| File name: | main.exe |
| Full analysis: | https://app.any.run/tasks/601f83bc-a4f2-48bc-953c-731b704cbbc9 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 06:06:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 80AE0E96E4E057CFE872955F9D86DFF0 |
| SHA1: | 63EB9F6379C98BA0ABB36AFF2B99D186327D7A8C |
| SHA256: | BEED4D442FD269463F58FED10AA54CDBC7BD93A1337F0F02F1C63F1F00D4BEF1 |
| SSDEEP: | 98304:IjIpn/rHoG3Auv9TQnAqr/E4hpOPdJ7c9NBf9sXlXEt5GrXTCUXToWAhDGXz+sW6:614id |
MALICIOUS
Adds path to the Windows Defender exclusion list
- main.exe (PID: 6876)
Changes powershell execution policy (Bypass)
- main.exe (PID: 6876)
Changes Windows Defender settings
- main.exe (PID: 6876)
Adds process to the Windows Defender exclusion list
- main.exe (PID: 6876)
Bypass execution policy to execute commands
- powershell.exe (PID: 6004)
- powershell.exe (PID: 5692)
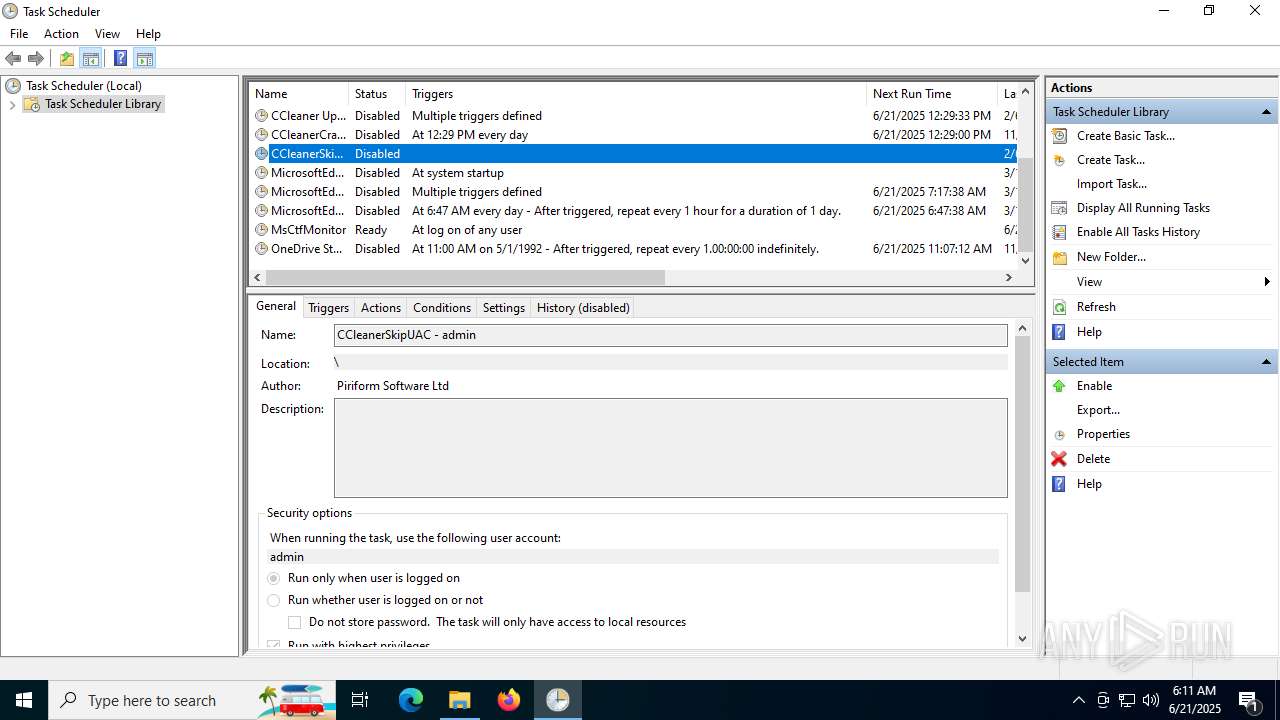
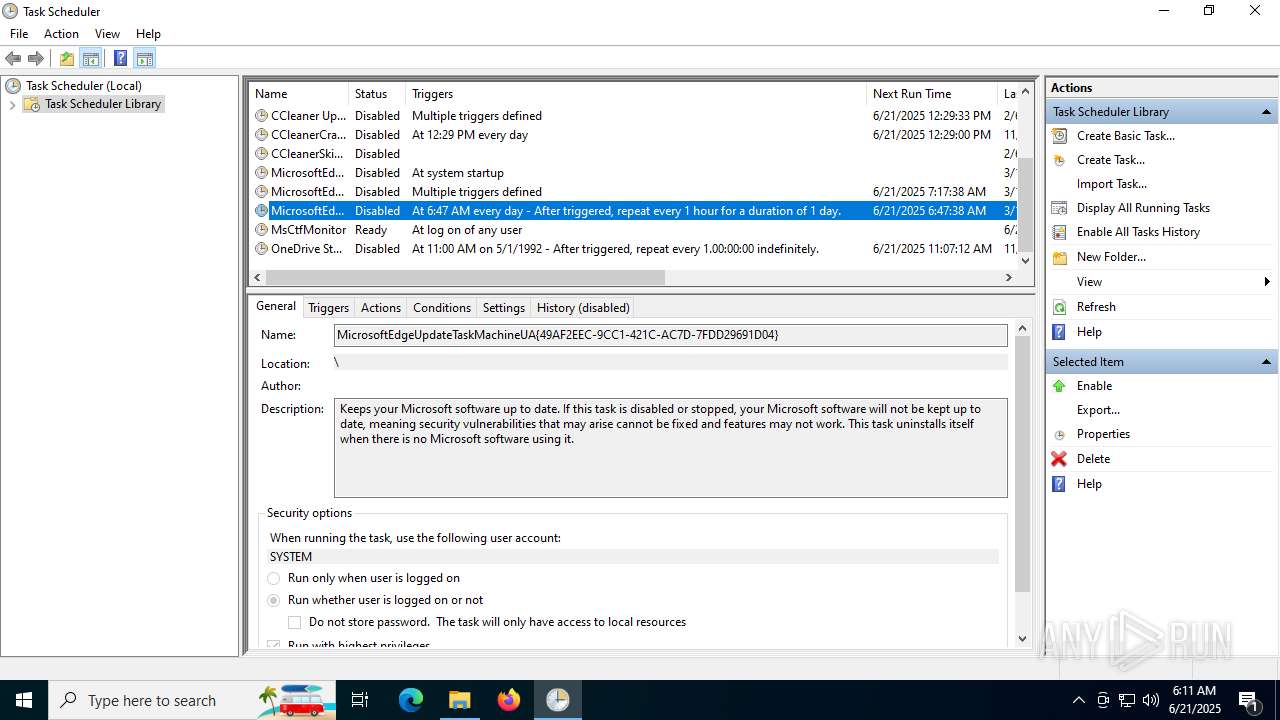
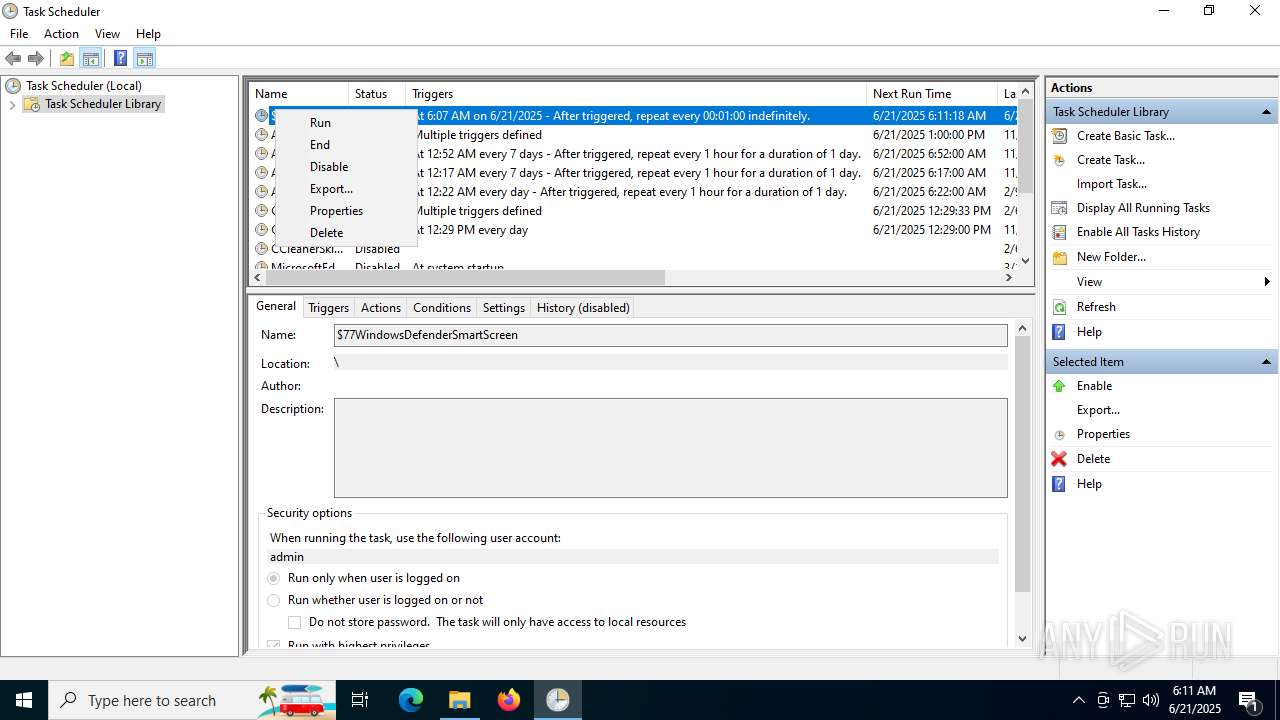
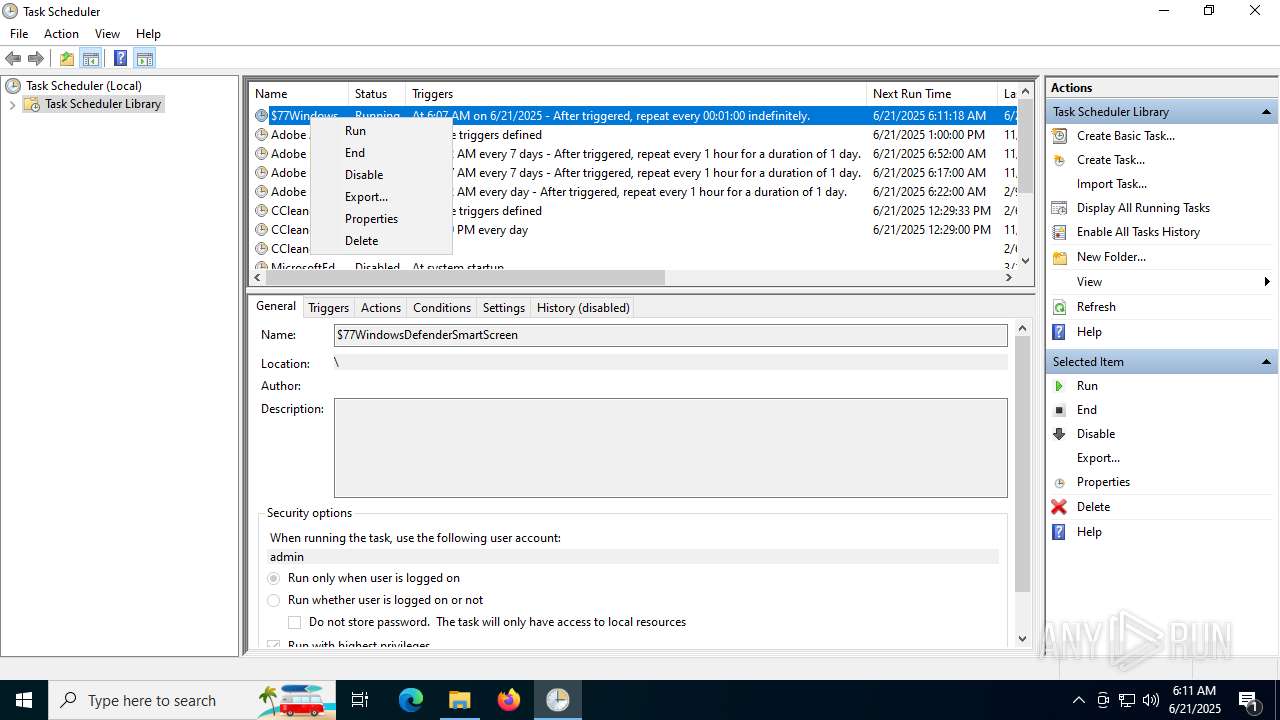
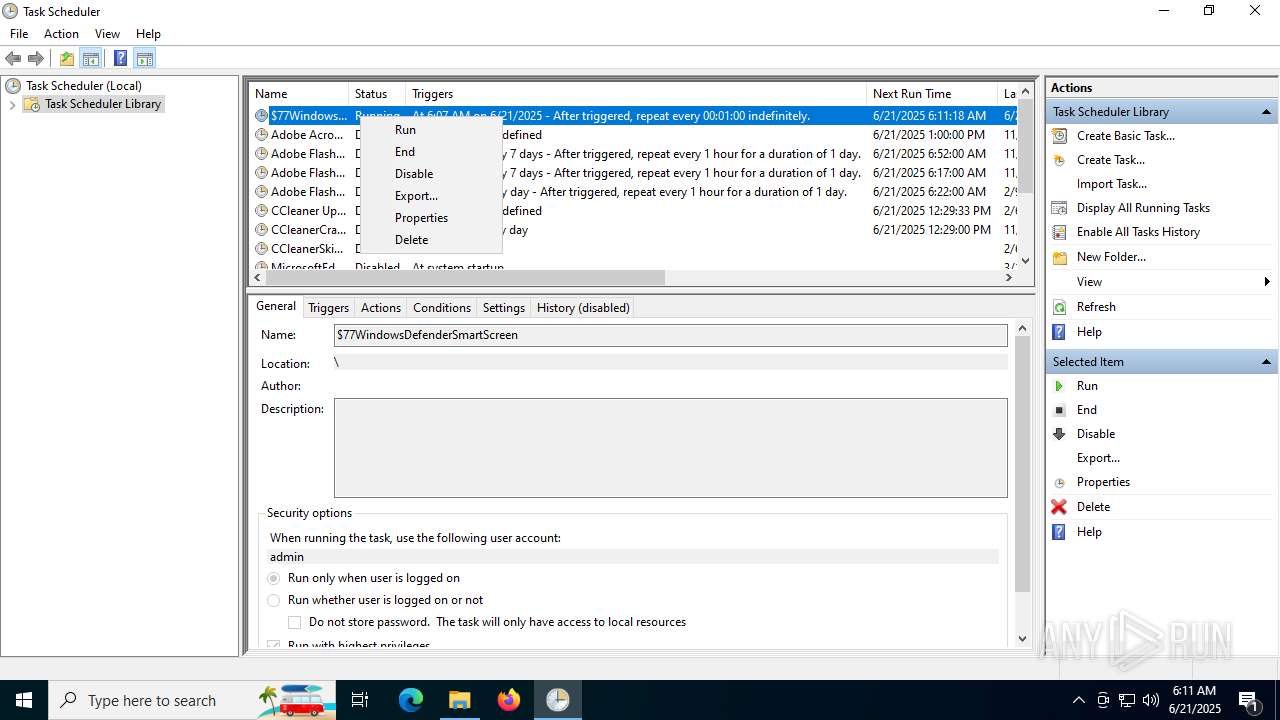
UAC/LUA settings modification
- $77smartscreen.exe (PID: 6656)
- $77smartscreen.exe (PID: 812)
Known privilege escalation attack
- dllhost.exe (PID: 6140)
SUSPICIOUS
Reads security settings of Internet Explorer
- main.exe (PID: 6536)
- main.exe (PID: 6876)
- ShellExperienceHost.exe (PID: 5628)
Runs shell command (SCRIPT)
- mshta.exe (PID: 6388)
- mshta.exe (PID: 5904)
The executable file from the user directory is run by the CMD process
- main.exe (PID: 6876)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 6388)
Reads the date of Windows installation
- main.exe (PID: 6876)
- main.exe (PID: 6536)
Starts POWERSHELL.EXE for commands execution
- main.exe (PID: 6876)
Script adds exclusion path to Windows Defender
- main.exe (PID: 6876)
Script adds exclusion process to Windows Defender
- main.exe (PID: 6876)
Uses TASKKILL.EXE to kill process
- mshta.exe (PID: 5904)
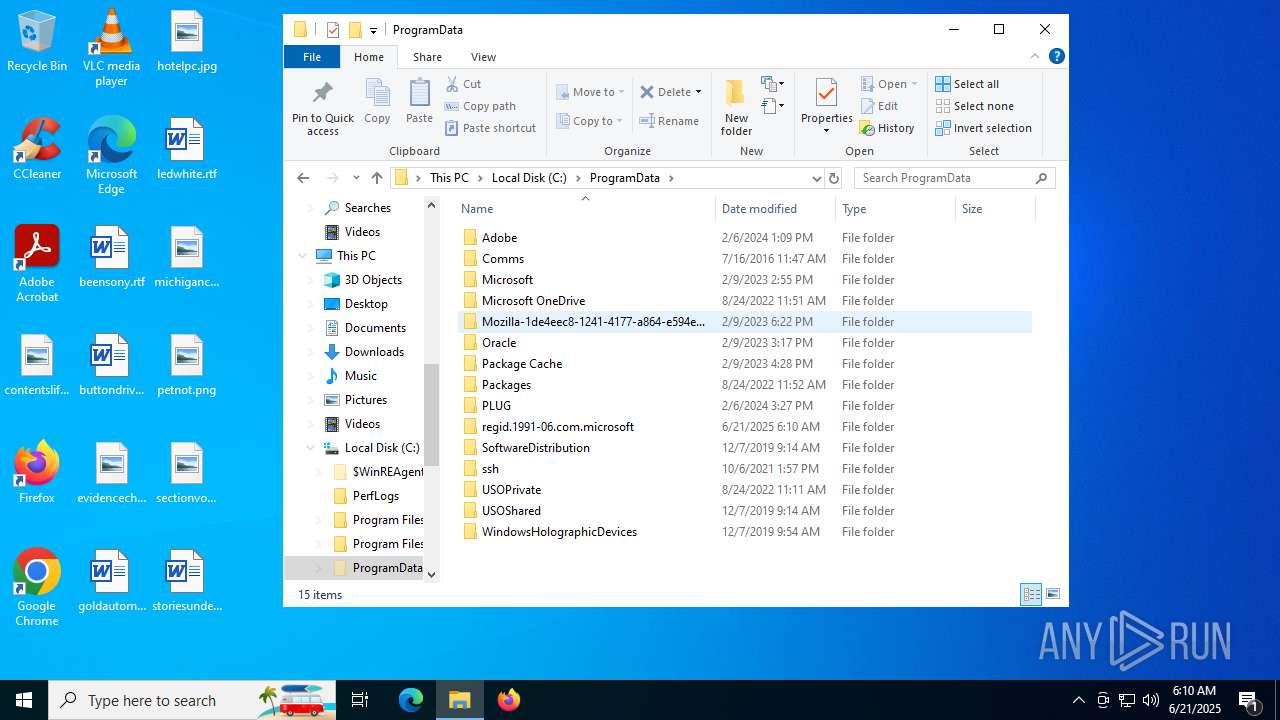
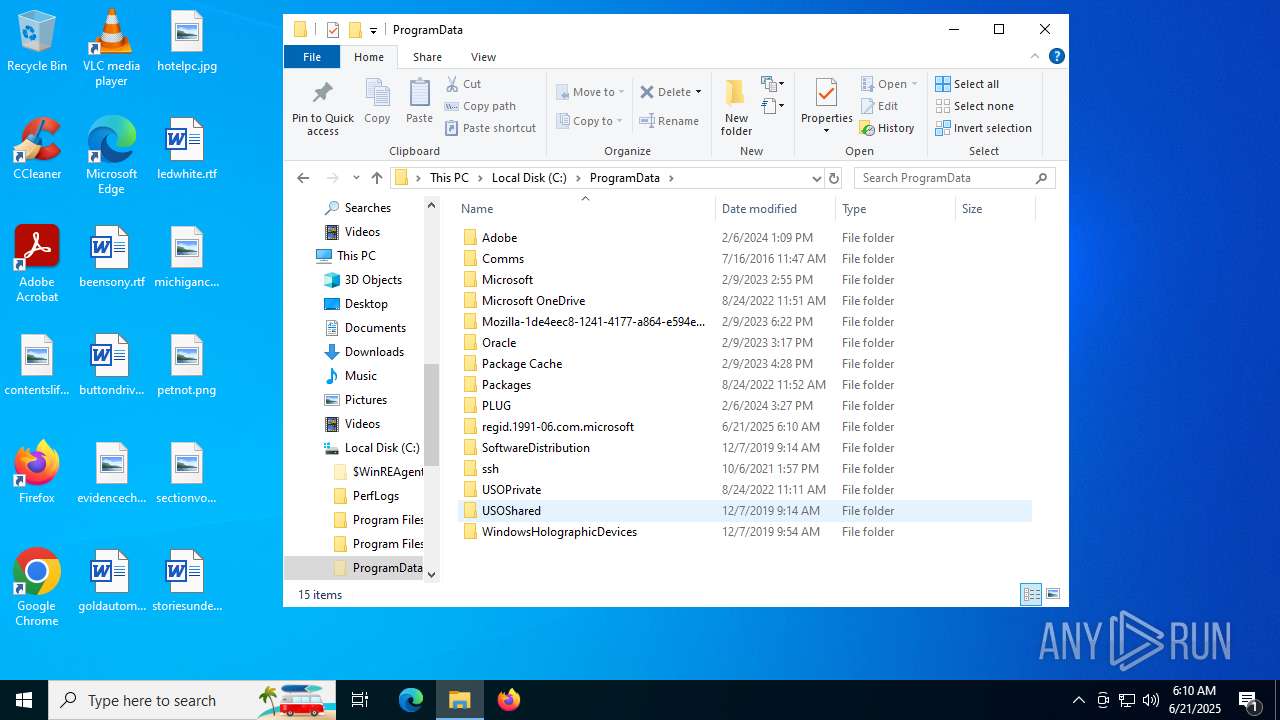
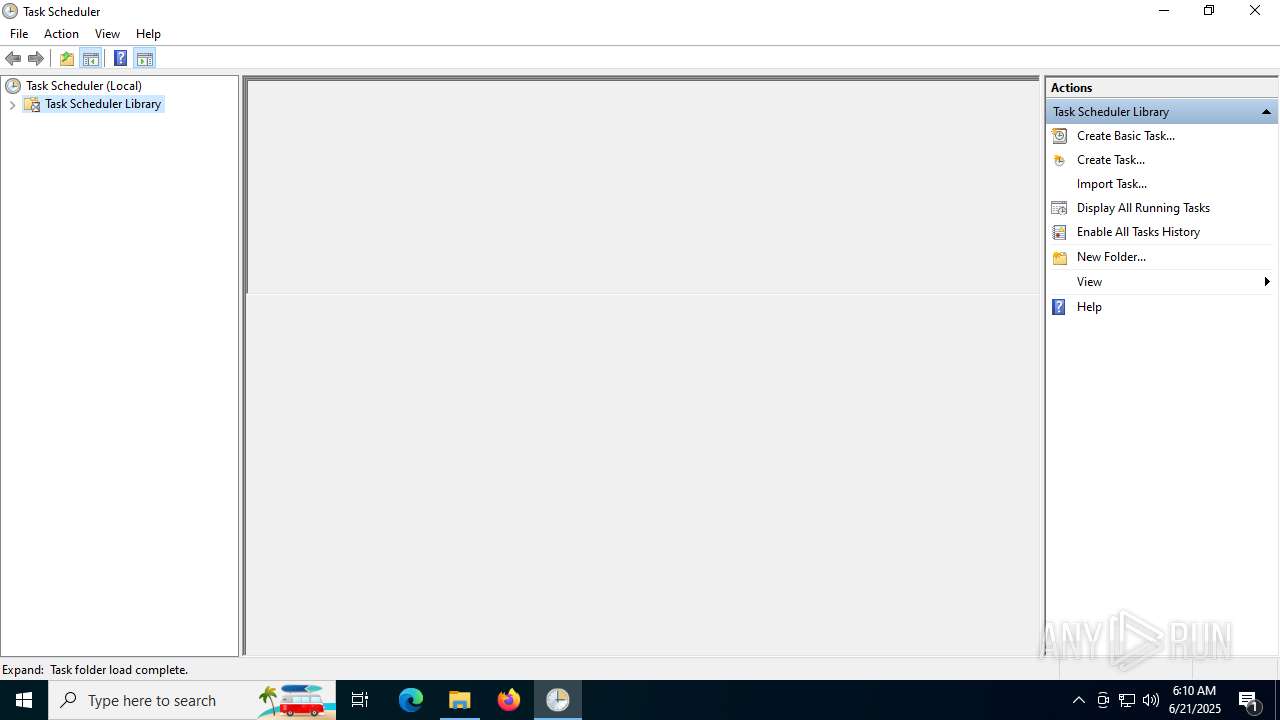
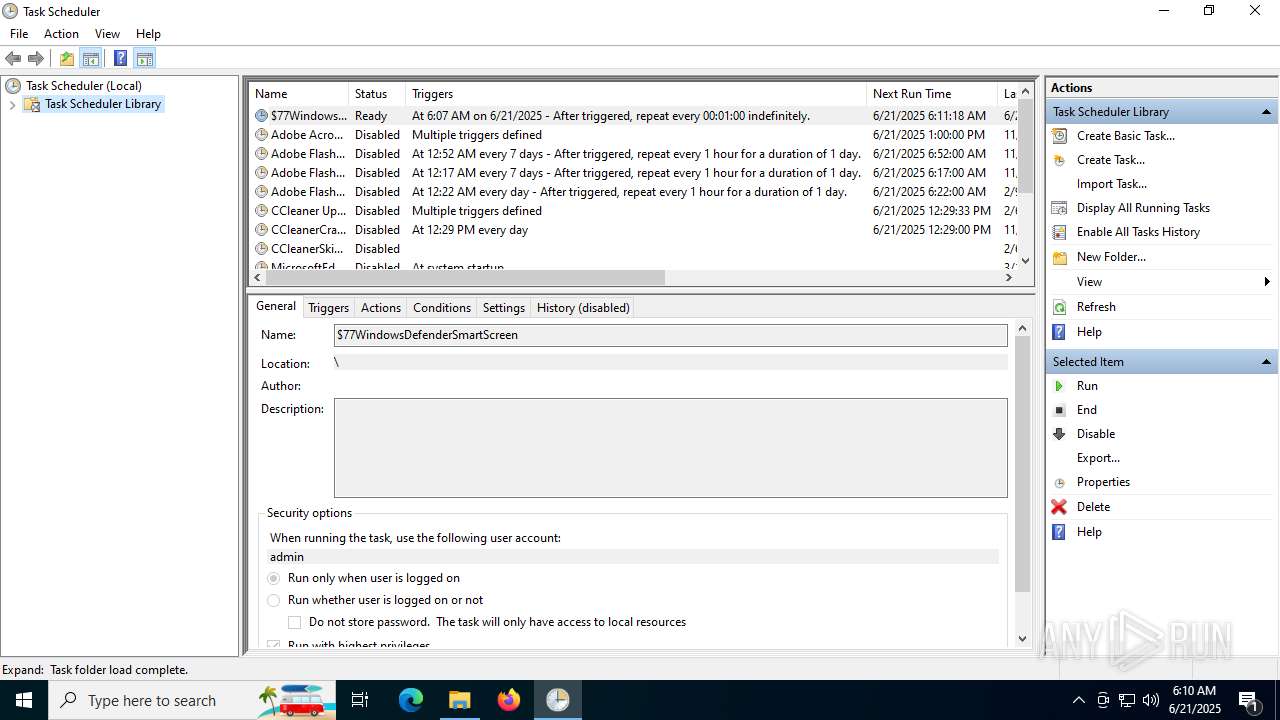
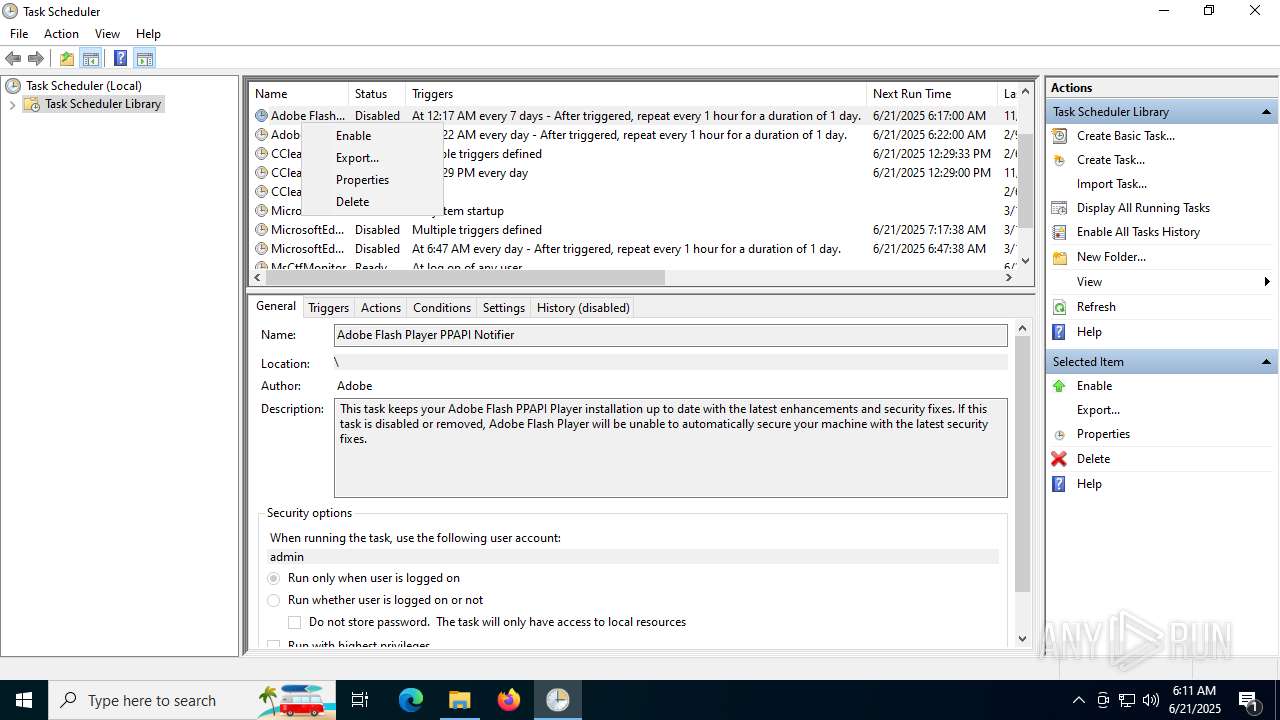
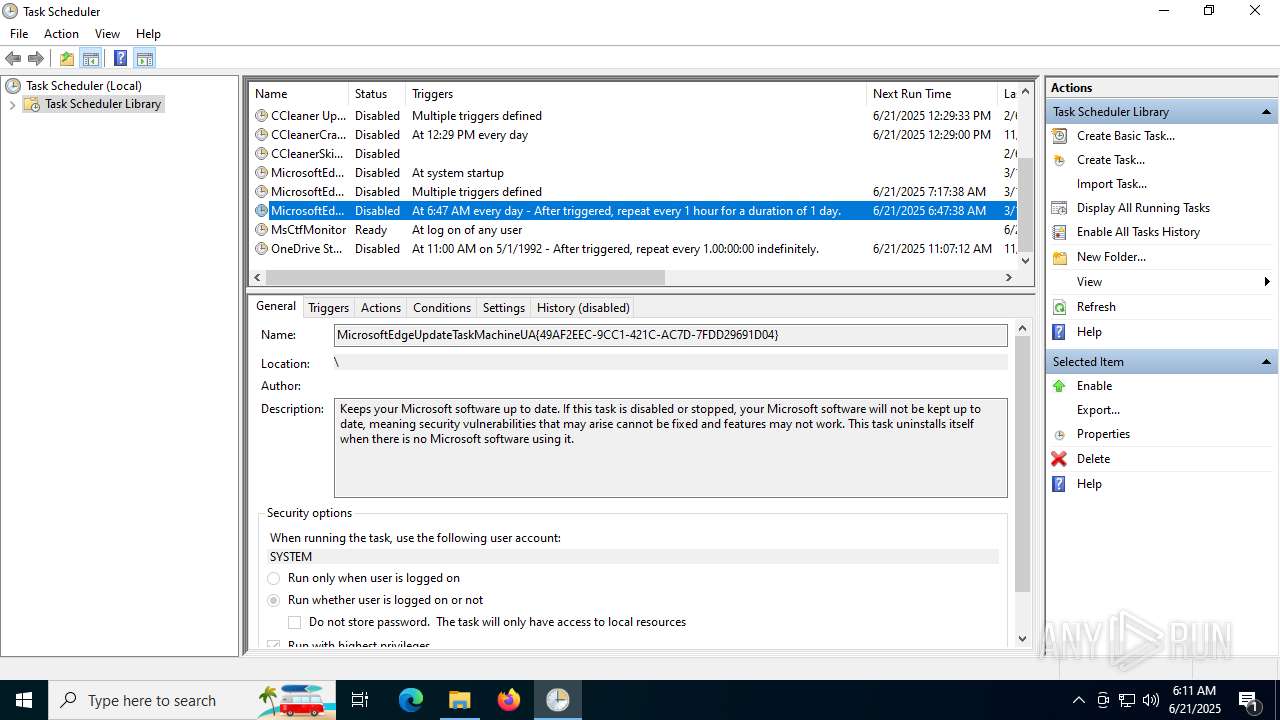
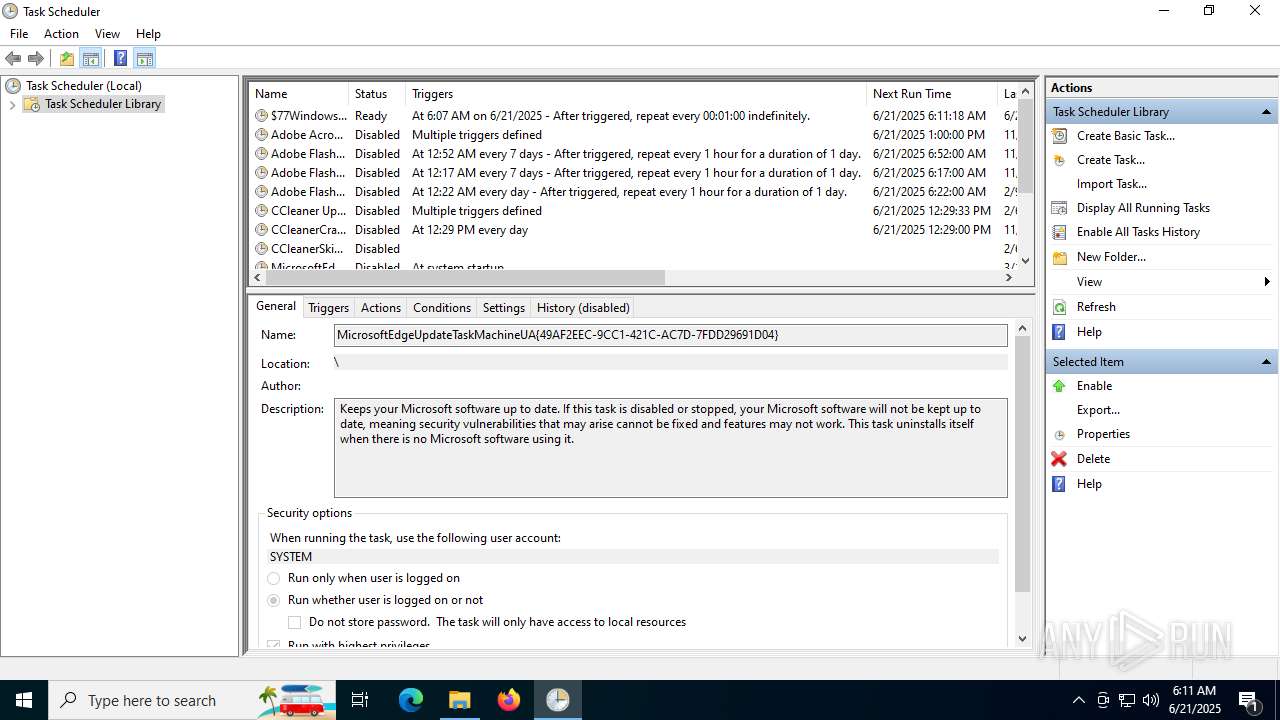
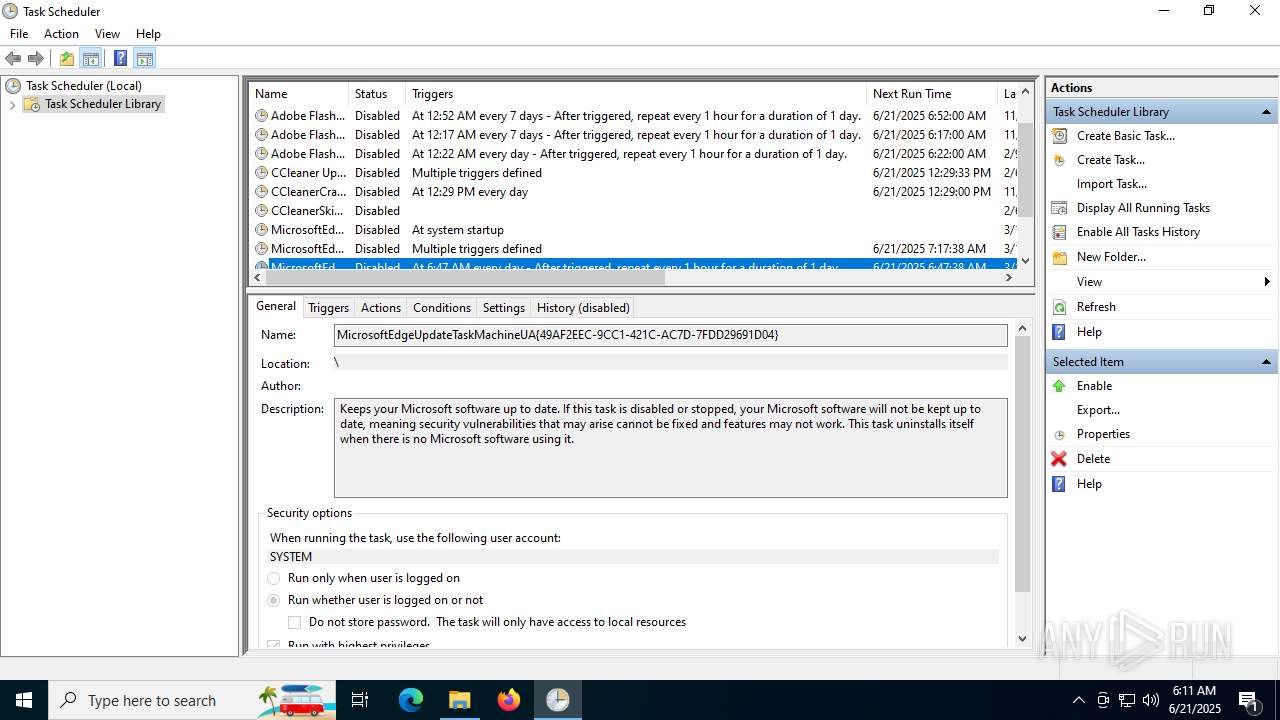
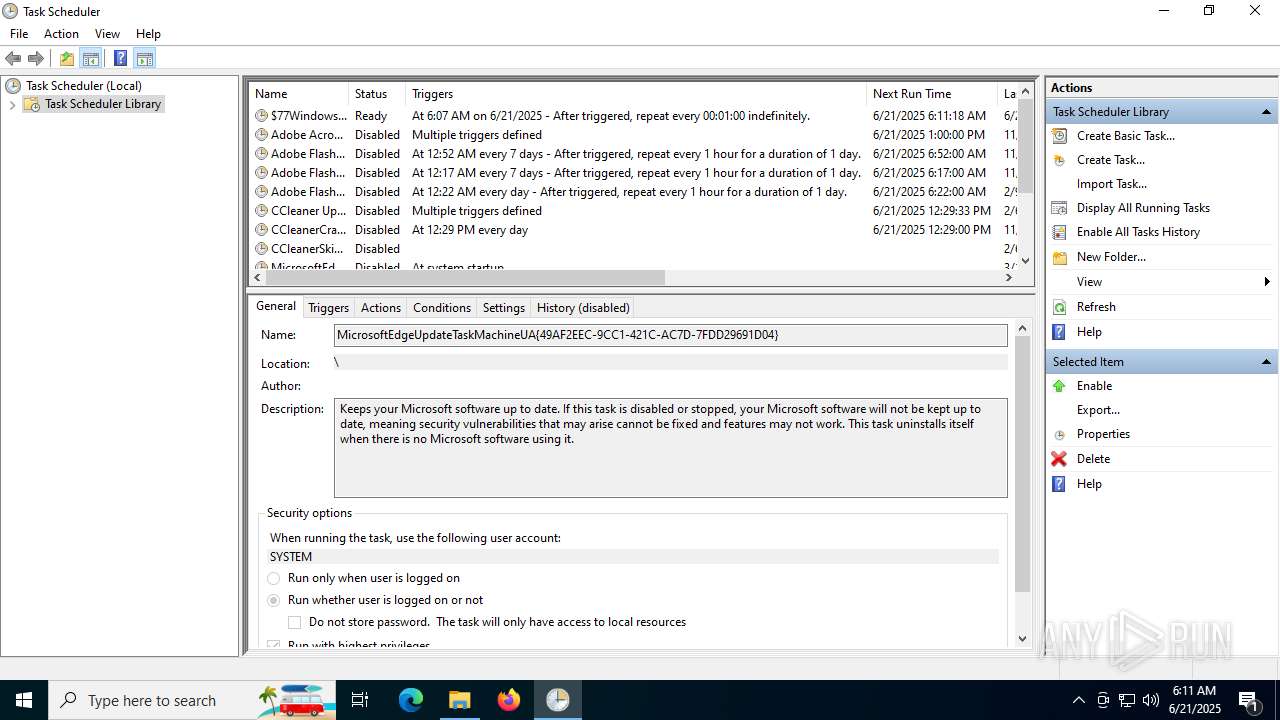
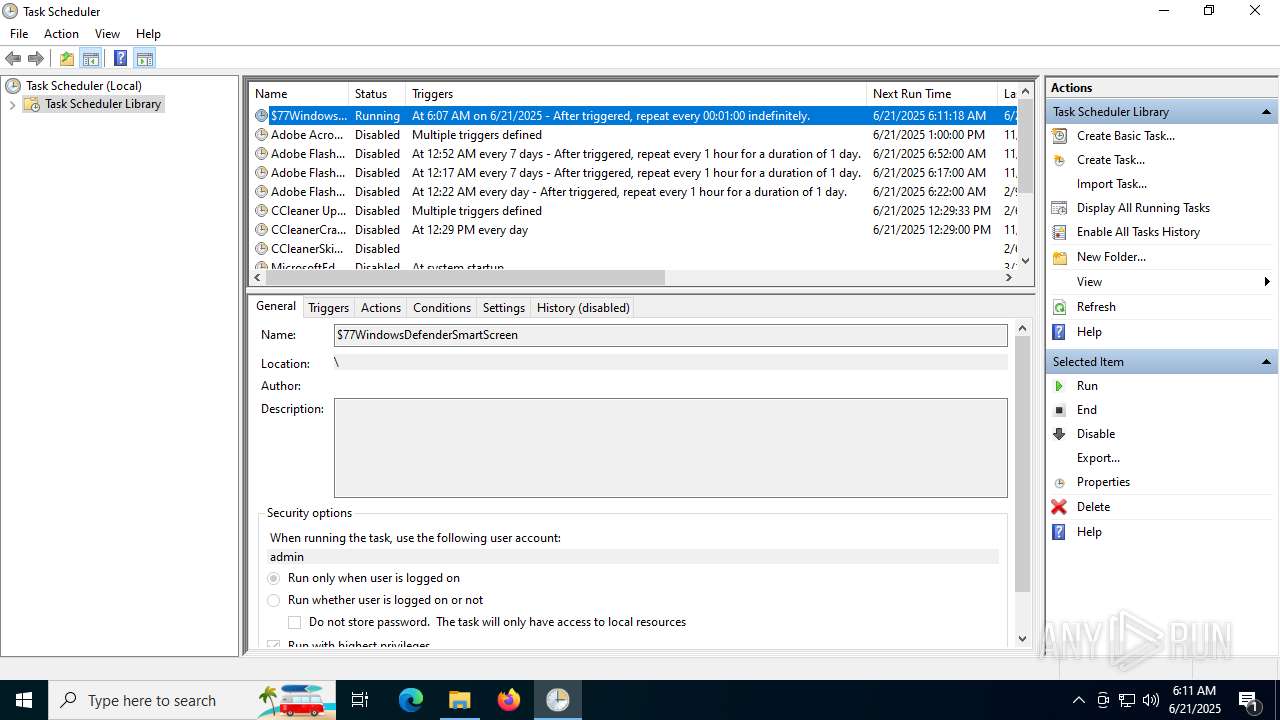
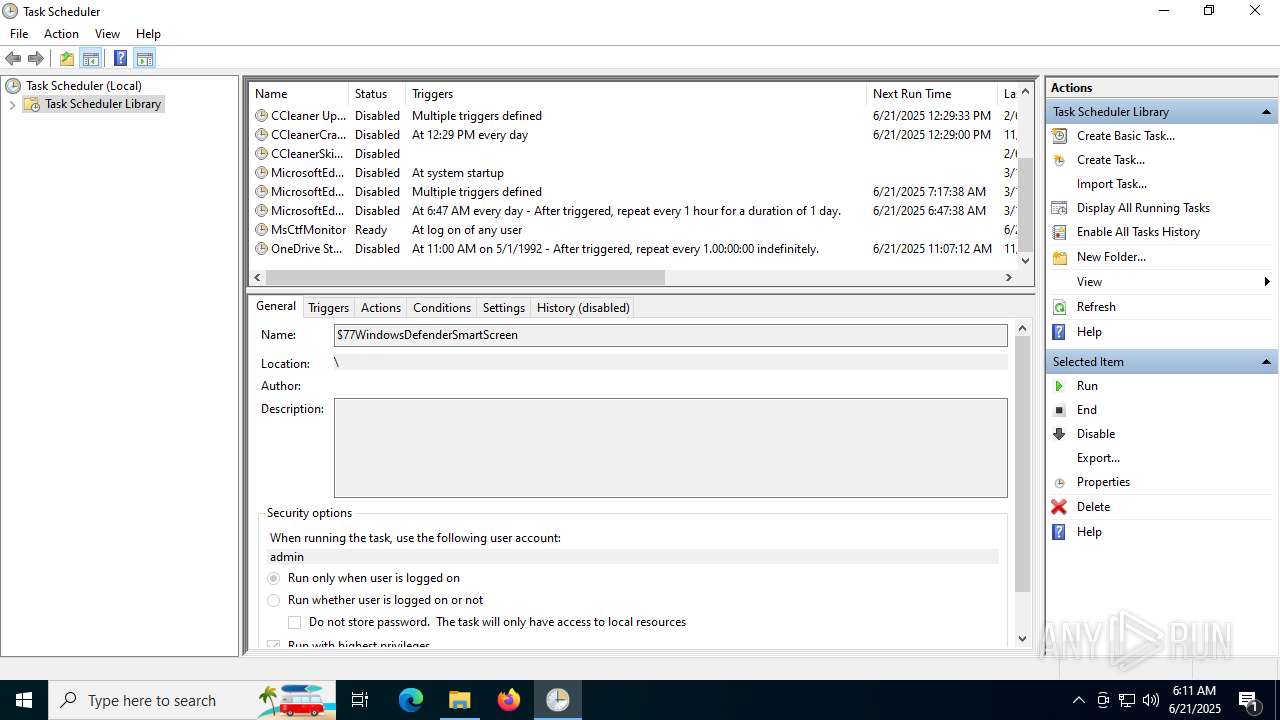
The process executes via Task Scheduler
- $77smartscreen.exe (PID: 6656)
- updater.exe (PID: 4032)
- PLUGScheduler.exe (PID: 4104)
- $77smartscreen.exe (PID: 812)
- PLUGScheduler.exe (PID: 3648)
- updater.exe (PID: 4120)
- $77smartscreen.exe (PID: 1244)
- $77smartscreen.exe (PID: 1292)
- $77smartscreen.exe (PID: 6308)
- $77smartscreen.exe (PID: 4232)
- $77smartscreen.exe (PID: 1140)
- $77smartscreen.exe (PID: 2404)
Lists all scheduled tasks
- schtasks.exe (PID: 2596)
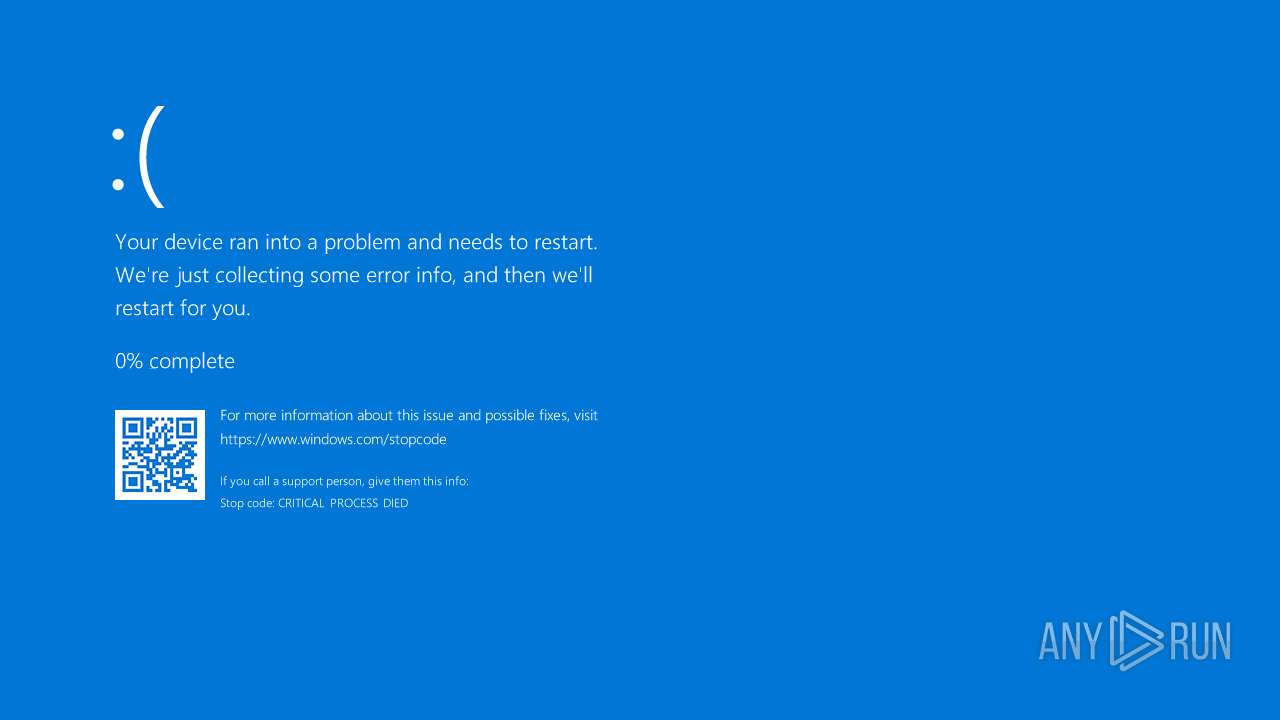
Executes application which crashes
- $77smartscreen.exe (PID: 6656)
- $77smartscreen.exe (PID: 812)
- $77smartscreen.exe (PID: 1244)
- $77smartscreen.exe (PID: 6308)
- $77smartscreen.exe (PID: 1292)
- $77smartscreen.exe (PID: 4232)
- $77smartscreen.exe (PID: 1140)
Executable content was dropped or overwritten
- main.exe (PID: 6876)
Application launched itself
- updater.exe (PID: 4032)
- updater.exe (PID: 4120)
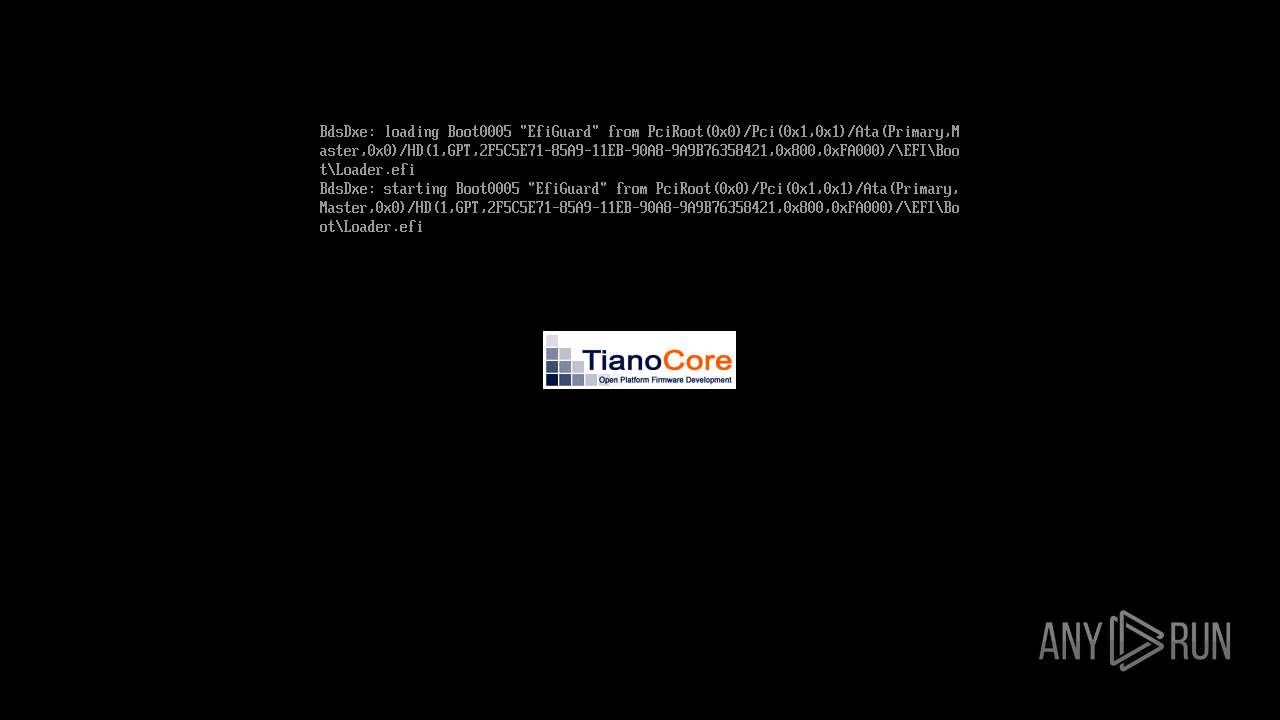
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- main.exe (PID: 6536)
INFO
Checks supported languages
- main.exe (PID: 6536)
- main.exe (PID: 6876)
- $77smartscreen.exe (PID: 6656)
- ShellExperienceHost.exe (PID: 5628)
- updater.exe (PID: 4032)
- PLUGScheduler.exe (PID: 4104)
- updater.exe (PID: 4952)
- PLUGScheduler.exe (PID: 3648)
- updater.exe (PID: 4120)
- $77smartscreen.exe (PID: 812)
- updater.exe (PID: 4980)
- $77smartscreen.exe (PID: 1244)
- $77smartscreen.exe (PID: 6308)
- $77smartscreen.exe (PID: 1292)
- $77smartscreen.exe (PID: 4232)
- $77smartscreen.exe (PID: 1140)
- $77smartscreen.exe (PID: 2404)
Reads the machine GUID from the registry
- main.exe (PID: 6536)
- $77smartscreen.exe (PID: 6656)
- $77smartscreen.exe (PID: 812)
- $77smartscreen.exe (PID: 1244)
- $77smartscreen.exe (PID: 6308)
- $77smartscreen.exe (PID: 1292)
- $77smartscreen.exe (PID: 4232)
- $77smartscreen.exe (PID: 1140)
Reads the computer name
- main.exe (PID: 6536)
- main.exe (PID: 6876)
- $77smartscreen.exe (PID: 6656)
- ShellExperienceHost.exe (PID: 5628)
- PLUGScheduler.exe (PID: 4104)
- updater.exe (PID: 4032)
- $77smartscreen.exe (PID: 812)
- $77smartscreen.exe (PID: 1244)
- PLUGScheduler.exe (PID: 3648)
- updater.exe (PID: 4120)
- $77smartscreen.exe (PID: 6308)
- $77smartscreen.exe (PID: 1292)
- $77smartscreen.exe (PID: 4232)
- $77smartscreen.exe (PID: 1140)
- $77smartscreen.exe (PID: 2404)
Reads Internet Explorer settings
- mshta.exe (PID: 6388)
- mshta.exe (PID: 5904)
Process checks computer location settings
- main.exe (PID: 6876)
- main.exe (PID: 6536)
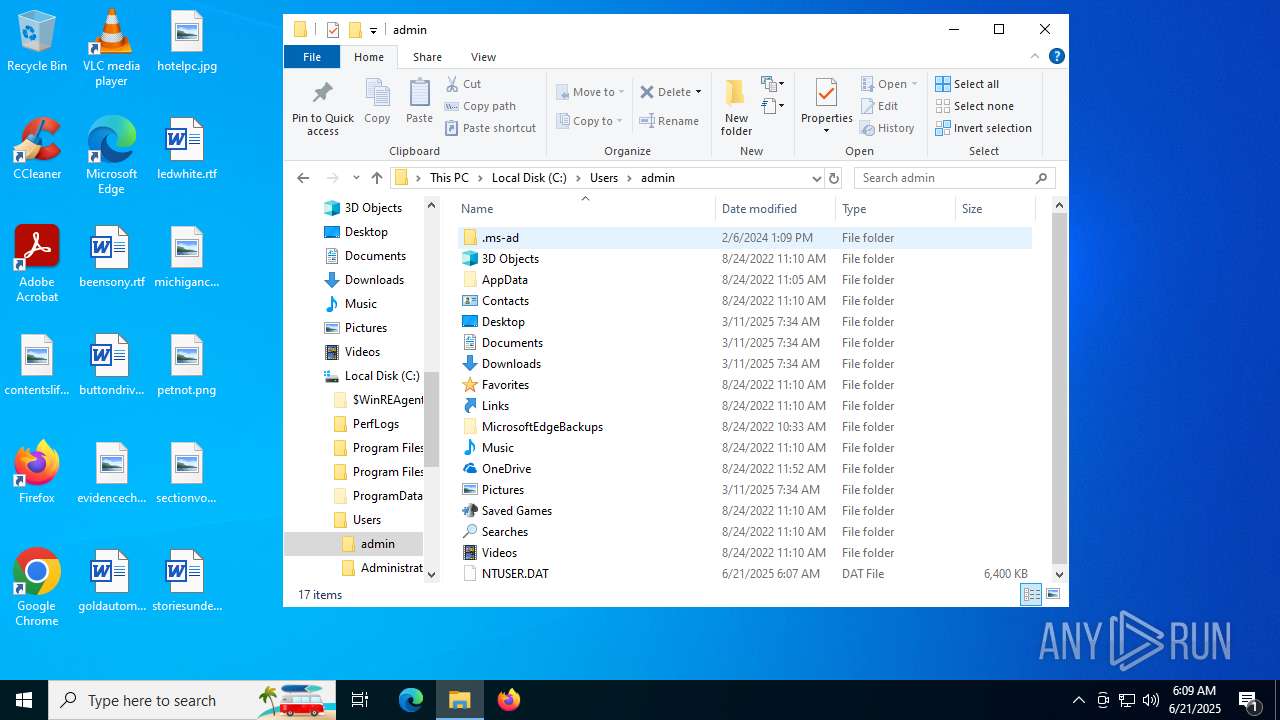
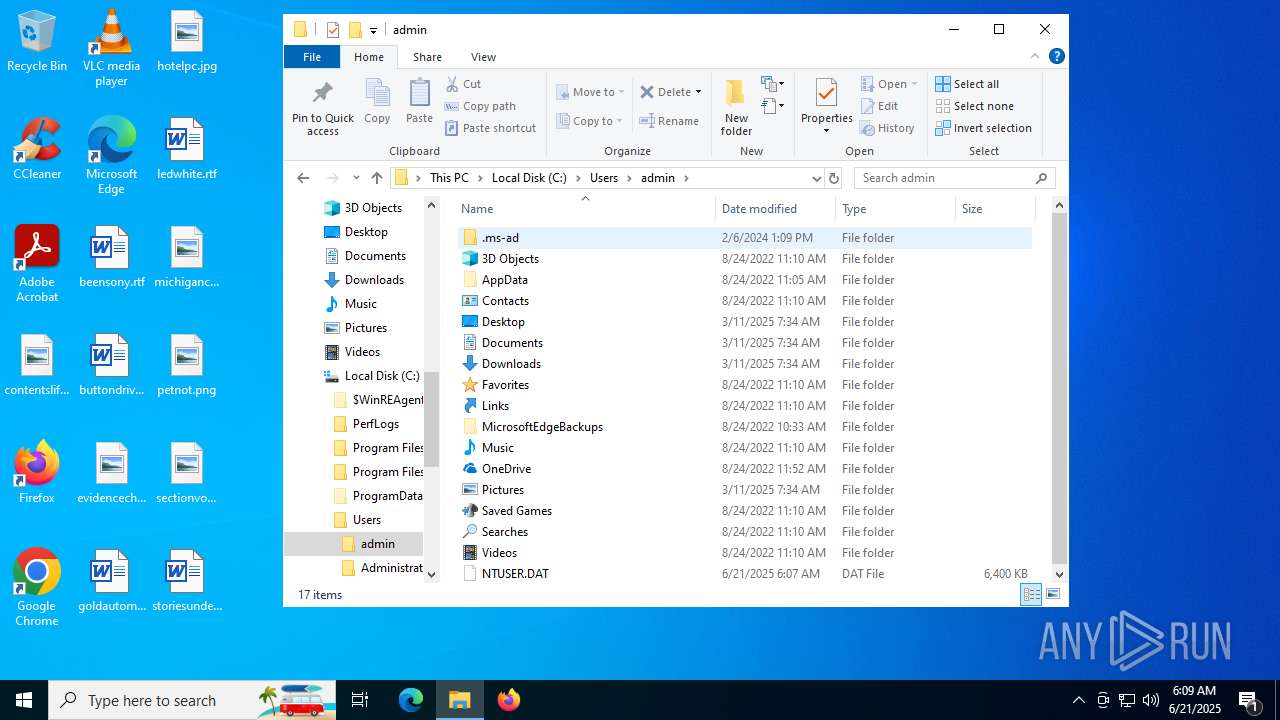
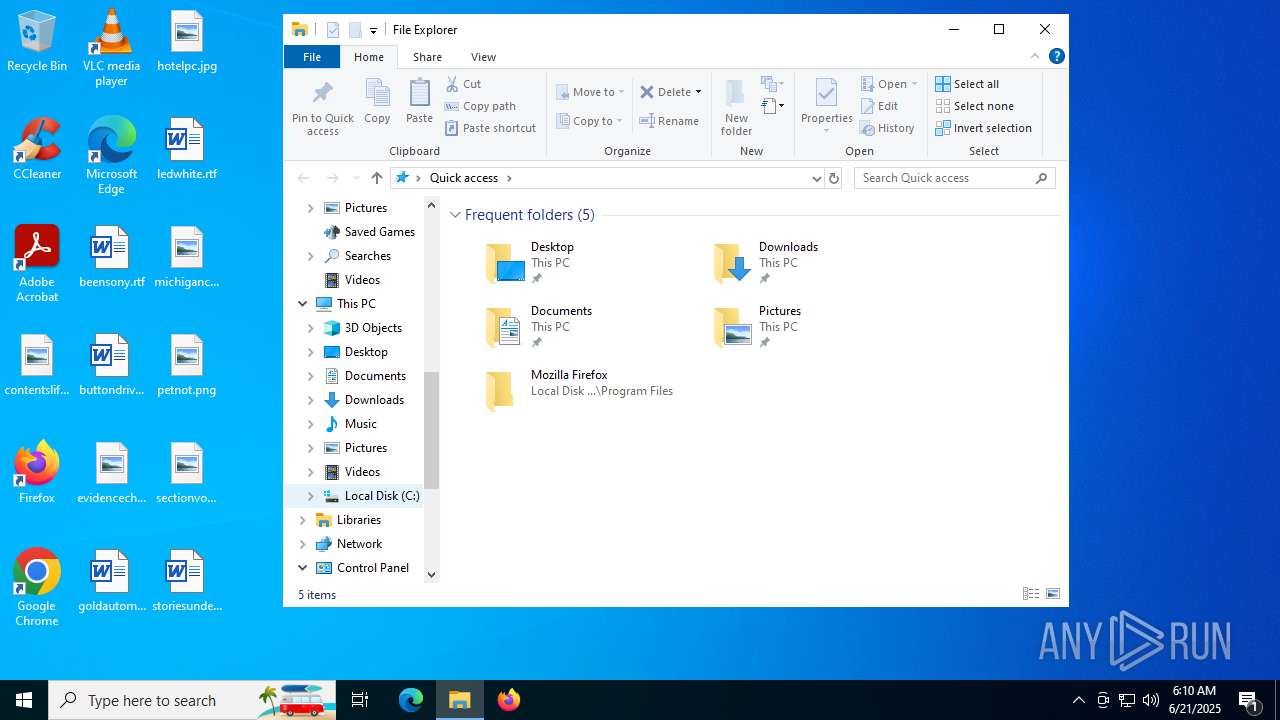
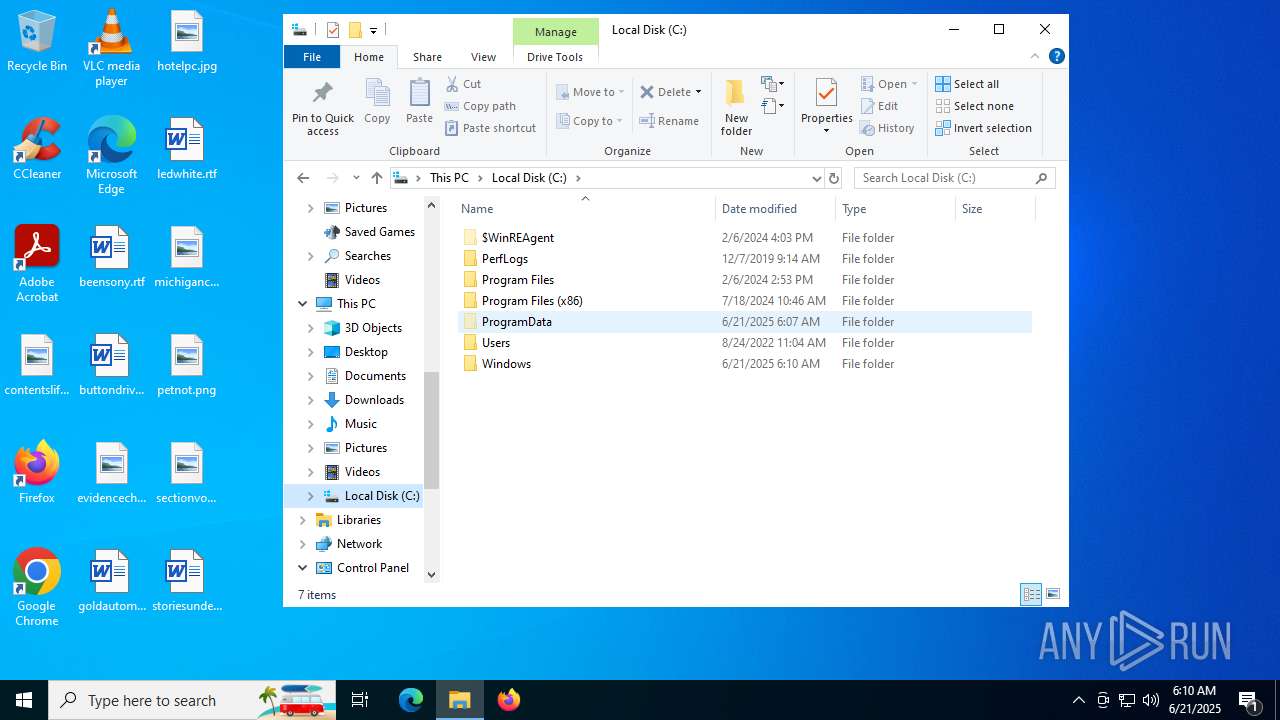
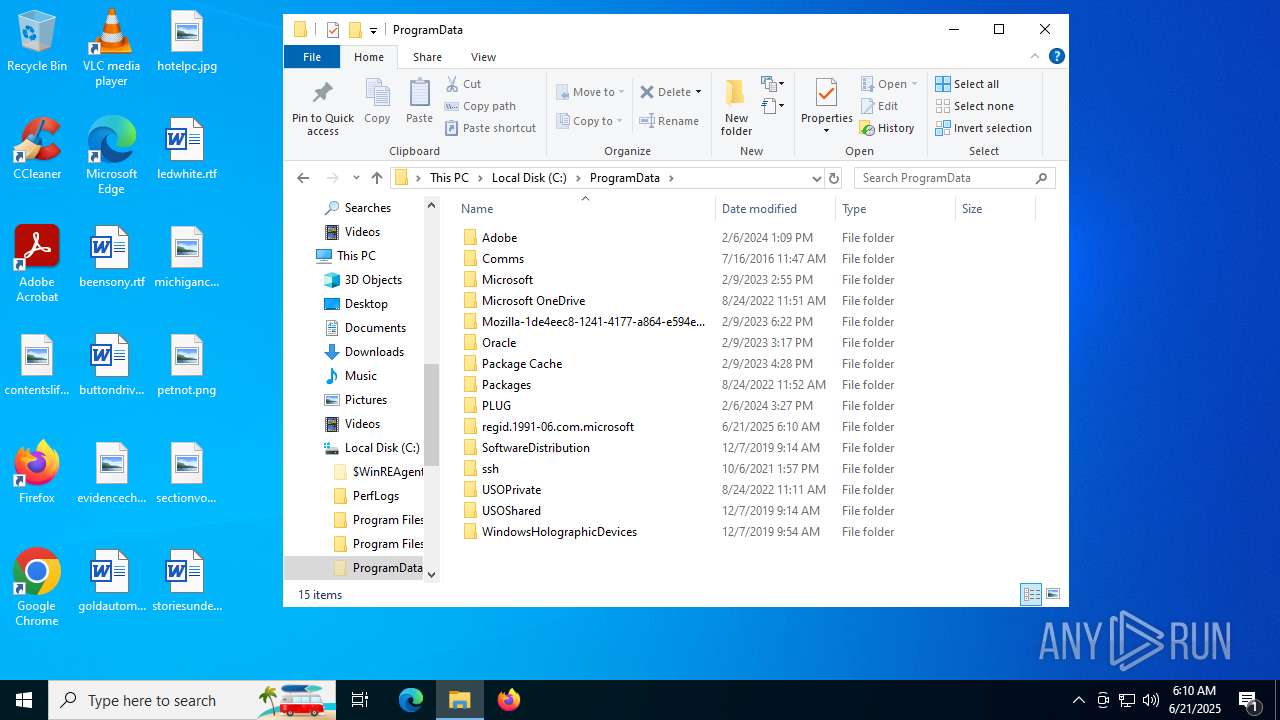
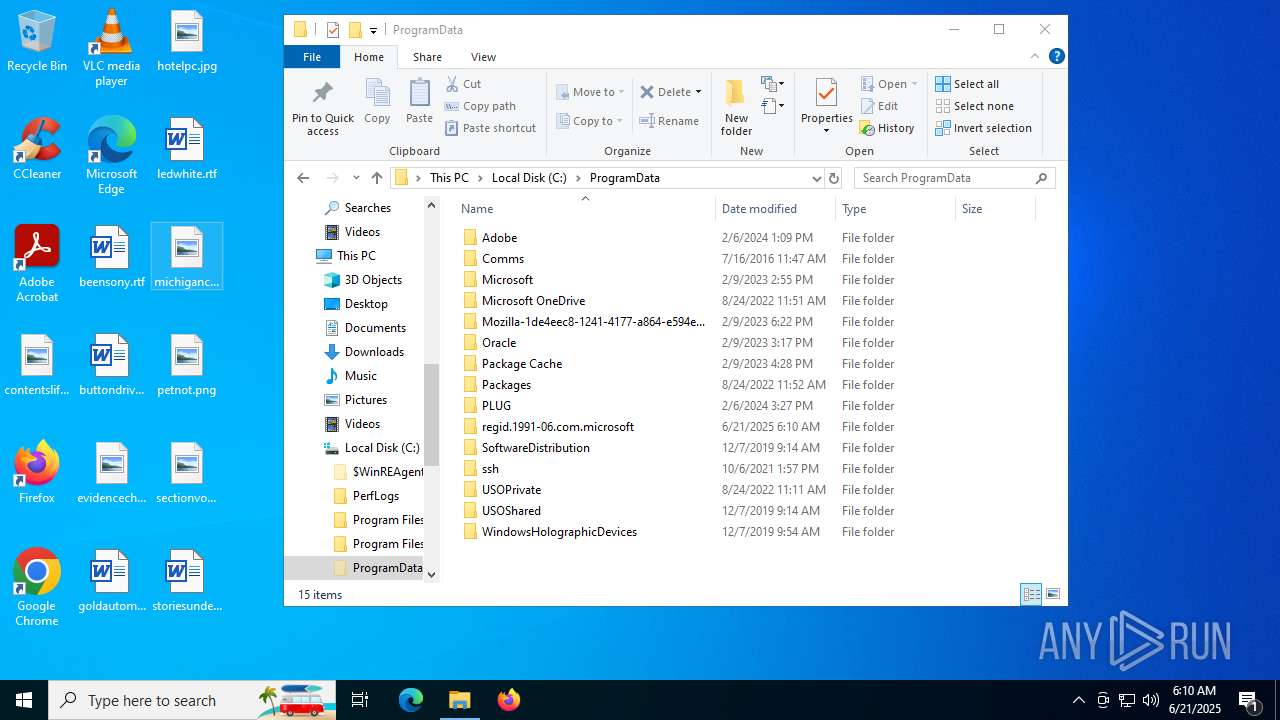
Creates files in the program directory
- dllhost.exe (PID: 6140)
- main.exe (PID: 6876)
- PLUGScheduler.exe (PID: 4104)
- PLUGScheduler.exe (PID: 3648)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5692)
- powershell.exe (PID: 6004)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5692)
- powershell.exe (PID: 6004)
Process checks whether UAC notifications are on
- $77smartscreen.exe (PID: 6656)
- updater.exe (PID: 4032)
- $77smartscreen.exe (PID: 812)
- updater.exe (PID: 4120)
Reads the software policy settings
- WerFault.exe (PID: 1036)
- WerFault.exe (PID: 5012)
- WerFault.exe (PID: 1196)
- WerFault.exe (PID: 2548)
- WerFault.exe (PID: 5100)
- WerFault.exe (PID: 1796)
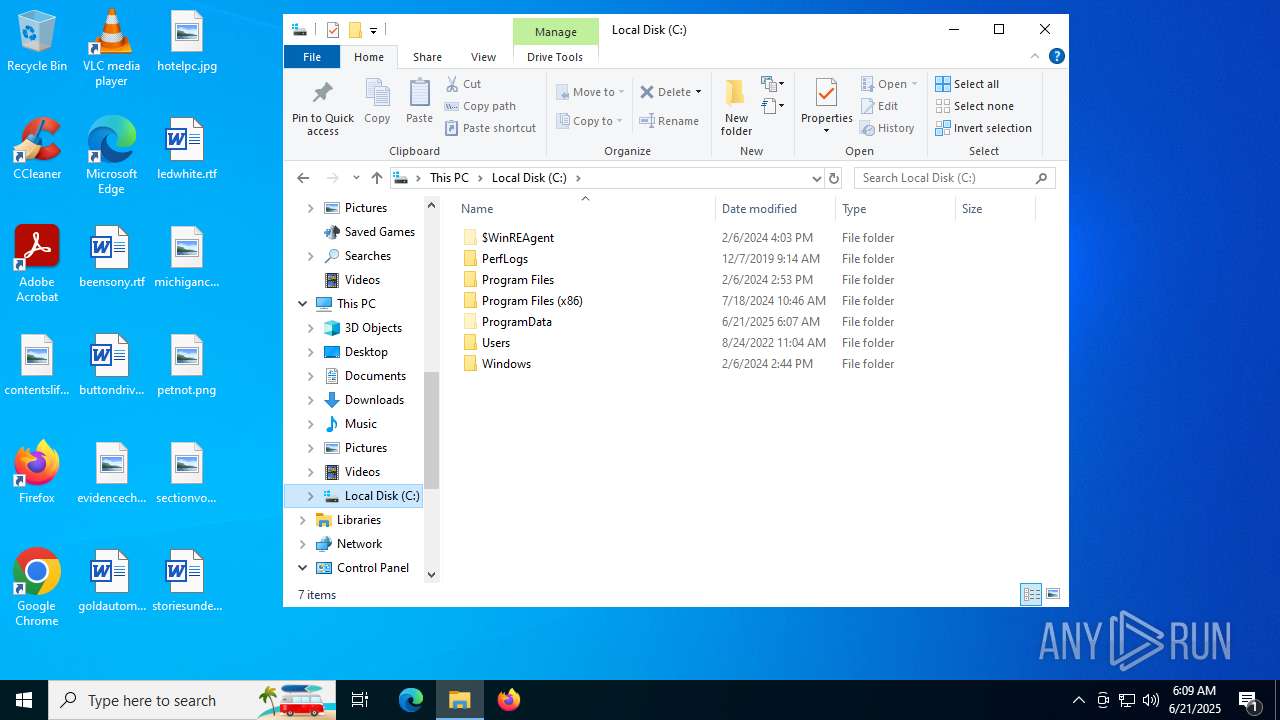
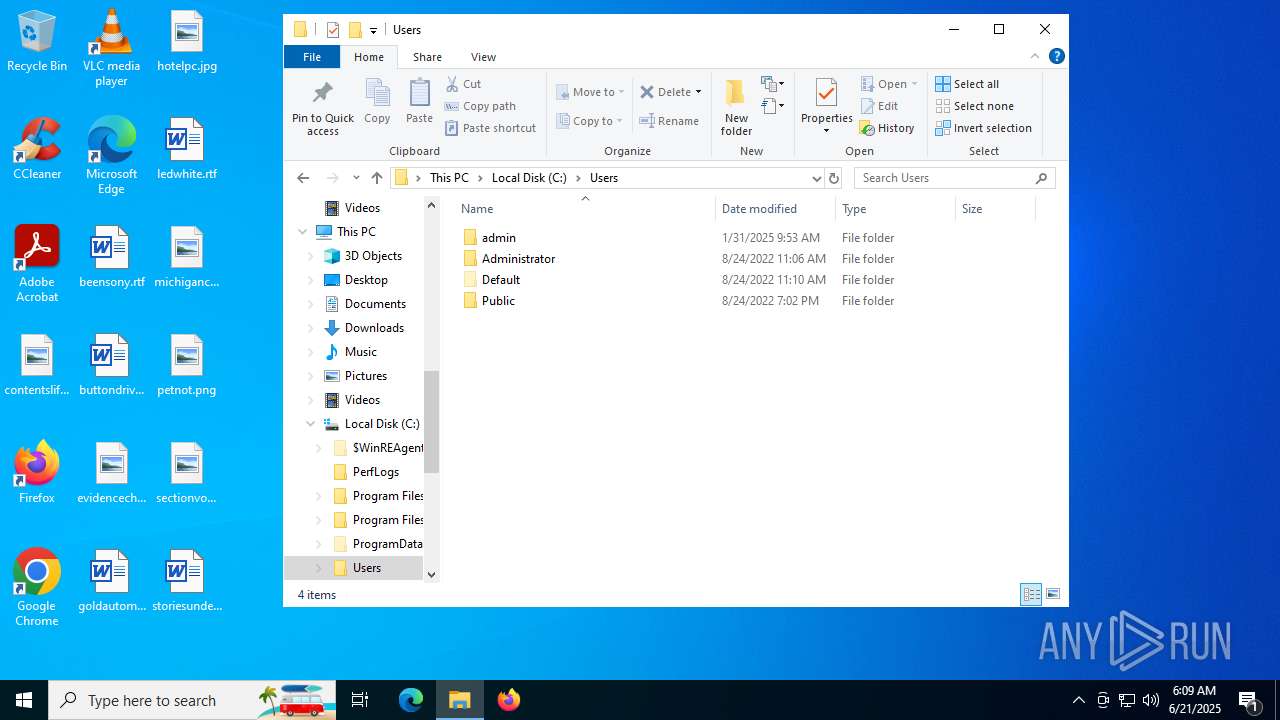
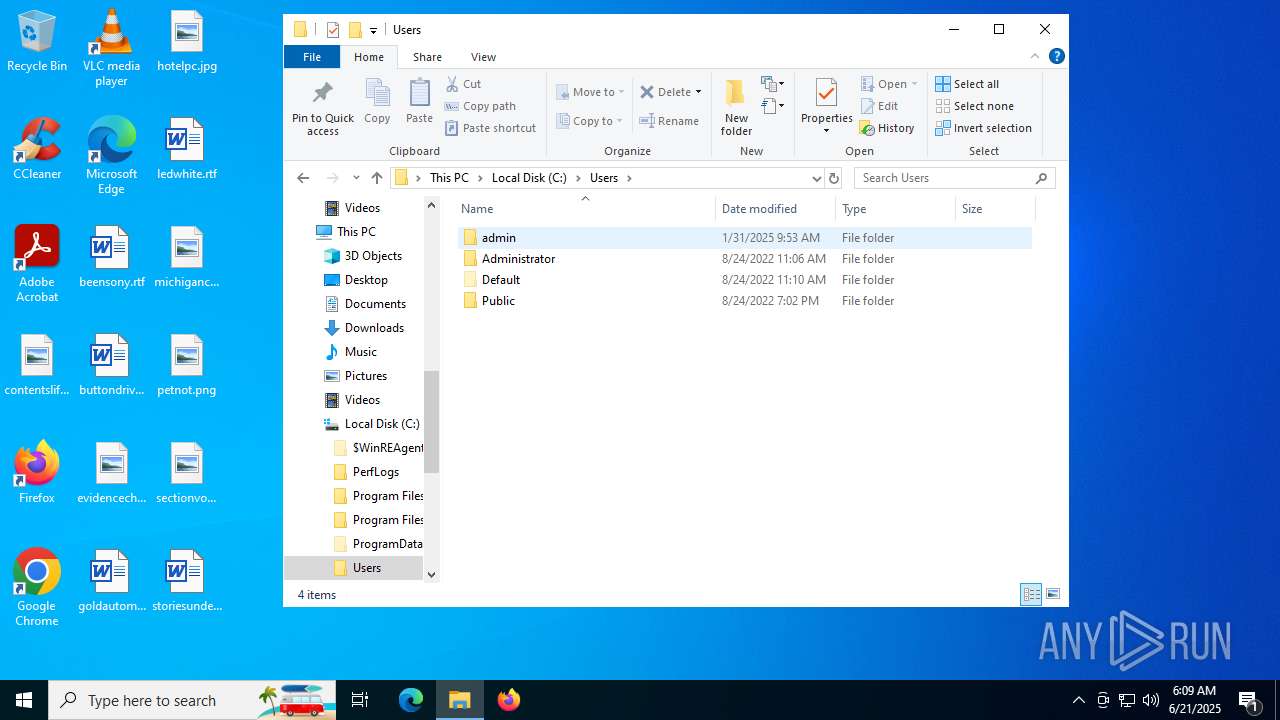
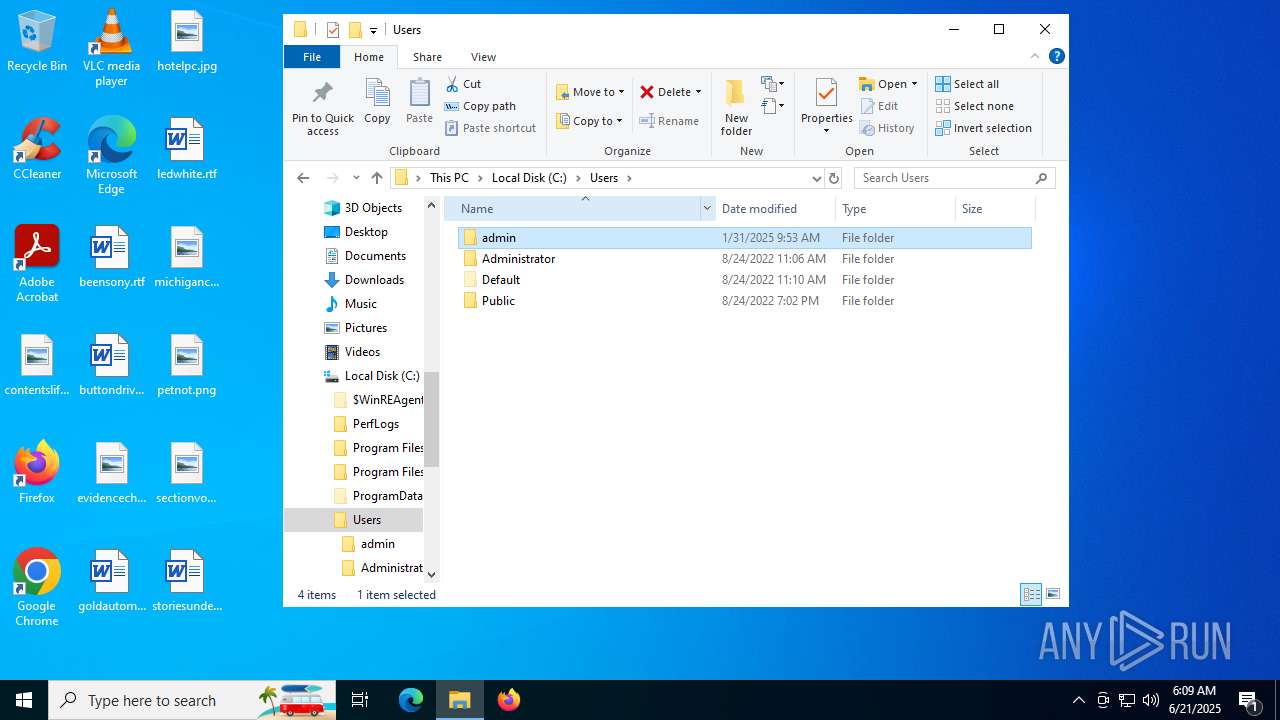
Creates files or folders in the user directory
- WerFault.exe (PID: 1036)
- WerFault.exe (PID: 2672)
- WerFault.exe (PID: 5012)
- WerFault.exe (PID: 1196)
- WerFault.exe (PID: 2548)
- WerFault.exe (PID: 5100)
- WerFault.exe (PID: 1796)
Checks proxy server information
- WerFault.exe (PID: 1036)
- WerFault.exe (PID: 5012)
- WerFault.exe (PID: 1196)
- WerFault.exe (PID: 2548)
- WerFault.exe (PID: 5100)
- WerFault.exe (PID: 1796)
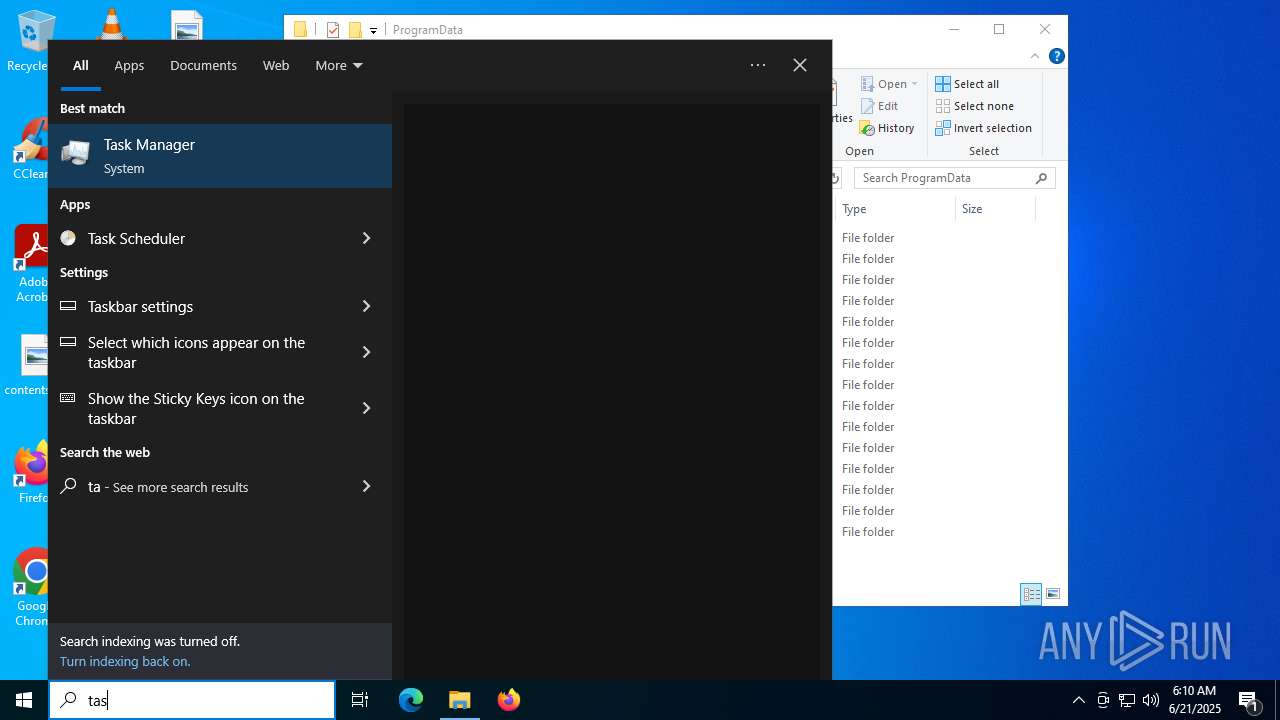
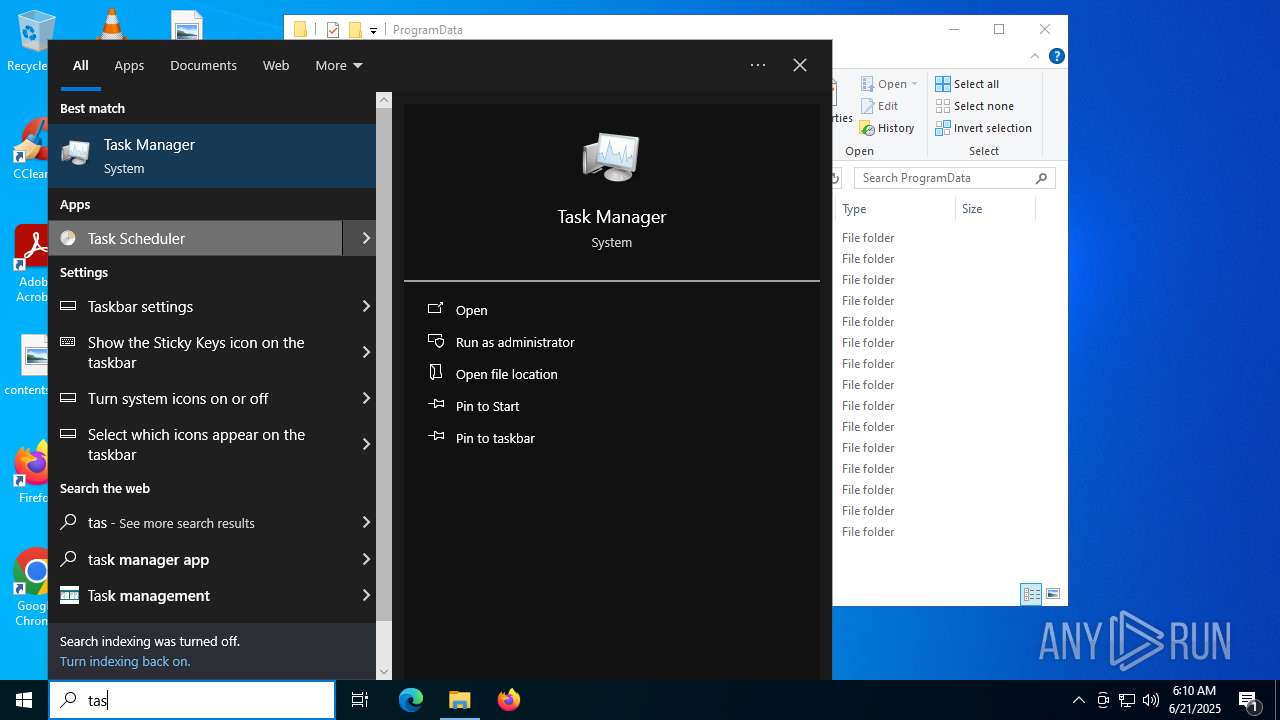
Manual execution by a user
- mmc.exe (PID: 6928)
Disables trace logs
- cmstp.exe (PID: 864)
Checks transactions between databases Windows and Oracle
- cmstp.exe (PID: 864)
Reads security settings of Internet Explorer
- mmc.exe (PID: 6928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:21 06:06:44+00:00 |
| ImageFileCharacteristics: | Executable |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3294208 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3261f6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | main.exe |
| LegalCopyright: | |
| OriginalFileName: | main.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
427
Monitored processes
38
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 812 | "C:\ProgramData\$77smartscreen.exe" | C:\ProgramData\$77smartscreen.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 864 | "C:\WINDOWS\system32\cmstp.exe" /au C:\WINDOWS\temp\3m2yon0p.inf | C:\Windows\System32\cmstp.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 1 Version: 7.2.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | C:\WINDOWS\system32\WerFault.exe -u -p 6656 -s 208 | C:\Windows\System32\WerFault.exe | $77smartscreen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | "C:\ProgramData\$77smartscreen.exe" | C:\ProgramData\$77smartscreen.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 2148734499 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\system32\WerFault.exe -u -p 6308 -s 1008 | C:\Windows\System32\WerFault.exe | $77smartscreen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | "C:\ProgramData\$77smartscreen.exe" | C:\ProgramData\$77smartscreen.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 2148734499 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1292 | "C:\ProgramData\$77smartscreen.exe" | C:\ProgramData\$77smartscreen.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 2148734499 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1796 | C:\WINDOWS\system32\WerFault.exe -u -p 1140 -s 976 | C:\Windows\System32\WerFault.exe | $77smartscreen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1932 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1936 | "C:\Windows\System32\taskkill.exe" /IM cmstp.exe /F | C:\Windows\System32\taskkill.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
38 216
Read events
38 132
Write events
63
Delete events
21
Modification events
| (PID) Process: | (864) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (864) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (864) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (864) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (864) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (864) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (864) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6140) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\cmmgr32.exe |
| Operation: | write | Name: | ProfileInstallPath |
Value: C:\ProgramData\Microsoft\Network\Connections\Cm | |||
| (PID) Process: | (6140) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | SM_AccessoriesName |
Value: Accessories | |||
| (PID) Process: | (6140) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | PF_AccessoriesName |
Value: Accessories | |||
Executable files
2
Suspicious files
95
Text files
20
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1036 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_$77smartscreen.e_b957fa212b847b78d46bfe193bdcf886997fa1d_ff0858ef_60cdfdc4-8317-4426-9486-e218de4dd94b\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1036 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\$77smartscreen.exe.6656.dmp | — | |
MD5:— | SHA256:— | |||
| 6004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dsov4m2l.nds.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4oedr530.wte.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6536 | main.exe | C:\Windows\Temp\3m2yon0p.inf | text | |
MD5:2CF2420FEB33030872FFEBAB10A67376 | SHA256:BFF54FF14013B61F24F01A78F3736FDD782C805856EB67711ECEBD5A2C088ACB | |||
| 5692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jgfesdsd.1qn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_y2bnsxox.2th.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4104 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.047.etl | binary | |
MD5:F9485F2BA891697F8B6CF8FB1E7F42C0 | SHA256:69146D4AAEFB8609745B6CA780B48ABC66054AA3CDB8061248CF7B32F3B32617 | |||
| 5692 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1F9F47C5EB95BD223492D45329619963 | SHA256:35D74B9CC25A72D0D843E28457E921266FAF0F6F816660E5A8A78B75A22786BE | |||
| 1036 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA8E3.tmp.WERInternalMetadata.xml | xml | |
MD5:B56C72F175241C468075CC28E73103AB | SHA256:1966BB3119858309FDDF8A27351F17320B7426604B4D880322963E80AA84B75C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
96
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5240 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1036 | WerFault.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1036 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3288 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3288 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5396 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5396 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3668 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5240 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5240 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
$77smartscreen.exe | CLR: Managed code called FailFast, saying " |
$77smartscreen.exe | "
|
$77smartscreen.exe | Detected tampering |