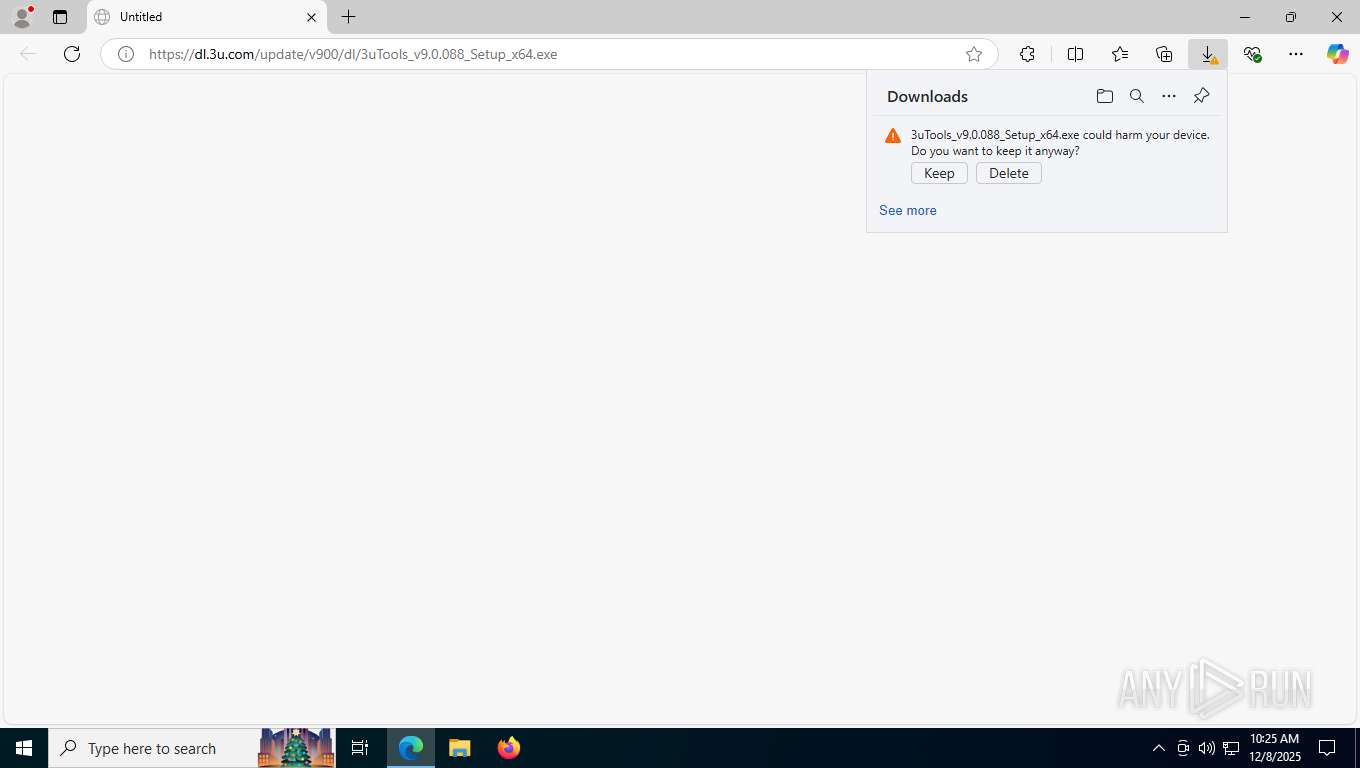
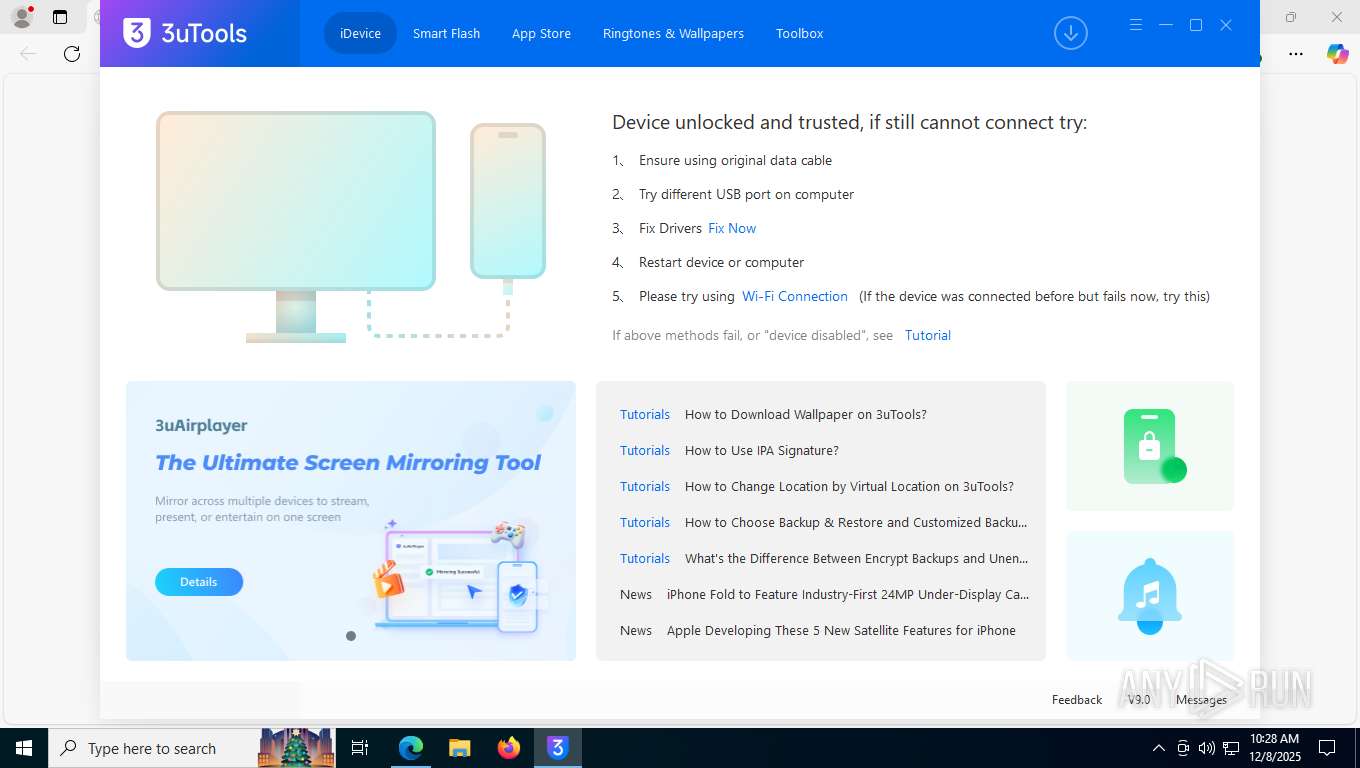
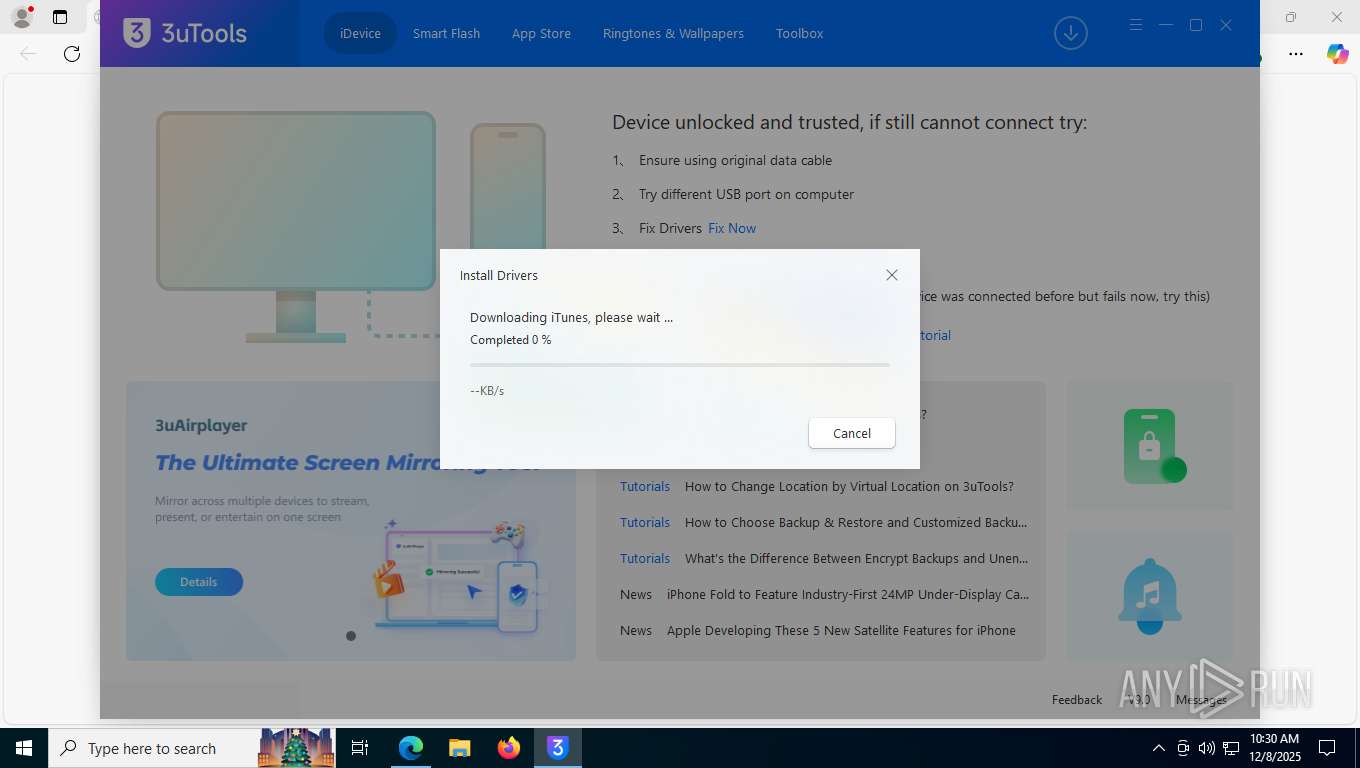
| URL: | https://dl.3u.com/update/v900/dl/3uTools_v9.0.088_Setup_x64.exe |
| Full analysis: | https://app.any.run/tasks/05ff9f5e-d7db-41bf-a260-8280e634d38c |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2025, 10:25:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D3817A53F8389744D01217FECE99A4DB |
| SHA1: | B5EF07635013EA04434C859EBEDEB55A14869B39 |
| SHA256: | BEDFE95B3DE043B32D7355ACC7EA9D76775468219F9E3C10D704D0060816C5A1 |
| SSDEEP: | 3:N8RRNmE/KN9Af6nzTtAC:2BR/GvzT |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process creates files with name similar to system file names
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
Executable content was dropped or overwritten
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uTools.exe (PID: 9124)
- pnputil.exe (PID: 8504)
- pnputil.exe (PID: 8652)
- pnputil.exe (PID: 3088)
Drops 7-zip archiver for unpacking
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
Process drops legitimate windows executable
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uTools.exe (PID: 9124)
Reads security settings of Internet Explorer
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uLauncher.exe (PID: 9080)
- updater.exe (PID: 9100)
- 3uTools.exe (PID: 9124)
The process drops C-runtime libraries
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
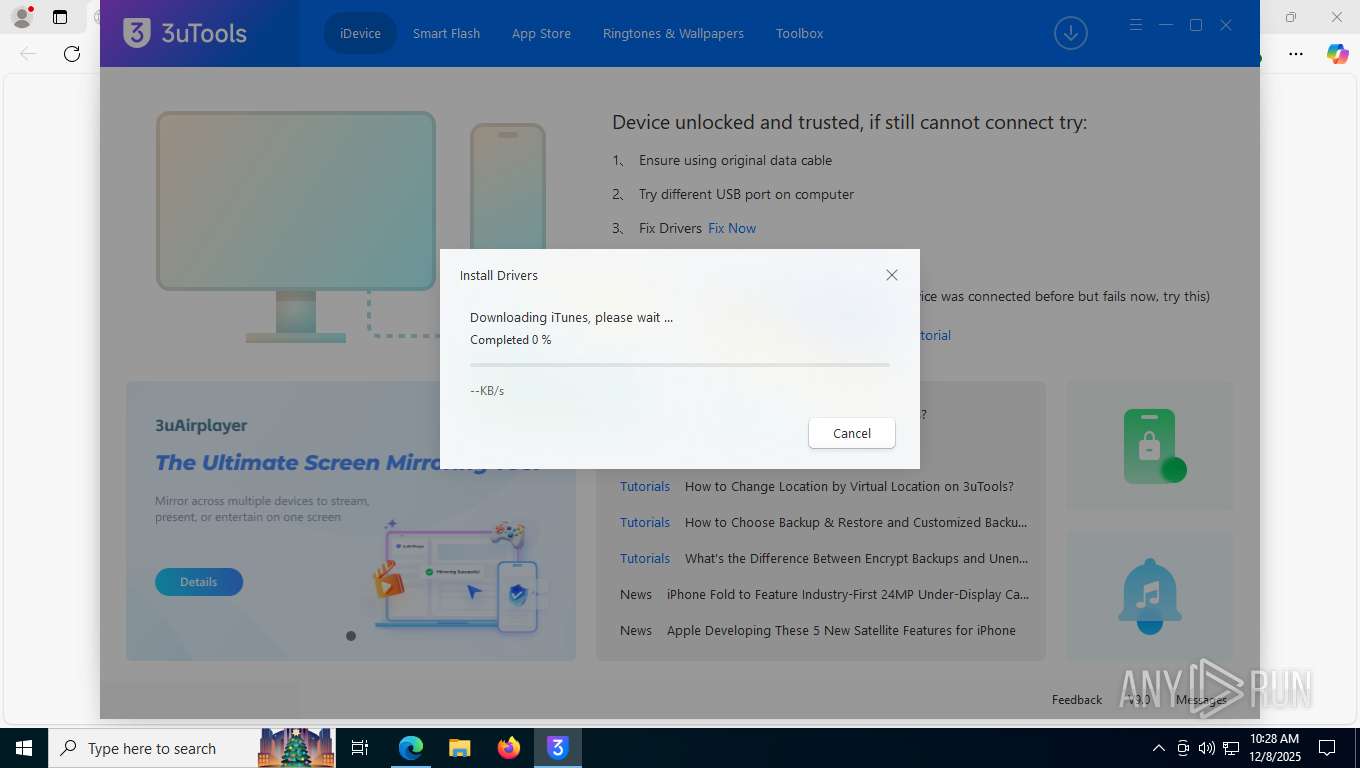
Drops a system driver (possible attempt to evade defenses)
- 3uTools.exe (PID: 9124)
- pnputil.exe (PID: 8652)
- drvinst.exe (PID: 2580)
- pnputil.exe (PID: 8504)
- drvinst.exe (PID: 816)
- pnputil.exe (PID: 3088)
- drvinst.exe (PID: 8996)
Takes ownership (TAKEOWN.EXE)
- InfInstallerx64.exe (PID: 1044)
- InfInstallerx64.exe (PID: 8684)
- InfInstallerx64.exe (PID: 6460)
Uses ICACLS.EXE to modify access control lists
- InfInstallerx64.exe (PID: 1044)
- InfInstallerx64.exe (PID: 8684)
- InfInstallerx64.exe (PID: 6460)
There is functionality for taking screenshot (YARA)
- 3uTools.exe (PID: 9124)
- QtWebEngineProcess.exe (PID: 4104)
- QtWebEngineProcess.exe (PID: 3316)
- QtWebEngineProcess.exe (PID: 6272)
- QtWebEngineProcess.exe (PID: 8988)
INFO
Application launched itself
- msedge.exe (PID: 7552)
Executable content was dropped or overwritten
- msedge.exe (PID: 7552)
Reads the computer name
- identity_helper.exe (PID: 6600)
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uLauncher.exe (PID: 9080)
- updater.exe (PID: 9100)
- 3uTools.exe (PID: 9124)
- QtWebEngineProcess.exe (PID: 4104)
- drvinst.exe (PID: 2580)
- drvinst.exe (PID: 816)
- drvinst.exe (PID: 8996)
Checks supported languages
- identity_helper.exe (PID: 6600)
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8912)
- 3uLauncher.exe (PID: 9080)
- updater.exe (PID: 9100)
- 3uTools.exe (PID: 9124)
- QtWebEngineProcess.exe (PID: 4104)
- QtWebEngineProcess.exe (PID: 3316)
- QtWebEngineProcess.exe (PID: 6272)
- 3uViewer.exe (PID: 3168)
- 3uViewer.exe (PID: 7224)
- InfInstallerx64.exe (PID: 1044)
- QtWebEngineProcess.exe (PID: 8988)
- drvinst.exe (PID: 2580)
- InfInstallerx64.exe (PID: 8684)
- drvinst.exe (PID: 816)
- InfInstallerx64.exe (PID: 6460)
- drvinst.exe (PID: 8996)
Reads Environment values
- identity_helper.exe (PID: 6600)
Creates files in the program directory
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uLauncher.exe (PID: 9080)
- updater.exe (PID: 9100)
- 3uTools.exe (PID: 9124)
Create files in a temporary directory
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uTools.exe (PID: 9124)
- pnputil.exe (PID: 8652)
- pnputil.exe (PID: 8504)
- pnputil.exe (PID: 3088)
The sample compiled with english language support
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uTools.exe (PID: 9124)
- drvinst.exe (PID: 2580)
- pnputil.exe (PID: 8504)
- drvinst.exe (PID: 816)
- pnputil.exe (PID: 8652)
- drvinst.exe (PID: 8996)
- pnputil.exe (PID: 3088)
The sample compiled with chinese language support
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
Creates a software uninstall entry
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
Checks proxy server information
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- slui.exe (PID: 8304)
- 3uLauncher.exe (PID: 9080)
- updater.exe (PID: 9100)
Process checks computer location settings
- 3uTools_v9.0.088_Setup_x64.exe (PID: 8884)
- 3uTools.exe (PID: 9124)
- QtWebEngineProcess.exe (PID: 6272)
- QtWebEngineProcess.exe (PID: 8988)
- QtWebEngineProcess.exe (PID: 3316)
Creates files or folders in the user directory
- 3uLauncher.exe (PID: 9080)
- 3uTools.exe (PID: 9124)
- QtWebEngineProcess.exe (PID: 4104)
Reads the machine GUID from the registry
- 3uLauncher.exe (PID: 9080)
- 3uTools.exe (PID: 9124)
- drvinst.exe (PID: 2580)
- drvinst.exe (PID: 816)
- drvinst.exe (PID: 8996)
Detects GO elliptic curve encryption (YARA)
- 3uTools.exe (PID: 9124)
UPX packer has been detected
- 3uTools.exe (PID: 9124)
Application based on Golang
- 3uTools.exe (PID: 9124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
77
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 816 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{fb5684ae-5528-bf46-8f41-c7cad9fc8fd0}\AppleRSM.inf" "9" "4c7809927" "00000000000001F8" "WinSta0\Default" "00000000000001FC" "208" "C:\Users\admin\AppData\Local\Temp\itunes_fix\applersm\x64" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 940 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | InfInstallerx64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | "C:\Program Files\3uTools9\files\inf\InfInstallerx64.exe" -i "C:\Users\admin\AppData\Local\Temp\itunes_fix\applekis\x64\AppleKIS.inf" | C:\Program Files\3uTools9\files\inf\InfInstallerx64.exe | — | 3uTools.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pnputil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2016 | takeown /F C:\Windows\System32\DriverStore\FileRepository\ /A | C:\Windows\System32\takeown.exe | — | InfInstallerx64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{30bef985-c9d6-c242-bbd2-e10ea4cba975}\AppleKIS.inf" "9" "4639b046f" "00000000000001CC" "WinSta0\Default" "00000000000001C8" "208" "C:\Users\admin\AppData\Local\Temp\itunes_fix\applekis\x64" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3088 | pnputil -i -a "C:\Users\admin\AppData\Local\Temp\itunes_fix\appleusbdevice\x64\AppleUsb.inf" | C:\Windows\System32\pnputil.exe | InfInstallerx64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft PnP Utility - Tool to add, delete, export, and enumerate driver packages. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3168 | 3uViewer.exe /reg 1 | C:\Program Files\3uTools9\3uViewer.exe | — | 3uTools.exe | |||||||||||
User: admin Company: Shenzhen Aidapu Network Technology Co.,Ltd. Integrity Level: HIGH Description: Image Viewer Exit code: 0 Version: 1.0.3.0 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\3uTools9\QtWebEngineProcess.exe" --type=renderer --no-sandbox --disable-speech-api --enable-threaded-compositing --enable-features=AllowContentInitiatedDataUrlNavigations,TracingServiceInProcess --disable-features=BackgroundFetch,ConsolidatedMovementXY,DnsOverHttpsUpgrade,FormControlsRefresh,MojoVideoCapture,PictureInPicture,SmsReceiver,UseSkiaRenderer,WebPayments,WebUSB --disable-gpu-compositing --lang=en-US --webengine-schemes=qrc:sLV --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=3144 /prefetch:1 | C:\Program Files\3uTools9\QtWebEngineProcess.exe | — | 3uTools.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: HIGH Description: C++ Application Development Framework Version: 5.15.2.0 Modules
| |||||||||||||||
| 3464 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=6056,i,6435374218743601307,1776493227380778180,262144 --variations-seed-version --mojo-platform-channel-handle=6096 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
26 884
Read events
26 850
Write events
28
Delete events
6
Modification events
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\3uTools9_x64 |
| Operation: | write | Name: | AppPath |
Value: C:\Program Files\3uTools9\ | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\3uTools9_x64 |
| Operation: | write | Name: | Version |
Value: 9.0.088 | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\3uTools9_x64 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\3uTools9\3uLauncher.exe | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\3uTools9_x64 |
| Operation: | write | Name: | DisplayName |
Value: 3uTools | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\3uTools9_x64 |
| Operation: | write | Name: | DisplayVersion |
Value: 9.0.088 | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\3uTools9_x64 |
| Operation: | write | Name: | Publisher |
Value: Shenzhen Aidapu Network Technology Co.,Ltd. | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\3uTools9_x64 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\3uTools9\Uninstall.exe | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\3uTools9_x64 |
| Operation: | write | Name: | URLInfoAbout |
Value: https://www.3u.com | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8884) 3uTools_v9.0.088_Setup_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
288
Suspicious files
465
Text files
250
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFf699e.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFf69cd.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFf69cd.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFf69cd.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFf69cd.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
108
DNS requests
80
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4920 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5596 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7880 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:GuTJa8pdsjvCTC9Ioj4GITqAcfkQJLc6GmOD88fDCcA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 97 b | whitelisted |
8944 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
4920 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
8944 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
8944 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 408 b | whitelisted |
8944 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 401 b | whitelisted |
8944 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
8944 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4920 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5628 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 184.86.251.14:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
7880 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7880 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7880 | msedge.exe | 142.250.185.161:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
7880 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
dl.3u.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
— | — | Potentially Bad Traffic | ET HUNTING Double User-Agent (User-Agent User-Agent) |
Process | Message |
|---|---|
3uTools_v9.0.088_Setup_x64.exe | AdjustTokenPrivileges succed! |
3uTools.exe | Sandboxing disabled by user.
|
3uTools.exe | "https://tools.3u.com/hotUpdate/winpcupdate?params=dJkkpD4r9rYooJ7VjFEIL1u4D5pPPasFgKxidPBPF7ynhx1efLjcoszV4qF2e64f5JxJWjTEJTmw2j8WLSKVeoQn5%2BYaSZEgyCY6RhKPs%2Br6Tflyk2jAkP3rAacrqMaufGEjL8CbG%2B%2BUJpwpIfamy58%2B1nATLfRjc3oKY%2Bhu5rw%3D"
|
3uTools.exe | "{\"code\":0,\"message\":\"success\",\"data\":{\"update\":0,\"newVersion\":\"9.0.088\",\"url\":\"https://dl.3u.com/update/v900/x64/config_9.0.088.xml\",\"fileSize\":0,\"fileMd5\":\"\",\"fileType\":\"xml\",\"versionUpdateDate\":\"2025-11-11\",\"versionUpdate\":\"??:9.0.088 [2025-11-11 00:00]\\n1. The new 3uTools is launched.\\n\"}}"
|
3uTools.exe | new itunes "12.13.9.1"
|
3uTools.exe | SetUpKisDriver ret: 0 |
3uTools.exe | SetUpRSMDriver ret: 0 |
3uTools.exe | SetUpAppleUSBDeviceDriver ret: 0 |