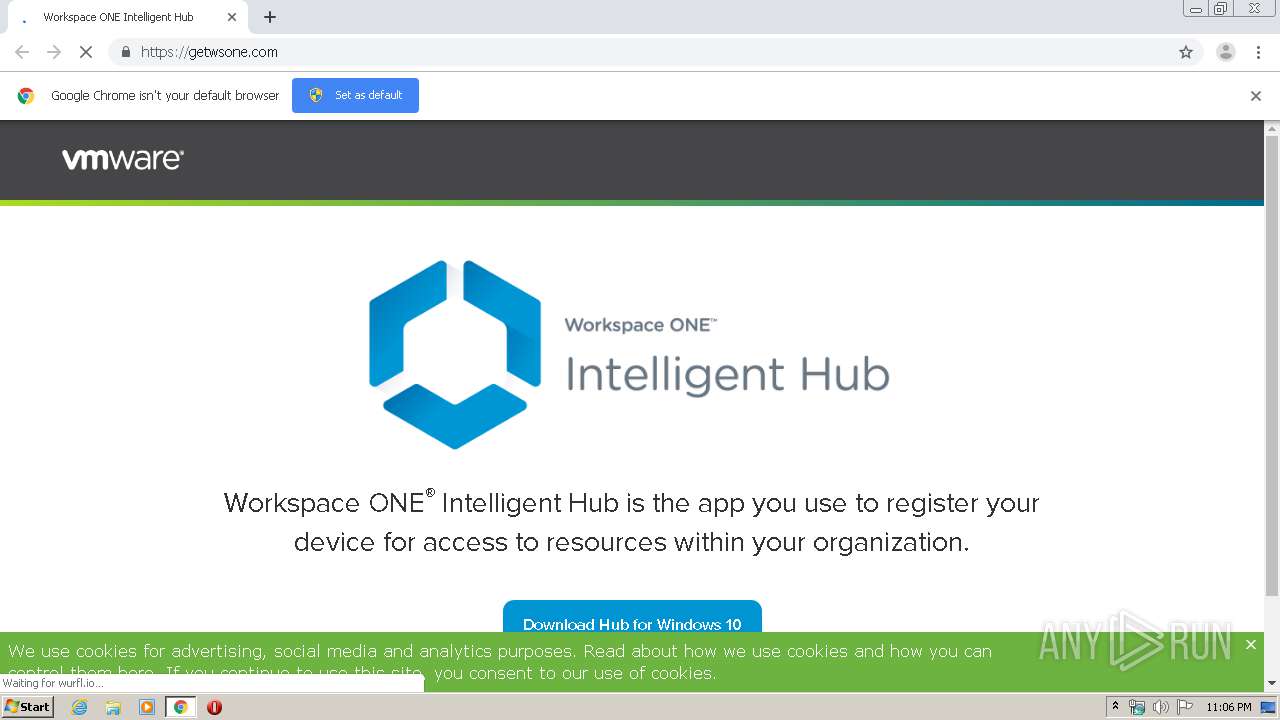
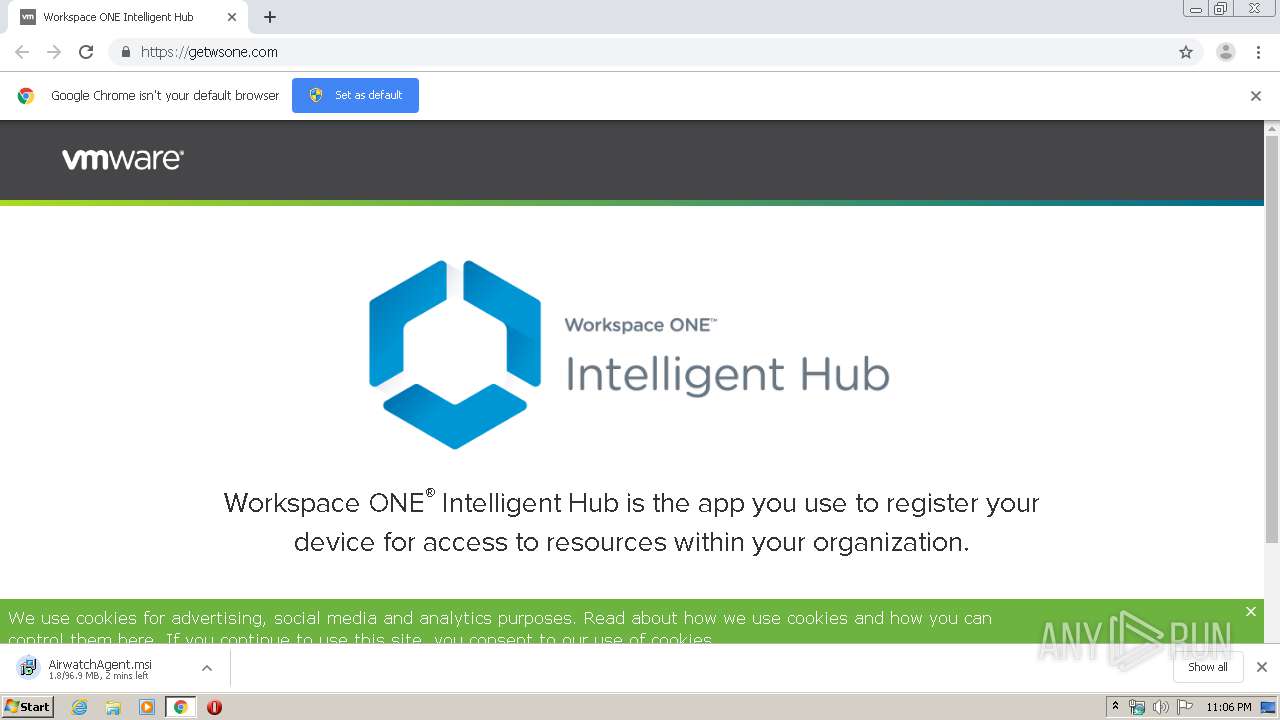
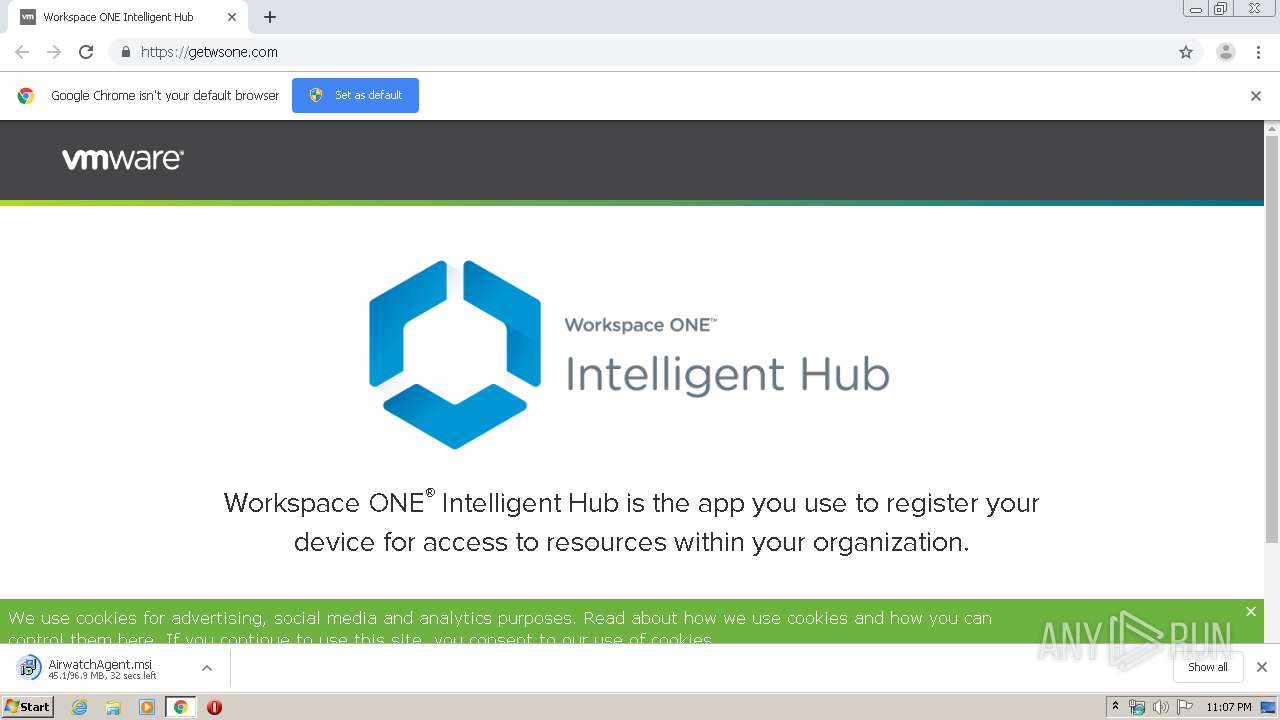
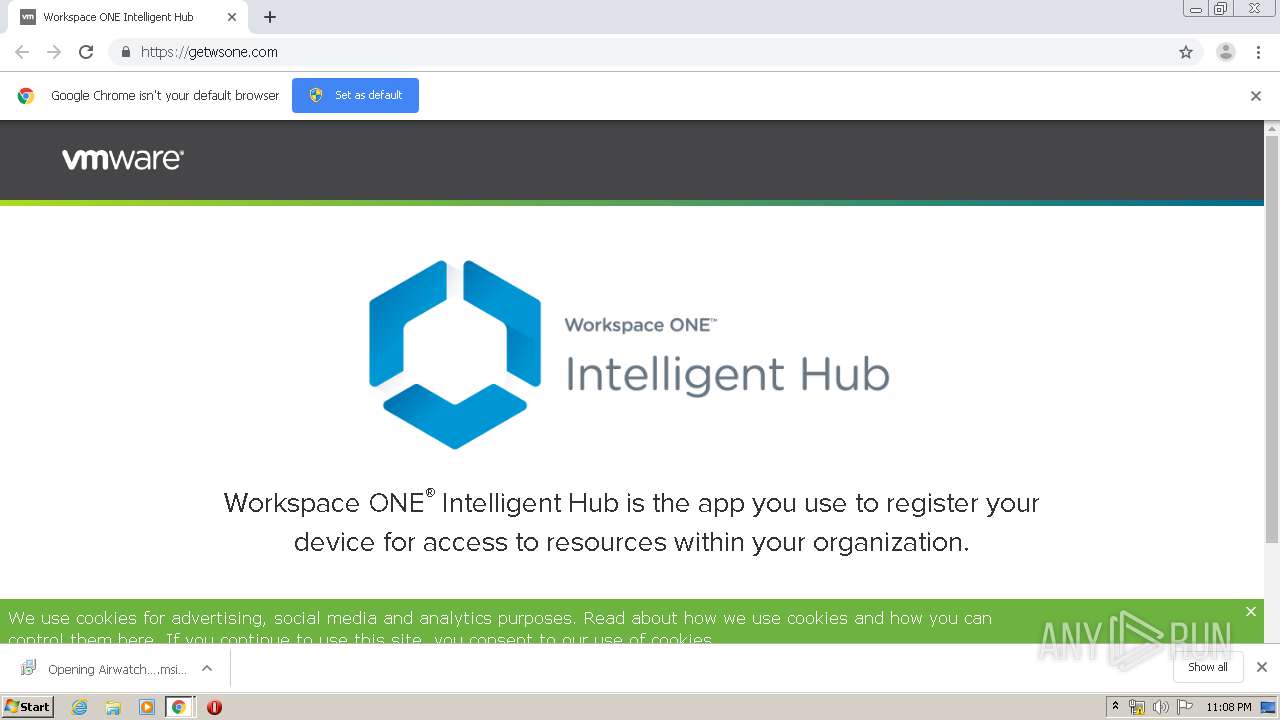
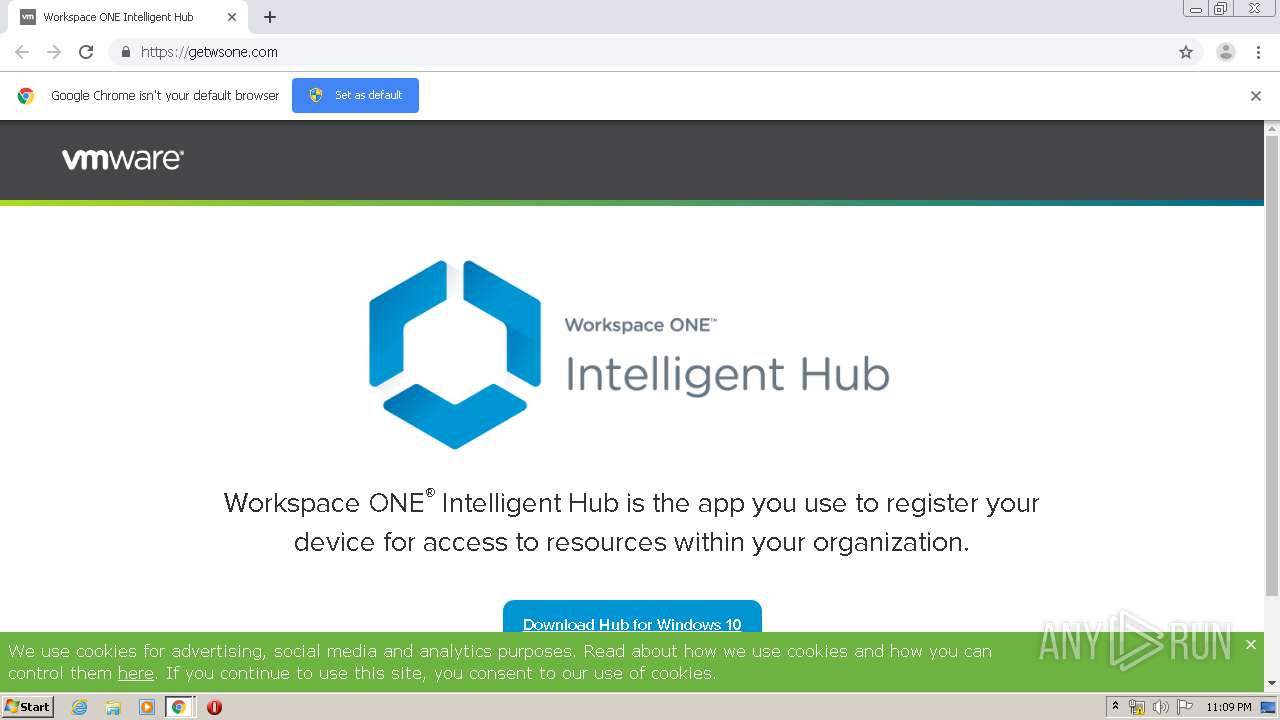
| URL: | https://getwsone.com/ |
| Full analysis: | https://app.any.run/tasks/b3506563-2287-4798-8cd4-e779a19ba795 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2020, 22:06:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D254CE2EE81F373D25955DE401E00A02 |
| SHA1: | 21140358EFB63CBD2B6D2D57FFCEF7673055964D |
| SHA256: | BEE3FFCF3CCFC71645EC0D4C27639ABCB38319654321F248C031A87F3B8AFEC5 |
| SSDEEP: | 3:N8hvPn:21 |
MALICIOUS
Application was dropped or rewritten from another process
- MSIB3DA.tmp (PID: 392)
SUSPICIOUS
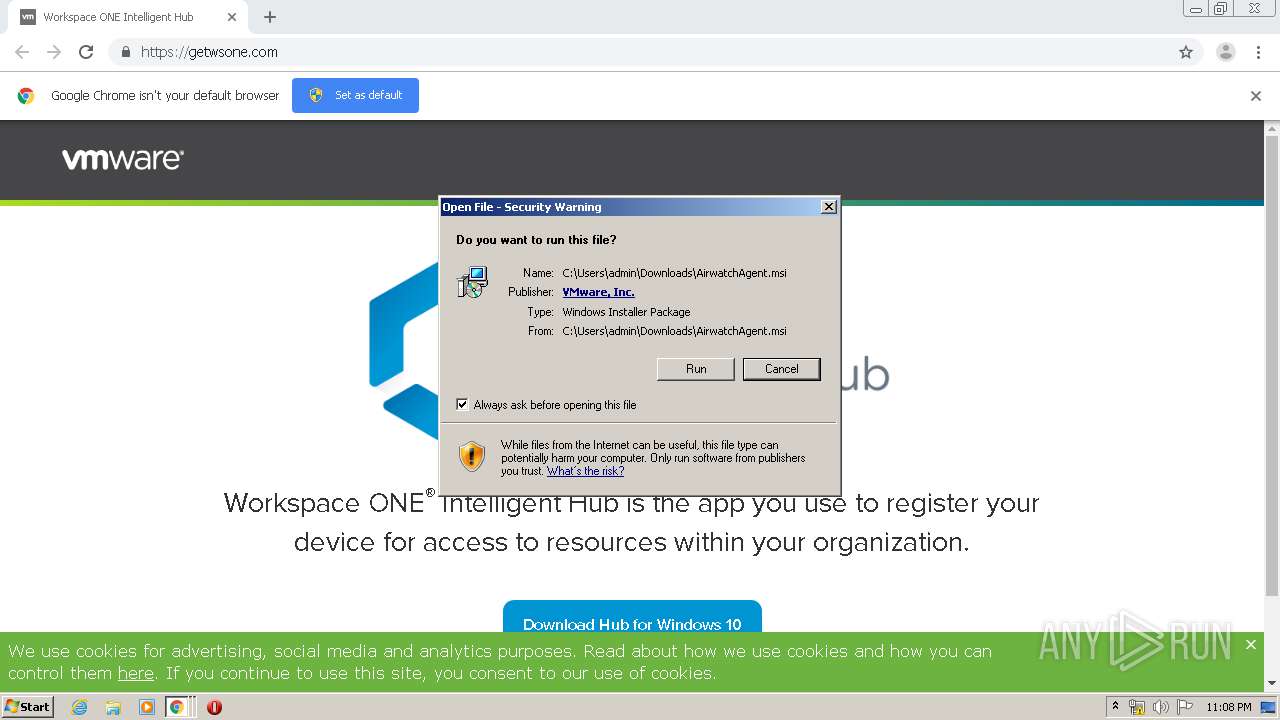
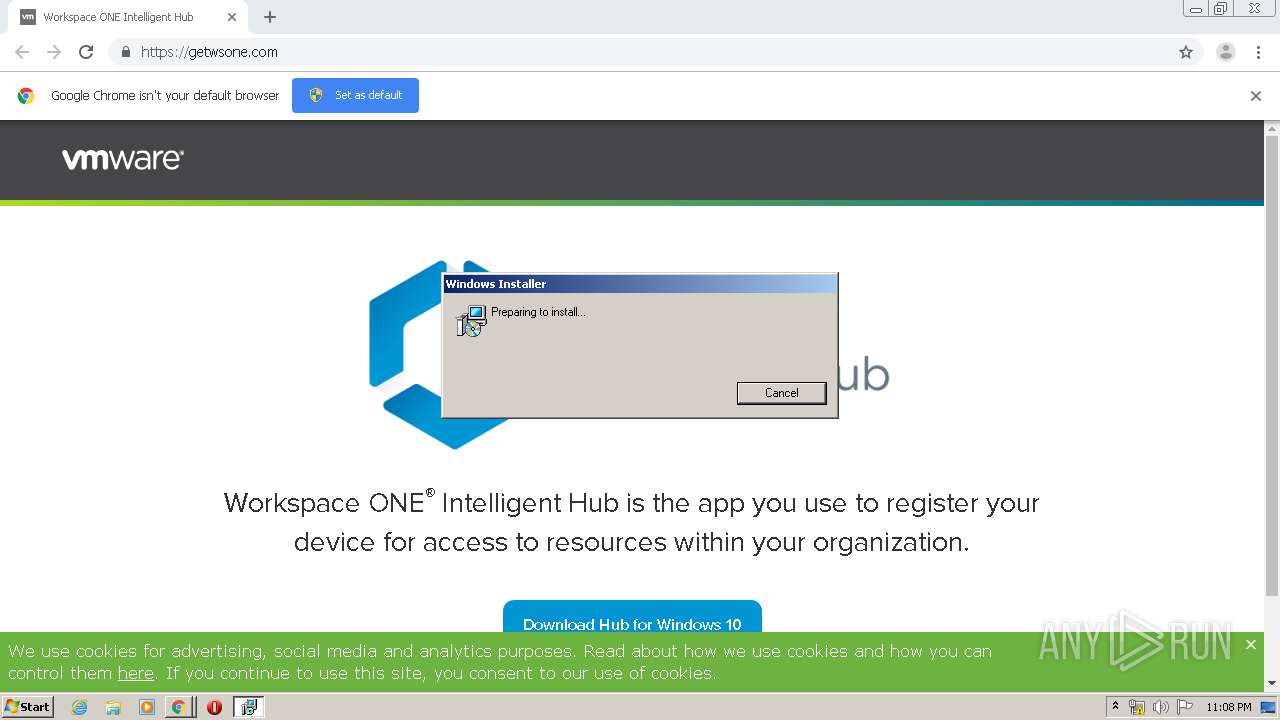
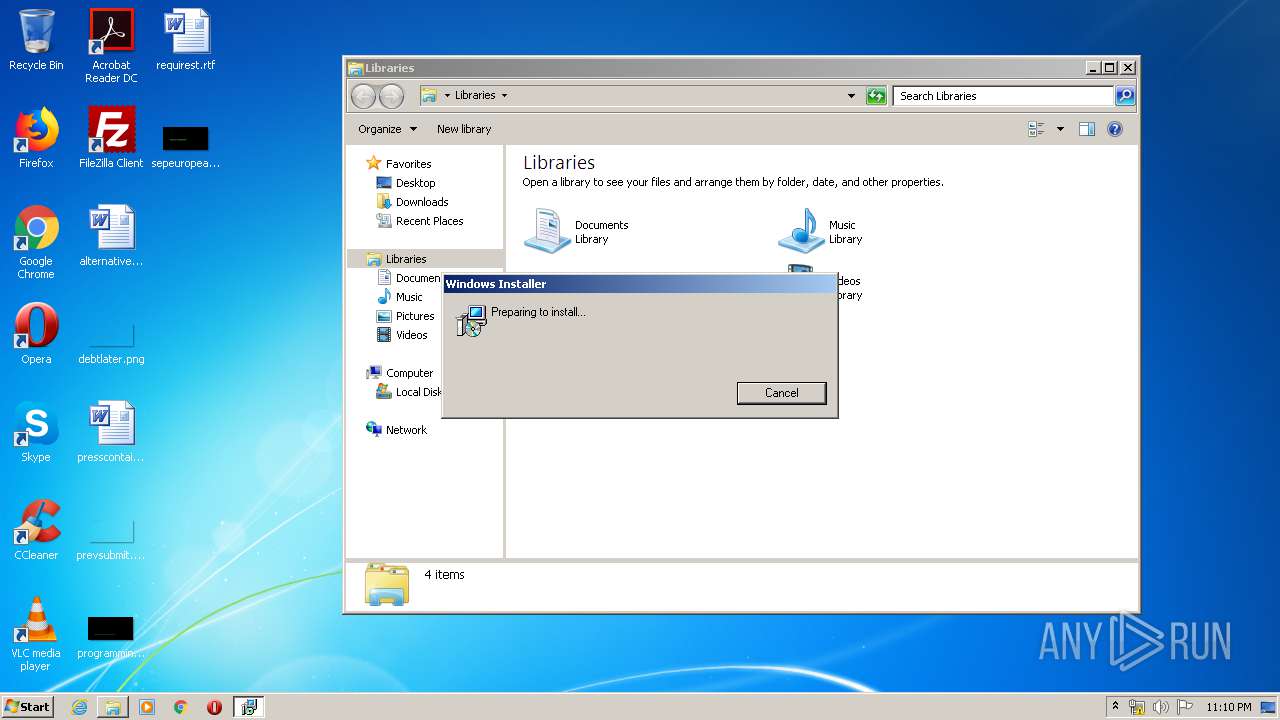
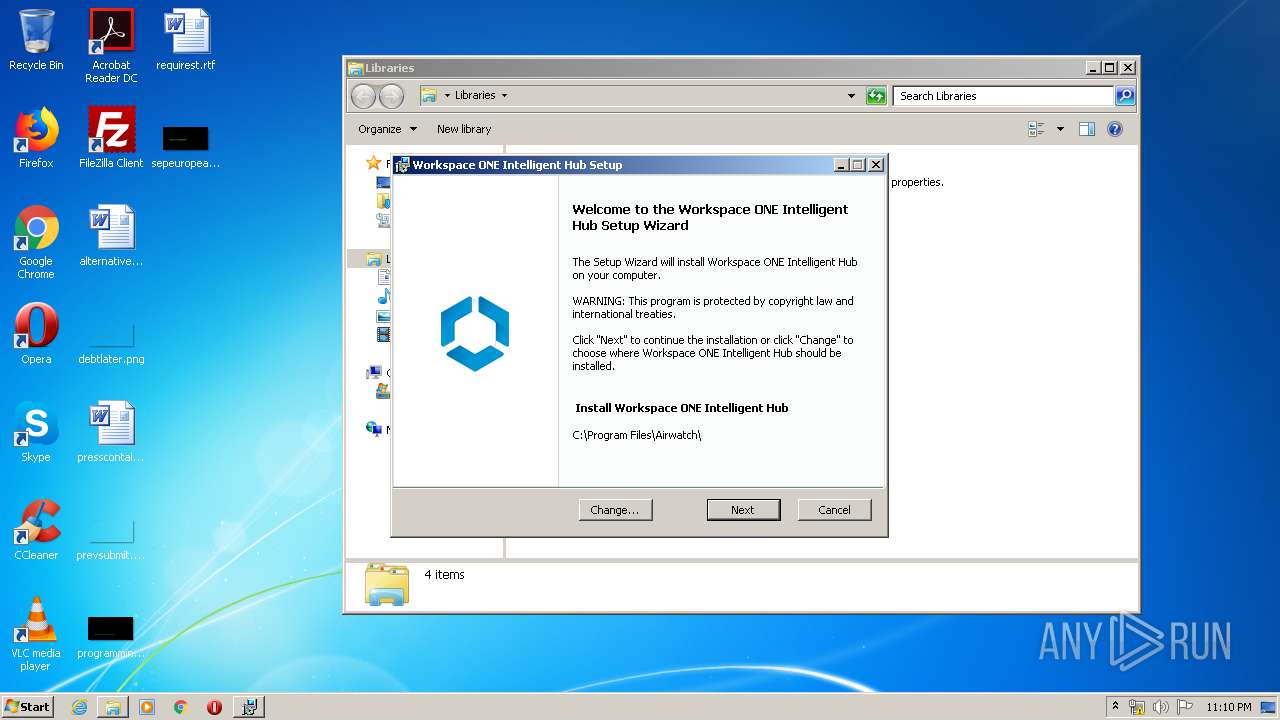
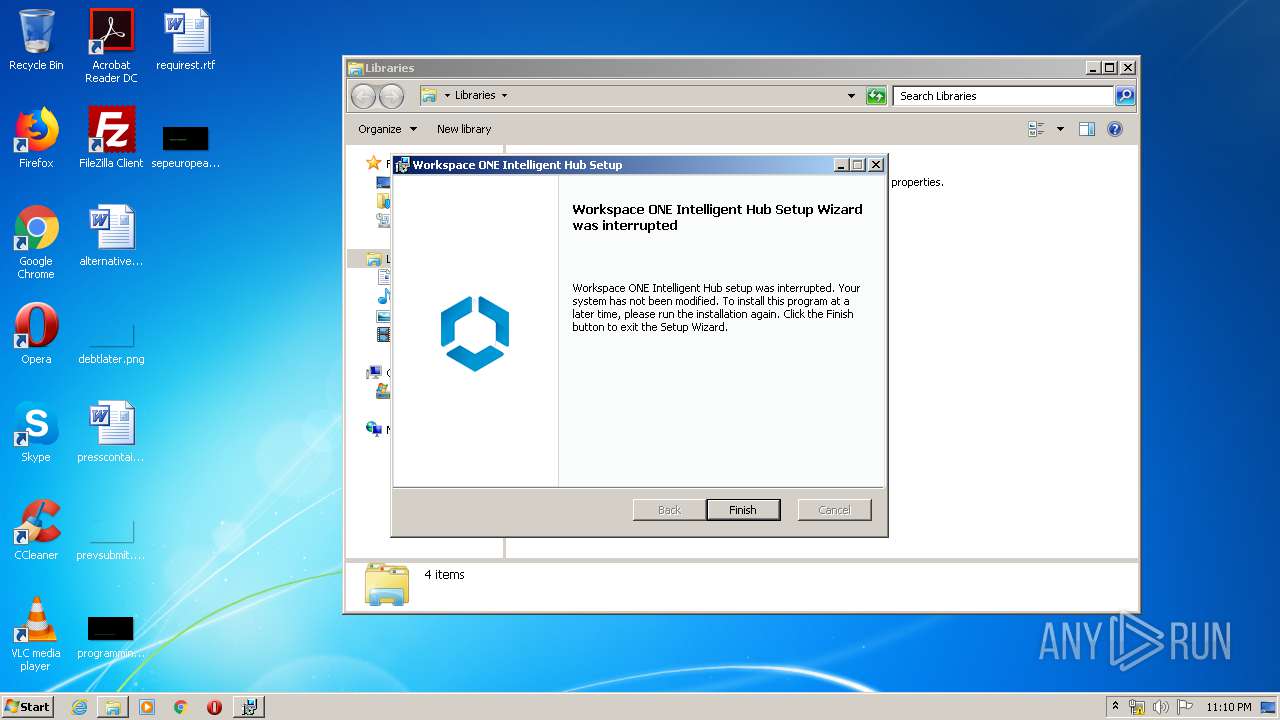
Starts Microsoft Installer
- chrome.exe (PID: 620)
Modifies files in Chrome extension folder
- chrome.exe (PID: 620)
Executed as Windows Service
- vssvc.exe (PID: 2540)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 3344)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2908)
- cmd.exe (PID: 3940)
Starts application with an unusual extension
- msiexec.exe (PID: 3664)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3664)
- msiexec.exe (PID: 628)
INFO
Reads the hosts file
- chrome.exe (PID: 620)
- chrome.exe (PID: 3928)
Reads settings of System Certificates
- chrome.exe (PID: 620)
Application launched itself
- chrome.exe (PID: 620)
- msiexec.exe (PID: 628)
Reads Internet Cache Settings
- chrome.exe (PID: 620)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 628)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2540)
Creates a software uninstall entry
- msiexec.exe (PID: 628)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 3344)
Starts application with an unusual extension
- msiexec.exe (PID: 628)
Application was dropped or rewritten from another process
- MSI8F9F.tmp (PID: 3908)
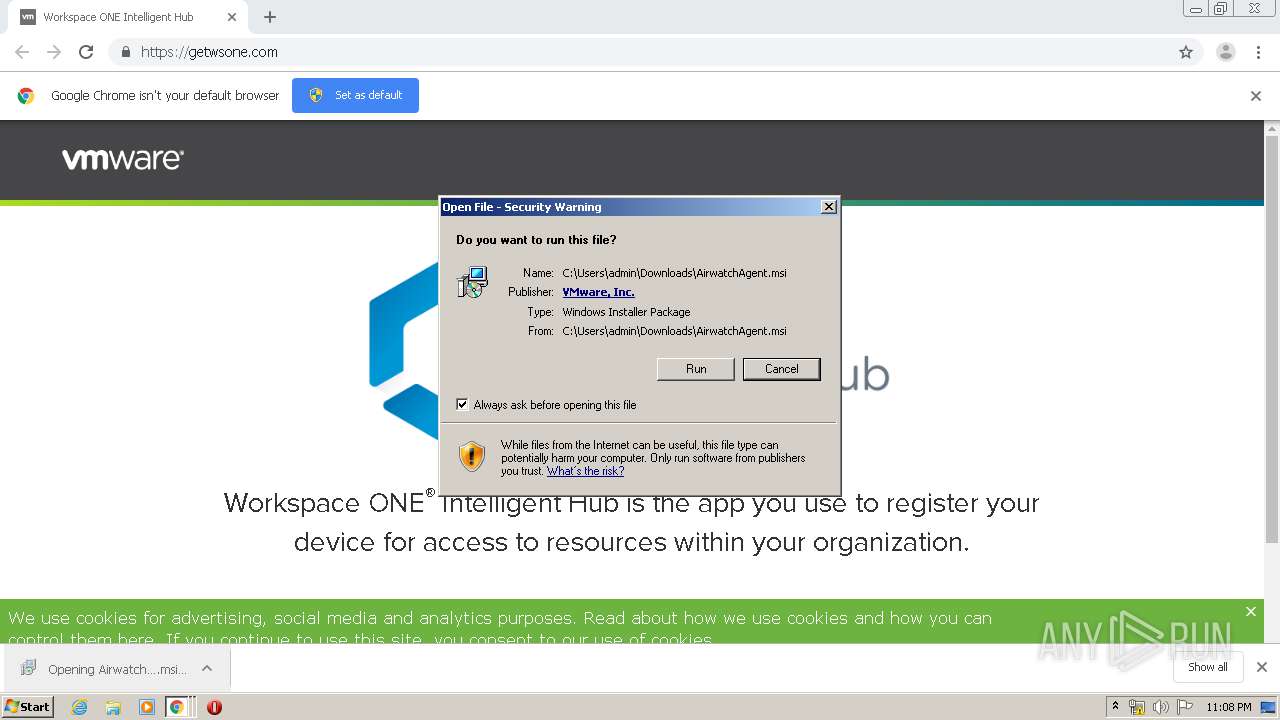
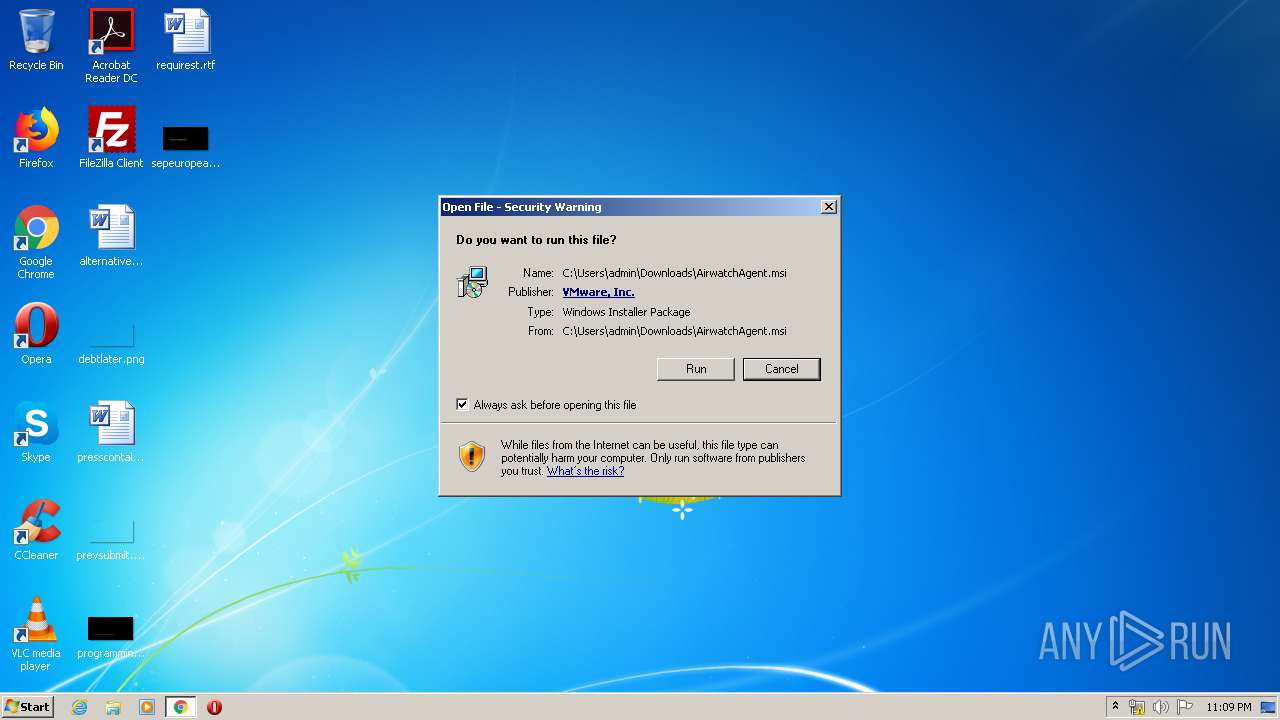
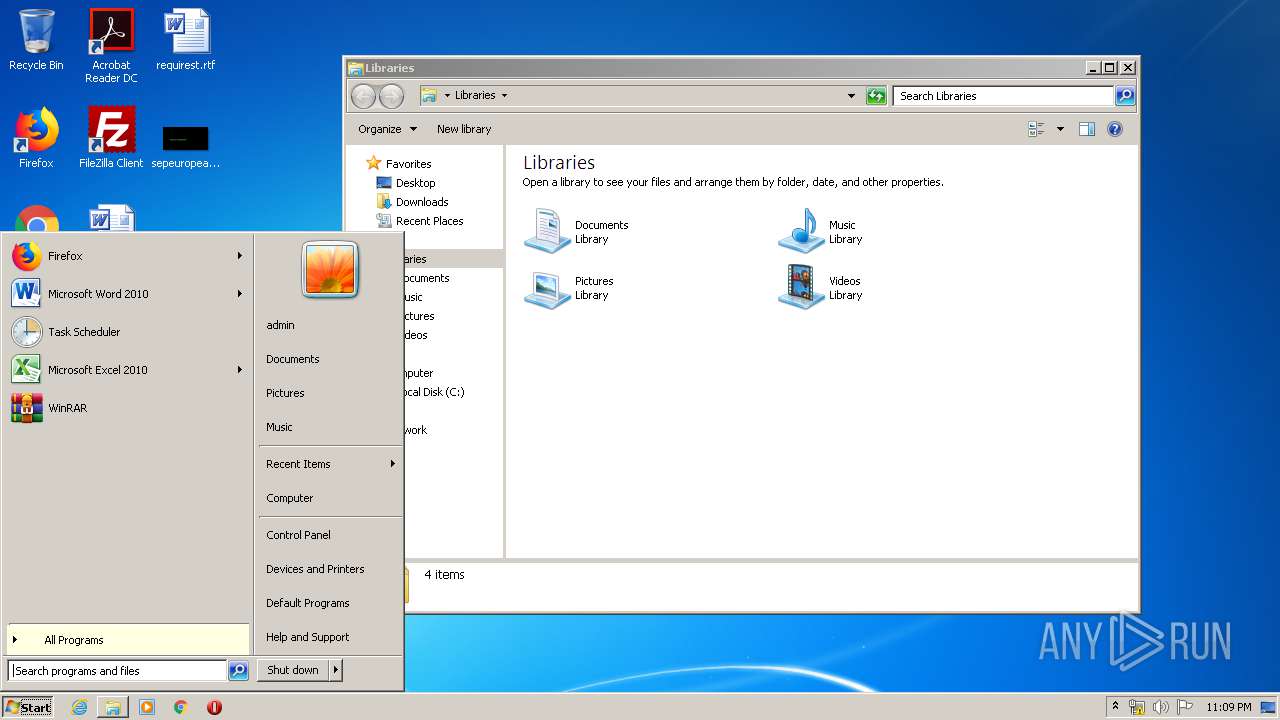
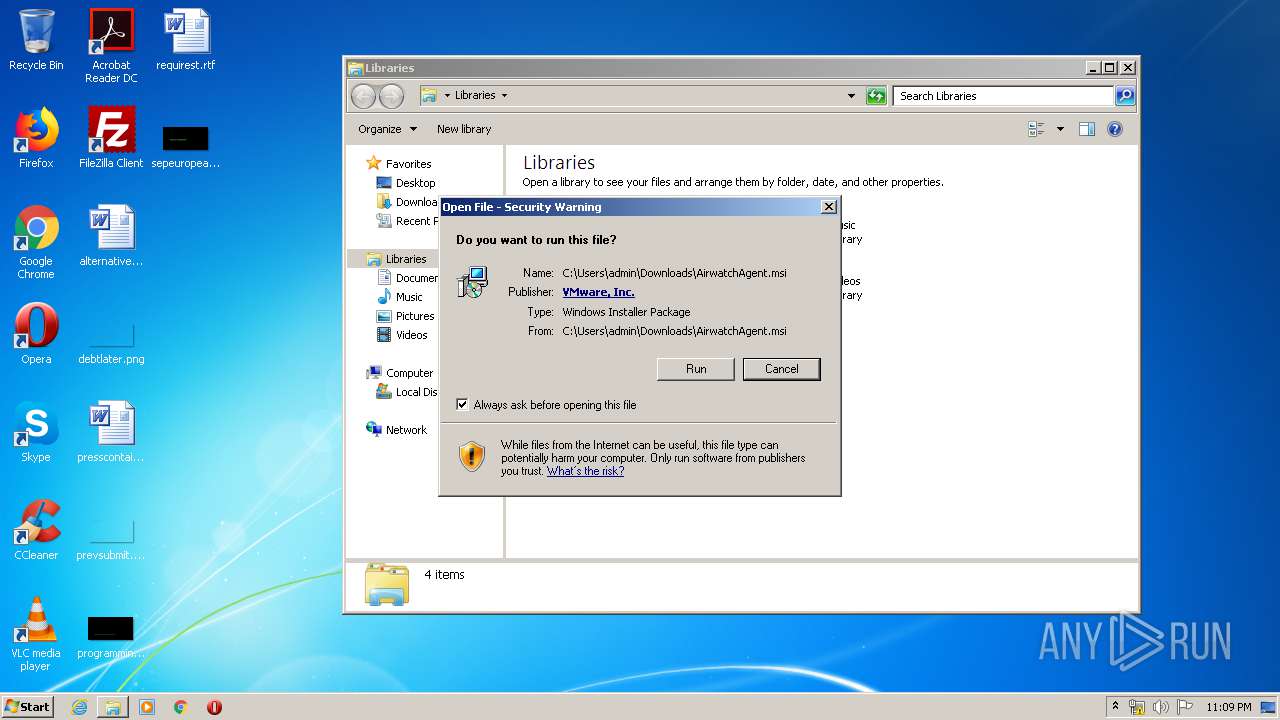
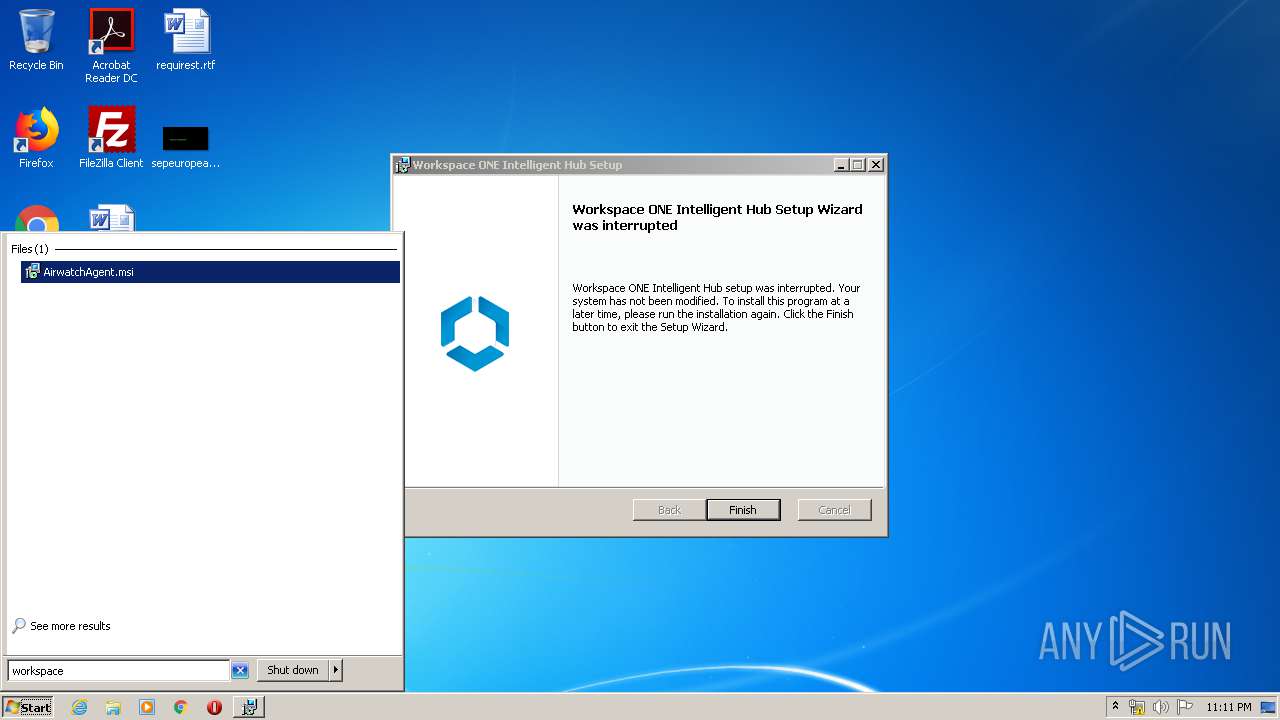
Manual execution by user
- explorer.exe (PID: 3224)
- msiexec.exe (PID: 2664)
Creates files in the program directory
- msiexec.exe (PID: 628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
44
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Users\admin\AppData\Local\Temp\MSIB3DA.tmp" 1 "C:\Users\admin\AppData\Local\Temp\MSI8f5e8.LOG" | C:\Users\admin\AppData\Local\Temp\MSIB3DA.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 20.04.1.0 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11177638804555645811 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10271895837729411312 --mojo-platform-channel-handle=4152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8788790151709130126 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://getwsone.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15183900079841307148 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14111059463870078017 --mojo-platform-channel-handle=4132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe" "C:\Program Files\Airwatch\AgentUI\VMware.WUA.ComLibraryX86.dll" /codebase /u | C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft .NET Assembly Registration Utility Exit code: 100 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\MsiExec.exe -Embedding 2442155334B66317A803A527E9C1DB31 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 983
Read events
1 519
Write events
701
Delete events
763
Modification events
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 620-13231461985774375 |
Value: 259 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
242
Suspicious files
93
Text files
238
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E978562-26C.pma | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\871a030a-14a2-47c5-b733-e16b742baa76.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6e1fc.TMP | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa6e24a.TMP | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e392.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
118
DNS requests
89
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3928 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3928 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3928 | chrome.exe | GET | 200 | 74.125.173.137:80 | http://r4---sn-4g5ednsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=89.187.165.47&mm=28&mn=sn-4g5ednsy&ms=nvh&mt=1586988312&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3928 | chrome.exe | GET | 200 | 173.194.188.7:80 | http://r2---sn-4g5edns7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=89.187.165.47&mm=28&mn=sn-4g5edns7&ms=nvh&mt=1586988312&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 45.60.131.96:443 | getwsone.com | — | US | unknown |
3928 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 216.58.207.42:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 13.225.73.59:443 | api.demandbase.com | — | US | malicious |
3928 | chrome.exe | 66.117.29.11:443 | vmware.tt.omtrdc.net | Adobe Systems Inc. | US | whitelisted |
3928 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 2.20.168.134:443 | c.evidon.com | Akamai Technologies, Inc. | — | unknown |
3928 | chrome.exe | 104.111.215.74:443 | use.typekit.net | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getwsone.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
api.demandbase.com |
| whitelisted |
tags.tiqcdn.com |
| whitelisted |
storage.googleapis.com |
| whitelisted |
www.vmware.com |
| whitelisted |
wurfl.io |
| whitelisted |