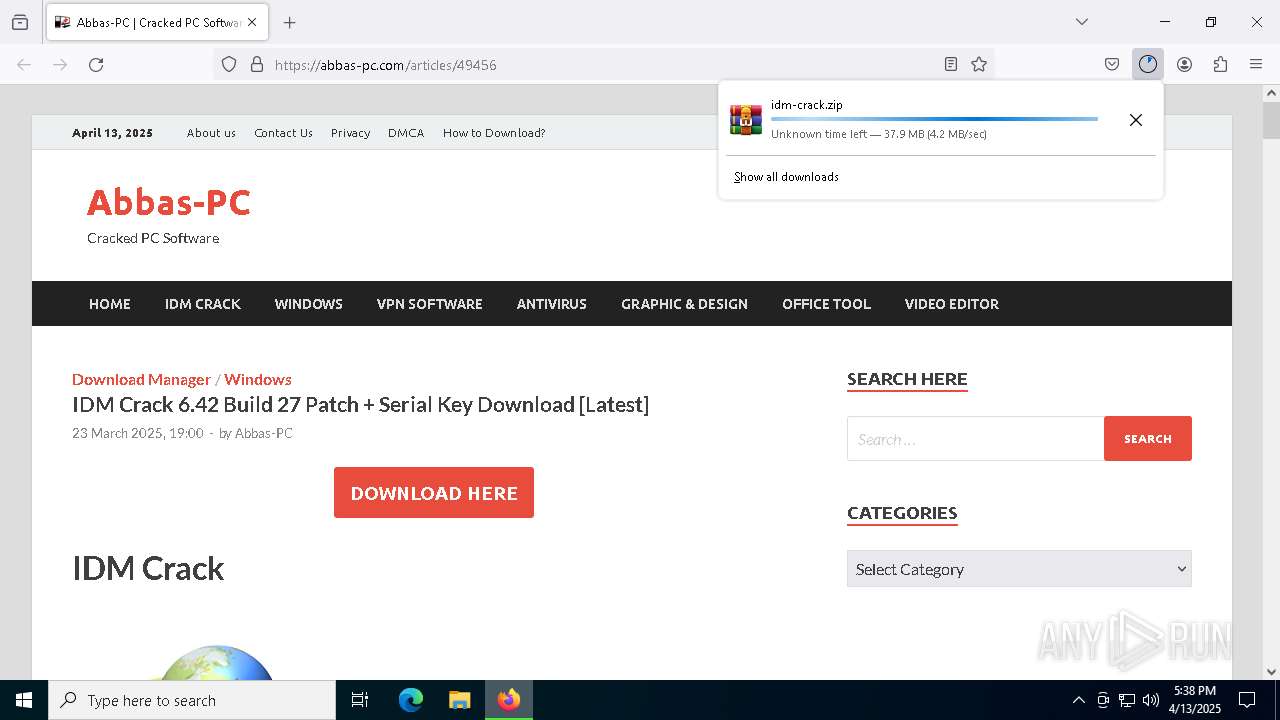
| URL: | https://abbas-pc.com/articles/49456 |
| Full analysis: | https://app.any.run/tasks/c48111b2-8d1e-4597-9be1-4c2198499c2f |
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2025, 17:38:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3095B9DC940E55574481D8FFF672439F |
| SHA1: | 2BCC00A946481F51842561F1B47BE68CC870B7FC |
| SHA256: | BEFC0E95AE3EF44E0887492E9709821423A8BD591F64BC2A5BC32704E836BD3B |
| SSDEEP: | 3:N84LouWK62T:2GgKX |
MALICIOUS
Accesses environment variables (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Opens an HTTP connection (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Creates internet connection object (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Sends HTTP request (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Gets %appdata% folder path (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Creates a new folder (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Checks whether a specified folder exists (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Gets path to any of the special folders (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Opens a text file (SCRIPT)
- Launcher.exe (PID: 7788)
Uses base64 encoding (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Bypass execution policy to execute commands
- powershell.exe (PID: 5744)
- powershell.exe (PID: 5800)
Changes powershell execution policy (Bypass)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Gets username (SCRIPT)
- setup_helper.exe (PID: 1096)
Uses Task Scheduler to run other applications
- setup_helper.exe (PID: 1096)
Uses sleep, probably for evasion detection (SCRIPT)
- setup_helper.exe (PID: 1096)
Deletes a file (SCRIPT)
- setup_helper.exe (PID: 1096)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- CfgHelper.exe (PID: 924)
Accesses the network adapter (Win32_NetworkAdapter) via WMI (SCRIPT)
- CfgHelper.exe (PID: 924)
SUSPICIOUS
Reads security settings of Internet Explorer
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Adds, changes, or deletes HTTP request header (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Adds/modifies Windows certificates
- Launcher.exe (PID: 7788)
Creates FileSystem object to access computer's file system (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- wscript.exe (PID: 3020)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Saves data to a binary file (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Creates a Folder object (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 1096)
The process executes VB scripts
- Launcher.exe (PID: 7788)
Executable content was dropped or overwritten
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 1096)
- WinRAR.exe (PID: 6416)
Runs shell command (SCRIPT)
- Launcher.exe (PID: 7788)
- wscript.exe (PID: 3020)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Writes binary data to a Stream object (SCRIPT)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Executes WMI query (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Accesses product unique identifier via WMI (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Gets full path of the running script (SCRIPT)
- setup_helper.exe (PID: 7316)
- CfgHelper.exe (PID: 924)
Checks whether a specific file exists (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Reads data from a binary Stream object (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Changes charset (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Sets XML DOM element text (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Creates XML DOM element (SCRIPT)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Base64-obfuscated command line is found
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
BASE64 encoded PowerShell command has been detected
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Starts POWERSHELL.EXE for commands execution
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
Accesses current user name via WMI (SCRIPT)
- setup_helper.exe (PID: 1096)
Gets computer name (SCRIPT)
- CfgHelper.exe (PID: 924)
Accesses computer name via WMI (SCRIPT)
- CfgHelper.exe (PID: 924)
Executes application which crashes
- CfgHelper.exe (PID: 924)
INFO
Application launched itself
- firefox.exe (PID: 7428)
- firefox.exe (PID: 7452)
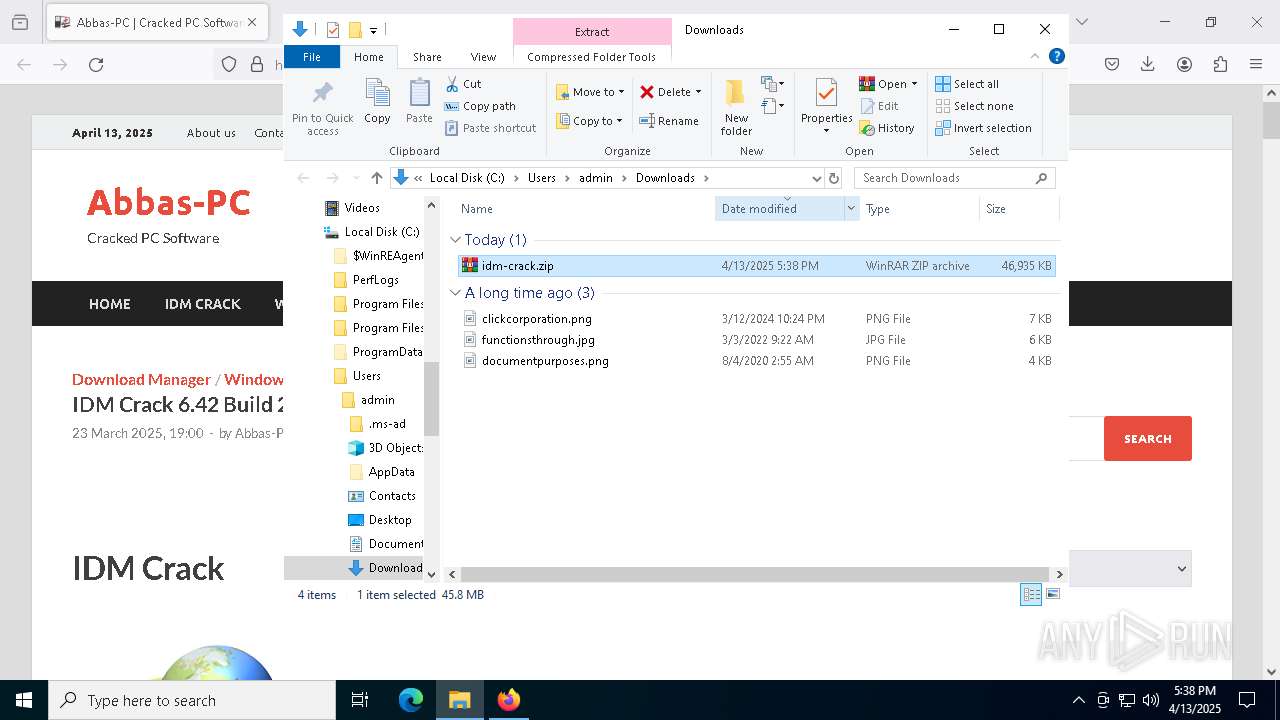
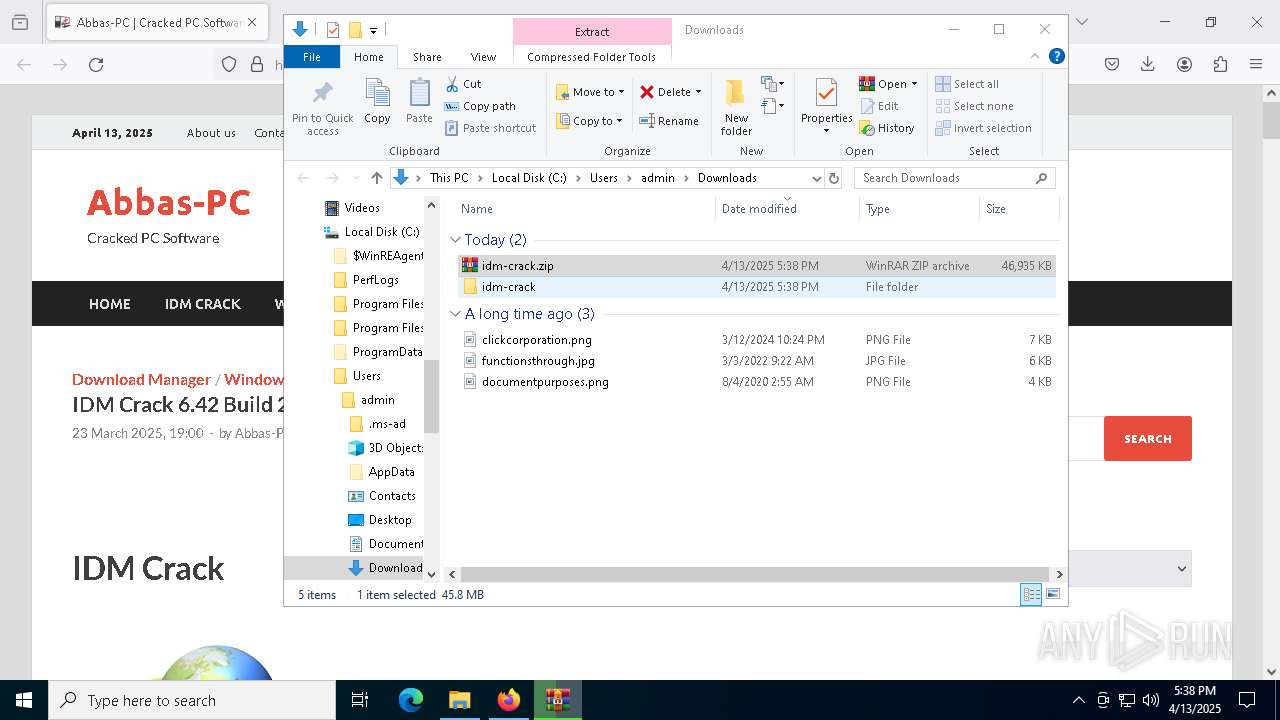
Autorun file from Downloads
- firefox.exe (PID: 7452)
The sample compiled with english language support
- WinRAR.exe (PID: 7488)
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 1096)
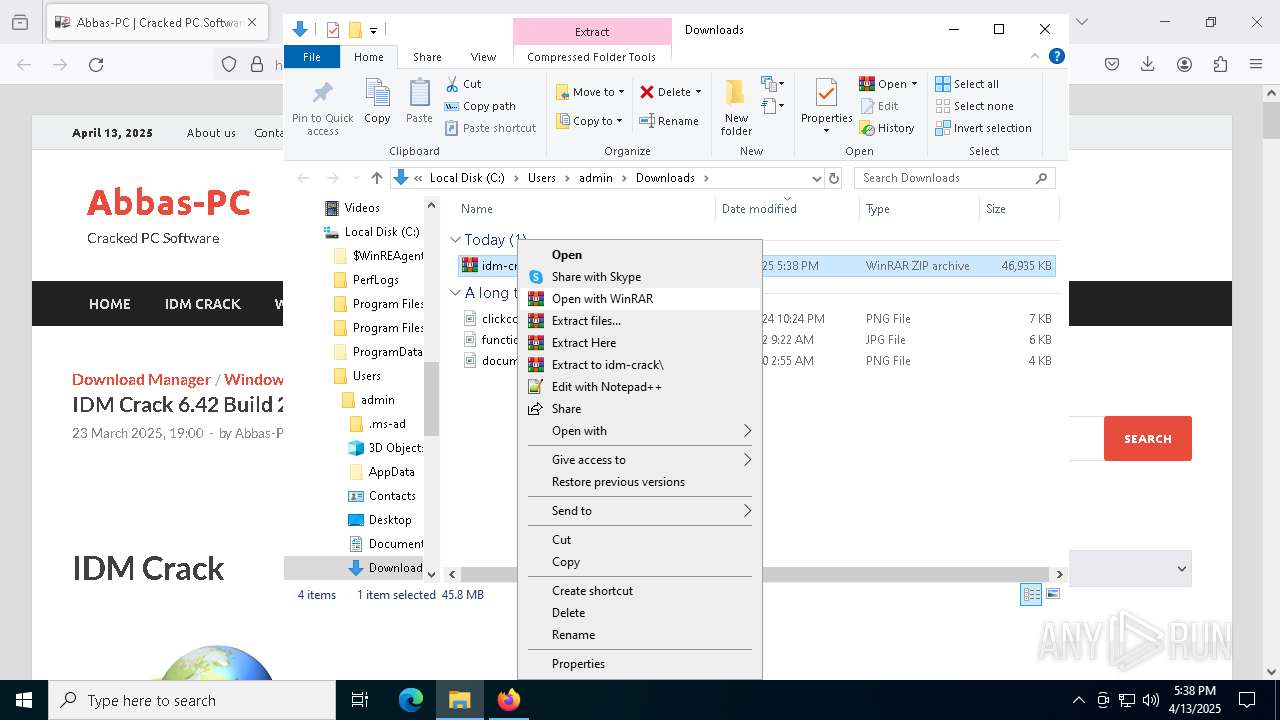
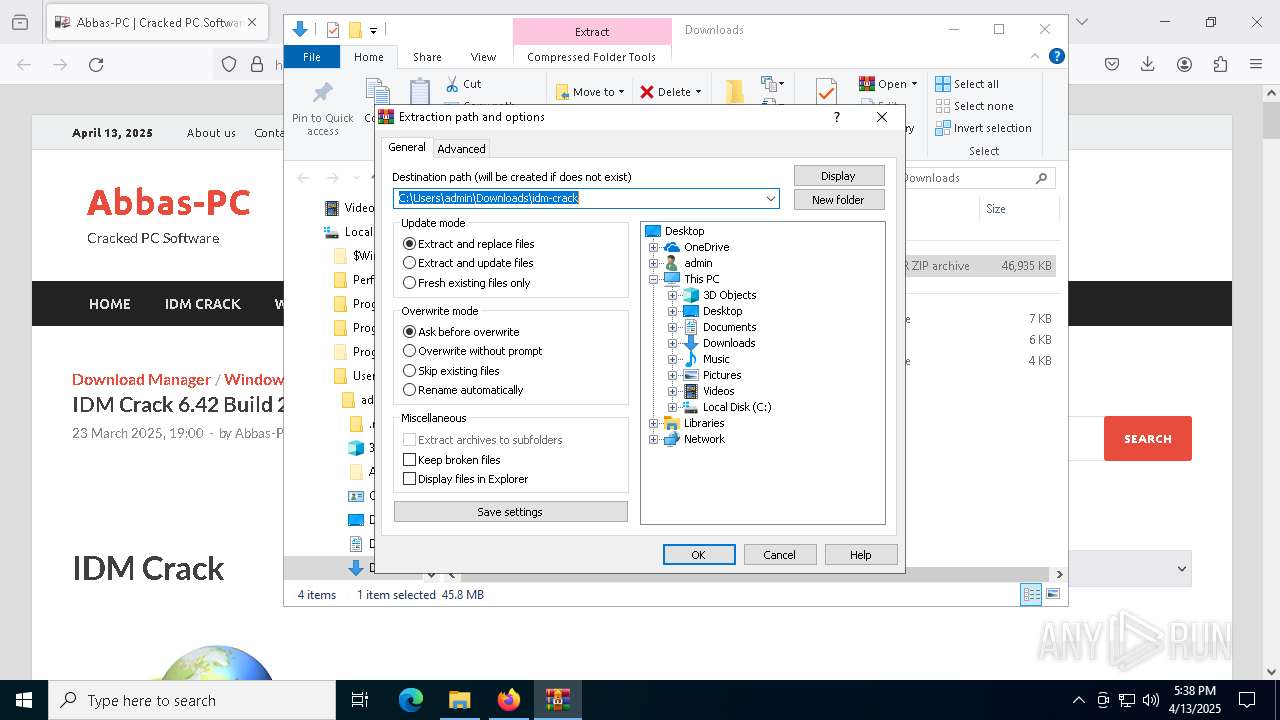
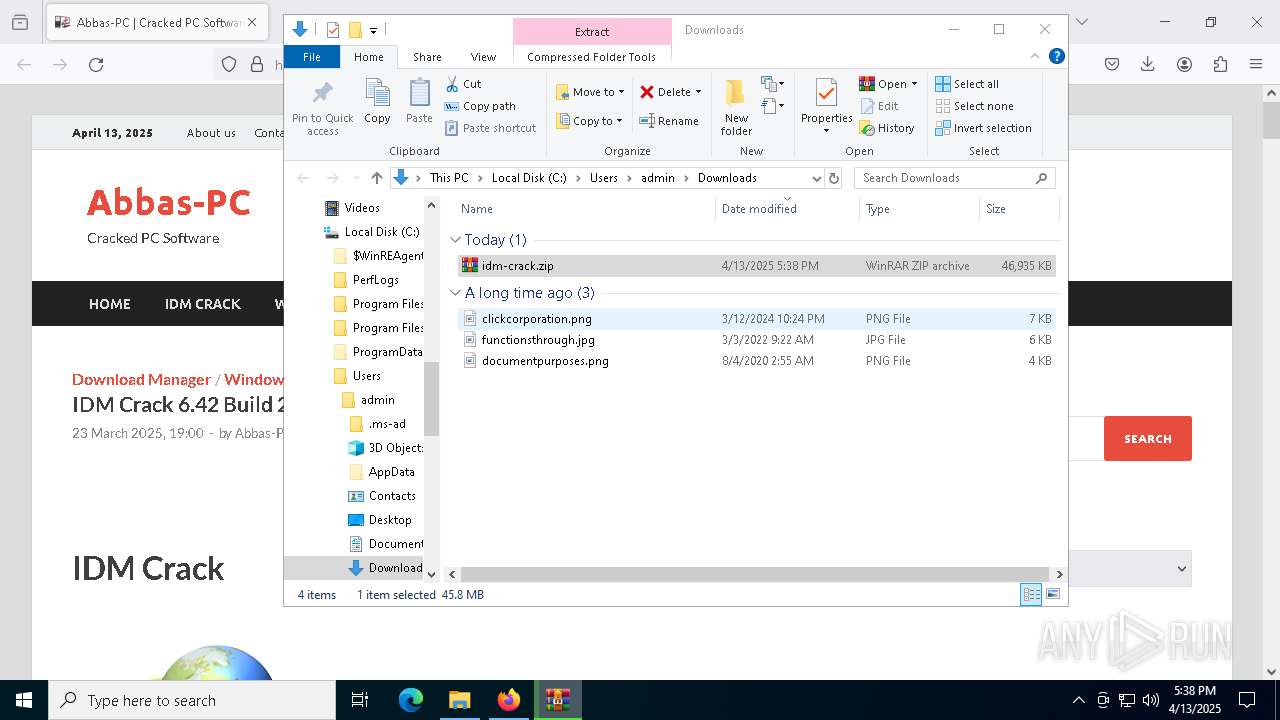
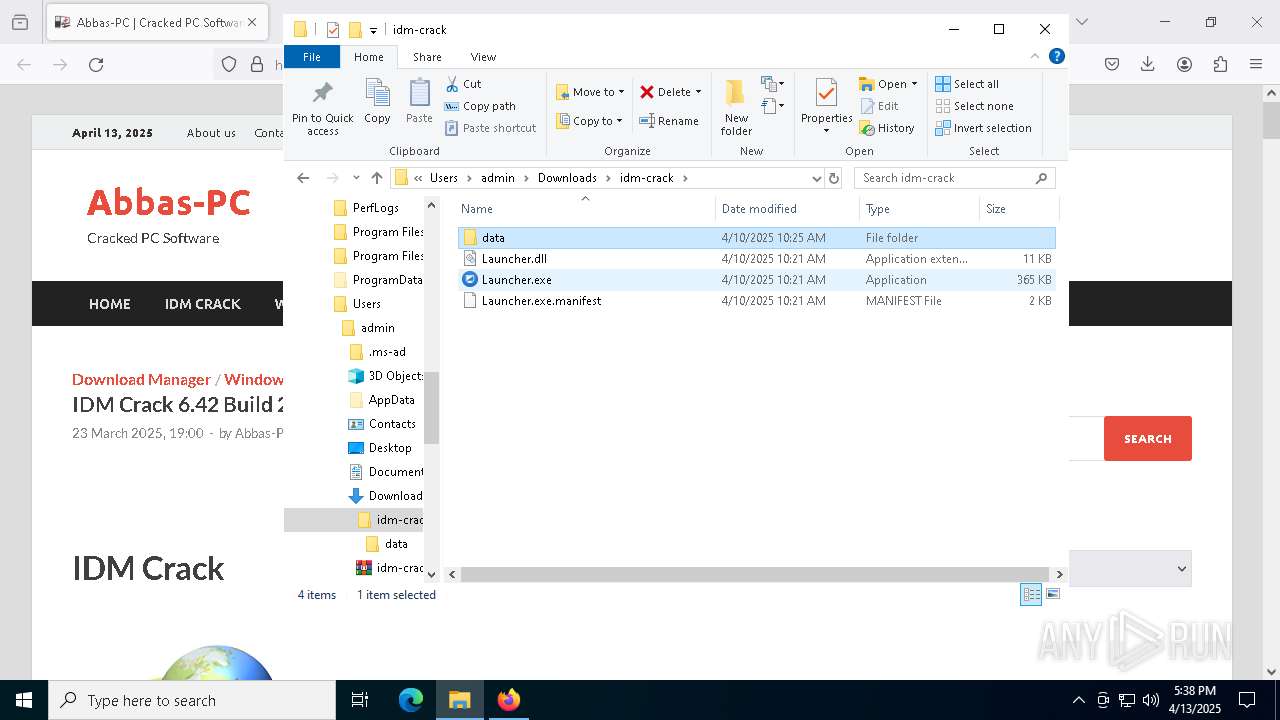
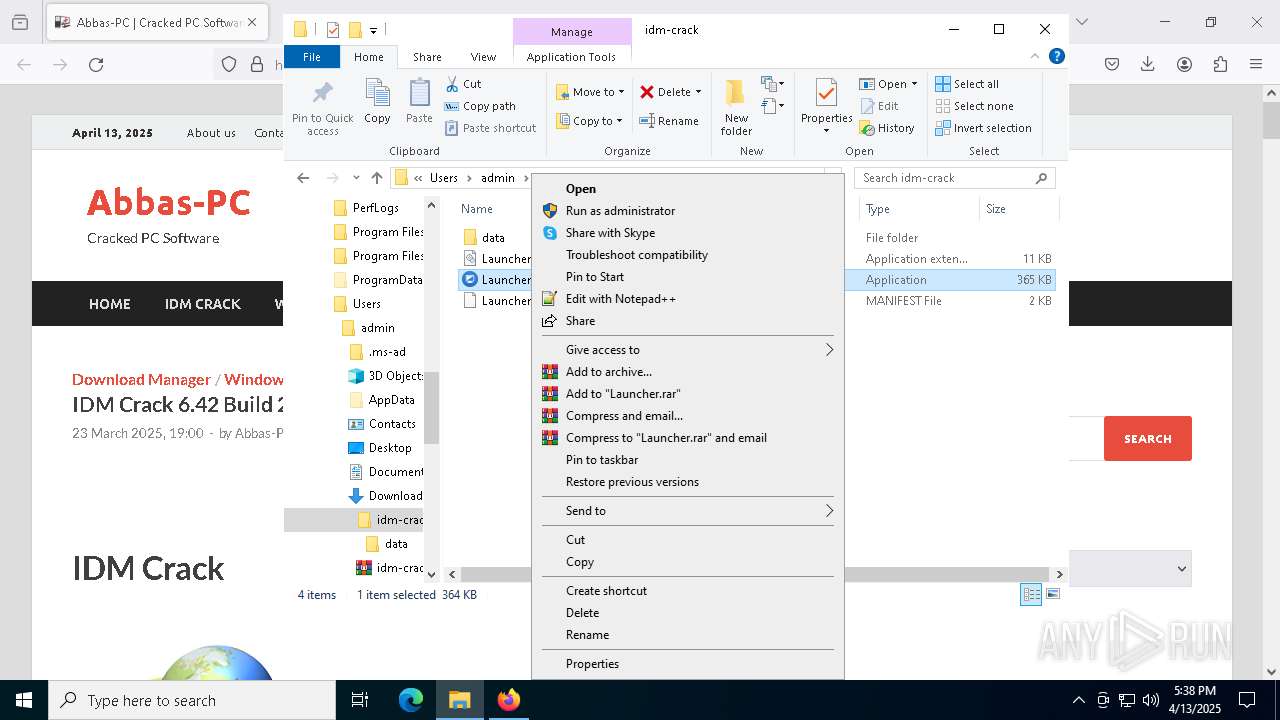
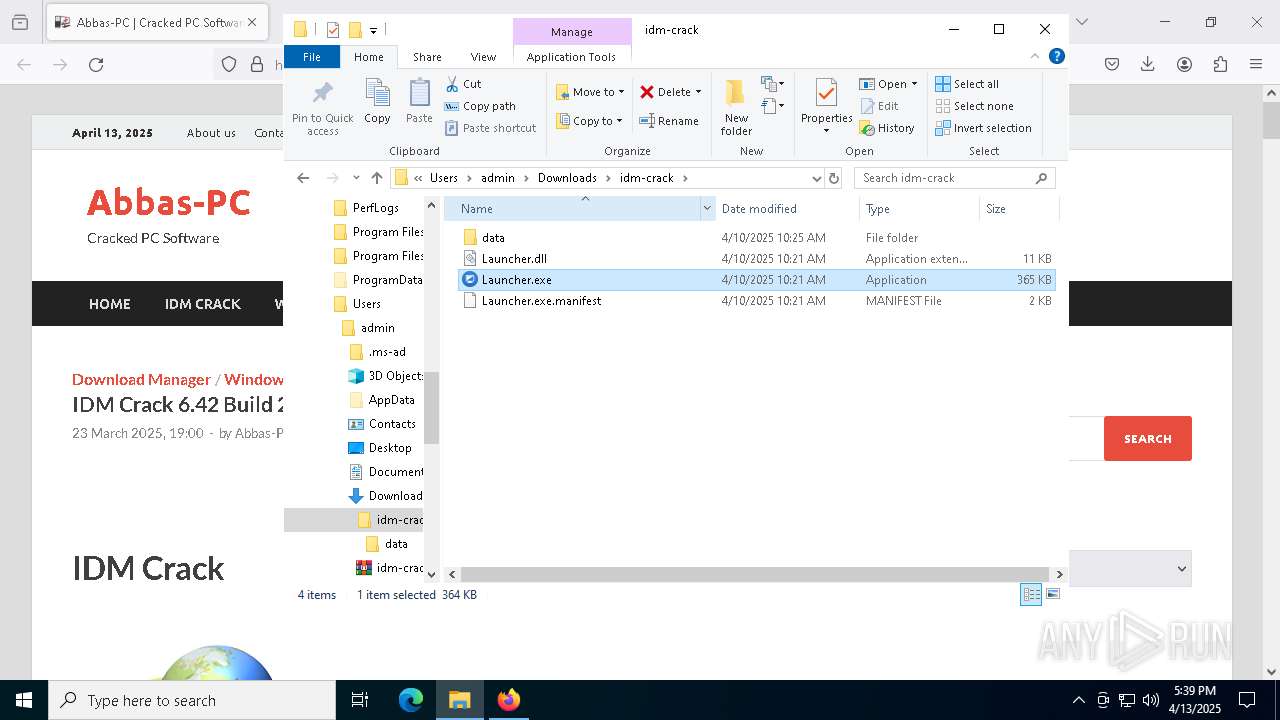
Manual execution by a user
- Launcher.exe (PID: 7788)
- WinRAR.exe (PID: 7488)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7488)
Checks supported languages
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
- WinRAR.exe (PID: 6416)
Reads the machine GUID from the registry
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
- WinRAR.exe (PID: 6416)
Reads the software policy settings
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 5800)
- CfgHelper.exe (PID: 924)
- slui.exe (PID: 6036)
- slui.exe (PID: 840)
Reads the computer name
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
- WinRAR.exe (PID: 6416)
Creates files or folders in the user directory
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- WerFault.exe (PID: 6264)
Process checks computer location settings
- Launcher.exe (PID: 7788)
- setup_helper.exe (PID: 7316)
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 5800)
Create files in a temporary directory
- powershell.exe (PID: 5744)
- powershell.exe (PID: 5800)
Reads security settings of Internet Explorer
- powershell.exe (PID: 5744)
- powershell.exe (PID: 5800)
Creates files in the program directory
- setup_helper.exe (PID: 1096)
- CfgHelper.exe (PID: 924)
- WinRAR.exe (PID: 6416)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5800)
Checks proxy server information
- slui.exe (PID: 840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
167
Monitored processes
31
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "C:\ProgramData\app_config\CfgHelper.exe" | C:\ProgramData\app_config\CfgHelper.exe | setup_helper.exe | ||||||||||||
User: admin Company: Adersoft Integrity Level: HIGH Description: VbsEdit Script Launcher Exit code: 3221225477 Version: 9.9.13.7 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Roaming\app_config\setup_helper.exe" | C:\Users\admin\AppData\Roaming\app_config\setup_helper.exe | powershell.exe | ||||||||||||
User: admin Company: Adersoft Integrity Level: HIGH Description: VbsEdit Script Launcher Exit code: 0 Version: 9.9.13.7 Modules
| |||||||||||||||
| 1748 | "C:\Windows\System32\schtasks.exe" /create /tn "CfgMgr" /tr "C:\ProgramData\app_config\CfgMgr.exe" /sc minute /mo 5 /RL HIGHEST /ru admin /f | C:\Windows\SysWOW64\schtasks.exe | — | setup_helper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\run_helper.vbs" | C:\Windows\SysWOW64\wscript.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4608 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5212 -childID 4 -isForBrowser -prefsHandle 5040 -prefMapHandle 5204 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1108 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {18051db1-c6c1-4659-9aab-7ce980b82c83} 7452 "\\.\pipe\gecko-crash-server-pipe.7452" 1c2bf4bcd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4988 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5432 -childID 6 -isForBrowser -prefsHandle 5352 -prefMapHandle 5356 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1108 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {41a26462-d440-4c95-8735-d724d8f69d71} 7452 "\\.\pipe\gecko-crash-server-pipe.7452" 1c2c0352850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5544 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5340 -childID 5 -isForBrowser -prefsHandle 5260 -prefMapHandle 5264 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1108 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {622bebcb-3407-4e9b-9f3e-48235957ccbe} 7452 "\\.\pipe\gecko-crash-server-pipe.7452" 1c2c0352690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
51 128
Read events
51 065
Write events
43
Delete events
20
Modification events
| (PID) Process: | (7452) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (7488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
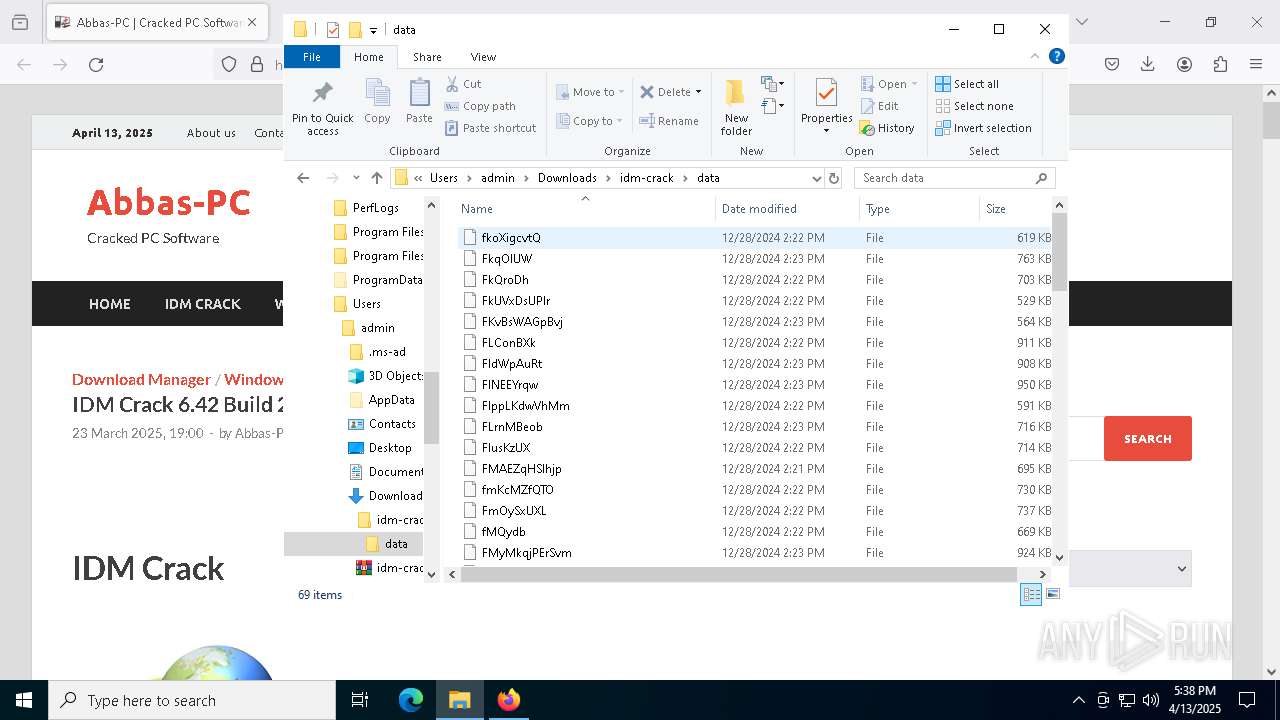
Executable files
8
Suspicious files
266
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7452 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:483D3EC4CEA0627DB43BF448D0D1E73C | SHA256:CA423B9C6A8B670B2441E52708B0EA99BFABD1827F52325A9597482D3D3675CD | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
105
DNS requests
129
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7452 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
7452 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7452 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7452 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7452 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7452 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7452 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.174:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7452 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7452 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.174:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7452 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
7452 | firefox.exe | 104.21.32.1:443 | abbas-pc.com | — | — | unknown |
7452 | firefox.exe | 142.250.185.106:443 | safebrowsing.googleapis.com | — | — | whitelisted |
7452 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | whitelisted |
7452 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
abbas-pc.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |