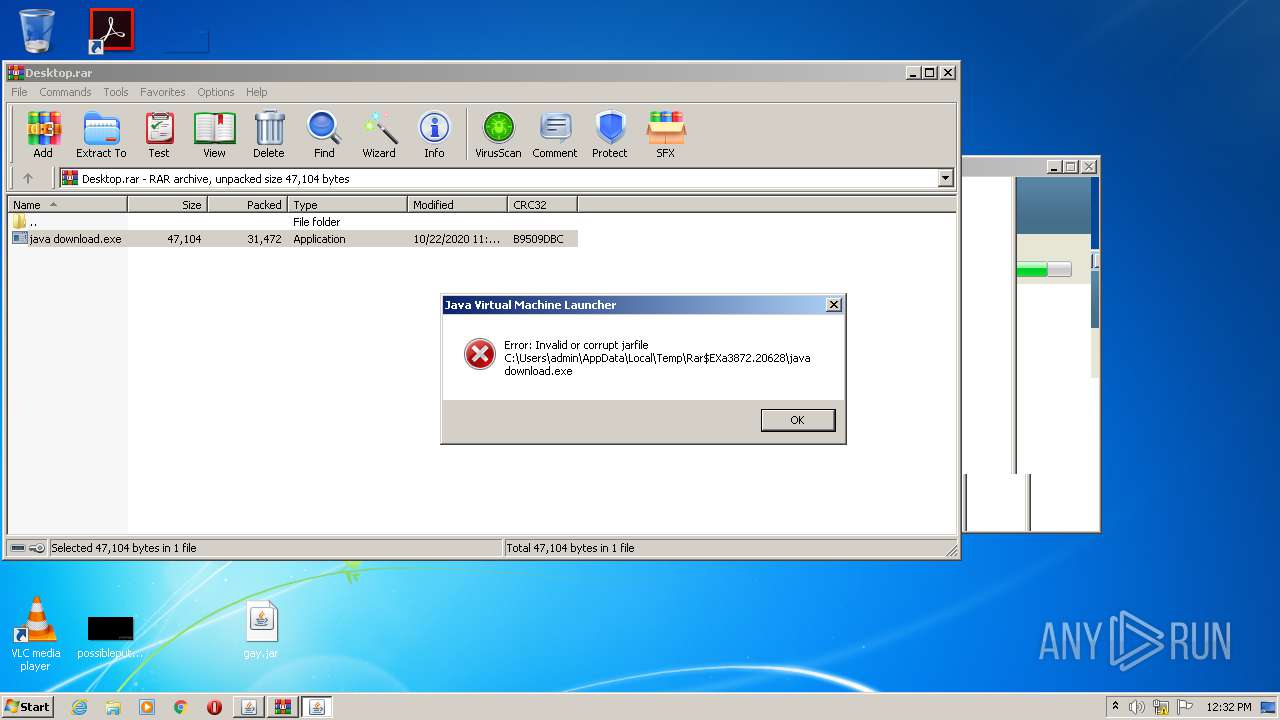
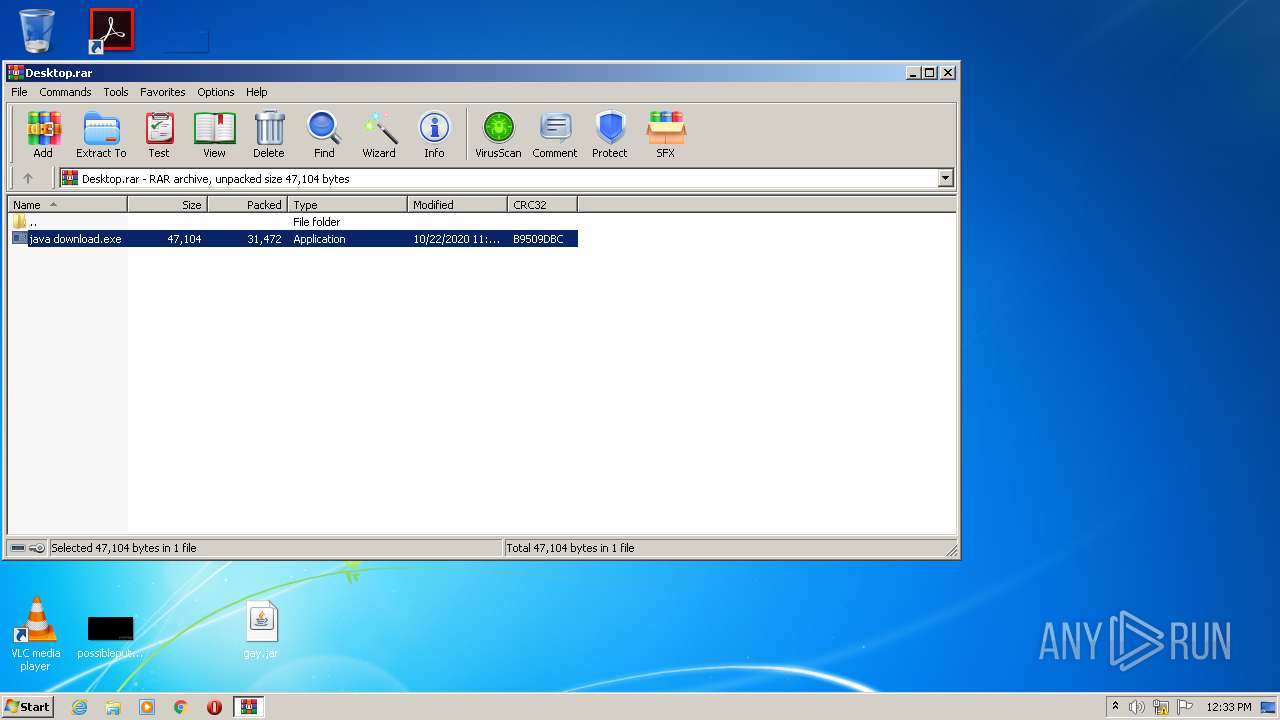
Manual execution by user
- chrome.exe (PID: 2636)
- explorer.exe (PID: 2792)
- WinRAR.exe (PID: 3872)
Reads the hosts file
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2636)
Reads settings of System Certificates
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2636)
Application launched itself
- chrome.exe (PID: 2636)
- msiexec.exe (PID: 1144)
Reads Internet Cache Settings
- chrome.exe (PID: 2636)
Creates files in the program directory
- msiexec.exe (PID: 1144)
Creates a software uninstall entry
- msiexec.exe (PID: 1144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
120
Monitored processes
64
Malicious processes
20
Suspicious processes
2
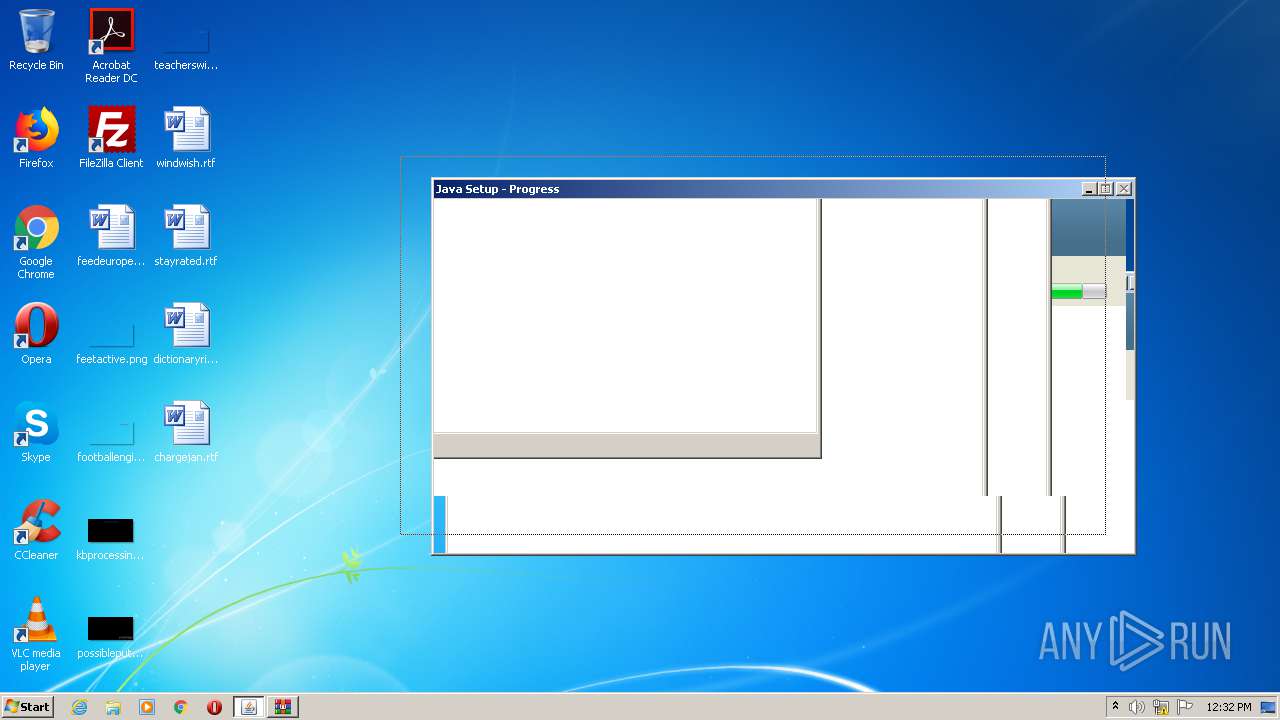
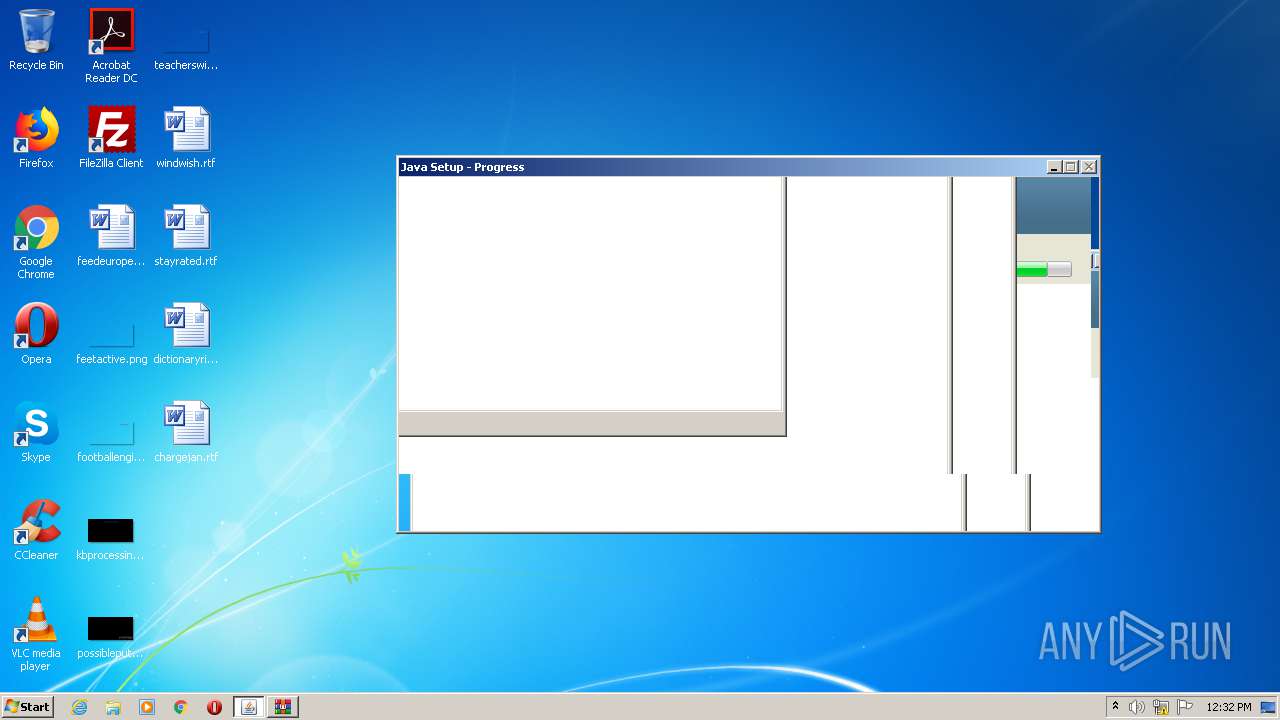
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Program Files\Java\jre1.8.0_271\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_271\lib/plugin.pack" "C:\Program Files\Java\jre1.8.0_271\lib/plugin.jar" | C:\Program Files\Java\jre1.8.0_271\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 612 | "C:\Program Files\Java\jre1.8.0_271\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_271\lib/charsets.pack" "C:\Program Files\Java\jre1.8.0_271\lib/charsets.jar" | C:\Program Files\Java\jre1.8.0_271\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 664 | C:\Windows\system32\MsiExec.exe -Embedding 245CFC57A4F58EB2CFDF3E29EF71D734 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5863717010234300919,2914546166498959318,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5982469795350962561 --mojo-platform-channel-handle=2548 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,5863717010234300919,2914546166498959318,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15468982614833787596 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,5863717010234300919,2914546166498959318,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10898708515507525769 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" -wait -fix -permissions -silent | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5863717010234300919,2914546166498959318,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=260062520228251637 --mojo-platform-channel-handle=3932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
43 736
Read events
2 846
Write events
28 248
Delete events
12 642
Modification events
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Desktop.rar | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
167
Suspicious files
114
Text files
660
Unknown types
40
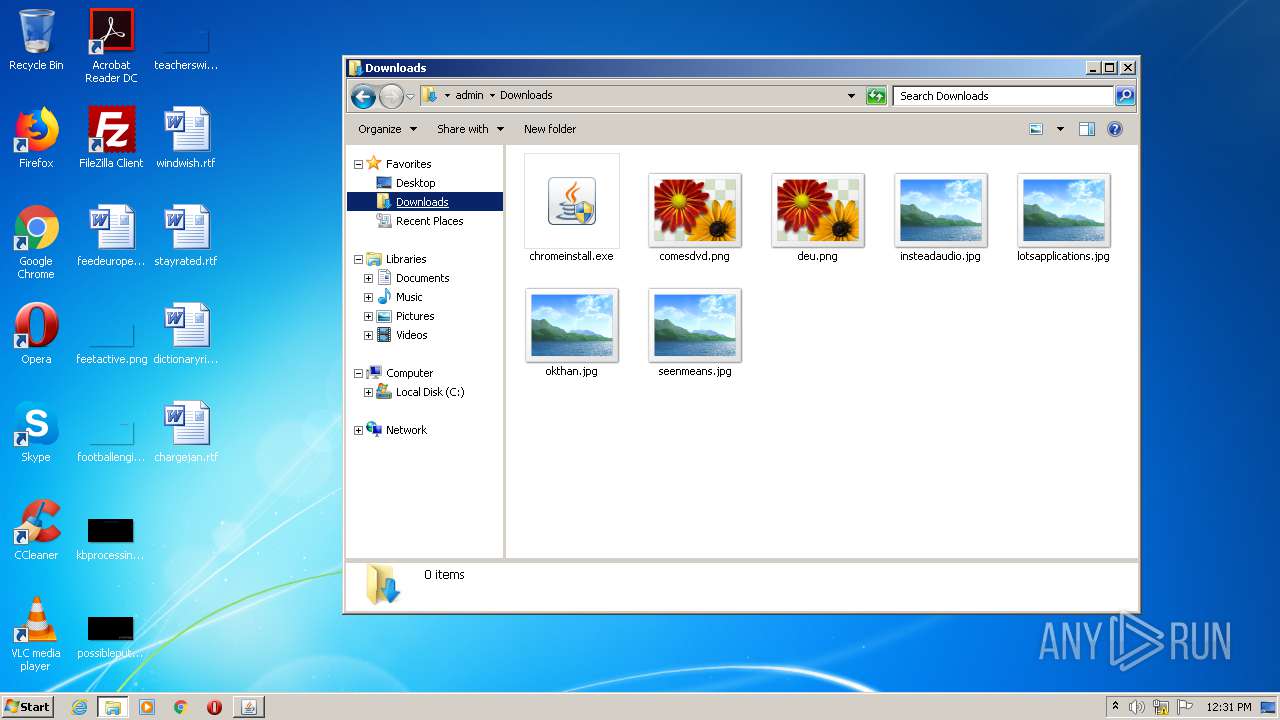
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F916D15-A4C.pma | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c1ca77f3-be59-4dcf-9900-25a10235ba0e.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 872 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2da7fd.TMP | text | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF2da935.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2da82b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
57
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2756 | chrome.exe | GET | 200 | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDM4QUFXaVZ5bThYeHlpdXd5bzU1RzRQUQ/8220.313.1.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=i8&mip=159.148.186.185&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1603366105&mv=m&mvi=3&pl=24&shardbypass=yes | LV | crx | 839 Kb | whitelisted |
2756 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDM4QUFXaVZ5bThYeHlpdXd5bzU1RzRQUQ/8220.313.1.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
2964 | chromeinstall.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2756 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2756 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 216.58.206.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 172.217.21.238:80 | ogs.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 172.217.21.206:443 | consent.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 159.148.69.142:80 | r3---sn-a5uoxu-gpme.gvt1.com | LATNET SERVISS Ltd. | LV | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
consent.google.com |
| shared |