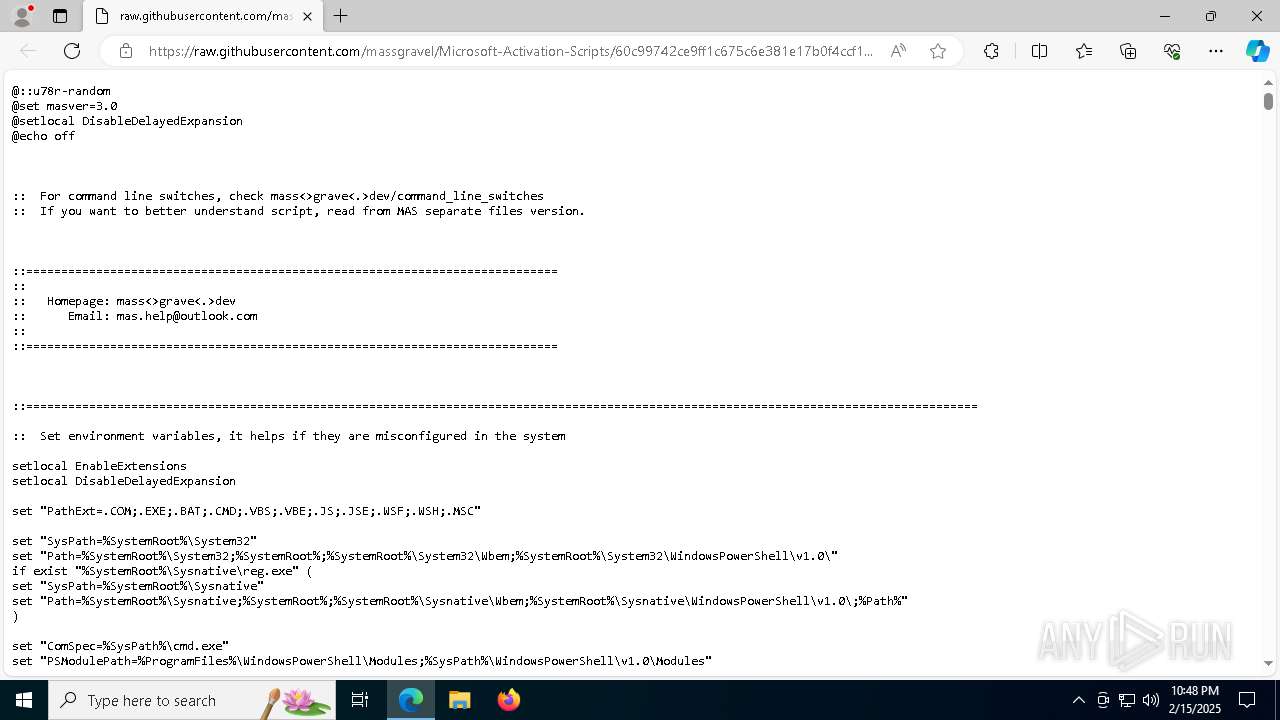
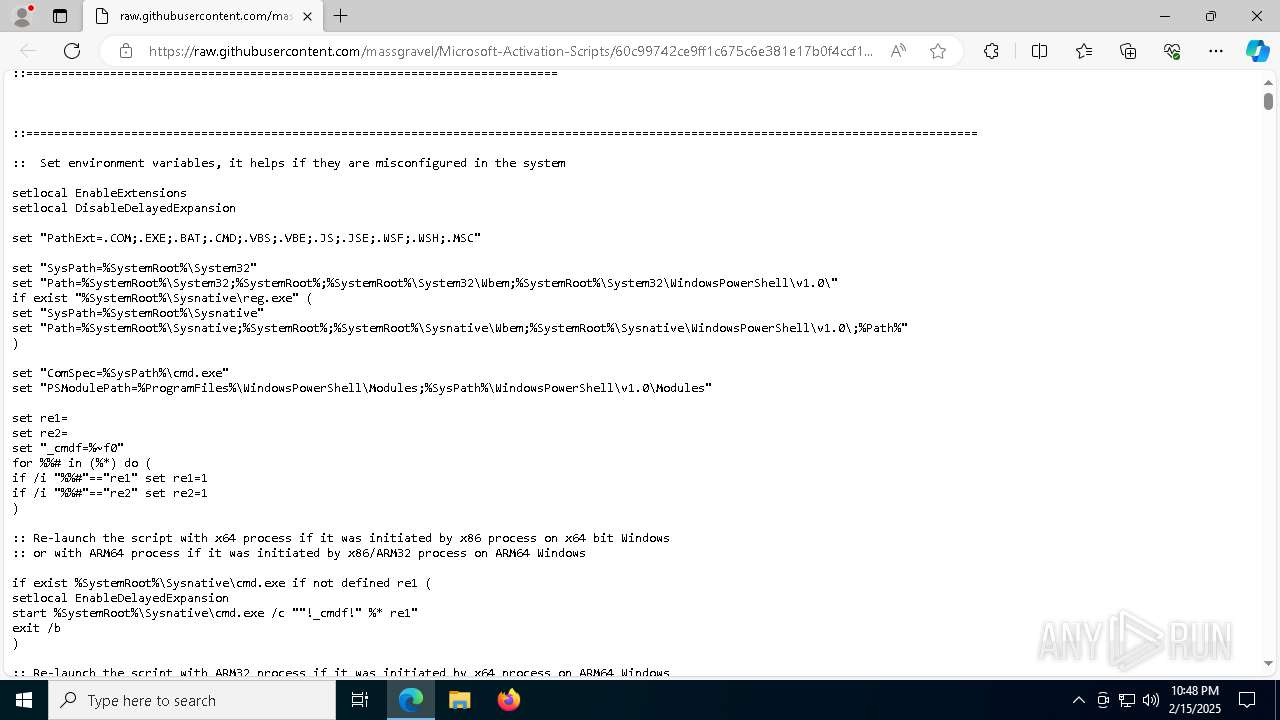
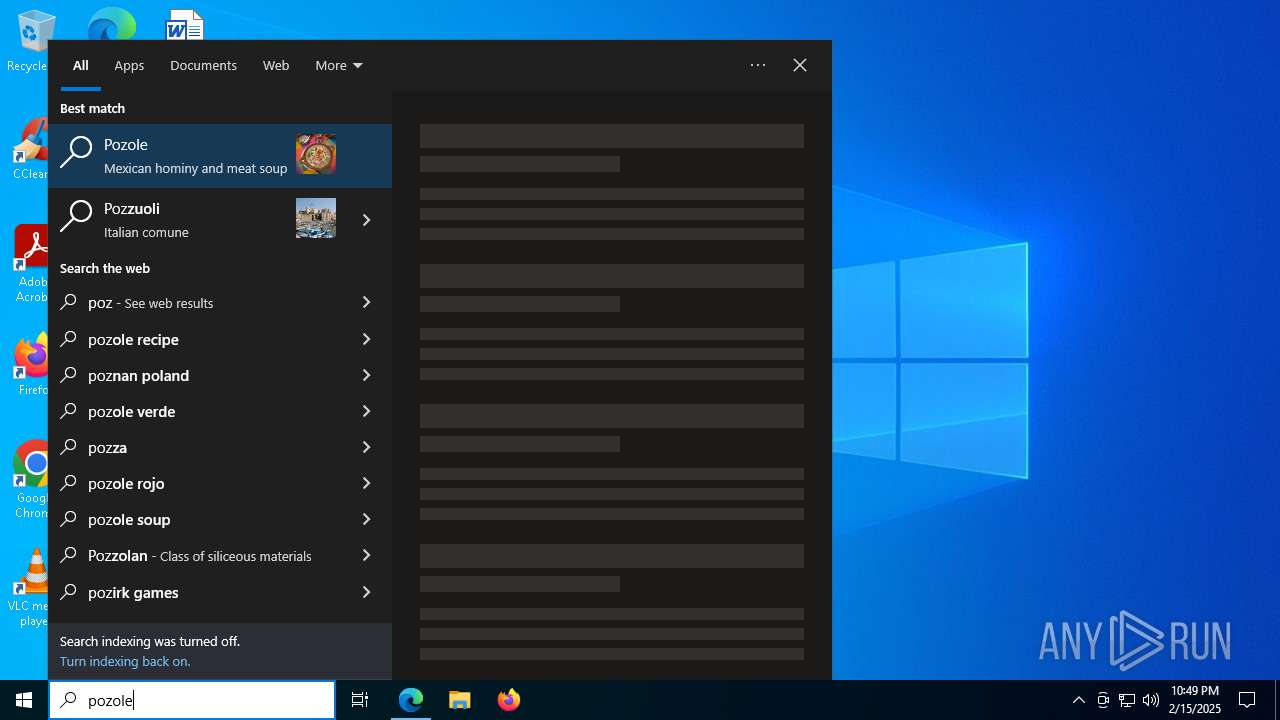
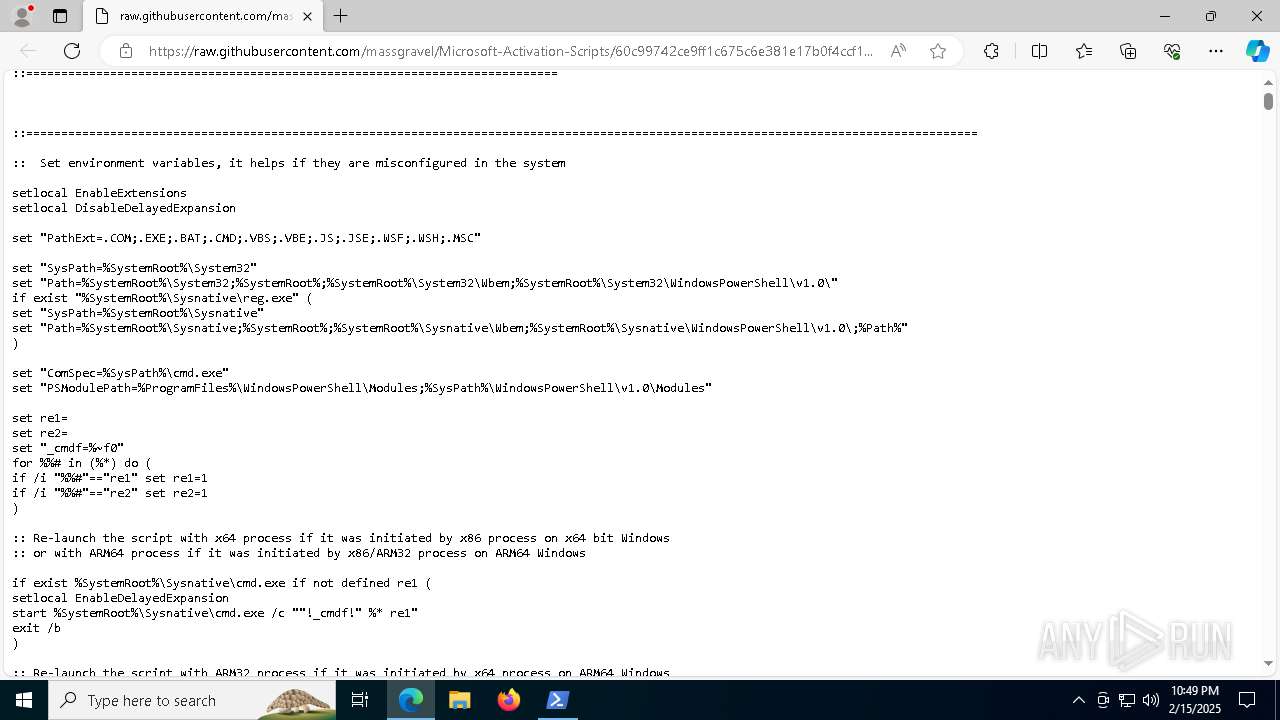
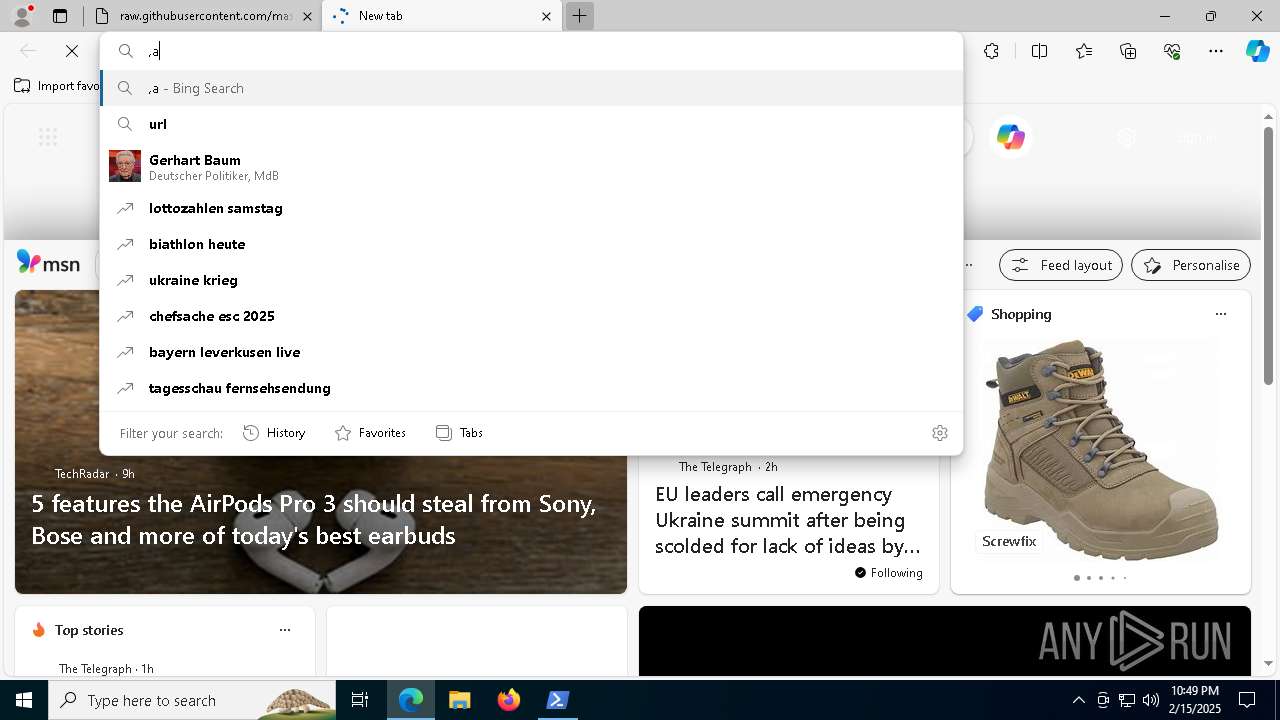
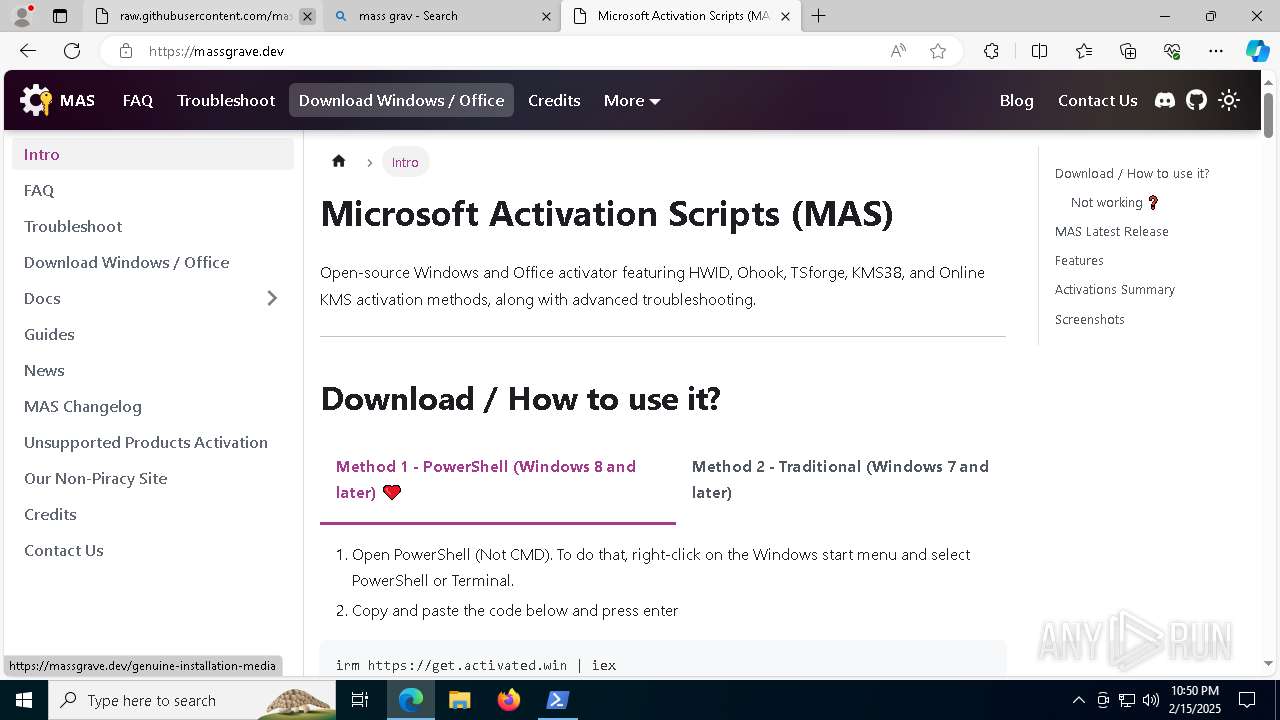
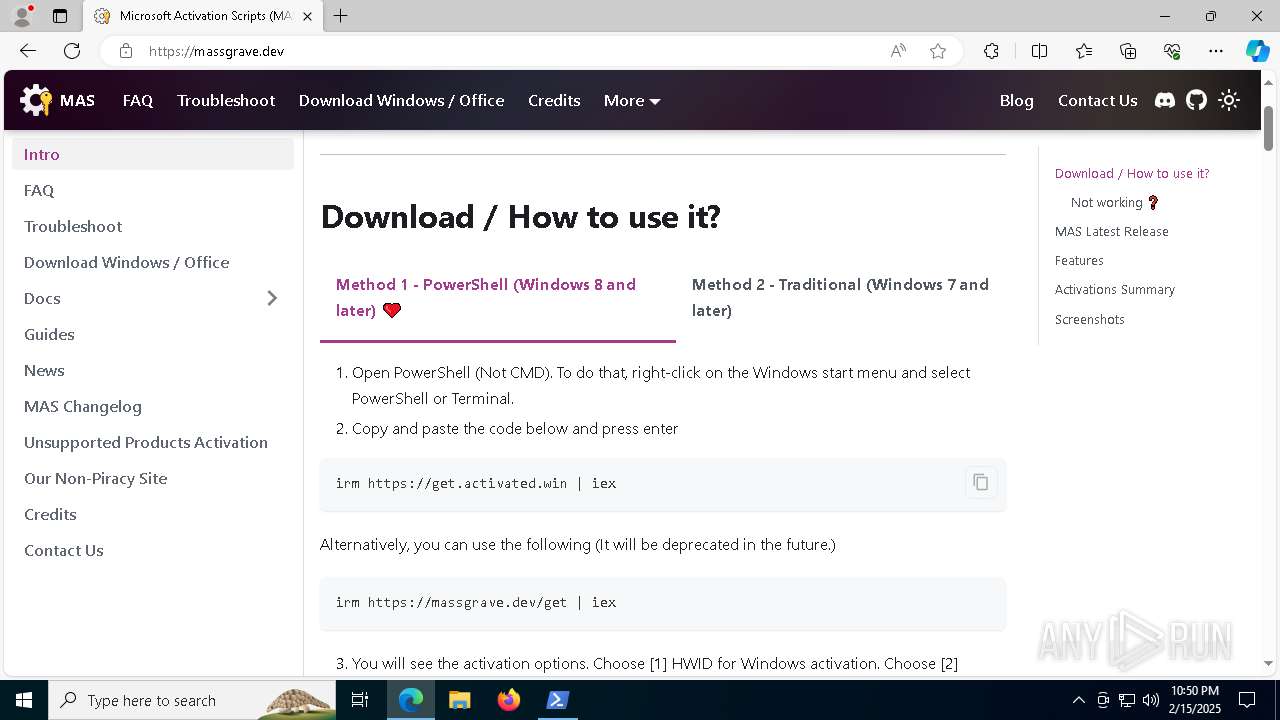
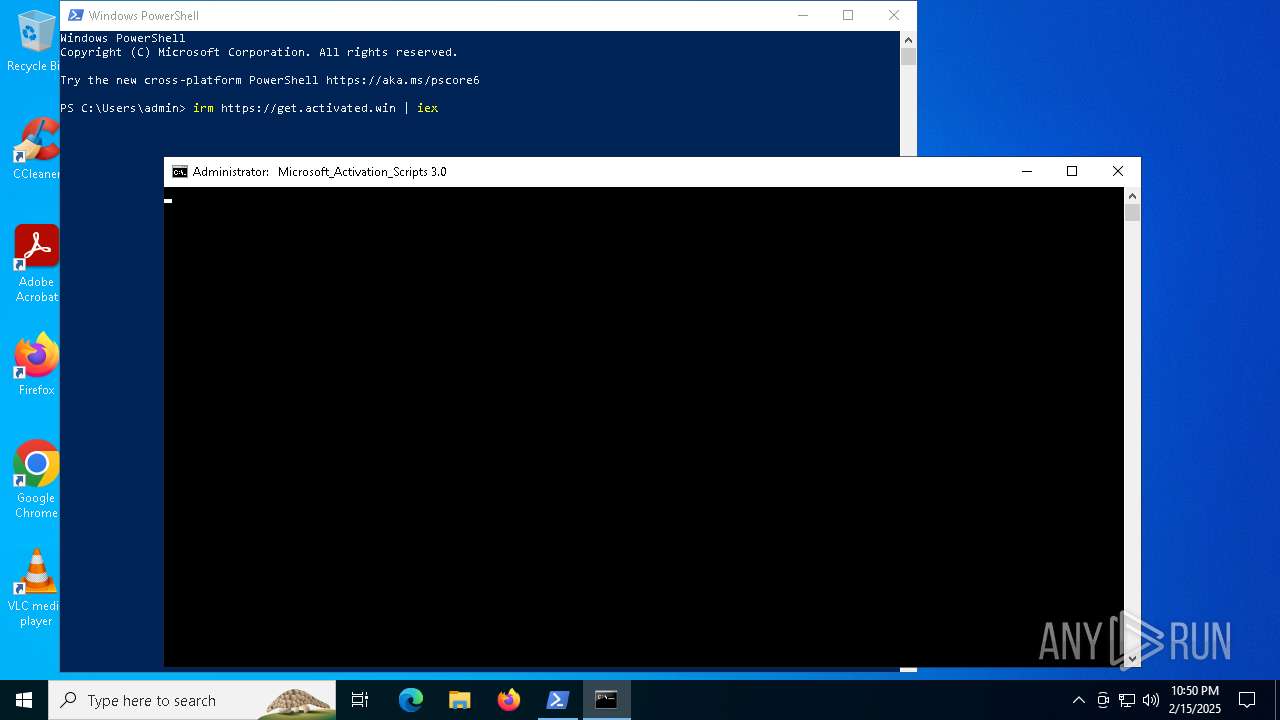
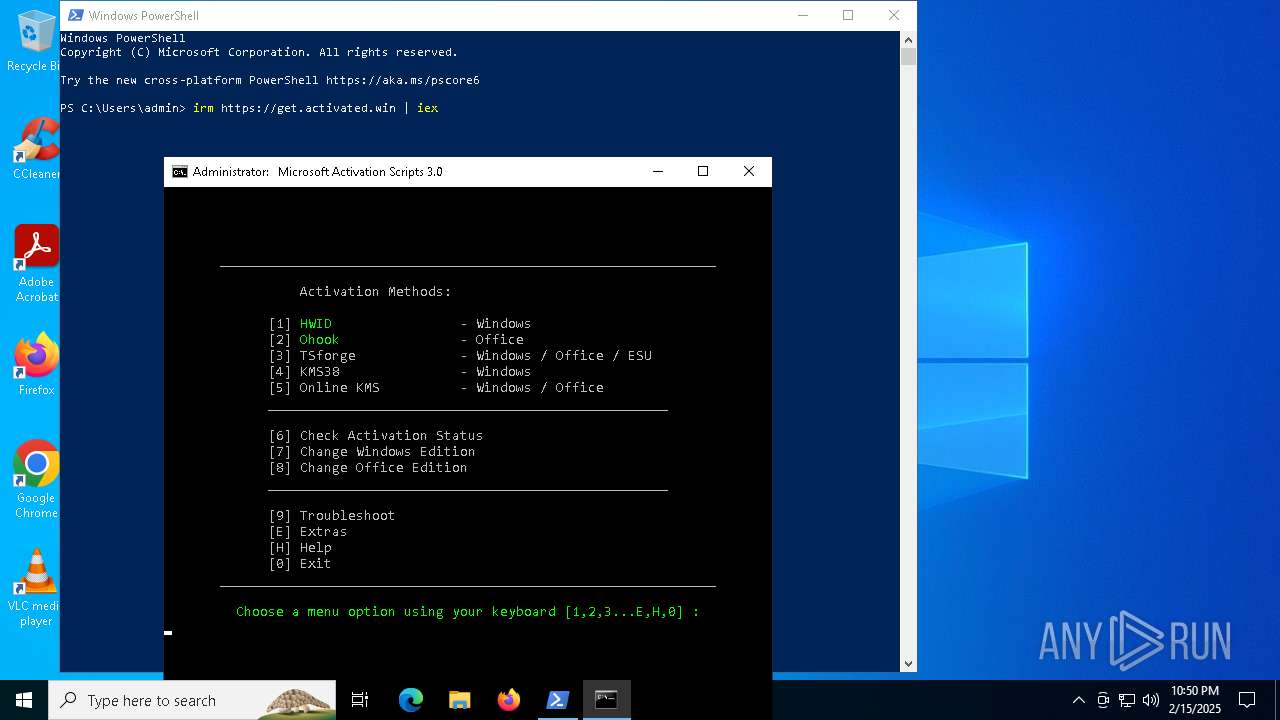
| URL: | https://raw.githubusercontent.com/massgravel/Microsoft-Activation-Scripts/60c99742ce9ff1c675c6e381e17b0f4ccf1a57bd/MAS/All-In-One-Version-KL/MAS_AIO.cmd |
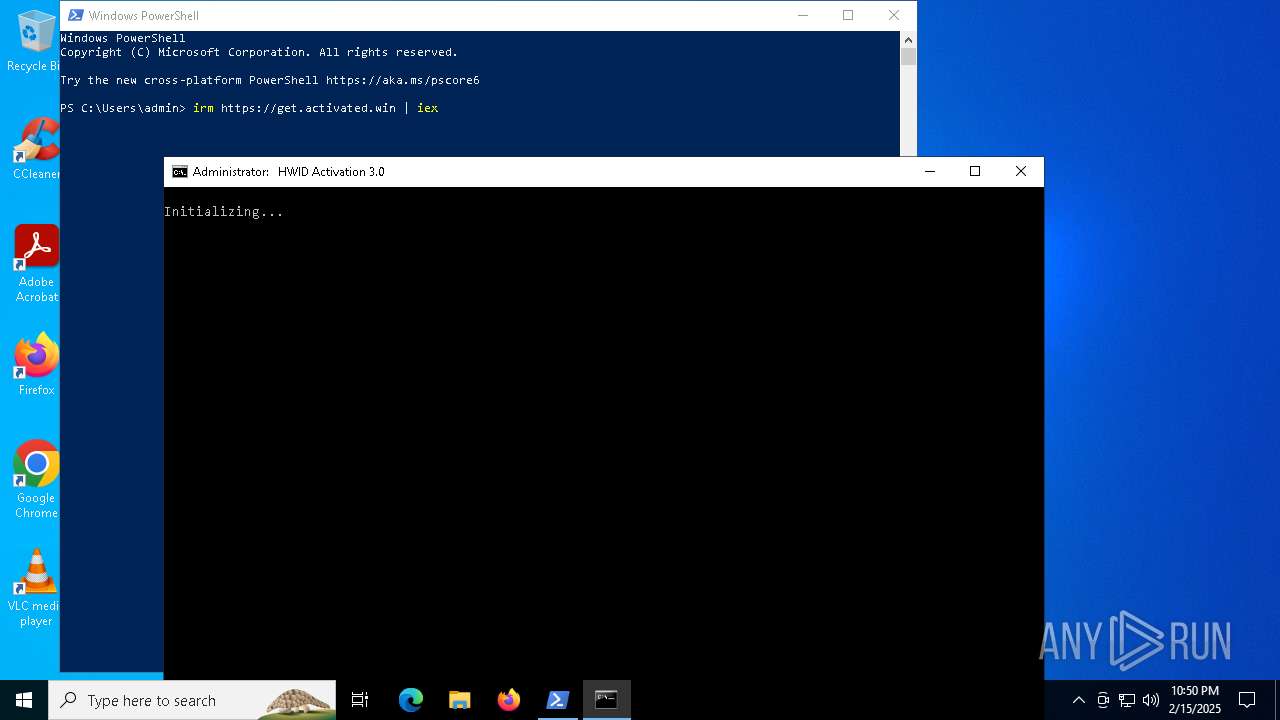
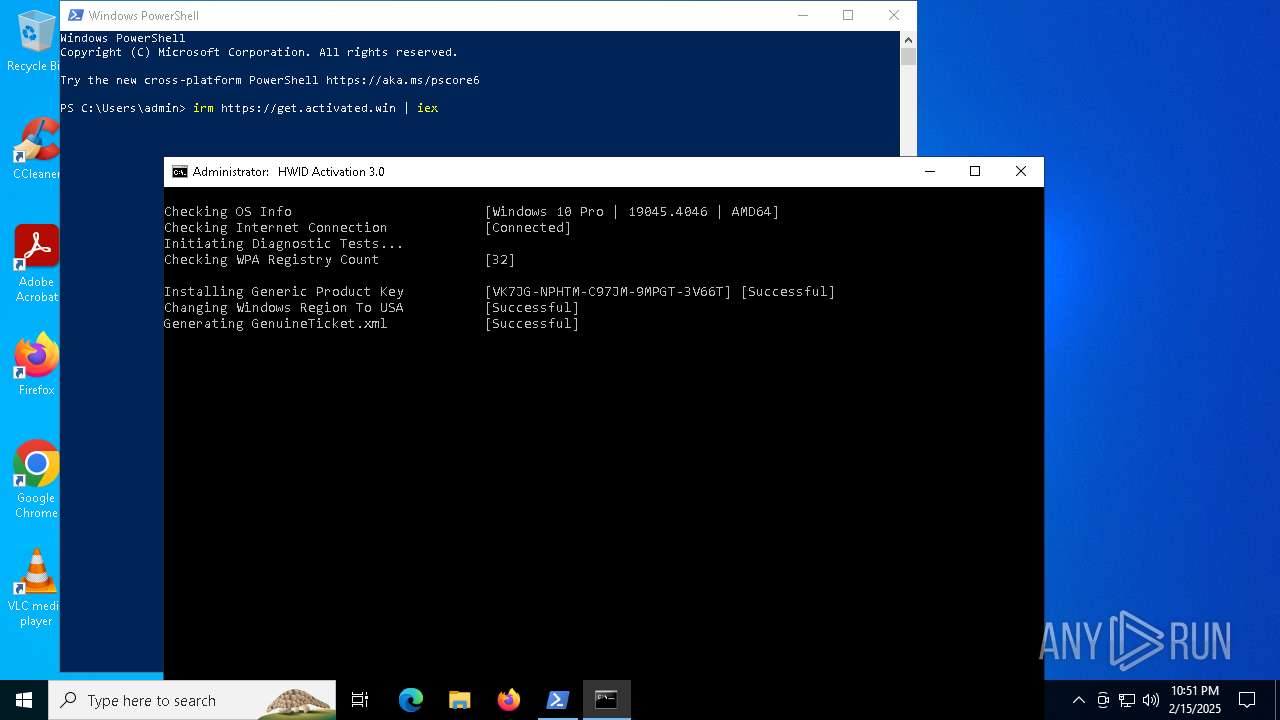
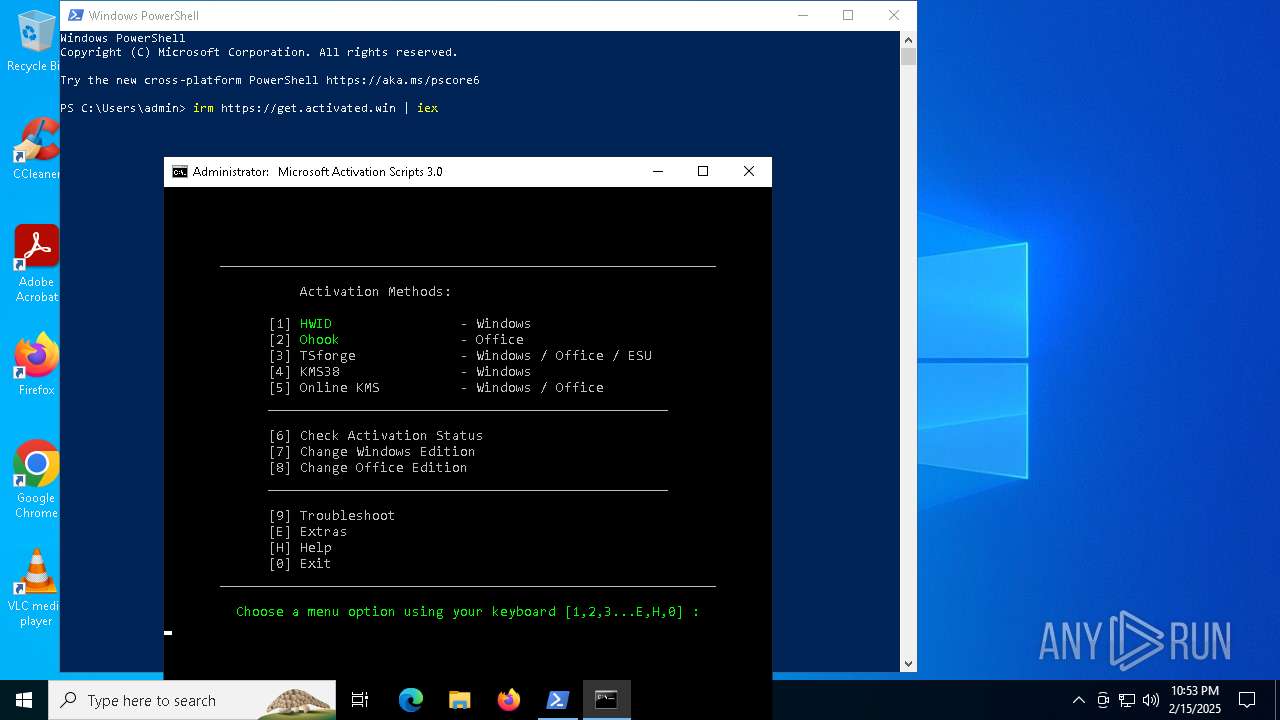
| Full analysis: | https://app.any.run/tasks/bddb68b1-687f-48ea-8a15-3d3d75d8fbd9 |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2025, 22:48:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 757AF8044650672FB17DC4AD0AC2B9D0 |
| SHA1: | 76E05B7C6159C933EFCB191CD39A78A4B5319C94 |
| SHA256: | BEDAB09BEA05190B9CBC199F4A9C68B028EE566326DE2CCD1231343FE0E0AB54 |
| SSDEEP: | 3:N8SGfALtGTzKoHXuukGR3RLLLGXUbVphEjGTz0SHVNO6//HtIqLAOAh9wln:2FMGnKzukGv/LGXUxXUGT4yV/50vDG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7620)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 7080)
- powershell.exe (PID: 3808)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7392)
Starts SC.EXE for service management
- cmd.exe (PID: 3544)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 6500)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7620)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 5488)
- powershell.exe (PID: 5028)
- cmd.exe (PID: 1760)
- powershell.exe (PID: 6380)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 6500)
Executing commands from ".cmd" file
- powershell.exe (PID: 7620)
- cmd.exe (PID: 3544)
- powershell.exe (PID: 5028)
- cmd.exe (PID: 5488)
- powershell.exe (PID: 6380)
- cmd.exe (PID: 6500)
Windows service management via SC.EXE
- sc.exe (PID: 5916)
- sc.exe (PID: 2092)
- sc.exe (PID: 6520)
- sc.exe (PID: 7504)
- sc.exe (PID: 8112)
- sc.exe (PID: 7088)
- sc.exe (PID: 7564)
- sc.exe (PID: 6632)
- sc.exe (PID: 7324)
- sc.exe (PID: 7100)
- sc.exe (PID: 7924)
- sc.exe (PID: 4968)
- sc.exe (PID: 7208)
- sc.exe (PID: 5696)
- sc.exe (PID: 5316)
- sc.exe (PID: 6580)
- sc.exe (PID: 4056)
- sc.exe (PID: 2452)
- sc.exe (PID: 6800)
- sc.exe (PID: 1808)
- sc.exe (PID: 7560)
- sc.exe (PID: 7260)
- sc.exe (PID: 1616)
- sc.exe (PID: 3040)
- sc.exe (PID: 7052)
- sc.exe (PID: 4908)
- sc.exe (PID: 900)
- sc.exe (PID: 1868)
- sc.exe (PID: 7488)
- sc.exe (PID: 7756)
- sc.exe (PID: 2420)
- sc.exe (PID: 7344)
- sc.exe (PID: 5032)
- sc.exe (PID: 7060)
- sc.exe (PID: 6976)
- sc.exe (PID: 5032)
- sc.exe (PID: 4512)
Application launched itself
- cmd.exe (PID: 7340)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 6384)
- powershell.exe (PID: 6904)
- powershell.exe (PID: 8028)
- powershell.exe (PID: 7244)
- ClipUp.exe (PID: 6384)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7260)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 7576)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3544)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 6500)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7260)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 7576)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7080)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 3808)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7392)
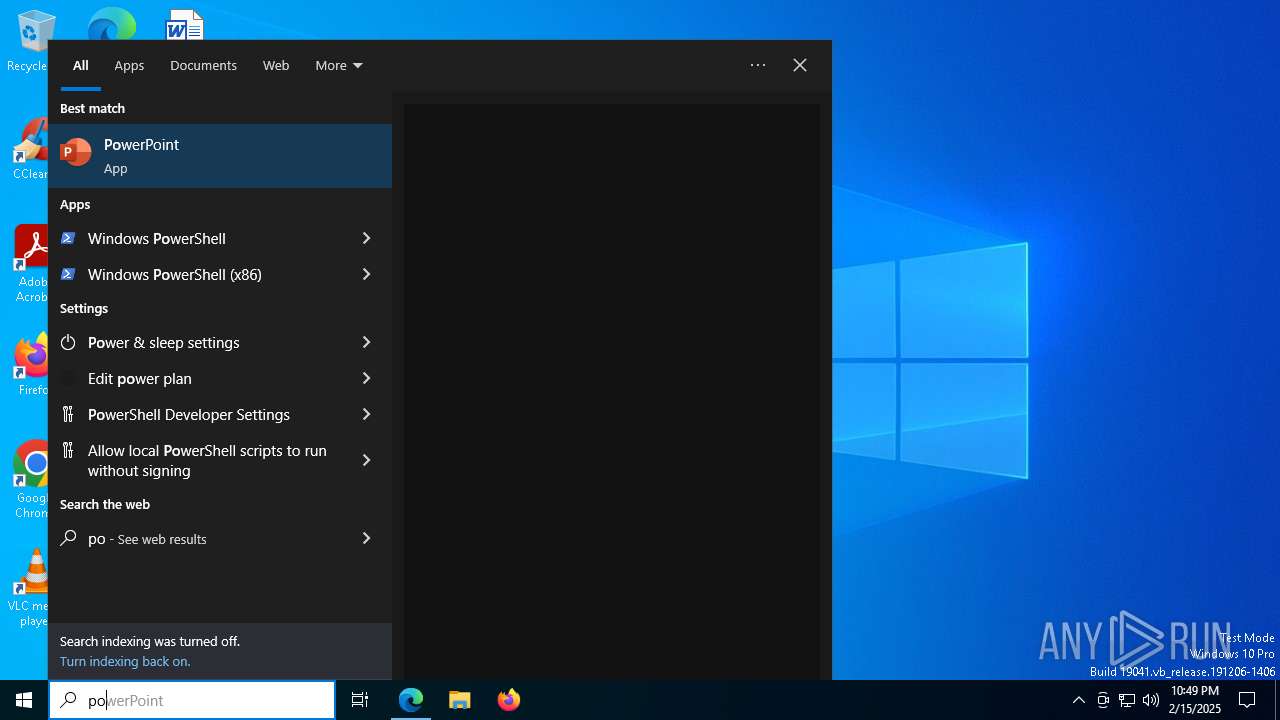
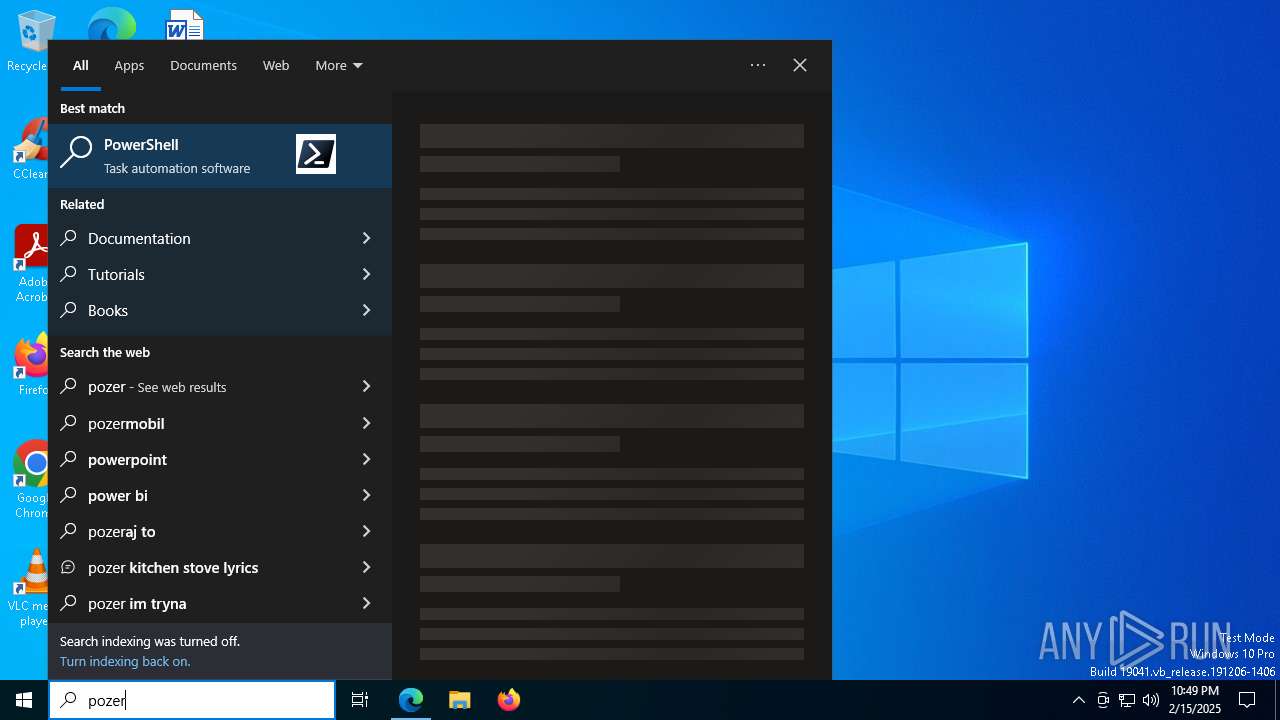
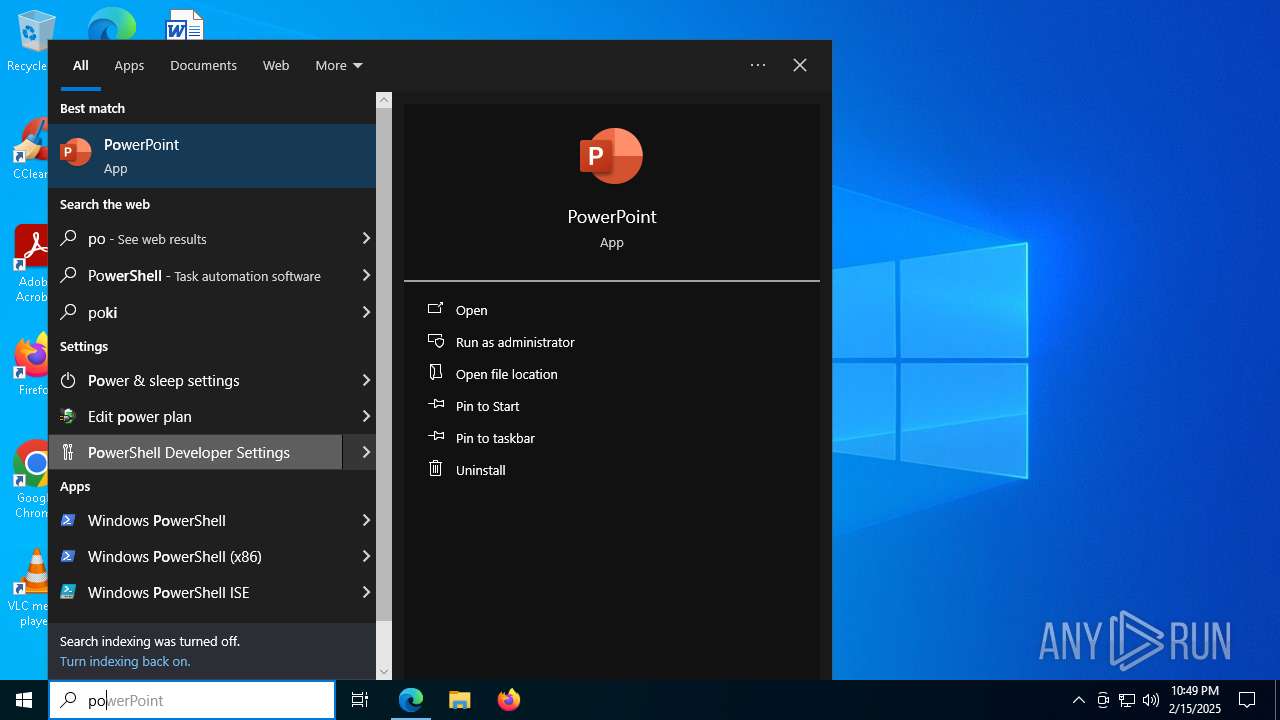
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7260)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 6412)
- cmd.exe (PID: 6452)
- powershell.exe (PID: 6904)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 4596)
- powershell.exe (PID: 8028)
- cmd.exe (PID: 6340)
- powershell.exe (PID: 7244)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7080)
- powershell.exe (PID: 3808)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7392)
- powershell.exe (PID: 364)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7620)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6500)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 2440)
- cmd.exe (PID: 6500)
Hides command output
- cmd.exe (PID: 364)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 2464)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 5836)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 7668)
- cmd.exe (PID: 7976)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 5576)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 6904)
- powershell.exe (PID: 8028)
- powershell.exe (PID: 7244)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6904)
- powershell.exe (PID: 8028)
- powershell.exe (PID: 7244)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6500)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 5836)
- cmd.exe (PID: 3680)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 6500)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6500)
INFO
Application launched itself
- msedge.exe (PID: 6224)
- msedge.exe (PID: 5444)
Checks supported languages
- identity_helper.exe (PID: 7604)
- identity_helper.exe (PID: 6944)
- mode.com (PID: 4804)
- mode.com (PID: 7540)
- mode.com (PID: 6656)
Reads Environment values
- identity_helper.exe (PID: 7604)
- identity_helper.exe (PID: 6944)
Reads the computer name
- identity_helper.exe (PID: 7604)
- identity_helper.exe (PID: 6944)
Disables trace logs
- powershell.exe (PID: 7620)
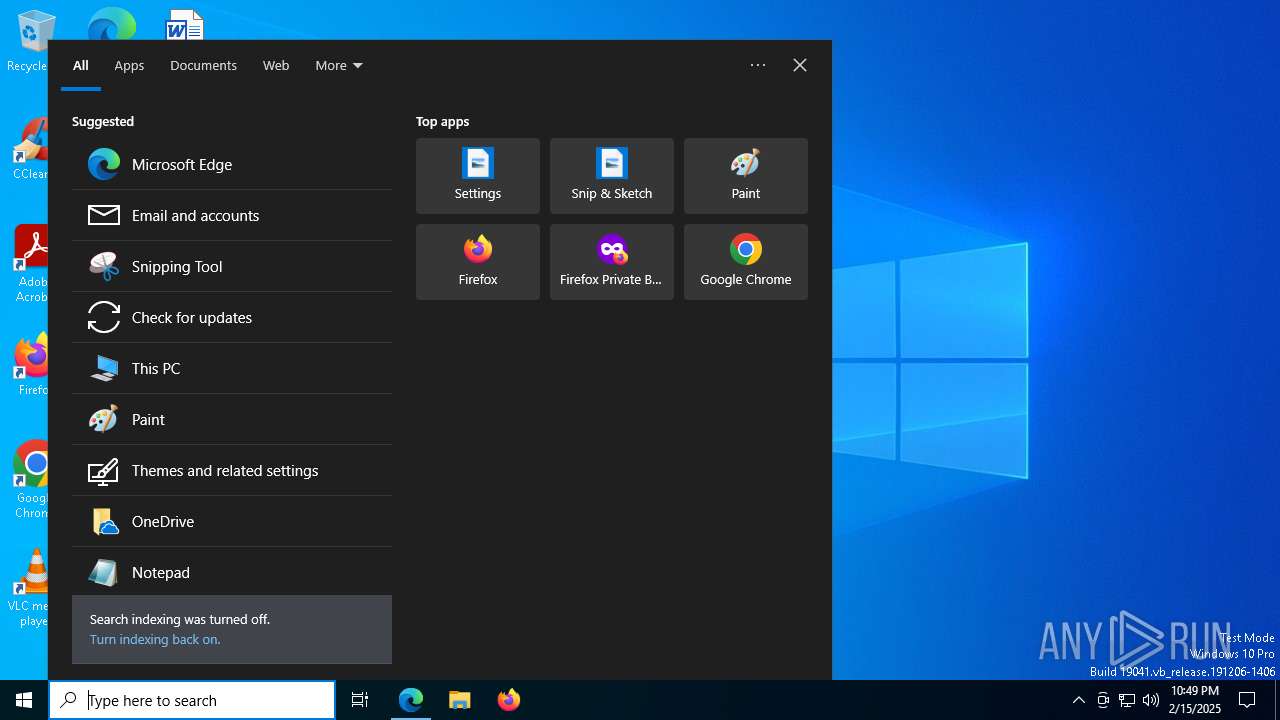
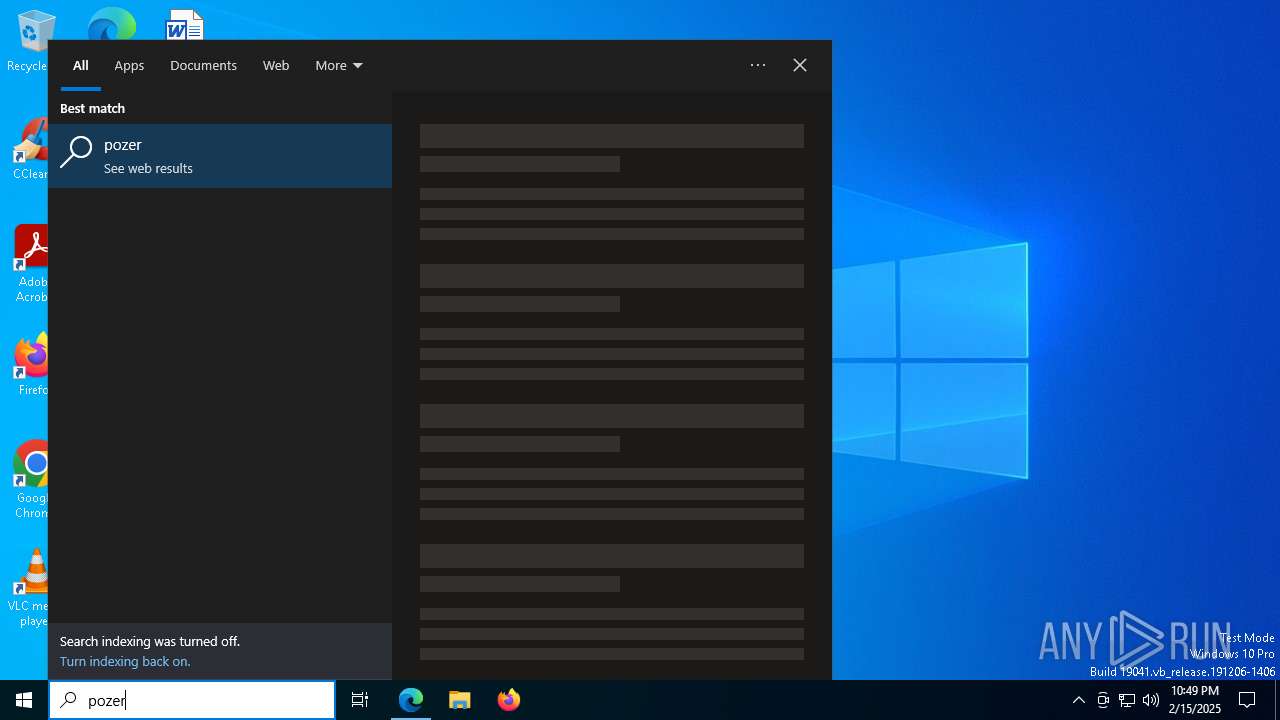
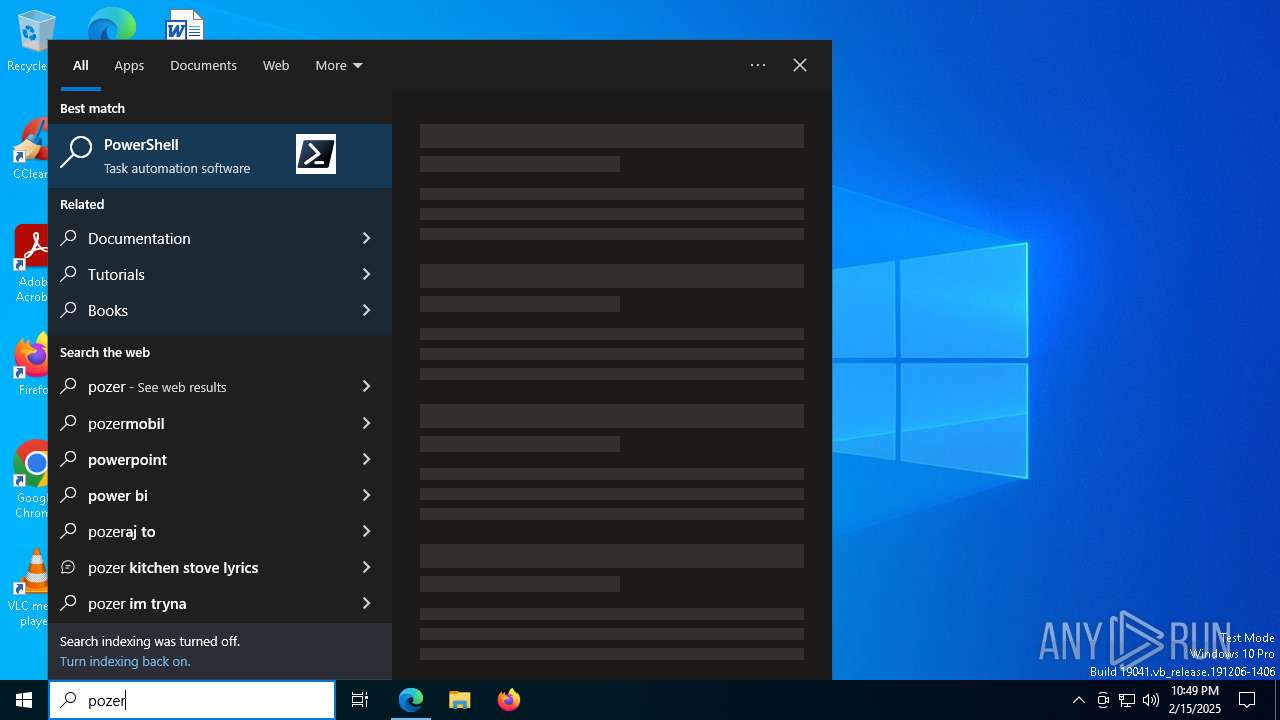
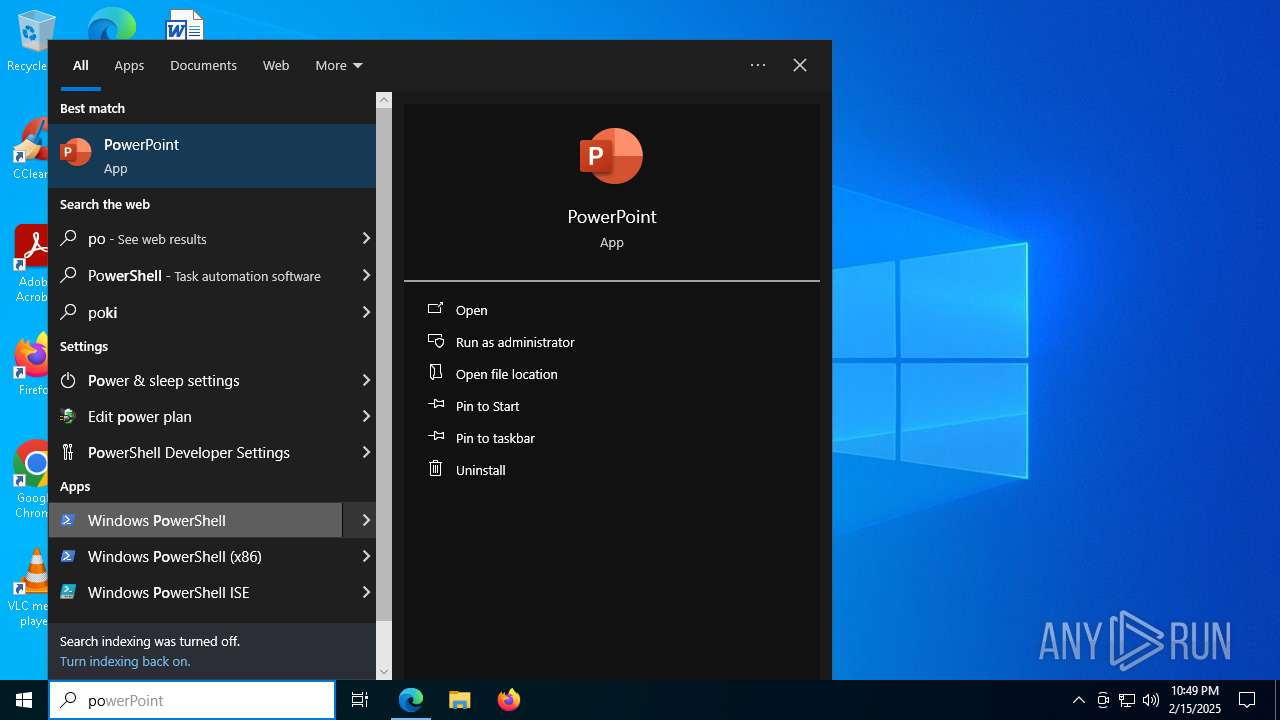
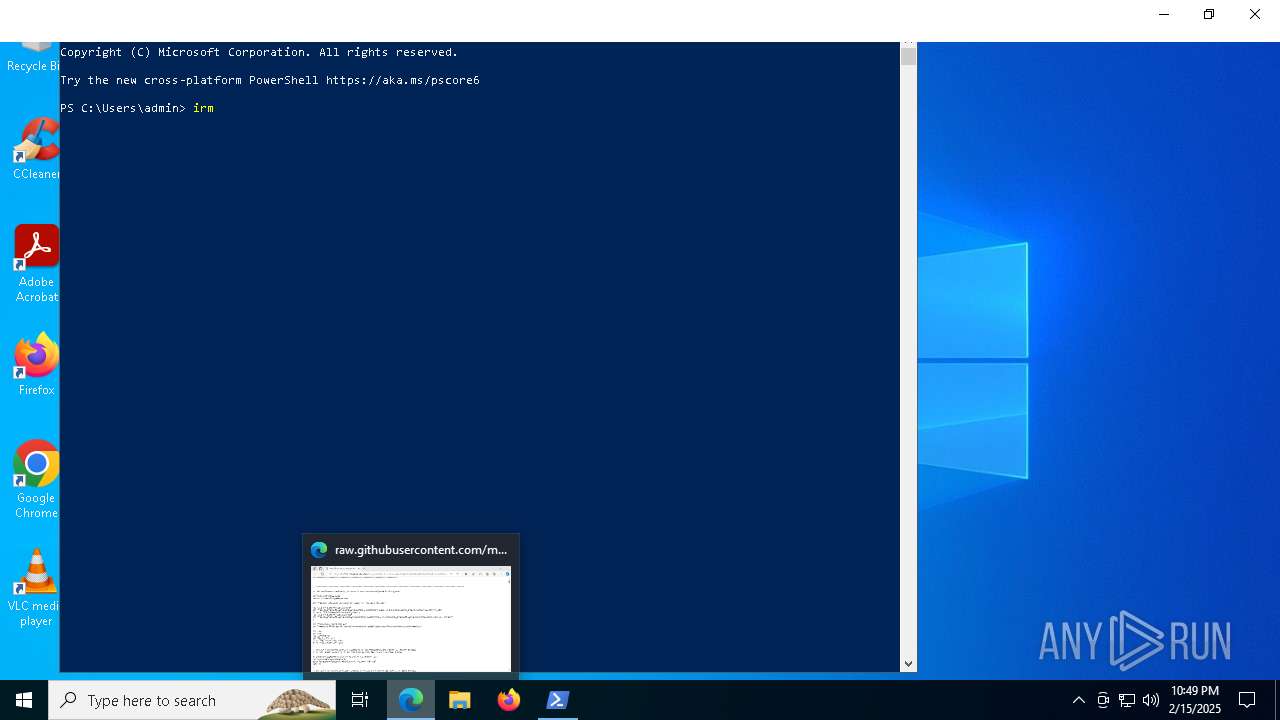
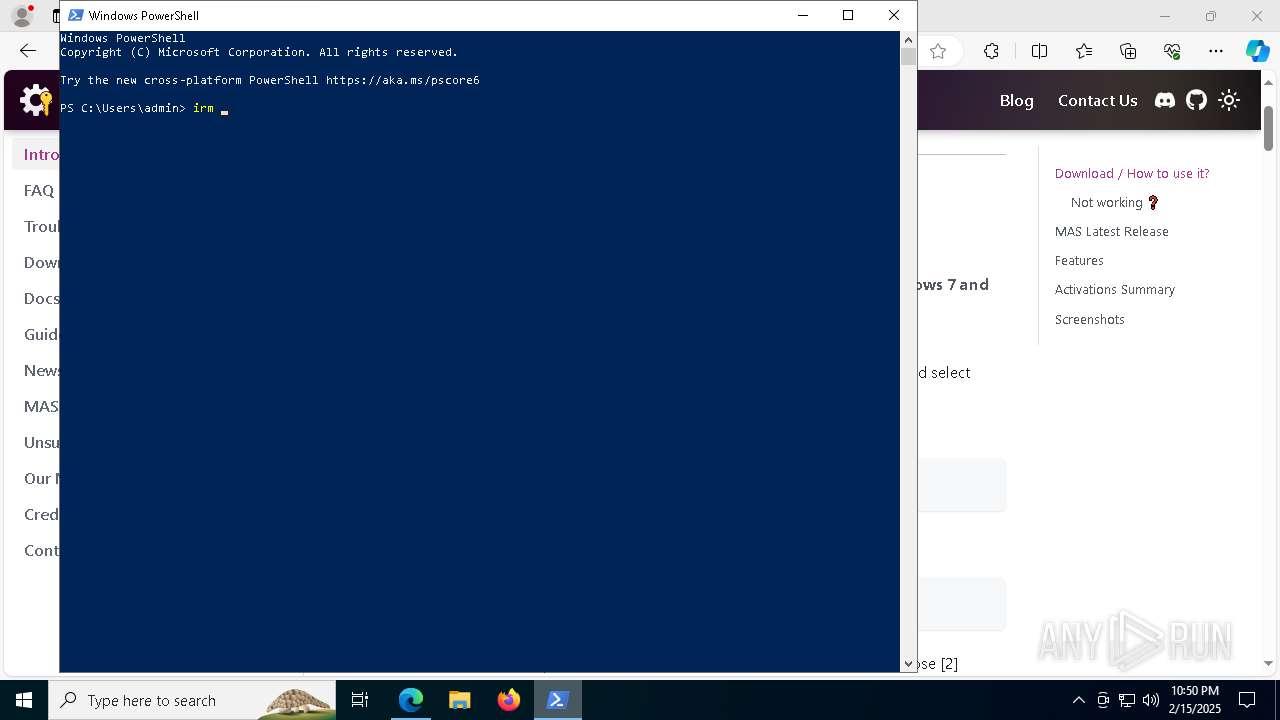
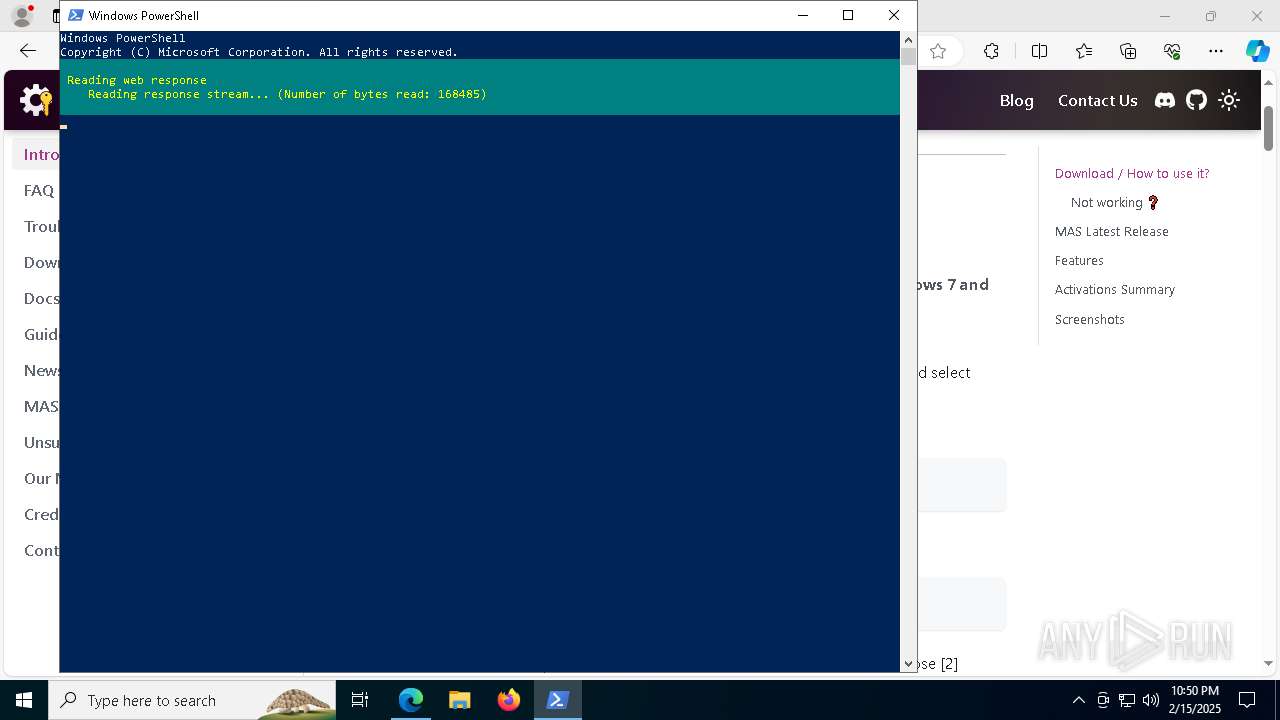
Manual execution by a user
- powershell.exe (PID: 7620)
Checks proxy server information
- powershell.exe (PID: 7620)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7620)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 7080)
- powershell.exe (PID: 3808)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7392)
Checks operating system version
- cmd.exe (PID: 3544)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 6500)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7080)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 3808)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7392)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7080)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 3808)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7392)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7080)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 3808)
- powershell.exe (PID: 1224)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7392)
Starts MODE.COM to configure console settings
- mode.com (PID: 4804)
- mode.com (PID: 7540)
- mode.com (PID: 6656)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 4540)
- WMIC.exe (PID: 6768)
- WMIC.exe (PID: 7452)
- WMIC.exe (PID: 6372)
- WMIC.exe (PID: 2428)
- WMIC.exe (PID: 2744)
- WMIC.exe (PID: 7036)
- WMIC.exe (PID: 7712)
- WMIC.exe (PID: 1144)
- WMIC.exe (PID: 6896)
- WMIC.exe (PID: 3664)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6392)
Creates files in the program directory
- cmd.exe (PID: 6500)
- ClipUp.exe (PID: 3032)
Create files in a temporary directory
- ClipUp.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
514
Monitored processes
370
Malicious processes
6
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "1056" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 364 | C:\WINDOWS\System32\cmd.exe /c reg query "HKLM\SYSTEM\CurrentControlSet\Control\ProductOptions" /v OSProductPfn 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 364 | powershell.exe [convert]::ToBase64String([Text.Encoding]::Unicode.GetBytes("""OSMajorVersion=5;OSMinorVersion=1;OSPlatformId=2;PP=0;Pfn=Microsoft.Windows.48.X19-98841_8wekyb3d8bbwe;PKeyIID=465145217131314304264339481117862266242033457260311819664735280;$([char]0)""")) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | reg query HKLM\SYSTEM\CurrentControlSet\Services\LicenseManager /v DependOnService | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v Description | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | reg query HKLM\SYSTEM\CurrentControlSet\Services\ClipSVC /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | powershell.exe "$acl = (Get-Acl 'HKLM:\SYSTEM\WPA' | fl | Out-String); if (-not ($acl -match 'NT SERVICE\\sppsvc Allow QueryValues, EnumerateSubKeys, WriteKey') -or ($acl -match 'NT SERVICE\\sppsvc Deny')) {Exit 2}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | choice /C:10 /N /M "> [1] Activate Anyway [0] Go back : " | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | find /i "4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
150 139
Read events
150 079
Write events
58
Delete events
2
Modification events
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262902 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {000134C2-2EB6-4B33-B6E2-70B5134792CE} | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 63C2E55FCC8C2F00 | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6ACAF95FCC8C2F00 | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262902 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {339E211D-9520-423C-A968-C9830DD47995} | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 291D6A60CC8C2F00 | |||
| (PID) Process: | (6224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
52
Suspicious files
1 122
Text files
257
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1379e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF137a05.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1379f6.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF137a05.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF137a05.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
140
DNS requests
160
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.135:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2744 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2744 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6776 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6564 | msedge.exe | GET | 304 | 184.30.131.245:80 | http://cacerts.digicert.com/DigiCertGlobalRootG2.crt | unknown | — | — | whitelisted |
6564 | msedge.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/certs/Microsoft%20Azure%20RSA%20TLS%20Issuing%20CA%2007%20-%20xsign.crt | unknown | — | — | whitelisted |
6164 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1740138389&P2=404&P3=2&P4=f09GzqXk%2bWi8%2f%2fHtbDmedIjMwTPxS3yPY6Kuw7KjRWCrdp3K5YDAQHtiayoWYGs3HS8nXGwzfHOK4S3%2fjzUwRA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.135:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6564 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6564 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6564 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6564 | msedge.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
6564 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6564 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6564 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |